Cyber security risk management powerpoint presentation slides
Critical assets security requires planning and due importance in businesses today to keep the vital information confidential with integrity, availability and assurance. Here is an efficiently designed template on Cyber Security Risk Management at Workplace that will reduce the risk of crisis in your company and the effects of that crisis occurring outside. This template aims to identify high safety risks, enable cyber threat security to protect the company from fears, and set up safety plans to reduce such risks. One can display their current security plans critical success factors and significant reasons for poor security to know the companys challenges. Security tasks require organizations to show the elements that affect the operations and overcome them by setting an advanced safety plan for IT. Businesses evaluate information processing assets for analyzing the risk and clearly define the threat management system through adopting high-tech assessment controls for themselves. Book a free demo with our research or design team and customize this 100 percent editable template based on your needs. Get access now.
Critical assets security requires planning and due importance in businesses today to keep the vital information confidentia..
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
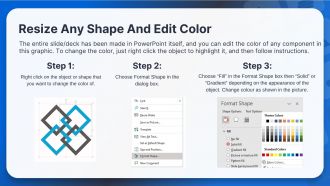
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Enthrall your audience with this Cyber Security Risk Management Powerpoint Presentation Slides. Increase your presentation threshold by deploying this well-crafted template. It acts as a great communication tool due to its well-researched content. It also contains stylized icons, graphics, visuals etc, which make it an immediate attention-grabber. Comprising sixty seven slides, this complete deck is all you need to get noticed. All the slides and their content can be altered to suit your unique business setting. Not only that, other components and graphics can also be modified to add personal touches to this prefabricated set.
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
Slide 1: This slide introduces Cyber Security Risk Management. State Your Company Name and begin.
Slide 2: This slide shows Agenda of Cyber Security Risk Management.
Slide 3: This slide presents Table of Content for the presentation.
Slide 4: This is another slide continuing Table of Content for the presentation.
Slide 5: This slide depicts title for 'Current scenraio assessment'.
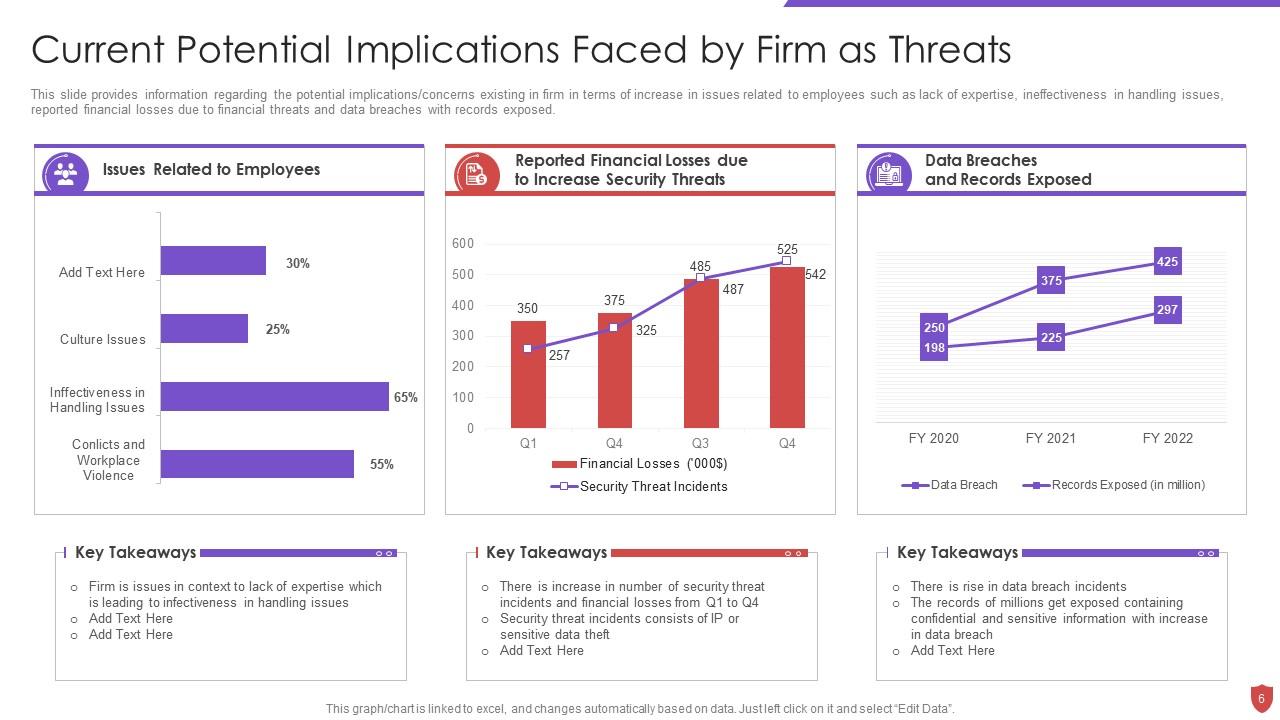
Slide 6: This slide provides information regarding the potential implications/concerns existing in firm.
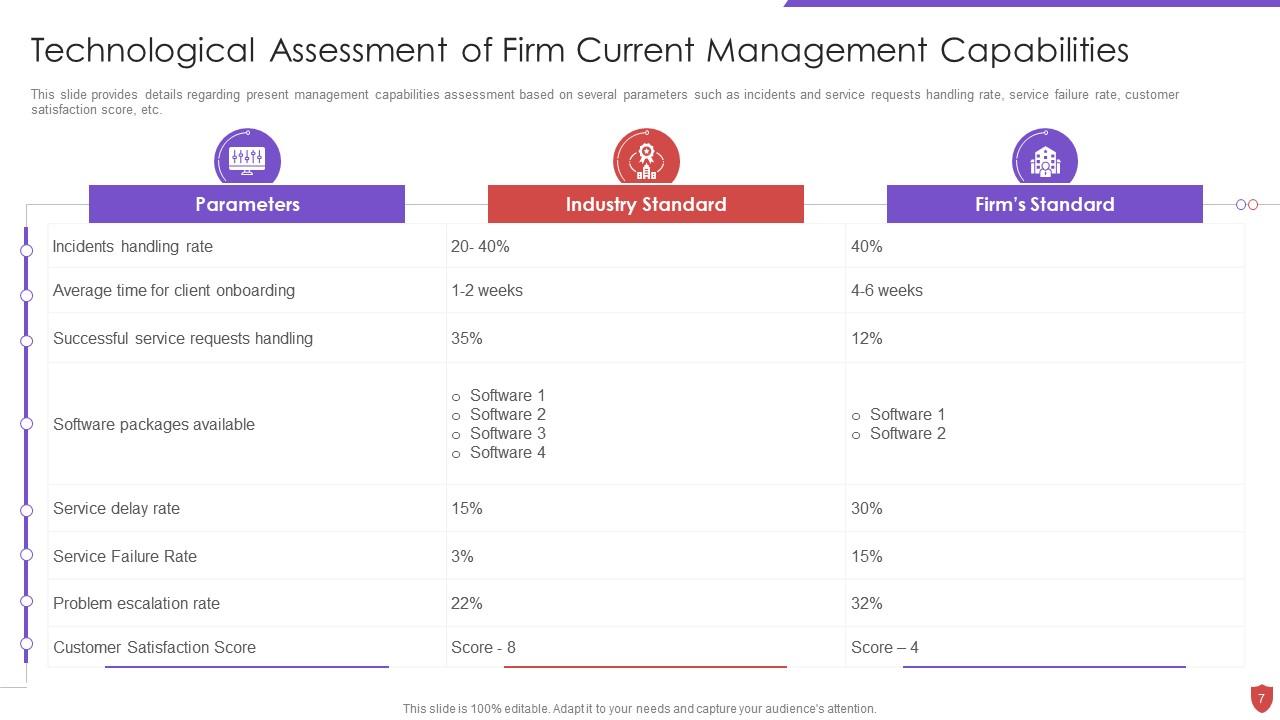
Slide 7: This slide provides details regarding present management capabilities assessment.
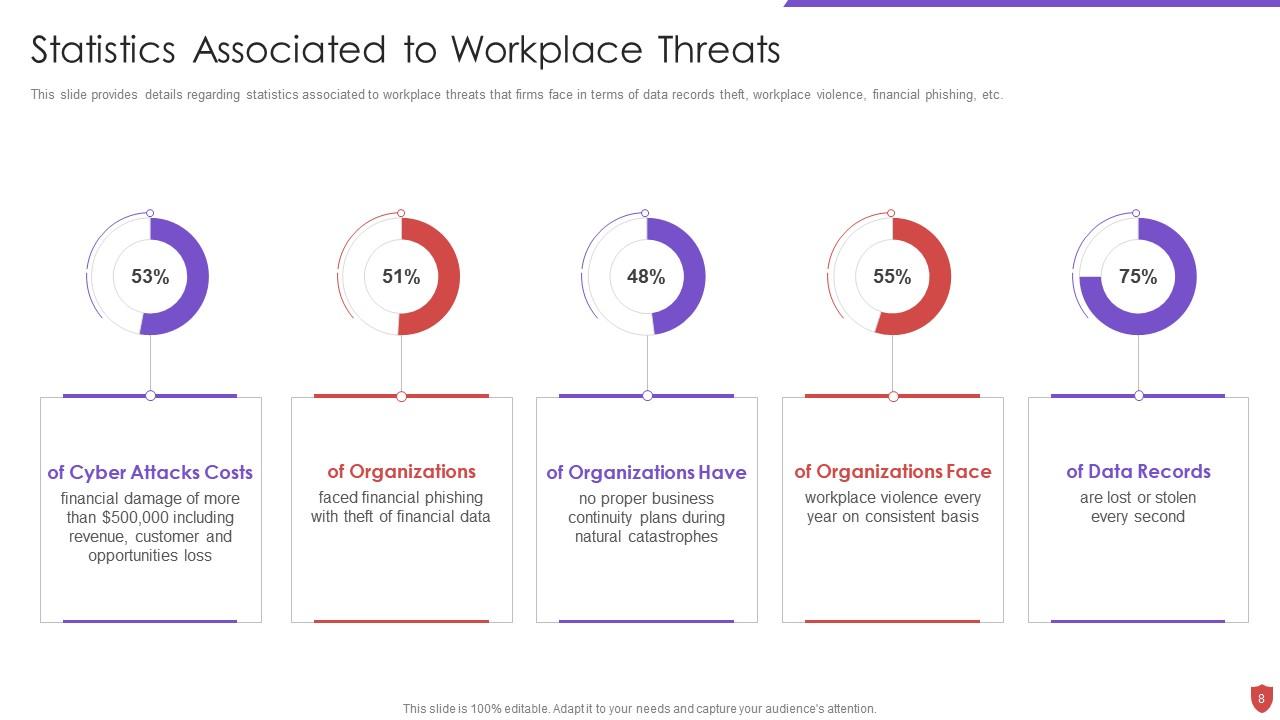
Slide 8: This slide provides details regarding statistics associated to workplace threats.
