How to handle cybersecurity risk powerpoint presentation slides
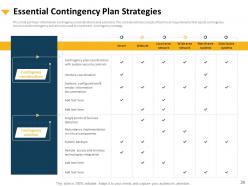
Information technology experts can now take advantage of How To Handle Cybersecurity Risk Powerpoint Presentation Slides. This information security PPT theme infuses top-quality design with data obtained by industry experts. Explain the present situation of the target firm’s information security management employing this PowerPoint layout. The data visualizations featured here simplify the elucidation of complex data such as the analysis of the current IT department. Showcase the cybersecurity framework roadmap and risks of the internet using our PPT presentation. Elaborate on the cybersecurity risk management action plan using the tabular format via this PowerPoint slideshow. Demonstrate the cybersecurity contingency plan with appreciable ease. Our information security management system PPT templates deck assists you in assigning risk handling responsibilities to the staff. Explain the duties of the management in successful information security governance. This PowerPoint presentation also addresses the cost of cybersecurity management and staff training. Hit the download icon and start personalization. Our Cybersecurity PPT Powerpoint Presentation Slides are explicit and effective. They combine clarity and concise expression.
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Presenting How To Handle Cybersecurity Risk Powerpoint Presentation Slides. This complete PPT deck is composed of 55 visually-stunning templates. Build a presentation faster using our 100% customizable PowerPoint slideshow. Edit text, font, colors, orientation, shapes, background, and patterns however you choose. Change the file format into PDF, PNG, or JPG as and when convenient. This presentation works well with standard and widescreen resolutions. Use Google Slides for a quick view.
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
Slide 1: This slide introduces How to Handle Cybersecurity Risk. State your Company name and begin.
Slide 2: This slide displays Agenda for Cybersecurity Management
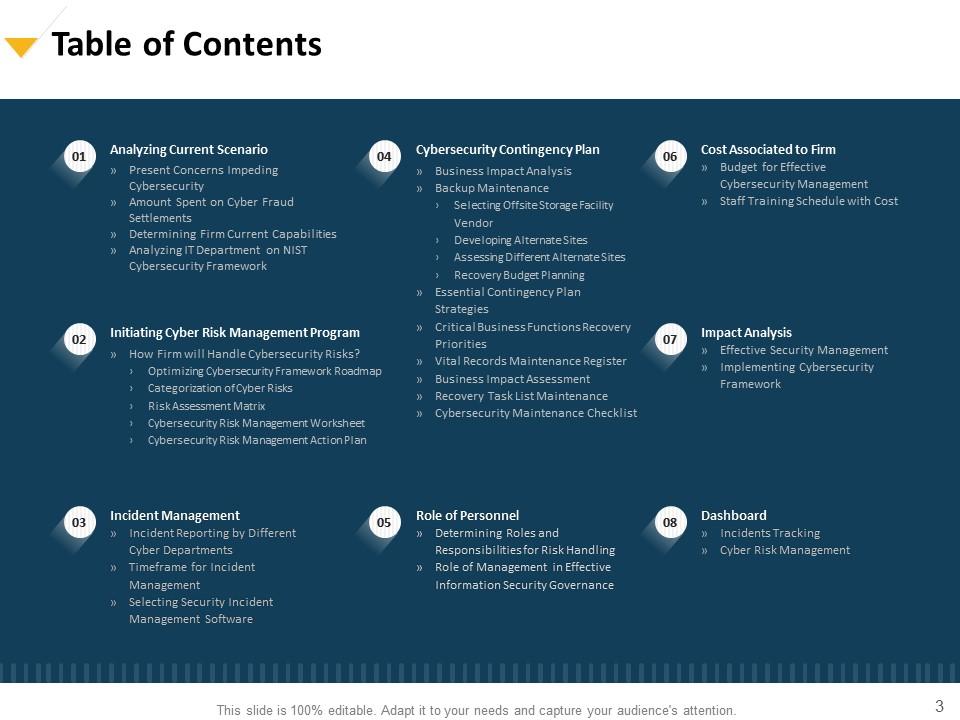
Slide 3: This slide shows Table of Contents of the presentation.
Slide 4: This slide displays Table of Contents.
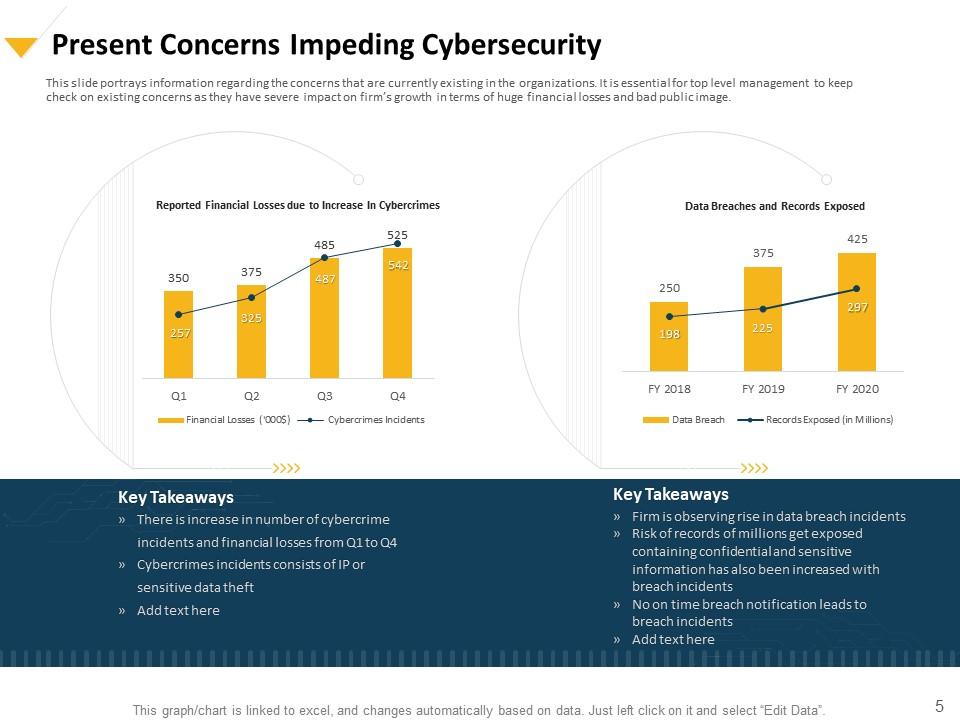
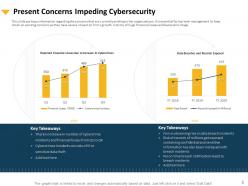
Slide 5: This slide portrays information regarding the concerns that are currently existing in the organizations. It is essential for top level management to keep check on existing concerns as they have severe impact on firm’s growth in terms of huge financial losses and bad public image.
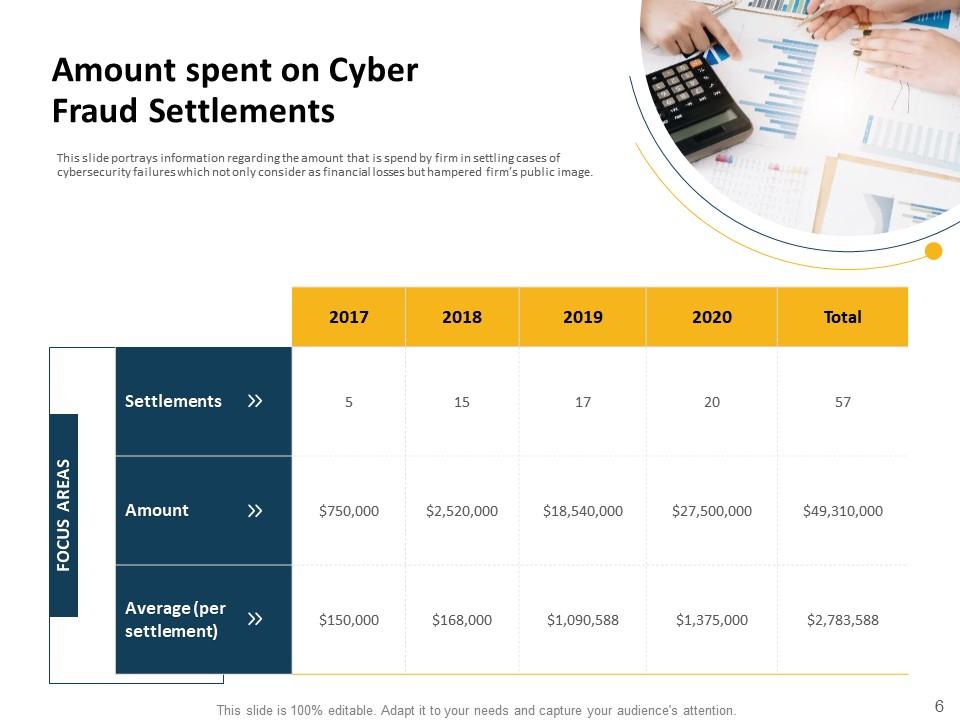
Slide 6: This slide portrays information regarding the amount that is spend by firm in settling cases of cybersecurity failures which not only consider as financial losses but hampered firm’s public image.
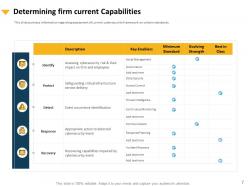
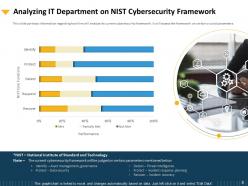
Slide 7: This slide portrays information regarding assessment of current cybersecurity framework on certain standards.
Slide 8: This slide depicts information regarding how firm will analyze its current cybersecurity framework. It will assess the framework on certain crucial parameters.
Slide 9: This slide displays Table of Contents.
