Cybersecurity powerpoint presentation slides
Let your team understand the importance of Computer security with the assistance of our Cyber Security PowerPoint Presentation Deck. In today’s time, it is quite essential to pay attention towards the protection of computer systems from theft or damage as there is a every chance of your data being accessed by someone else. Our creative designing team has crafted this PPT Deck with 17 slides for you to share the information related to IT security. Although there are cyber security standards available but still there are people in the market who try to capture your data to either use it for their own purpose or sell it to some other organization. This presentation deck enables you to highlight the information related to cyber attacks that can create concerns such as backdoor, direct-access attacks, eavesdropping, phishing, spoofing, tampering etc. By taking certain security measures you can protect your data. Cyber Security standards attempt to protect the cyber environment of a user or an organization. The PowerPoint deck contains some slides which include information related to tips, initiatives, step to ensure that your data is protected at every step. So, download it and take precautionary steps to secure your IT system. Cater for crazy cravings with our Cyber Security Powerpoint Presentation Slides. Find a harmless way to fulfill deep desires.
Let your team understand the importance of Computer security with the assistance of our Cyber Security PowerPoint Presentat..
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Ready to use PowerPoint sample assist you in saving both your time and effort. Luxury to add or remove content in the design. Transmute the PPT layout with industry information i.e. banner and icon. Flexible as can be adapted in JPEG or PDF documents. Text and font can be easily reformed as the presentation need. Presentation template design shown in both standard and widescreen slide
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
