Powerpoint Templates and Google slides for Cyber Monitoring Of System Using Biometric Security Identification Icon
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Progressive continuous monitoring plan to terminate cyber risks powerpoint presentation slides
Progressive continuous monitoring plan to terminate cyber risks powerpoint presentation slidesDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Progressive Continuous Monitoring Plan To Terminate Cyber Risks Powerpoint Presentation Slides is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the fourty seven slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Effective security monitoring plan to eliminate cyber threats and data breaches complete deck
Effective security monitoring plan to eliminate cyber threats and data breaches complete deckEnthrall your audience with this Effective Security Monitoring Plan To Eliminate Cyber Threats And Data Breaches Complete Deck. Increase your presentation threshold by deploying this well crafted template. It acts as a great communication tool due to its well researched content. It also contains stylized icons, graphics, visuals etc, which make it an immediate attention grabber. Comprising fourty four slides, this complete deck is all you need to get noticed. All the slides and their content can be altered to suit your unique business setting. Not only that, other components and graphics can also be modified to add personal touches to this prefabricated set.
-
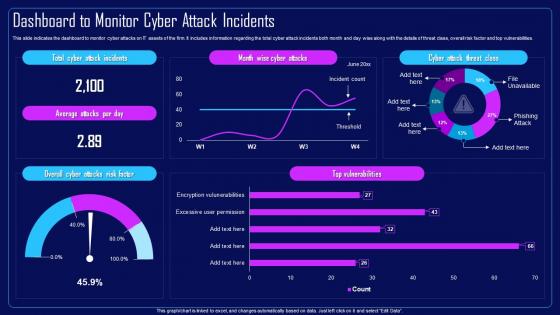 Action Plan To Combat Cyber Crimes Dashboard To Monitor Cyber Attack Incidents
Action Plan To Combat Cyber Crimes Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Dashboard To Monitor Cyber Attack Incidents. Use it as a tool for discussion and navigation on Dashboard To Monitor, Cyber Attacks, IT Assets Of The Firm, Risk Factor And Top Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
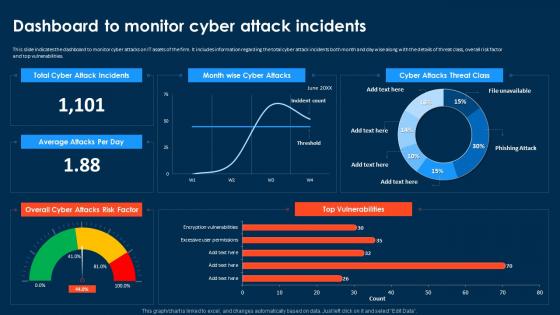 Compressive Planning Guide Dashboard To Monitor Cyber Attack Incidents
Compressive Planning Guide Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Present the topic in a bit more detail with this Compressive Planning Guide Dashboard To Monitor Cyber Attack Incidents. Use it as a tool for discussion and navigation on Dashboard To Monitor, Cyber Attacks On IT Assets, Top Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
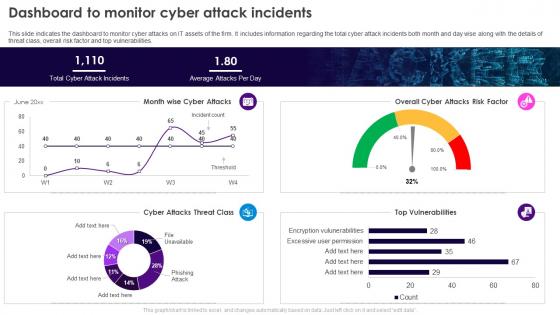 Security Plan To Prevent Cyber Dashboard To Monitor Cyber Attack Incidents
Security Plan To Prevent Cyber Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Deliver an outstanding presentation on the topic using this Security Plan To Prevent Cyber Dashboard To Monitor Cyber Attack Incidents. Dispense information and present a thorough explanation of Dashboard To Monitor, Cyber Attacks, IT Assets Of The Firm, Risk Factor And Top Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Monitor And Assess Vendor Risk Management Cyber Risk Assessment
Monitor And Assess Vendor Risk Management Cyber Risk AssessmentThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Deliver an outstanding presentation on the topic using this Monitor And Assess Vendor Risk Management Cyber Risk Assessment Dispense information and present a thorough explanation of Information Security, Physical Assets, Vendor Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Monitor And Assess Vendor Risk Management Creating Cyber Security Awareness
