Enterprise security operations powerpoint presentation slides
Our Enterprise Security Operations Powerpoint Presentation Slides are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Deliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Enterprise Security Operations Powerpoint Presentation Slides is the best tool you can utilize. Personalize its content and graphics to make it unique and thought provoking. All the fifty five slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
Slide 1: This is the title slide illustrating Enterprise Security Operations.
Slide 2: This is a Table of Contents slide including Present Scenario Assessment, Security Operations Implementation Timeline, Impact Analysis, etc.
Slide 3: This is a table of contents slide showing the Present Scenario Assessment.
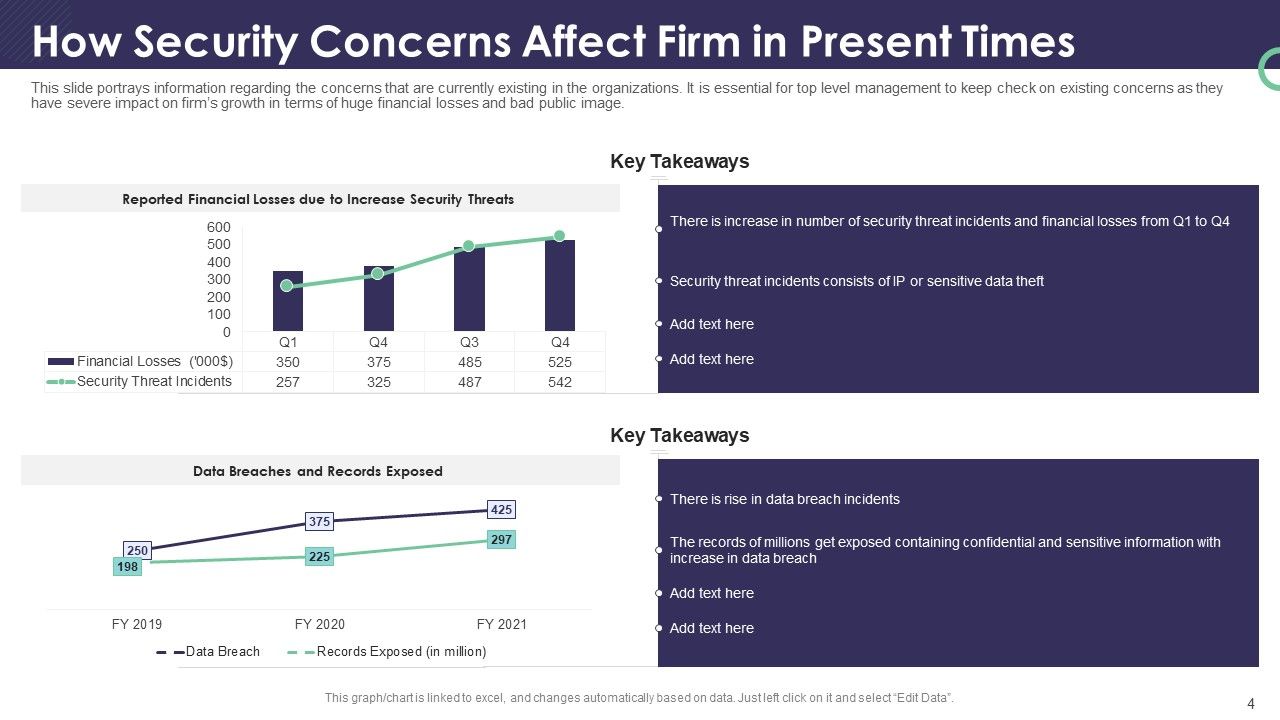
Slide 4: This slide portrays information regarding the concerns that currently exist in the organizations. It is essential for top-level management to keep a check on existing concerns as they have a severe impact on the firm’s growth in terms of huge financial losses and bad public image.
Slide 5: This slide portrays information regarding the various threats that are faced by firms at present times with their cause of the threat, risks associated with threats, the occurrence of threats, and monetary loss to the firm.
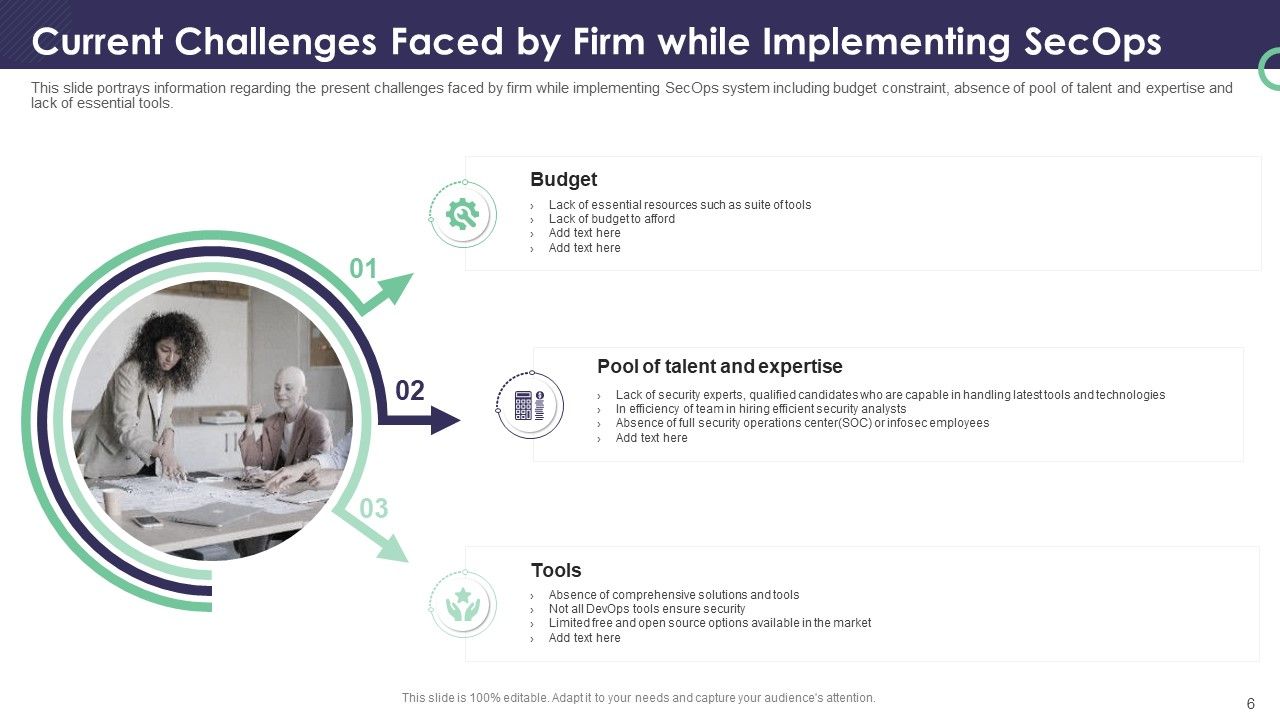
Slide 6: This slide portrays information regarding the present challenges faced by firms while implementing the SecOps system, including budget constraints, the absence of a pool of talent and expertise, and the lack of essential tools.
Slide 7: This is a table of contents slide showing Moving Towards Security Operations Collaboration.
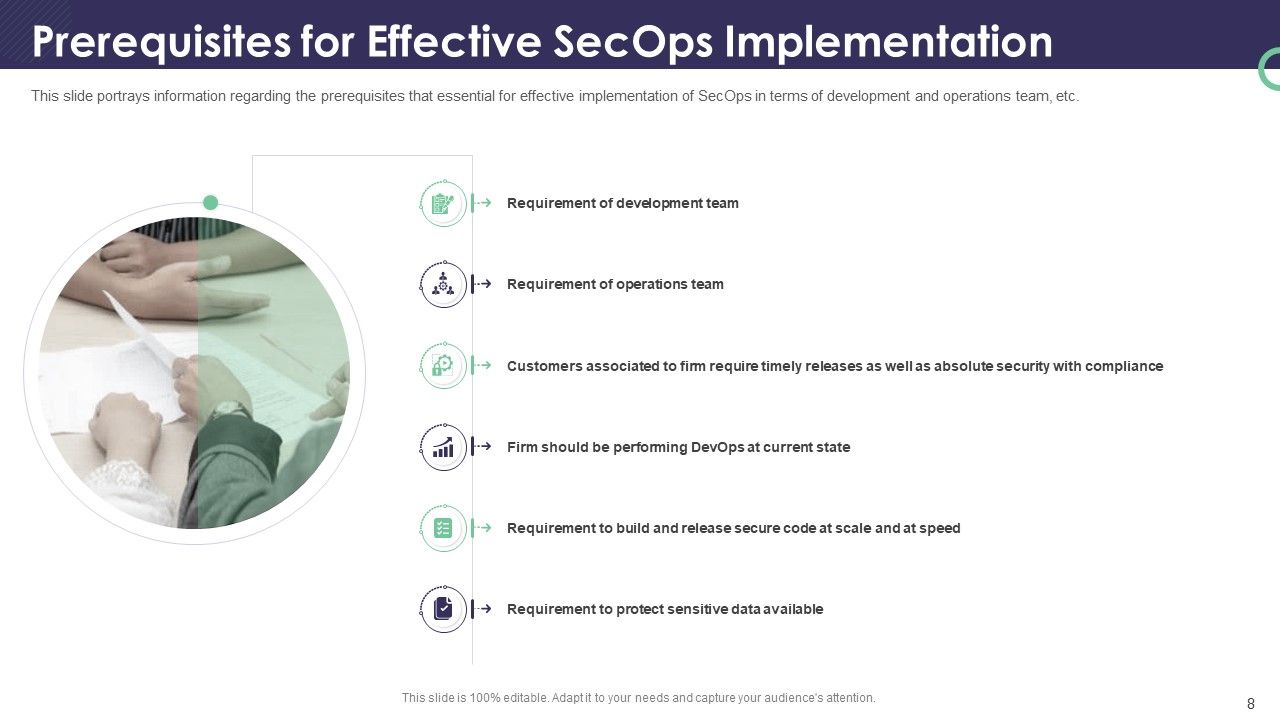
Slide 8: This slide portrays information regarding the prerequisites that are essential for effective implementation of SecOps in terms of development and operations team, etc.
