Cyber security it powerpoint presentation slides
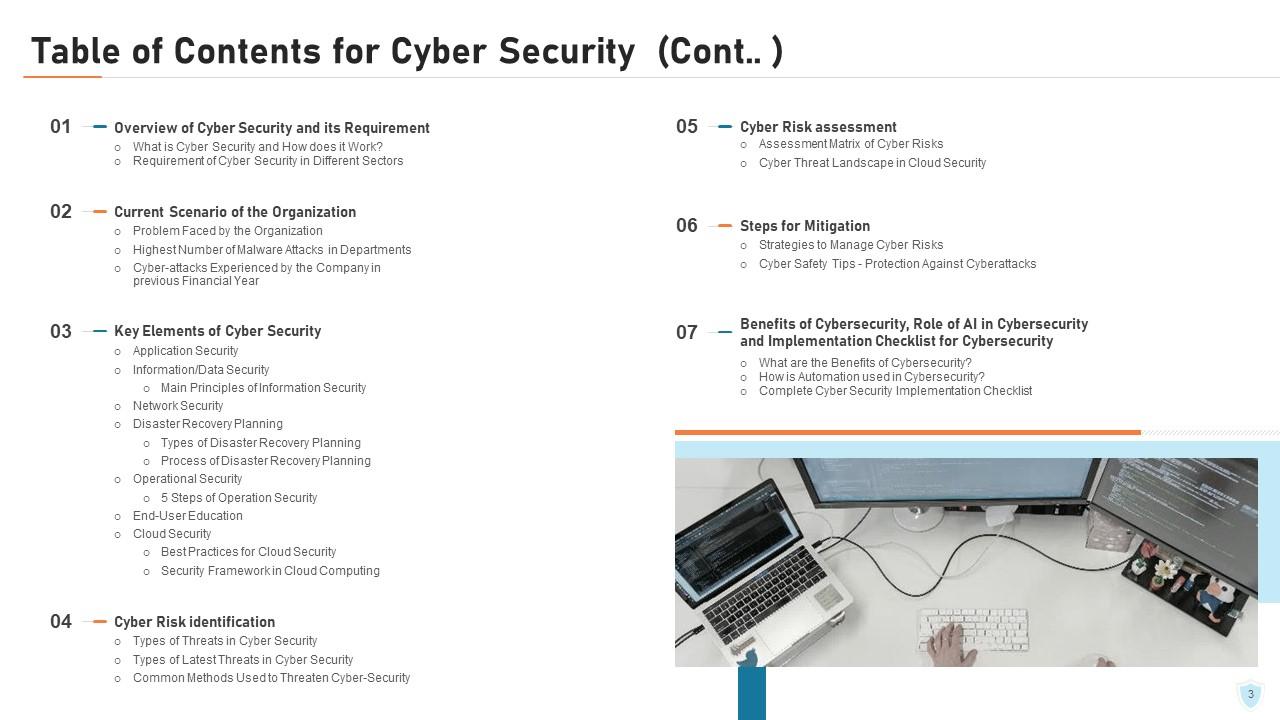
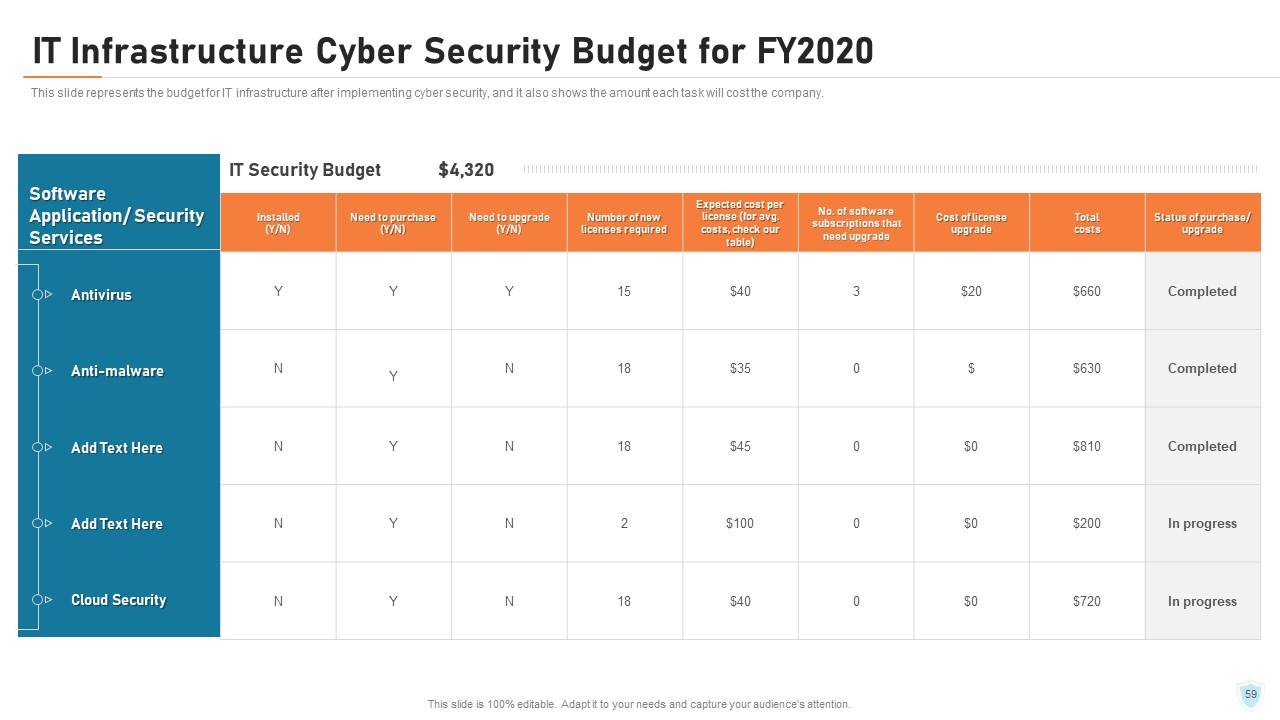
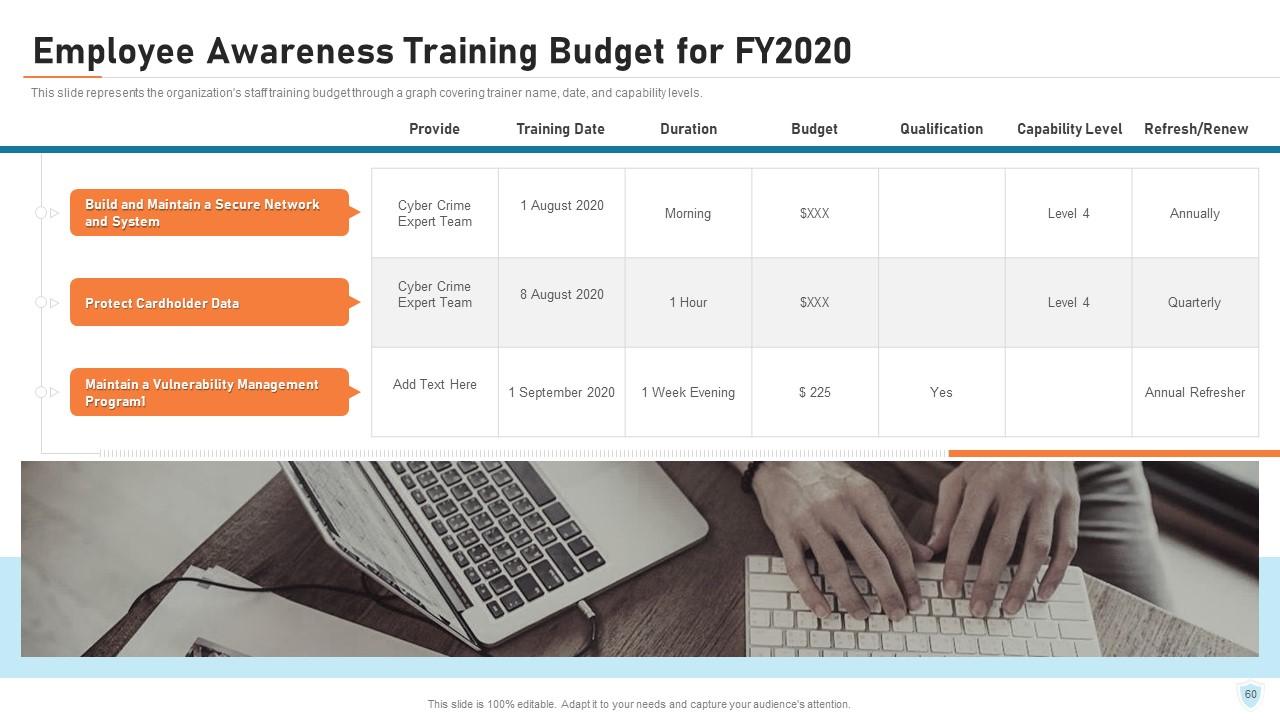
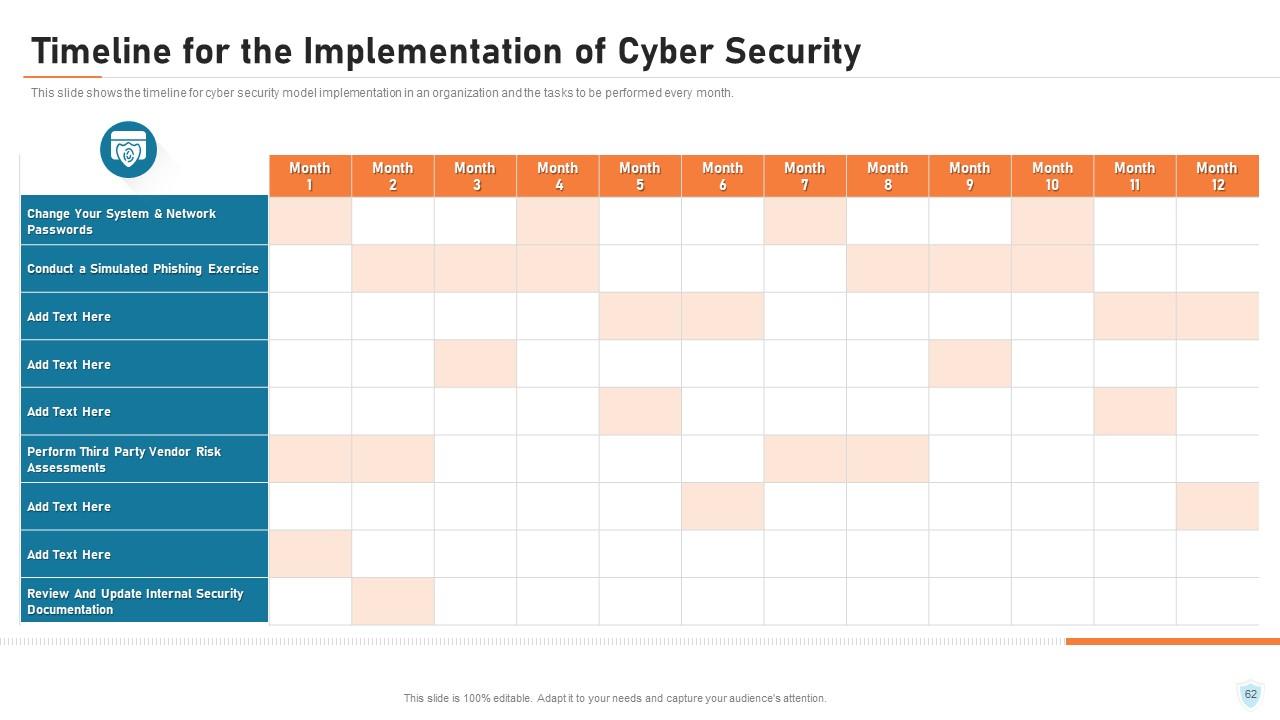
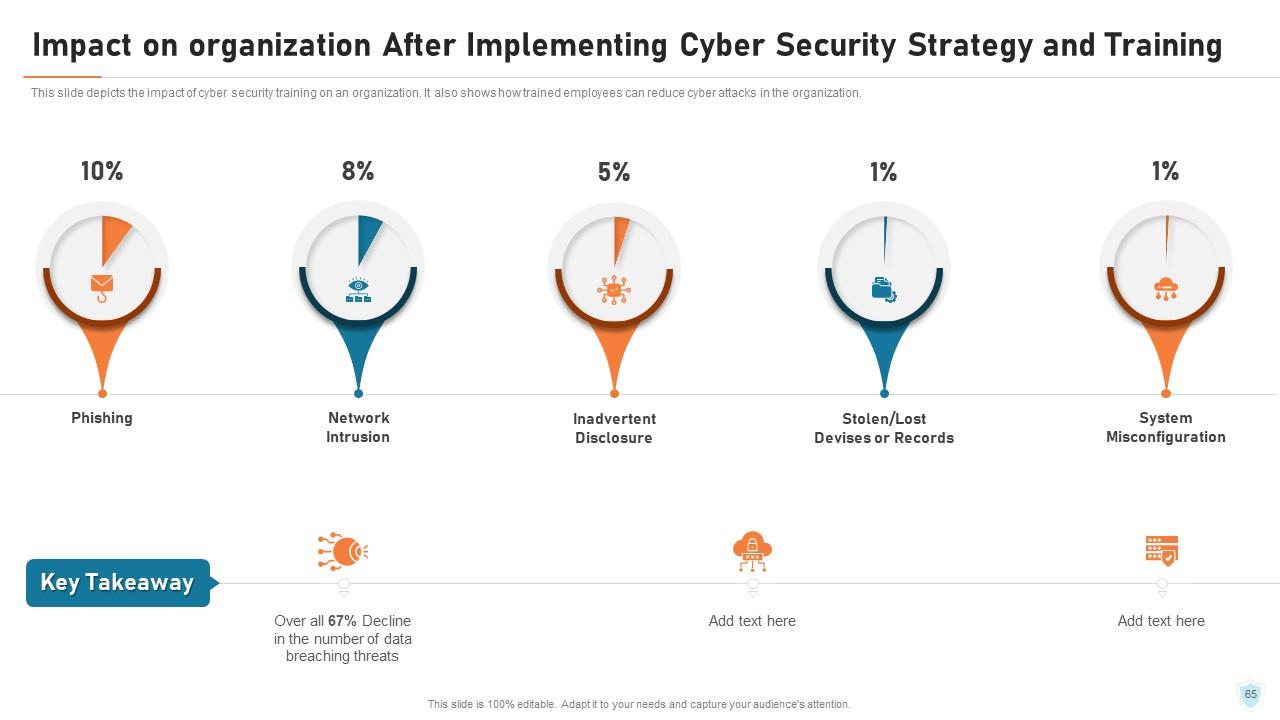
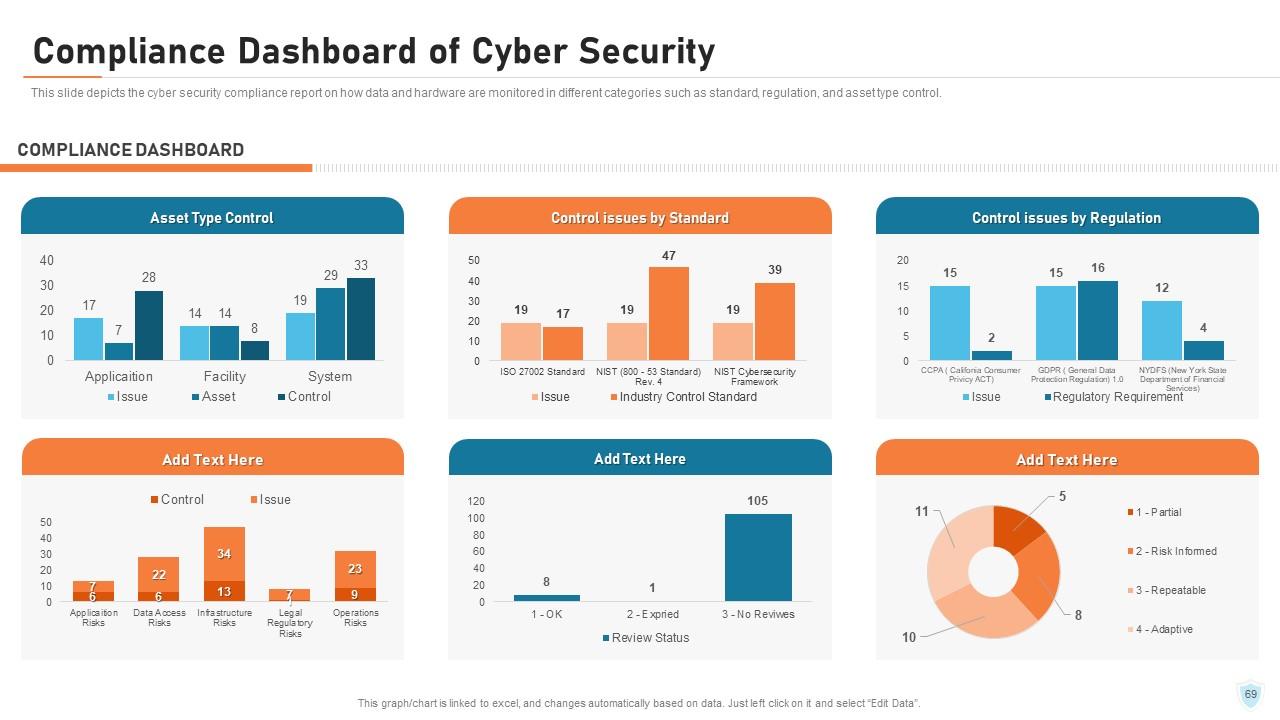
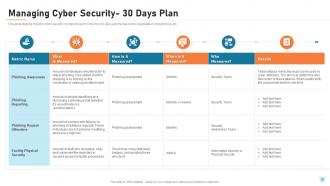
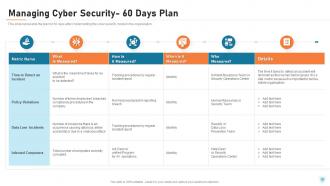
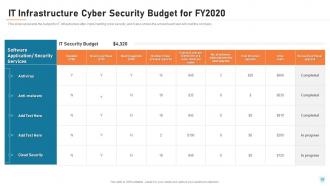
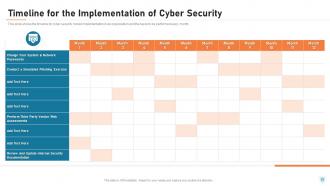
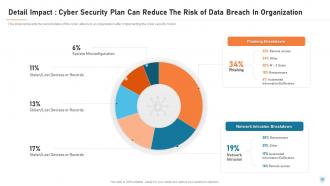
Cyber Security is the process of protecting electronic devices such as computers, servers, mobile gadgets, data, electronic systems, and networks from cyber-attacks. This PowerPoint presentation illustrates significant details about cybersecurity. Incorporating this PPT, you can present and share details on the common threats against data and information systems and the process to identify the information that needs to be protected. This network security PowerPoint presentation will be helpful to throw light on the current scenario of the organization, the requirement of cybersecurity in different sectors, and it's working. In addition, computer security PPT contains the critical elements of cybersecurity, cyber risk identification and assessment, steps to mitigate those risks, and benefits of cybersecurity, along with automation's role in cybersecurity. Further, this data security presentation comes with a checklist to implement cybersecurity in the organization, a 30-60-90-day plan to manage cybersecurity, and the budget to implement the same. The Information Security deck also showcases a roadmap to monitor cybersecurity and a timeline to implement cybersecurity in the organization. Lastly, this electronic information security PPT shows the effects of cybersecurity implementation on the organization and dashboard for threat tracking in cybersecurity. Talk to our expert and get access to our cybersecurity ppt template for generating a security framework for yourself. Download it now.