Monitor And Assess Vendor Risk Management Creating Cyber Security AwarenessThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Deliver an outstanding presentation on the topic using this Monitor And Assess Vendor Risk Management Creating Cyber Security Awareness Dispense information and present a thorough explanation of Select Strong Password, Conduct Password Test, Password Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
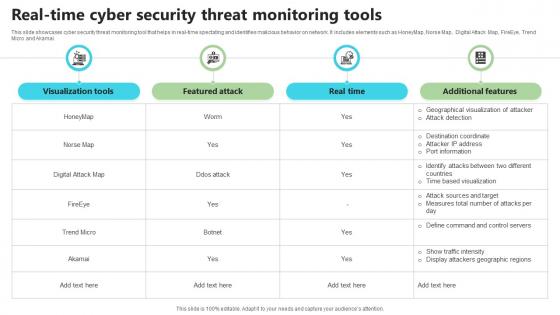 Real Time Cyber Security Threat Monitoring Tools
Real Time Cyber Security Threat Monitoring ToolsThis slide showcases cyber security threat monitoring tool that helps in real-time spectating and identifies malicious behavior on network. It includes elements such as HoneyMap, Norse Map, Digital Attack Map, FireEye, Trend Micro and Akamai. Presenting our well structured Real Time Cyber Security Threat Monitoring Tools. The topics discussed in this slide are Visualization Tools, Real Time, Additional Features. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Monitor And Assess Vendor Risk Management Implementing Cyber Risk Management Process
Monitor And Assess Vendor Risk Management Implementing Cyber Risk Management ProcessThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Introducing Monitor And Assess Vendor Risk Management Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Details, Reviews, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Monitoring And Management Icon
Cyber Security Monitoring And Management IconPresenting our set of slides with Cyber Security Monitoring And Management Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security, Monitoring And Management Icon.
-
 Cyber Security Crisis Monitoring Solutions
Cyber Security Crisis Monitoring SolutionsThe purpose of this slide is to help cybersecurity professionals in monitoring potential threats and implementing proactive solutions such as detecting security incidents, assessing account activity, monitoring network traffic, etc. Presenting our set of slides with Cyber Security Crisis Monitoring Solutions This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detect Security Incidents, Cyber Risk Management, Assess Account Activity
-
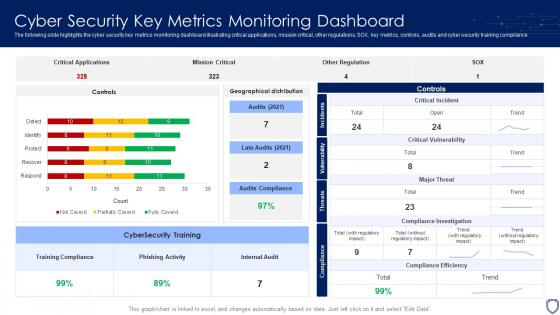 Cyber Security Key Metrics Monitoring Dashboard
Cyber Security Key Metrics Monitoring DashboardThe following slide highlights the cyber security key metrics monitoring dashboard illustrating critical applications, mission critical, other regulations, SOX, key metrics, controls, audits and cyber security training compliance. Introducing our Cyber Security Key Metrics Monitoring Dashboard set of slides. The topics discussed in these slides are Training Compliance, Phishing Activity, Internal Audit. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Kpi Dashboard To Monitor Cyber Building A Security Awareness Program
