Powerpoint Templates and Google slides for IT Cyber Security Chip Icon For Network Protection
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyberterrorism it employee access control protocols ppt slides files
Cyberterrorism it employee access control protocols ppt slides filesThis slide highlights how it is critical to limit employee rights and access in order to keep data safe and prevent it from being deleted or manipulated. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Employee Access Control Protocols Ppt Slides Files. This template helps you present information on one stages. You can also present information on Physical Access Control, Proximity Card, Buildings, And Other Physical Assets, Access Control, Cyber Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it employee awareness training budget against cyber terrorism fy2020
Cyberterrorism it employee awareness training budget against cyber terrorism fy2020This slide demonstrates the employee awareness training budget against cyber-terrorism by a graph that includes the training date, and the degree of capacity. Present the topic in a bit more detail with this Cyberterrorism IT Employee Awareness Training Budget Against Cyber Terrorism FY2020. Use it as a tool for discussion and navigation on Provider, Training Date, Duration, Budget, Capability Level. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyberterrorism it financial loss faced by the business ppt slides idea
Cyberterrorism it financial loss faced by the business ppt slides ideaThis slide depicts the average financial loss faced by the business when projects of different scales are attacked. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Financial Loss Faced By The Business Ppt Slides Idea. This template helps you present information on two stages. You can also present information on Average Financial Loss Per Cyber Attack, Small Project, Medium Project, Large Project using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it how to prevent ddos attacks in the company
Cyberterrorism it how to prevent ddos attacks in the companyThis slide represents the ways to prevent DDoS attacks in the company, which include network monitoring, updating security elements, etc. Introducing Cyberterrorism IT How To Prevent Ddos Attacks In The Company to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Service Providers, Cloud Services, Network Monitoring, Combat Cybercrime, using this template. Grab it now to reap its full benefits.
-
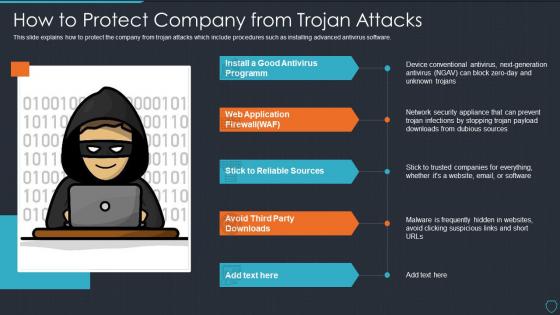 Cyberterrorism it how to protect company from trojan attacks
Cyberterrorism it how to protect company from trojan attacksThis slide explains how to protect the company from trojan attacks which include procedures such as installing advanced antivirus software. Deliver an outstanding presentation on the topic using this Cyberterrorism IT How To Protect Company From Trojan Attacks. Dispense information and present a thorough explanation of Install Good Antivirus Programm, Web Application Firewall, Stick To Reliable Sources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyberterrorism it implementing least privilege administrative model
Cyberterrorism it implementing least privilege administrative modelThis slide depicts that administration and employees should have limited access to the information and confidential data. Introducing Cyberterrorism IT Implementing Least Privilege Administrative Model to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Employees Still, Phishing Emails, Limited Access, Control Risk Levels, Prevent Cybercriminals, using this template. Grab it now to reap its full benefits.
-
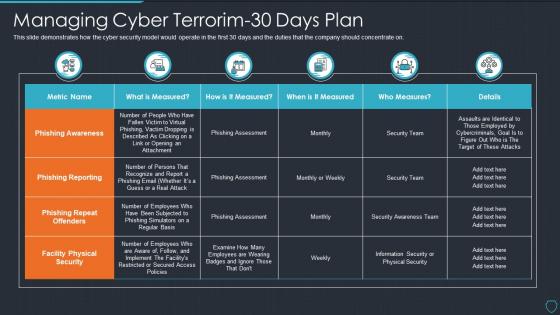 Cyberterrorism it managing cyber terrorim 30 days plan
Cyberterrorism it managing cyber terrorim 30 days planThis slide demonstrates how the cyber security model would operate in the first 30 days and the duties that the company should concentrate on. Present the topic in a bit more detail with this Cyberterrorism IT Managing Cyber Terrorim 30 Days Plan. Use it as a tool for discussion and navigation on Phishing Awareness, Phishing Reporting, Phishing Repeat Offende, Facility Physical Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
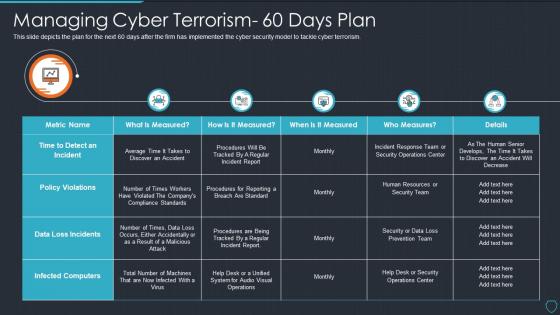 Cyberterrorism it managing cyber terrorism 60 days plan
Cyberterrorism it managing cyber terrorism 60 days planThis slide depicts the plan for the next 60 days after the firm has implemented the cyber security model to tackle cyber terrorism. Deliver an outstanding presentation on the topic using this Cyberterrorism IT Managing Cyber Terrorism 60 Days Plan. Dispense information and present a thorough explanation of Data Loss Incidents, Infected Computers, Policy Violations, Measures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
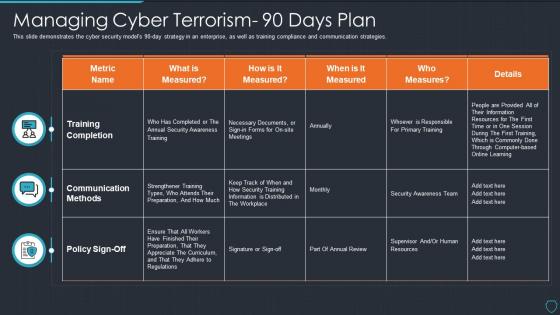 Cyberterrorism it managing cyber terrorism 90 days plan
Cyberterrorism it managing cyber terrorism 90 days planThis slide demonstrates the cyber security models 90 day strategy in an enterprise, as well as training compliance and communication strategies. Present the topic in a bit more detail with this Cyberterrorism IT Managing Cyber Terrorism 90 Days Plan. Use it as a tool for discussion and navigation on Training Completion, Communication Methods, Measured. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyberterrorism it peroration of cyber terrorism ppt slides layout
Cyberterrorism it peroration of cyber terrorism ppt slides layoutThis slide explains the conclusion or peroration of cyber terrorism and how it is different from information warfare as it targets civilians rather than operations. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Peroration Of Cyber Terrorism Ppt Slides Layout. This template helps you present information on six stages. You can also present information on Cyber Terrorism, Information Warfare, Except IT Targets, Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it phishing cyber terrorism tool ppt slides graphics
Cyberterrorism it phishing cyber terrorism tool ppt slides graphicsThis slide describes phishing in which an attacker tricks a victim to open an email, provide card credentials or any sensitive information. Introducing Cyberterrorism IT Phishing Cyber Terrorism Tool Ppt Slides Graphics to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Obtain Sensitive Information, Credit Card Details, Business, Consumer Confidence, using this template. Grab it now to reap its full benefits.