Slide 9: This slide displays title for 'Handling cyber threats to secure digital assets'.
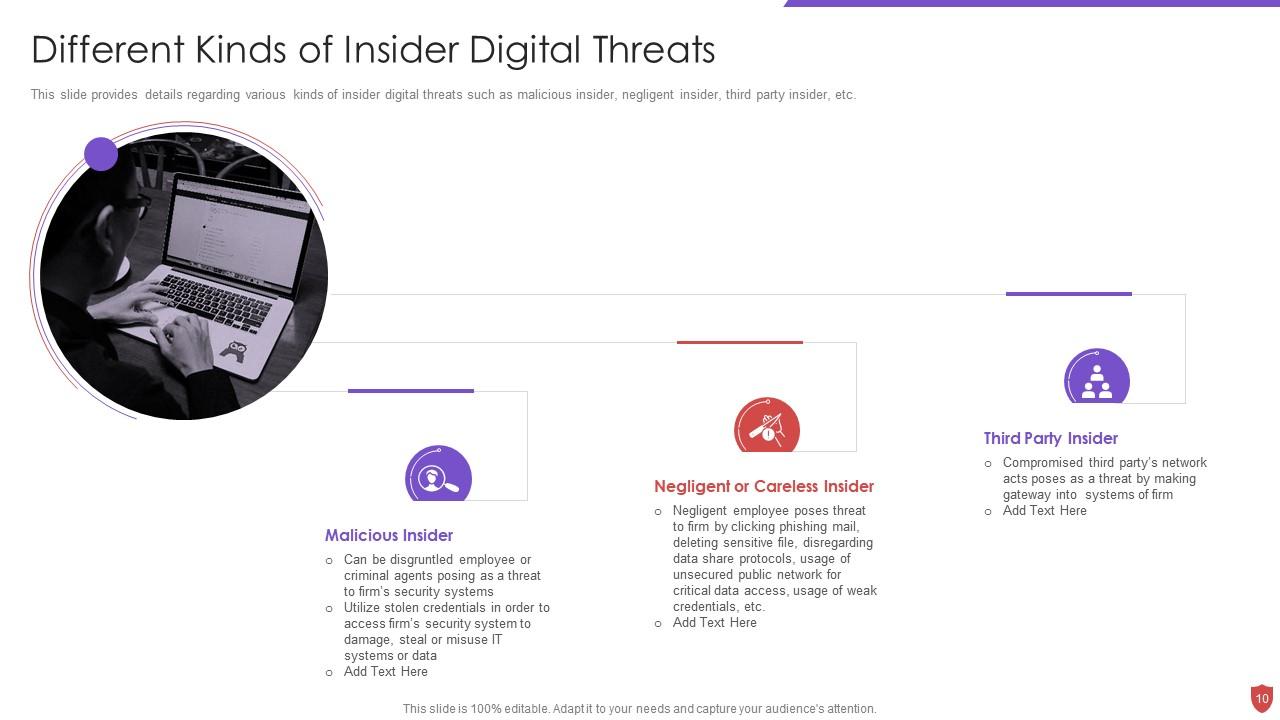
Slide 10: This slide provides details regarding various kinds of insider digital threats.
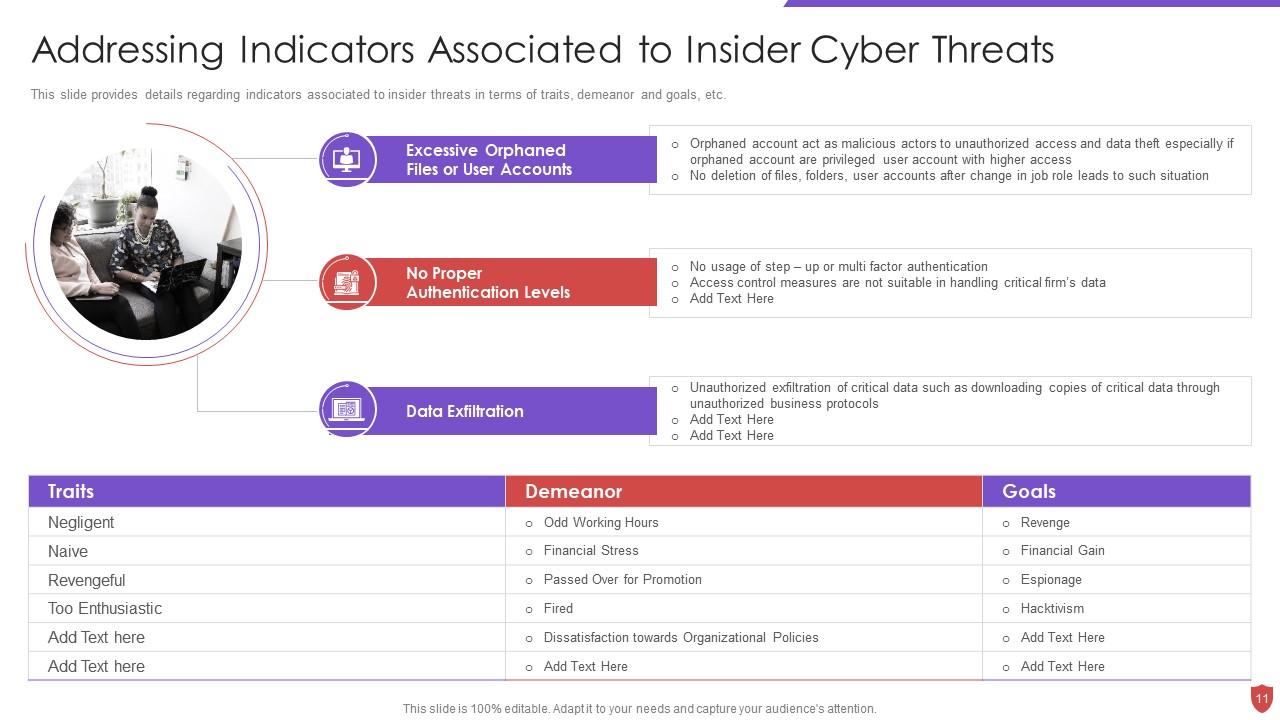
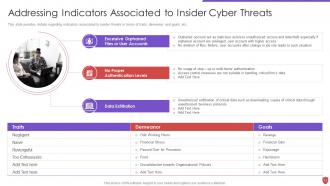
Slide 11: This slide provides details regarding indicators associated to insider threats.
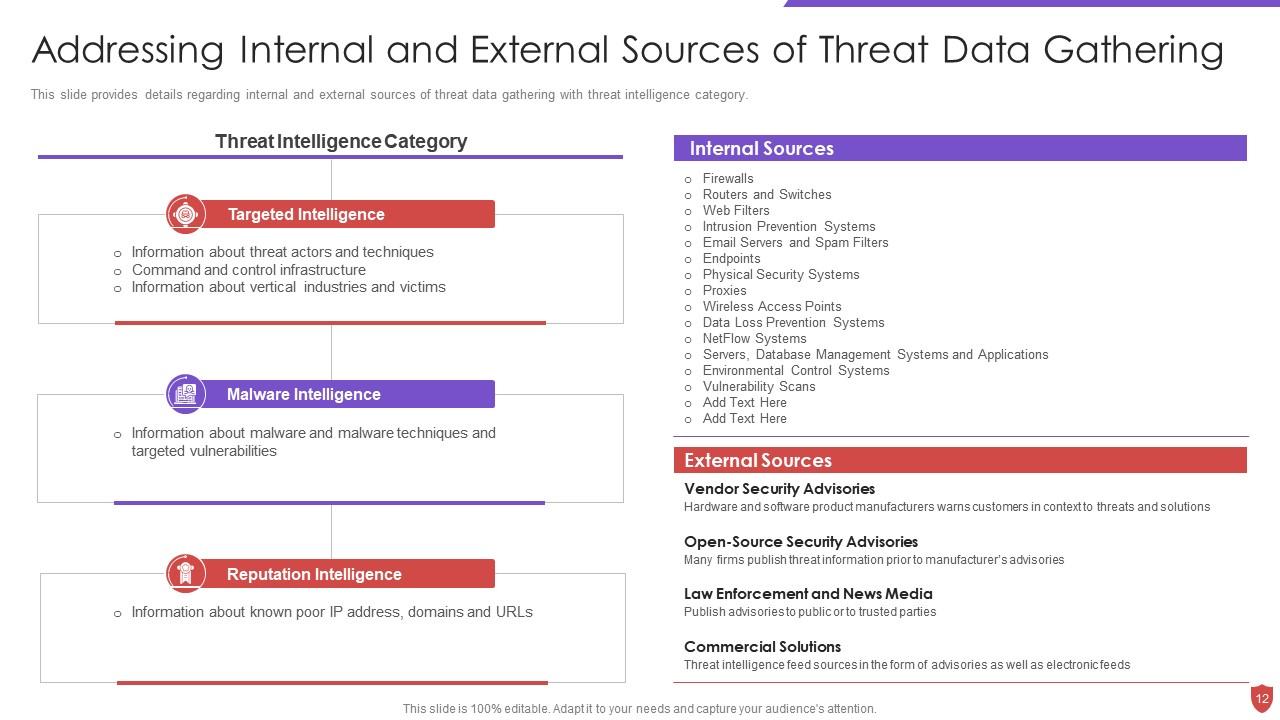
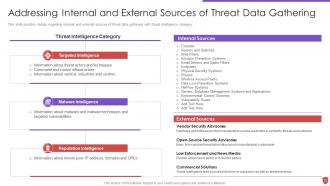
Slide 12: This slide provides details regarding internal and external sources of threat data.