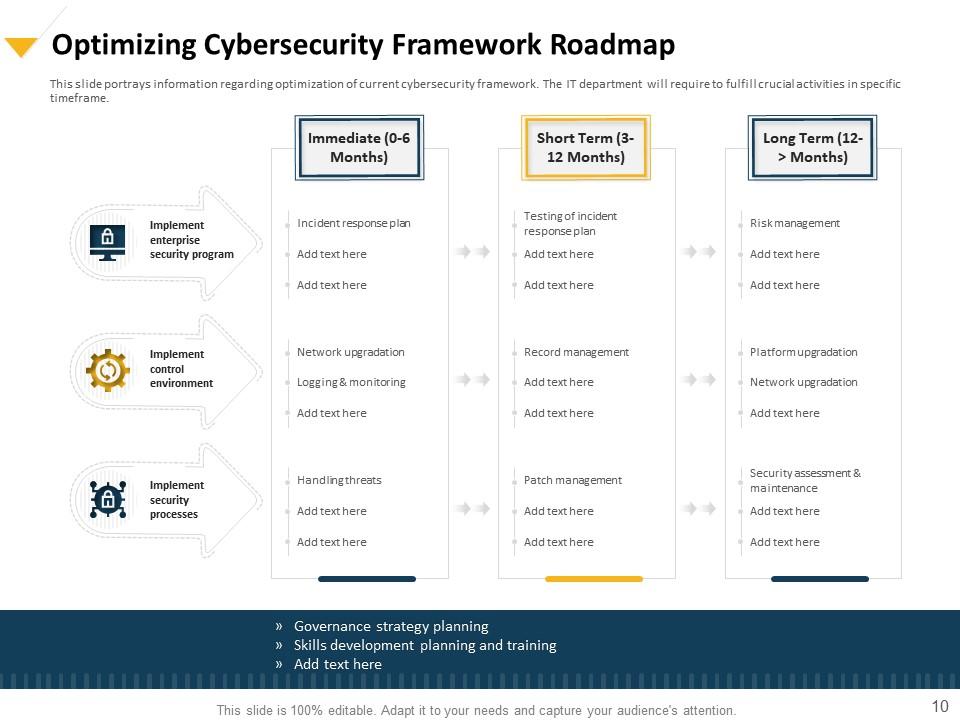
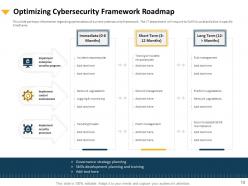
Slide 10: This slide portrays information regarding optimization of current cybersecurity framework. The IT department will require to fulfill crucial activities in specific timeframe.
Slide 11: This slide provides information reading the various cyber risks that firm might face. These risks are categorized into different categories such as low, medium, high, severe and extreme. This categorization is based on certain parameters such as financial impact, damage extent.
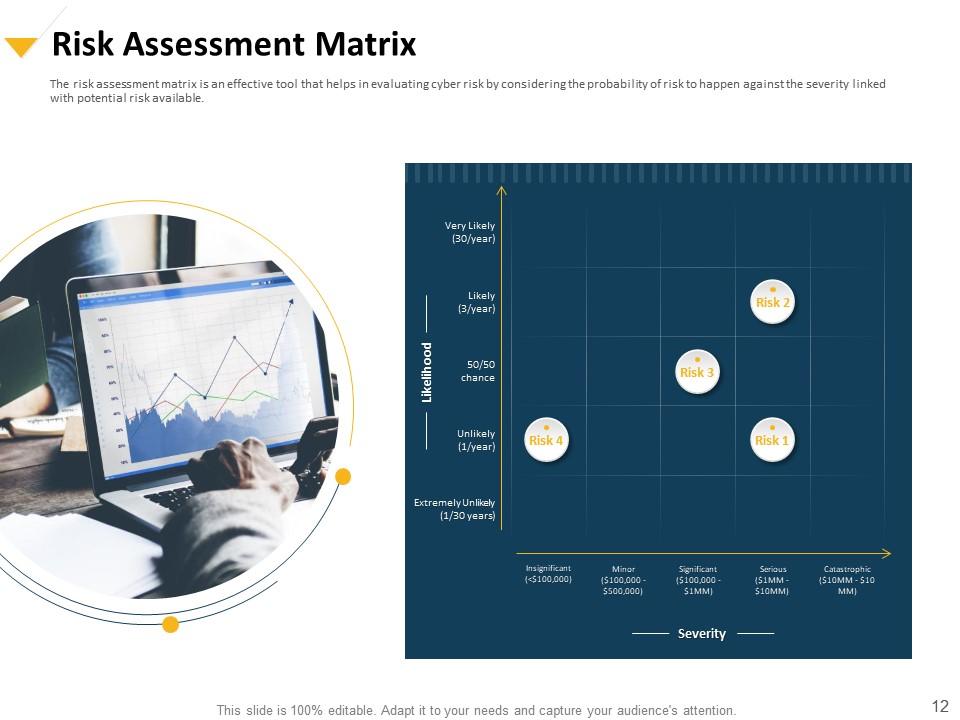
Slide 12: This slide showcases Risk Assessment Matrix.
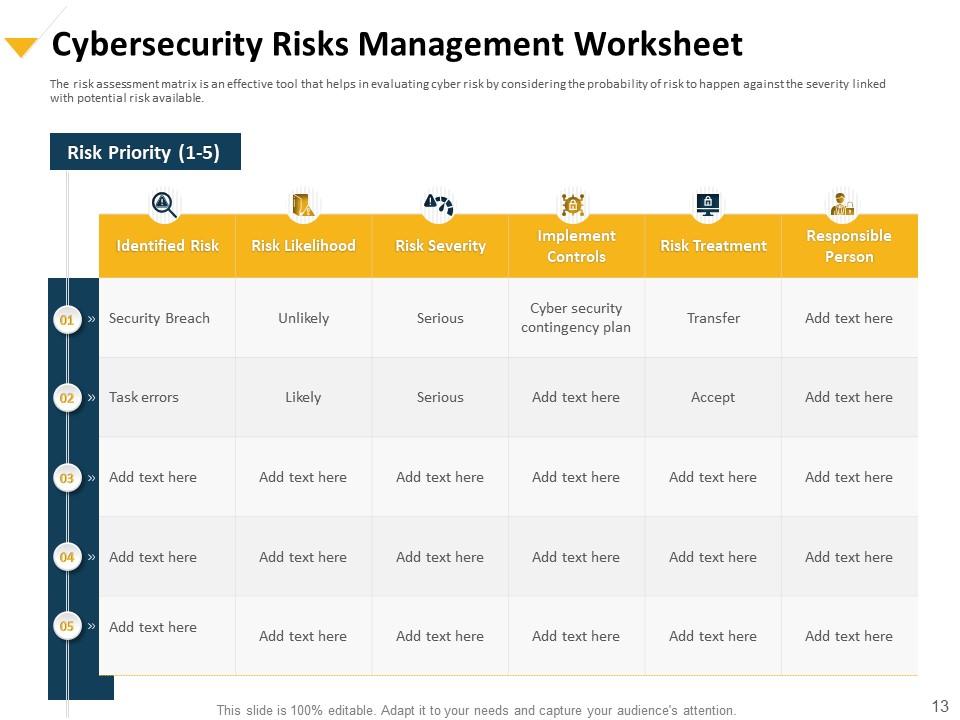
Slide 13: This slide displays Cybersecurity Risk Management worksheet.
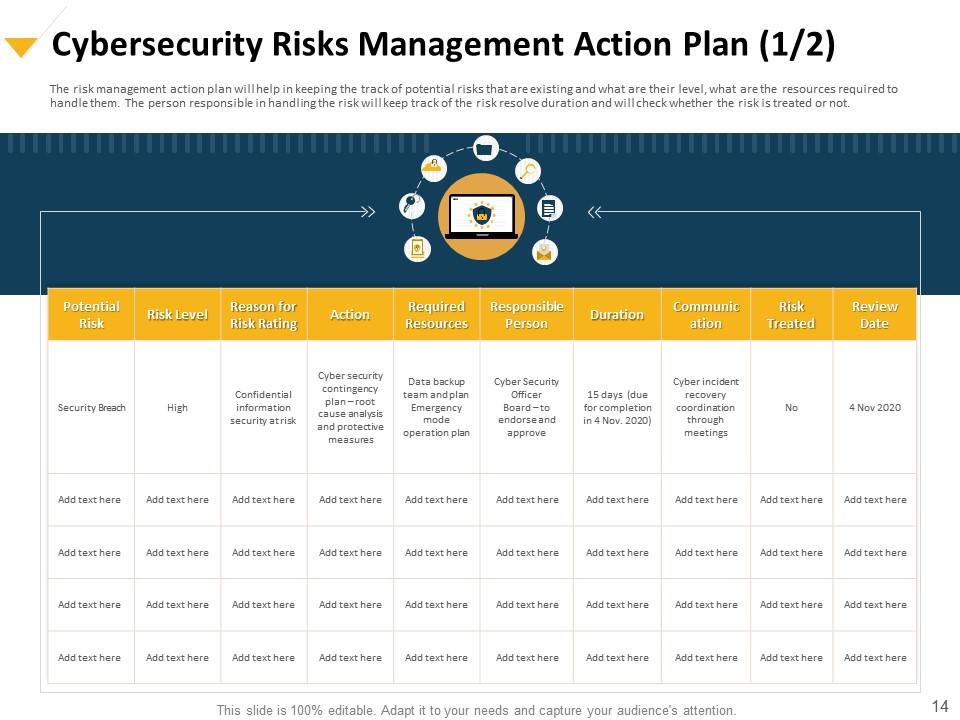
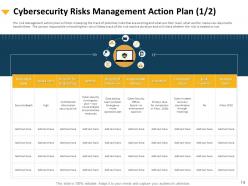
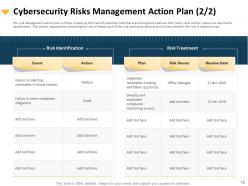
Slide 14: This slide displays Cybersecurity Risk Management Action Plan.