-
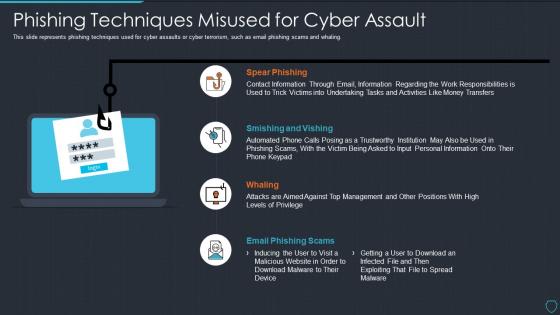 Cyberterrorism it phishing techniques misused for cyber assault
Cyberterrorism it phishing techniques misused for cyber assaultThis slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Phishing Techniques Misused For Cyber Assault. This template helps you present information on four stages. You can also present information on Spear Phishing, Smishing And Vishing, Whaling, Email Phishing Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it reputational loss faced by the company
Cyberterrorism it reputational loss faced by the companyThis slide demonstrates the reputational loss of the company due to cyber terrorism, which leads to the customers leaving and a decline in sales. Introducing Cyberterrorism IT Reputational Loss Faced By The Company to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Assaults Harm, Brand And Diminish, Resolved Claims, using this template. Grab it now to reap its full benefits.
-
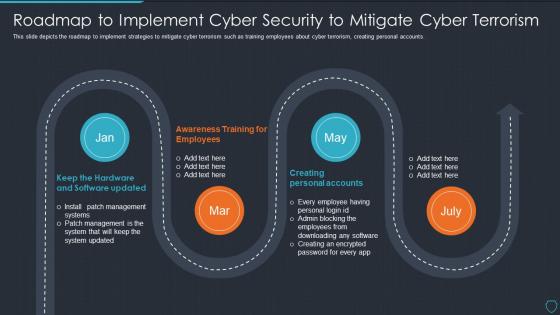 Cyberterrorism it roadmap to implement cyber security to mitigate cyber terrorism
Cyberterrorism it roadmap to implement cyber security to mitigate cyber terrorismThis slide depicts the roadmap to implement strategies to mitigate cyber terrorism such as training employees about cyber terrorism, creating personal accounts. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Roadmap To Implement Cyber Security To Mitigate Cyber Terrorism. This template helps you present information on four stages. You can also present information on Creating Personal Accounts, Awareness Training Employees, Keep Hardware And Software Updated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
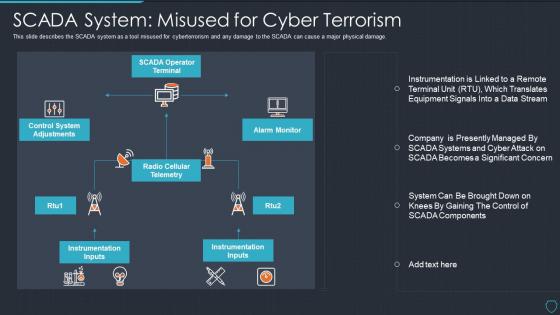 Cyberterrorism it scada system misused for cyber terrorism
Cyberterrorism it scada system misused for cyber terrorismThis slide describes the SCADA system as a tool misused for cyberterrorism and any damage to the SCADA can cause a major physical damage. Introducing Cyberterrorism IT SCADA System Misused For Cyber Terrorism to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on SCADA Operator Terminal, Alarm Monitor, Radio Cellular Telemetry, Control System Adjustments, Instrumentation Inputs, using this template. Grab it now to reap its full benefits.
