Powerpoint Templates and Google slides for Cyber
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Icon For Ensuring Cybersecurity In Financial Services Sector
Icon For Ensuring Cybersecurity In Financial Services SectorIntroducing our premium set of slides with Icon For Ensuring Cybersecurity In Financial Services Sector. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon, Ensuring Cybersecurity, Financial Services Sector. So download instantly and tailor it with your information.
-
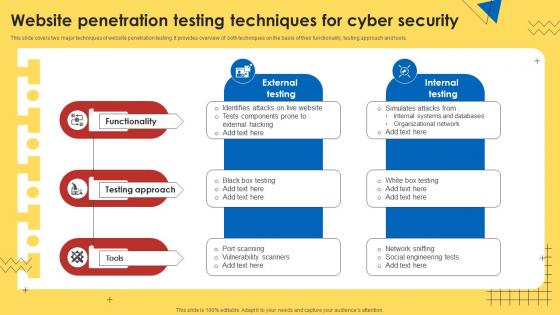 Website Penetration Testing Techniques For Cyber Security
Website Penetration Testing Techniques For Cyber SecurityThis slide covers two major techniques of website penetration testing. It provides overview of both techniques on the basis of their functionality, testing approach and tools. Introducing our premium set of slides with Website Penetration Testing Techniques For Cyber Security. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Functionality, Testing Approach, Tools. So download instantly and tailor it with your information.
-
 30 60 90 Day Plan For Cyber Security Framework Implementation
30 60 90 Day Plan For Cyber Security Framework ImplementationThis slide discusses the 30-60-90-day plan for cyber security framework implementation which include stakeholder alignment, awareness training and so on. Introducing 30 60 90 Day Plan For Cyber Security Framework Implementation to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Stakeholder Alignment, Conduct Initial Gap Analysis, Conduct Awareness Training, using this template. Grab it now to reap its full benefits.
-
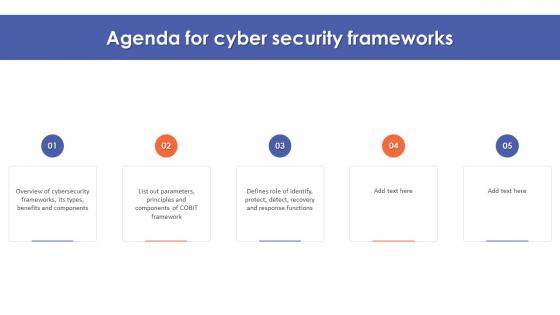 Agenda For Cyber Security Frameworks
Agenda For Cyber Security FrameworksIncrease audience engagement and knowledge by dispensing information using Agenda For Cyber Security Frameworks. This template helps you present information on five stages. You can also present information on Cyber Security Frameworks, Benefits And Components, Response Functions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
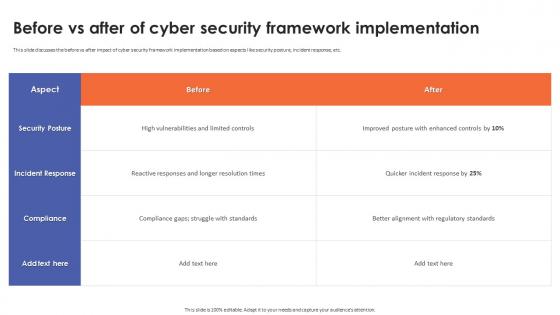 Before Vs After Of Cyber Security Framework Implementation
Before Vs After Of Cyber Security Framework ImplementationThis slide discusses the before vs after impact of cyber security framework implementation based on aspects like security posture, incident response, etc. Present the topic in a bit more detail with this Before Vs After Of Cyber Security Framework Implementation. Use it as a tool for discussion and navigation on Incident Response, Cyber Security, Framework Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
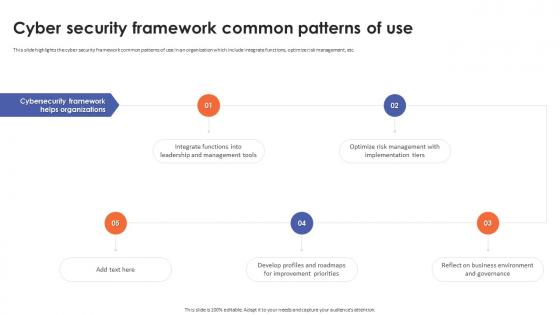 Cyber Security Framework Common Patterns Of Use
Cyber Security Framework Common Patterns Of UseThis slide highlights the cyber security framework common patterns of use in an organization which include integrate functions, optimize risk management, etc. Increase audience engagement and knowledge by dispensing information using Cyber Security Framework Common Patterns Of Use. This template helps you present information on five stages. You can also present information on Cyber Security Framework, Integrate Functions, Optimize Risk Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Framework Implementation Budget
Cyber Security Framework Implementation BudgetThis slide discusses the implementation budget for cyber security framework which includes compliance requirements, risk assessments and security training. Deliver an outstanding presentation on the topic using this Cyber Security Framework Implementation Budget. Dispense information and present a thorough explanation of Compliance Requirements, Risk Assessments, Security Training, Security Requirements For Business Initiatives using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Framework Implementation Challenges
Cyber Security Framework Implementation ChallengesThis slide discusses the major challenges of cyber security framework implementation which include budget constraints, lack of integration and so on. Introducing Cyber Security Framework Implementation Challenges to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Insufficiently Trained Personnel, Budget Constraints, Cyber Security Framework, Implementation Challenges, using this template. Grab it now to reap its full benefits.