With cybersecurity becoming such an important part of our personal and professional lives today, it is imperative that the world accords it the importance it deserves.
It needs to be paid for by each of us, along with other utilities like water, power, and roads.
This milestone, however, is a fair time away, with businesses and consumers both caught in two minds about whether something that is not seen is actually worth this much money and resources.
For cybersecurity key performance indicators, we have special-purpose slides. Click here.
Until people in the industry resolve this pain point of what it costs to ensure cybersecurity on a daily basis, we will continue to have organizations lose data and put the financial security of millions of users in peril, as happened in the 2017 ransomware attack, which affected 150 counties and 200,000 computers.
To battle this inertia in cybersecurity, tips, tricks, and policy initiatives are needed. Awareness plus action that moves things forward is also needed, and SlideTeam is the best option for this. We curate templates on cybersecurity that have expert backing, world-class aesthetics, and actionable pointers to ensure users can act on the information.
These slides are provided based on your business goals, from tactical tips to a strategy that must guide your cybersecurity effort.
Each slide is 100% editable and customizable. You get structure, a starting point, and the capability to tailor each presentation to the audience’s profile.
Let’s explore these templates now!
Template 1 Cybersecurity Seven-Step Template
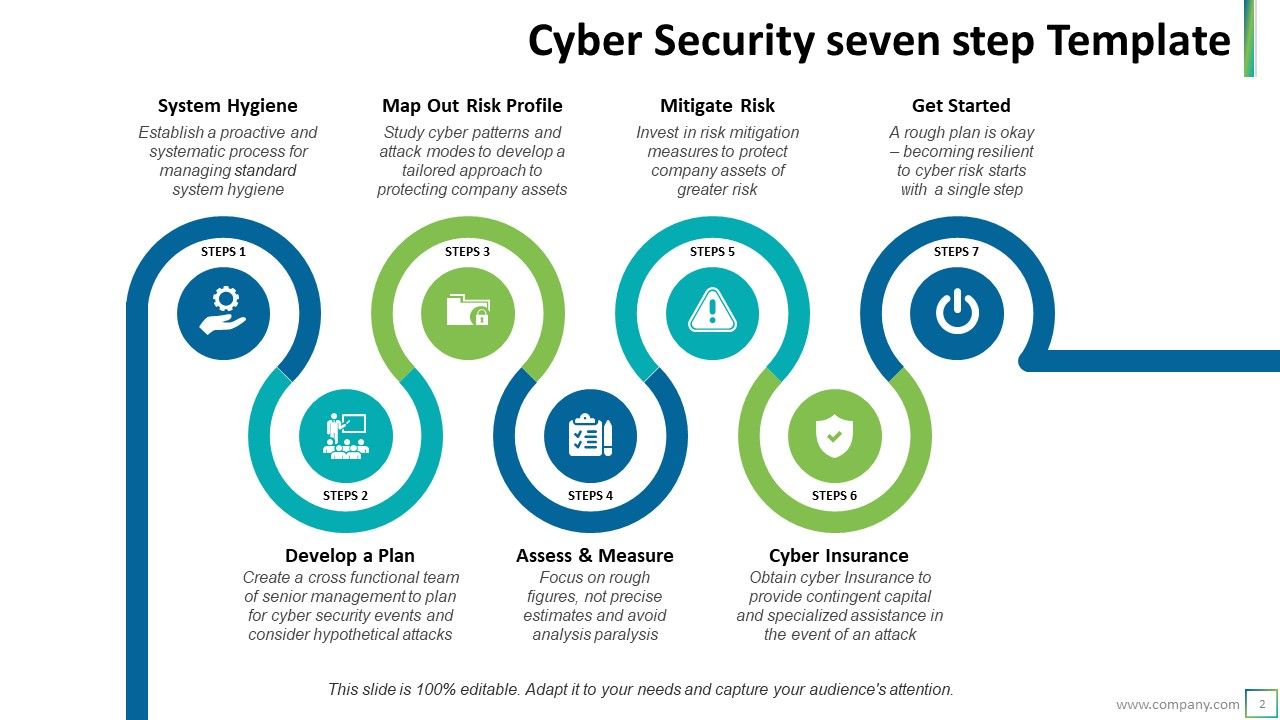
Getting started can be tricky in something that appears as scary and as complicated as ensuring cybersecurity. Use this PPT Template as the base on which to build your base to be safe against cybercrime in seven steps. The seven steps in cybersecurity that the slide puts forward are creating system hygiene and developing a plan where senior management is active. With these steps, you can map out what your company is most at risk from, with the management able to assess and measure risks, threats, and possible courses of action. Cyber insurance has to be taken, and voila, you are ready to invest in cybersecurity as a fundamental business practice.