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Deliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Cyber Security It Powerpoint Presentation Slides is the best tool you can utilize. Personalize its content and graphics to make it unique and thought provoking. All the eighty one slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
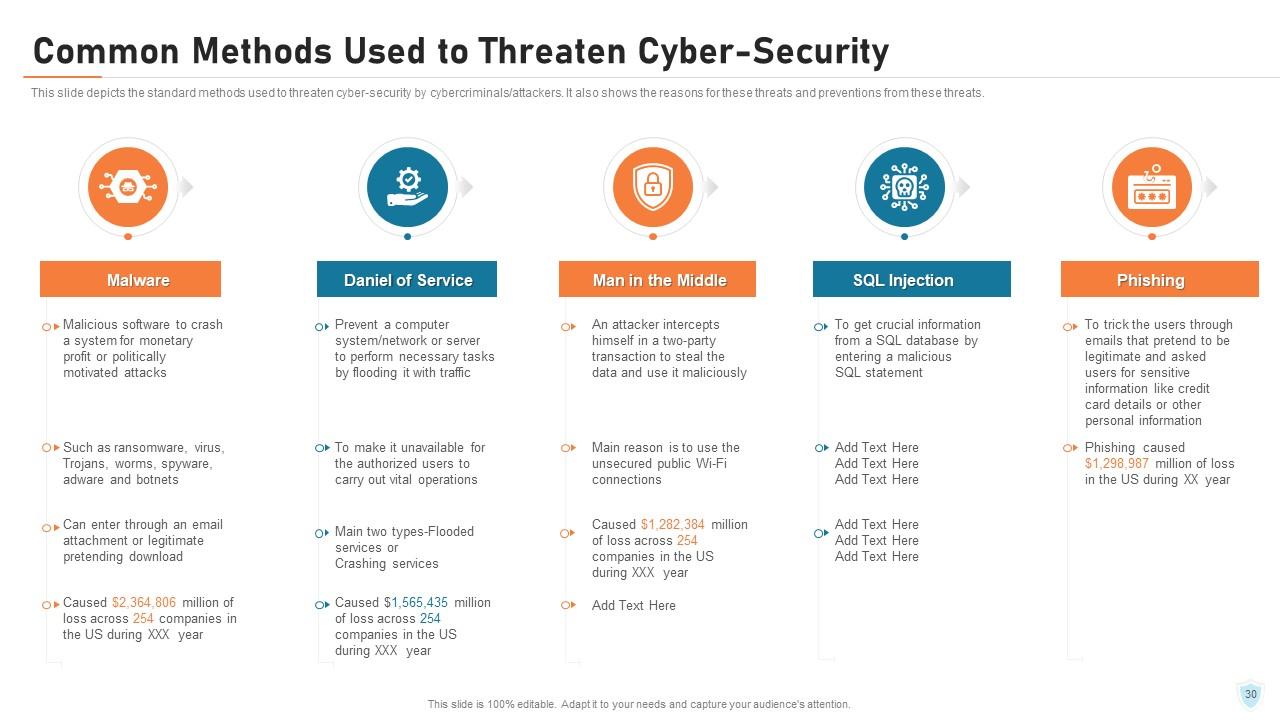
Today, we witness an increasing reliance on digital technologies in all aspects of life. This is why cybersecurity has become a critical concern for individuals, organizations, and governments across the world. According to a recent statistic that Forbes has published, 2,365 cyberattacks were reported in 2023 and these targeted 343 million victims. Additionally, 35% of malware was delivered via email, and more than 94% of organizations reported email security incidents. The effect of cyberattacks can be overwhelming for a business. This includes financial disruption, severe damage to reputation, and legal issues.
To gain insights on cybersecurity, refer to these well-crafted slides.
It is high time that businesses realize the need to learn and spread knowledge about cybersecurity, ways to minimize the risk of cyberattacks, and strategies to respond appropriately to cyber threats. Providing awareness of cybersecurity fosters a culture of security within society. As a result, we shall begin to prioritize cybersecurity practices that help to protect digital assets from theft, loss, or unauthorized access.
You may check out the best PowerPoint presentation slides for providing training on cybersecurity awareness. Click here!
Organizations need to know about their level of readiness to defend themselves and their digital assets, which is Cybersecurity Maturity. To check out the best templates on cybersecurity maturity. Click here!
For a better understanding of cybersecurity, SlideTech Systems offer a wide variety of PPT Slide templates. These are created by the professional experts and involve world-class aesthetics, and actionable pointers to ensure users can act on the information. Each slide is 100% editable and customizable so you can tailor each presentation as per your needs and preferences.
Let’s explore each of these templates!
Template 1 – What is Cyber Security and How it Works?
The beginning of your presentation sets the impression. Remember that Well Begun is Half Done. Cybersecurity awareness can only be explained when people understand its concept. Here is the first PPT Slide in which you can describe and define Cybersecurity and also explain how it works. Put all the ideas in pointers in a clear and concise way leaving no room for doubt. Now, you are good to go ahead!
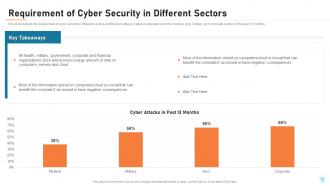
Template 2 – Requirement of Cyber Security in Different Sectors
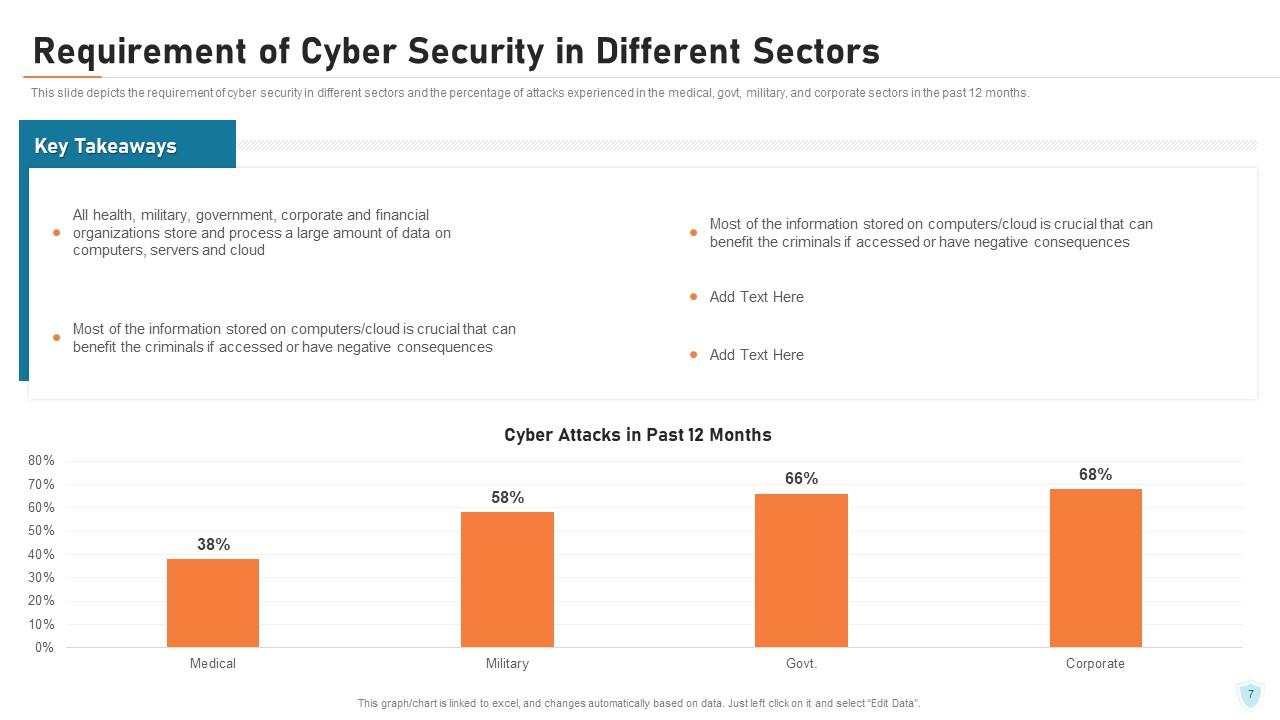
This PPT Template depicts the need for cybersecurity across sectors You can see the percentage of attacks on the military, government and corporate sectors in the past 12 months. Using this slide, you can mention how fast and to what extent cyber attacks have affected our society. Facts are the best way to convince people regarding the seriousness of an issue. Raise an alarm to minimize cyber crimes!
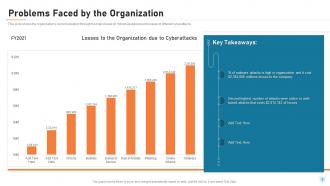
Template 3 – Problems Faced by the Organization
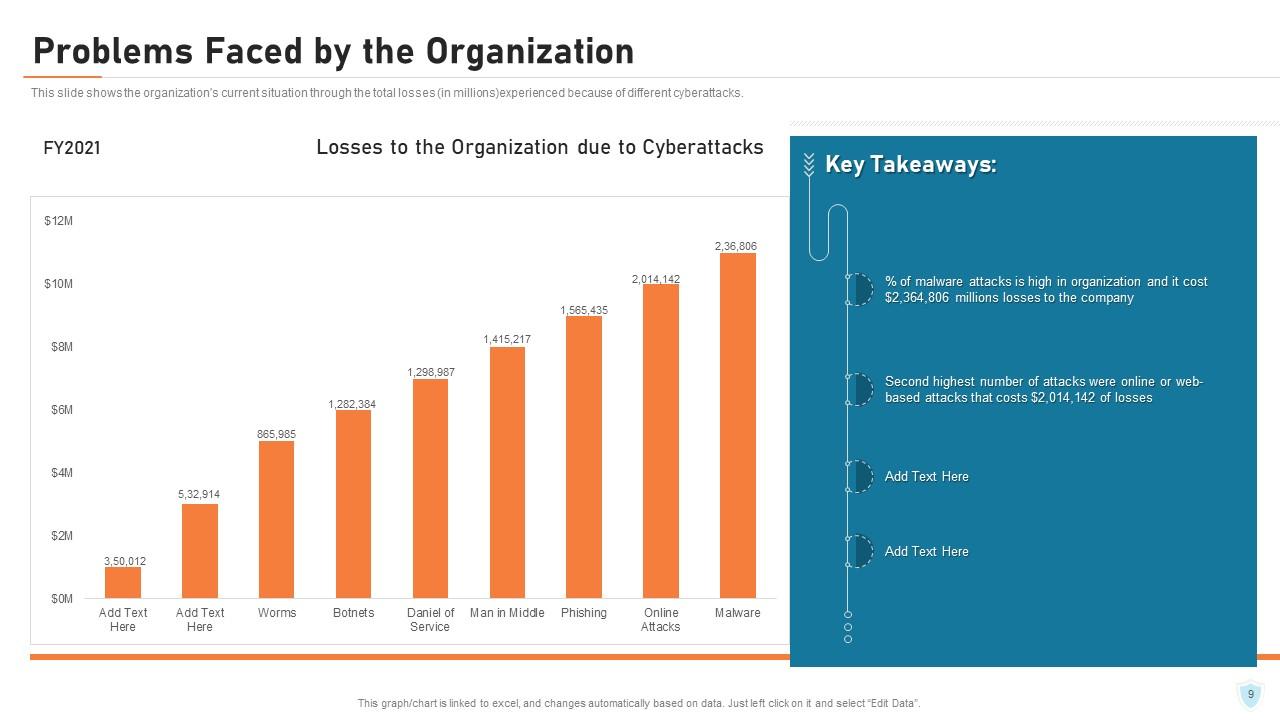
Organizations have been deeply affected due to Cyberattacks. These attacks led to financial losses and disruption of operations, etc. This PPT Slide displays the situation of the organization as a result of cyberattacks. Users will find this template helpful to know about the severity of the damage caused by negligence of cybersecurity.