-
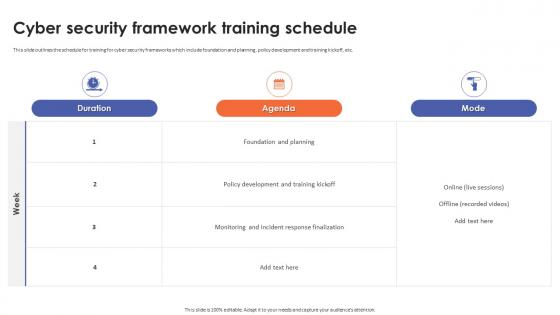 Cyber Security Framework Training Schedule
Cyber Security Framework Training ScheduleThis slide outlines the schedule for training for cyber security frameworks which include foundation and planning, policy development and training kickoff, etc. Present the topic in a bit more detail with this Cyber Security Framework Training Schedule. Use it as a tool for discussion and navigation on Foundation And Planning, Policy Development, Training Kickoff, Incident Response Finalization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
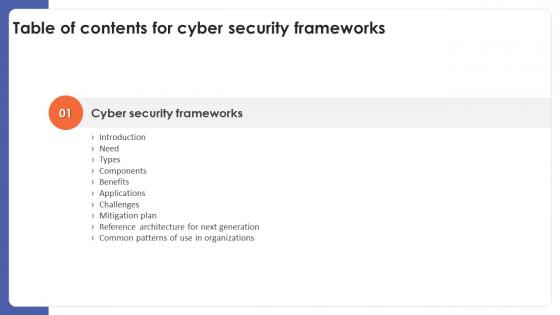 Cyber Security Frameworks For Table Of Contents
Cyber Security Frameworks For Table Of ContentsDeliver an outstanding presentation on the topic using this Cyber Security Frameworks For Table Of Contents. Dispense information and present a thorough explanation of Cyber Security Frameworks, Benefits, Applications, Challenges, Mitigation Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
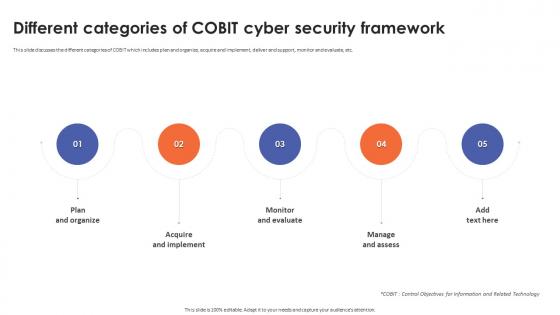 Different Categories Of Cobit Cyber Security Framework
Different Categories Of Cobit Cyber Security FrameworkThis slide discusses the different categories of COBIT which includes plan and organize, acquire and implement, deliver and support, monitor and evaluate, etc. Increase audience engagement and knowledge by dispensing information using Different Categories Of Cobit Cyber Security Framework. This template helps you present information on five stages. You can also present information on Acquire And Implement, Monitor And Evaluate, Plan And Organize, Cyber Security Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Distinct Types Of Cyber Security Frameworks
Distinct Types Of Cyber Security FrameworksThis slide discusses the different types of cyber security framework which includes control frameworks, program frameworks and risk frameworks. Introducing Distinct Types Of Cyber Security Frameworks to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Control Frameworks, Program Frameworks, Risk Frameworks, Cyber Security Frameworks, using this template. Grab it now to reap its full benefits.
-
 Essential Components Of Cyber Security Frameworks
Essential Components Of Cyber Security FrameworksThis slide highlights the key components of cyber security framework which includes framework core, implementation tiers, profiles and so on. Introducing Essential Components Of Cyber Security Frameworks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Framework Core, Implementation Tiers, Guides Vulnerability Reduction , using this template. Grab it now to reap its full benefits.