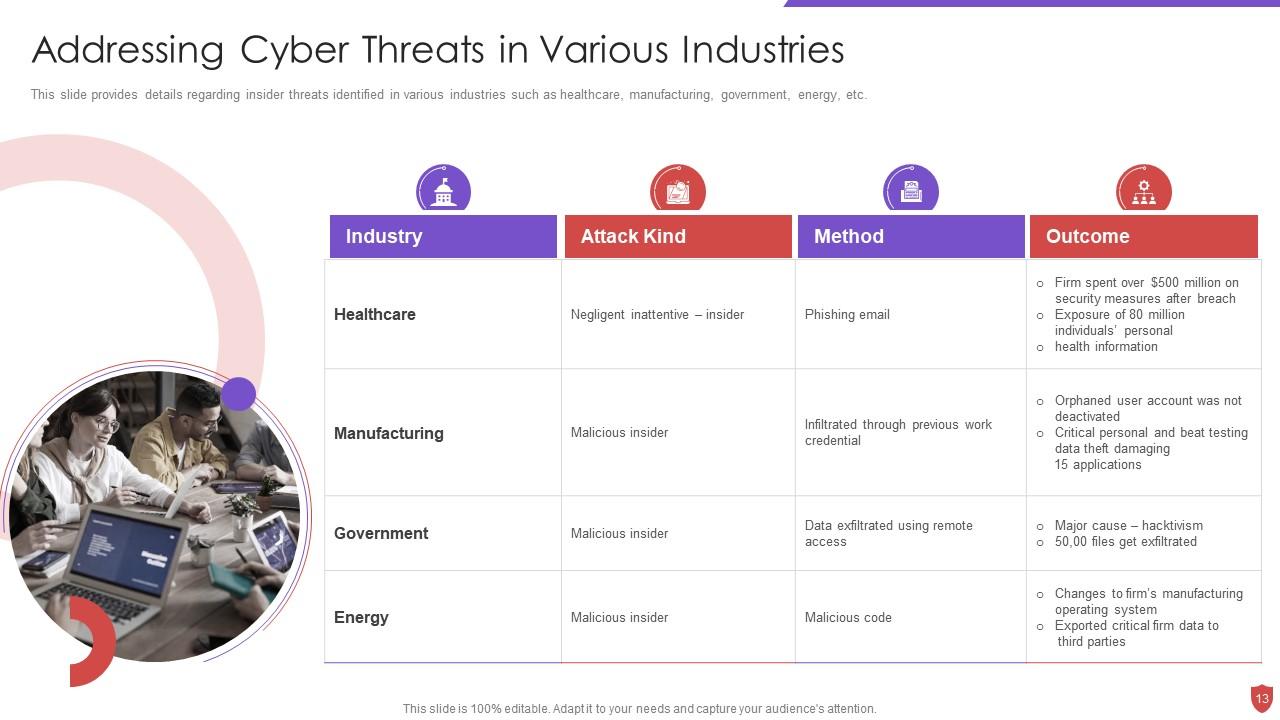
Slide 13: This slide provides details regarding insider threats identified in various industries.
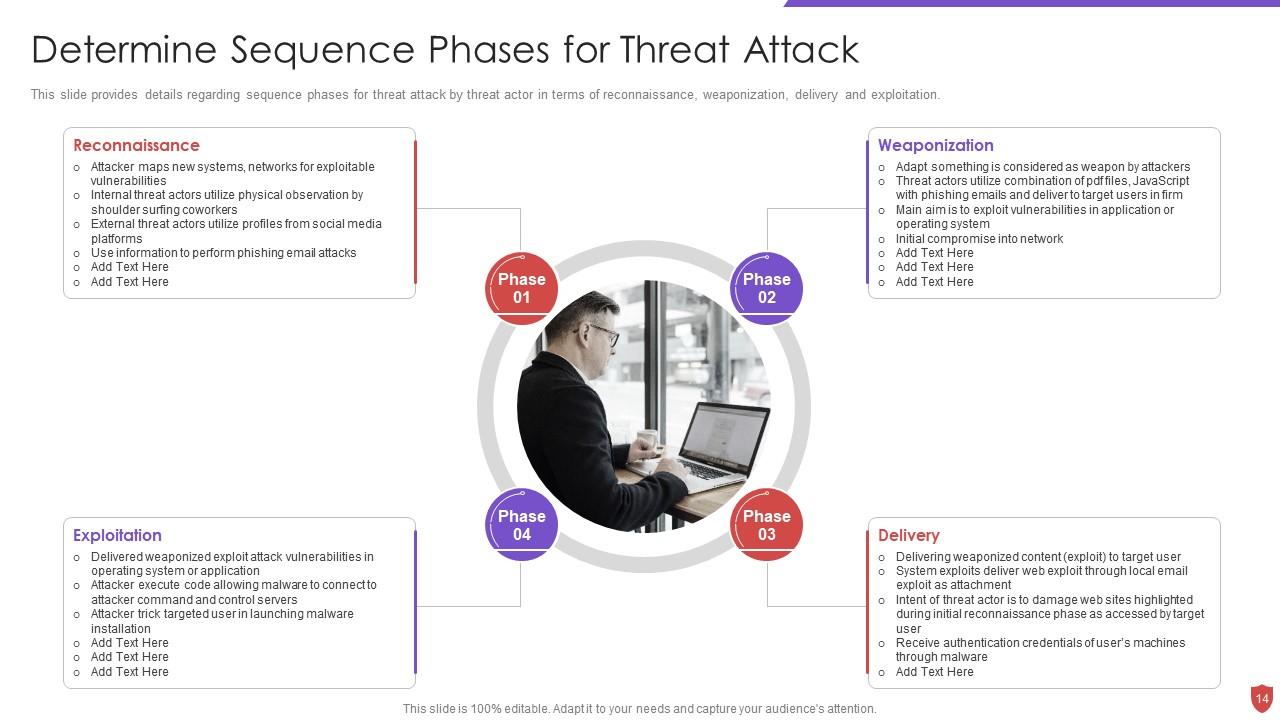
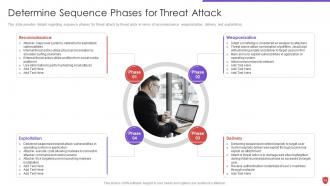
Slide 14: This slide provides details regarding sequence phases for threat attack by threat actor.
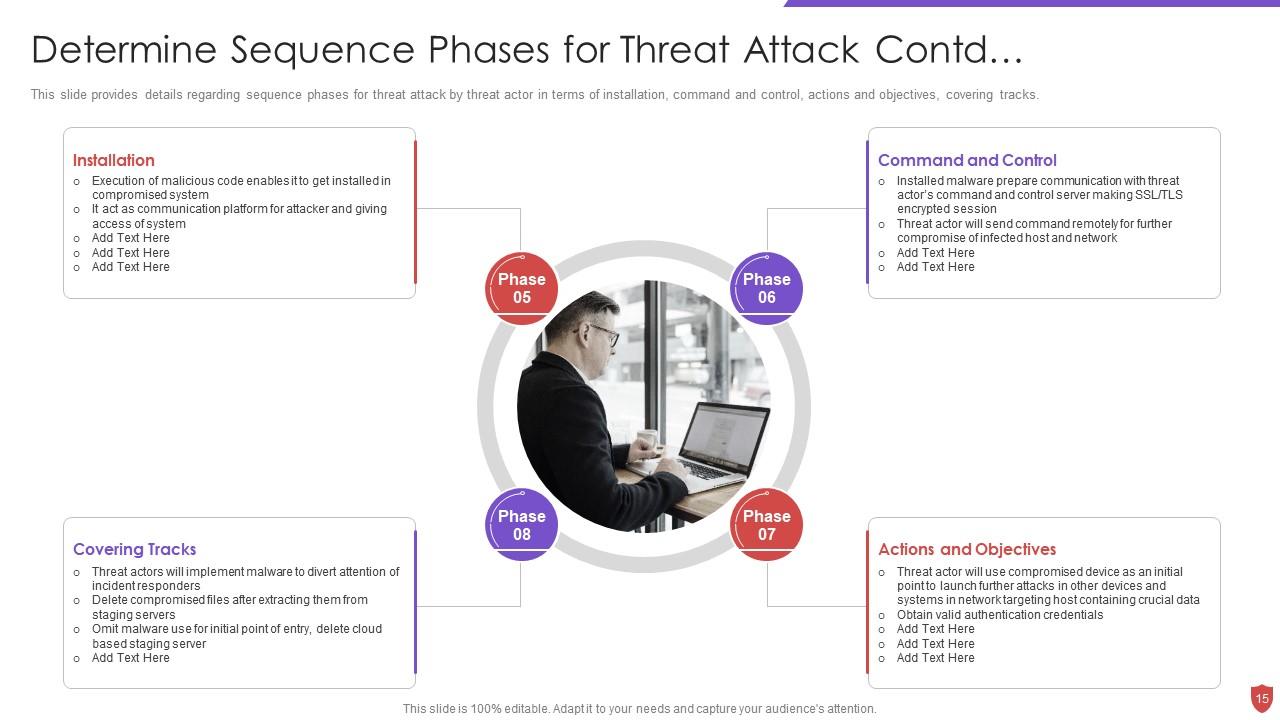
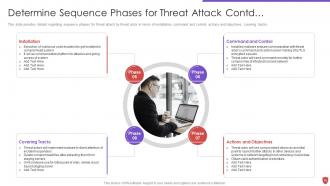
Slide 15: This slide presents continued content.