Kpi Dashboard To Monitor Cyber Building A Security Awareness ProgramThe purpose of this slide is to highlight key performance indicator KPI dashboard which can be used to track the performance of organization cyber security. The KPI metrics covered in the slide are asset type control, control issues by standard and regulation etc. Deliver an outstanding presentation on the topic using this KPI Dashboard To Monitor Cyber Building A Security Awareness Program. Dispense information and present a thorough explanation of Control Review Effectiveness, Performance Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
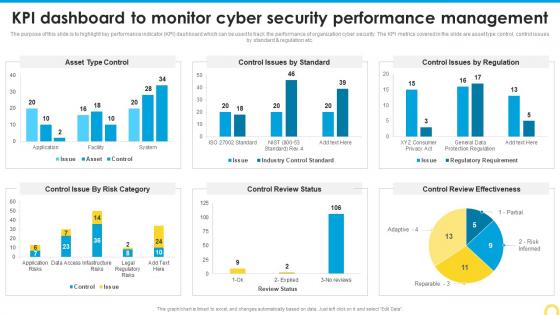
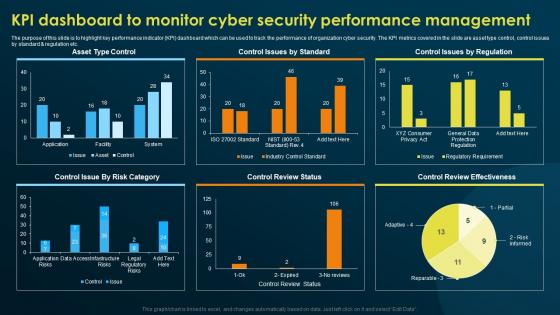 KPI Dashboard To Monitor Cyber Security Performance Implementing Security Awareness Training
KPI Dashboard To Monitor Cyber Security Performance Implementing Security Awareness TrainingThe purpose of this slide is to highlight key performance indicator KPI dashboard which can be used to track the performance of organization cyber security. The KPI metrics covered in the slide are asset type control, control issues by standard and regulation etc. Deliver an outstanding presentation on the topic using this KPI Dashboard To Monitor Cyber Security Performance Implementing Security Awareness Training. Dispense information and present a thorough explanation of Asset Type Control, Control Issues By Standard, Review Effectiveness using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
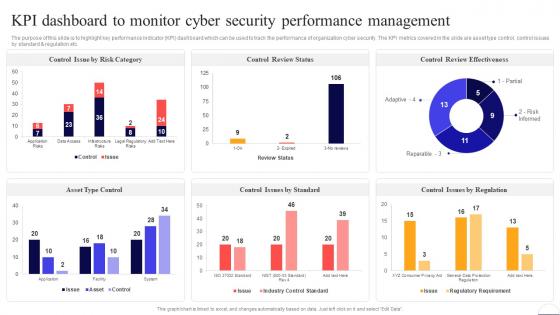 Kpi Dashboard To Monitor Cyber Security Performance Preventing Data Breaches Through Cyber Security
Kpi Dashboard To Monitor Cyber Security Performance Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight key performance indicator KPI dashboard which can be used to track the performance of organization cyber security. The KPI metrics covered in the slide are asset type control, control issues by standard and regulation etc. Deliver an outstanding presentation on the topic using this Kpi Dashboard To Monitor Cyber Security Performance Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Control Review Status, Management, Cyber Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 KPI Dashboard To Monitor Cyber Security Performance Management Developing Cyber Security Awareness
KPI Dashboard To Monitor Cyber Security Performance Management Developing Cyber Security AwarenessThe purpose of this slide is to highlight key performance indicator KPI dashboard which can be used to track the performance of organization cyber security. The KPI metrics covered in the slide are asset type control, control issues by standard and regulation etc. Deliver an outstanding presentation on the topic using this KPI Dashboard To Monitor Cyber Security Performance Management Developing Cyber Security Awareness. Dispense information and present a thorough explanation of KPI Dashboard, Monitor Cyber Security, Performance Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
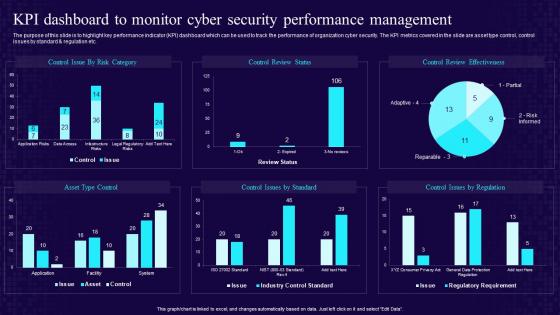
 KPI Dashboard To Monitor Cyber Security Performance Management Conducting Security Awareness
KPI Dashboard To Monitor Cyber Security Performance Management Conducting Security AwarenessThe purpose of this slide is to highlight key performance indicator KPI dashboard which can be used to track the performance of organization cyber security. The KPI metrics covered in the slide are asset type control, control issues by standard and regulation etc. Present the topic in a bit more detail with this KPI Dashboard To Monitor Cyber Security Performance Management Conducting Security Awareness. Use it as a tool for discussion and navigation on Asset Type Control, Control Review Status, Control Review Effectiveness. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