Slide 15: This slide shows Cybersecurity Management Action Plan.
Slide 16: This slide shows Incident Reporting by Different Cyber Departments.
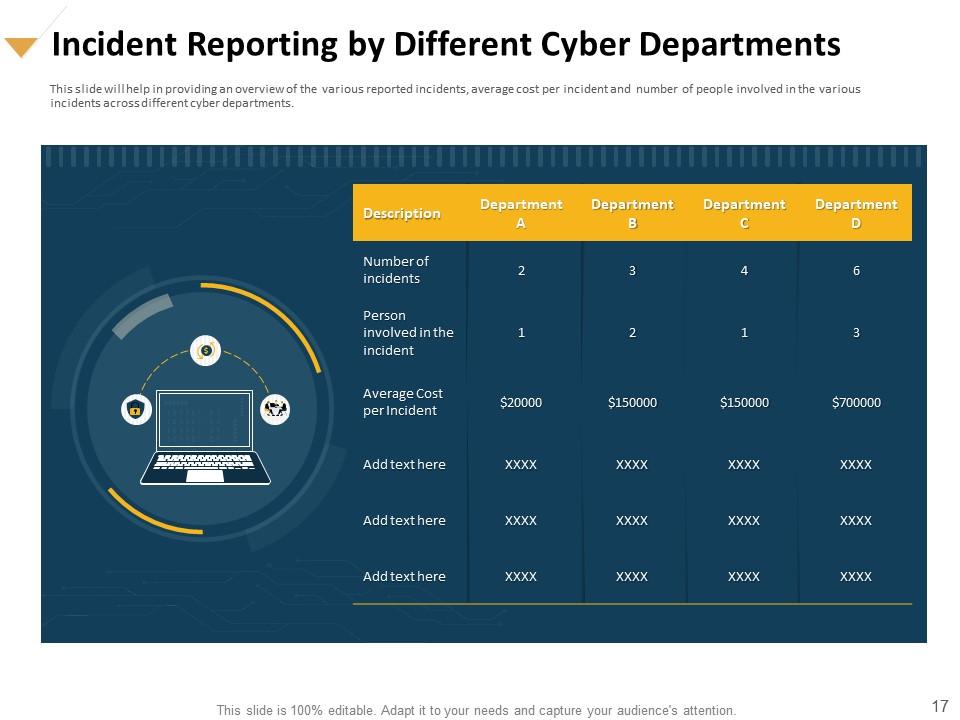
Slide 17: This slide will help in providing an overview of the various reported incidents, average cost per incident and number of people involved in the various incidents across different cyber departments.
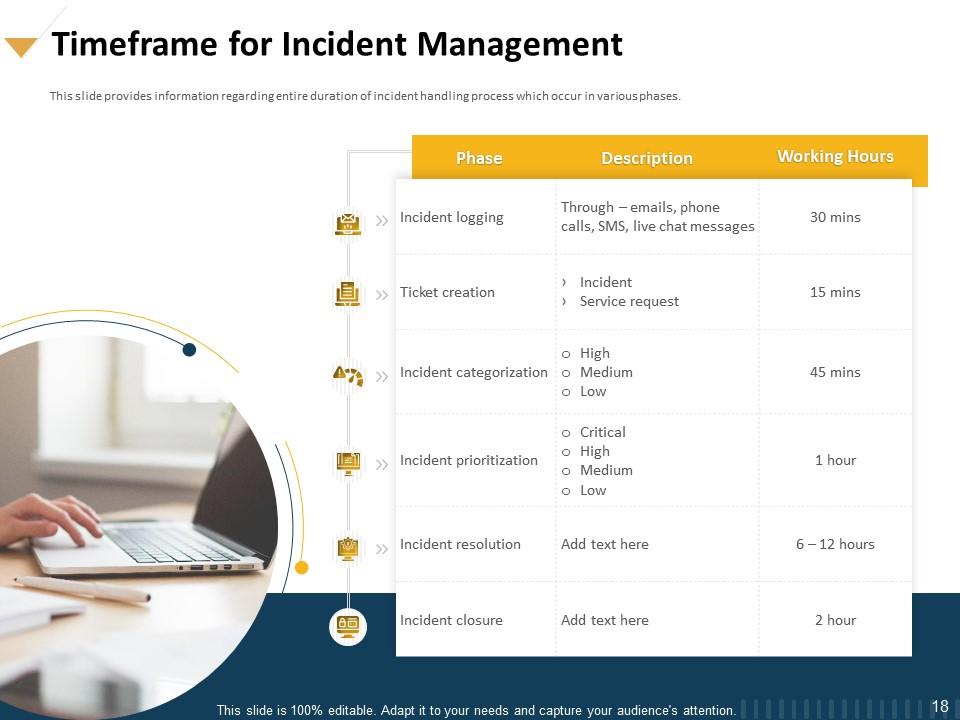
Slide 18: This slide provides information regarding entire duration of incident handling process which occur in various phases.
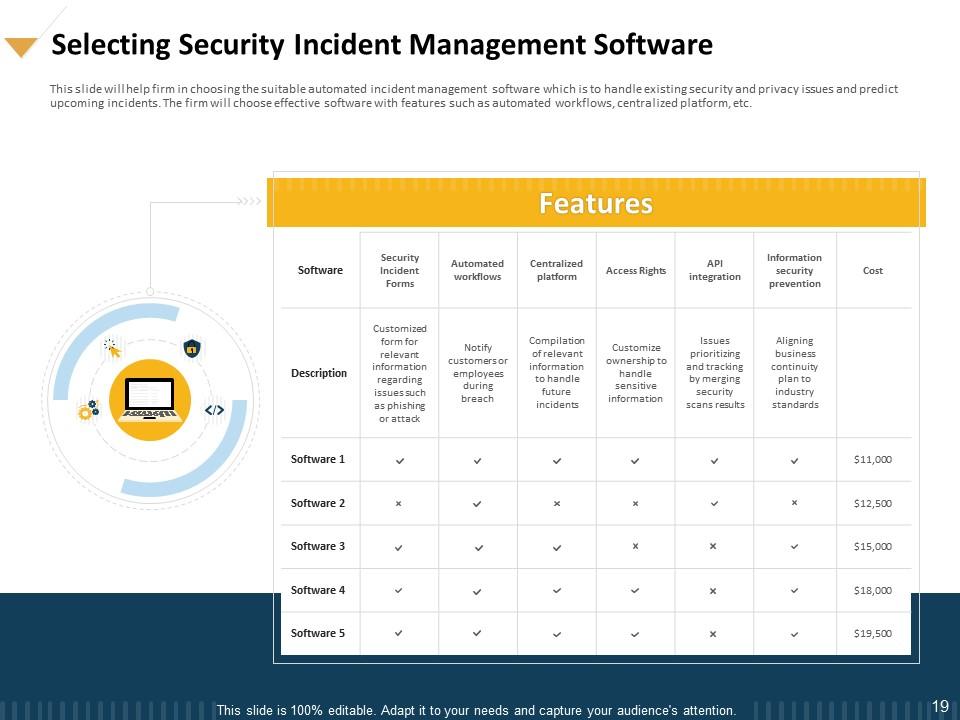
Slide 19: This slide will help firm in choosing the suitable automated incident management software which is to handle existing security and privacy issues and predict upcoming incidents. The firm will choose effective software with features such as automated workflows, centralized platform, etc.
Slide 20: This slide shows Table of Contents.