-
 Identify Function Activities In Cyber Security Framework
Identify Function Activities In Cyber Security FrameworkThis slide is an introduction to the key activities of identify function in cyber security framework which includes identify physical and software assets. Increase audience engagement and knowledge by dispensing information using Identify Function Activities In Cyber Security Framework. This template helps you present information on five stages. You can also present information on Identify Physical And Software Assets, Assess Asset Vulnerabilities, Conduct Risk Response Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Introduction To Cobit Cyber Security Framework
Introduction To Cobit Cyber Security FrameworkThis slide gives an overview of COBIT cyber security framework which provides principles, practices, tools and model to aligning IT strategies with objectives. Introducing Introduction To Cobit Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Emphasizes Risk Management, Cyber Security Framework, Optimizing IT Performance, using this template. Grab it now to reap its full benefits.
-
 Introduction To Cyber Security Frameworks Series
Introduction To Cyber Security Frameworks SeriesThis slide gives an overview to cyber security framework and defines it as a set of documents with guidelines and best practices used for risk management. Increase audience engagement and knowledge by dispensing information using Introduction To Cyber Security Frameworks Series. This template helps you present information on five stages. You can also present information on Organizations Security Methodologies, Used For Risk Management, Guidelines And Best Practices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Iso 27000 Series In Cyber Security Framework
Iso 27000 Series In Cyber Security FrameworkThis slide highlights the ISO 27000 series in cyber security framework which comprises 60 standards addressing various information security issues. Introducing Iso 27000 Series In Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Focuses On Cloud Computing, Protection Of Digital Evidence, Deals With Storage Security, Security In Healthcare, using this template. Grab it now to reap its full benefits.
-
 Iso 27001 And 27002 Cyber Security Frameworks
Iso 27001 And 27002 Cyber Security FrameworksThis slide discusses the concept of two major cyber security frameworks which are ISO 27001 and ISO 27002 following code of practice. Increase audience engagement and knowledge by dispensing information using Iso 27001 And 27002 Cyber Security Frameworks. This template helps you present information on three stages. You can also present information on Code Of Practice, Detailed Security Controls, Systematic Approach To Risk Assessment
-
 Main Applications Of Cyber Security Framework
Main Applications Of Cyber Security FrameworkThis slide outlines the main applications of cyber security framework which includes enhance cybersecurity program, prioritize improvement tasks, etc. Introducing Main Applications Of Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Enhance Cybersecurity Program, Prioritize Improvement Tasks, Know Security Status, Guide Investment Decisions, using this template. Grab it now to reap its full benefits.
-
 Main Components Of Cobit Framework In Cyber Security
Main Components Of Cobit Framework In Cyber SecurityThis slide gives an overview of key components of COBIT which includes process descriptions, control objectives, maturity models and management guidelines. Increase audience engagement and knowledge by dispensing information using Main Components Of Cobit Framework In Cyber Security. This template helps you present information on five stages. You can also present information on Process Descriptions, Maturity Models, Management Guidelines, Control Objectives using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigation Plan For Cyber Security Frameworks
Mitigation Plan For Cyber Security FrameworksThis slide depicts the mitigation plan for cyber security frameworks which include identify and prioritize vulnerabilities, allocate budget and skilled personnel. Increase audience engagement and knowledge by dispensing information using Mitigation Plan For Cyber Security Frameworks. This template helps you present information on five stages. You can also present information on Cyber Security Frameworks, Prioritize Vulnerabilities, Allocate Budget, Skilled Personnel using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Need For Implementing Cyber Security Framework
Need For Implementing Cyber Security FrameworkThis slide highlights the need for implementing cyber security framework which includes easily adaptable and cost efficient, collaboration opportunities, etc. Introducing Need For Implementing Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Collaboration Opportunities, Easily Maintain Compliance, Secure Supply Chain, using this template. Grab it now to reap its full benefits.
-
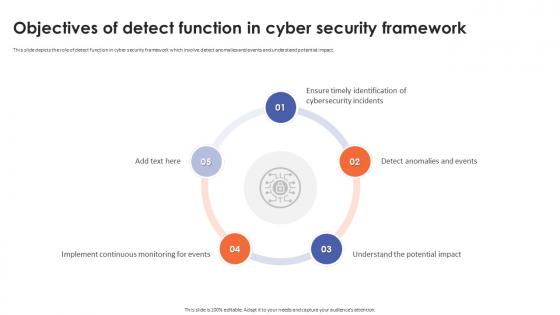 Objectives Of Detect Function In Cyber Security Framework
Objectives Of Detect Function In Cyber Security FrameworkThis slide depicts the role of detect function in cyber security framework which involve detect anomalies and events and understand potential impact. Introducing Objectives Of Detect Function In Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Implement Continuous Monitoring For Events, Understand The Potential Impact, Detect Anomalies And Events, using this template. Grab it now to reap its full benefits.