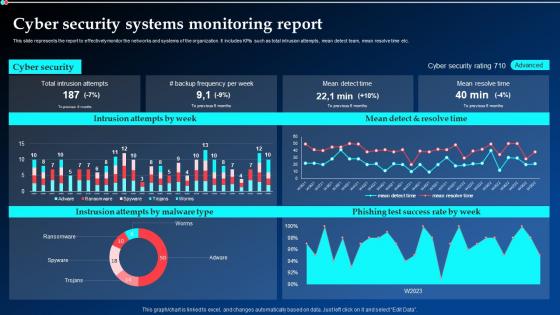 Cyber Security Systems Monitoring Report Ppt Powerpoint Presentation Show Background Images
Cyber Security Systems Monitoring Report Ppt Powerpoint Presentation Show Background ImagesThis slide represents the report to effectively monitor the networks and systems of the organization. It includes KPIs such as total intrusion attempts, mean detect team, mean resolve time etc. Deliver an outstanding presentation on the topic using this Cyber Security Systems Monitoring Report Ppt Powerpoint Presentation Show Background Images. Dispense information and present a thorough explanation of Cyber Security, Intrusion Attempts, Monitoring Report using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
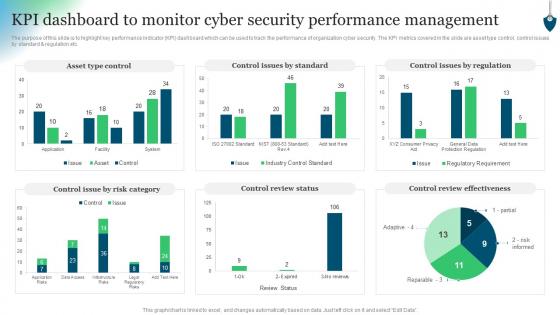
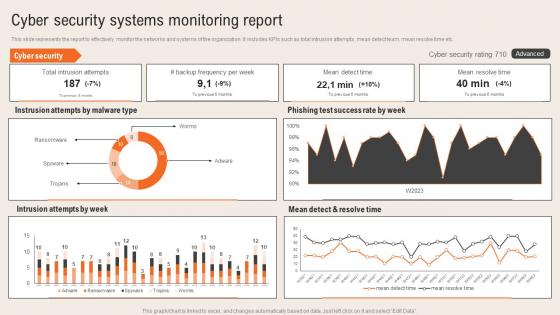 Cyber Security Systems Monitoring Report Deploying Computer Security Incident Management
Cyber Security Systems Monitoring Report Deploying Computer Security Incident ManagementThis slide represents the report to effectively monitor the networks and systems of the organization. It includes KPIs such as total intrusion attempts, mean detect team, mean resolve time etc.Present the topic in a bit more detail with this Cyber Security Systems Monitoring Report Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Intrusion Attempts, Ransomware, Phishing Test Success. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
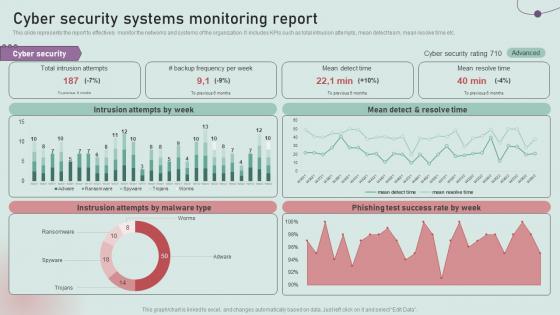 Cyber Security Systems Monitoring Report Development And Implementation Of Security Incident Management
Cyber Security Systems Monitoring Report Development And Implementation Of Security Incident ManagementThis slide represents the report to effectively monitor the networks and systems of the organization. It includes KPIs such as total intrusion attempts, mean detect team, mean resolve time etc. Deliver an outstanding presentation on the topic using this Cyber Security Systems Monitoring Report Development And Implementation Of Security Incident Management. Dispense information and present a thorough explanation of Intrusion Attempts, Mean Detect, Resolve Time using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
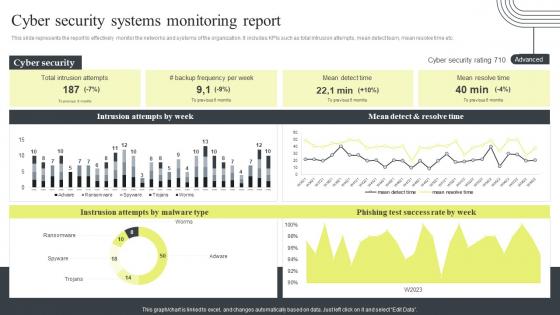 Cyber Security Attacks Response Plan Cyber Security Systems Monitoring Report
Cyber Security Attacks Response Plan Cyber Security Systems Monitoring ReportThis slide represents the report to effectively monitor the networks and systems of the organization. It includes KPIs such as total intrusion attempts, mean detect team, mean resolve time etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Cyber Security Systems Monitoring Report. Use it as a tool for discussion and navigation on Cyber Security Systems, Monitoring Report, Mean Detect And Resolve Time. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
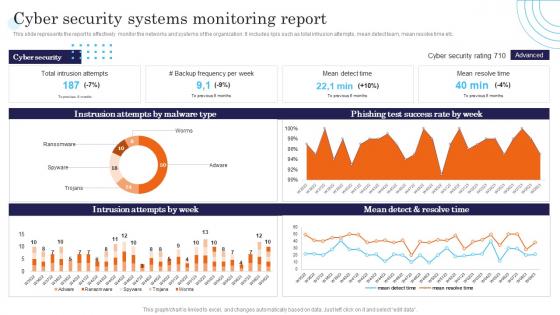 Cyber Security Systems Monitoring Report Incident Response Strategies Deployment