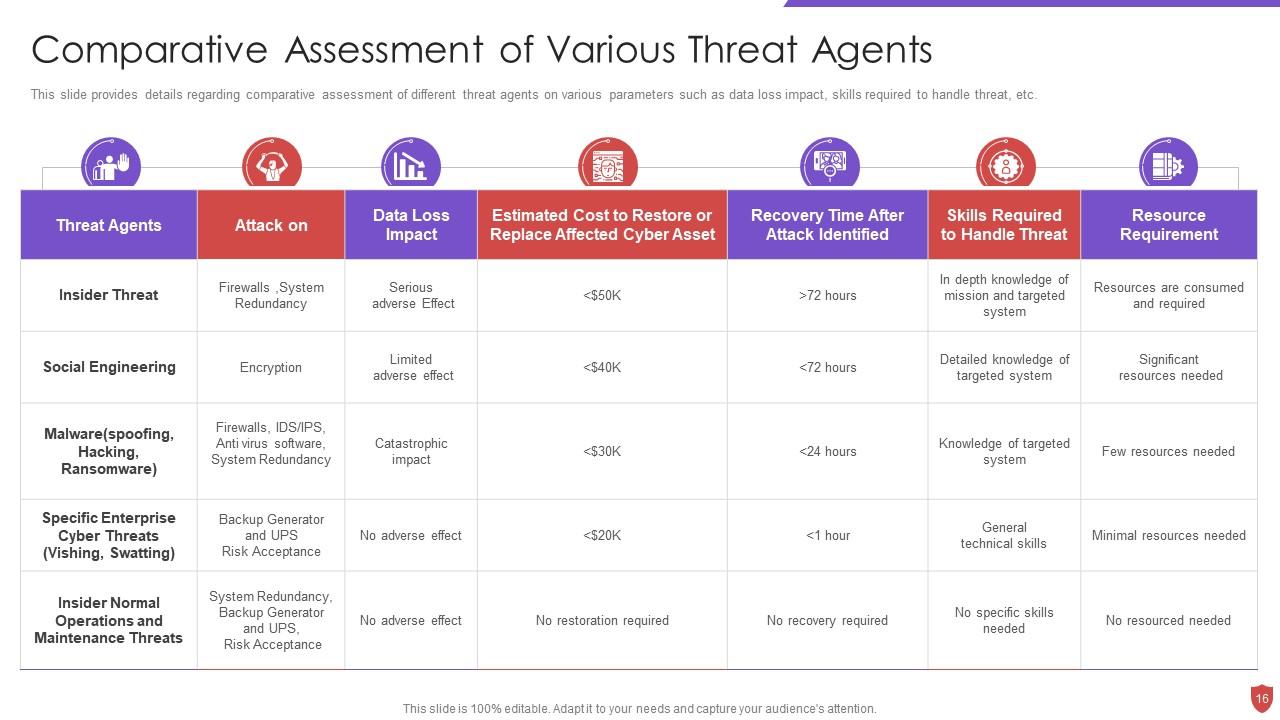
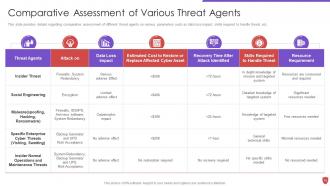
Slide 16: This slide provides details regarding comparative assessment of different threat agents on various parameters.
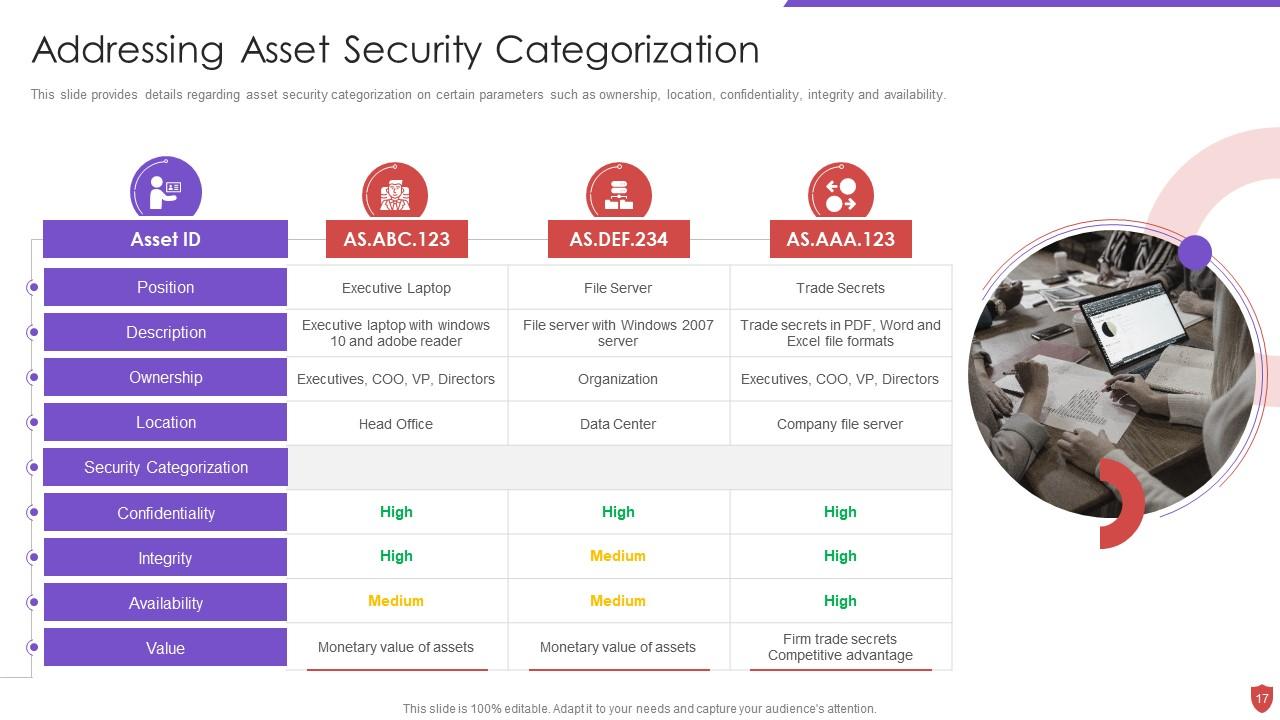
Slide 17: This slide provides details regarding asset security categorization on certain parameters.
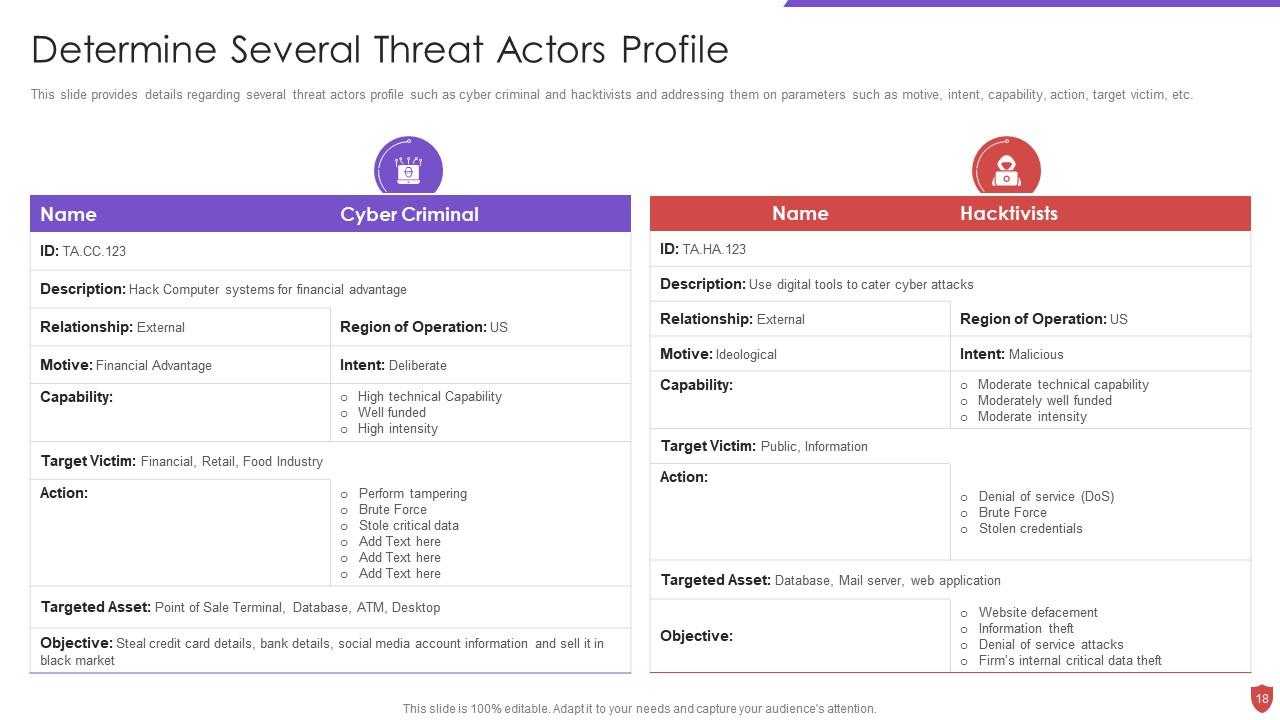
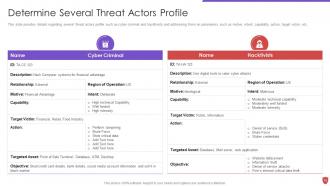
Slide 18: This slide provides details regarding several threat actors profile.
