Powerpoint Templates and Google slides for Cyber Data Security Icon For Fraud Risk Management
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
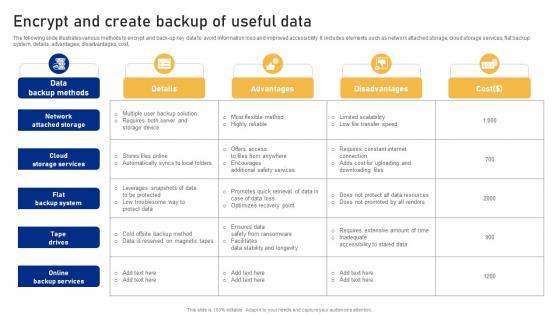 Encrypt And Create Backup Of Useful Data Cyber Risk Assessment
Encrypt And Create Backup Of Useful Data Cyber Risk AssessmentThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Cyber Risk Assessment Dispense information and present a thorough explanation of Network Attached, Backup System, Backup Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
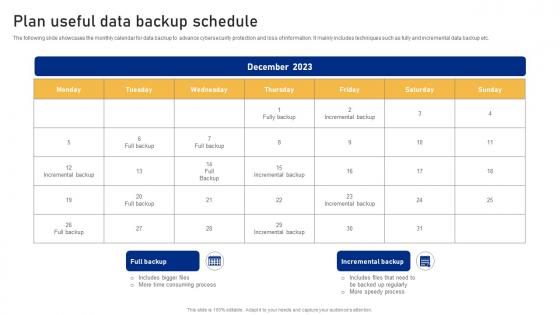 Plan Useful Data Backup Schedule Cyber Risk Assessment
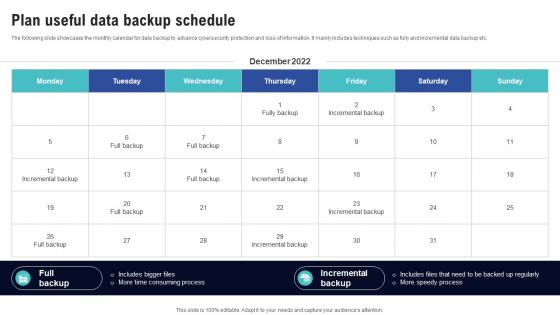
Plan Useful Data Backup Schedule Cyber Risk AssessmentThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Deliver an outstanding presentation on the topic using this Plan Useful Data Backup Schedule Cyber Risk Assessment Dispense information and present a thorough explanation of Plan Useful, Data Backup Schedule using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloning In Cyber Security For Data Protection
Cloning In Cyber Security For Data ProtectionThis slide shows benefits of cloning for cyber protection. It aims to prevent cloning security risks to mitigate unauthorized access to technical assets. It covers four cyber security measures such as data protection, integrity, loss prevention and transfers. Presenting our set of slides with name Cloning In Cyber Security For Data Protection. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Data Integrity, Data Transfers.
-
 Cyber Security Policy Icon For Data Theft Prevention
Cyber Security Policy Icon For Data Theft PreventionIntroducing our Cyber Security Policy Icon For Data Theft Prevention set of slides. The topics discussed in these slides are Cyber Security Policy, Icon For Data Theft Prevention. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS VThis slide covers techniques to secure customers confidential data through several cyber security strategies. The purpose for this template is to provide an overview on important elements of top techniques deployed by the company . It includes strategies such as people, process, data and technology and regulatory. Introducing Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on People, Process, Regulatory, using this template. Grab it now to reap its full benefits.
-
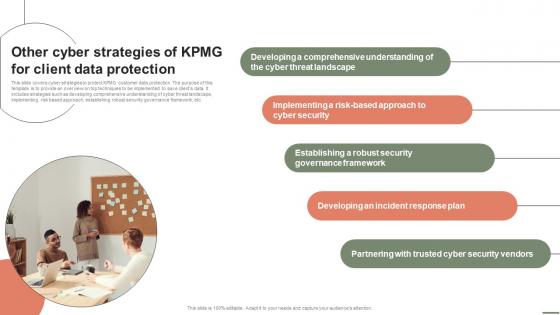 Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS VThis slide covers cyber strategies to protect KPMG customer data protection. The purpose of this template is to provide an overview on top techniques to be implemented to save clients data. It includes strategies such as developing comprehensive understanding of cyber threat landscape, implementing risk based approach, establishing robust security governance framework, etc. Increase audience engagement and knowledge by dispensing information using Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V. This template helps you present information on five stages. You can also present information on Threat Landscape, Cyber Security, Governance Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Highlighting Cyber Security Unawareness Among Employees Creating Cyber Security Awareness
Data Highlighting Cyber Security Unawareness Among Employees Creating Cyber Security AwarenessThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Increase audience engagement and knowledge by dispensing information using Data Highlighting Cyber Security Unawareness Among Employees Creating Cyber Security Awareness This template helps you present information on Five stages. You can also present information on Future Goal Analysis, Business Unit, Risk Category using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
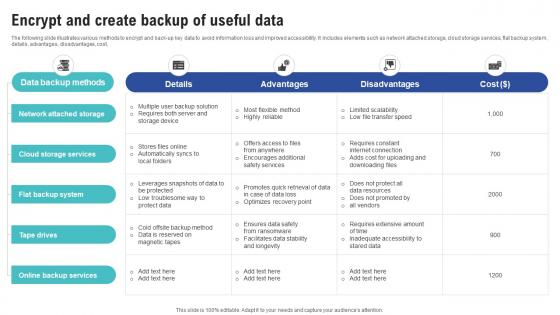 Encrypt And Create Backup Of Useful Data Creating Cyber Security Awareness
Encrypt And Create Backup Of Useful Data Creating Cyber Security AwarenessThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost,. Present the topic in a bit more detail with this Encrypt And Create Backup Of Useful Data Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Accountable, Consulted, Responsible This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Plan Useful Data Backup Schedule Creating Cyber Security Awareness
Plan Useful Data Backup Schedule Creating Cyber Security AwarenessThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Deliver an outstanding presentation on the topic using this Plan Useful Data Backup Schedule Creating Cyber Security Awareness Dispense information and present a thorough explanation of Security And Privacy, Web Application Security, Infrastructure Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Icon For Insurancing Data Breaches
Cyber Security Icon For Insurancing Data BreachesPresenting our set of slides with Cyber Security Icon For Insurancing Data Breaches. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Icon, Insurancing Data Breaches.