-
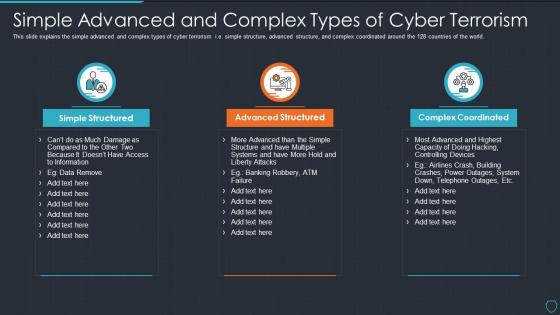 Cyberterrorism it simple advanced and complex types of cyber terrorism
Cyberterrorism it simple advanced and complex types of cyber terrorismThis slide explains the simple advanced and complex types of cyber terrorism i.e. simple structure, advanced structure, and complex coordinated around the 128 countries of the world. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Simple Advanced And Complex Types Of Cyber Terrorism. This template helps you present information on three stages. You can also present information on Simple Structured, Advanced Structured, Complex Coordinated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
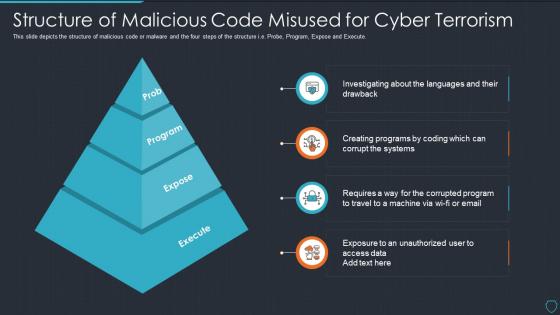 Cyberterrorism it structure of malicious code misused for cyber terrorism
Cyberterrorism it structure of malicious code misused for cyber terrorismThis slide depicts the structure of malicious code or malware and the four steps of the structure i.e. Probe, Program, Expose and Execute. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Structure Of Malicious Code Misused For Cyber Terrorism. This template helps you present information on four stages. You can also present information on Prob, Program, Expose, Execute using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it table of contents for cyber terrorism ppt slides sample
Cyberterrorism it table of contents for cyber terrorism ppt slides samplePresent the topic in a bit more detail with this Cyberterrorism IT Table Of Contents For Cyber Terrorism Ppt Slides Sample. Use it as a tool for discussion and navigation on Assessment Matrix, Cyber Terrorism, Timeline, Dashboard, Threat Tracking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
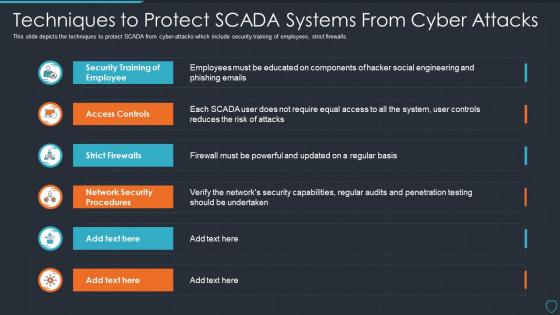 Cyberterrorism it techniques to protect scada systems from cyber attacks
Cyberterrorism it techniques to protect scada systems from cyber attacksThis slide depicts the techniques to protect SCADA from cyber-attacks which include security training of employees, strict firewalls. Deliver an outstanding presentation on the topic using this Cyberterrorism IT Techniques To Protect SCADA Systems From Cyber Attacks. Dispense information and present a thorough explanation of Security Training, Employee, Access Controls, Strict Firewalls, Network Security Procedures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
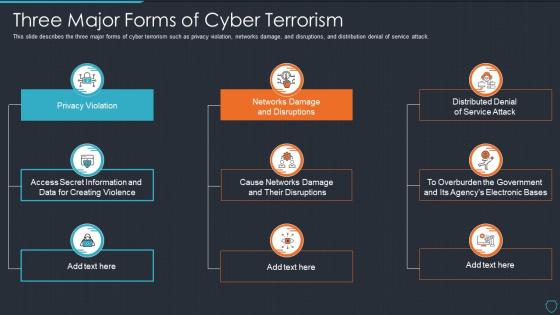 Cyberterrorism it three major forms of cyber terrorism ppt slides tips
Cyberterrorism it three major forms of cyber terrorism ppt slides tipsThis slide describes the three major forms of cyber terrorism such as privacy violation, networks damage, and disruptions, and distribution denial of service attack. Introducing Cyberterrorism IT Three Major Forms Of Cyber Terrorism Ppt Slides Tips to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Violation, Networks Damage And Disruptions, Distributed Denial Service Attack, Cause Networks Damage And Their Disruptions, using this template. Grab it now to reap its full benefits.
-
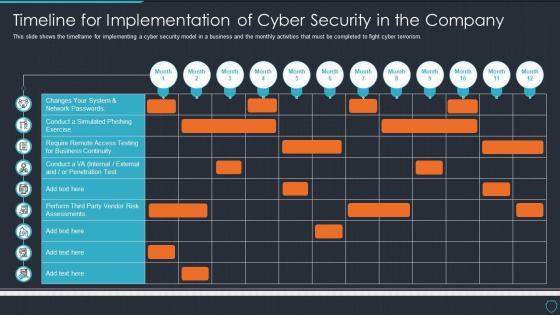 Cyberterrorism it timeline for implementation of cyber security in the company
Cyberterrorism it timeline for implementation of cyber security in the companyThis slide shows the timeframe for implementing a cyber security model in a business and the monthly activities that must be completed to fight cyber terrorism. Present the topic in a bit more detail with this Cyberterrorism IT Timeline For Implementation Of Cyber Security In The Company. Use it as a tool for discussion and navigation on Changes System, Network Passwords, Penetration Test. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
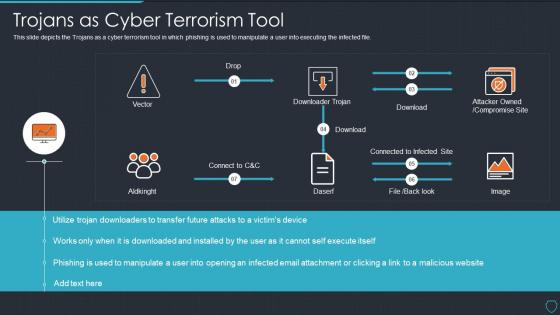 Cyberterrorism it trojans as cyber terrorism tool ppt slides aids
Cyberterrorism it trojans as cyber terrorism tool ppt slides aidsThis slide depicts the Trojans as a cyber terrorism tool in which phishing is used to manipulate a user into executing the infected file. Deliver an outstanding presentation on the topic using this Cyberterrorism IT Trojans As Cyber Terrorism Tool Ppt Slides Aids. Dispense information and present a thorough explanation of Attacker Owned, Compromise Site, Downloader Trojan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
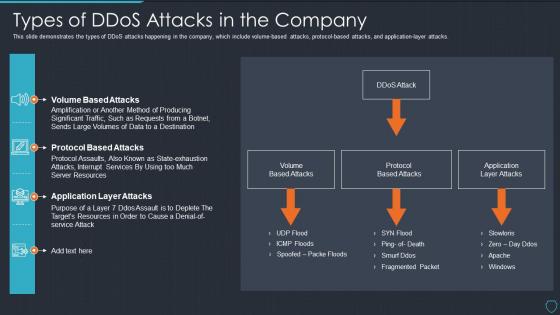 Cyberterrorism it types of ddos attacks in the company ppt slides show
Cyberterrorism it types of ddos attacks in the company ppt slides showThis slide demonstrates the types of DDoS attacks happening in the company, which include volume based attacks, protocol based attacks, and application layer attacks. Present the topic in a bit more detail with this Cyberterrorism IT Types Of Ddos Attacks In The Company Ppt Slides Show. Use it as a tool for discussion and navigation on Ddos Attack Volume, Based Attacks, Protocol Based Attacks, Application Layer Attacks, Volume Based Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
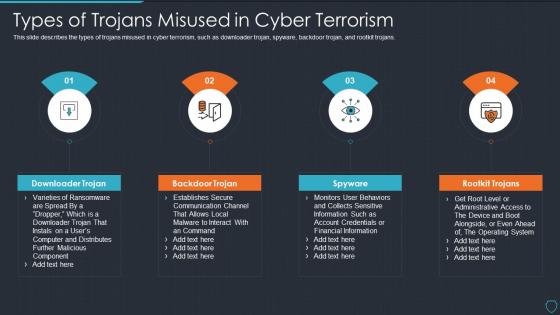 Cyberterrorism it types of trojans misused in cyber terrorism ppt slides tips
Cyberterrorism it types of trojans misused in cyber terrorism ppt slides tipsThis slide describes the types of trojans misused in cyber terrorism, such as downloader trojan, spyware, backdoor trojan, and rootkit trojans. Introducing Cyberterrorism IT Types Of Trojans Misused In Cyber Terrorism Ppt Slides Tips to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Downloader Trojan, Backdoor Trojan, Spyware, Rootkit Trojans, using this template. Grab it now to reap its full benefits.