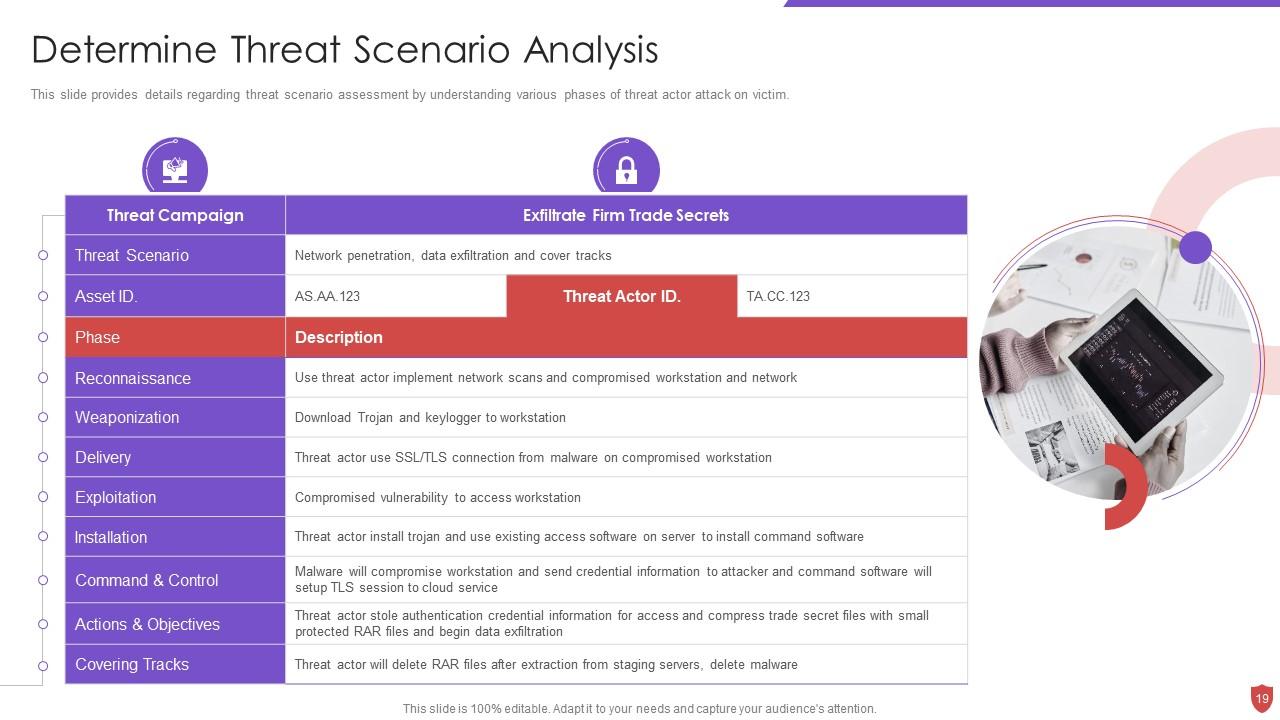
Slide 19: This slide provides details regarding threat scenario assessment by understanding various phases of threat actor attack on victim.
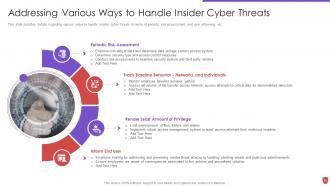
Slide 20: This slide provides details regarding various ways to handle insider cyber threats.
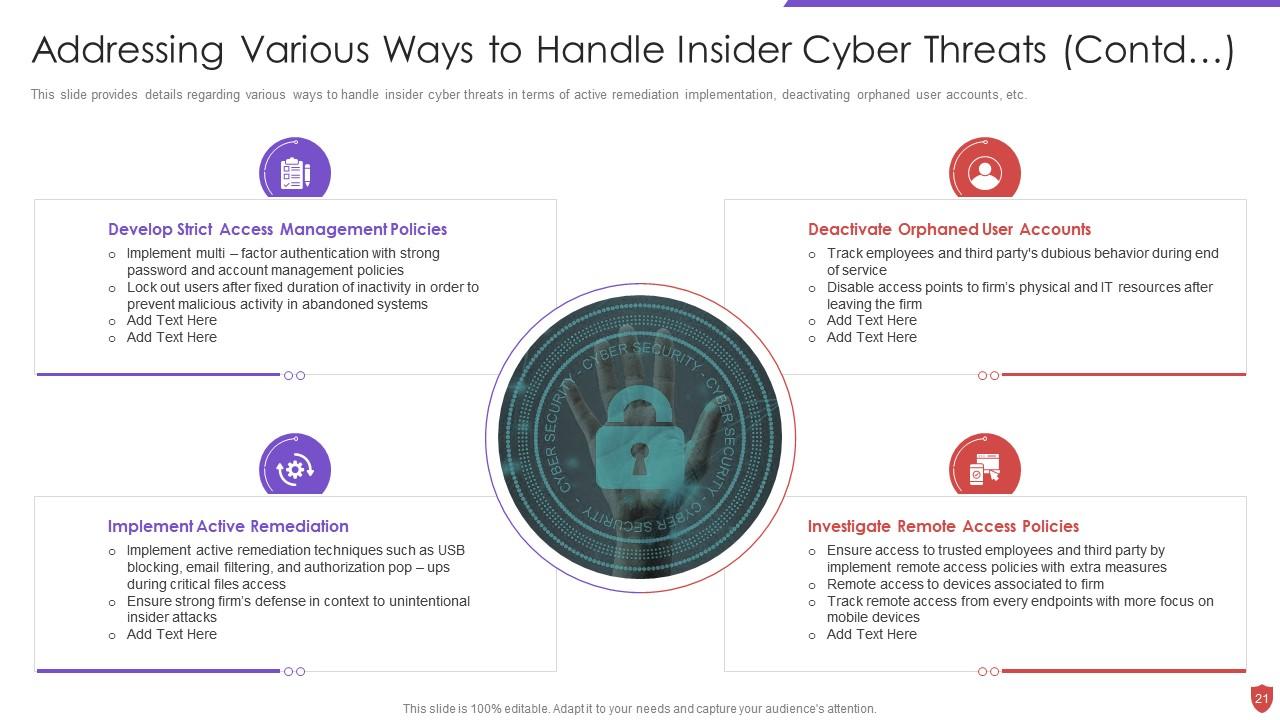
Slide 21: This slide exhibits continued content.
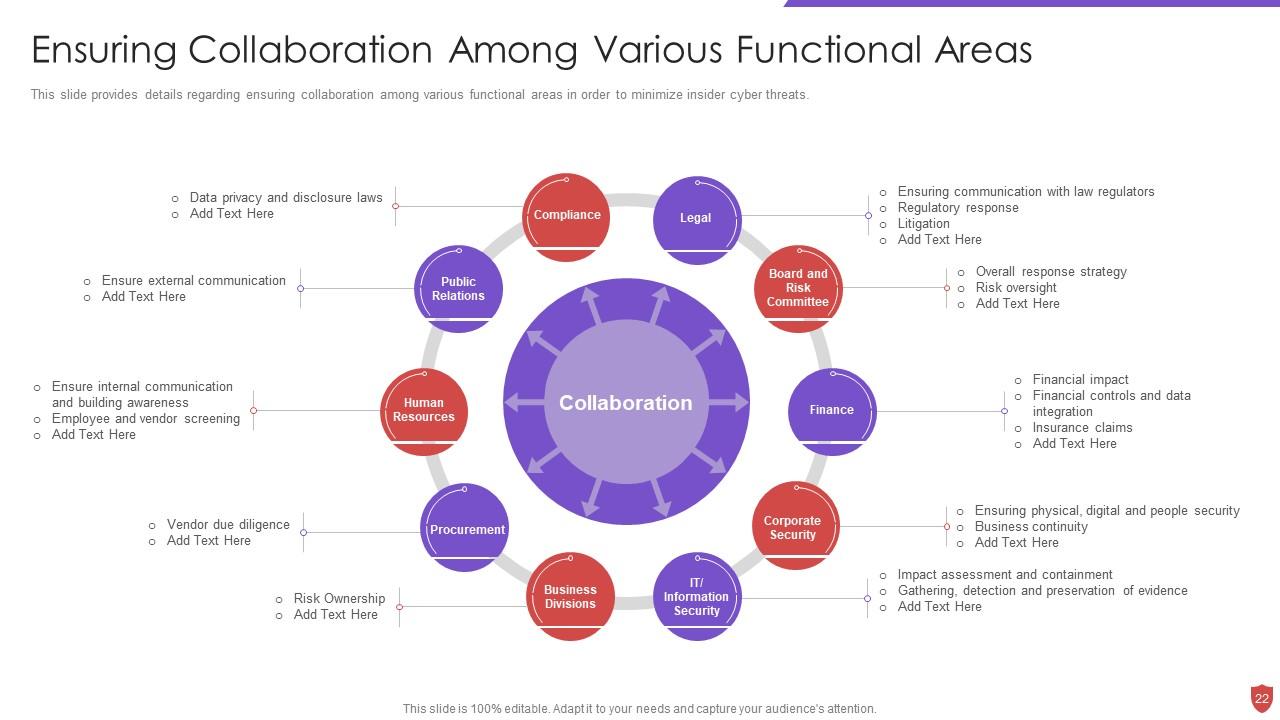
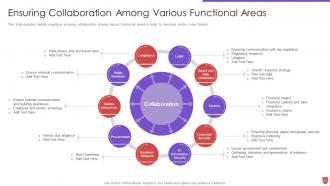
Slide 22: This slide provides details regarding ensuring collaboration among various functional areas.
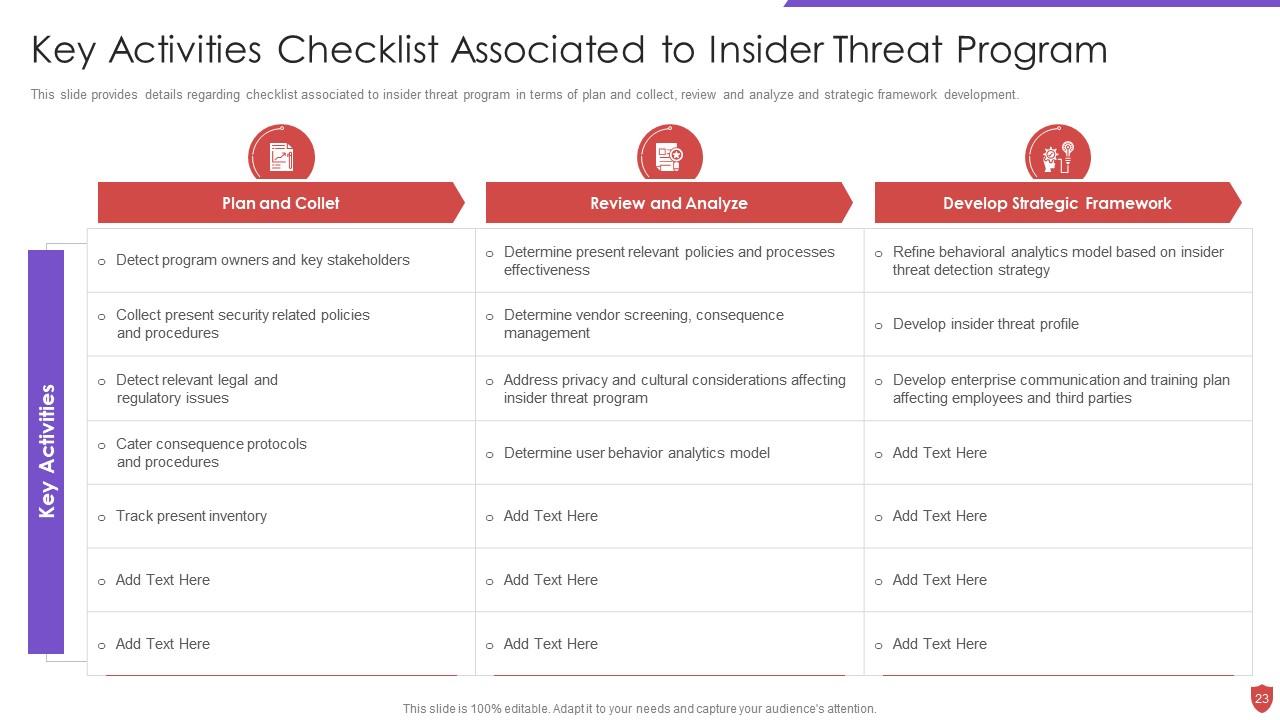
Slide 23: This slide provides details regarding checklist associated to insider threat program.