-
 Online Data Cyber Security Services
Online Data Cyber Security ServicesThis slide showcases data cyber security services that protect personal data and help to preserve reputation. It includes elements such as firewall, antivirus, email filtering, device control and content filtering. Presenting our set of slides with Online Data Cyber Security Services. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Firewall, Antivirus, Device Control.
-
 Big Data Analytics Cyber Protection Tools
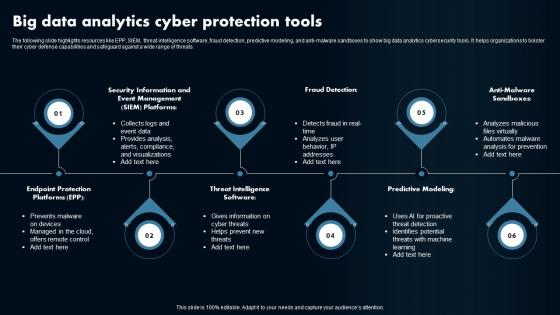
Big Data Analytics Cyber Protection ToolsThe following slide highlights resources like EPP, SIEM, threat intelligence software, fraud detection, predictive modeling, and anti-malware sandboxes to show big data analytics cybersecurity tools. It helps organizations to bolster their cyber defense capabilities and safeguard against a wide range of threats. Presenting our set of slides with Big Data Analytics Cyber Protection Tools. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Fraud Detection, Predictive Modeling, Anti-Malware Sandboxes.
-
 Implementation Stats Of Big Data Analytics For Cyber Protection
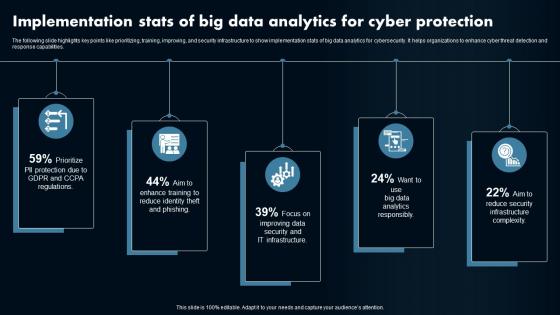
Implementation Stats Of Big Data Analytics For Cyber ProtectionThe following slide highlights key points like prioritizing, training, improving, and security infrastructure to show implementation stats of big data analytics for cybersecurity. It helps organizations to enhance cyber threat detection and response capabilities. Presenting our set of slides with Implementation Stats Of Big Data Analytics For Cyber Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Data Analytics, Cybersecurity.
-
 Strategies For Big Data Cyber Protection Analytics
Strategies For Big Data Cyber Protection AnalyticsThe following slide highlights key points like data collection, data normalization, expansion, enrichment, automation, standardization, and advanced detection to show strategies for big data analytics cybersecurity. It helps organizations to proactively defend against cyber threats and enhance overall security posture. Introducing our premium set of slides with Strategies For Big Data Cyber Protection Analytics. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Collection, Data Normalization, Expansion. So download instantly and tailor it with your information.
-
 Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V
Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Automated Backup, Track Backup using this template. Grab it now to reap its full benefits.