-
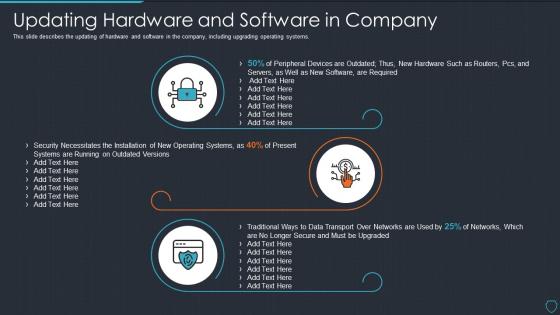 Cyberterrorism it updating hardware and software in company
Cyberterrorism it updating hardware and software in companyThis slide describes the updating of hardware and software in the company, including upgrading operating systems. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Updating Hardware And Software In Company. This template helps you present information on three stages. You can also present information on Peripheral Devices, Security Necessitates, Data Transport using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons slide for cyberterrorism it
Icons slide for cyberterrorism itPresenting our premium Icons Slide For Cyberterrorism IT set of slides with flexible icons. The icons are designed by our group of professionals. Add these Icons Slide For Cyberterrorism IT to your presentation to make it visually appealing. Also, edit them according to your requirement. Download it and captive your audience.
-
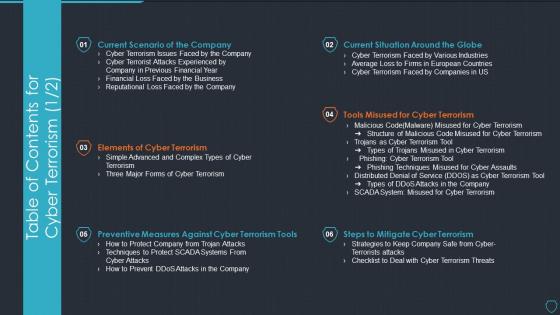 Table of contents for cyber terrorism cyberterrorism it ppt slides tools
Table of contents for cyber terrorism cyberterrorism it ppt slides toolsPresent the topic in a bit more detail with this Table Of Contents For Cyber Terrorism Cyberterrorism IT Ppt Slides Tools. Use it as a tool for discussion and navigation on Current Scenario Company, Elements Cyber Terrorism, Preventive Measures, Against Cyber Terrorism Tools, Steps To Mitigate Cyber Terrorism, Tools Misused Cyber Terrorism, Current Situation Around Globe. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
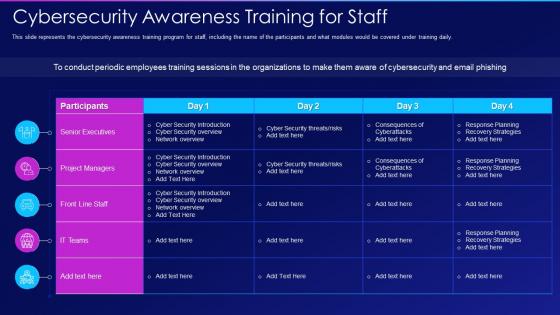 Hacking it cybersecurity awareness training for staff
Hacking it cybersecurity awareness training for staffThis slide represents the cybersecurity awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Present the topic in a bit more detail with this Hacking It Cybersecurity Awareness Training For Staff. Use it as a tool for discussion and navigation on Cybersecurity Awareness Training For Staff. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
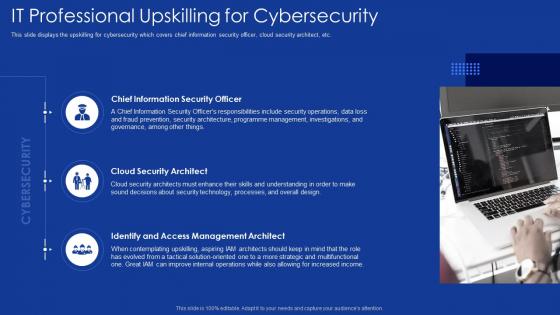 Role of it professionals in digitalization it professional upskilling for cybersecurity
Role of it professionals in digitalization it professional upskilling for cybersecurityThis slide displays the upskilling for cybersecurity which covers chief information security officer, cloud security architect, etc. Increase audience engagement and knowledge by dispensing information using Role Of IT Professionals In Digitalization It Professional Upskilling For Cybersecurity. This template helps you present information on three stages. You can also present information on Chief Information Security Officer, Cloud Security Architect, Identify And Access Management Architect, Security Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
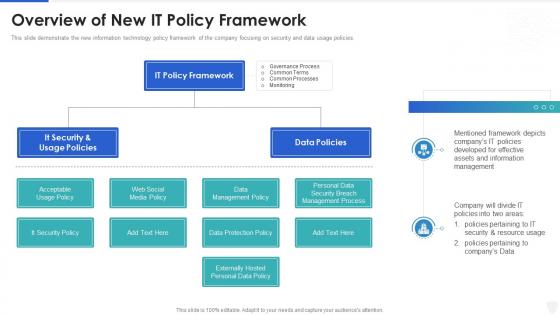 Cybersecurity and digital business risk management overview of new it policy framework
Cybersecurity and digital business risk management overview of new it policy frameworkThis slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies. Deliver an outstanding presentation on the topic using this Cybersecurity And Digital Business Risk Management Overview Of New It Policy Framework. Dispense information and present a thorough explanation of Information, Management, Framework using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
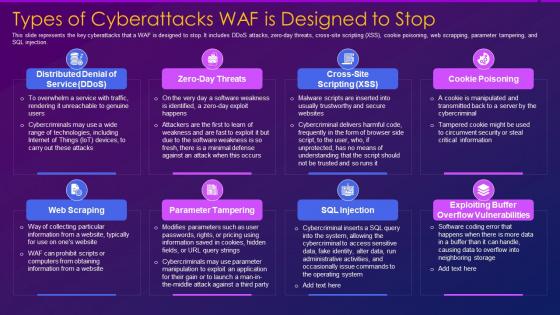 Types of cyberattacks waf is designed web application firewall waf it
Types of cyberattacks waf is designed web application firewall waf itThis slide represents the key cyberattacks that a WAF is designed to stop. It includes DDoS attacks, zero day threats, cross site scripting XSS, cookie poisoning, web scrapping, parameter tampering, and SQL injection. Increase audience engagement and knowledge by dispensing information using Types Of Cyberattacks Waf Is Designed Web Application Firewall Waf It. This template helps you present information on eight stages. You can also present information on Parameter Tampering, Vulnerabilities, Service using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 IT In Manufacturing Industry Managing Cyber Security In Manufacturing 90 Days Plan