Template 2 Cybersecurity Prevention Setting Policy
This is the point from where you can start your action plan. With this PPT Slide, signal that you mean business and list the three central planks of your fight against cybersecurity listed on it. The text can be all yours to ensure your reality is reflected through the slide. In the first step, you research and dig deep into what you can do. In step 2, there is more action as the rubber of your action plans hits the rounds. Finally, in the last step, you analyze the impact of your work.
Template 3 Cybersecurity Prevention Understanding The Requirements
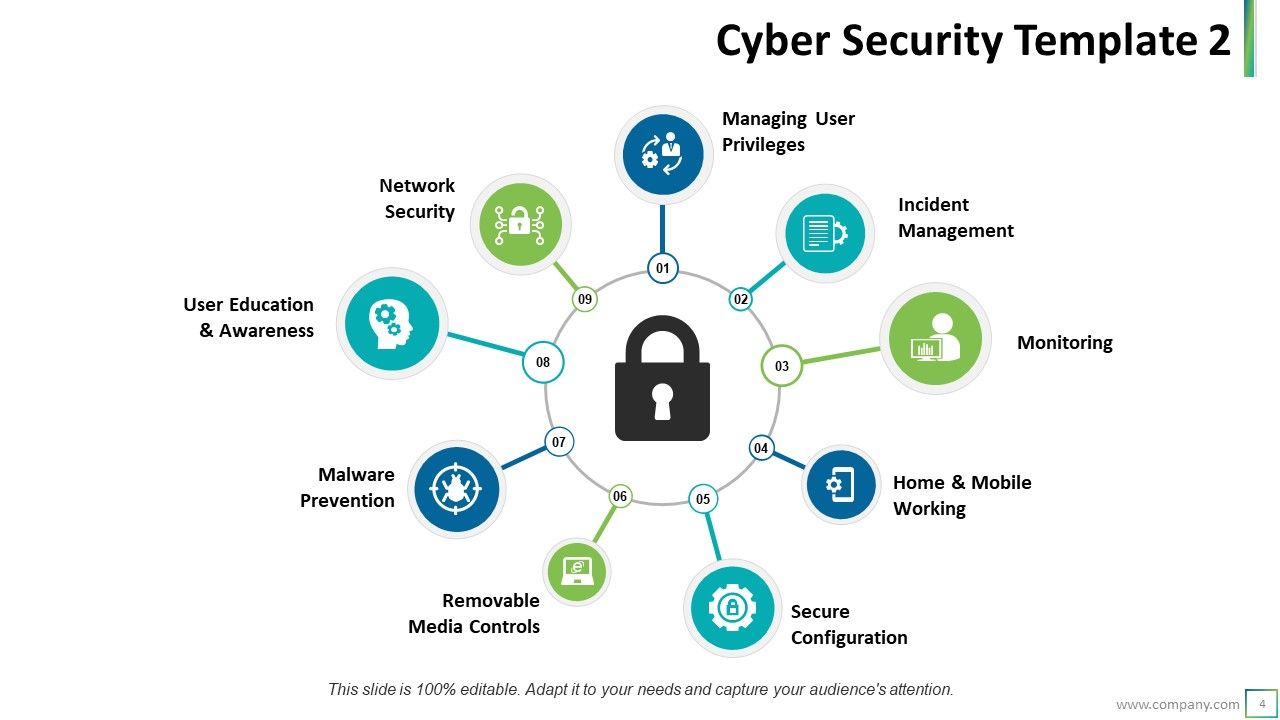
Do you want to know what are the crucial keys that feed into a robust lock on your vital installations and systems for cybersecurity? Nearly a dozen inputs are needed to ensure your cybersystems become safe. This PPT Template lists some of these as user education and awareness, home and work networking, monitoring, network security, removable media controls, and secure configuration. Understand the mechanics of a robust system of cybersecurity culture with a download of this template.
Template 4 Cybersecurity Prevention: Numbers that Reflect Need
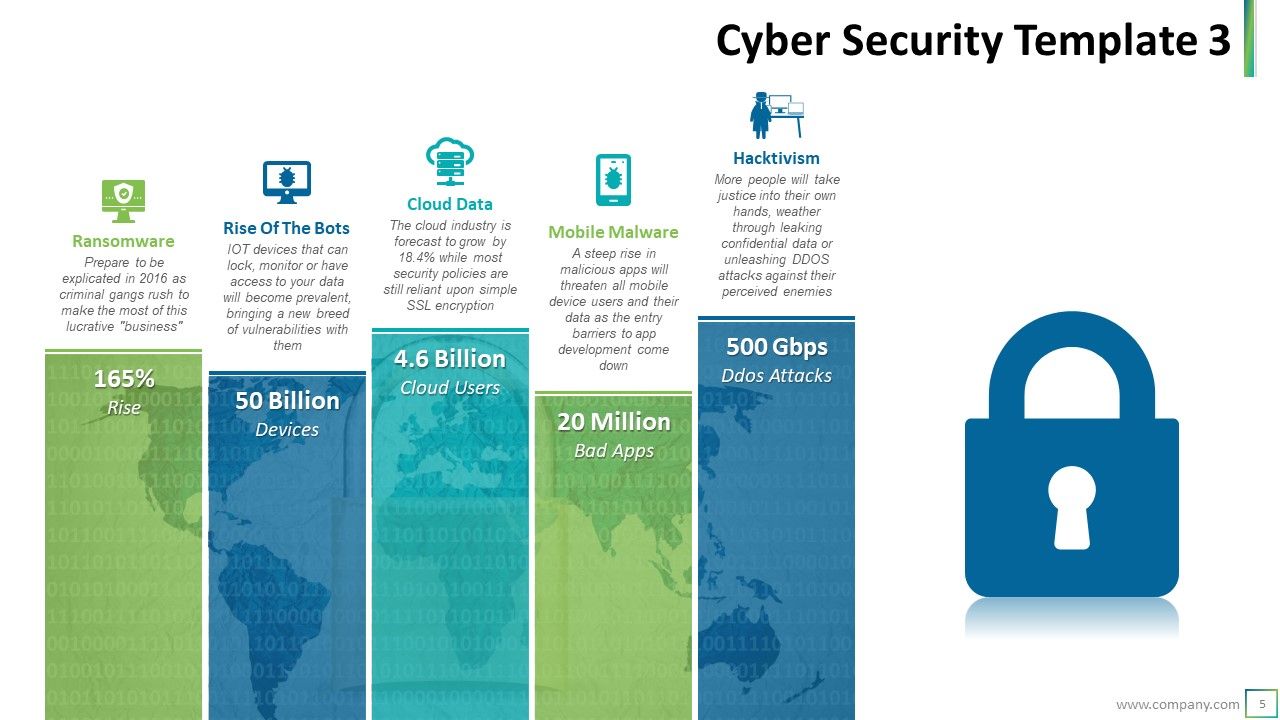
Users will find this template helpful in understanding the threat that ignoring cybersecurity poses in terms of statistics. For instance, cases of ransomware tend to double every year; mobile malware will see a steep rise, with apps specifically targeting people based on profiles as the cost of developing the app comes down. Cloud-based data will need more protection, as the slide shows. The template also depicts how hacktivism will also see a rise. Get this PPT Template now to understand how big a threat cybersecurity is.
