Enterprise Cyber Safety And Security Proposal Powerpoint Presentation Slides
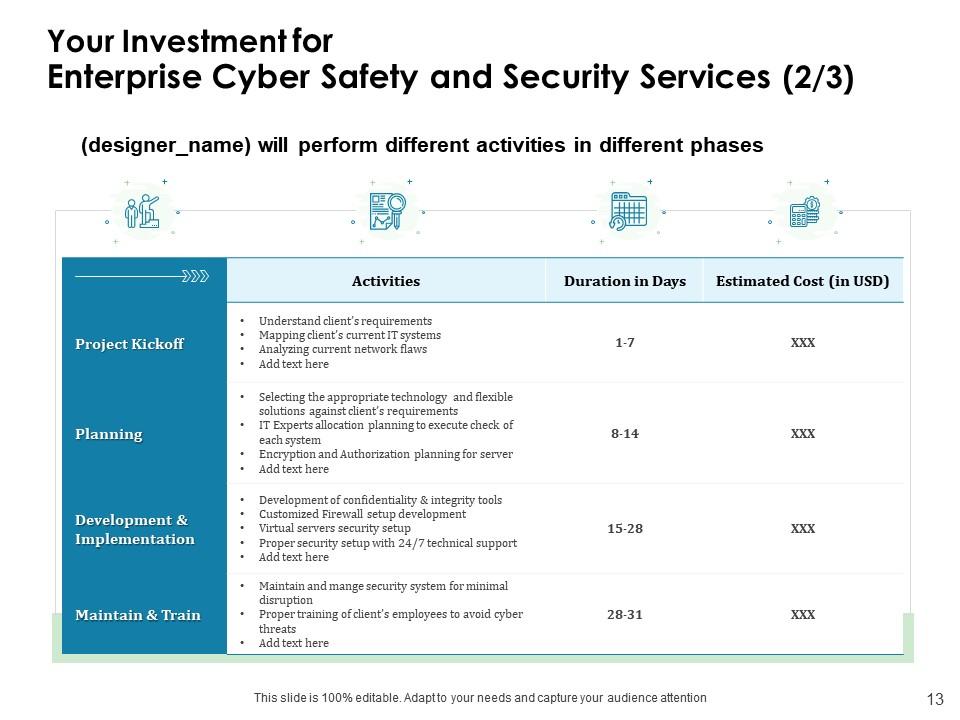
The increase in the number of cyberattacks on systems has called for cybersecurity methods. Cybersecurity refers to the practice of securing company information or data from being exposed. With rising cyberattacks, no company wants to take the risk ever, and due to this reason, corporations have started collaborating with cybersecurity service providers to keep their systems secure and safe. Therefore, incorporate our expertly-designed Enterprise Cyber Safety And Security Proposal PowerPoint Presentation Slides and propose your services confidently in front of your clients. Guarantee uninterrupted protection to all programs, best defense system to secure information, and network security monitoring through our professionally-designed internet protection PowerPoint template. The overall presentation is appealing enough to increase audience engagement. Explain your motive in the well-composed cover letter of this PPT layout. List the various components of your presentation in the table of contents slide. Identify the issues in securing the IT system and devise solutions to overcome the same. With our computer protection PowerPoint slideshow, explain project context and objectives thoroughly. Explain the importance of installing software in today’s times and ensure them to provide quality service by employing our network protection PowerPoint slideshow. Illustrate the process you follow while installing the software, such as project kickoff, planning, development, implementation, maintenance, and training. Take the assistance of the time frame layout to assign the timeline to each activity. Inform the mode of communication to your customers like weekly calls, monthly catch up, and review sessions with our expertly-created information protection PowerPoint graphic. Present the additional services of your company that include, software development, security, networking, and cloud services separately. Depict the budget plan and mention the cost involved in each activity, so clients know the total amount to arrange. Establish credibility by including testimonials and accomplishments of the past. Therefore, download our firewall PowerPoint design and amaze your audience with your proposal.