IT In Manufacturing Industry Managing Cyber Security In Manufacturing 90 Days PlanThis slide depicts the next 90 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Deliver an outstanding presentation on the topic using this IT In Manufacturing Industry Managing Cyber Security In Manufacturing 90 Days Plan. Dispense information and present a thorough explanation of Communication Methods, Training Completion, Awareness Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
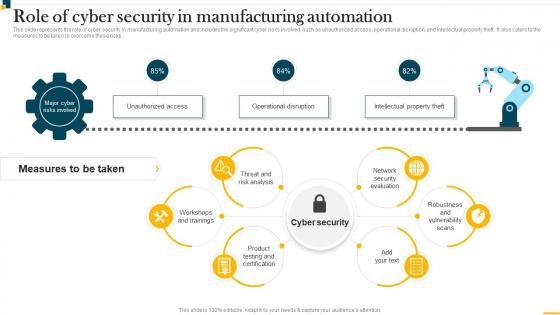 IT In Manufacturing Industry Role Of Cyber Security In Manufacturing Automation
IT In Manufacturing Industry Role Of Cyber Security In Manufacturing AutomationThis slide represents the role of cyber security in manufacturing automation and includes the significant cyber risks involved, such as unauthorized access, operational disruption, and intellectual property theft. It also caters to the measures to be taken to overcome these risks. Present the topic in a bit more detail with this IT In Manufacturing Industry Role Of Cyber Security In Manufacturing Automation. Use it as a tool for discussion and navigation on Threat And Risk Analysis, Network Security Evaluation, Workshops And Trainings. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Managing Cyber Security In Manufacturing 30 Days Plan IT In Manufacturing Industry
Managing Cyber Security In Manufacturing 30 Days Plan IT In Manufacturing IndustryThis slide describes the first 30 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Present the topic in a bit more detail with this Managing Cyber Security In Manufacturing 30 Days Plan IT In Manufacturing Industry. Use it as a tool for discussion and navigation on Phishing Awareness, Facility Physical Security, Phishing Reporting. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Managing Cyber Security In Manufacturing 60 Days Plan IT In Manufacturing Industry
Managing Cyber Security In Manufacturing 60 Days Plan IT In Manufacturing IndustryThis slide represents the next 60 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Deliver an outstanding presentation on the topic using this Managing Cyber Security In Manufacturing 60 Days Plan IT In Manufacturing Industry. Dispense information and present a thorough explanation of Data Loss Incidents, Security Operations Center, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
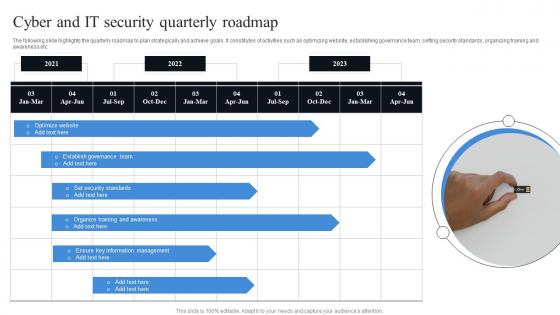 Cyber And It Security Quarterly Roadmap
Cyber And It Security Quarterly RoadmapThe following slide highlights the quarterly roadmap to plan strategically and achieve goals. It constitutes of activities such as optimizing website, establishing governance team, setting security standards, organizing training and awareness etc. Presenting our well structured Cyber And It Security Quarterly Roadmap. The topics discussed in this slide are Optimize Website, Establish Governance Team, Set Security Standards. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Post It Notes Cybersecurity Risk Analysis And Management Plan Ppt Slides Infographic Template
Post It Notes Cybersecurity Risk Analysis And Management Plan Ppt Slides Infographic TemplateIncrease audience engagement and knowledge by dispensing information using Post It Notes Cybersecurity Risk Analysis And Management Plan Ppt Slides Infographic Template. This template helps you present information on four stages. You can also present information on Post It Notes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
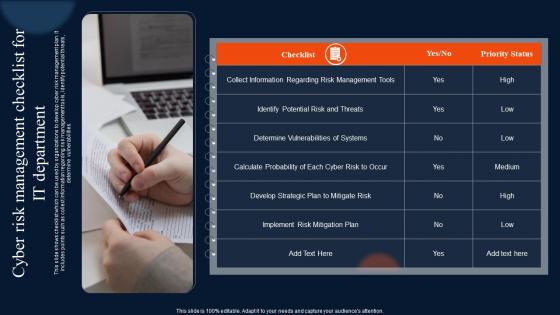 Cyber Risk Management Checklist For It Department
Cyber Risk Management Checklist For It DepartmentThis slide shows checklist which can be used by organizations to develop cyber risk management plan. It includes points such as collect information regarding risk management tools, identify potential threats, determine vulnerabilities. Presenting our well structured Cyber Risk Management Checklist For It Department. The topics discussed in this slide are Management, Department, Information. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
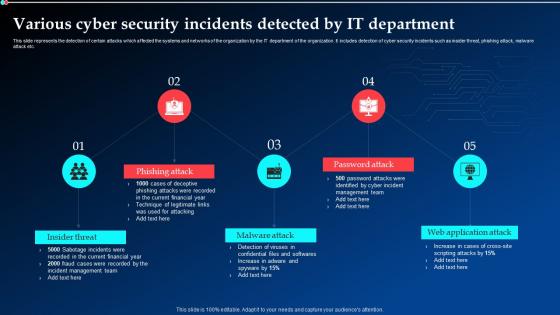 Various Cyber Security Incidents Detected By It Department Ppt Themes