-
 Overview Of Coso Cyber Security Framework
Overview Of Coso Cyber Security FrameworkThis slide gives an overview of COSO cyber security framework based on key components such as control environment, risk assessment and management. Increase audience engagement and knowledge by dispensing information using Overview Of Coso Cyber Security Framework. This template helps you present information on six stages. You can also present information on Control Environment, Risk Assessment And Management, Control Activities, Information And Communications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
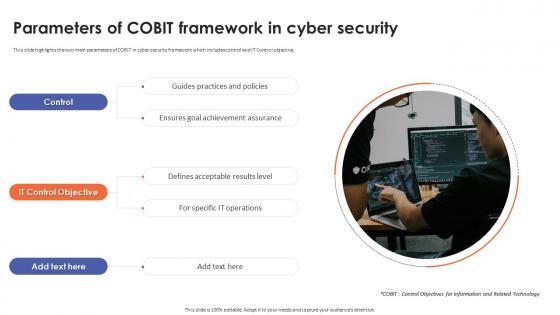 Parameters Of Cobit Framework In Cyber Security
Parameters Of Cobit Framework In Cyber SecurityThis slide highlights the two main parameters of COBIT in cyber security framework which includes control and IT Control objective. Introducing Parameters Of Cobit Framework In Cyber Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Guides Practices And Policies, Ensures Goal Achievement Assurance, Framework In Cyber Security, using this template. Grab it now to reap its full benefits.
-
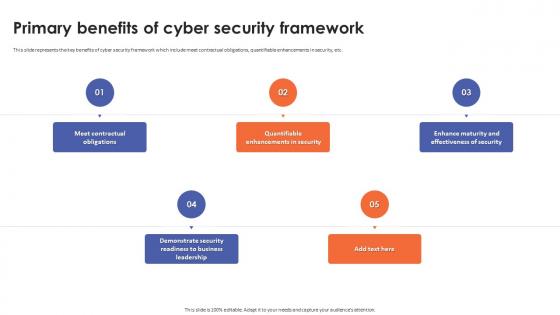 Primary Benefits Of Cyber Security Framework
Primary Benefits Of Cyber Security FrameworkThis slide represents the key benefits of cyber security framework which include meet contractual obligations, quantifiable enhancements in security, etc. Increase audience engagement and knowledge by dispensing information using Primary Benefits Of Cyber Security Framework. This template helps you present information on five stages. You can also present information on Meet Contractual Obligations, Cyber Security Framework, Maturity And Effectiveness Of Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Purpose Of Response Function In Cyber Security Framework
Purpose Of Response Function In Cyber Security FrameworkThis slide highlights the functions of response in cyber security framework which includes execute response plans, manage communications, analyze incidents, etc. Introducing Purpose Of Response Function In Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Event Expansion, Coordinate Communications, Cyber Security Framework, using this template. Grab it now to reap its full benefits.
-
 Recovery Function In Cyber Security Framework
Recovery Function In Cyber Security FrameworkThis slide gives an overview of role of recovery function which includes implement recovery plans, improve strategies and coordinate communications. Increase audience engagement and knowledge by dispensing information using Recovery Function In Cyber Security Framework. This template helps you present information on four stages. You can also present information on Coordinate Communications, Implement Recovery Plans, Cyber Security Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
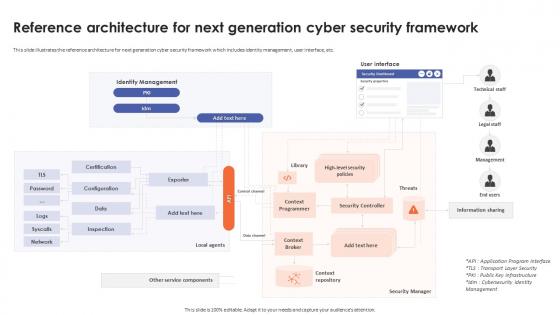 Reference Architecture For Next Generation Cyber Security Framework
Reference Architecture For Next Generation Cyber Security FrameworkThis slide illustrates the reference architecture for next generation cyber security framework which includes identity management, user interface, etc. Deliver an outstanding presentation on the topic using this Reference Architecture For Next Generation Cyber Security Framework. Dispense information and present a thorough explanation of Reference Architecture, Cyber Security Framework, Identity Management, Context Repository using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Role Of Protect Function In Cyber Security Framework
Role Of Protect Function In Cyber Security FrameworkThis slide gives an outline of role of protect function in cyber security framework which controls identity management and secure resources. Introducing Role Of Protect Function In Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Security Awareness Training, Data Security With Risk Strategy, Maintain Information System Protections, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Cyber Security Frameworks
Table Of Contents For Cyber Security FrameworksIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Cyber Security Frameworks. This template helps you present information on seven stages. You can also present information on Types Of Frameworks, Training And Budget, Execution Plan, Cyber Security Frameworks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vital Functions Of Cyber Security Framework
Vital Functions Of Cyber Security FrameworkThis slide gives an overview of the vital functions of cyber security framework which includes identify, protect, detect and respond. Introducing Vital Functions Of Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Recognizes Cybersecurity Incidents, Potential Threats, Structured Cybersecurity Approach, using this template. Grab it now to reap its full benefits.
