Powerpoint Templates and Google slides for Protection From Erosion
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 AML Transaction Assessment Tool For Protecting Organizations From Frauds DK MD
AML Transaction Assessment Tool For Protecting Organizations From Frauds DK MDIntroduce your topic and host expert discussion sessions with this AML Transaction Assessment Tool For Protecting Organizations From Frauds DK MD. This template is designed using high-quality visuals, images, graphics, etc, that can be used to showcase your expertise. Different topics can be tackled using the sixteen slides included in this template. You can present each topic on a different slide to help your audience interpret the information more effectively. Apart from this, this PPT slideshow is available in two screen sizes, standard and widescreen making its delivery more impactful. This will not only help in presenting a birds-eye view of the topic but also keep your audience engaged. Since this PPT slideshow utilizes well-researched content, it induces strategic thinking and helps you convey your message in the best possible manner. The biggest feature of this design is that it comes with a host of editable features like color, font, background, etc. So, grab it now to deliver a unique presentation every time.
-
 Tips To Protect Yourself From Adware Training Ppt
Tips To Protect Yourself From Adware Training PptPresenting Tips to Protect Yourself from Adware. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Protecting Your Organizations From Cyber Risks Training Ppt
Protecting Your Organizations From Cyber Risks Training PptPresenting Protecting Your Organizations from Cyber Risks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
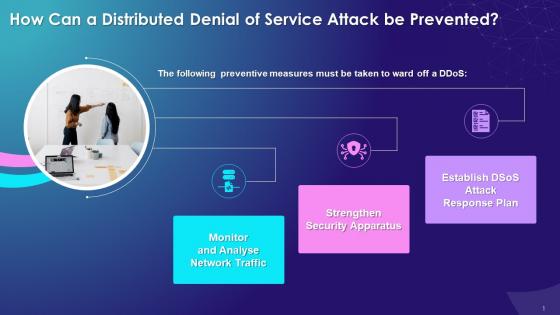 Prevention And Protection From Ddos In Blockchain Technology Training Ppt
Prevention And Protection From Ddos In Blockchain Technology Training PptPresenting Prevention and Protection from Distributed Denial of Service Attack DDoS in Blockchain Technology. Our PowerPoint experts have included all the necessary templates, designs, icons, graphs, and other essential material. This deck is well crafted by extensive research. Slides consist of amazing visuals and appropriate content. These PPT slides can be instantly downloaded with just a click. Compatible with all screen types and monitors. Supports Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
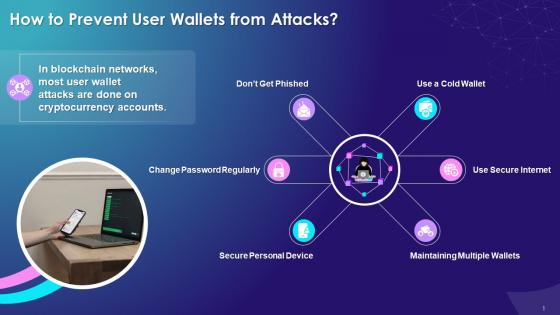 Preventive Measures To Protect Blockchain From User Wallet Attacks Training Ppt
Preventive Measures To Protect Blockchain From User Wallet Attacks Training PptPresenting Preventive Measures to Protect Blockchain from User Wallet Attacks. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
 Network Security Icon For Protecting Data From Theft
Network Security Icon For Protecting Data From TheftIntroducing our Network Security Icon For Protecting Data From Theft set of slides. The topics discussed in these slides are Network Security Protecting Data. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
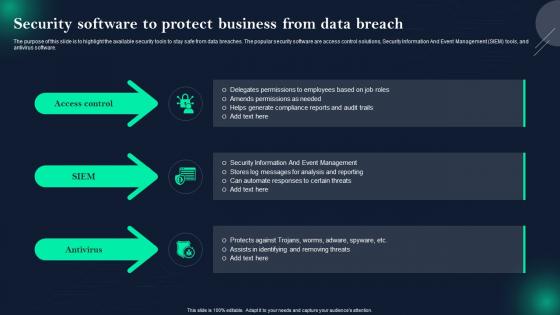 Data Breach Prevention Security Software To Protect Business From Data Breach
Data Breach Prevention Security Software To Protect Business From Data BreachThe purpose of this slide is to highlight the available security tools to stay safe from data breaches. The popular security software are access control solutions, Security Information And Event Management SIEM tools, and antivirus software. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention Security Software To Protect Business From Data Breach. This template helps you present information on three stages. You can also present information on Security Information And Event Management, Amends Permissions As Needed, Security Software To Protect Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Phishing Attacks And Strategies To Mitigate Them V2 How To Protect Users From Vishing Attacks
Phishing Attacks And Strategies To Mitigate Them V2 How To Protect Users From Vishing AttacksThis slide talks about the ways to protect users from vishing attacks. These include avoid calls from robots, never respond to audio-automated calls, verify the identity of the caller, never share personal information over the call, use multi-factor authentication, etc. Deliver an outstanding presentation on the topic using this Phishing Attacks And Strategies To Mitigate Them V2 How To Protect Users From Vishing Attacks. Dispense information and present a thorough explanation of Vishing Attacks, Audio Automated Calls, Personal Information, Multi Factor Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