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Presenting our Enterprise Cyber Safety And Security Proposal PowerPoint Presentation Slides. You can easily make the changes within this presentation as it can be easily edited. Also, access the presentation in PDF, JPG, and PNG format. Besides this, you can display the presentation theme in widescreen and standard screen format. The theme can be accessed on all applications including Google slides and Microsoft PowerPoint. Grab it right away!
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
Slide 1: This slide introduces Enterprise Cyber Safety and Security Proposal. State Proposal name, Submission date, User assigned and begin.
Slide 2: This slide displays Cover Letter for Cyber Security Services.
Slide 3: This slide showcases Table of Contents.
Slide 4: This slide depicts Table of Contents with- Project Context & Objectives.
Slide 5: This slide describes Project Context and Objectives for Cyber Security Services.
Slide 6: This slide shows Table of Contents.
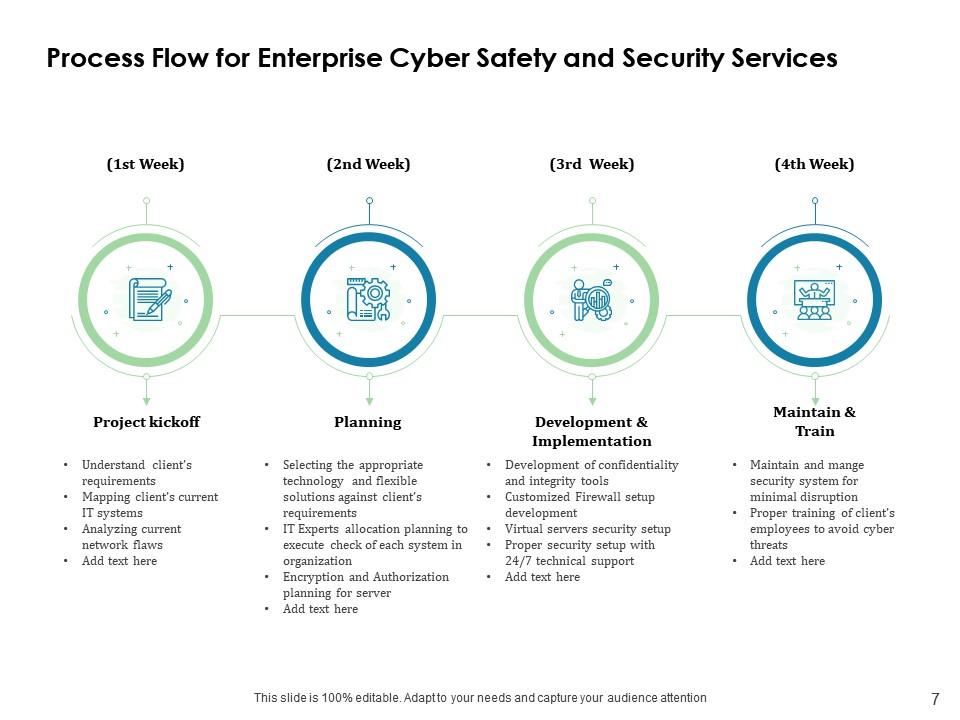
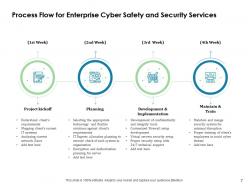
Slide 7: This slide depicts Process Flow for Cyber Security Service.