Various Cyber Security Incidents Detected By It Department Ppt ThemesThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Increase audience engagement and knowledge by dispensing information using Various Cyber Security Incidents Detected By It Department Ppt Themes. This template helps you present information on five stages. You can also present information on Phishing Attack, Malware Attack, Password Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
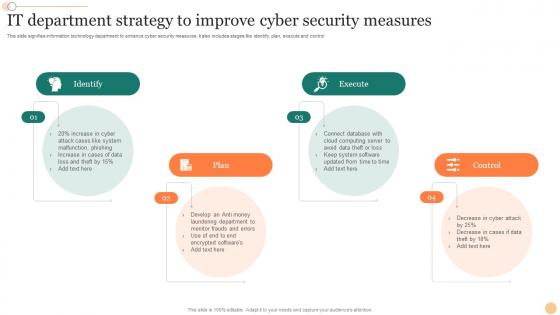 IT Department Strategy To Improve Cyber Security Measures
IT Department Strategy To Improve Cyber Security MeasuresThis slide signifies information technology department to enhance cyber security measures. It also includes stages like identify, plan, execute and control. Presenting our set of slides with name IT Department Strategy To Improve Cyber Security Measures. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Plan, Execute, Control.
-
 Icon Showcasing It Cybersecurity Pain Point
Icon Showcasing It Cybersecurity Pain PointIntroducing our premium set of slides with name Icon Showcasing It Cybersecurity Pain Point. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon Showcasing IT, Testing Expertise. So download instantly and tailor it with your information.
-
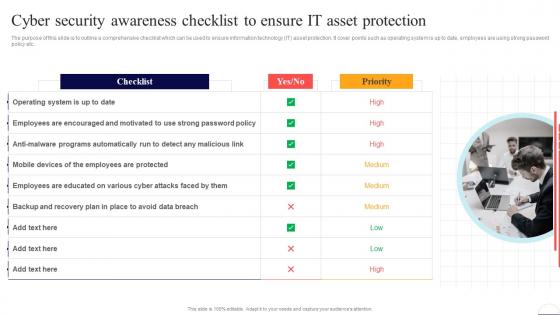 Cyber Security Awareness Checklist To Ensure It Asset Preventing Data Breaches Through Cyber Security
Cyber Security Awareness Checklist To Ensure It Asset Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline a comprehensive checklist which can be used to ensure information technology IT asset protection. It cover points such as operating system is up to date, employees are using strong password policy etc. Introducing Cyber Security Awareness Checklist To Ensure It Asset Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Data Breach, Operating System, using this template. Grab it now to reap its full benefits.
-
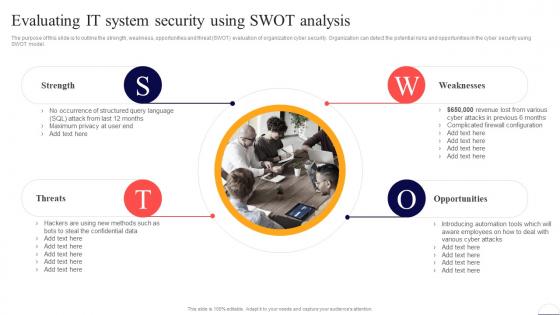 Evaluating It System Security Using Swot Analysis Preventing Data Breaches Through Cyber Security
Evaluating It System Security Using Swot Analysis Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline the strength, weakness, opportunities and threat SWOT evaluation of organization cyber security. Organization can detect the potential risks and opportunities in the cyber security using SWOT model. Increase audience engagement and knowledge by dispensing information using Evaluating It System Security Using Swot Analysis Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Strength, Threats, Weaknesses using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
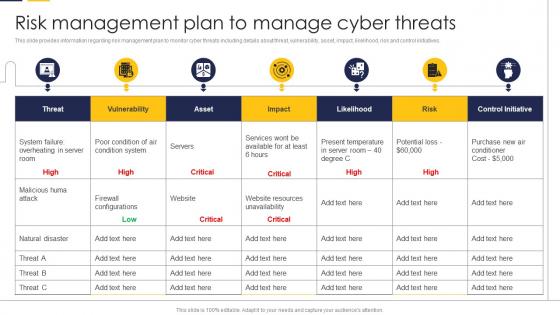 Risk Management Plan To Manage Cyber Threats Guide To Build It Strategy Plan For Organizational Growth
Risk Management Plan To Manage Cyber Threats Guide To Build It Strategy Plan For Organizational GrowthThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Deliver an outstanding presentation on the topic using this Risk Management Plan To Manage Cyber Threats Guide To Build It Strategy Plan For Organizational Growth. Dispense information and present a thorough explanation of Management, Information, Vulnerability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation Plan
IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation PlanThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Increase audience engagement and knowledge by dispensing information using IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation Plan. This template helps you present information on one stages. You can also present information on Threat, Risk, Risk Priority, Risk Reduction Timeline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
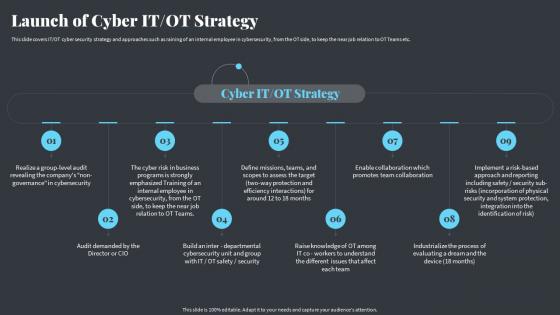 Launch Of Cyber It Ot Strategy Strategies Ot And It Modern Pi System
Launch Of Cyber It Ot Strategy Strategies Ot And It Modern Pi SystemThis slide covers IT or OT cyber security strategy and approaches such as raining of an internal employee in cybersecurity, from the OT side, to keep the near job relation to OT Teams etc. Introducing Launch Of Cyber It Ot Strategy Strategies Ot And It Modern Pi System to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Strategy, Approaches, Cybersecurity, using this template. Grab it now to reap its full benefits.