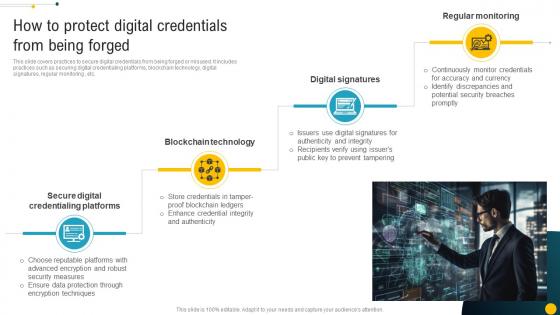 How To Protect Digital Credentials From Being Forged Blockchain Role In Education BCT SS
How To Protect Digital Credentials From Being Forged Blockchain Role In Education BCT SSThis slide covers practices to secure digital credentials from being forged or misused. It includes practices such as securing digital credentialing platforms, blockchain technology, digital signatures, regular monitoring , etc. Introducing How To Protect Digital Credentials From Being Forged Blockchain Role In Education BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Blockchain Technology, Digital Signatures, Regular Monitoring using this template. Grab it now to reap its full benefits.
-
 Techniques To Protect E Commerce Sites From Hacking
Techniques To Protect E Commerce Sites From HackingThis template presents various strategies to improve security of e commerce website. The purpose of this slide is to help online retail businesses in ensuring website security and strengthening data privacy by minimizing hacking threats. It covers techniques such as SSL monitoring, ensuring firewall safety, removing third party access, etc.Presenting our set of slides with Techniques To Protect E Commerce Sites From Hacking This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Conducting Regular, Performing Network, Ensure Chosen.
-
 Key Approaches To Protect From Honeypot Scams Hands On Blockchain Security Risk BCT SS V
Key Approaches To Protect From Honeypot Scams Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some methods to protect blockchain network users from honeypot scams and implement defensive actions. It includes elements such as no dead coins, audits, check social media, scrutinize website, etc. Increase audience engagement and knowledge by dispensing information using Key Approaches To Protect From Honeypot Scams Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Audits, Check Social Media, Scrutinize Website using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
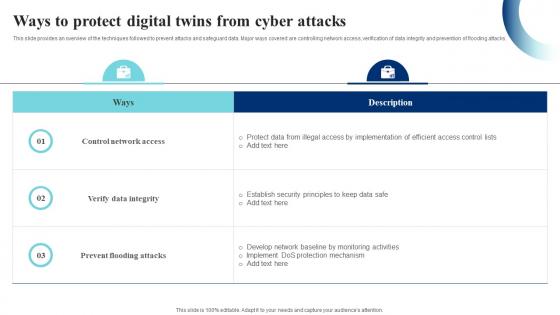 Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SS
Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SSThis slide provides an overview of the techniques followed to prevent attacks and safeguard data. Major ways covered are controlling network access, verification of data integrity and prevention of flooding attacks. Present the topic in a bit more detail with this Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SS. Use it as a tool for discussion and navigation on Control Network Access, Prevent Flooding Attacks, Verify Data Integrity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
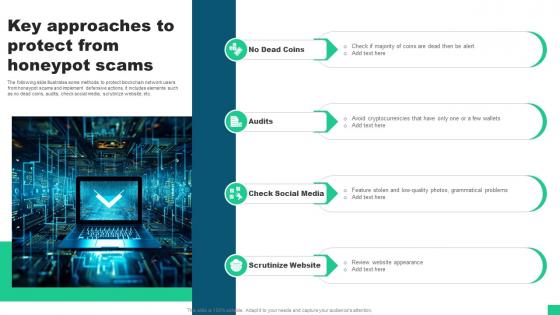 Key Approaches To Protect From Honeypot Scams Guide For Blockchain BCT SS V
Key Approaches To Protect From Honeypot Scams Guide For Blockchain BCT SS VThe following slide illustrates some methods to protect blockchain network users from honeypot scams and implement defensive actions. It includes elements such as no dead coins, audits, check social media, scrutinize website, etc. Increase audience engagement and knowledge by dispensing information using Key Approaches To Protect From Honeypot Scams Guide For Blockchain BCT SS V This template helps you present information on four stages. You can also present information on Audits, Check Social Media, Scrutinize Website using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
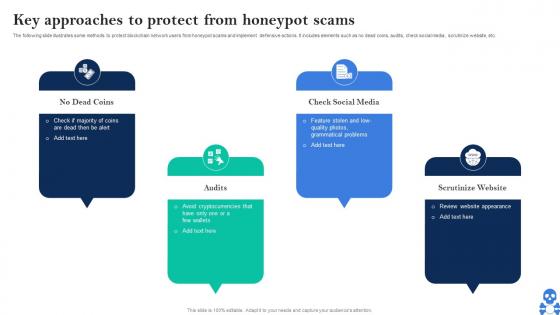 Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS V
Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS VThe following slide illustrates some methods to protect blockchain network users from honeypot scams and implement defensive actions. It includes elements such as no dead coins, audits, check social media, scrutinize website, etc. Introducing Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on No Dead Coins, Check Social Media, Scrutinize Website using this template. Grab it now to reap its full benefits.