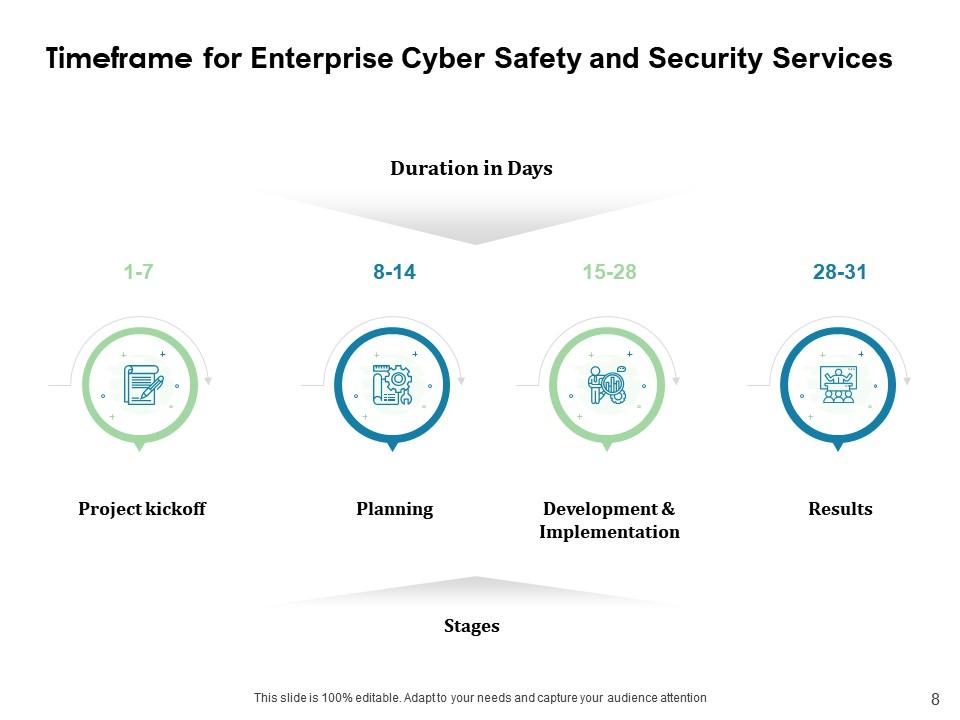
Slide 8: This slide showcases Timeframe for Cyber Security Services.
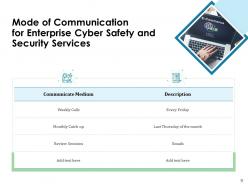
Slide 9: This slide displays Mode of Communication for Cyber Security Services.
Slide 10: This slide showcases Additional Service Offerings for Cyber Security Services such as- Security & Networking, Cyber attacks protection, Strategic recommendation for site, Comprehensive visibility into Network traffic, etc.
Slide 11: This slide displays Table of Contents with- Your Investment.
Slide 12: This slide represents Investment details for Cyber Security Services.
Slide 13: This slide shows Investment details for Cyber Security Services.
Slide 14: This slide presents Additional Services for Cyber Security.
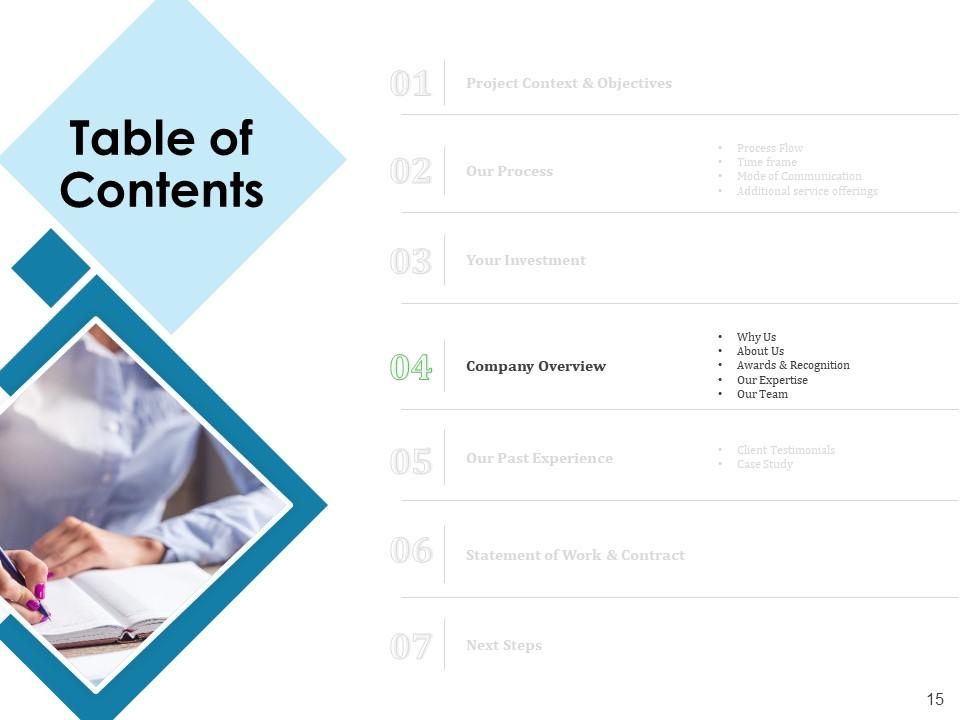
Slide 15: This slide depicts Table of Contents with- Company Overview, Why Us, About Us, Awards & Recognition, Our Expertise, Our Team.