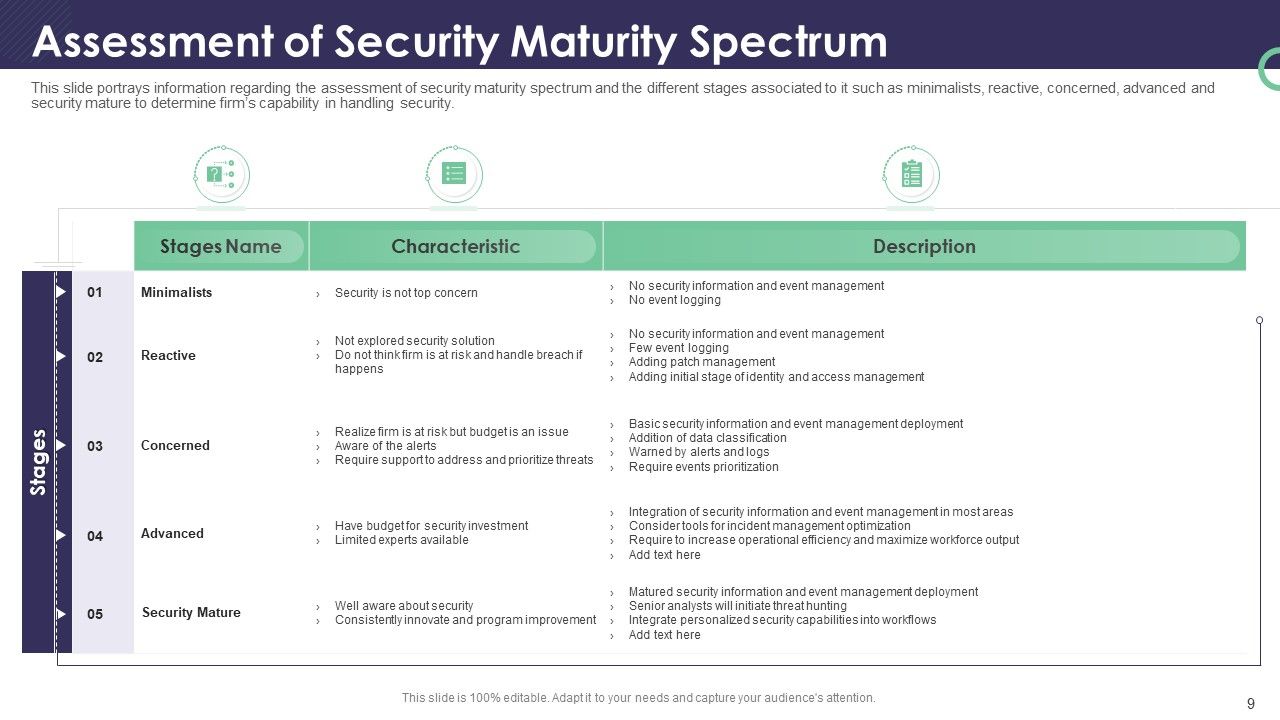
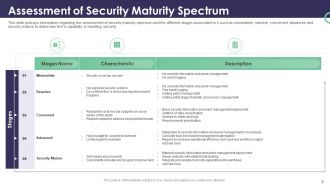
Slide 9: This slide portrays information regarding the assessment of the security maturity spectrum and the different stages associated with it, such as minimalists, reactive, concerned, advanced, and security mature, to determine the firm’s capability in handling safety.
Slide 10: This is a table of contents slide showing the Security Operations Implementation Timeline.
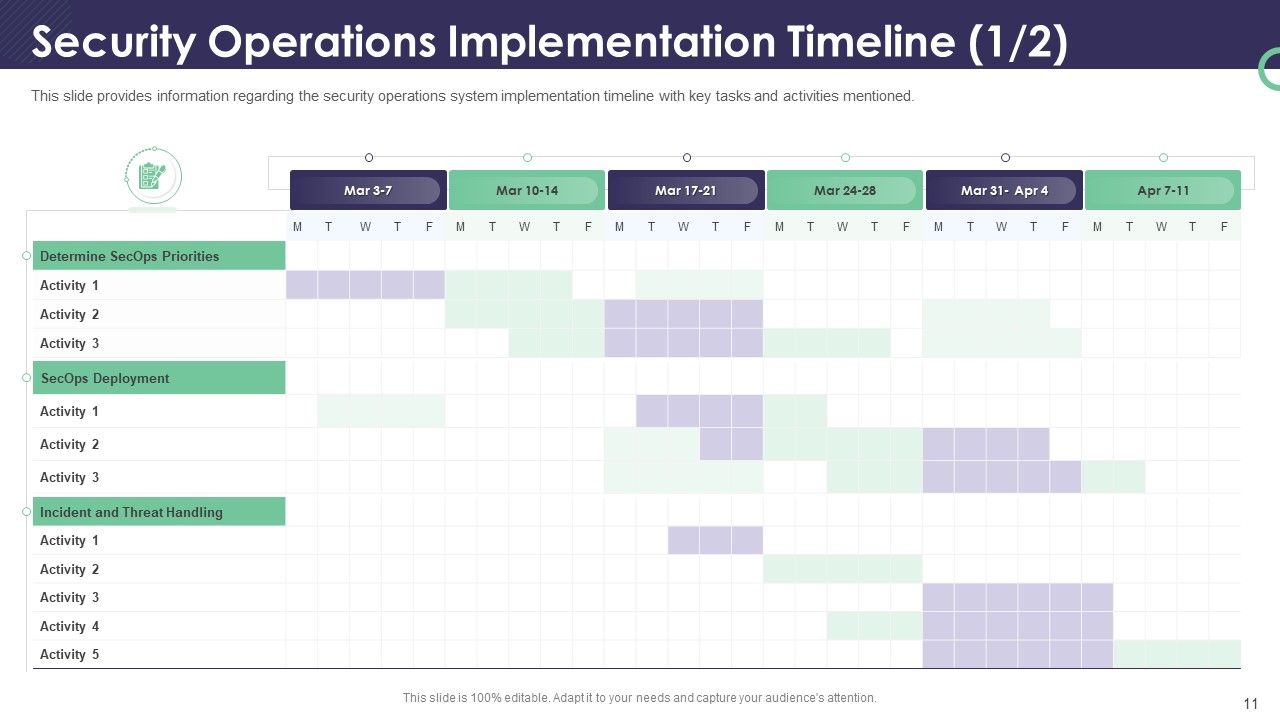
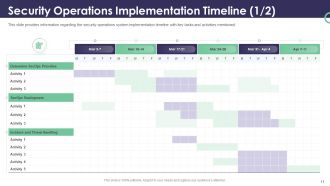
Slide 11: This slide provides information regarding the security operations system implementation timeline with key tasks and activities mentioned.
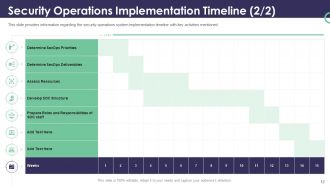
Slide 12: This slide provides the security operations system implementation timeline with key activities mentioned.
Slide 13: This is a table of contents slide showing the Developing Security Operations Centre.
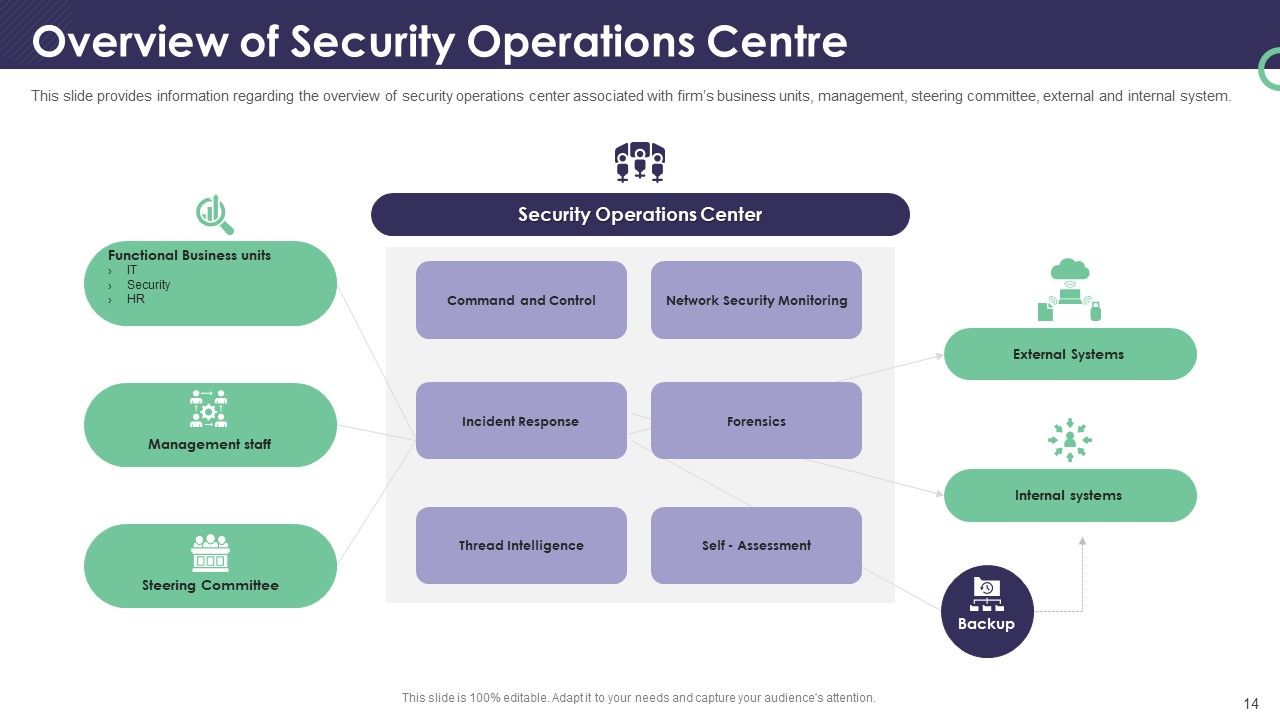
Slide 14: This slide provides an overview of the security operations center associated with the firm’s business units, management, steering committee, external and internal system.