-
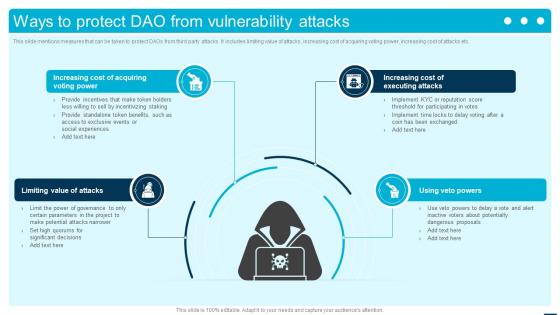 Ways To Protect DAO From Vulnerability Attacks Introduction To Decentralized Autonomous BCT SS
Ways To Protect DAO From Vulnerability Attacks Introduction To Decentralized Autonomous BCT SSThis slide mentions measures that can be taken to protect DAOs from third party attacks. It includes limiting value of attacks, increasing cost of acquiring voting power, increasing cost of attacks etc. Introducing Ways To Protect DAO From Vulnerability Attacks Introduction To Decentralized Autonomous BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Limiting Value Of Attacks, Increasing Cost Of Acquiring Voting Power, Increasing Cost Of Executing Attacks, using this template. Grab it now to reap its full benefits.
-
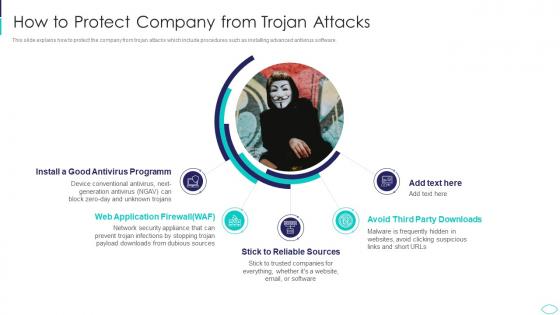 How To Protect Company From Trojan Attacks Cyber Terrorism Attacks
How To Protect Company From Trojan Attacks Cyber Terrorism AttacksThis slide explains how to protect the company from trojan attacks which include procedures such as installing advanced antivirus software. Increase audience engagement and knowledge by dispensing information using How To Protect Company From Trojan Attacks Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Antivirus Programm, Application Firewall, Reliable Sources, Avoid Third Party Downloads using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Techniques To Protect SCADA Systems From Cyber Terrorism Attacks
Techniques To Protect SCADA Systems From Cyber Terrorism AttacksThis slide depicts the techniques to protect SCADA from cyber attacks which include security training of employees, strict firewalls. Increase audience engagement and knowledge by dispensing information using Techniques To Protect SCADA Systems From Cyber Terrorism Attacks. This template helps you present information on six stages. You can also present information on Security Training, Access Controls, Strict Firewalls, Security Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
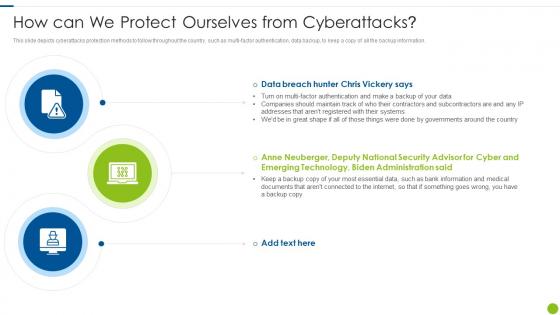 Cyber Attacks On Ukraine How Can We Protect Ourselves From Cyberattacks
Cyber Attacks On Ukraine How Can We Protect Ourselves From CyberattacksThis slide depicts cyberattacks protection methods to follow throughout the country, such as multi factor authentication, data backup, to keep a copy of all the backup information. Introducing Cyber Attacks On Ukraine How Can We Protect Ourselves From Cyberattacks to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on How Can We Protect Ourselves From Cyberattacks, using this template. Grab it now to reap its full benefits.