-
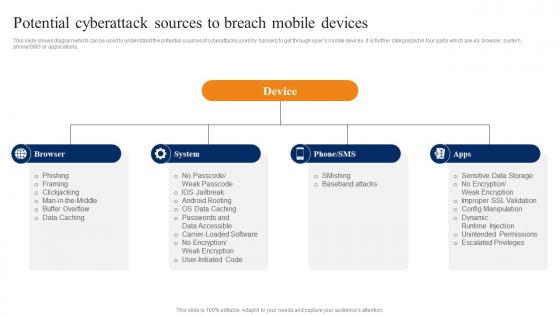 Potential Cyberattack Sources To Breach Smartphone Banking For Transferring Funds Digitally Fin SS V
Potential Cyberattack Sources To Breach Smartphone Banking For Transferring Funds Digitally Fin SS VThis slide shows diagram which can be used to understand the potential sources of cyberattacks used by hackers to get through users mobile devices. It is further categorized in four parts which are via browser, system, phoneSMS or applications. Increase audience engagement and knowledge by dispensing information using Potential Cyberattack Sources To Breach Smartphone Banking For Transferring Funds Digitally Fin SS V. This template helps you present information on one stages. You can also present information on Phishing, Framing, Clickjacking, Man Middle using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
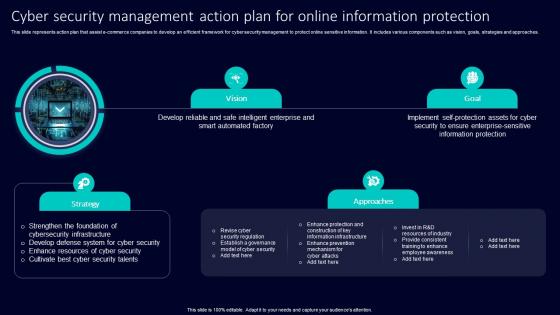 Cyber Security Management Action Plan For Online Information Protection
Cyber Security Management Action Plan For Online Information ProtectionThis slide represents action plan that assist e commerce companies to develop an efficient framework for cyber security management to protect online sensitive information. It includes various components such as vision, goals, strategies and approaches. Presenting our set of slides with Cyber Security Management Action Plan For Online Information Protection. This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strengthen Foundation Cybersecurity Infrastructure, Develop Defense System Cyber Security, Enhance Resources Cyber Security.
-
 System Shock Cyberspace In Powerpoint And Google Slides Cpb
System Shock Cyberspace In Powerpoint And Google Slides CpbPresenting our System Shock Cyberspace In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on System Shock Cyberspace This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
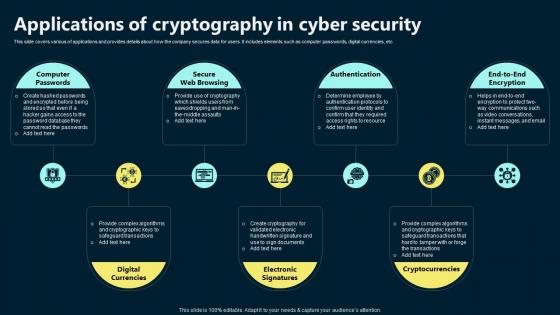 Applications Of Cryptography In Cyber Security
Applications Of Cryptography In Cyber SecurityThis slide covers various of applications and provides details about how the company secures data for users. It includes elements such as computer passwords, digital currencies, etc. Presenting our set of slides with Applications Of Cryptography In Cyber Security. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Computer Passwords, Secure Web Browsing, Authentication.