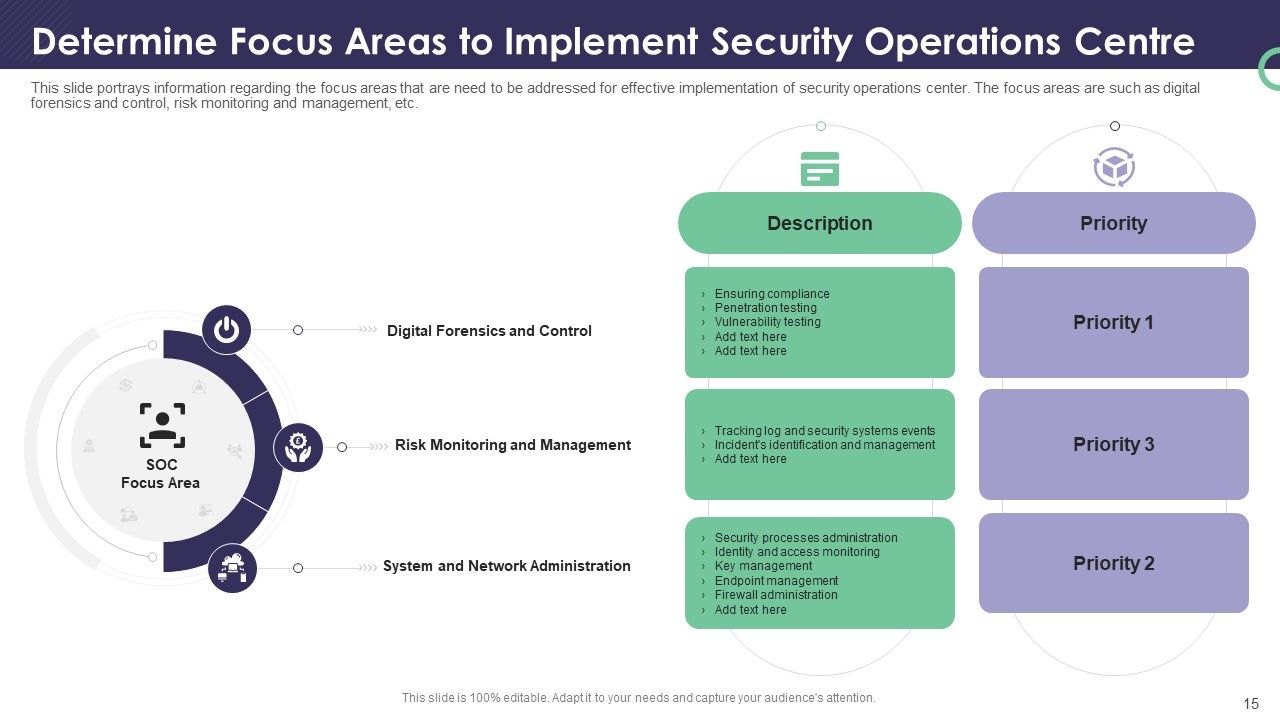
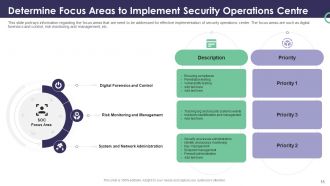
Slide 15: This slide portrays information regarding the focus areas that are needed to be addressed for effective implementation of the security operations center. The focus areas include digital forensics and control, risk monitoring and management, etc.
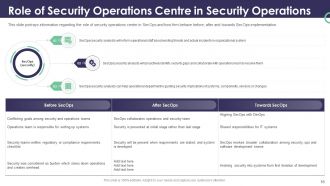
Slide 16: This slide portrays information regarding the role of the security operations center in SecOps and how firms behave before, after, and towards SecOps implementation.
Slide 17: This slide provides information regarding the development of the facility as a security operations center, which is built so that security staff will monitor enterprise systems, protect them against security breaches, and consistently identify and mitigate security risks.
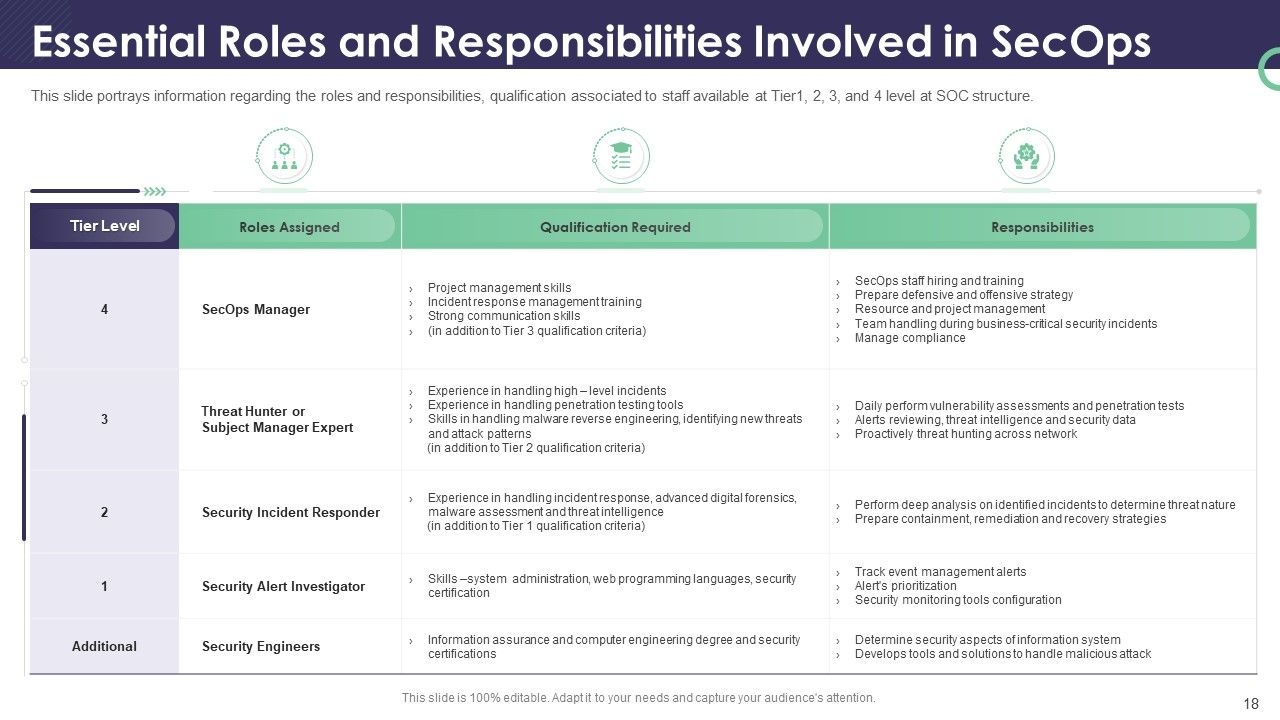
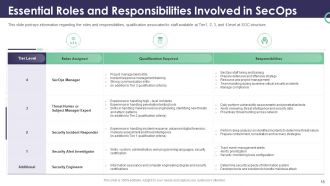
Slide 18: This slide portrays the roles and responsibilities, and qualifications associated with staff available at Tier 1, 2, 3, and 4 levels at SOC structure.
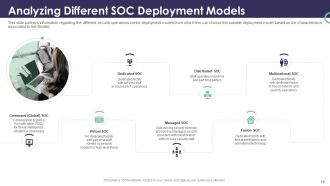
Slide 19: This slide portrays information regarding the different security operations center deployment models from which firms can choose the suitable deployment model based on the characteristics associated with the Models.
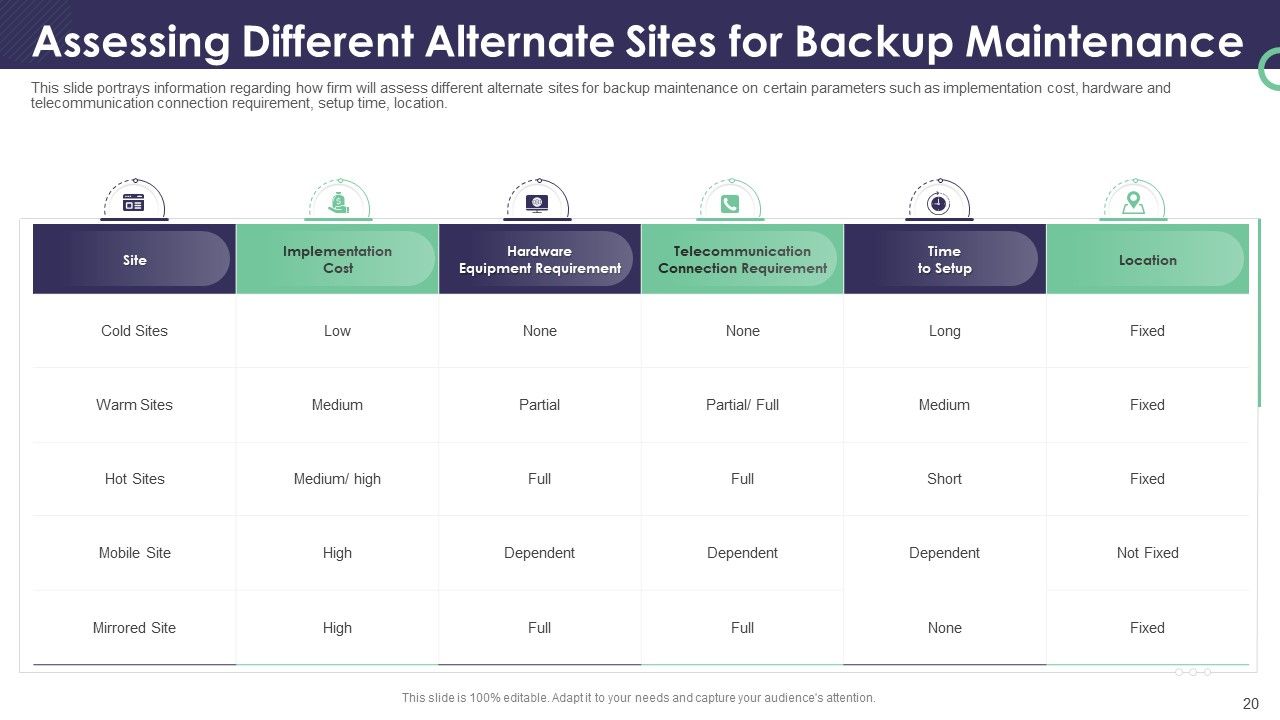
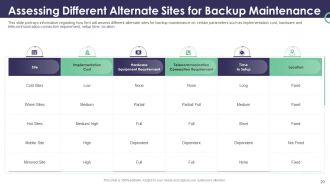
Slide 20: This slide portrays how a firm will assess alternate sites for backup maintenance on certain parameters such as implementation cost, hardware, and telecommunication connection requirement, setup time, and location.