-
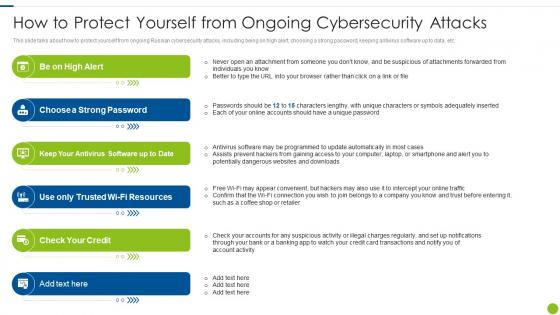 Cyber Attacks On Ukraine How To Protect Yourself From Ongoing Cybersecurity
Cyber Attacks On Ukraine How To Protect Yourself From Ongoing CybersecurityThis slide talks about how to protect yourself from ongoing Russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Increase audience engagement and knowledge by dispensing information using Cyber Attacks On Ukraine How To Protect Yourself From Ongoing Cybersecurity. This template helps you present information on six stages. You can also present information on Suspicious, Individuals, Adequately, Programmed using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Wiper Malware Attack How Can We Protect Ourselves From Cyberattacks
Wiper Malware Attack How Can We Protect Ourselves From CyberattacksThis slide depicts cyberattacks protection methods to follow throughout the country, such as multi factor authentication, data backup, to keep a copy of all the backup information. Introducing Wiper Malware Attack How Can We Protect Ourselves From Cyberattacks to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Security, Administration, Authentication, using this template. Grab it now to reap its full benefits.
-
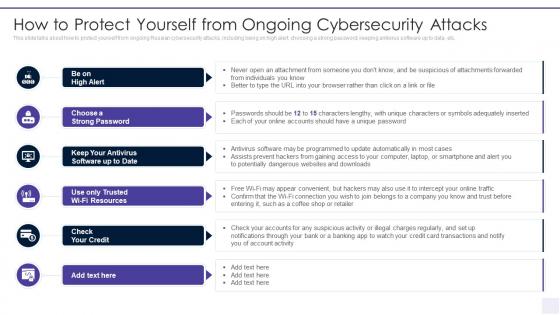 Wiper Malware Attack How To Protect Yourself From Ongoing
Wiper Malware Attack How To Protect Yourself From OngoingThis slide talks about how to protect yourself from ongoing Russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack How To Protect Yourself From Ongoing. This template helps you present information on six stages. You can also present information on Convenient, Connection, Intercept, Notifications, Transactions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
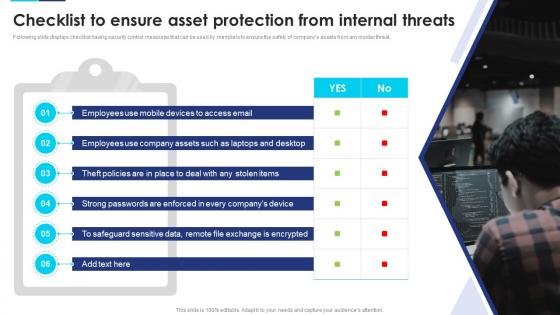 Incident Response Playbook Checklist To Ensure Asset Protection From Internal Threats
Incident Response Playbook Checklist To Ensure Asset Protection From Internal ThreatsFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Introducing Incident Response Playbook Checklist To Ensure Asset Protection From Internal Threats to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Mobile Devices, Company Assets, Employees, using this template. Grab it now to reap its full benefits.
-
 Protection From Hacker Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Protection From Hacker Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Protection from hacker colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Protection From Hacker Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Protection From Hacker Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Protection from hacker monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 How can we protect ourselves from cyberattacks ukraine and russia cyber warfare it
How can we protect ourselves from cyberattacks ukraine and russia cyber warfare itThis slide depicts cyberattacks protection methods to follow throughout the country, such as multi factor authentication, data backup, to keep a copy of all the backup information. Increase audience engagement and knowledge by dispensing information using How Can We Protect Ourselves From Cyberattacks Ukraine And Russia Cyber Warfare It. This template helps you present information on three stages. You can also present information on How CAN We Protect Ourselves FROM Cyberattacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ukraine and russia cyber warfare it how to protect yourself from ongoing cybersecurity attacks
Ukraine and russia cyber warfare it how to protect yourself from ongoing cybersecurity attacksThis slide talks about how to protect yourself from ongoing Russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Introducing Ukraine And Russia Cyber Warfare It How To Protect Yourself From Ongoing Cybersecurity Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Resources, Antivirus, Software, using this template. Grab it now to reap its full benefits.