Slide 16: This slide describes Why Us for Cyber Security Services.
Slide 17: This is About Us slide to showcase Company Specifications.
Slide 18: This slide displays Awards & Recognition for Cyber Security Services
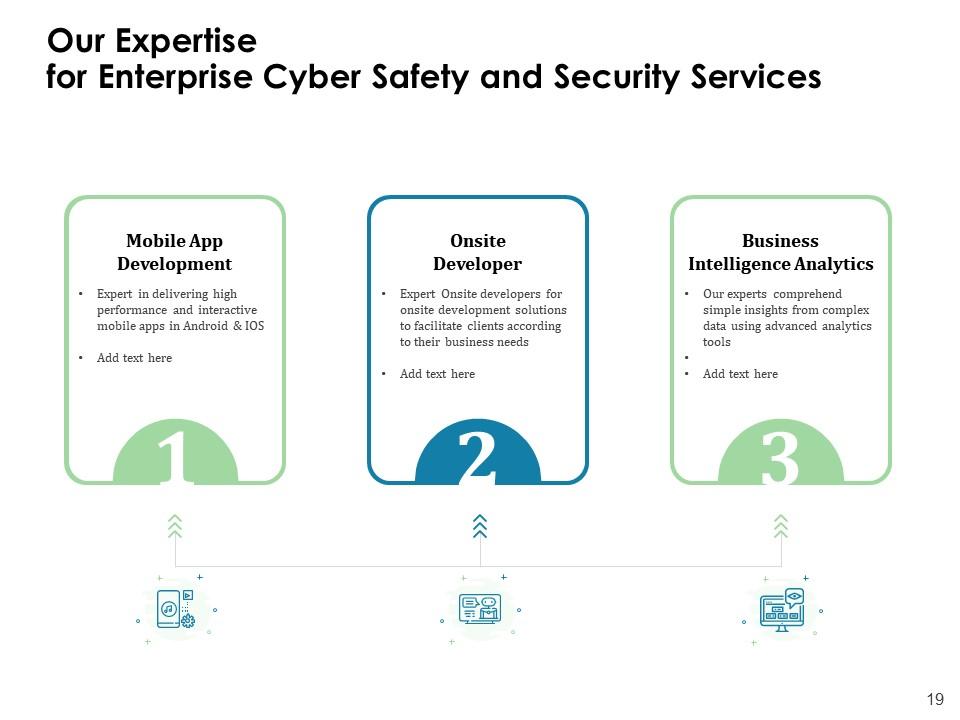
Slide 19: This slide shows Our Expertise contaning- Mobile App Development, Onsite Developer, Business Intelligence Analytics.
Slide 20: This is Our Team slide with Names and Designations.
Slide 21: This is Our Team for Cyber Security Organization.
Slide 22: This slide showcases Client Testimonials with Names and Designations.
Slide 23: This slide showcases Client Testimonials with Names and Designations.