Slide 21: This is a table of contents slide showing the Handling Insider Attack.
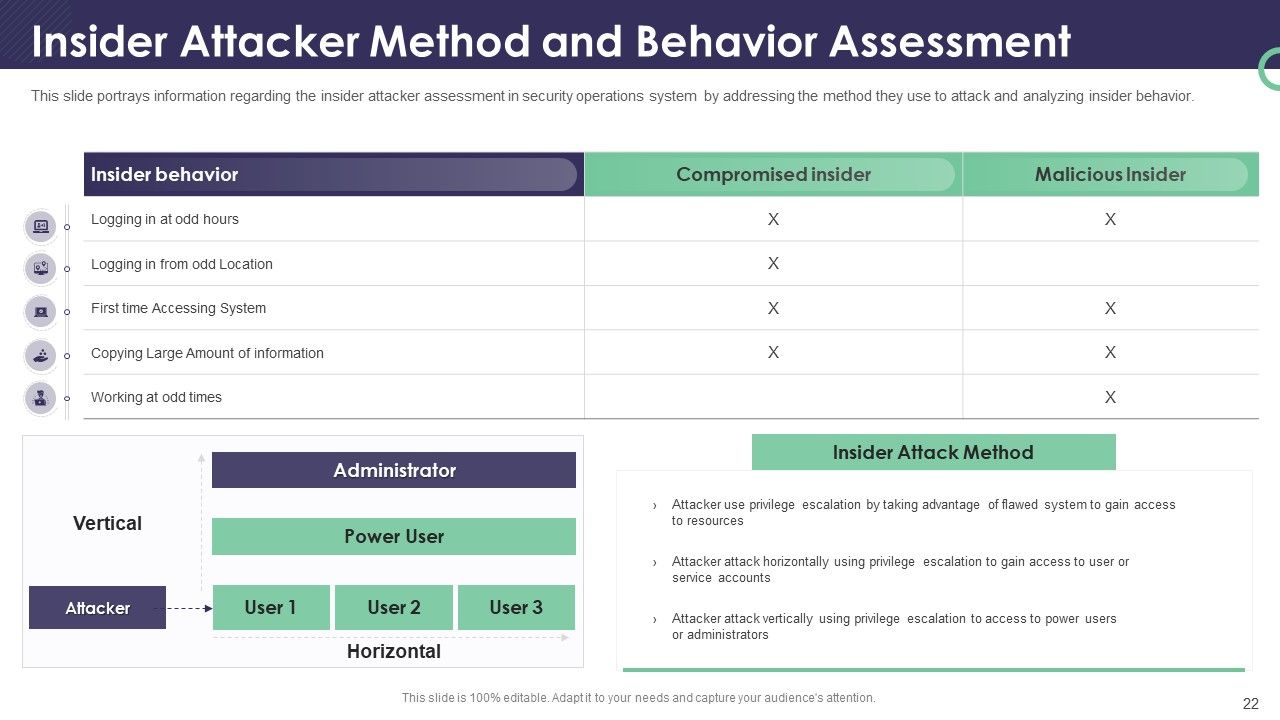
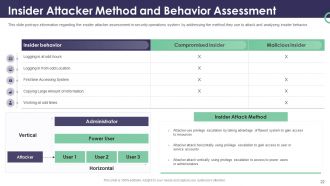
Slide 22: This slide portrays information regarding the insider attacker assessment in security operations systems by addressing the method they use to attack and analyze insider behavior.
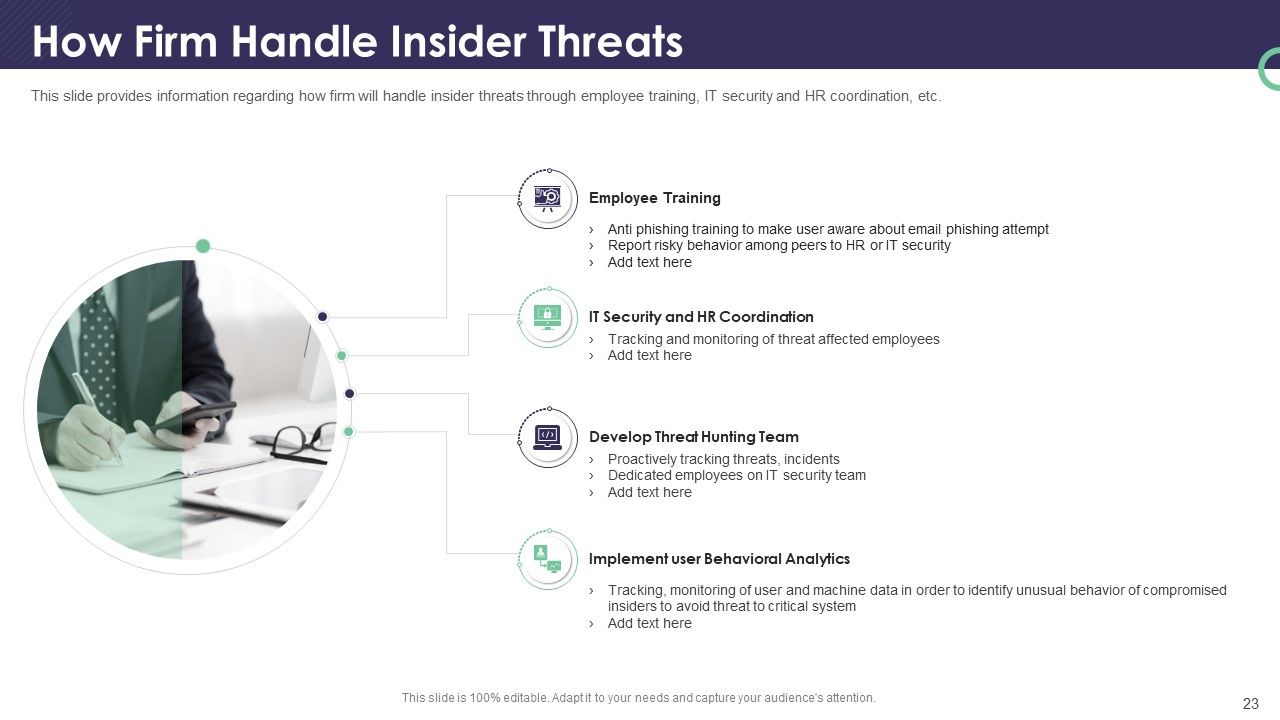
Slide 23: This slide provides information on how the firm will handle insider threats through employee training, IT security, HR coordination, etc.
Slide 24: This is a table of contents slide showing the Incident Management.
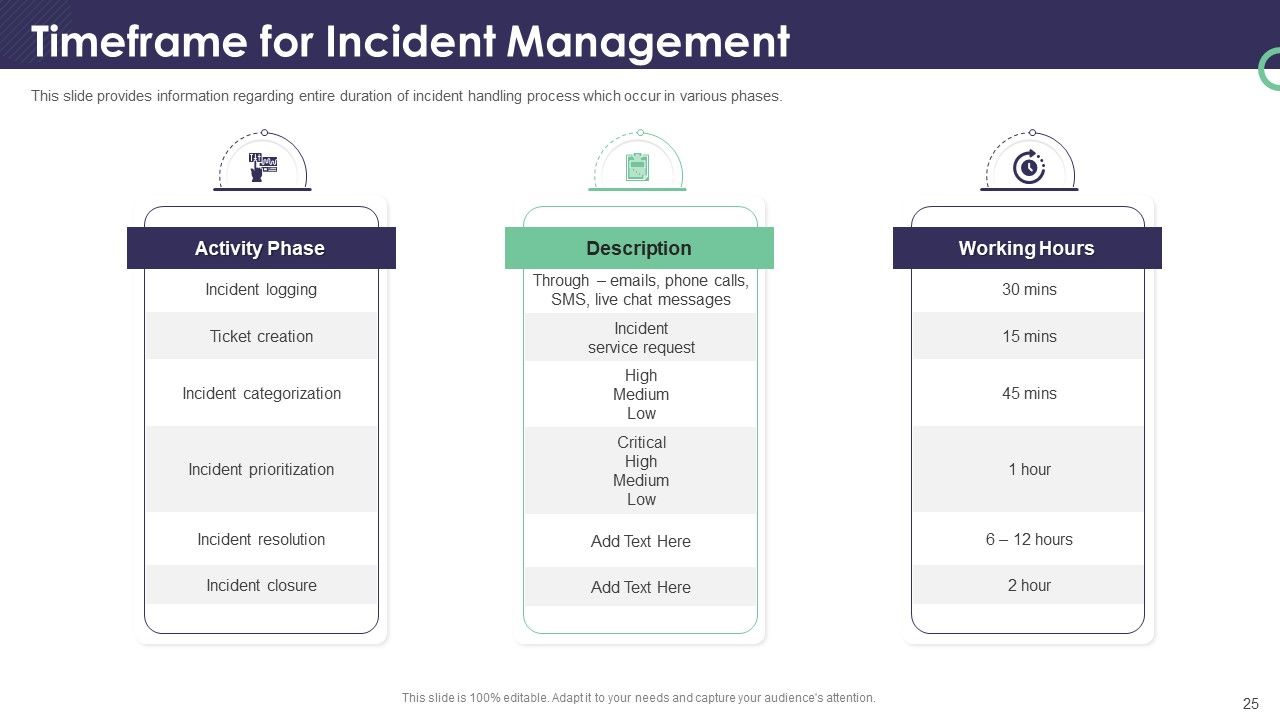
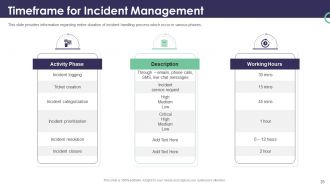
Slide 25: This slide provides information regarding the entire duration of the incident handling process, which occurs in various phases.
