Powerpoint Templates and Google slides for Hacked Or Misused
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Ethical Hacking And Network Security White Hat Or Ethical Hackers
Ethical Hacking And Network Security White Hat Or Ethical HackersThis slide represents the white hat or ethical hackers and how they test the information systems of the organizations with the techniques and methods of black hat hackers. Introducing Ethical Hacking And Network Security White Hat Or Ethical Hackers to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on White Hat Or Ethical Hackers, Malware Scans On Networks, Seek To Penetrate Information Systems, Malware Infections, using this template. Grab it now to reap its full benefits.
-
 BYOD Lost Stolen Hacked Or Damaged Equipment Information Technology Policy
BYOD Lost Stolen Hacked Or Damaged Equipment Information Technology PolicyThis slide describes the scenarios of lost, stolen, hacked, or damaged personal equipment under BYOD policy. It also includes that remote wipe software should be installed on employees devices to remove the work data remotely in case of theft. Introducing BYOD Lost Stolen Hacked Or Damaged Equipment Information Technology Policy to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Business, It Department, Employees, using this template. Grab it now to reap its full benefits.
-
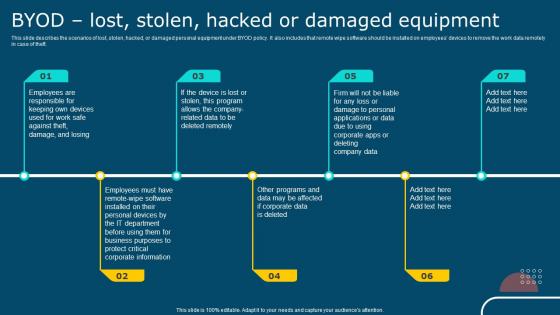 IT Policy Byod Lost Stolen Hacked Or Damaged Equipment
IT Policy Byod Lost Stolen Hacked Or Damaged EquipmentThis slide describes the scenarios of lost, stolen, hacked, or damaged personal equipment under BYOD policy. It also includes that remote wipe software should be installed on employees devices to remove the work data remotely in case of theft. Introducing IT Policy Byod Lost Stolen Hacked Or Damaged Equipment to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Lost, Stolen, Hacked, Damaged Equipment, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Byod Lost Stolen Hacked Or Damaged Equipment
Cyber Security Policy Byod Lost Stolen Hacked Or Damaged EquipmentThis slide describes the scenarios of lost, stolen, hacked, or damaged personal equipment under BYOD policy. It also includes that remote wipe software should be installed on employees devices to remove the work data remotely in case of theft. Introducing Cyber Security Policy Byod Lost Stolen Hacked Or Damaged Equipment to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Equipment, Information, Department, using this template. Grab it now to reap its full benefits.