-
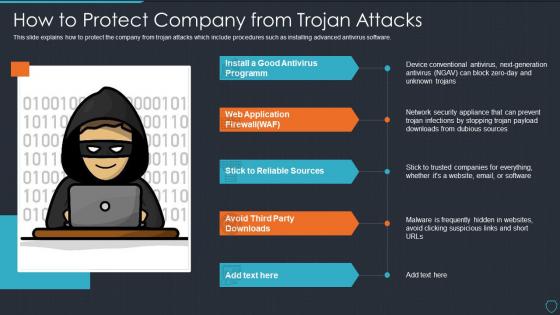 Cyberterrorism it how to protect company from trojan attacks
Cyberterrorism it how to protect company from trojan attacksThis slide explains how to protect the company from trojan attacks which include procedures such as installing advanced antivirus software. Deliver an outstanding presentation on the topic using this Cyberterrorism IT How To Protect Company From Trojan Attacks. Dispense information and present a thorough explanation of Install Good Antivirus Programm, Web Application Firewall, Stick To Reliable Sources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
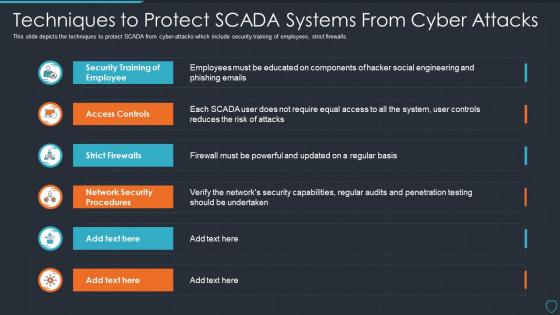 Cyberterrorism it techniques to protect scada systems from cyber attacks
Cyberterrorism it techniques to protect scada systems from cyber attacksThis slide depicts the techniques to protect SCADA from cyber-attacks which include security training of employees, strict firewalls. Deliver an outstanding presentation on the topic using this Cyberterrorism IT Techniques To Protect SCADA Systems From Cyber Attacks. Dispense information and present a thorough explanation of Security Training, Employee, Access Controls, Strict Firewalls, Network Security Procedures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Protect bank account from hackers ppt powerpoint presentation slides slideshow cpb
Protect bank account from hackers ppt powerpoint presentation slides slideshow cpbPresenting Protect Bank Account From Hackers Ppt Powerpoint Presentation Slides Slideshow Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Protect Bank Account From Hackers. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
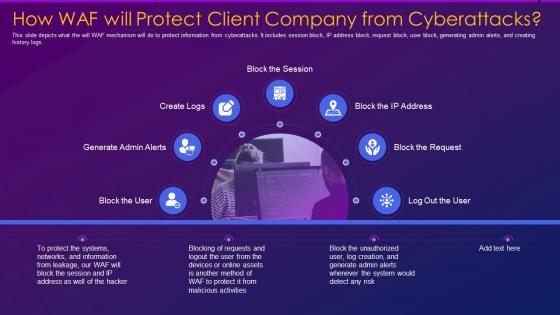 Web application firewall waf how waf will protect client company from cyberattacks
Web application firewall waf how waf will protect client company from cyberattacksThis slide depicts what the will WAF mechanism will do to protect information from cyberattacks. It includes session block, IP address block, request block, user block, generating admin alerts, and creating history logs. Introducing Web Application Firewall Waf How Waf Will Protect Client Company From Cyberattacks to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Information, Cyberattacks, Unauthorized, using this template. Grab it now to reap its full benefits.
-
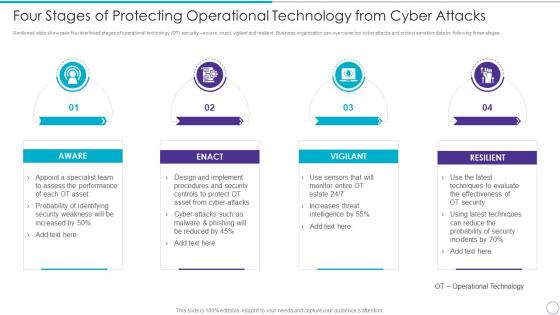 Four Stages Of Protecting Operational Technology From Cyber Attacks
Four Stages Of Protecting Operational Technology From Cyber AttacksMentioned slide showcase four interlinked stages of operational technology OT security aware, enact, vigilant and resilient. Business organization can overcome top cyber attacks and protect sensitive data by following these stages. Increase audience engagement and knowledge by dispensing information using four Stages Of Protecting Operational Technology From Cyber Attacks. This template helps you present information on four stages. You can also present information on Aware, Enact, Vigilant, Resilient using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Checklist To Ensure Asset Protection From Internal Upgrading Cybersecurity With Incident Response Playbook
Checklist To Ensure Asset Protection From Internal Upgrading Cybersecurity With Incident Response PlaybookFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Present the topic in a bit more detail with this Checklist To Ensure Asset Protection From Internal Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Protection, Measures, Ensure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
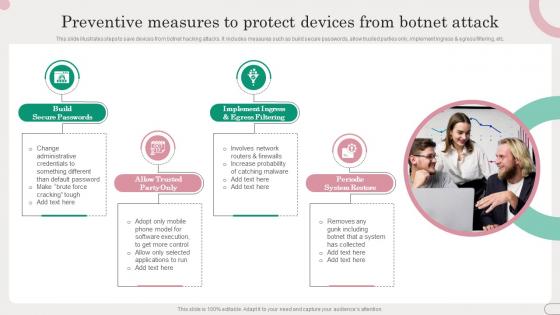 Preventive Measures To Protect Devices From Botnet Attack
Preventive Measures To Protect Devices From Botnet AttackThis slide illustrates steps to save devices from botnet hacking attacks. It includes measures such as build secure passwords, allow trusted parties only, implement ingress and egress filtering, etc. Introducing our premium set of slides with Preventive Measures To Protect Devices From Botnet Attack. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Build Secure Passwords, Periodic System Restore. So download instantly and tailor it with your information.