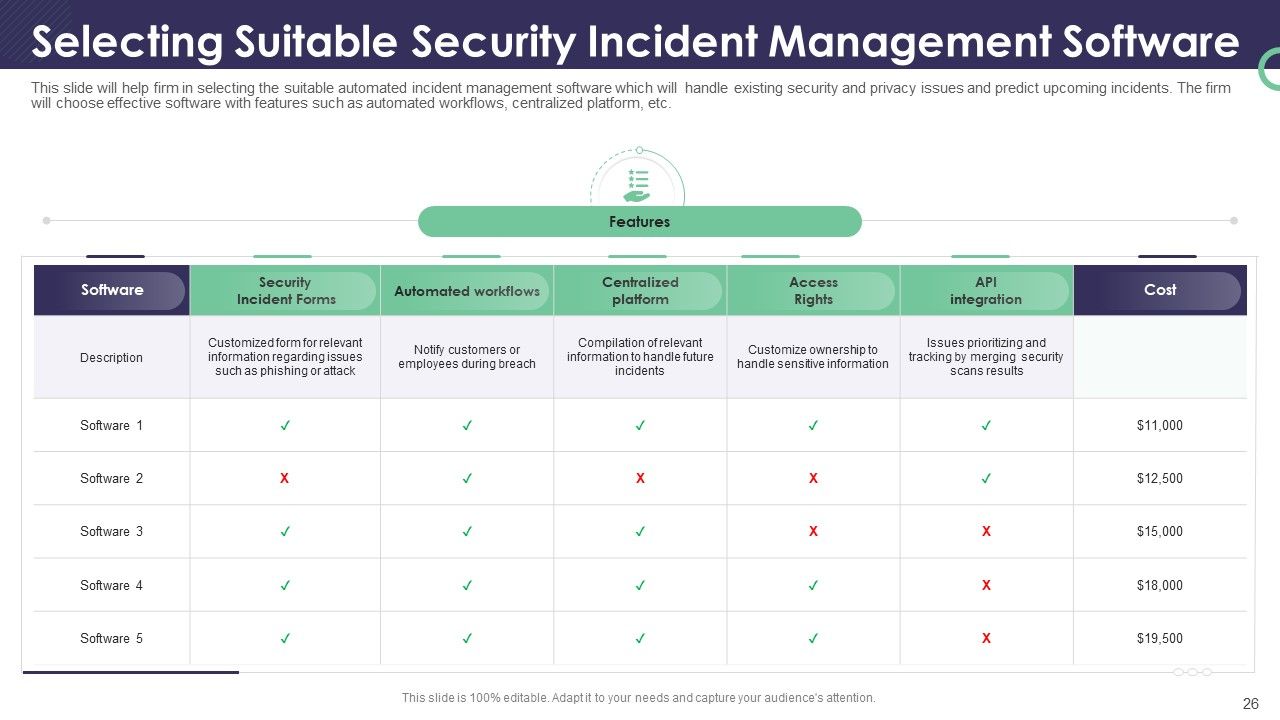
Slide 26: This slide will help the firm select the suitable automated incident management software that will handle existing security and privacy issues and predict upcoming incidents. The firm will choose effective software with features such as automated workflows, centralized platforms, etc.
Slide 27: This is a table of contents slide showing the Contingency Plan for Threat Handling in SecOps.
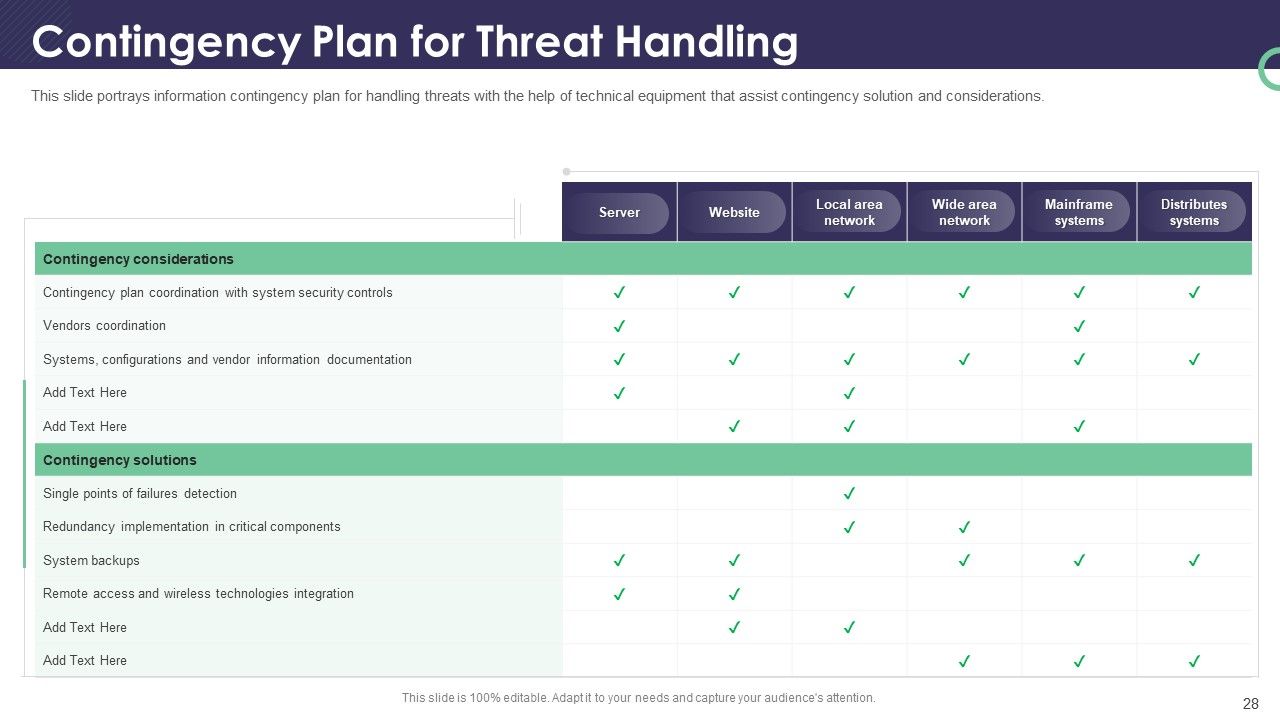
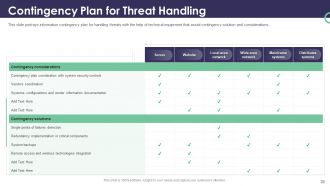
Slide 28: This slide portrays an information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations.
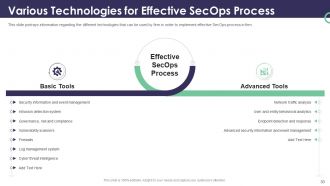
Slide 29: This is a table of contents slide showing the Various Technologies for Effective SecOps Processes.
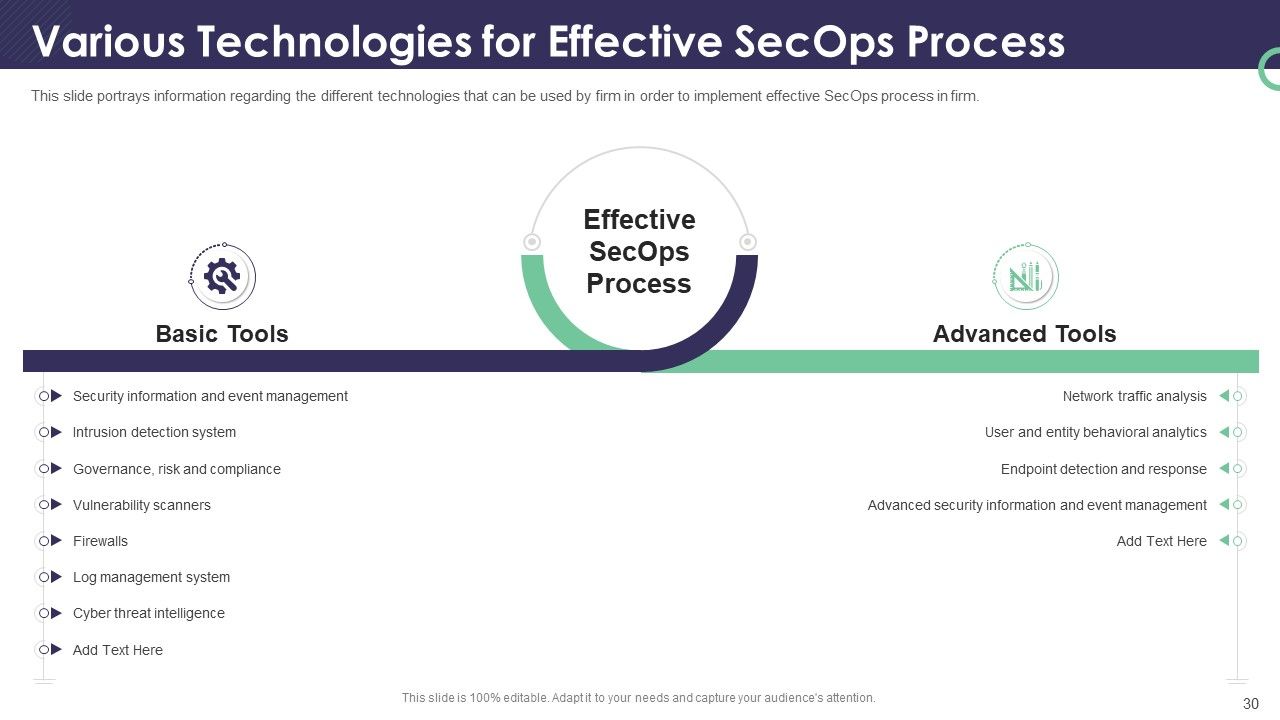
Slide 30: This slide portrays information regarding the different technologies that firms can use to implement effective SecOps processes in a firm.