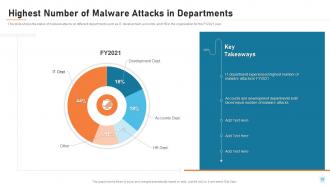
Template 4 - Highest Number of Malware Attacks in Departments
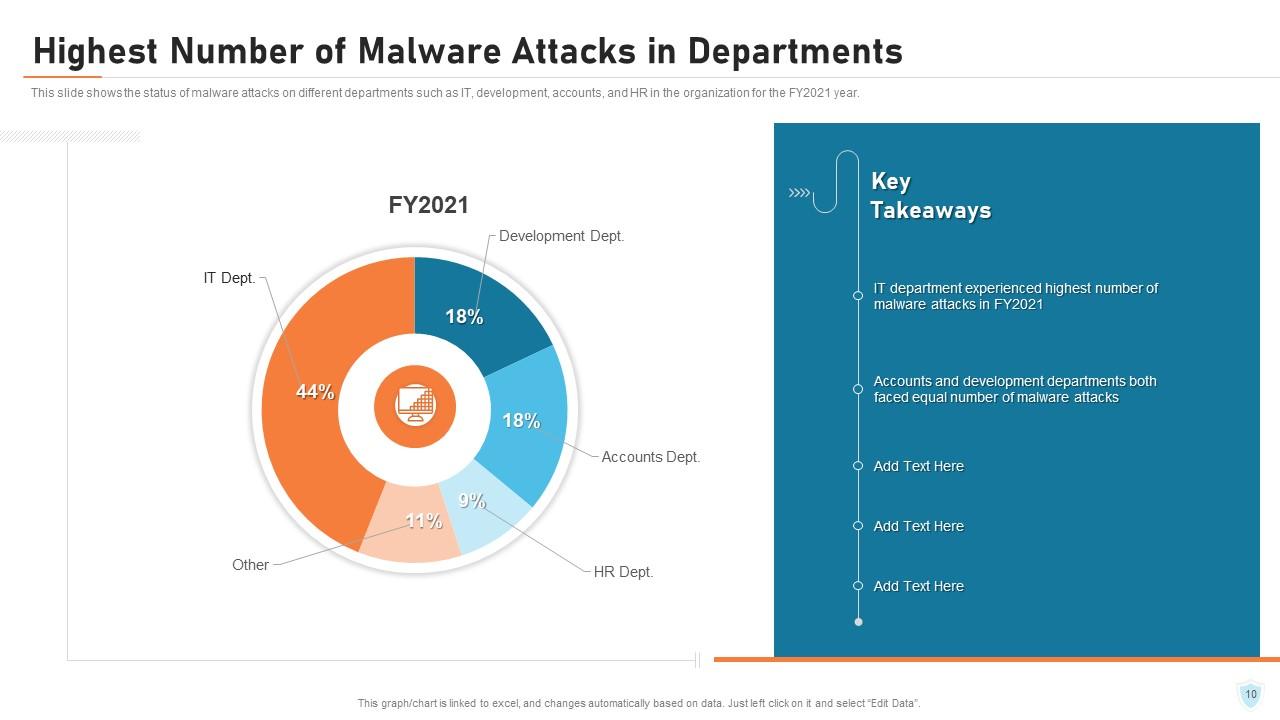
Having an understanding of which departments are most vulnerable to malware attacks is critical for risk management. This PPT Slide illustrates the status of malware attacks on departments such as IT, Development, Accounts,HR and others. Writing statistical information presents the authenticity of data. It also grabs more attention than other details. You must collect accurate data on the cyberattacks and use this template for an appealing cybersecurity powerpoint presentation.
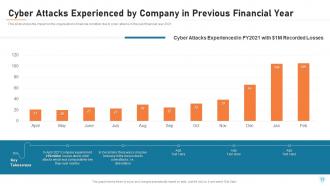
Template 5 - Cyber Attacks Experienced by Company in Previous Financial Year

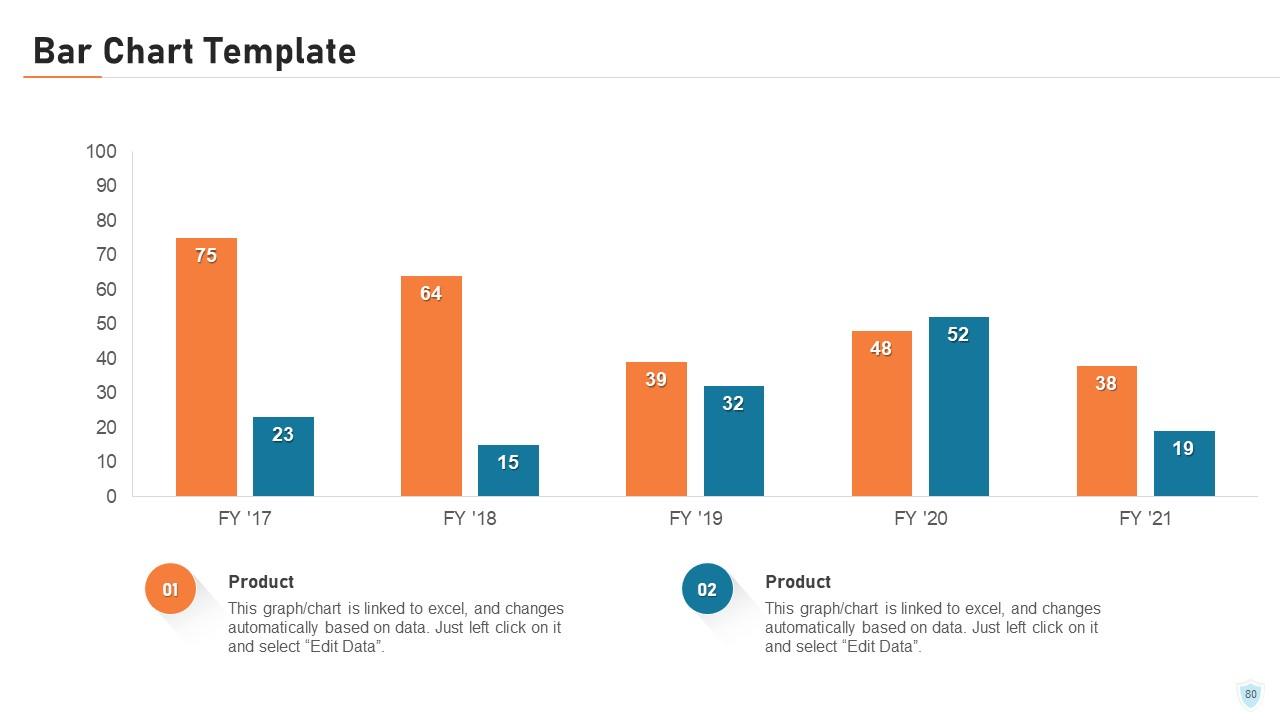
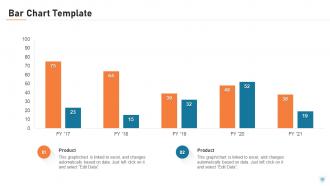
Cyber attacks can occur at any point of time and it can deplete the financial condition of an organization causing losses due to theft of funds, extortion demands, or disruption of financial transactions. Fraudulent transactions may drain accounts. This PPT Template depicts the impact of cyberattacks on a company’s financial condition in a particular year which will be helpful to keep an account of the losses incurred in that year.
Template 6 - Key Elements of Cyber Security