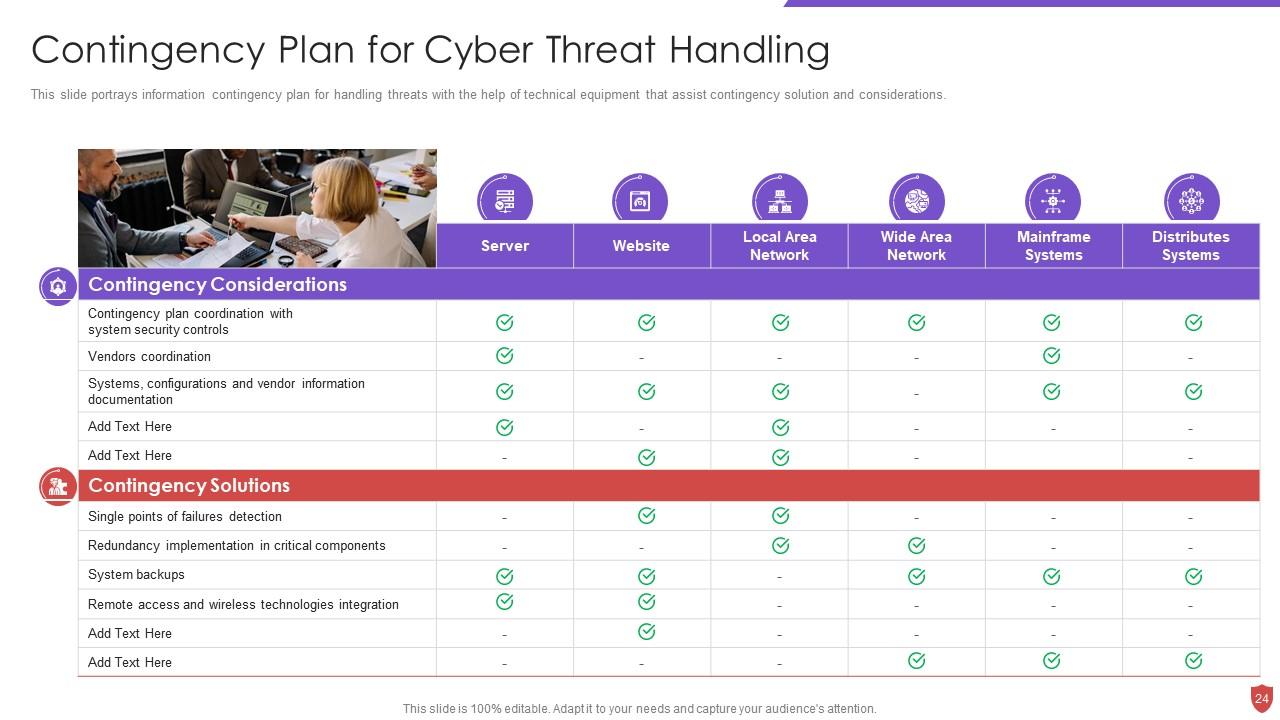
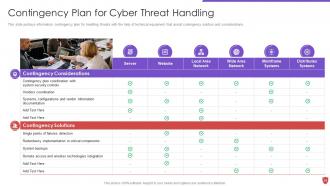
Slide 24: This slide portrays information contingency plan for handling threats with the help of technical equipment.
Slide 25: This slide shows title for 'People security against workplace violence or threat'.
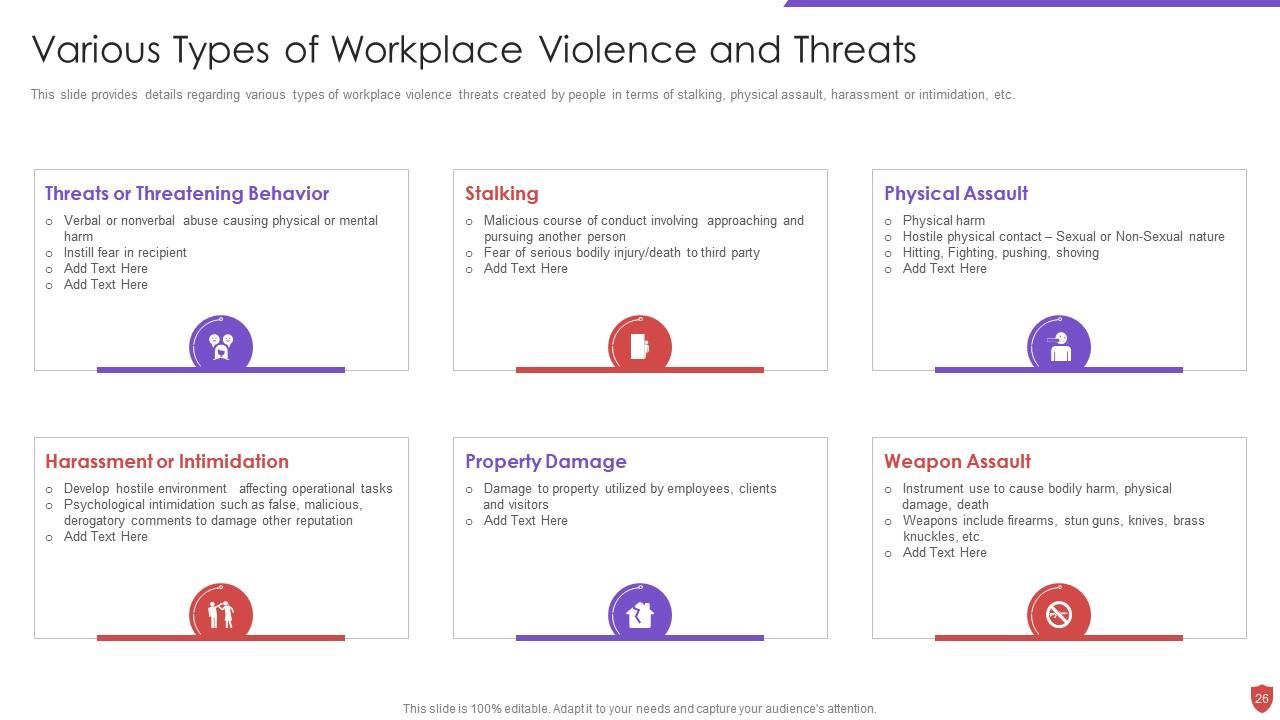
Slide 26: This slide provides details regarding various types of workplace violence threats created by people.
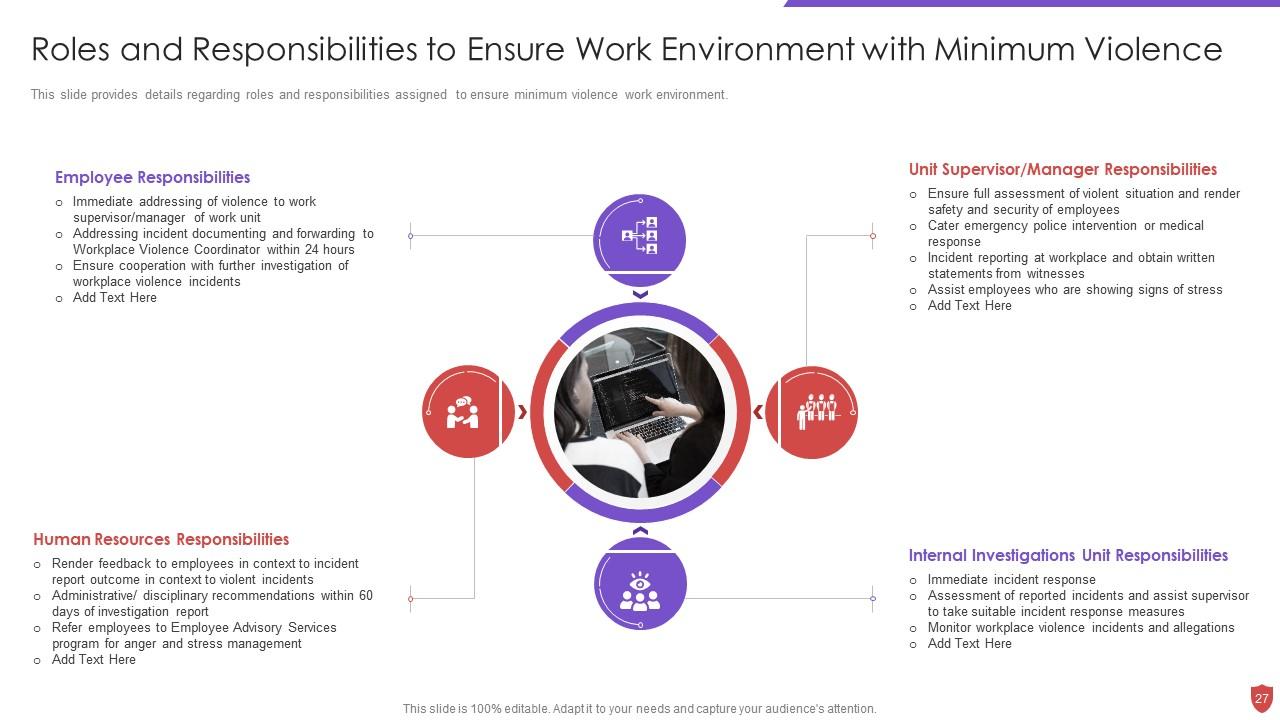
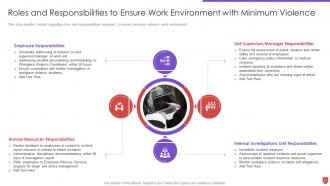
Slide 27: This slide provides details regarding roles and responsibilities assigned to ensure minimum violence work environment.