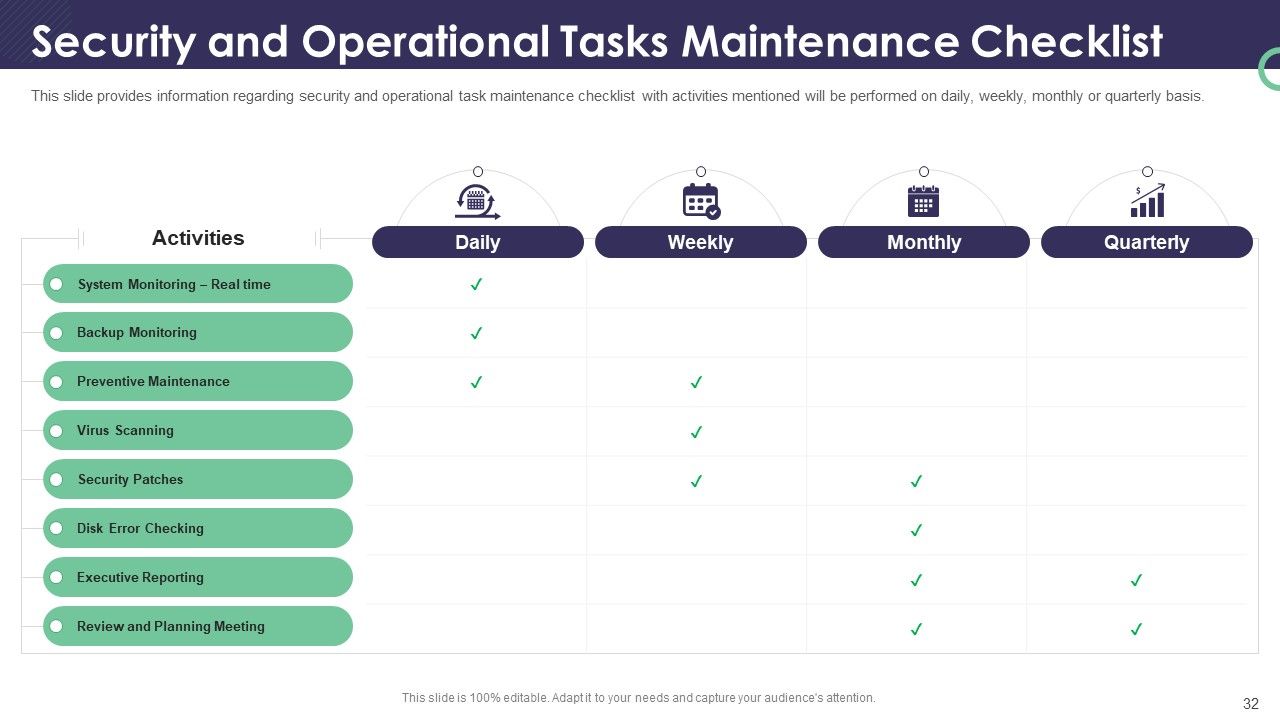
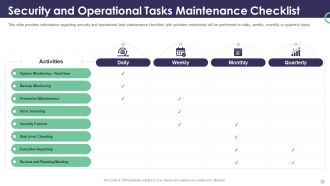
Slide 31: This is a table of contents slide showing the Security and Operational Tasks Maintenance Checklist.
Slide 32: This slide provides information regarding the security and operational task maintenance checklist with activities mentioned that will be performed on a daily, weekly, monthly, or quarterly basis.
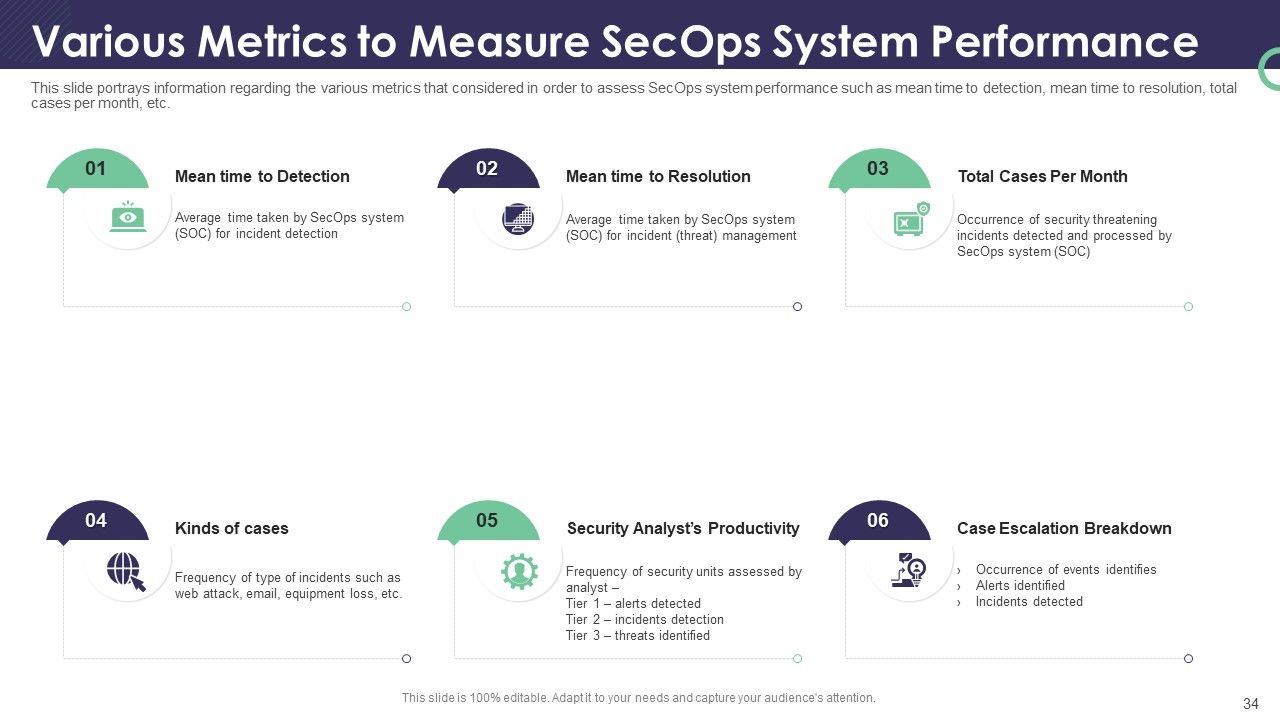
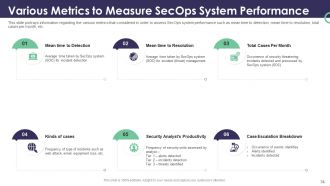
Slide 33: This is a table of contents slide showing the Various Metrics to Measure SecOps System Performance.
Slide 34: This slide portrays information regarding the various metrics that are considered in order to assess SecOps system performance, such as mean time to detection, mean time to resolution, total cases per month, etc.
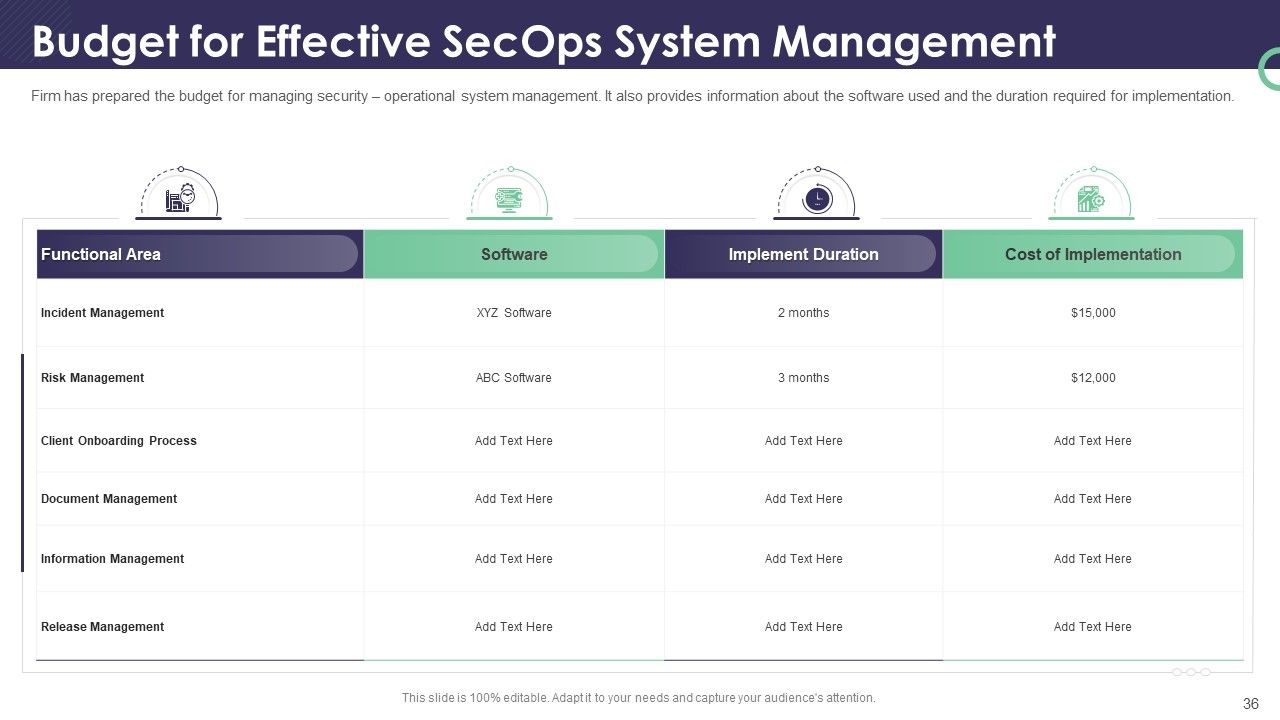
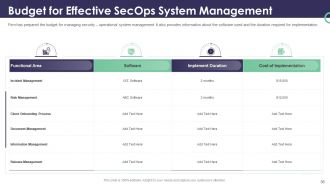
Slide 35: This is a table of contents slides showing the Cost Associated to SecOps Implementation.