-
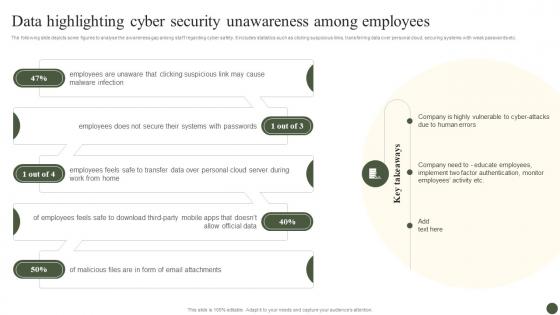 Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process
Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management ProcessThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Increase audience engagement and knowledge by dispensing information using Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process. This template helps you present information on five stages. You can also present information on Malware Infection, Systems With Passwords, Employees Feels, Allow Official Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
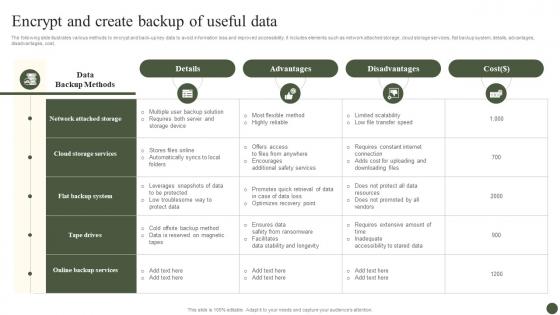 Encrypt And Create Backup Of Useful Data Implementing Cyber Risk Management Process
Encrypt And Create Backup Of Useful Data Implementing Cyber Risk Management ProcessThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost. Present the topic in a bit more detail with this Encrypt And Create Backup Of Useful Data Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Details, Advantages, Disadvantages. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Plan Useful Data Backup Schedule Implementing Cyber Risk Management Process
Plan Useful Data Backup Schedule Implementing Cyber Risk Management ProcessThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Deliver an outstanding presentation on the topic using this Plan Useful Data Backup Schedule Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Monday, Tuesday, Wednesday, Thursday using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Encryption And Authentication In Automotive Cyber Security
Data Encryption And Authentication In Automotive Cyber SecurityThis slide highlights data privacy and encryption in automotive cybersecurity. The purpose of this slide is to aid organizations in implementing measures for securing sensitive data from possible manipulation. It includes various measures for authentication and data encryption. Presenting our set of slides with Data Encryption And Authentication In Automotive Cyber Security This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication, Data Encryption, Authenticity Of Software
-
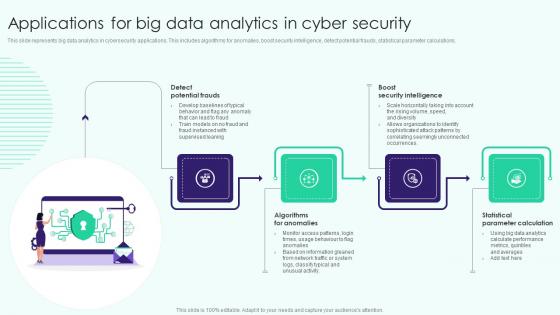 Applications For Big Data Analytics In Cyber Security
Applications For Big Data Analytics In Cyber SecurityThis slide represents big data analytics in cybersecurity applications. This includes algorithms for anomalies, boost security intelligence, detect potential frauds, statistical parameter calculations. Presenting our set of slides with name Applications For Big Data Analytics In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detect Potential Frauds, Algorithms For Anomalies, Statistical Parameter Calculation .
-
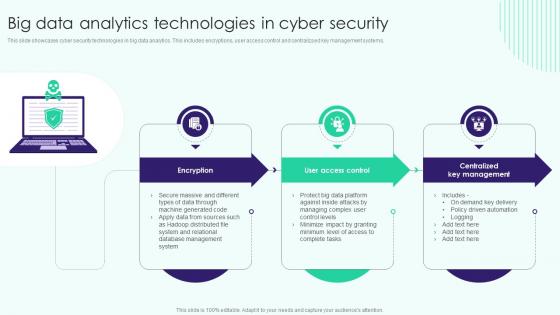 Big Data Analytics Technologies In Cyber Security
Big Data Analytics Technologies In Cyber SecurityThis slide showcases cyber security technologies in big data analytics. This includes encryptions, user access control and centralizsed key management systems. Presenting our set of slides with name Big Data Analytics Technologies In Cyber Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Big Data Analytics, Centralized Key Management, Technologies In Cyber Security.
-
 Csirt Cyber Security Icon For Data Safety
Csirt Cyber Security Icon For Data SafetyPresenting our set of slides with Csirt Cyber Security Icon For Data Safety. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Csirt Cyber Security, Data Safety.
-
 Csirt Cyber Security Icon For Protecting Data
Csirt Cyber Security Icon For Protecting DataIntroducing our premium set of slides with Csirt Cyber Security Icon For Protecting Data. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Csirt Cyber Security, Protecting Data. So download instantly and tailor it with your information.
