Powerpoint Templates and Google slides for Threat From Competitors
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
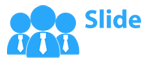
 Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS V
Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS VThe following slide illustrates some methods to protect blockchain network users from honeypot scams and implement defensive actions. It includes elements such as no dead coins, audits, check social media, scrutinize website, etc. Introducing Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on No Dead Coins, Check Social Media, Scrutinize Website using this template. Grab it now to reap its full benefits.
-
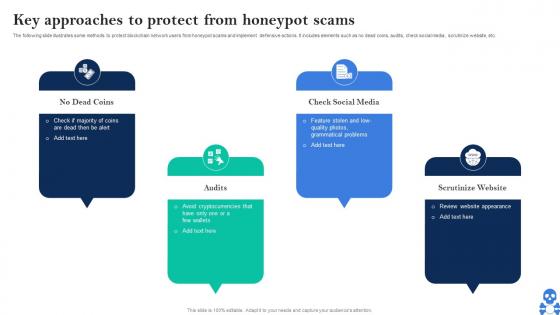
 How To Protect Company From Trojan Attacks Cyber Terrorism Attacks
How To Protect Company From Trojan Attacks Cyber Terrorism AttacksThis slide explains how to protect the company from trojan attacks which include procedures such as installing advanced antivirus software. Increase audience engagement and knowledge by dispensing information using How To Protect Company From Trojan Attacks Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Antivirus Programm, Application Firewall, Reliable Sources, Avoid Third Party Downloads using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
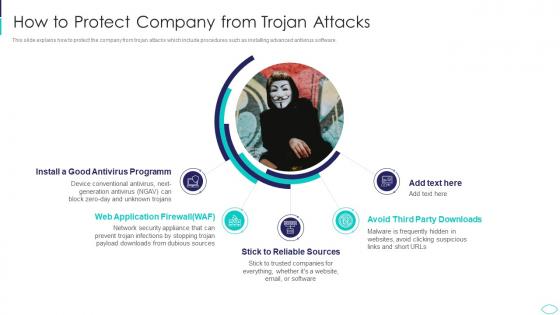
 Strategies To Keep Company Safe From Cyber Terrorism Attacks
Strategies To Keep Company Safe From Cyber Terrorism AttacksThis slide describes the checklist to deal with cyber terrorism threats and counter it such as go after the perpetrators and prosecute them. Introducing Strategies To Keep Company Safe From Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Reduce, Implemented, Restoration, Organization, using this template. Grab it now to reap its full benefits.
-
 Techniques To Protect SCADA Systems From Cyber Terrorism Attacks
Techniques To Protect SCADA Systems From Cyber Terrorism AttacksThis slide depicts the techniques to protect SCADA from cyber attacks which include security training of employees, strict firewalls. Increase audience engagement and knowledge by dispensing information using Techniques To Protect SCADA Systems From Cyber Terrorism Attacks. This template helps you present information on six stages. You can also present information on Security Training, Access Controls, Strict Firewalls, Security Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
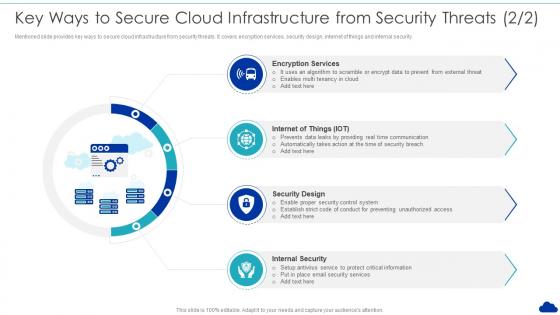 Key Ways To Secure Cloud Infrastructure From Security Threats Optimization Of Cloud Computing
Key Ways To Secure Cloud Infrastructure From Security Threats Optimization Of Cloud ComputingMentioned slide provides key ways to secure cloud infrastructure from security threats. It covers encryption services, security design, internet of things and internal security.Introducing Key Ways To Secure Cloud Infrastructure From Security Threats Optimization Of Cloud Computing to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Key Takeaways, Hardware Maintenance, Improvement In Service using this template. Grab it now to reap its full benefits.
-
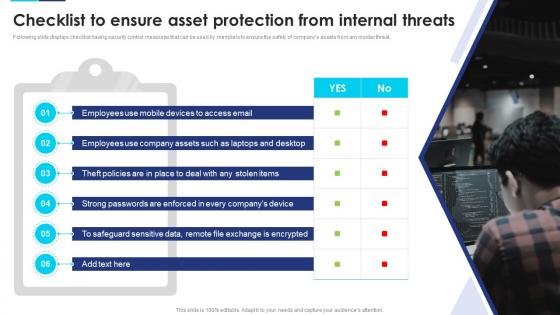 Incident Response Playbook Checklist To Ensure Asset Protection From Internal Threats
Incident Response Playbook Checklist To Ensure Asset Protection From Internal ThreatsFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Introducing Incident Response Playbook Checklist To Ensure Asset Protection From Internal Threats to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Mobile Devices, Company Assets, Employees, using this template. Grab it now to reap its full benefits.