Template 5 Cybersecurity Framework Covering all Bases PPT Template
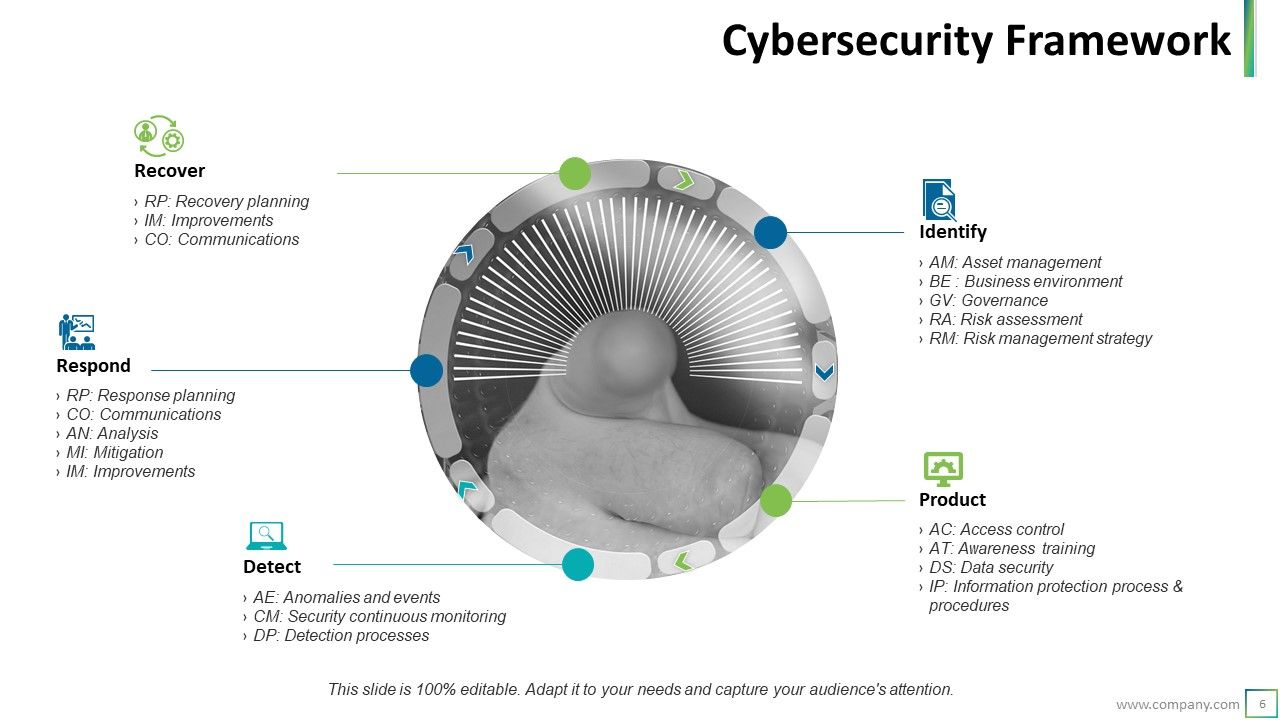
This PPT Template gives users a cybersecurity framework that starts with stage 1 of DETECT. Any framework must be adept at continuously monitoring security and excellent at detecting processes and red-flag anomalies and events. After detection, the following four stages are responding, recovering, identifying, and focusing on the product. The slide’s actionable points are abbreviated to ensure the business finds it easy to work on aspects of the cybersecurity framework.