-
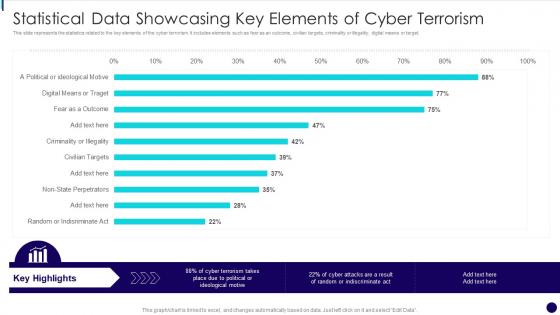 Statistical Data Showcasing Key Elements Of Cyber Terrorism
Statistical Data Showcasing Key Elements Of Cyber TerrorismThis slide represents the statistics related to the key elements of the cyber terrorism. It includes elements such as fear as an outcome, civilian targets, criminality or illegality, digital means or target. Presenting our well structured Statistical Data Showcasing Key Elements Of Cyber Terrorism. The topics discussed in this slide are Statistical Data Showcasing Key Elements Of Cyber Terrorism. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
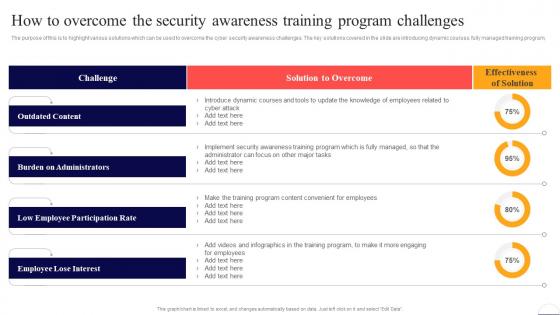 How To Overcome The Security Awareness Training Program Preventing Data Breaches Through Cyber Security
How To Overcome The Security Awareness Training Program Preventing Data Breaches Through Cyber SecurityThe purpose of this is to highlight various solutions which can be used to overcome the cyber security awareness challenges. The key solutions covered in the slide are introducing dynamic courses, fully managed training program. Deliver an outstanding presentation on the topic using this How To Overcome The Security Awareness Training Program Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Outdated Content, Burden On Administrators, Low Employee Participation Rate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
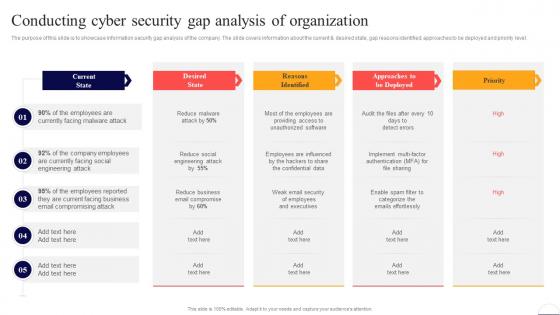 Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber Security
Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase information security gap analysis of the company. The slide covers information about the current and desired state, gap reasons identified, approaches to be deployed and priority level. Deliver an outstanding presentation on the topic using this Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Current State, Email, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
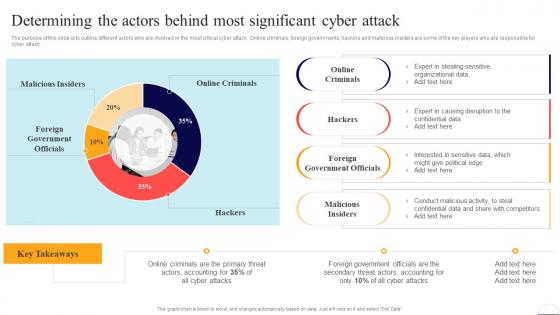 Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber Security
Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Present the topic in a bit more detail with this Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Online Criminals, Foreign Government Officials, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
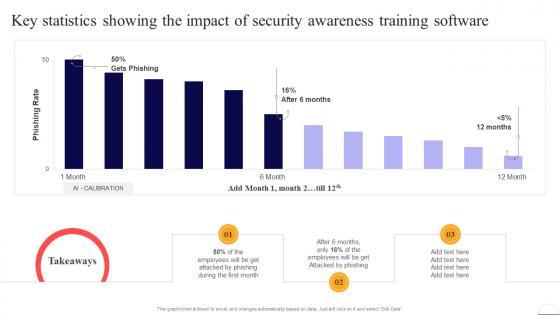 Key Statistics Showing The Impact Of Security Awarenesspreventing Data Breaches Through Cyber Security
Key Statistics Showing The Impact Of Security Awarenesspreventing Data Breaches Through Cyber SecurityPresent the topic in a bit more detail with this Key Statistics Showing The Impact Of Security Awarenesspreventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Employees, Security, Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
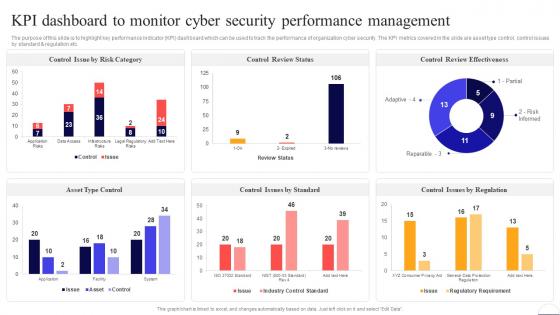 Kpi Dashboard To Monitor Cyber Security Performance Preventing Data Breaches Through Cyber Security
Kpi Dashboard To Monitor Cyber Security Performance Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight key performance indicator KPI dashboard which can be used to track the performance of organization cyber security. The KPI metrics covered in the slide are asset type control, control issues by standard and regulation etc. Deliver an outstanding presentation on the topic using this Kpi Dashboard To Monitor Cyber Security Performance Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Control Review Status, Management, Cyber Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber Security
Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Risk By Threats, Threat Report, Current Risk Status. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
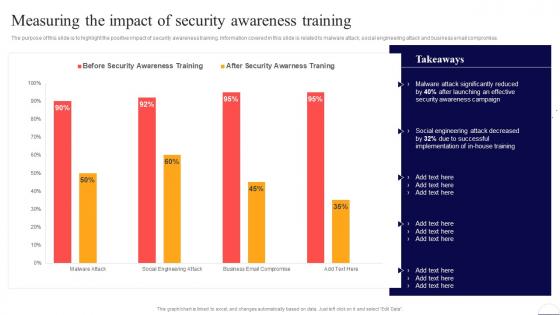 Measuring The Impact Of Security Awareness Training Preventing Data Breaches Through Cyber Security
Measuring The Impact Of Security Awareness Training Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight the positive impact of security awareness training. Information covered in this slide is related to malware attack, social engineering attack and business email compromise. Present the topic in a bit more detail with this Measuring The Impact Of Security Awareness Training Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Security Awareness, Social Engineering. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
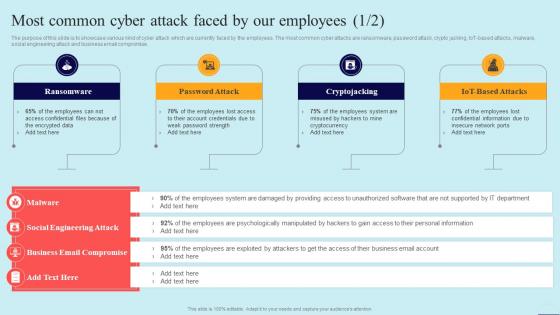 Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber Security
Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT-based attacks, malware, social engineering attack and business email compromise. Introducing Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Password Attack, Cryptojacking, using this template. Grab it now to reap its full benefits.