-
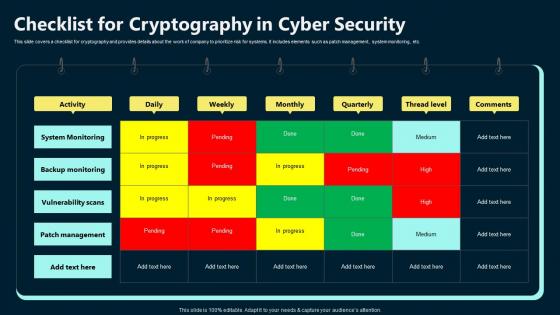 Checklist For Cryptography In Cyber Security
Checklist For Cryptography In Cyber SecurityThis slide covers a checklist for cryptography and provides details about the work of company to prioritize risk for systems. It includes elements such as patch management, system monitoring, etc. Introducing our Checklist For Cryptography In Cyber Security set of slides. The topics discussed in these slides are System Monitoring, Backup Monitoring, Vulnerability Scans . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
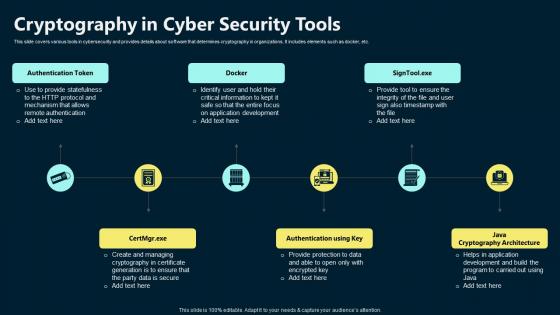 Cryptography In Cyber Security Tools
Cryptography In Cyber Security ToolsThis slide covers various tools in cybersecurity and provides details about software that determines cryptography in organizations. It includes elements such as docker Introducing our premium set of slides with Cryptography In Cyber Security Tools. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Authentication Token, Authentication Using Key, Java Cryptography Architecture. So download instantly and tailor it with your information.
-
 Cryptography In Cybersecurity For Blockchain Icon
Cryptography In Cybersecurity For Blockchain IconPresenting our set of slides with Cryptography In Cybersecurity For Blockchain Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cryptography, Cybersecurity, Blockchain Icon.
-
 Cryptography In Cybersecurity For Business Icon
Cryptography In Cybersecurity For Business IconIntroducing our premium set of slides with Cryptography In Cybersecurity For Business Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Business Icon, Cybersecurity, Cryptography. So download instantly and tailor it with your information.
-
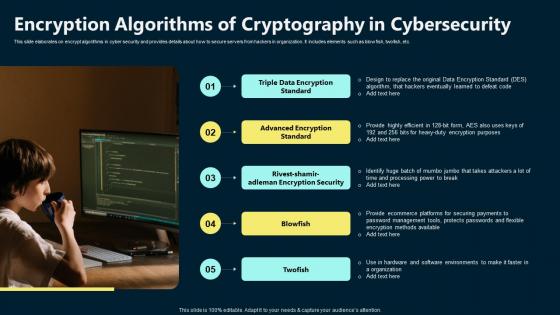 Encryption Algorithms Of Cryptography In Cybersecurity
Encryption Algorithms Of Cryptography In CybersecurityThis slide elaborates on encrypt algorithms in cyber security and provides details about how to secure servers from hackers in organization. It includes elements such as blowfish, twofish, etc. Presenting our set of slides with Encryption Algorithms Of Cryptography In Cybersecurity. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Triple Data Encryption Standard, Advanced Encryption Standard, Blowfish.
-
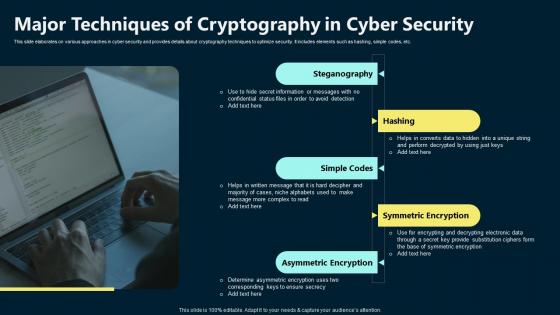 Major Techniques Of Cryptography In Cyber Security
Major Techniques Of Cryptography In Cyber SecurityThis slide elaborates on various approaches in cyber security and provides details about cryptography techniques to optimize security. It includes elements such as hashing, simple codes, etc. Introducing our premium set of slides with Major Techniques Of Cryptography In Cyber Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Steganography, Simple Codes, Symmetric Encryption. So download instantly and tailor it with your information.
-
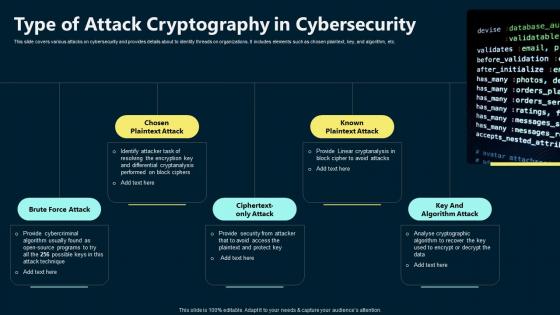 Type Of Attack Cryptography In Cybersecurity
Type Of Attack Cryptography In CybersecurityThis slide covers various attacks on cybersecurity and provides details about to identity threads on organizations. It includes elements such as chosen plaintext, key, and algorithm, etc. Presenting our set of slides with Type Of Attack Cryptography In Cybersecurity. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Brute Force Attack, Key And Algorithm Attack, Known Plaintext Attack.