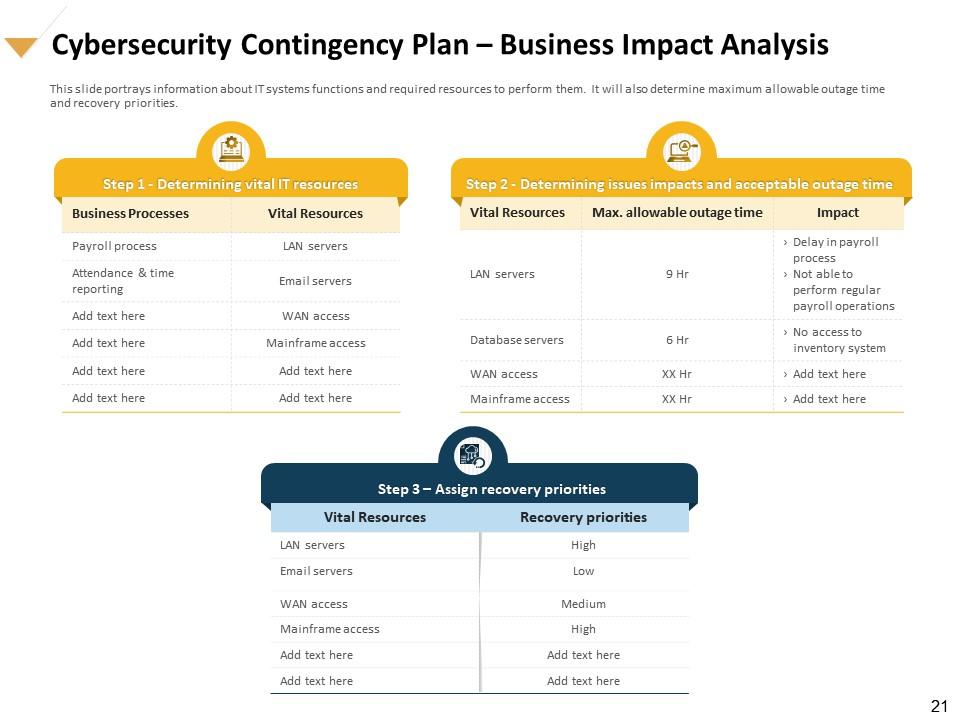
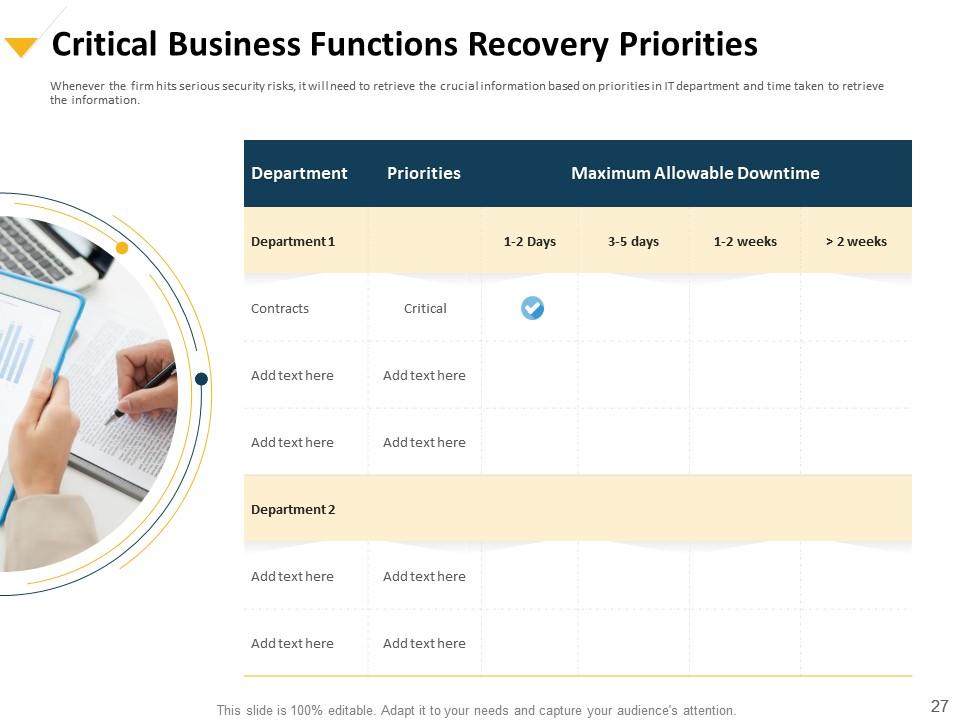
Slide 21: This slide portrays information about IT systems functions and required resources to perform them. It will also determine maximum allowable outage time and recovery priorities.
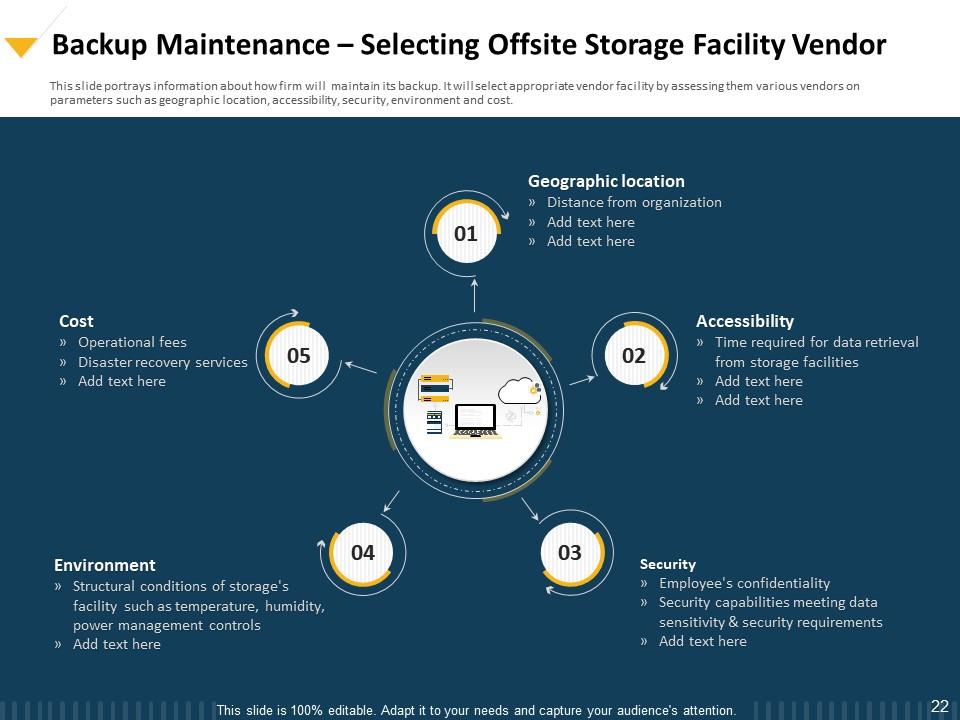
Slide 22: This slide highlights information about how firm will maintain its backup. It will select appropriate vendor facility by assessing them various vendors on parameters such as geographic location, accessibility, security, environment and cost.
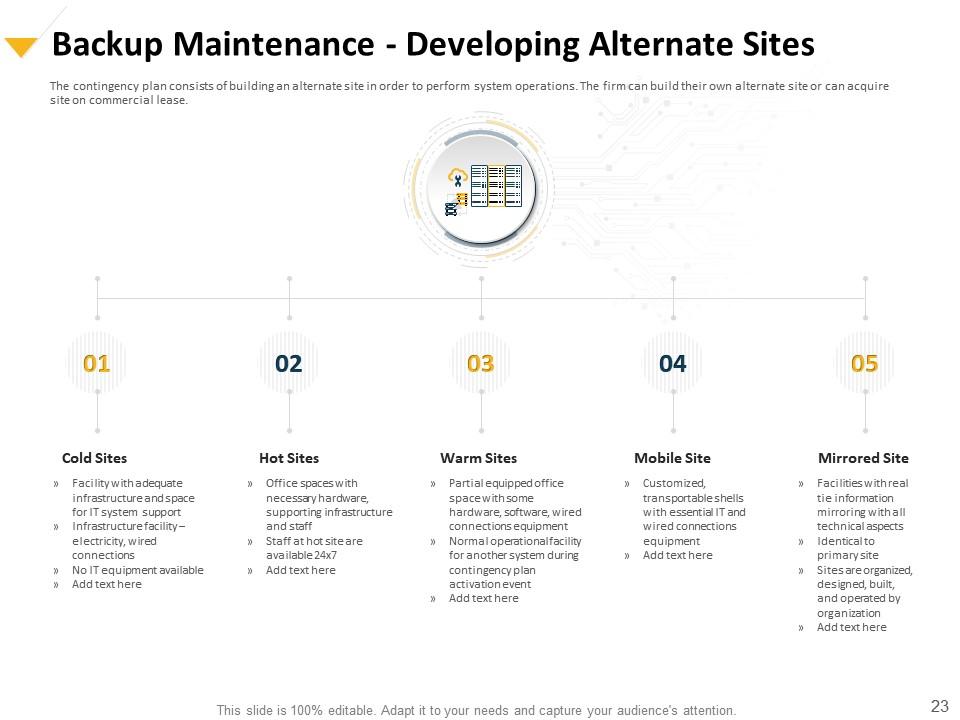
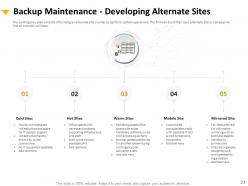
Slide 23: This slide shows Backup Maintenance - Developing Alternate Sites
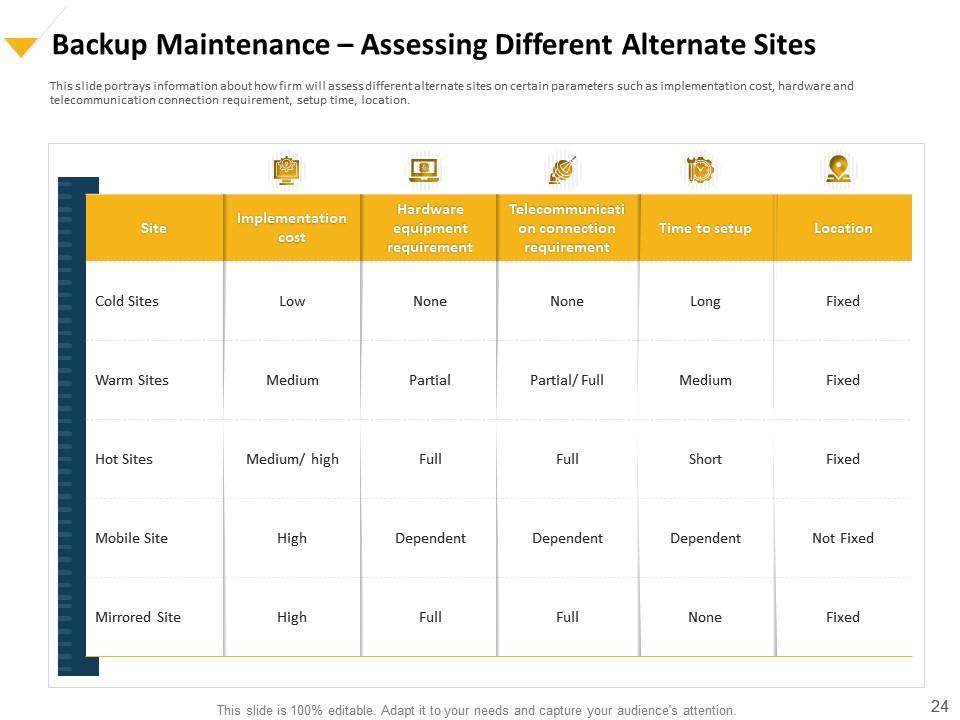
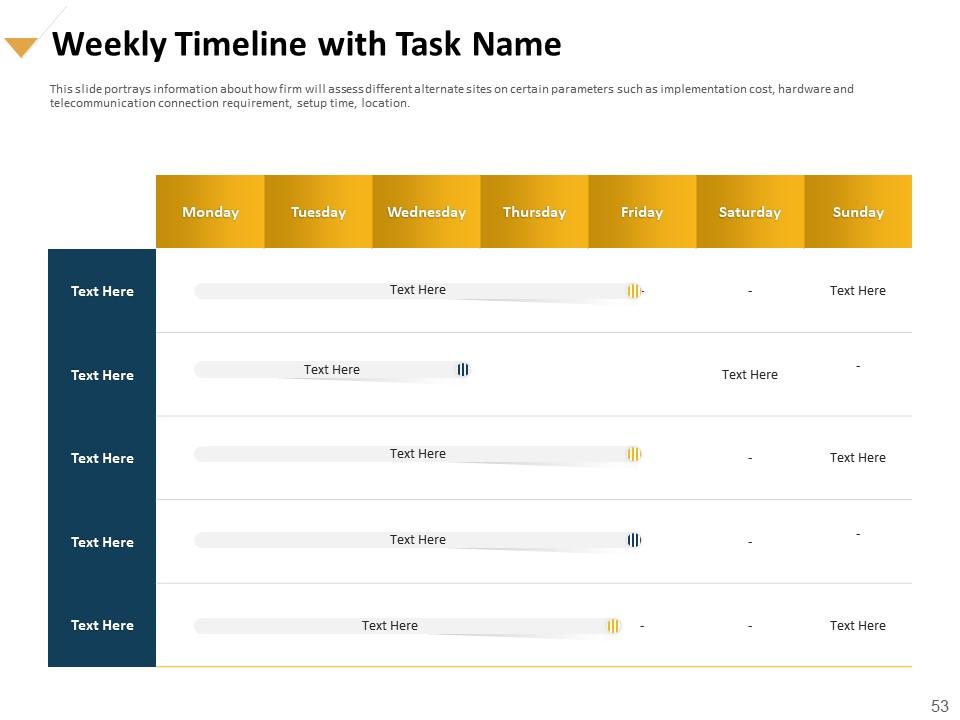
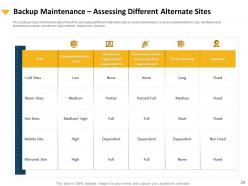
Slide 24: This slide portrays information about how firm will assess different alternate sites on certain parameters such as implementation cost, hardware and telecommunication connection requirement, setup time, location.