-
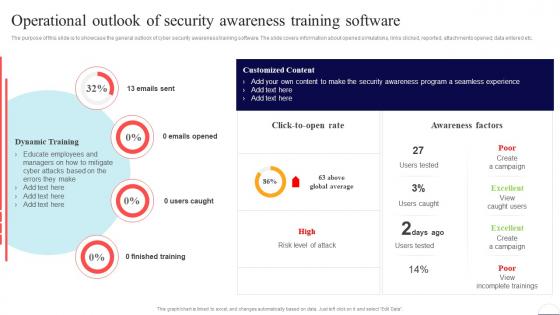 Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber Security
Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the general outlook of cyber security awareness training software. The slide covers information about opened simulations, links clicked, reported, attachments opened, data entered etc. Present the topic in a bit more detail with this Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Finished Training, Awareness Factors, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Practices To Improve Security Awareness Level Amongst The Preventing Data Breaches Through Cyber Security
Practices To Improve Security Awareness Level Amongst The Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline multiple ways which can be used by the organization to improve the cyber security awareness level of employees. The key practices mentioned in the slide are involving top level management, developing robust policies, and setting guidelines. Increase audience engagement and knowledge by dispensing information using Practices To Improve Security Awareness Level Amongst The Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Get Management Involved, Develop Robust Policies, Set Guidelines using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
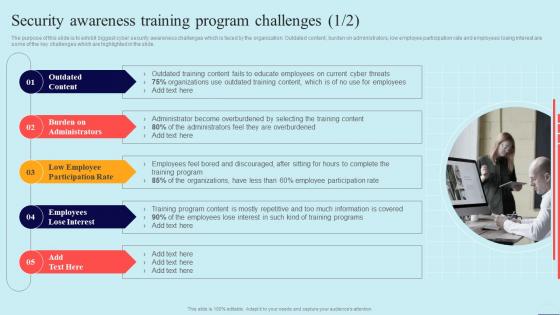 Security Awareness Training Program Challenges Preventing Data Breaches Through Cyber Security
Security Awareness Training Program Challenges Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to exhibit biggest cyber security awareness challenges which is faced by the organization. Outdated content, burden on administrators, low employee participation rate and employees losing interest are some of the key challenges which are highlighted in the slide. Increase audience engagement and knowledge by dispensing information using Security Awareness Training Program Challenges Preventing Data Breaches Through Cyber Security. This template helps you present information on five stages. You can also present information on Outdated Content, Employees Lose Interest, Burden On Administrators using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
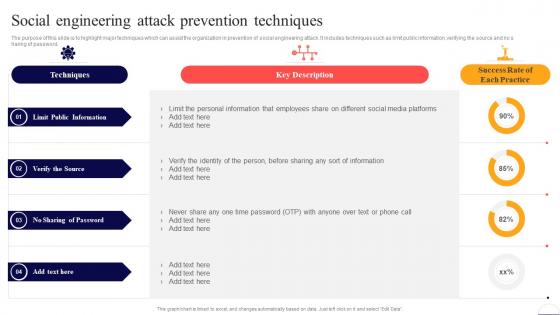 Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber Security
Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no sharing of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Limit Public Information, Verify The Source, No Sharing Of Password. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents For Preventing Data Breaches Through Cyber Security Awareness
Table Of Contents For Preventing Data Breaches Through Cyber Security AwarenessDeliver an outstanding presentation on the topic using this Table Of Contents For Preventing Data Breaches Through Cyber Security Awareness. Dispense information and present a thorough explanation of Cyber Security Awareness, Online Courses, Automation Tools using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
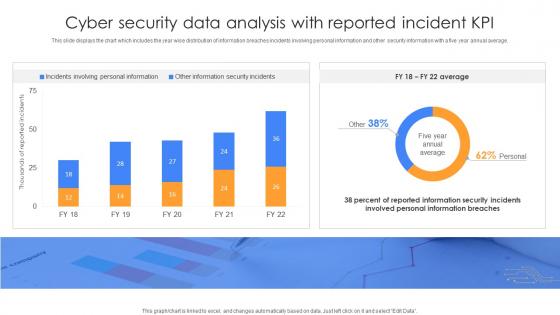 Cyber Security Data Analysis With Reported Incident KPI
Cyber Security Data Analysis With Reported Incident KPIThis slide displays the chart which includes the year wise distribution of information breaches incidents involving personal information and other security information with a five year annual average. Introducing our Cyber Security Data Analysis With Reported Incident KPI set of slides. The topics discussed in these slides are Cyber Security Data Analysis, Reported Incident KPI. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
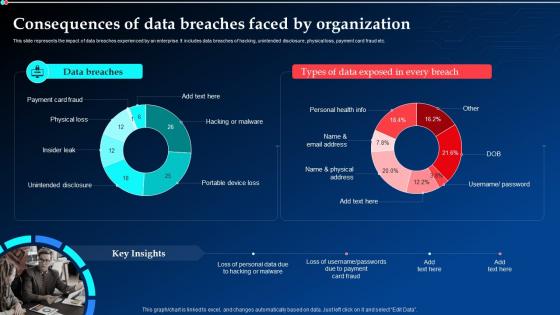 Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt Diagrams
Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt DiagramsThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Deliver an outstanding presentation on the topic using this Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt Diagrams. Dispense information and present a thorough explanation of Data Breaches, Consequences, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
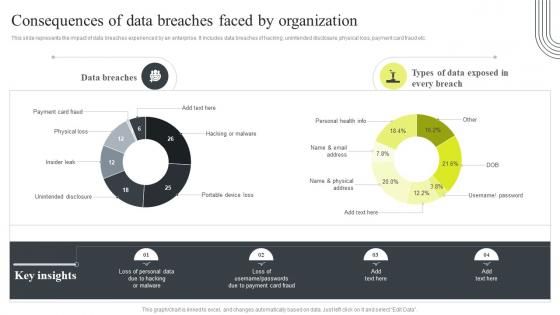 Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization
Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By OrganizationThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization. Use it as a tool for discussion and navigation on Consequences, Data Breaches, Unintended Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
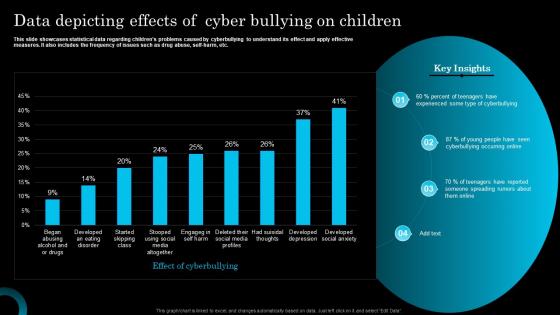 Data Depicting Effects Of Cyber Bullying On Children
Data Depicting Effects Of Cyber Bullying On ChildrenThis slide showcases statistical data regarding childrens problems caused by cyberbullying to understand its effect and apply effective measures. It also includes the frequency of issues such as drug abuse, self harm, etc. Introducing our Data Depicting Effects Of Cyber Bullying On Children set of slides. The topics discussed in these slides are Experienced, Cyberbullying, Spreading. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
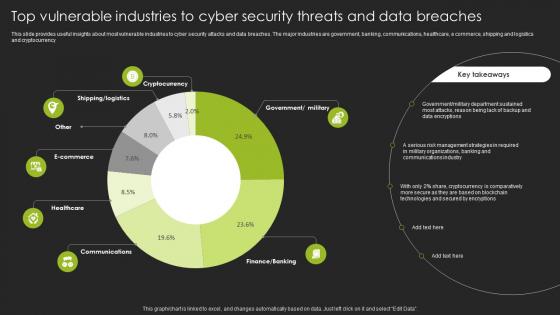 Top Vulnerable Industries To Cyber Security Threats And Data Breaches
Top Vulnerable Industries To Cyber Security Threats And Data BreachesThis slide provides useful insights about most vulnerable industries to cyber security attacks and data breaches. The major industries are government, banking, communications, healthcare, e commerce, shipping and logistics and cryptocurrency Introducing our Top Vulnerable Industries To Cyber Security Threats And Data Breaches set of slides. The topics discussed in these slides are Government, Department. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
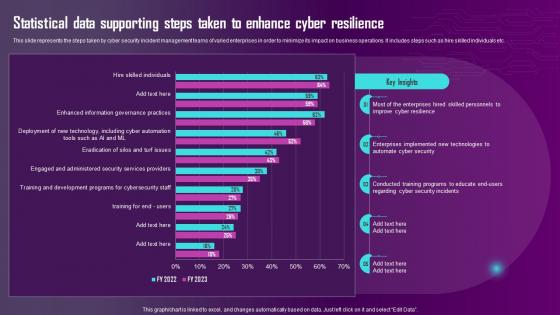 Statistical Data Supporting Steps Taken To Enhance Cyber Resilience Ppt Show Portfolio
Statistical Data Supporting Steps Taken To Enhance Cyber Resilience Ppt Show PortfolioThis slide represents the steps taken by cyber security incident management teams of varied enterprises in order to minimize its impact on business operations. It includes steps such as hire skilled individuals etc.Present the topic in a bit more detail with this Statistical Data Supporting Steps Taken To Enhance Cyber Resilience Ppt Show Portfolio. Use it as a tool for discussion and navigation on Enterprises Implemented, Automate Cyber Security, Enterprises Hired . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Data Theft Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Data Theft Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cyber data theft colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cyber Data Theft Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Data Theft Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cyber data theft monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Cyber Phishing Attack Icon To Steal Confidential Data
Cyber Phishing Attack Icon To Steal Confidential DataPresenting our well structured Cyber Phishing Attack Icon To Steal Confidential Data. The topics discussed in this slide are Cyber Phishing Attack Icon To Steal Confidential Data. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Confidential Data Should Be Backup Cyber Terrorism Attacks
Confidential Data Should Be Backup Cyber Terrorism AttacksThis slide emphasizes the significance of backing up private data, which enables for data recovery in the event of an attack. Introducing Confidential Data Should Be Backup Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Unanticipated, Occurrence, Recovered, Business, Assurance, using this template. Grab it now to reap its full benefits.