-
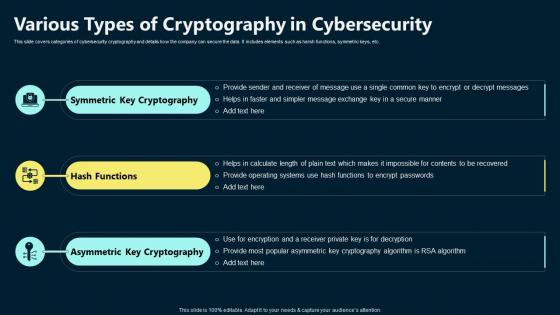 Various Types Of Cryptography In Cybersecurity
Various Types Of Cryptography In CybersecurityThis slide covers categories of cybersecurity cryptography and details how the company can secure the data. It includes elements such as harsh functions, symmetric keys, etc. Introducing our premium set of slides with Various Types Of Cryptography In Cybersecurity. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Symmetric Key Cryptography, Hash Functions, Asymmetric Key Cryptography. So download instantly and tailor it with your information.
-
 Cyber Security Denial Service In Powerpoint And Google Slides Cpb
Cyber Security Denial Service In Powerpoint And Google Slides CpbPresenting Cyber Security Denial Service In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Denial Service. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cybers Security Business In Powerpoint And Google Slides Cpb
Cybers Security Business In Powerpoint And Google Slides CpbPresenting Cybers Security Business In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cybers Security Business. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Largest Cybersecurity Companies Revenue In Powerpoint And Google Slides Cpb
Largest Cybersecurity Companies Revenue In Powerpoint And Google Slides CpbPresenting our Largest Cybersecurity Companies Revenue In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Largest Cybersecurity Companies Revenue. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Awareness In Powerpoint And Google Slides Cpb
Cyber Security Awareness In Powerpoint And Google Slides CpbPresenting Cyber Security Awareness In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Awareness. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber Security Business Network Security In Powerpoint And Google Slides Cpb
Cyber Security Business Network Security In Powerpoint And Google Slides CpbPresenting Cyber Security Business Network Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Business Network Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS VThis slide covers techniques to secure customers confidential data through several cyber security strategies. The purpose for this template is to provide an overview on important elements of top techniques deployed by the company . It includes strategies such as people, process, data and technology and regulatory. Introducing Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on People, Process, Regulatory, using this template. Grab it now to reap its full benefits.
-
 Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS VThis slide covers cyber strategies to protect KPMG customer data protection. The purpose of this template is to provide an overview on top techniques to be implemented to save clients data. It includes strategies such as developing comprehensive understanding of cyber threat landscape, implementing risk based approach, establishing robust security governance framework, etc. Increase audience engagement and knowledge by dispensing information using Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V. This template helps you present information on five stages. You can also present information on Threat Landscape, Cyber Security, Governance Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
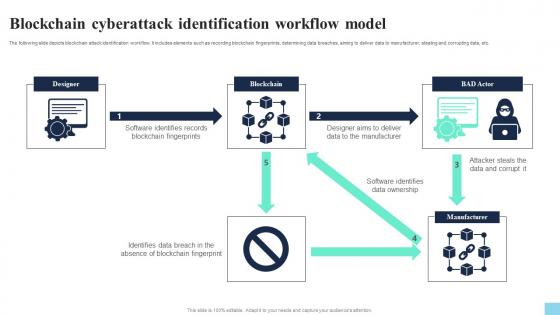 Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS V
Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS VThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Blockchain Fingerprints, Data Ownership, Data And Corrupt. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS V
Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction ,blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS V. Dispense information and present a thorough explanation of Trainer Name, Mode, Proposed Date using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
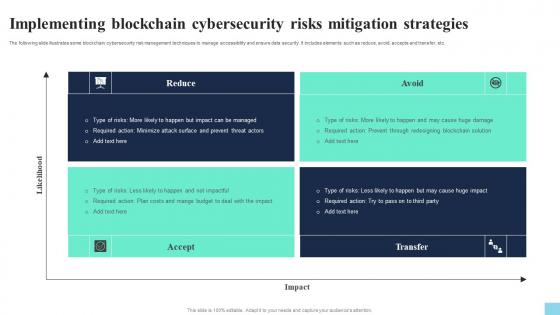 Implementing Blockchain Cybersecurity Risks Mitigation Hands On Blockchain Security Risk BCT SS V
Implementing Blockchain Cybersecurity Risks Mitigation Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Present the topic in a bit more detail with this Implementing Blockchain Cybersecurity Risks Mitigation Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Reduce, Accept, Avoid. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Introducing Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Architecture, Public Key Cryptography, Smart Contracts, using this template. Grab it now to reap its full benefits.