-
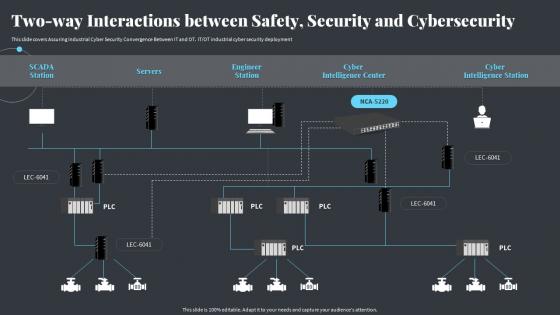 Two Way Interactions Between Safety Security And Cybersecurity Strategies Ot And It Modern Pi System
Two Way Interactions Between Safety Security And Cybersecurity Strategies Ot And It Modern Pi SystemThis slide covers Assuring Industrial Cyber Security Convergence Between IT and OT. IT or OT industrial cyber security deployment Deliver an outstanding presentation on the topic using this Two Way Interactions Between Safety Security And Cybersecurity Strategies Ot And It Modern Pi System. Dispense information and present a thorough explanation of Cybersecurity, Interactions, Intelligence Station using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
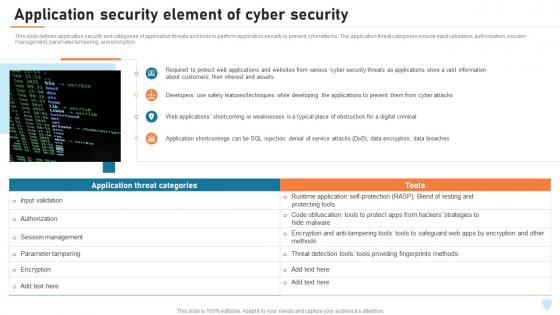 Cyber Security Elements IT Application Security Element Of Cyber Security Ppt Background
Cyber Security Elements IT Application Security Element Of Cyber Security Ppt BackgroundThis slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. The application threat categories include input validation, authorization, session management, parameter tampering, and encryption. Present the topic in a bit more detail with this Cyber Security Elements IT Application Security Element Of Cyber Security Ppt Background. Use it as a tool for discussion and navigation on Session Management, Application Security, Application Threat Categories. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
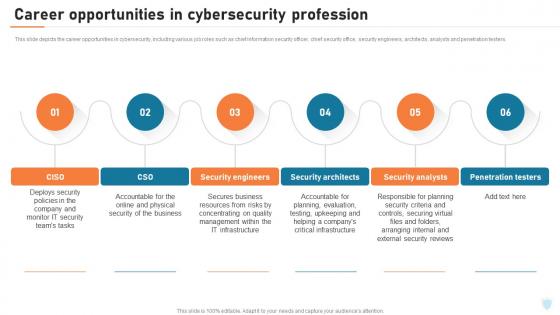 Cyber Security Elements IT Career Opportunities In Cybersecurity Profession Ppt Mockup
Cyber Security Elements IT Career Opportunities In Cybersecurity Profession Ppt MockupThis slide depicts the career opportunities in cybersecurity, including various job roles such as chief information security officer, chief security office, security engineers, architects, analysts and penetration testers. Introducing Cyber Security Elements IT Career Opportunities In Cybersecurity Profession Ppt Mockup to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Deploys Security, Security Engineers, Security Architects, Security Analysts, using this template. Grab it now to reap its full benefits.
-
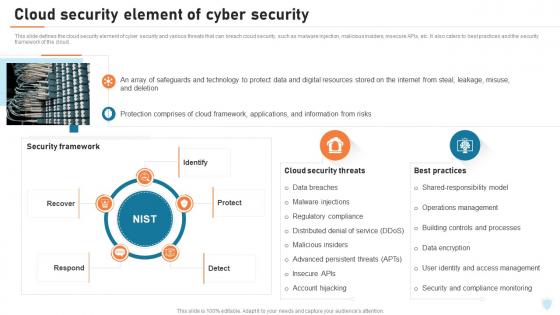 Cyber Security Elements IT Cloud Security Element Of Cyber Security Ppt Slides
Cyber Security Elements IT Cloud Security Element Of Cyber Security Ppt SlidesThis slide defines the cloud security element of cyber security and various threats that can breach cloud security, such as malware injection, malicious insiders, insecure APIs, etc. It also caters to best practices and the security framework of the cloud. Present the topic in a bit more detail with this Cyber Security Elements IT Cloud Security Element Of Cyber Security Ppt Slides. Use it as a tool for discussion and navigation on Security Framework, Protect, Identify, Respond. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
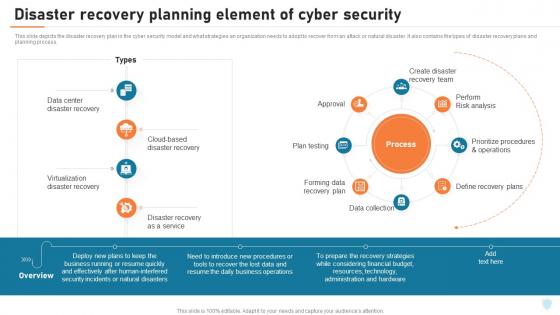 Cyber Security Elements IT Disaster Recovery Planning Element Of Cyber Security Ppt Microsoft
Cyber Security Elements IT Disaster Recovery Planning Element Of Cyber Security Ppt MicrosoftThis slide depicts the disaster recovery plan in the cyber security model and what strategies an organization needs to adopt to recover from an attack or natural disaster. It also contains the types of disaster recovery plans and planning process. Deliver an outstanding presentation on the topic using this Cyber Security Elements IT Disaster Recovery Planning Element Of Cyber Security Ppt Microsoft. Dispense information and present a thorough explanation of Disaster Recovery, Planning Element, Cyber Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Elements IT End User Security Element Of Cyber Security Ppt Sample
Cyber Security Elements IT End User Security Element Of Cyber Security Ppt SampleThis slide shows the end user education within the cyber security model. It also represents various factors that effective training plans should involve, such as hiring professionals, identifying weakest points in systems, assessing employees knowledge of cyber security and so on. Introducing Cyber Security Elements IT End User Security Element Of Cyber Security Ppt Sample to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Security Element, Cyber Security, Microlearning Opportunities, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Elements IT Information Security Element Of Cyber Security Ppt Microsoft
Cyber Security Elements IT Information Security Element Of Cyber Security Ppt MicrosoftThis slide depicts the information security methodology and core information security principles such as confidentiality, integrity, and availability. These are also known as cyber security objectives. Increase audience engagement and knowledge by dispensing information using Cyber Security Elements IT Information Security Element Of Cyber Security Ppt Microsoft. This template helps you present information on three stages. You can also present information on Confidentiality, Availability, Integrity, Information Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Elements IT Network Security Element Of Cyber Security Ppt Background