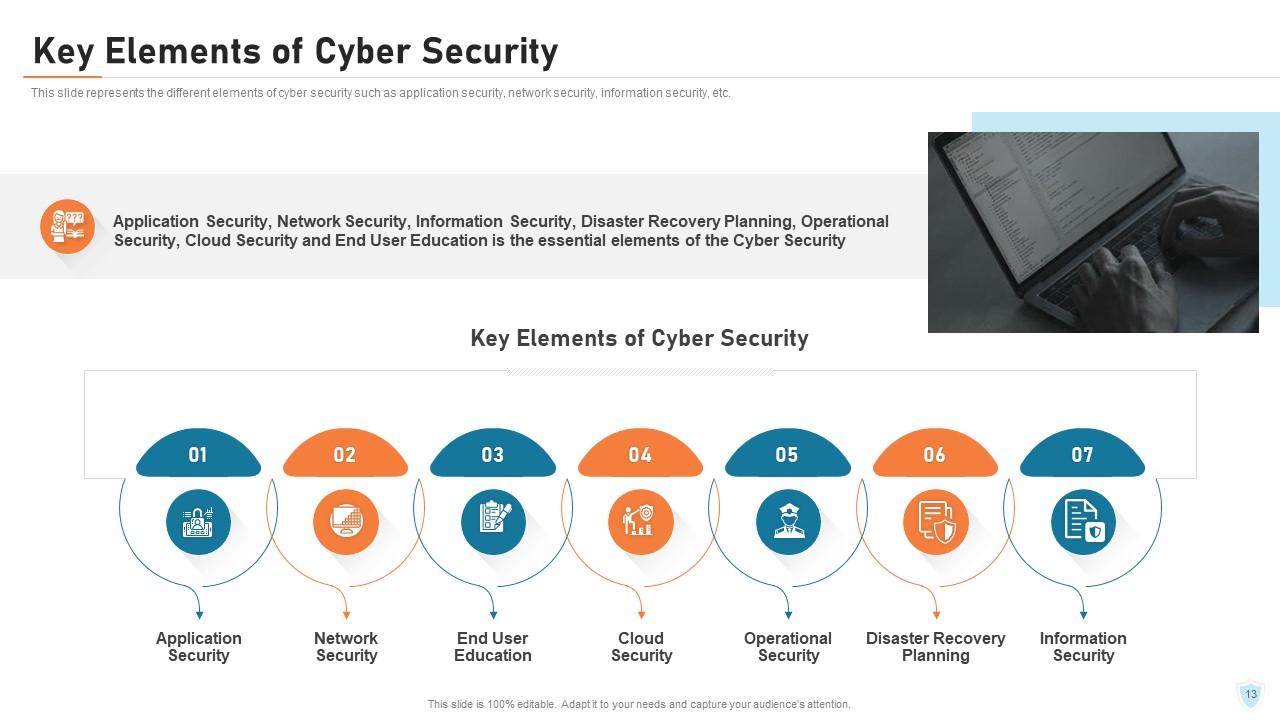
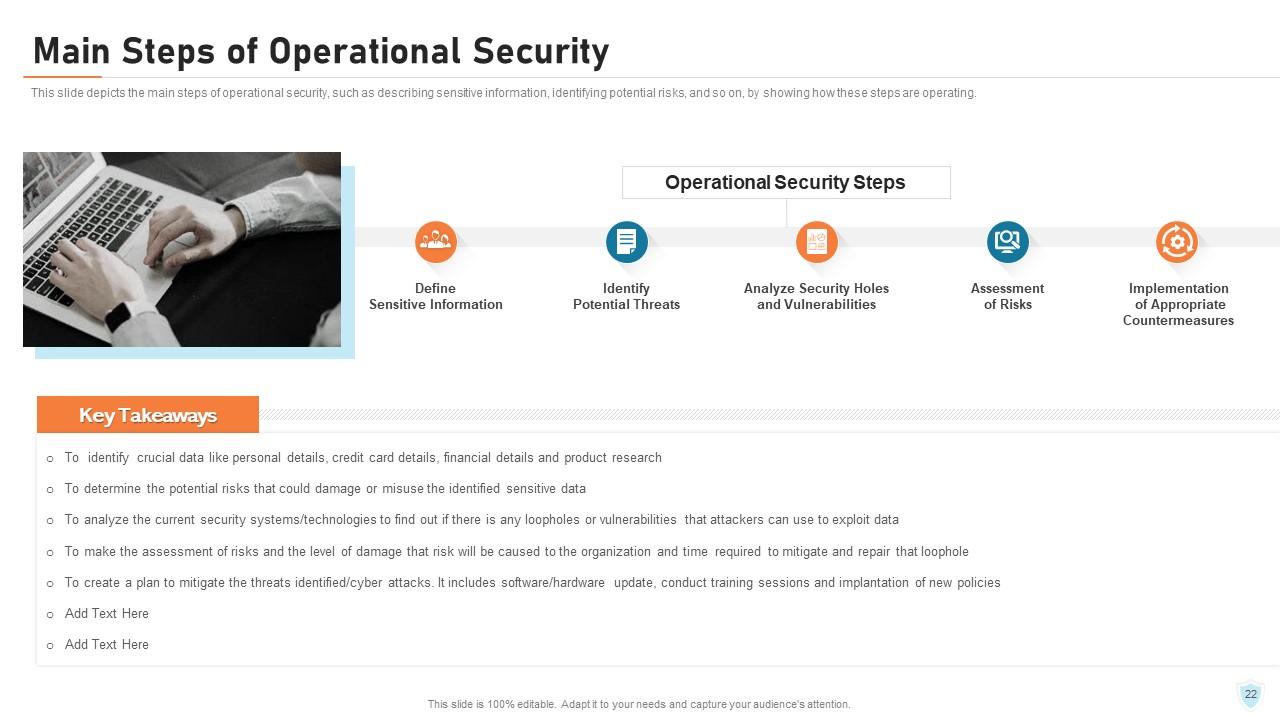
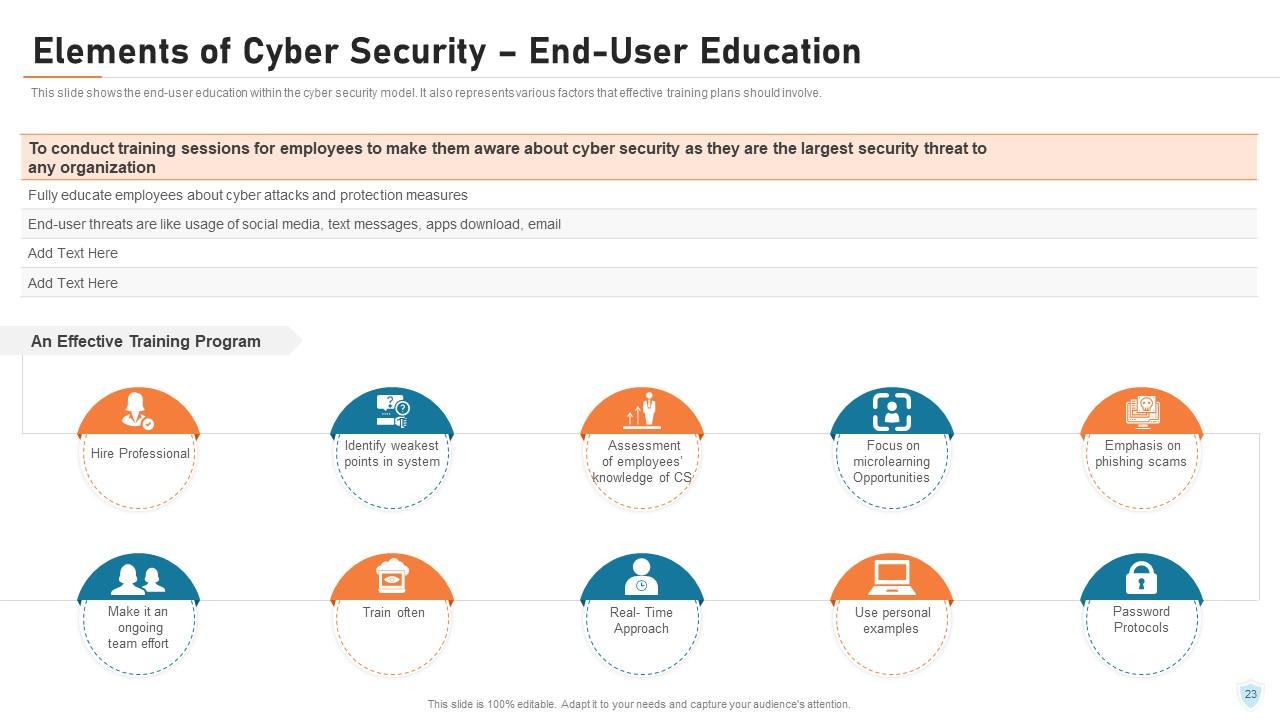
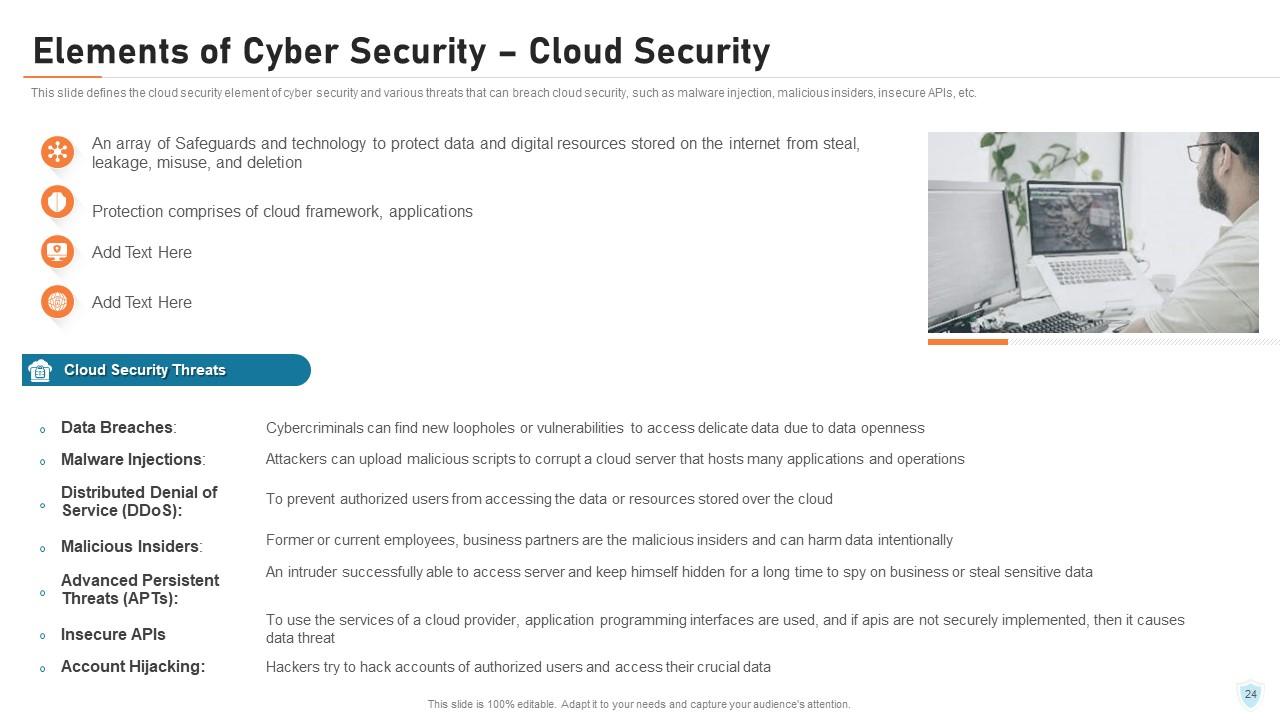
There are key elements of cybersecurity that organizations must enhance their ability to protect against cyber threats and safeguard their assets and information by incorporating these important elements. In the slide above, you can see some of them, for example, Application Security, Network Security, End User Education, Cloud Security, Operational Security, Disaster Recovery Planning and Information Security. Each of these elements play a vital role in protection against cyber threats.
Template 7 - Elements of Cyber Security - Application Security
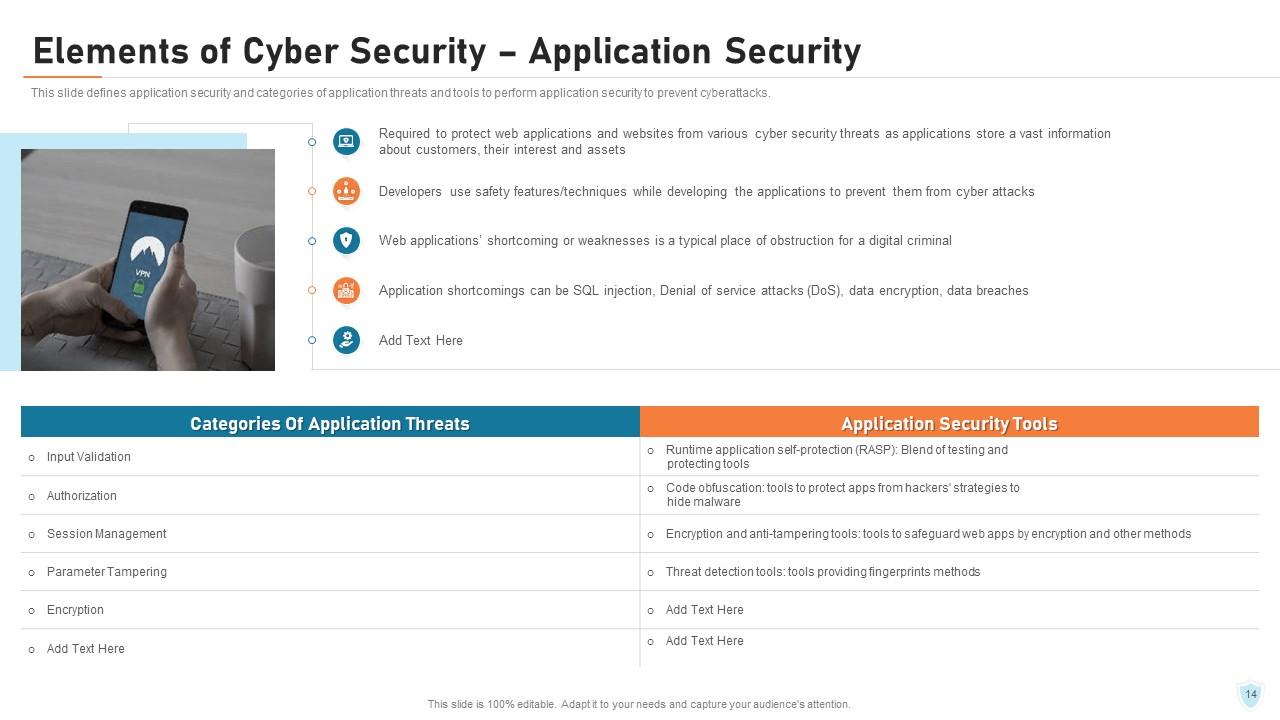
Applications are easily available over various networks and connected to the cloud, which increases vulnerabilities to security threats and breaches. You can protect software applications from cyber attacks using Application Security. It will help to ensure the confidentiality, integrity, and availability of data and functionality. This PPT Slide defines application security. Here you will find categories of application threats, for example, Input Validation, Authorozation, Session Management etc. and application security tools.