-
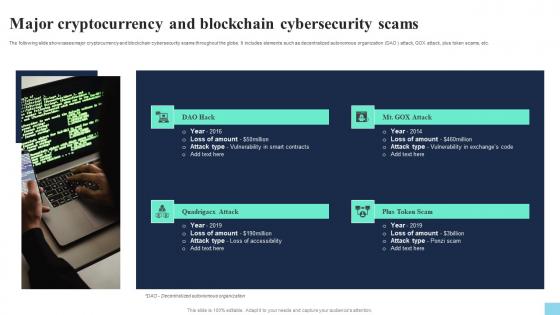 Major Cryptocurrency And Blockchain Cybersecurity Scams Hands On Blockchain Security Risk BCT SS V
Major Cryptocurrency And Blockchain Cybersecurity Scams Hands On Blockchain Security Risk BCT SS VThe following slide showcases major cryptocurrency and blockchain cybersecurity scams throughout the globe. It includes elements such as decentralized autonomous organization DAO attack, GOX attack, plus token scams, etc. Increase audience engagement and knowledge by dispensing information using Major Cryptocurrency And Blockchain Cybersecurity Scams Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Attack Hack, Attack, Plus Token Scam using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
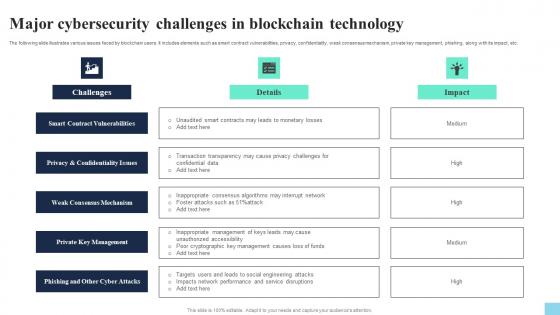 Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide illustrates various issues faced by blockchain users. It includes elements such as smart contract vulnerabilities, privacy, confidentiality, weak consensus mechanism, private key management, phishing, along with its impact, etc. Introducing Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Smart Contract Vulnerabilities, Weak Consensus Mechanism, Private Key Management, using this template. Grab it now to reap its full benefits.
-
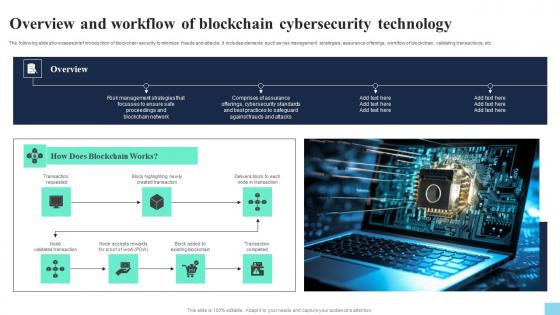 Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS V
Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS VThe following slide showcases brief introduction of blockchain security to minimize frauds and attacks. It includes elements such as risk management strategies, assurance offerings, workflow of blockchain, validating transactions, etc. Increase audience engagement and knowledge by dispensing information using Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS V. This template helps you present information on seven stages. You can also present information on Transaction Requested, Created Transaction, Existing Blockchain using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
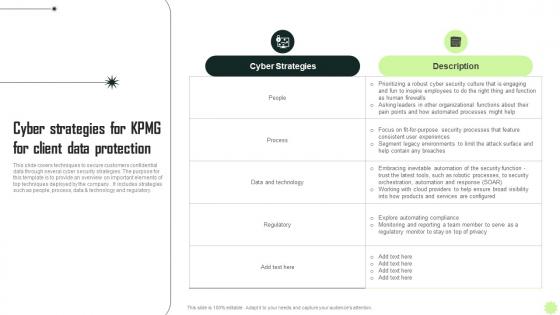 Cyber Strategies For KPMG For Client KPMG Operational And Marketing Strategy SS V
Cyber Strategies For KPMG For Client KPMG Operational And Marketing Strategy SS VThis slide covers techniques to secure customers confidential data through several cyber security strategies. The purpose for this template is to provide an overview on important elements of top techniques deployed by the company. It includes strategies such as people, process, data and technology and regulatory. Present the topic in a bit more detail with this Cyber Strategies For KPMG For Client KPMG Operational And Marketing Strategy SS V. Use it as a tool for discussion and navigation on Strategies, Protection, Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Other Cyber Strategies Of KPMG For Client KPMG Operational And Marketing Strategy SS V
Other Cyber Strategies Of KPMG For Client KPMG Operational And Marketing Strategy SS VThis slide covers cyber strategies to protect KPMG customer data protection. The purpose of this template is to provide an overview on top techniques to be implemented to save clients data. It includes strategies such as developing comprehensive understanding of cyber threat landscape, implementing risk based approach, establishing robust security governance framework, etc. Increase audience engagement and knowledge by dispensing information using Other Cyber Strategies Of KPMG For Client KPMG Operational And Marketing Strategy SS V. This template helps you present information on five stages. You can also present information on Developing, Implementing, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