Slide 25: This slide depicts Backup Maintenance – Recovery Budget Planning.
Slide 26: This slide portrays information contingency considerations and solutions. The considerations consists of technical requirements that assist contingency solution and contingency solution are used to implement contingency strategy.
Slide 27: This slide presents Agenda for Cybersecurity Incident Management.
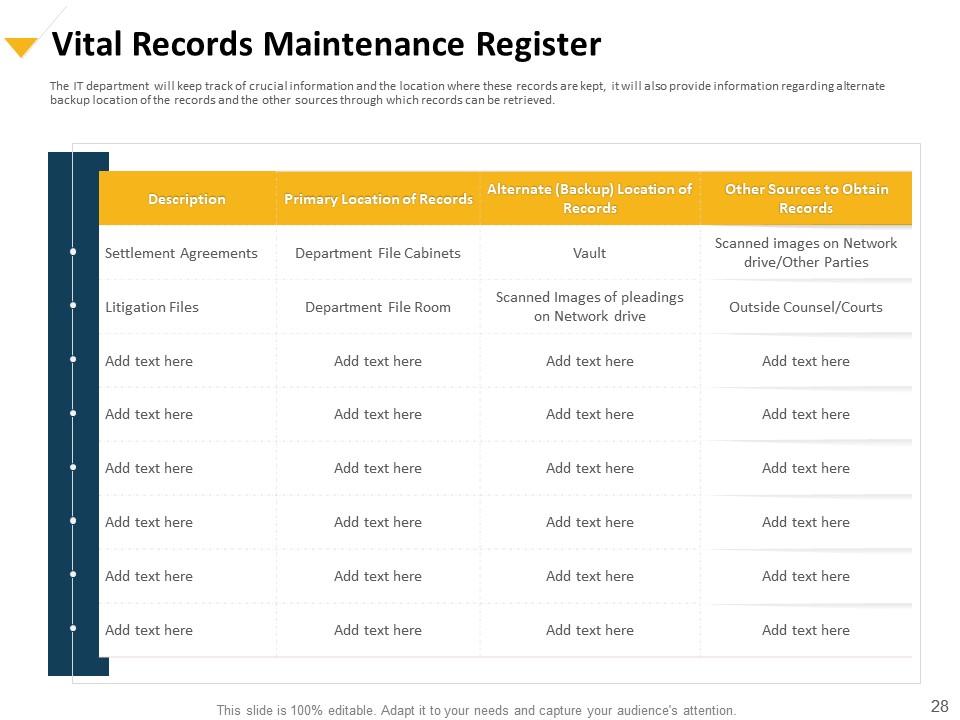
Slide 28: This slide shows Vital Records Maintenance Register
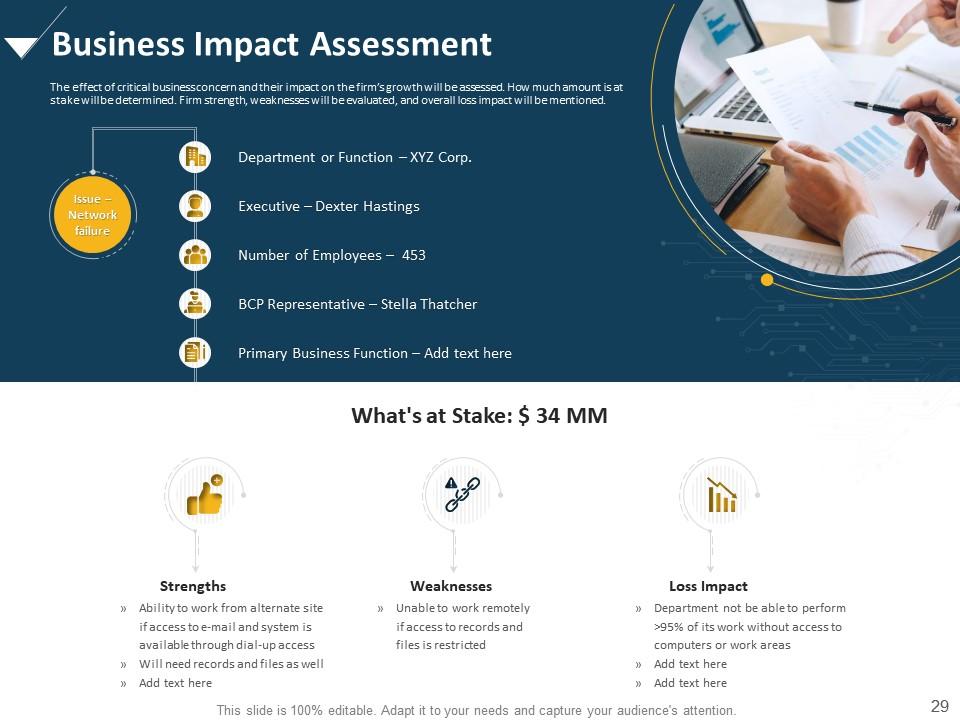
Slide 29: This slide shows Business Impact Assessment
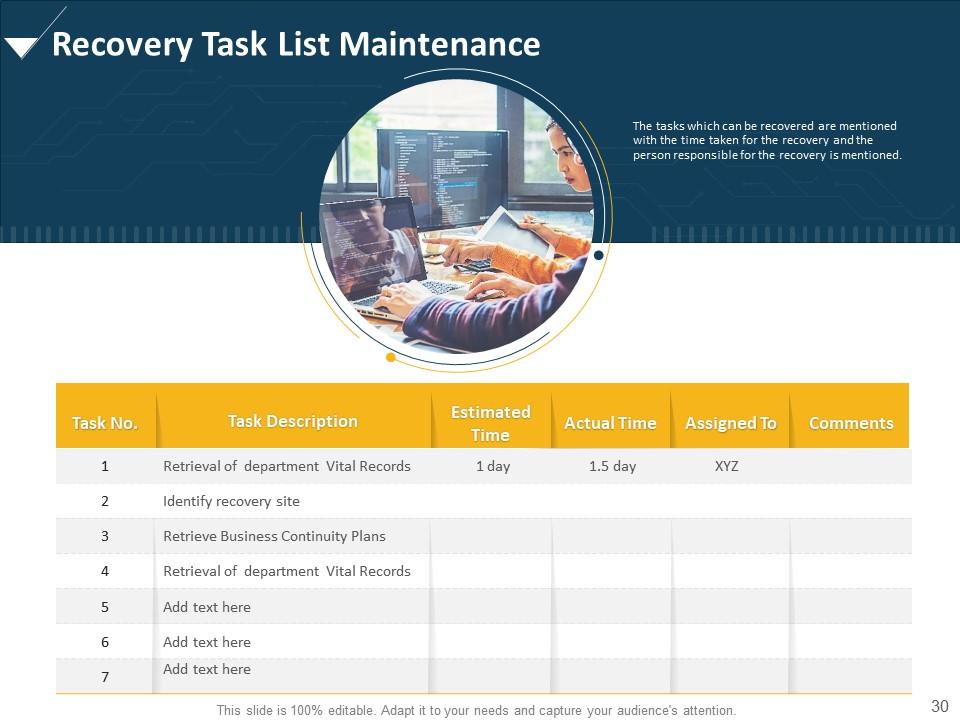
Slide 30: This slide shows Recovery Task List Maintenance. The tasks which can be recovered are mentioned with the time taken for the recovery and the person responsible for the recovery is mentioned.