Template 6 Cybersecurity Initiatives in Detail Outline for Complete Prevention

In this PPT Template, you will find the entire list of cybersecurity initiatives you can take to ensure better security at lower costs for longer. The best step in the positive direction of strengthening cybersecurity has to be to ensure training and awareness. Then, businesses must invest in risk assessments and metrics to measure and report effectiveness and operationalizing cyber security. Identity and access management and governance (roles, reporting structure & directors) become essential. Strategy and security operating centers are critical infrastructures that must be set up for a robust experience. Get this template now!
Template 7 Cybersecurity tips and tricks for daily implementation and action
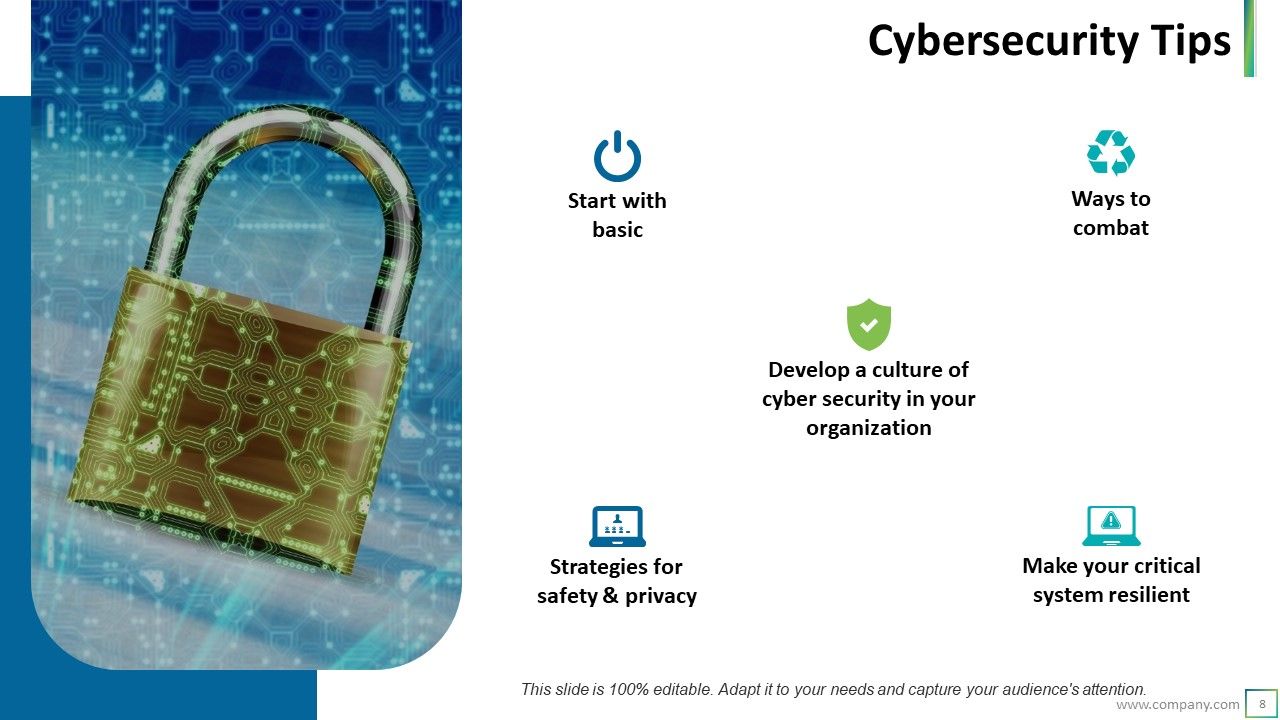
This blog lists the five significant tips needed to ensure that cybersecurity becomes a way of life at your organization. You need to start with the basics and ensure each individual knows the strategies for maintaining safety and privacy. In addition, you must make your critical system resilient, understand ways to combat threats when they arise, and develop a culture of cybersecurity in your organization.
PS For comprehensive training plans on cybersecurity awareness, please click here.
Cybersecurity powerpoint presentation slides with all 17 slides:
Clearly explain each important component with our Cybersecurity Powerpoint Presentation Slides. It helps break down the formula.
-
Best ppt
-
Great product with highly impressive and engaging designs.
-
The Designed Graphic are very professional and classic.
-
good
-
its very good