-
 Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability
Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And VulnerabilityFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Introducing Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Email, Mobile Devices, using this template. Grab it now to reap its full benefits.
-
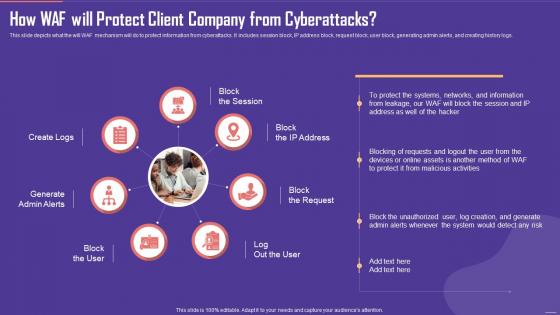 Application Firewall How WAF will Protect Client Company from Cyberattacks
Application Firewall How WAF will Protect Client Company from CyberattacksThis slide depicts what the will WAF mechanism will do to protect information from cyberattacks. It includes session block, IP address block, request block, user block, generating admin alerts, and creating history logs. Introducing Application Firewall How WAF will Protect Client Company from Cyberattacks to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Client Company, Cyberattacks, using this template. Grab it now to reap its full benefits.
-
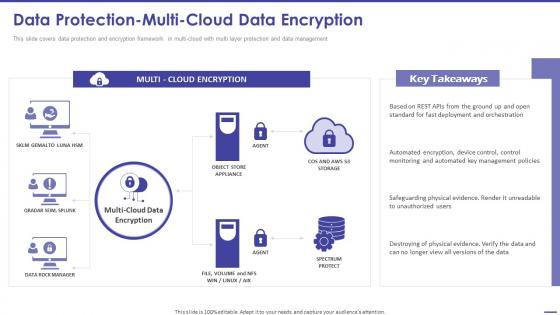 Todays Challenge Remove Complexity From Multi Cloud Data Protection Multi Cloud Data Encryption
Todays Challenge Remove Complexity From Multi Cloud Data Protection Multi Cloud Data EncryptionThis slide covers data protection and encryption framework in multi cloud with multi layer protection and data management. Present the topic in a bit more detail with this Todays Challenge Remove Complexity From Multi Cloud Data Protection Multi Cloud Data Encryption. Use it as a tool for discussion and navigation on Deployment And Orchestration, Management Policies, Unauthorized Users. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
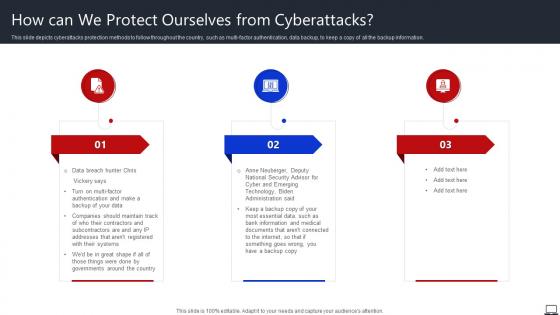 How Can We Protect Ourselves From Cyberattacks String Of Cyber Attacks Against
How Can We Protect Ourselves From Cyberattacks String Of Cyber Attacks AgainstThis slide depicts cyberattacks protection methods to follow throughout the country, such as multi factor authentication, data backup, to keep a copy of all the backup information. Increase audience engagement and knowledge by dispensing information using How Can We Protect Ourselves From Cyberattacks String Of Cyber Attacks Against. This template helps you present information on three stages. You can also present information on Governments, Backup Copy, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
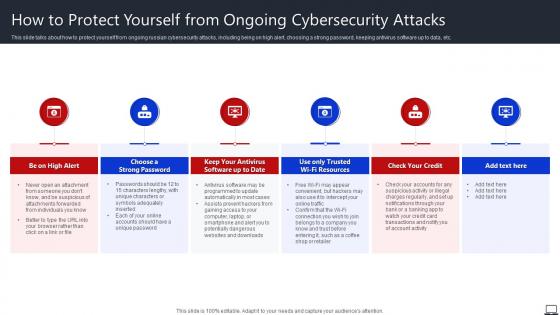 How To Protect Yourself From Ongoing Cybersecurity Attacks String Of Cyber Attacks
How To Protect Yourself From Ongoing Cybersecurity Attacks String Of Cyber AttacksThis slide talks about how to protect yourself from ongoing russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Introducing How To Protect Yourself From Ongoing Cybersecurity Attacks String Of Cyber Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Choose A Strong Password, Check Your Credit, Unique Password, using this template. Grab it now to reap its full benefits.