Cyber Security Systems Monitoring Report Incident Response Strategies DeploymentThis slide represents the report to effectively monitor the networks and systems of the organization. It includes kpis such as total intrusion attempts, mean detect team, mean resolve time etc. Present the topic in a bit more detail with this Cyber Security Systems Monitoring Report Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Success, Resolve, Intrusion. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
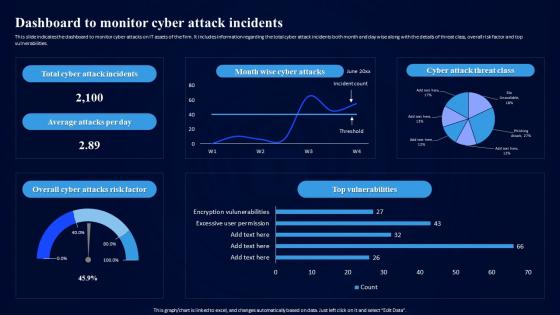 Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack Incidents
Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack Incidents. Use it as a tool for discussion and navigation on Dashboard To Monitor, Cyber Attack Incidents, Vulnerabilities, Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
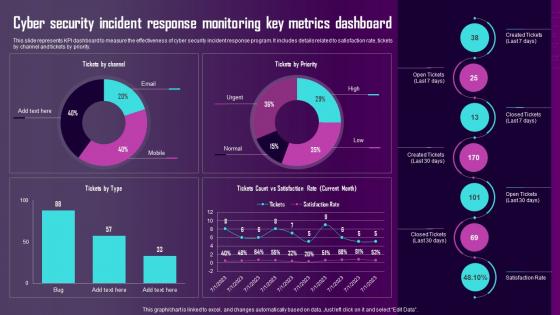 Cyber Security Incident Response Monitoring Key Metrics Dashboard Ppt Slides Inspiration
Cyber Security Incident Response Monitoring Key Metrics Dashboard Ppt Slides InspirationThis slide represents KPI dashboard to measure the effectiveness of cyber security incident response program. It includes details related to satisfaction rate, tickets by channel and tickets by priority.Deliver an outstanding presentation on the topic using this Cyber Security Incident Response Monitoring Key Metrics Dashboard Ppt Slides Inspiration. Dispense information and present a thorough explanation of Cyber Security, Incident Response, Monitoring Key using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
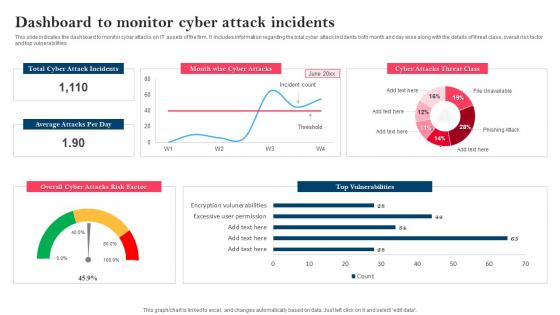 Strategy To Minimize Cyber Attacks Dashboard To Monitor Cyber Attack Incidents
Strategy To Minimize Cyber Attacks Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Dashboard To Monitor Cyber Attack Incidents. Dispense information and present a thorough explanation of Dashboard To Monitor, Cyber Attack Incidents, Top Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Dashboard For Cyber Security Real Time Monitoring
Dashboard For Cyber Security Real Time MonitoringPresenting our set of slides with name Dashboard For Cyber Security Real Time Monitoring. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Dashboard For Cyber Security, Real Time Monitoring.
-
 Agenda for progressive continuous monitoring plan to terminate cyber risks
Agenda for progressive continuous monitoring plan to terminate cyber risksIntroducing Agenda For Progressive Continuous Monitoring Plan To Terminate Cyber Risks to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Agenda For Progressive Continuous Monitoring Plan To Terminate Cyber Risks, using this template. Grab it now to reap its full benefits.
-
 Icons slide for progressive continuous monitoring plan to terminate cyber risks
Icons slide for progressive continuous monitoring plan to terminate cyber risksIntroducing our innovatively-crafted Icons Slide For Progressive Continuous Monitoring Plan To Terminate Cyber Risks template to create a stunning PowerPoint presentation. The Icons Slide For Progressive Continuous Monitoring Plan To Terminate Cyber Risks template displays icons that can be used to enhance the visual appeal of your presentations. The design is completely customizable. So feel free to download it instantly