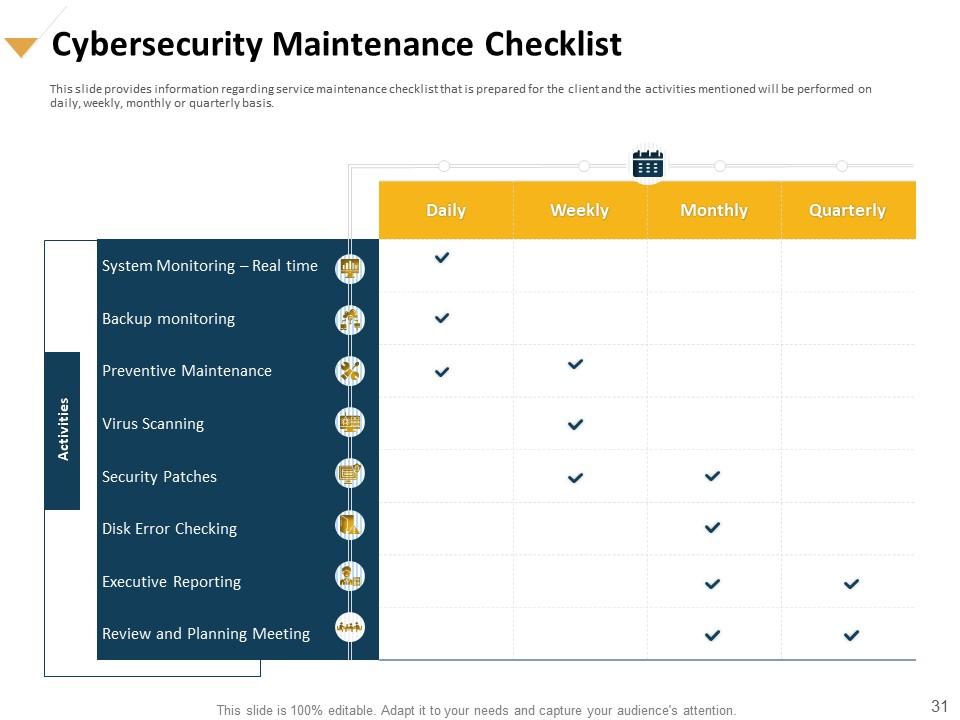
Slide 31: This slide provides information regarding service maintenance checklist that is prepared for the client and the activities mentioned will be performed on daily, weekly, monthly or quarterly basis.
Slide 32: This slide provides information regarding Determining Roles and Responsibilities for Risk Handling
Slide 33: This slide provides information regarding the roles and responsibilities of management in handling cyber security risks. Key people involved in risk handling are chief risk officer, chief information security officer, senior management and executives and line managers.
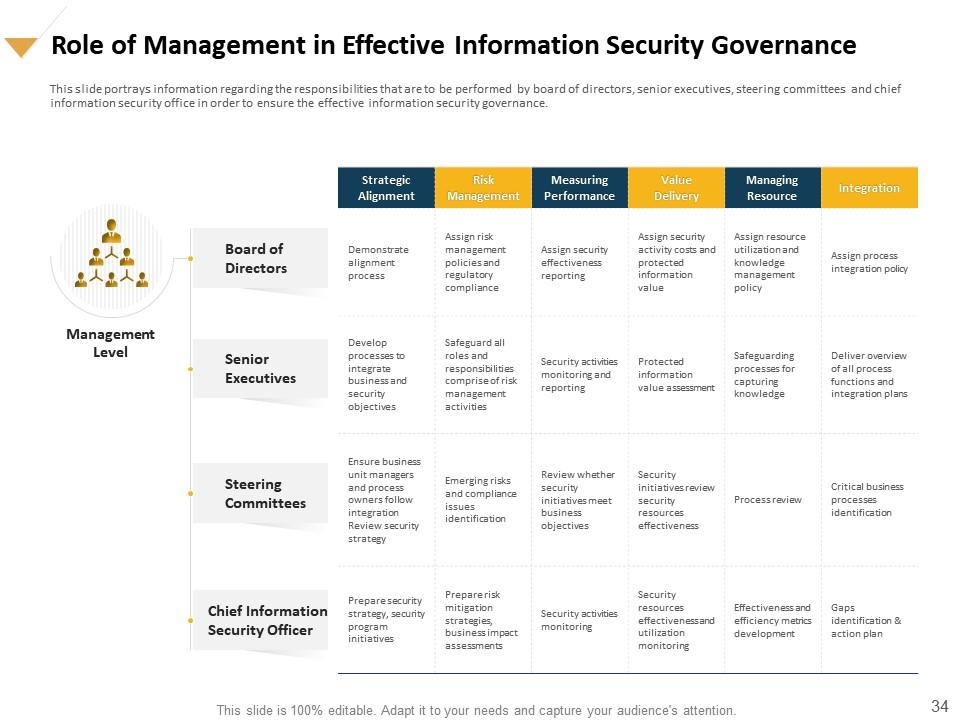
Slide 34: This slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief information security office in order to ensure the effective information security governance.
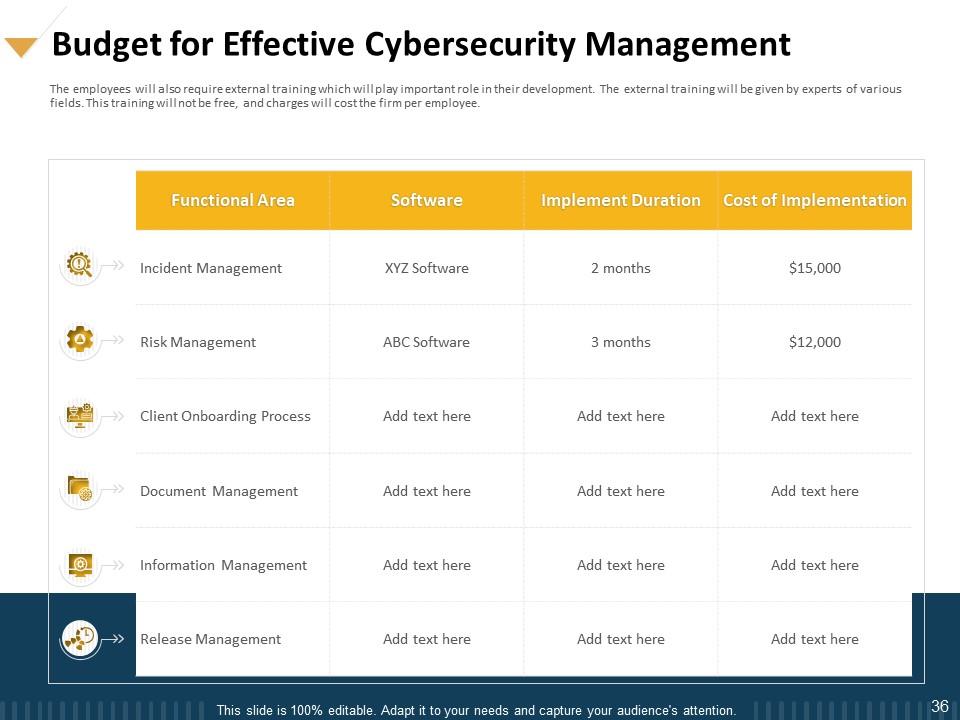
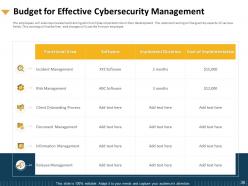
Slide 35: This slide shows Budget for Effective Cybersecurity Management
Slide 36: This slide presents Budget for Effective Cybersecurity Management
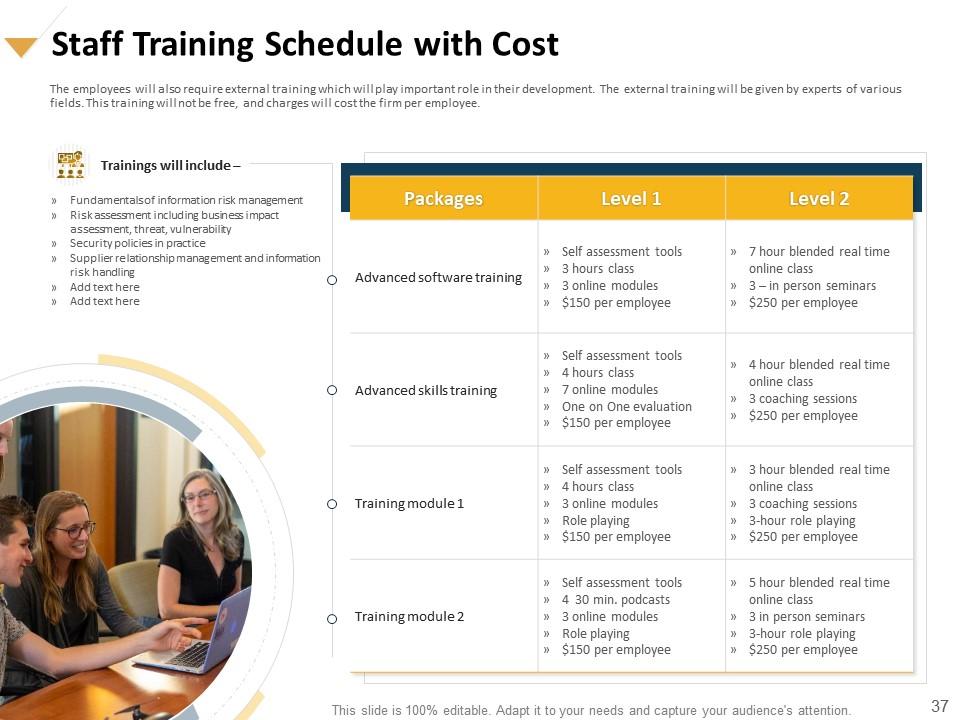
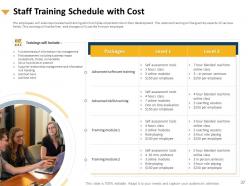
Slide 37: This slide depicts Staff Training Schedule with Cost.