-
 3 Step Cyber Security Plan For Data Protection
3 Step Cyber Security Plan For Data ProtectionThis slide signifies the three stage cyber security program to improve data protection. It covers information about steps like prevention, response and remediation. Presenting our set of slides with 3 Step Cyber Security Plan For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prevention, Response, Remediation.
-
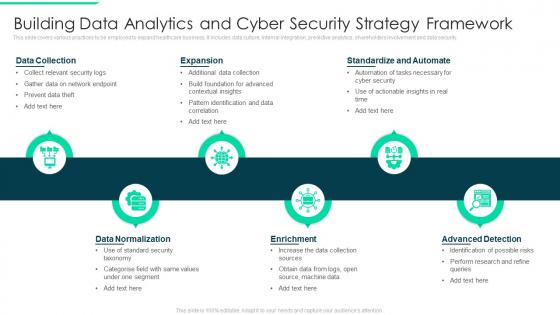 Building Data Analytics And Cyber Security Strategy Framework
Building Data Analytics And Cyber Security Strategy FrameworkThis slide covers various practices to be employed to expand healthcare business. It includes data culture, internal integration, predictive analytics, shareholders involvement and data security. Introducing our premium set of slides with Building Data Analytics And Cyber Security Strategy Framework. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Collection, Data Normalization, Expansion. So download instantly and tailor it with your information.
-
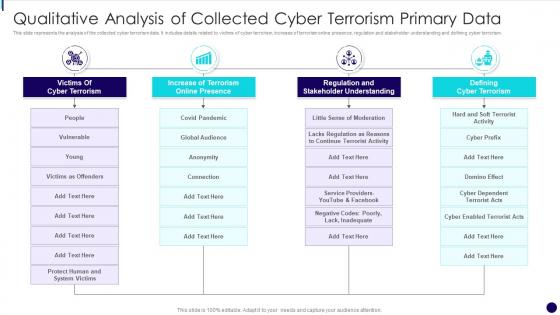 Qualitative Analysis Of Collected Cyber Terrorism Primary Data
Qualitative Analysis Of Collected Cyber Terrorism Primary DataThis slide represents the analysis of the collected cyber terrorism data. It includes details related to victims of cyber terrorism, increase of terrorism online presence, regulation and stakeholder understanding and defining cyber terrorism. Introducing our premium set of slides with name Qualitative Analysis Of Collected Cyber Terrorism Primary Data. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Regulation And Stakeholder Understanding, Defining Cyber Terrorism, Terrorism Online Presence. So download instantly and tailor it with your information.
-
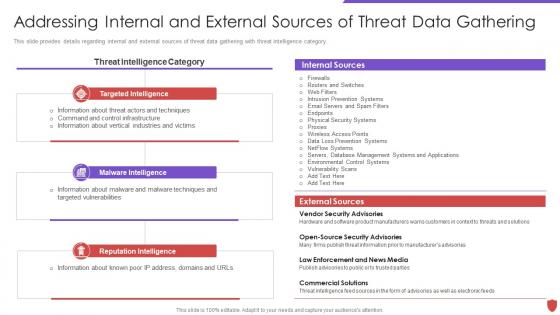 Addressing internal and external sources data cyber security risk management
Addressing internal and external sources data cyber security risk managementThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Deliver an outstanding presentation on the topic using this Addressing Internal And External Sources Data Cyber Security Risk Management. Dispense information and present a thorough explanation of Internal Sources, External Sources, Targeted Intelligence, Malware Intelligence using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Data Protection In Powerpoint And Google Slides Cpb
Cyber Security Data Protection In Powerpoint And Google Slides CpbPresenting our Cyber Security Data Protection In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Cyber Security Data Protection This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
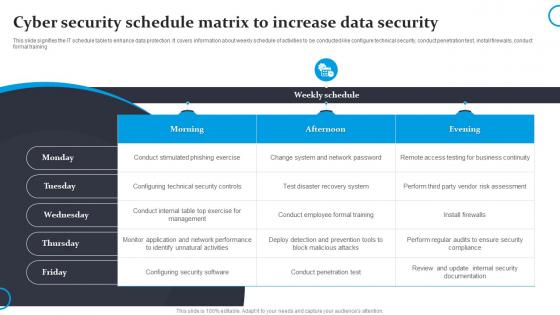 Cyber Security Schedule Matrix To Increase Data Security
Cyber Security Schedule Matrix To Increase Data SecurityThis slide signifies the IT schedule table to enhance data protection. It covers information about weekly schedule of activities to be conducted like configure technical security, conduct penetration test, install firewalls, conduct formal training.Presenting our well structured Cyber Security Schedule Matrix To Increase Data Security. The topics discussed in this slide are Conduct Stimulated, Configuring Technical, Unnatural Activities. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
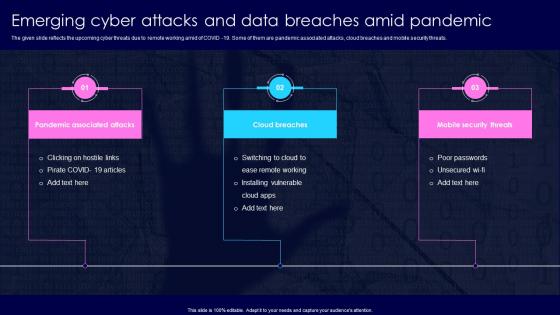 Emerging Cyber Attacks And Data Breaches Amid Pandemic
Emerging Cyber Attacks And Data Breaches Amid PandemicThe given slide reflects the upcoming cyber threats due to remote working amid of COVID 19. Some of them are pandemic associated attacks, cloud breaches and mobile security threats. Presenting our set of slides with Emerging Cyber Attacks And Data Breaches Amid Pandemic. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Breaches, Mobile Security Threats.