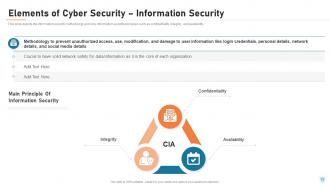
Template 8 – Elements of Cybersecurity: Information Security
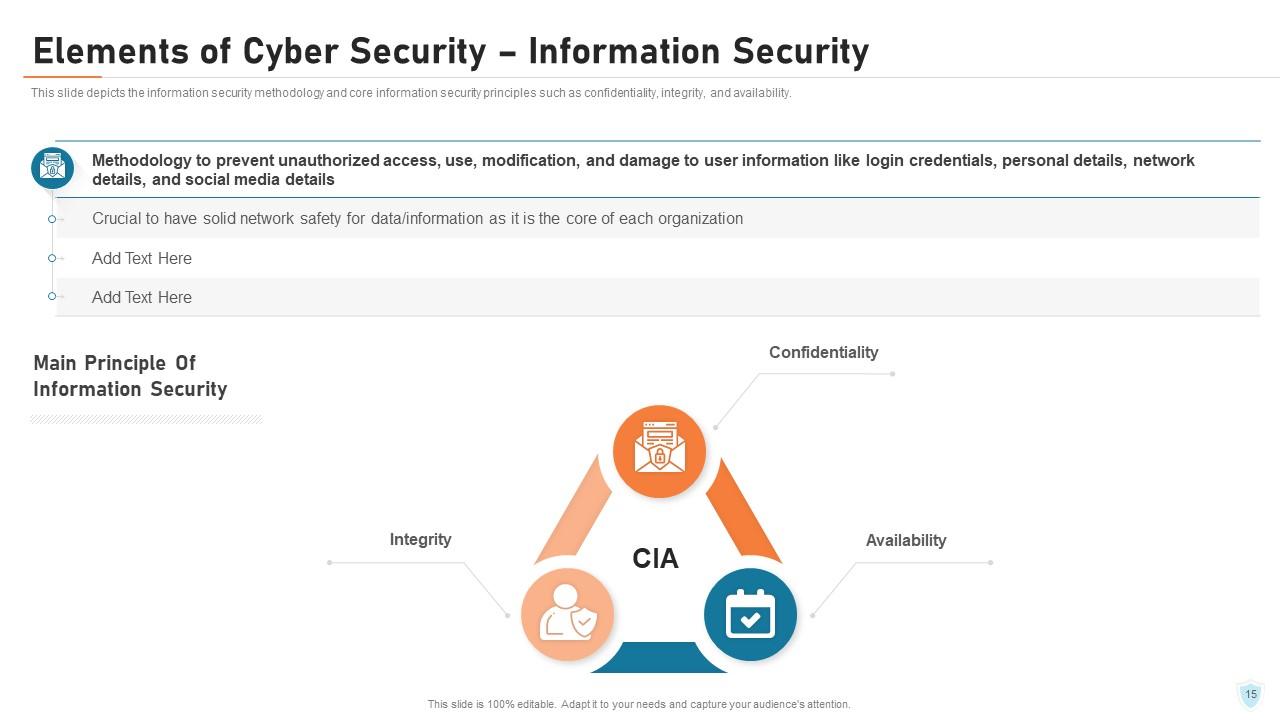
Information security is another aspect of an organization. It encompasses a range of practices and technologies required for protecting data and information systems from cyberattacks such as malware, phishing, ransomware, and hacking. Using this PPT Template, you can discuss about the information security methologies and core information security principles, namely Confidentiality, Integrity and Availability(CIA).
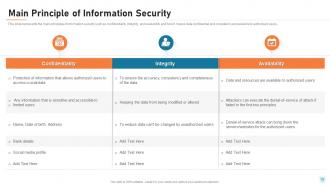
Template 9 – Main Principle of Information Security

This PPT Template shows the description of the main principles of Information Security which is commonly known as CIA.i. e Confidentiality, Integrity and Availability. Confidentiality ensures that sensitive information is only accessible to limited users. Certain measures such as encryption, access controls, are implemented to prevent unauthorized access to confidential data.Integrity assures data is accurate, consistent and complete. Availability ensures data and resources are available only to the authorized users.
Template 10 - Elements of Cyber Security - Network Security
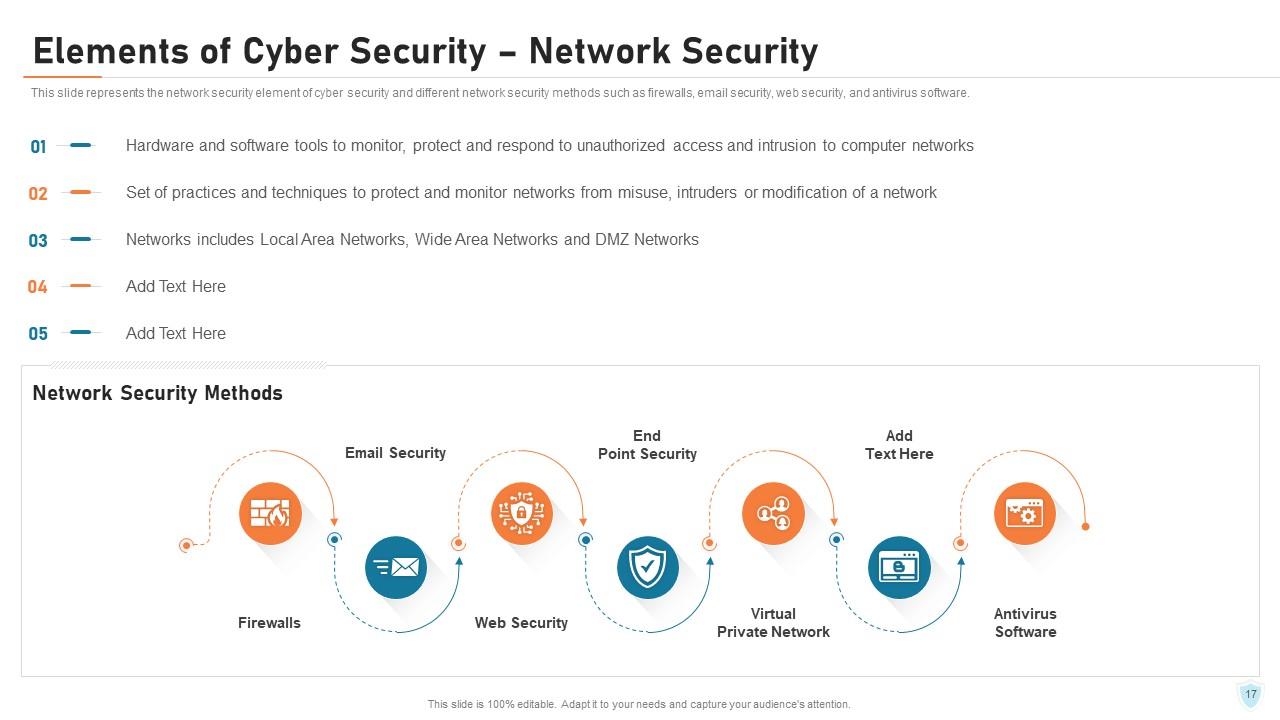
The prevention of cyberattack also requires ensuring Network Security. It refers to the measures implemented to protect the computer network and its data from unlawful access and misuse. In the slide above, you can find out the definition of Network Security explained in points. Additionally, it demonstrates network security methods such as Firewalls, Email Security, Web Security, End Point Security, Virtual Private Network, Antivirus Software etc.
*****
PROTECT YOUR CYBERWORLD TO SECURE YOUR BUSINESS
This blog helps us comprehend cybersecurity and outlines its importance especially for businesses. The PPT Slide templates shown above will help you to make people aware about the impact of cyberattack, instruct tips and tactics to prevent them and so much more.
P S Begin your cybersecurity awareness journey with well-structured and perfectly designed templates. Click here!
Cyber security it powerpoint presentation slides with all 81 slides:
Use our Cyber Security It Powerpoint Presentation Slides to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
FAQs
Cyber security is important for organizations as it helps prevent data breaches through different methods and techniques. Different sectors have experienced cyber attacks in the past, causing total losses to organizations.