-
 Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook
Checklist To Ensure Asset Protection From Internal Threats Security Incident Response PlaybookFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Deliver an outstanding presentation on the topic using this Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook. Dispense information and present a thorough explanation of Protection, Measures, Ensure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents AML Transaction Assessment Tool For Protecting Organizations From Frauds
Table Of Contents AML Transaction Assessment Tool For Protecting Organizations From FraudsPresent the topic in a bit more detail with this Table Of Contents AML Transaction Assessment Tool For Protecting Organizations From Frauds. Use it as a tool for discussion and navigation on Transactions Profiles, Blockchain Technology, Transactions Alerts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
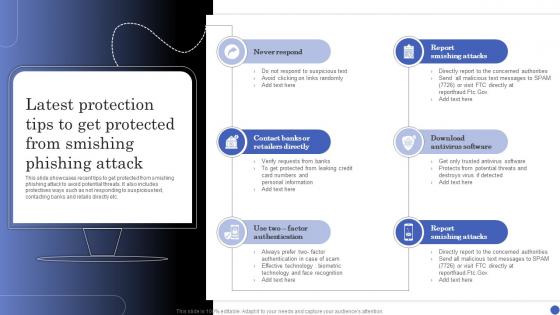 Latest Protection Tips To Get Protected From Smishing Phishing Attack
Latest Protection Tips To Get Protected From Smishing Phishing AttackThis slide showcases recent tips to get protected from smishing phishing attack to avoid potential threats. It also includes protectives ways such as not responding to suspicious text, contacting banks and retails directly etc. Presenting our set of slides with Latest Protection Tips To Get Protected From Smishing Phishing Attack. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Retailers Directly, Antivirus Software, Factor Authentication.
-
 Protect From Heat Resistant Materials Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Protect From Heat Resistant Materials Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis powerpoint icon is an illustration of a shield protecting from heat and radiation. It is coloured in a bright yellow and orange to represent the warmth and energy of the heat and radiation. It is perfect for presentations on safety, protection, and the environment.
-
 Protect From Heat Resistant Materials Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Protect From Heat Resistant Materials Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for protecting from heat and radiation. It features a black and white design with a shield like shape, making it a great visual representation of protection. Ideal for presentations, documents, and other projects.
-
 Simple Ways To Protect Oneself From Identity Fraud
Simple Ways To Protect Oneself From Identity FraudThis slide showcases approaches for protecting identity theft. This template focuses on applying different strategies which eliminate or reduce any chances of fraud occurrence. It includes information related to securing hard copies, setting strong passwords, etc.Introducing our premium set of slides with Simple Ways To Protect Oneself From Identity Fraud. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Anti Spyware Program, Hardware Hackers, Remember Password. So download instantly and tailor it with your information.
-
 Ultimate Guide For Blockchain Key Approaches To Protect From Honeypot Scams BCT SS
Ultimate Guide For Blockchain Key Approaches To Protect From Honeypot Scams BCT SSIntroducing Ultimate Guide For Blockchain Key Approaches To Protect From Honeypot Scams BCT SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Scrutinize Website, Check Social Media, Audits, No Dead Coins using this template. Grab it now to reap its full benefits.
-
 How To Protect Users From Vishing Attacks Phishing Attacks And Strategies
How To Protect Users From Vishing Attacks Phishing Attacks And StrategiesThis slide talks about the ways to protect users from vishing attacks. These include avoid calls from robots, never respond to audio automated calls, verify the identity of the caller, never share personal information over the call, use multi factor authentication, etc.Present the topic in a bit more detail with this How To Protect Users From Vishing Attacks Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Multi Factor Authentication, Employees Family, Government Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Protect From Heat And Radiation Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Protect From Heat And Radiation Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis powerpoint icon is an illustration of a shield protecting from heat and radiation. It is coloured in a bright yellow and orange to represent the warmth and energy of the heat and radiation. It is perfect for presentations on safety, protection, and the environment.