Slide 36: This slide represents how the Firm has prepared the budget for managing security – operational system management. It also provides information about the software used and the duration required for implementation.
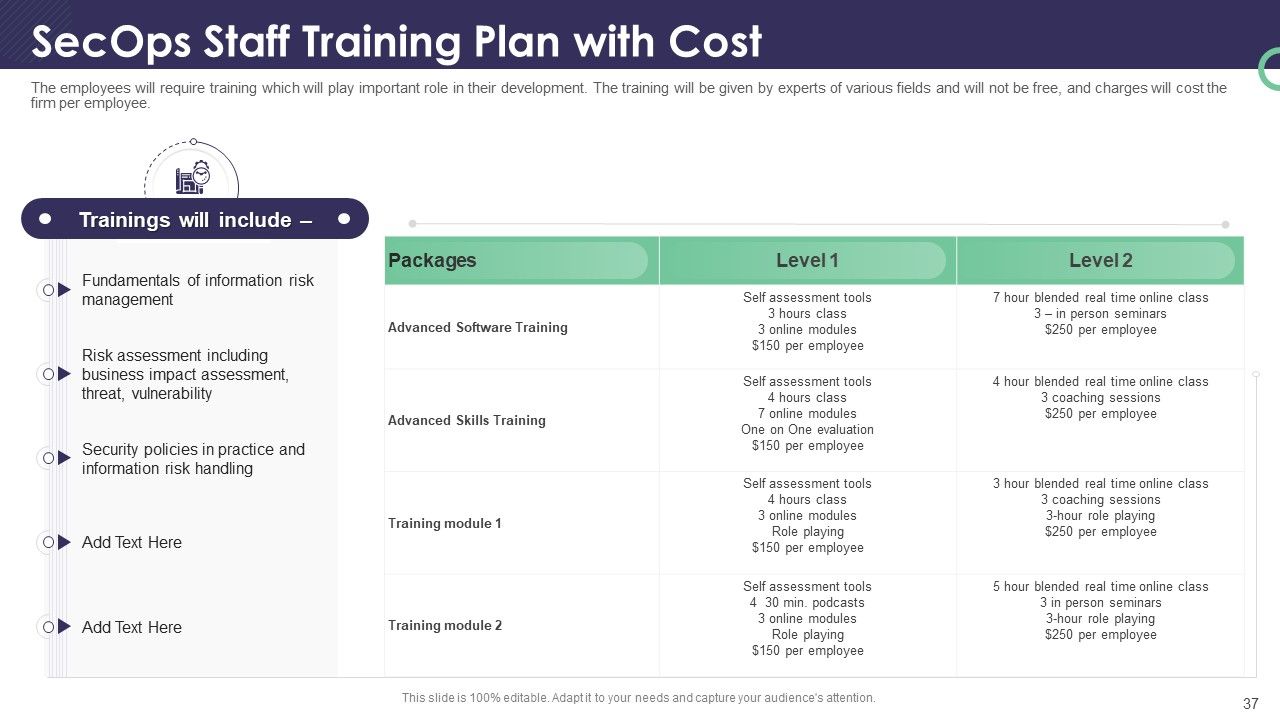
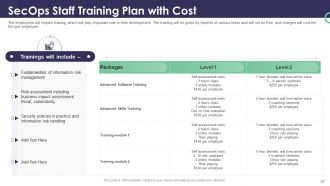
Slide 37: This slide depicts the employees will require training which will play an important role in their development. The training will be given by experts in various fields and will not be free, and charges will cost the firm per employee.
Slide 38: This is a table of contents slide showing the Impact Analysis.
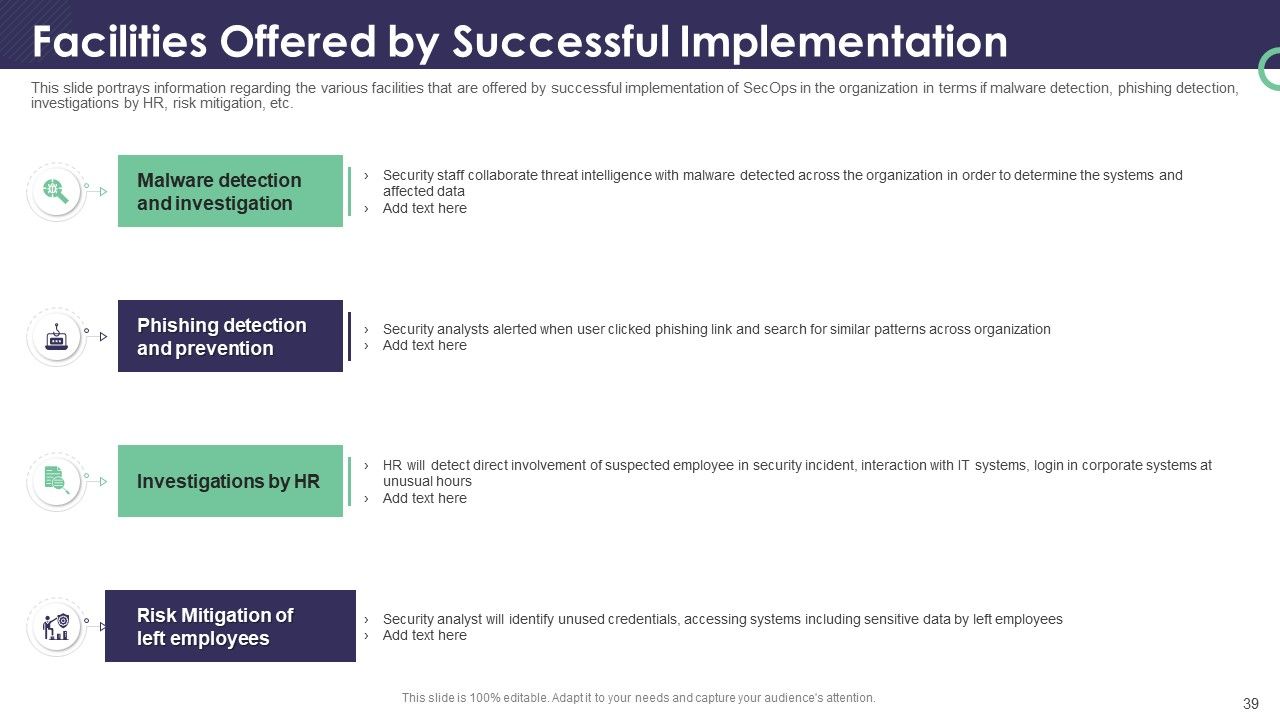
Slide 39: This slide portrays information regarding the various facilities offered by the successful implementation of SecOps in the organization in terms of malware detection, phishing detection, investigations by HR, risk mitigation, etc.
Slide 40: This slide portrays information regarding how the firm successfully handles security issues/events and can reduce the occurrence of events.
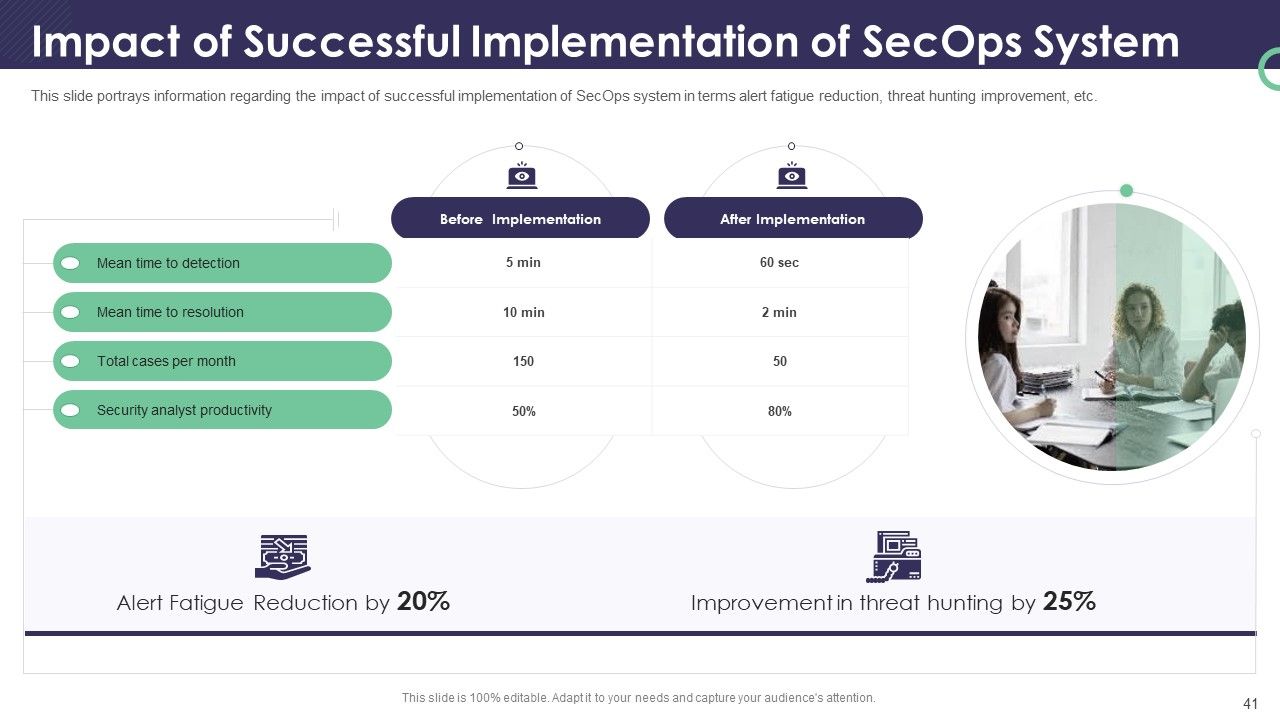
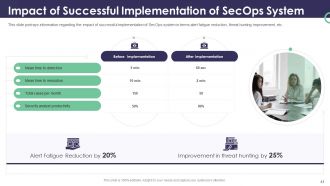
Slide 41: This slide portrays information regarding the impact of successful implementation of the SecOps system in terms of alert fatigue reduction, threat hunting improvement, etc.
Slide 42: This is a table of contents slide showing the Dashboard.