Slide 38: This slide shows Table of Content.
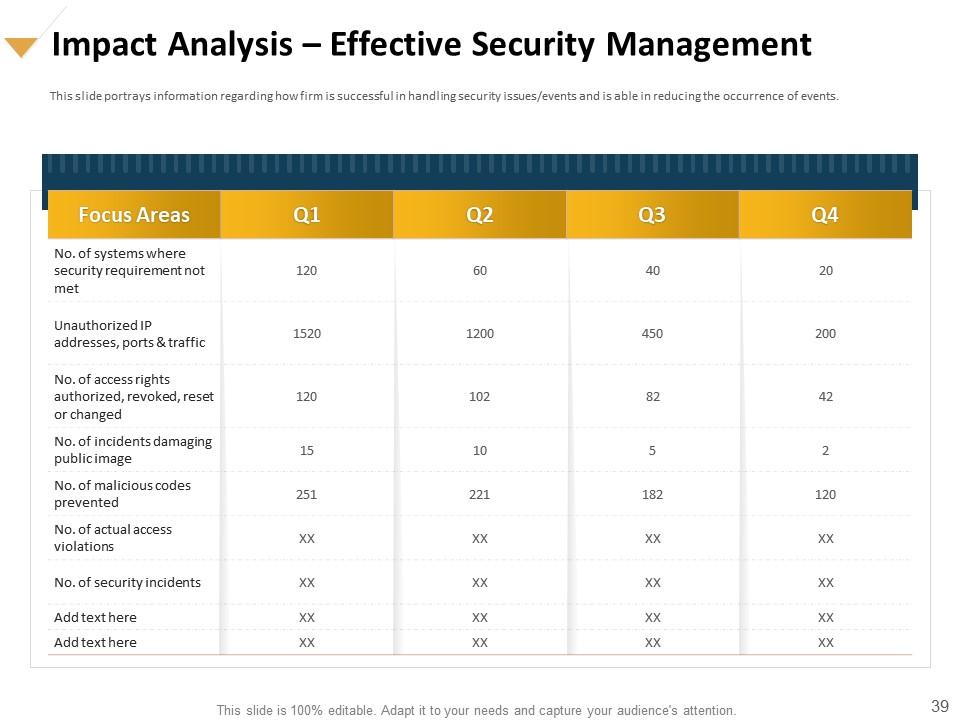
Slide 39: This slide portrays information regarding how firm is successful in handling security issues/events and is able in reducing the occurrence of events.
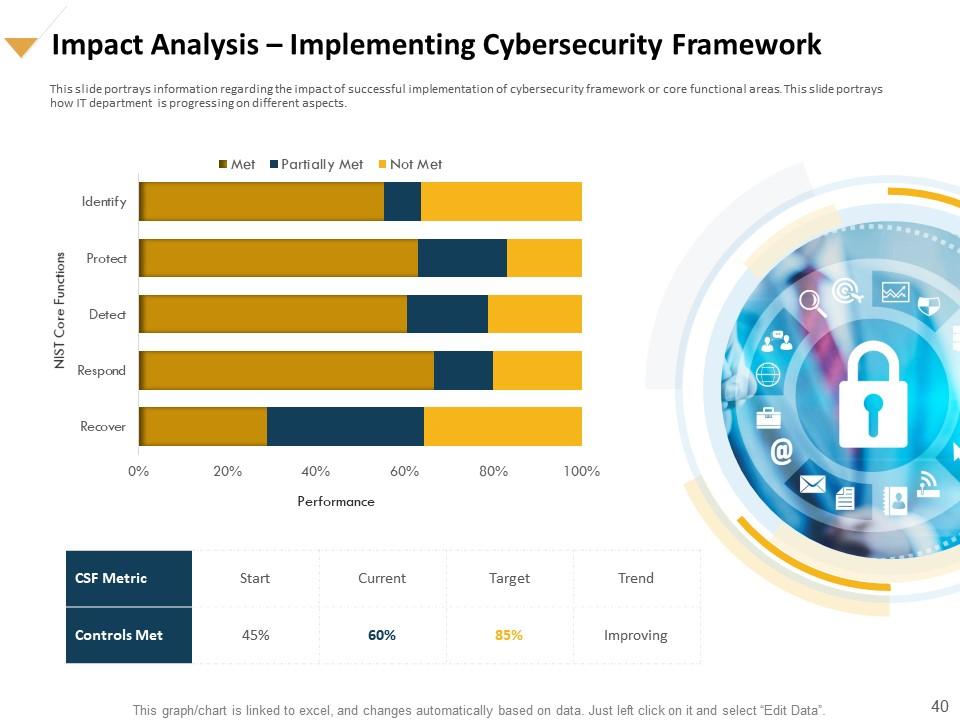
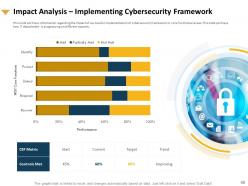
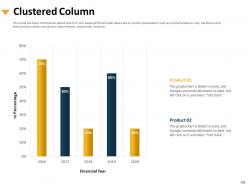
Slide 40: This slide depicts information regarding the impact of successful implementation of cybersecurity framework or core functional areas. This slide portrays how IT department is progressing on different aspects.
Slide 41: This slide displays Table of Contents
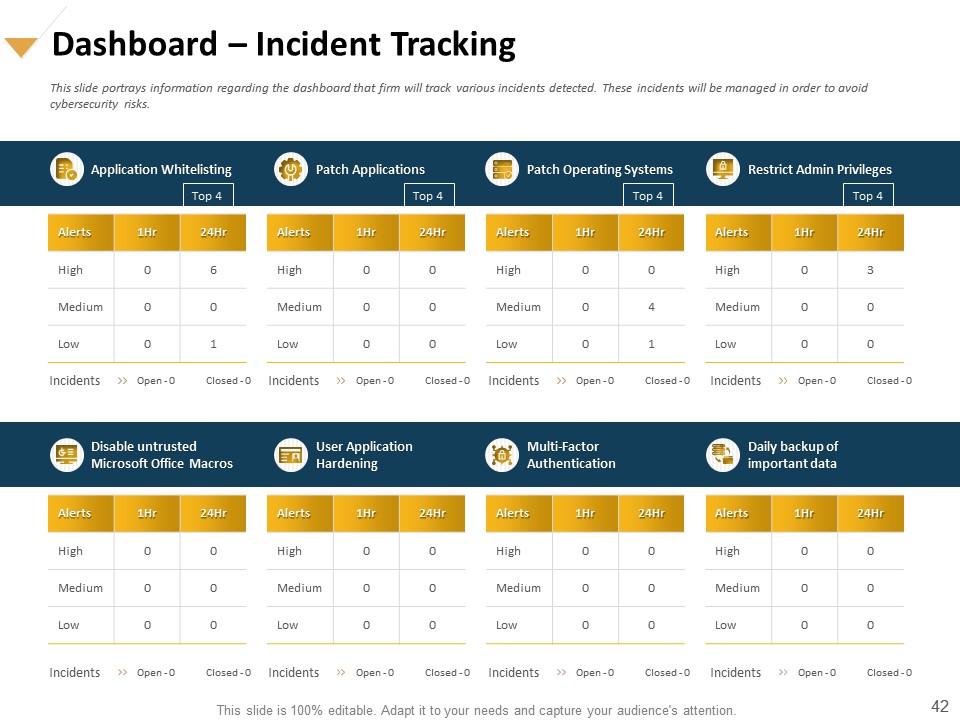
Slide 42: This slide portrays information regarding the dashboard that firm will track various incidents detected. These incidents will be managed in order to avoid cybersecurity risks.
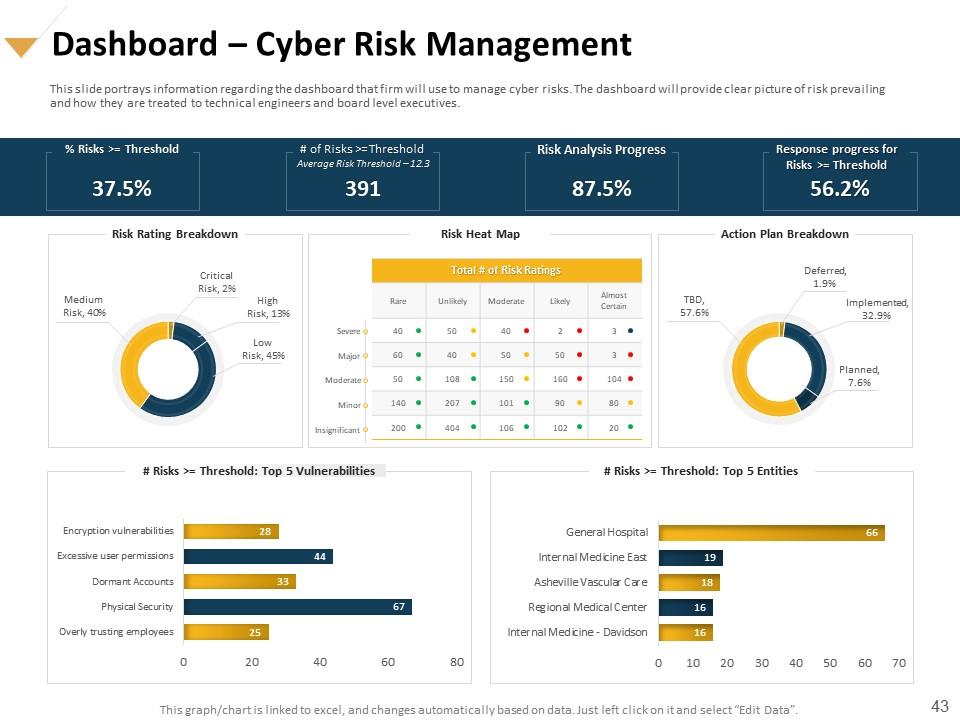
Slide 43: This slide portrays information regarding the dashboard that firm will use to manage cyber risks. The dashboard will provide clear picture of risk prevailing and how they are treated to technical engineers and board level executives.