-
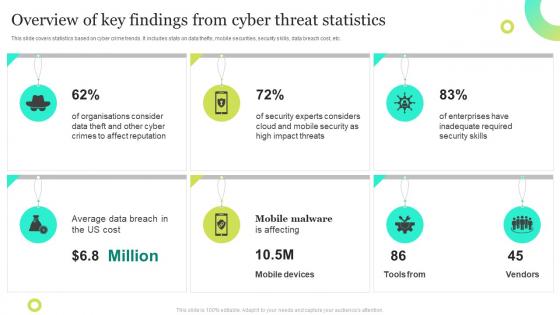 Overview Of Key Findings From Cyber Threat Statistics
Overview Of Key Findings From Cyber Threat StatisticsThis slide covers statistics based on cyber crime trends. It includes stats on data thefts, mobile securities, security skills, data breach cost, etc. Presenting our set of slides with Overview Of Key Findings From Cyber Threat Statistics. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Crimes, Mobile Security, Mobile Devices.
-
 Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability
Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And VulnerabilityFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Introducing Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Email, Mobile Devices, using this template. Grab it now to reap its full benefits.
-
 Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook
Checklist To Ensure Asset Protection From Internal Threats Security Incident Response PlaybookFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Deliver an outstanding presentation on the topic using this Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook. Dispense information and present a thorough explanation of Protection, Measures, Ensure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Project management consultant away from threats powerpoint templates ppt backgrounds for slides 0617
Project management consultant away from threats powerpoint templates ppt backgrounds for slides 0617We are proud to present our project management consultant away from threats powerpoint templates ppt backgrounds for slides 0617. Project management consultant for marketing strategy and stay away from threats is displayed in Power Point template. This diagram can be used for different business project management and result display in a power point presentation.
-
 Firewall for network protection from external threats icon
Firewall for network protection from external threats iconPresenting this set of slides with name Firewall For Network Protection From External Threats Icon. This is a three stage process. The stages in this process are Firewall For Network Protection From External Threats Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Icon depicting computer security from cyber threat
Icon depicting computer security from cyber threatPresenting this set of slides with name Icon Depicting Computer Security From Cyber Threat. This is a three stage process. The stages in this process are Icon Depicting Computer Security From Cyber Threat. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Icon of laptop protected with security software from cyber threat
Icon of laptop protected with security software from cyber threatPresenting this set of slides with name Icon Of Laptop Protected With Security Software From Cyber Threat. This is a three stage process. The stages in this process are Icon Of Laptop Protected With Security Software From Cyber Threat. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Icon showing database server security from cyber threat
Icon showing database server security from cyber threatPresenting this set of slides with name Icon Showing Database Server Security From Cyber Threat. This is a three stage process. The stages in this process are Icon Showing Database Server Security From Cyber Threat. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Icon depicting protection of datacenter from external threats
Icon depicting protection of datacenter from external threatsIntroducing our premium set of slides with Icon Depicting Protection Of Datacenter From External Threats. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon Depicting Protection Of Datacenter From External Threats. So download instantly and tailor it with your information.
-
 Cybercrime threat from hacker icon with virus image on screen
Cybercrime threat from hacker icon with virus image on screenIntroducing our premium set of slides with name Cybercrime Threat From Hacker Icon With Virus Image On Screen. Elucidate the one stage and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cybercrime Threat From Hacker Icon With Virus Image On Screen. So download instantly and tailor it with your information.
-
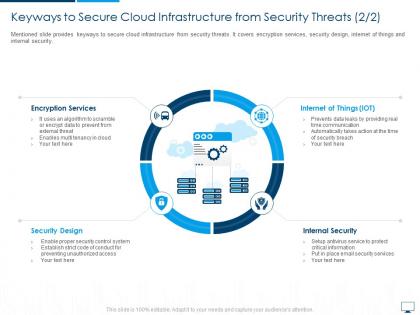 Keyways to secure cloud infrastructure from security threats cloud computing infrastructure adoption plan
Keyways to secure cloud infrastructure from security threats cloud computing infrastructure adoption planMentioned slide provides keyways to secure cloud infrastructure from security threats. It covers encryption services, security design, internet of things and internal security. Introducing Keyways To Secure Cloud Infrastructure From Security Threats Cloud Computing Infrastructure Adoption Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Encryption Services, Internet Of Things, Security Design, Internal Security, using this template. Grab it now to reap its full benefits.