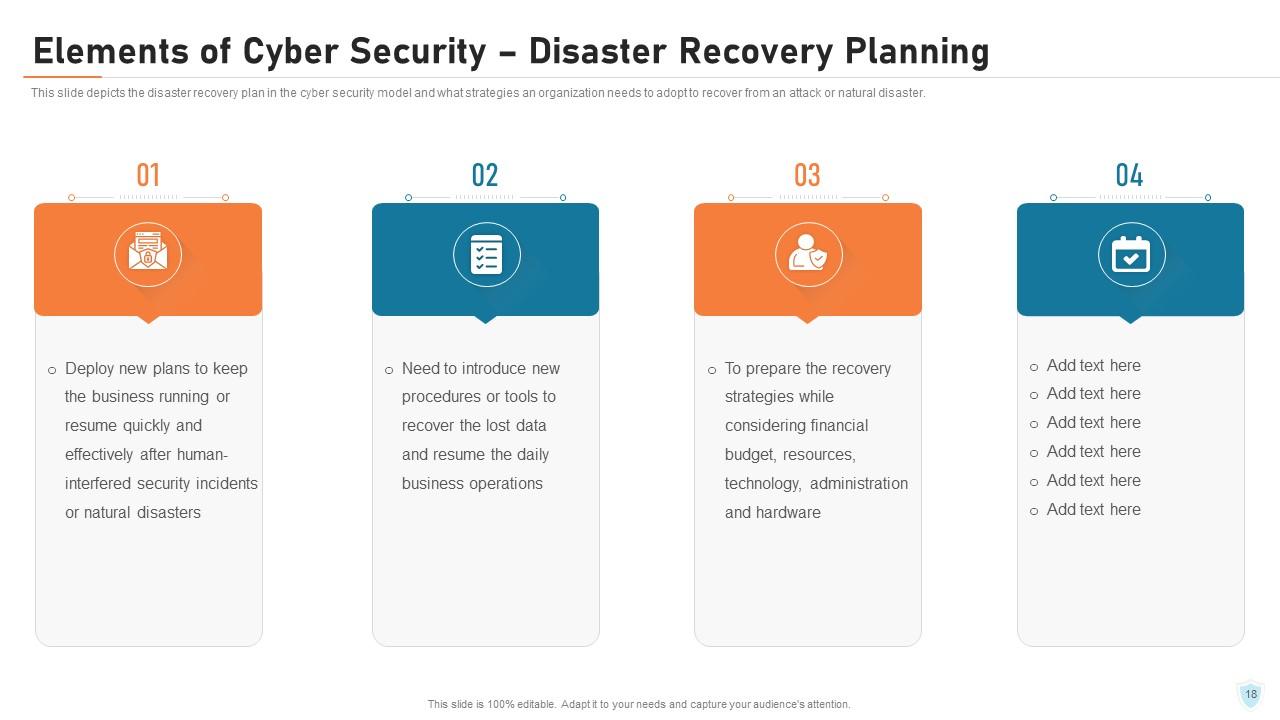
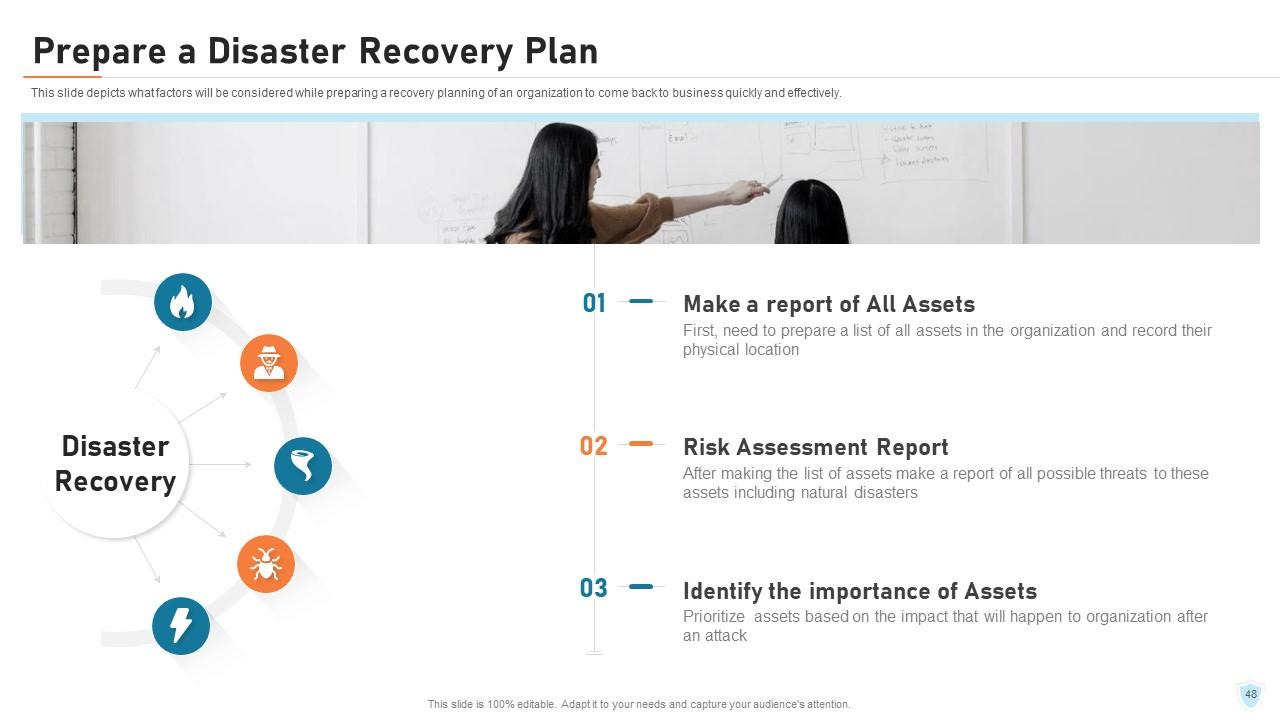
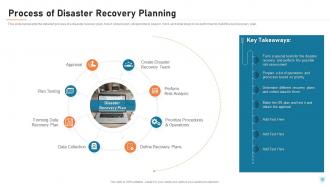
The key elements of cyber security include application security, network security, information security, disaster recovery plan, operational security, end-user education, and cloud security.
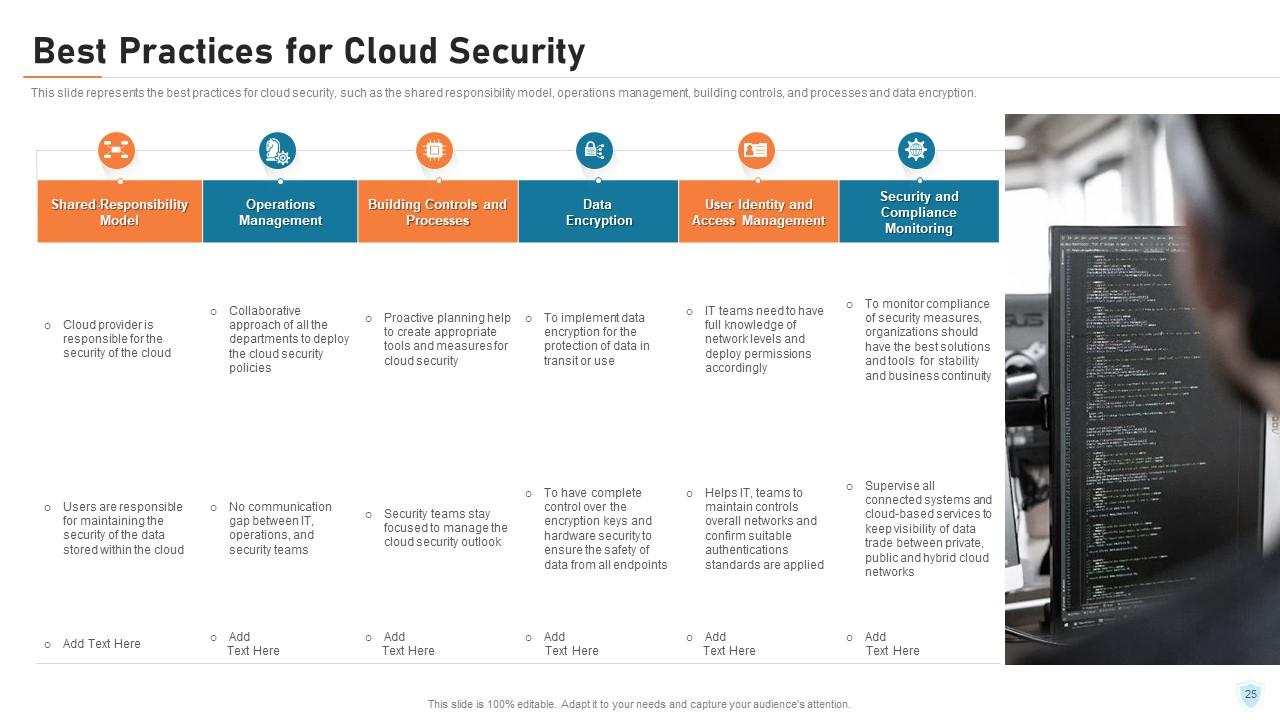
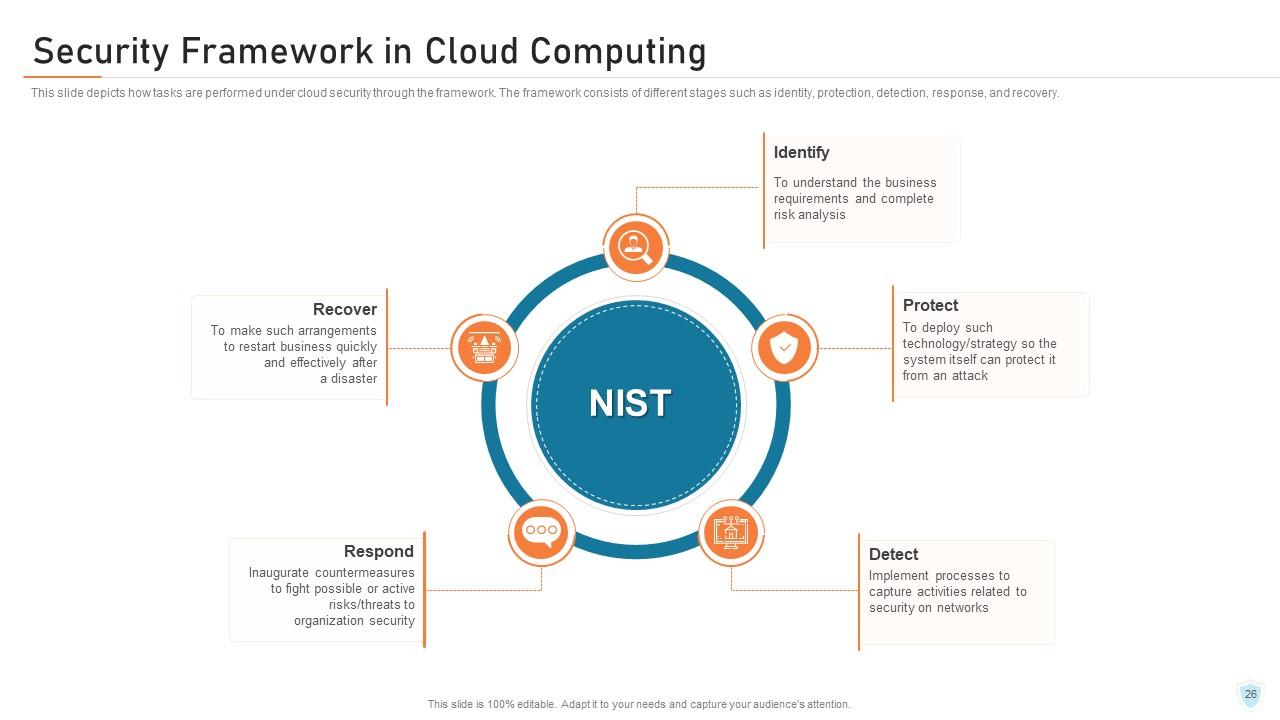
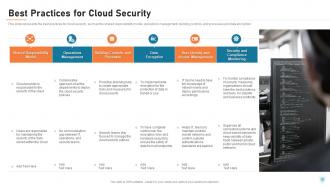
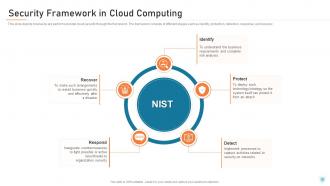
The best practices for cloud security include the shared responsibility model, operations management, building controls and processes, and data encryption.