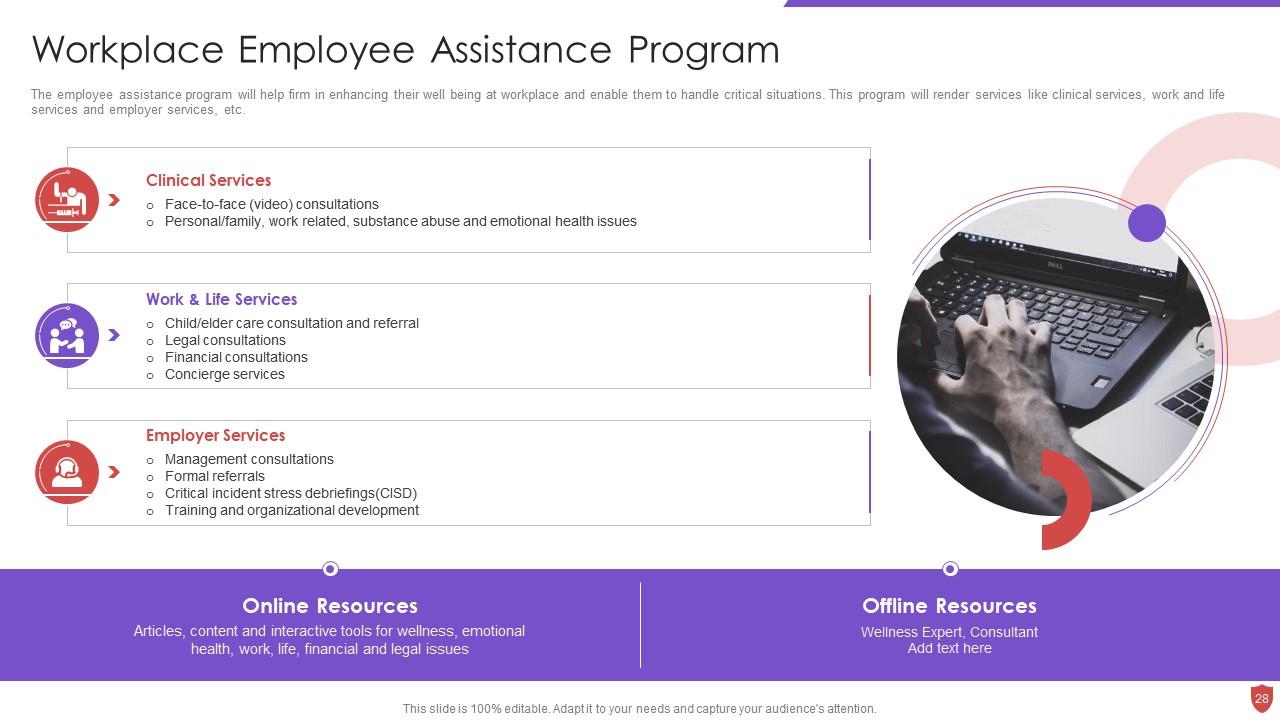
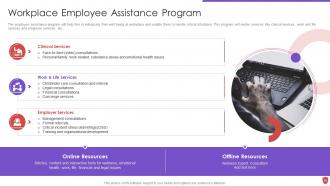
Slide 28: This slide depicts Workplace Employee Assistance Program.
Slide 29: This slide displays title for 'Ensuring physical security'.
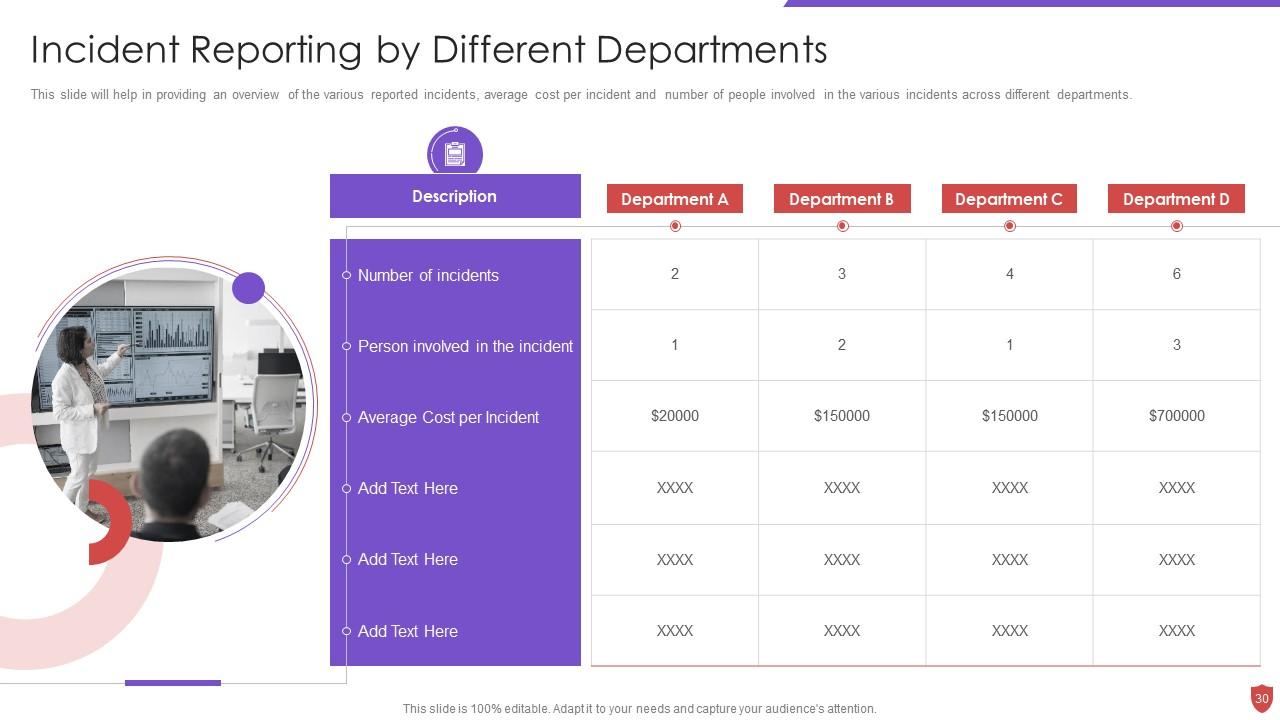
Slide 30: This slide provides overview of the various reported incidents.
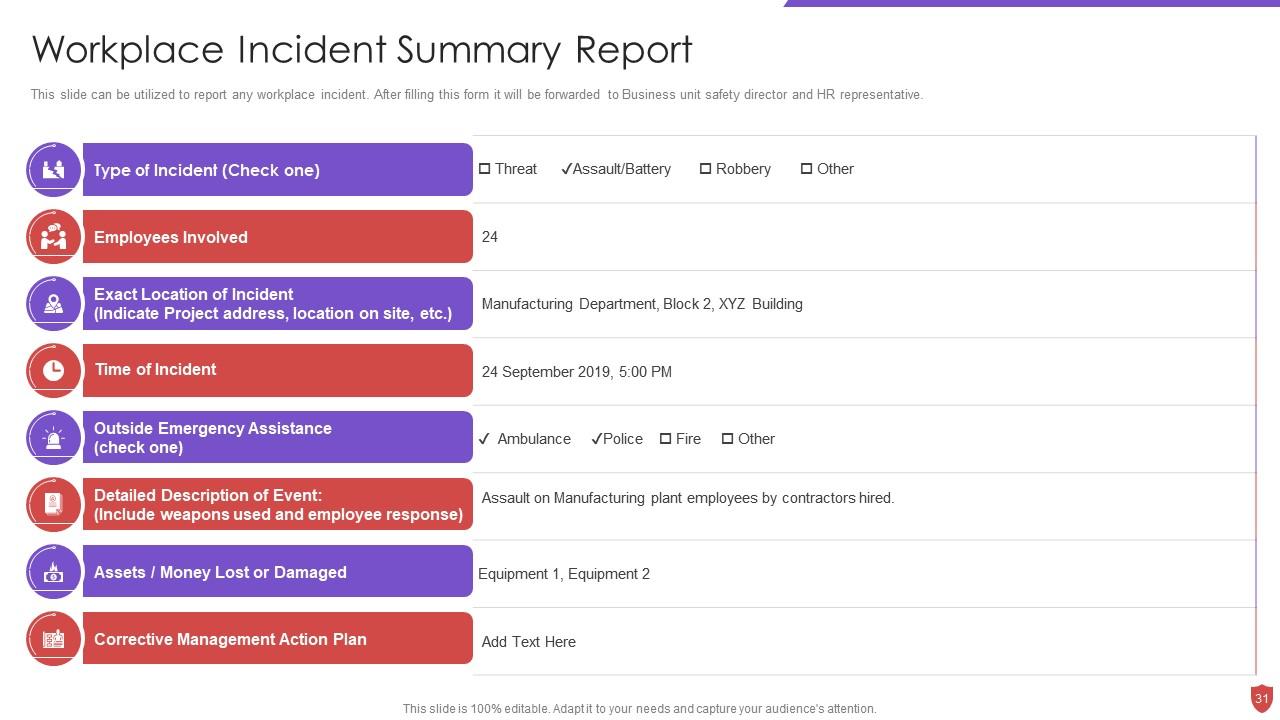
Slide 31: This slide can be utilized to report any workplace incident.