Cyber Security Elements IT Network Security Element Of Cyber Security Ppt BackgroundThis slide represents the network security element of cyber security and different network security methods such as firewalls, email security, web security, end point security, virtual private security and antivirus software. Introducing Cyber Security Elements IT Network Security Element Of Cyber Security Ppt Background to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Email Security, Virtual Private Network, Antivirus Software, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Elements IT Operational Security Element Of Cyber Security Ppt Introduction
Cyber Security Elements IT Operational Security Element Of Cyber Security Ppt IntroductionThis slide defines the operational security element of cyber security. It also shows the best practices for operational security, such as changing management processes, deploying automation, planning for disasters, restricting device access, and implementing dual control. Increase audience engagement and knowledge by dispensing information using Cyber Security Elements IT Operational Security Element Of Cyber Security Ppt Introduction. This template helps you present information on five stages. You can also present information on Deploy Automation, Restrict Device Access, Change Management Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
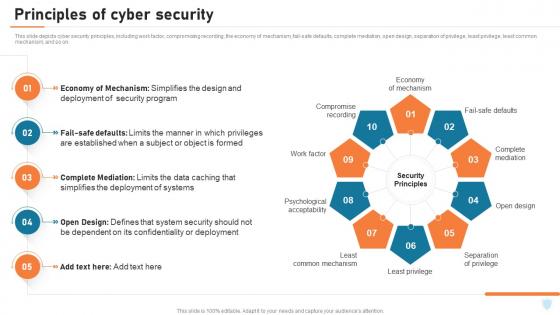 Cyber Security Elements IT Principles Of Cyber Security Ppt Demonstration
Cyber Security Elements IT Principles Of Cyber Security Ppt DemonstrationThis slide depicts cyber security principles, including work factor, compromising recording, the economy of mechanism, fail safe defaults, complete mediation, open design, separation of privilege, least privilege, least common mechanism, and so on. Introducing Cyber Security Elements IT Principles Of Cyber Security Ppt Demonstration to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Separation Of Privilege, Open Design, Economy Of Mechanism, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Elements IT Tools Used For Cyber Security Goals Ppt Brochure
Cyber Security Elements IT Tools Used For Cyber Security Goals Ppt BrochureThis slide outlines the tools used to achieve cyber security goals such as confidentiality, integrity, and availability. The tools for confidentiality include encryption, access control, authentication, authentication, authorization, and physical security. Increase audience engagement and knowledge by dispensing information using Cyber Security Elements IT Tools Used For Cyber Security Goals Ppt Brochure. This template helps you present information on one stage. You can also present information on Tools For Confidentiality, Tools For Integrity, Tools For Availability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Elements IT Types Of Cyber Attackers Ppt Professional
Cyber Security Elements IT Types Of Cyber Attackers Ppt ProfessionalThis slide represents the types of cyber attackers, including cyber criminals, hacktivists, state sponsored attackers, and insider threats. Insider threats can be occurred from within the organization and can be malicious, accidental or negligent. Introducing Cyber Security Elements IT Types Of Cyber Attackers Ppt Professional to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Criminals, Insider Threats, Hacktivists, using this template. Grab it now to reap its full benefits.
-
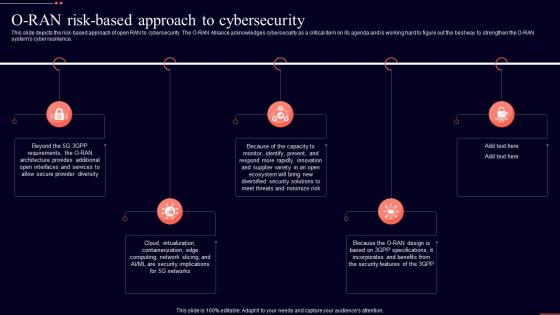 O Ran Risk Based Approach To Cybersecurity Open Ran It Ppt Show Graphics Download
O Ran Risk Based Approach To Cybersecurity Open Ran It Ppt Show Graphics DownloadThis slide depicts the risk-based approach of open RAN to cybersecurity. The O-RAN Alliance acknowledges cybersecurity as a critical item on its agenda and is working hard to figure out the best way to strengthen the O-RAN systems cyber resilience. Introducing O Ran Risk Based Approach To Cybersecurity Open Ran It Ppt Show Graphics Download to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Approach, Cybersecurity, Incorporates, using this template. Grab it now to reap its full benefits.
-
 Evaluating It System Security Using Swot Analysis Developing Cyber Security Awareness Training Program
Evaluating It System Security Using Swot Analysis Developing Cyber Security Awareness Training ProgramThe purpose of this slide is to outline the strength, weakness, opportunities and threat SWOT evaluation of organization cyber security. Organization can detect the potential risks and opportunities in the cyber security using SWOT model. Introducing Evaluating It System Security Using Swot Analysis Developing Cyber Security Awareness Training Program to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strengths, Weaknesses, Opportunities, Threats, using this template. Grab it now to reap its full benefits.