Slide 24: This slide displays Client Testimonials for Enterprise Cyber Safety and Security Services.
Slide 25: This slide represents Case Study for Enterprise Cyber Safety and Security Services.
Slide 26: This slide depicts Table of Contents with project context and objectives.
Slide 27: This slide showcases Statement of Work & Contract.
Slide 28: This slide displays Table of Contents.
Slide 29: This slide showcases Next Steps for Enterprise Cyber Safety and Security Services.
Slide 30: This is Contact Us slide with Email address, Contact number and Address.
Slide 31: This is Icons Slide for Enterprise Cyber Safety and Security Proposal.
Slide 32: This slide is titled as Additional Slides for moving forward.
Slide 33: This slide displays Organization Mission and Vision Statement.
Slide 34: This is About Us slide to showcase Company specifications.
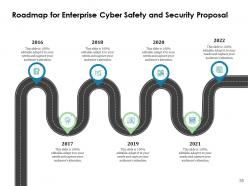
Slide 35: This slide displays Roadmap process.
Slide 36: This is 30 60 90 Days Plan slide.
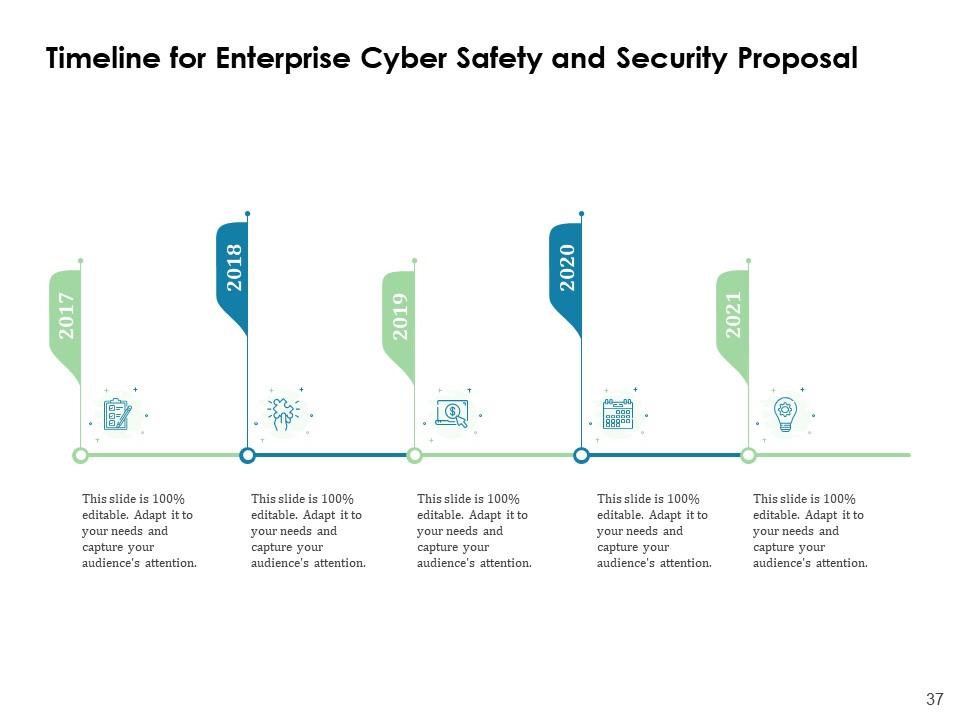
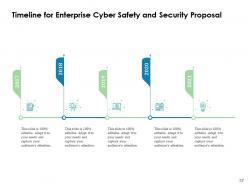
Slide 37: This slide showcases Timeline process.
Enterprise Cyber Safety And Security Proposal Powerpoint Presentation Slides with all 37 slides:
Use our Enterprise Cyber Safety And Security Proposal Powerpoint Presentation Slides to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
Easy to edit slides with easy to understand instructions.
-
The Designed Graphic are very professional and classic.
-
The content is very helpful from business point of view.