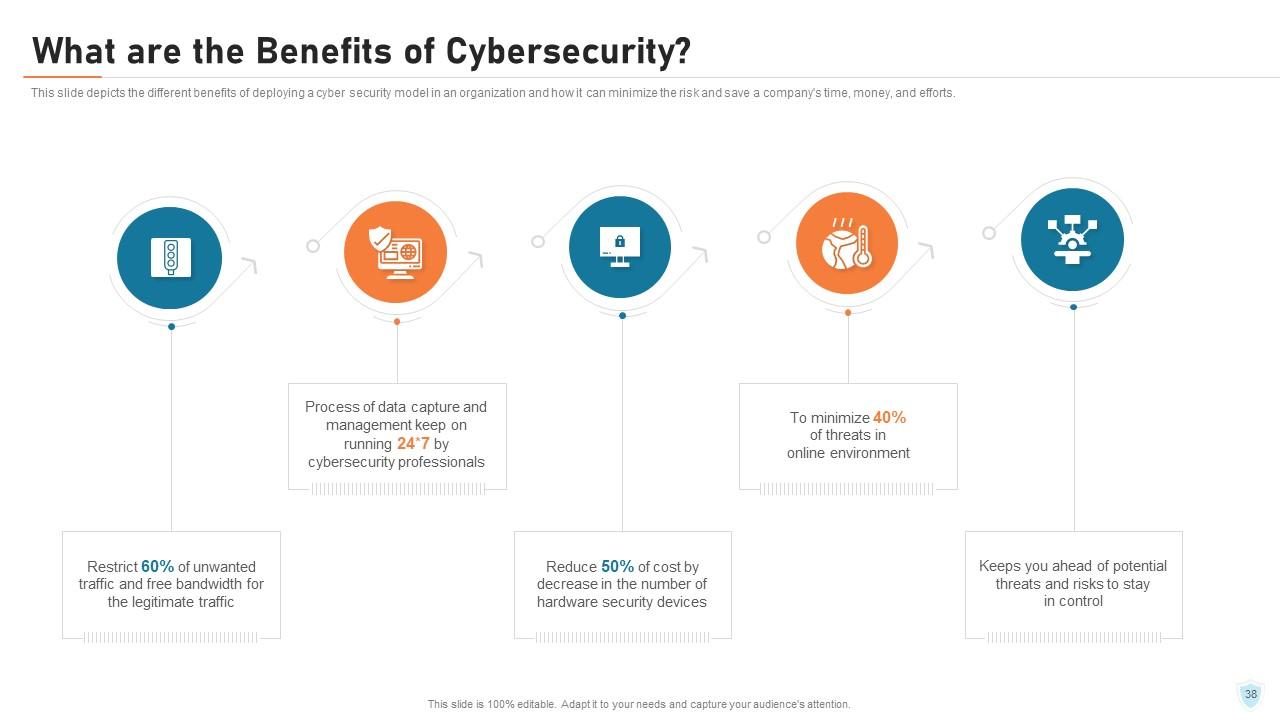
Deploying a cyber security model in an organization can minimize risk and save time, money, and efforts. It can prevent data breaches, protect company assets, and ensure business continuity.
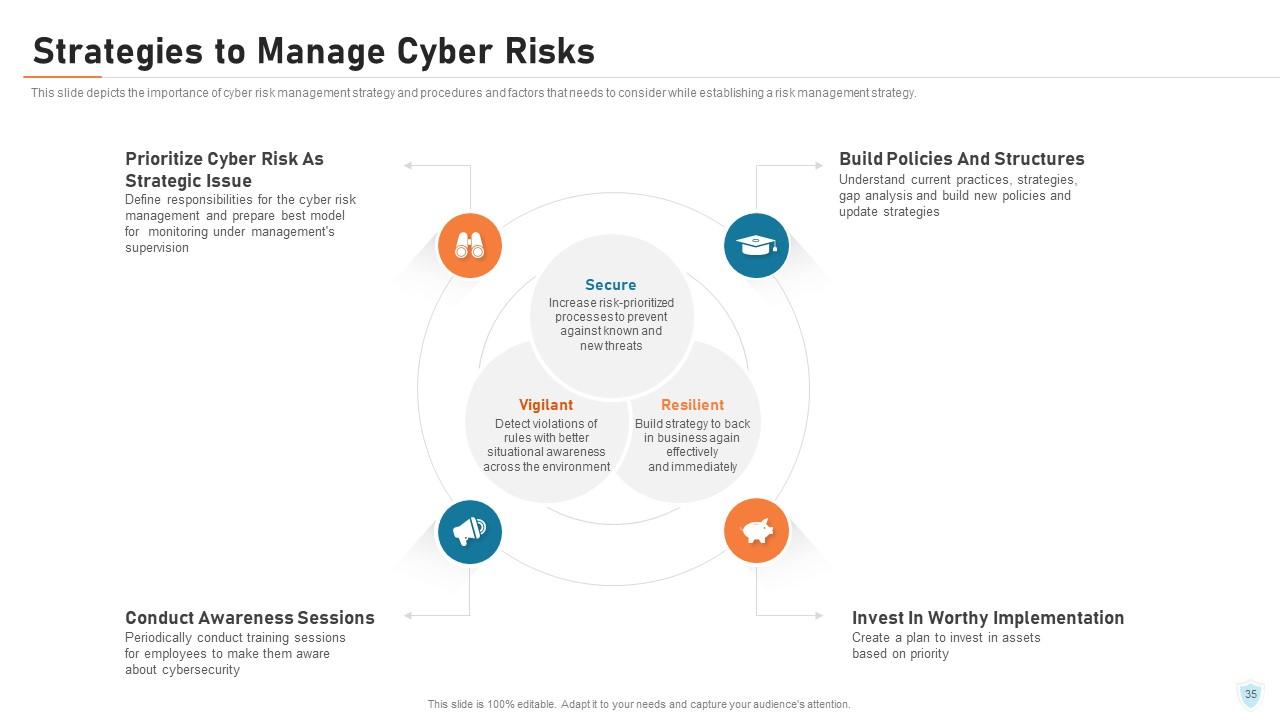
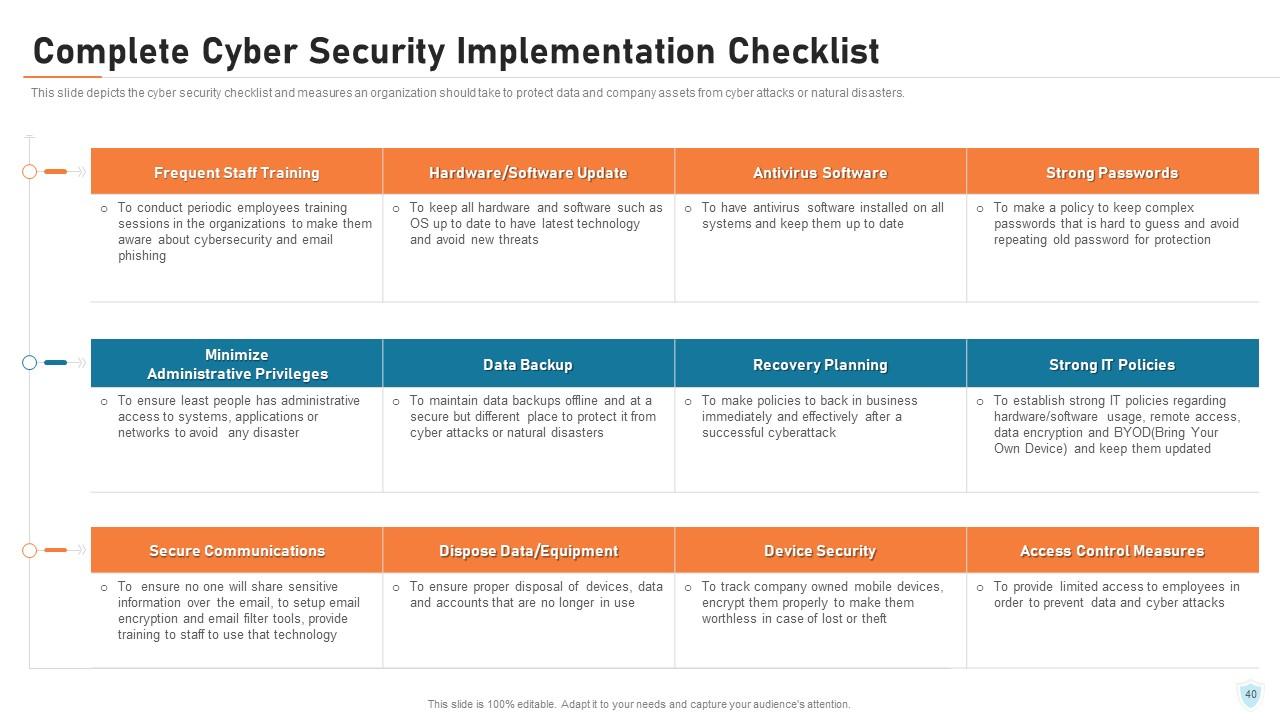
An organization can take various measures to protect data and company assets, including establishing a cyber risk management strategy, following cybersecurity best practices, conducting cyber risk assessment, and implementing a disaster recovery plan. A cyber security checklist can also be used to ensure the protection of data and company assets.
-
It is very good for those who wants to learn cyber security
-
I discovered this website through a google search, the services matched my needs perfectly and the pricing was very reasonable. I was thrilled with the product and the customer service. I will definitely use their slides again for my presentations and recommend them to other colleagues.