-
 Brand monitoring cyber security ppt powerpoint presentation visual aids pictures cpb
Brand monitoring cyber security ppt powerpoint presentation visual aids pictures cpbPresenting our Brand Monitoring Cyber Security Ppt Powerpoint Presentation Visual Aids Pictures Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Brand Monitoring Cyber Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Architecture Monitoring Cyber Security In Powerpoint And Google Slides Cpb
Architecture Monitoring Cyber Security In Powerpoint And Google Slides CpbPresenting our Architecture Monitoring Cyber Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Architecture Monitoring Cyber Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
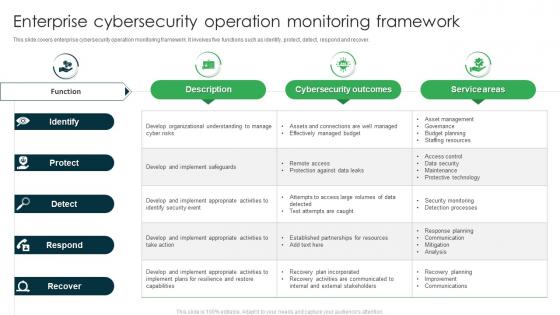 Enterprise Cyber security Operation Monitoring Framework
Enterprise Cyber security Operation Monitoring FrameworkThis slide covers enterprise cyber security operation monitoring framework. It involves five functions such as identify, protect, detect, respond and recover. Presenting our well structured Enterprise Cybersecurity Operation Monitoring Framework. The topics discussed in this slide are Cybersecurity Outcomes, Service Areas, Identify. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
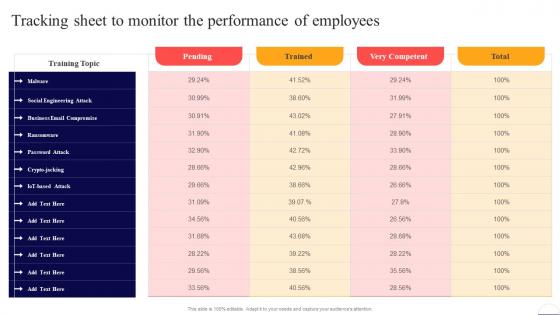 Tracking Sheet To Monitor The Performance Of Employees Preventing Data Breaches Through Cyber Security
Tracking Sheet To Monitor The Performance Of Employees Preventing Data Breaches Through Cyber SecurityPresent the topic in a bit more detail with this Tracking Sheet To Monitor The Performance Of Employees Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Social Engineering Attack, Business Email Compromise, Iot Based Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Tracking Sheet To Monitor The Performance Of Employees Developing Cyber Security Awareness Training
Tracking Sheet To Monitor The Performance Of Employees Developing Cyber Security Awareness TrainingDeliver an outstanding presentation on the topic using this Tracking Sheet To Monitor The Performance Of Employees Developing Cyber Security Awareness Training. Dispense information and present a thorough explanation of Social Engineering Attack, Business Email Compromise, Ransomware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managed Detection And Response Layer For Expert Monitoring Enabling Automation In Cyber Security Operations
Managed Detection And Response Layer For Expert Monitoring Enabling Automation In Cyber Security OperationsThis slide highlights the slide Managed Detection and Response security layer which include alter monitoring, attack investigation, threat hunting, and incident response. Introducing Managed Detection And Response Layer For Expert Monitoring Enabling Automation In Cyber Security Operations to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Alert Monitoring, Attack Investigation, Threat Hunting, using this template. Grab it now to reap its full benefits.
-
 Cyber Security KPI Icon With Monitor
Cyber Security KPI Icon With MonitorPresenting our set of slides with Cyber Security KPI Icon With Monitor. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security KPI Icon.
-