Slide 44: This is Icons Slide for How to Handle Cybersecurity Risk.
Slide 45: This slide is titled as Additional Slides for moving forward.
Slide 46: This slide portrays information about how firm will assess different alternate sites on certain parameters such as implementation cost, hardware and telecommunication connection requirement, setup time, location.
Slide 47: This slide portrays information about how firm will assess different alternate sites on certain parameters such as implementation cost, hardware and telecommunication connection requirement, setup time, location.
Slide 48: This slide shows information about how firm will assess different alternate sites on certain parameters such as implementation cost, hardware and telecommunication connection requirement, setup time, location.
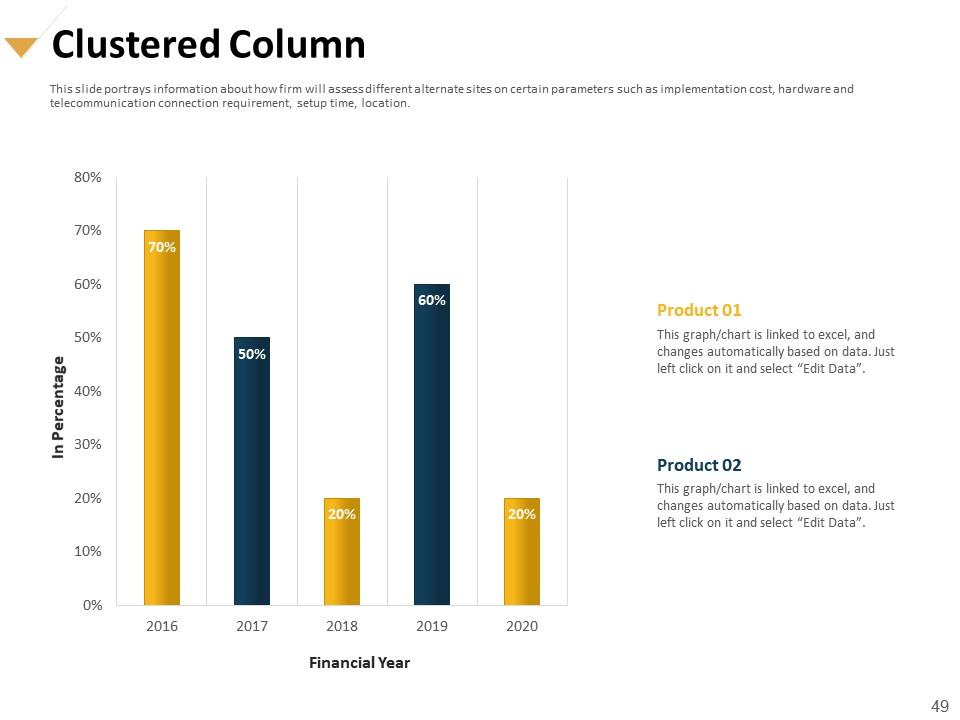
Slide 49: This slide portrays information about how firm will assess different alternate sites on certain parameters such as implementation cost, hardware and telecommunication connection requirement, setup time, location.
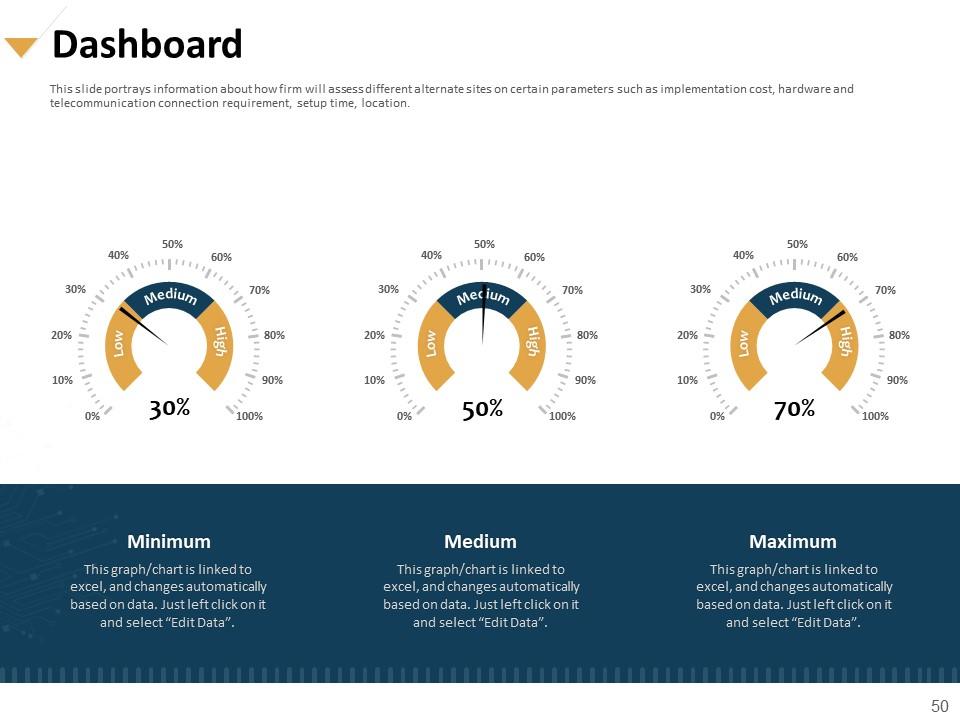
Slide 50: This slide highlights information about how firm will assess different alternate sites on certain parameters such as implementation cost, hardware and telecommunication connection requirement, setup time, location.
Slide 51: This slide portrays information regarding the amount that is spend by firm in settling cases of cybersecurity failures which not only consider as financial losses but hampered firm’s public image.
Slide 52: This slide portrays information regarding the amount that is spend by firm in settling cases of cybersecurity failures which not only consider as financial losses but hampered firm’s public image.
Slide 53: This slide shows information about how firm will assess different alternate sites on certain parameters such as implementation cost, hardware and telecommunication connection requirement, setup time, location.
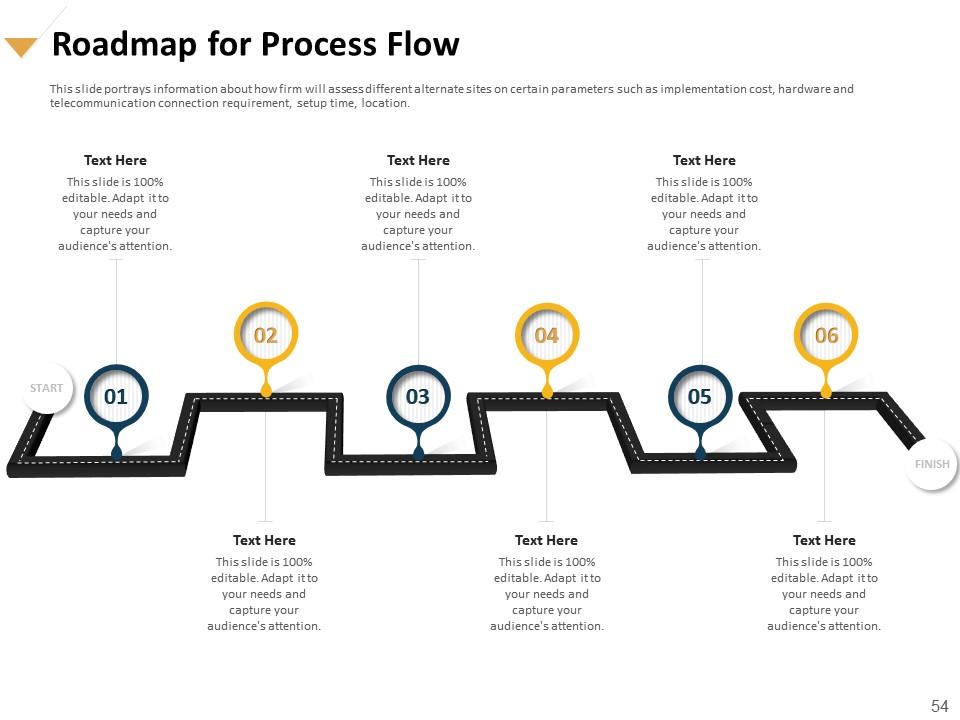
Slide 54: This slide presents Roadmap for Process Flow
Slide 55: This is Thank You slide with Contact details.
How to handle cybersecurity risk powerpoint presentation slides with all 55 slides:
Use our How To Handle Cybersecurity Risk Powerpoint Presentation Slides to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
Professional and unique presentations.
-
Out of the box and creative design.
-
Enough space for editing and adding your own content.
-
Professional and unique presentations.
-
Understandable and informative presentation.