-
 Protect From Heat And Radiation Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Protect From Heat And Radiation Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for protecting from heat and radiation. It features a black and white design with a shield-like shape, making it a great visual representation of protection. Ideal for presentations, documents, and other projects.
-
 Protect From Heat Shielding Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Protect From Heat Shielding Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis powerpoint icon is an illustration of a shield protecting from heat and radiation. It is coloured in a bright yellow and orange to represent the warmth and energy of the heat and radiation. It is perfect for presentations on safety, protection, and the environment.
-
 Protect From Heat Shielding Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Protect From Heat Shielding Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for protecting from heat and radiation. It features a black and white design with a shield-like shape, making it a great visual representation of protection. Ideal for presentations, documents, and other projects.
-
 Protection from cyber attacks ppt slide examples
Protection from cyber attacks ppt slide examplesPresenting protection from cyber attacks ppt slides examples PPT slide. The tension-free download is possible. Once downloaded, the presentation can be modified to any format like JPG, JPEG, PDF, etc. It’s also compatible with multiple software and Google Slides. The provided executive summary PPT presentation template can easily be used solely or as part of your pre-built presentation. Be happy to customize and personalize the presentation with company specifications.There is no hassle when any facts, figures or text is to be included or excluded in the presentation. Picture quality compatible with widescreen exposure.
-
 Umbrella with protection from sun
Umbrella with protection from sunPresenting umbrella with protection from sun. This is a umbrella with protection from sun. This is a three stage process. The stages in this process are umbrella icon, parasol icon, sunshade icon.
-
 Biological hazard showing protection mask from gas protection
Biological hazard showing protection mask from gas protectionPresenting biological hazard showing protection mask from gas protection presentation design. PPT slide can be expected in standard and widescreen view. Customize the PowerPoint design with company assets. Stunning picture quality as pixels doesn’t break even on large screen. Similar designs are available with different nodes and stages. PowerPoint diagram goes well with Google slides and can be merged accordingly. Easy to download and share into other format such as JPEG and PDF.
-
 Hands protecting earth from global warming effect
Hands protecting earth from global warming effectPresenting this set of slides with name Hands Protecting Earth From Global Warming Effect. The topics discussed in these slide is Hands Protecting Earth From Global Warming Effect. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Firewall for network protection from external threats icon
Firewall for network protection from external threats iconPresenting this set of slides with name Firewall For Network Protection From External Threats Icon. This is a three stage process. The stages in this process are Firewall For Network Protection From External Threats Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Vaccination icon for children health to protect from illness
Vaccination icon for children health to protect from illnessPresenting this set of slides with name Vaccination Icon For Children Health To Protect From Illness. This is a three stage process. The stages in this process are Vaccination Icon For Children Health To Protect From Illness. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Prohibited sign indicating shield protection from virus
Prohibited sign indicating shield protection from virusPresenting this set of slides with name Prohibited Sign Indicating Shield Protection From Virus. The topics discussed in these slides are Prohibited Sign Indicating Shield Protection From Virus. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Icon of laptop protected with security software from cyber threat
Icon of laptop protected with security software from cyber threatPresenting this set of slides with name Icon Of Laptop Protected With Security Software From Cyber Threat. This is a three stage process. The stages in this process are Icon Of Laptop Protected With Security Software From Cyber Threat. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
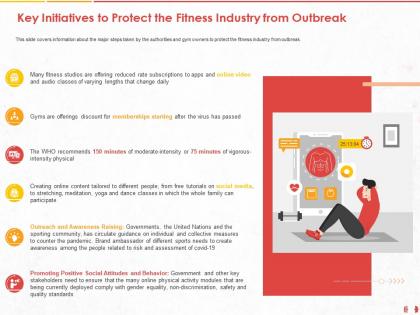 Key initiatives to protect the fitness industry from outbreak m1018 ppt powerpoint presentation show
Key initiatives to protect the fitness industry from outbreak m1018 ppt powerpoint presentation showThis slide covers information about the major steps taken by the authorities and gym owners to protect the fitness industry from outbreak. Presenting this set of slides with name Key Initiatives To Protect The Fitness Industry From Outbreak M1018 Ppt Powerpoint Presentation Show. The topics discussed in these slides are Social Media, Risk, Brand. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Key guidelines to protect from covid 19 parks and recreational facilities visit ppt powerpoint slides picture
Key guidelines to protect from covid 19 parks and recreational facilities visit ppt powerpoint slides pictureThe slides shows the guidelines Dos and Donts to get the protection from coronavirus impact while visiting parks or recreational facilities. Presenting this set of slides with name Key Guidelines To Protect From COVID 19 Parks And Recreational Facilities Visit Ppt Powerpoint Slides Picture. The topics discussed in these slides are Services, Facilities, Social Distancing. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.