Slide 43: This slide provides information regarding the dashboard, which is used to track and monitor various security risks and threats identified.
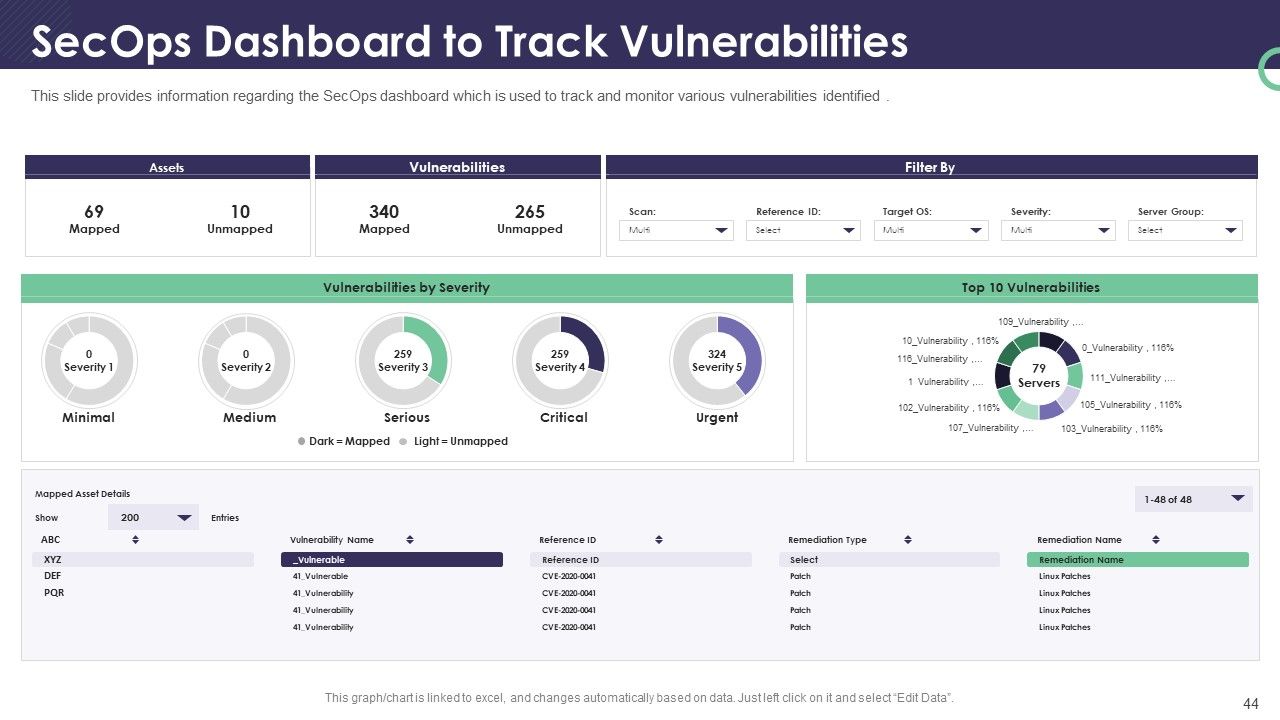
Slide 44: This slide provides information regarding the SecOps dashboard, which is used to track and monitor various vulnerabilities identified.
Slide 45: This is the Icons Slide for Enterprise Security Operations.
Slide 46: This slide presents the Additional Slides.
Slide 47: This slide provides the Mission for the entire company. This includes the vision, the mission, and the goal.
Slide 48: This slide shows the members of the company team with their name, designation, and photo.
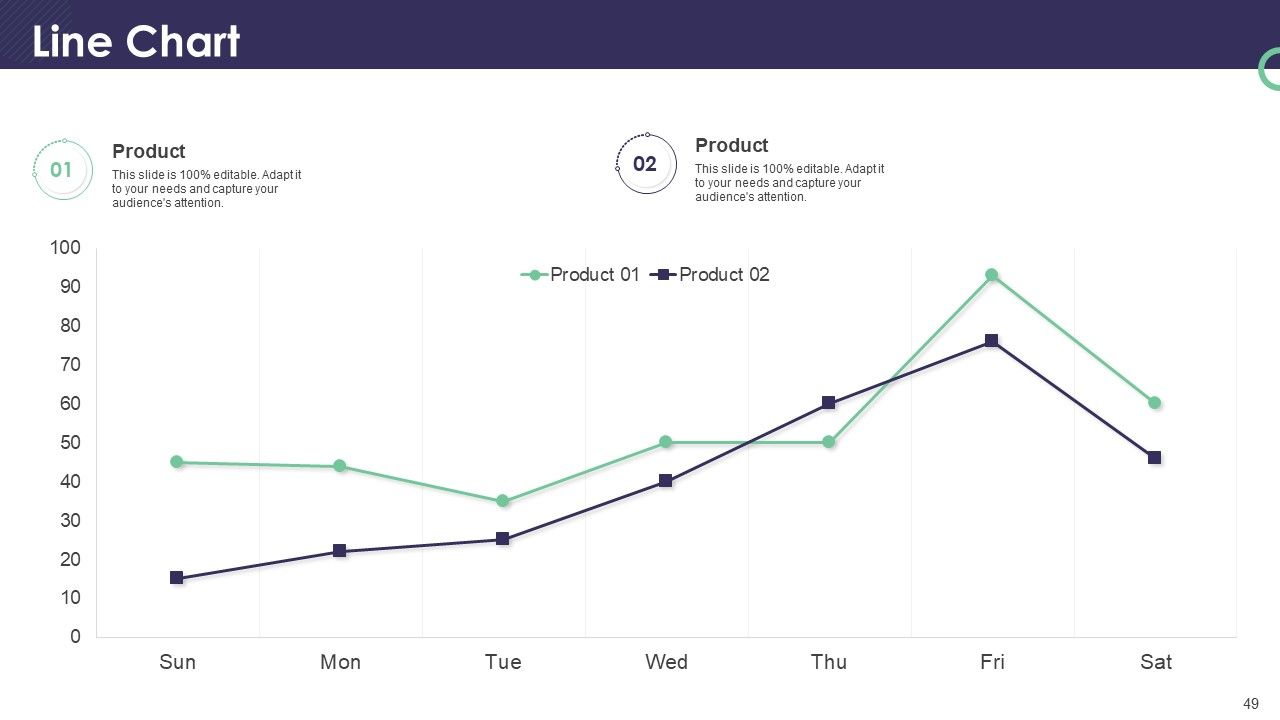
Slide 49: This slide presents the Line Chart. It compares the data and shows trends over time.
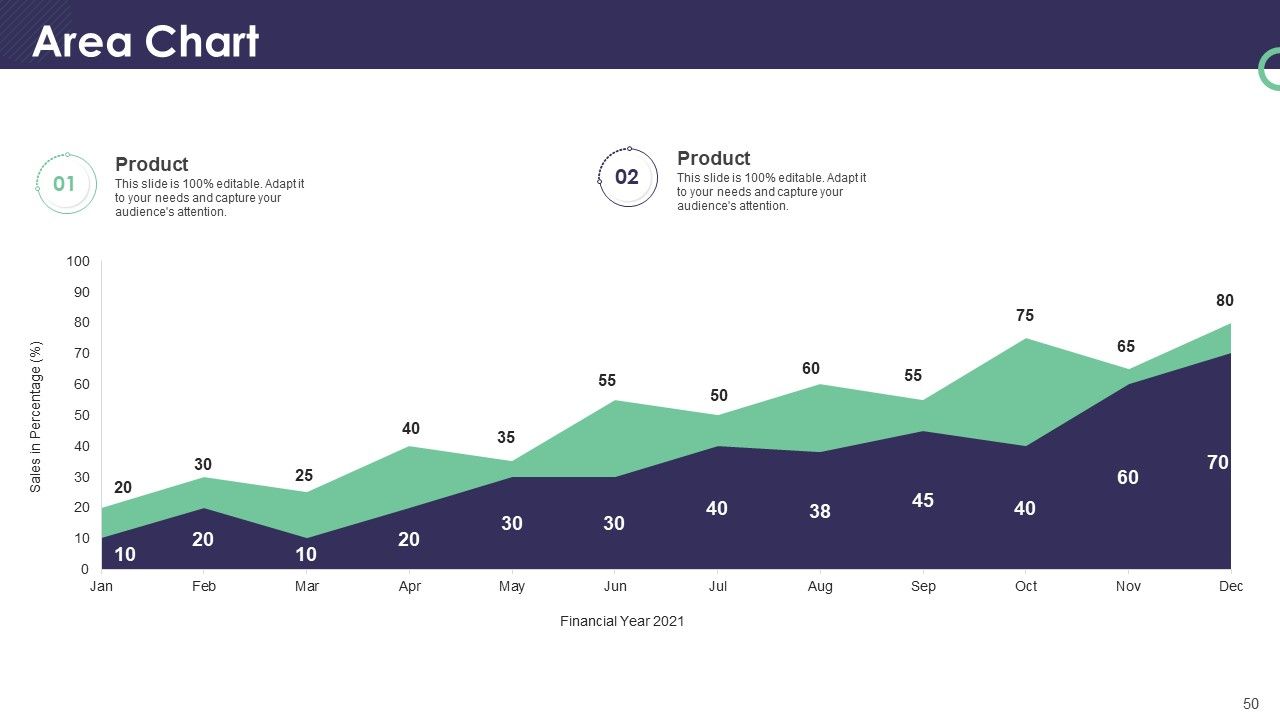
Slide 50: This slide presents the Area Chart. It emphasizes the magnitude of change over time.
Slide 51: This slide presents a quote.
Slide 52: This slide presents the overall Target of the company and smaller targets within that primary Target.
Slide 53: This slide presents the Financial data with the data’s numbers at minimum, medium, and maximum percentage.
Slide 54: This slide contains Post-It Notes that can express any brief thoughts or ideas.
Slide 55: This is a Thank You slide where details such as the address, contact number, and email address are added.
Enterprise security operations powerpoint presentation slides with all 55 slides:
Use our Enterprise Security Operations Powerpoint Presentation Slides to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
Really like the color and design of the presentation.
-
Informative design.
-
Great designs, really helpful.
-
Colors used are bright and distinctive.