-
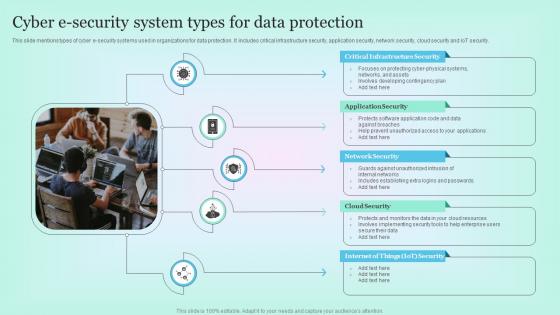 Cyber E Security System Types For Data Protection
Cyber E Security System Types For Data ProtectionThis slide mentions types of cyber e security systems used in organizations for data protection. It includes critical infrastructure security, application security, network security, cloud security and IoT security. Presenting our set of slides with name Cyber E Security System Types For Data Protection. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Critical Infrastructure Security, Application Security, Network Security.
-
 Cyber Risk Management Icon To Avoid Data Breaches
Cyber Risk Management Icon To Avoid Data BreachesPresenting our set of slides with name Cyber Risk Management Icon To Avoid Data Breaches. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Management, Cyber Risk, Data Breaches.
-
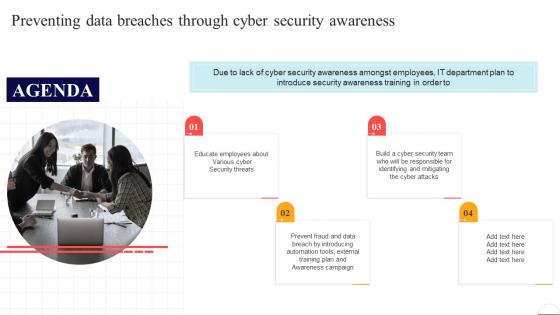 Agenda Preventing Data Breaches Through Cyber Security Awareness
Agenda Preventing Data Breaches Through Cyber Security AwarenessIntroducing Agenda Preventing Data Breaches Through Cyber Security Awareness to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Awareness Campaign, Security Threats, Employees, using this template. Grab it now to reap its full benefits.
-
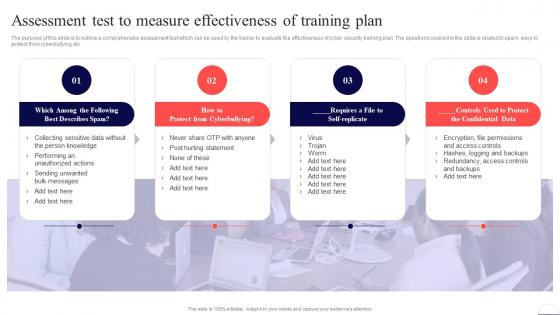 Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber Security
Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Cyberbullying, Confidential Data, Training Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
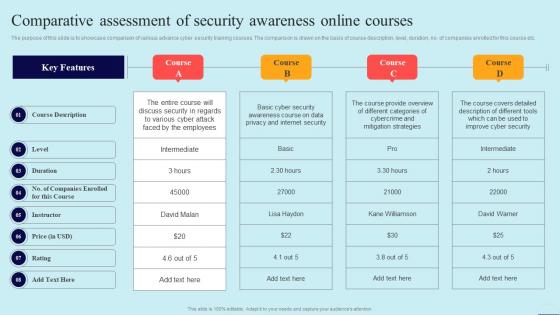 Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber Security
Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase comparison of various advance cyber security training courses. The comparison is drawn on the basis of course description, level, duration, no. of companies enrolled for this course etc. Present the topic in a bit more detail with this Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Course Description, Instructor, Rating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber Security
Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Deliver an outstanding presentation on the topic using this Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Security Reporting, Phishing Simulations, Deployment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