 Monitor And Assess Vendor Risk Management Cyber Attack Risks Mitigation
Monitor And Assess Vendor Risk Management Cyber Attack Risks MitigationThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Introducing Monitor And Assess Vendor Risk Management Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Web Application Security, Infrastructure Security, Vendor Management, using this template. Grab it now to reap its full benefits.
-
 Cyber threat analysis monitoring ppt powerpoint presentation inspiration cpb
Cyber threat analysis monitoring ppt powerpoint presentation inspiration cpbPresenting this set of slides with name Cyber Threat Analysis Monitoring Ppt Powerpoint Presentation Inspiration Cpb. This is an editable Powerpoint one stages graphic that deals with topics like Cyber Threat Analysis Monitoring to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber threat analysis monitoring ppt powerpoint presentation styles file formats cpb
Cyber threat analysis monitoring ppt powerpoint presentation styles file formats cpbPresenting this set of slides with name Cyber Threat Analysis Monitoring Ppt Powerpoint Presentation Styles File Formats Cpb. This is an editable Powerpoint one stages graphic that deals with topics like Cyber Threat Analysis Monitoring to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber monitoring of system using biometric security identification icon
Cyber monitoring of system using biometric security identification iconPresenting this set of slides with name Cyber Monitoring Of System Using Biometric Security Identification Icon. This is a three stage process. The stages in this process are Cyber Monitoring Of System Using Biometric Security Identification Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Monitoring cyber threats ppt powerpoint presentation layouts graphics cpb
Monitoring cyber threats ppt powerpoint presentation layouts graphics cpbPresenting this set of slides with name Monitoring Cyber Threats Ppt Powerpoint Presentation Layouts Graphics Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Monitoring Cyber Threats to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Real time cyber threat monitoring ppt powerpoint presentation icon shapes cpb
Real time cyber threat monitoring ppt powerpoint presentation icon shapes cpbPresenting this set of slides with name Real Time Cyber Threat Monitoring Ppt Powerpoint Presentation Icon Shapes Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Real Time Cyber Threat Monitoring to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
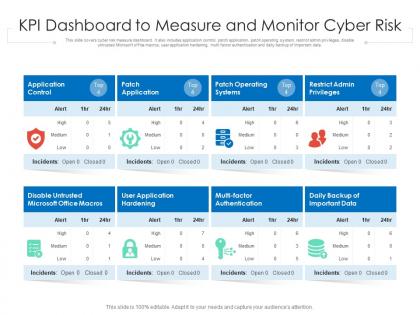 Kpi dashboard to measure and monitor cyber risk
Kpi dashboard to measure and monitor cyber riskThis slide covers cyber risk measure dashboard. It also includes application control, patch application, patch operating system, restrict admin privileges, disable untrusted Microsoft office macros, user application hardening, multi factor authentication and daily backup of important data Presenting our well-structured KPI Dashboard To Measure And Monitor Cyber Risk. The topics discussed in this slide are Dashboard, Measure, Monitor. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Powerpoint template and background with cyber security network data monitor as abstract
Powerpoint template and background with cyber security network data monitor as abstractMake your presentation crisp and attention-grabbing with our Powerpoint Template And Background With Cyber Security Network Data Monitor As Abstract. This pre-designed PPT is all you need to portray your ideas for the next presentation. This theme is equipped with high-resolution graphics and images, which helps you stand out from your competitors. This easily accessible PPT template is of great value due to its versatile nature. Different businesses can easily take advantage of this template by modifying the content as their needs and demands. Case studies, reports, data analysis, and interpretation can be shown effectively by downloading this well-researched PowerPoint slide. Our Powerpoint Template And Background With Cyber Security Network Data Monitor As Abstract template can elevate your presentations overall appeal due to the high-quality illustrations and images. Align the focus point and discuss the topic for productive brainstorming sessions using this template. Save time and increase productivity by downloading this professionally designed PPT template. Level up your presentation by incorporating an aesthetically pleasing PowerPoint slide and get your audience glued to it till the end.
-
 Icons slide for effective security monitoring plan to eliminate cyber threats and data breaches
Icons slide for effective security monitoring plan to eliminate cyber threats and data breachesIntroducing our well researched set of slides titled Icons Slide For Effective Security Monitoring Plan To Eliminate Cyber Threats And Data Breaches. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Cyber security monitoring tools ppt powerpoint presentation model information cpb
Cyber security monitoring tools ppt powerpoint presentation model information cpbPresenting Cyber Security Monitoring Tools Ppt Powerpoint Presentation Model Information Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Model Employee Service Team. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber attack monitoring ppt powerpoint presentation summary show cpb
Cyber attack monitoring ppt powerpoint presentation summary show cpbPresenting Cyber Attack Monitoring Ppt Powerpoint Presentation Summary Show Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase nine stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Attack Monitoring. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
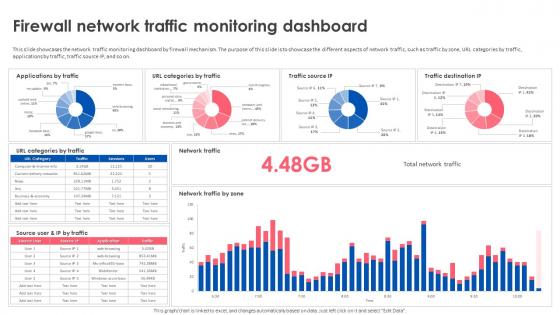 Firewall Implementation For Cyber Security Firewall Network Traffic Monitoring Dashboard
Firewall Implementation For Cyber Security Firewall Network Traffic Monitoring DashboardThis slide showcases the network traffic monitoring dashboard by firewall mechanism. The purpose of this slide is to showcase the different aspects of network traffic, such as traffic by zone, URL categories by traffic, applications by traffic, traffic source IP, and so on. Deliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security Firewall Network Traffic Monitoring Dashboard. Dispense information and present a thorough explanation of Firewall Network Traffic, Monitoring Dashboard, Applications By Traffic, Firewall Mechanism using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.