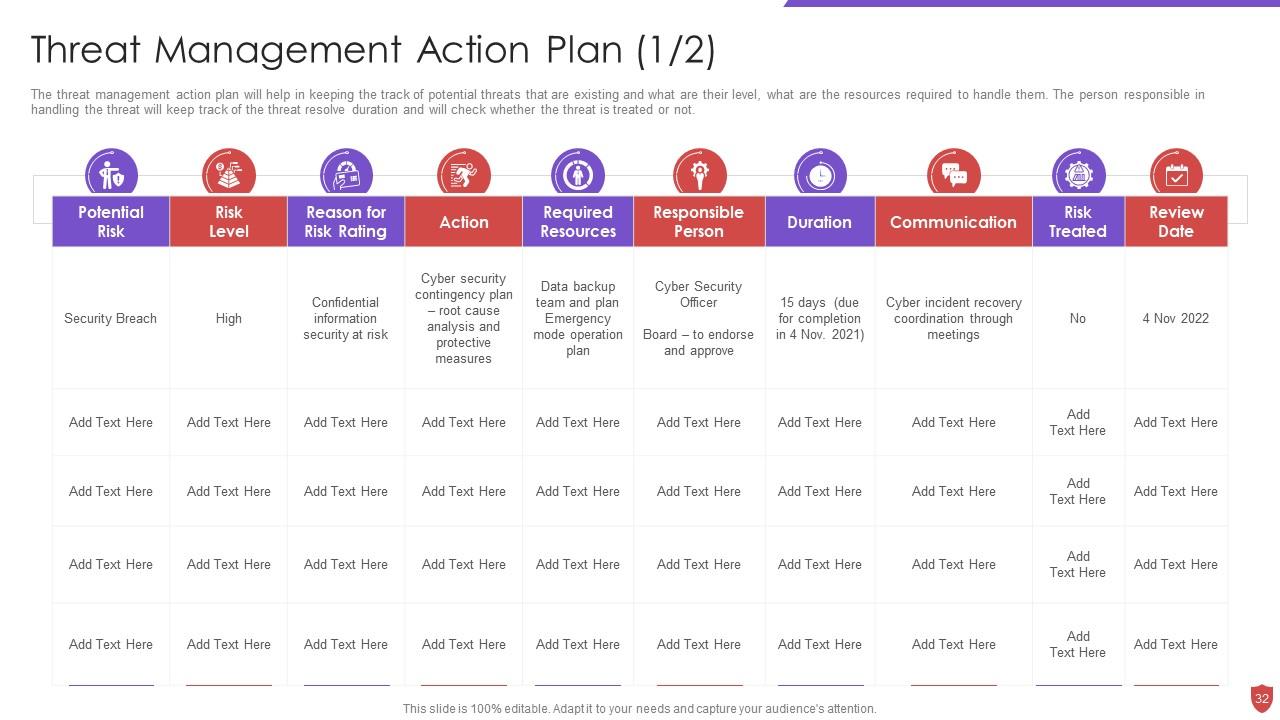
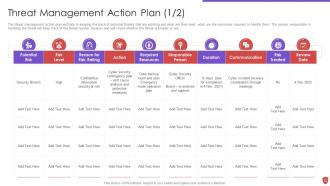
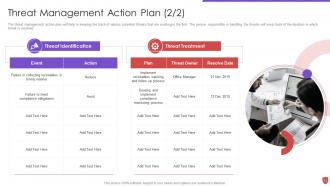
Slide 32: This slide presents Threat Management Action Plan.
Slide 33: This slide exhibits continued content.
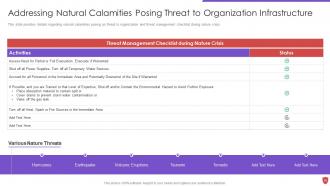
Slide 34: This slide shows title for 'Securing firm from natural calamity threats'.
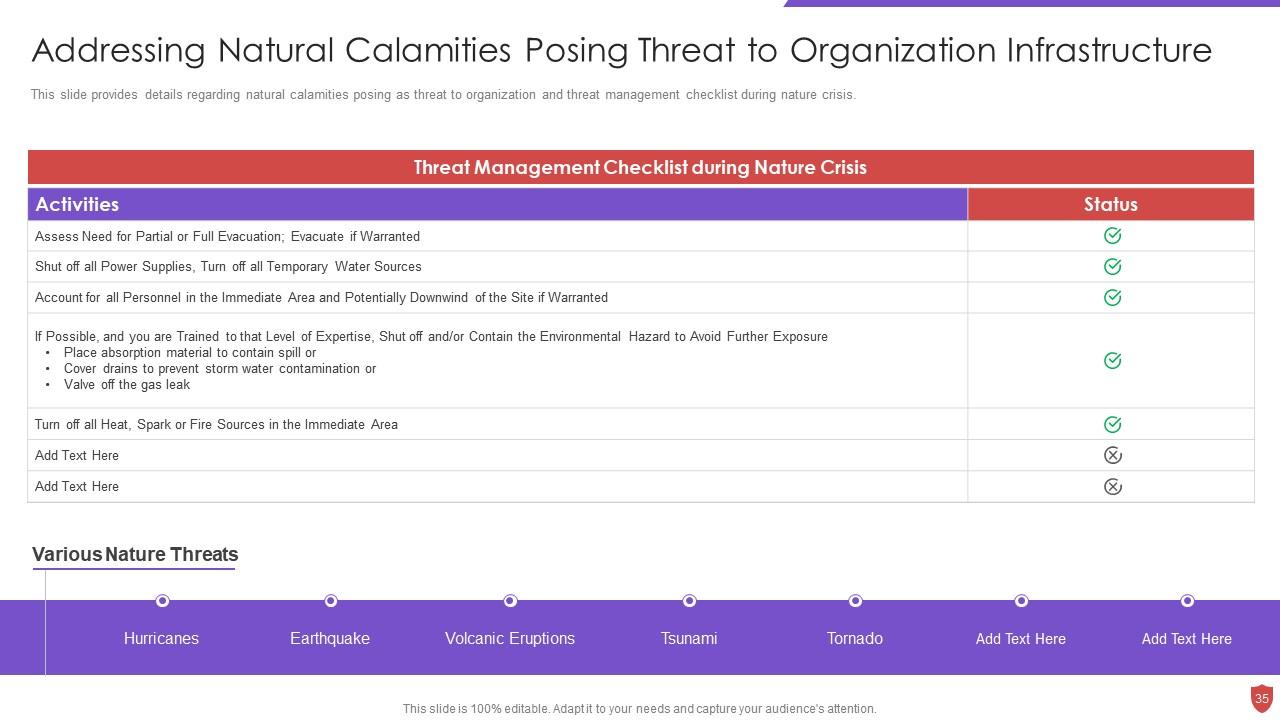
Slide 35: This slide provides details regarding natural calamities posing as threat.
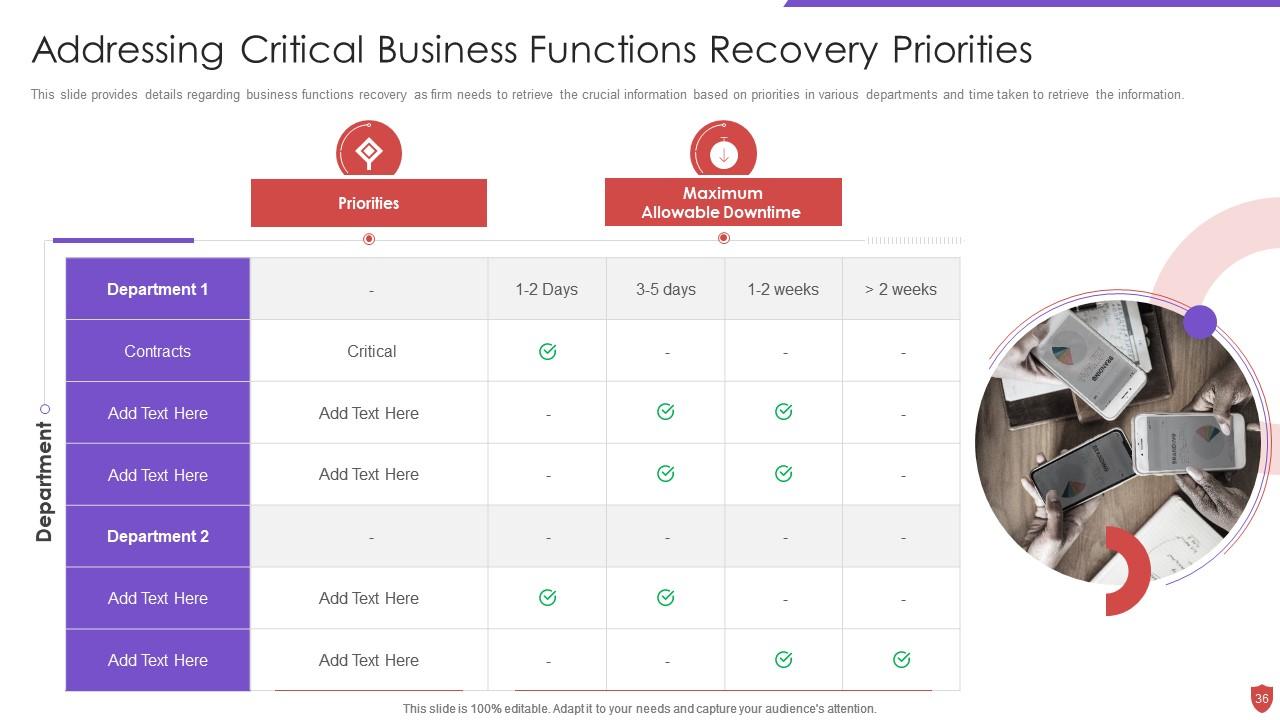
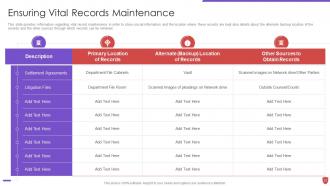
Slide 36: This slide provides details regarding business functions recovery as firm needs to retrieve the crucial information.
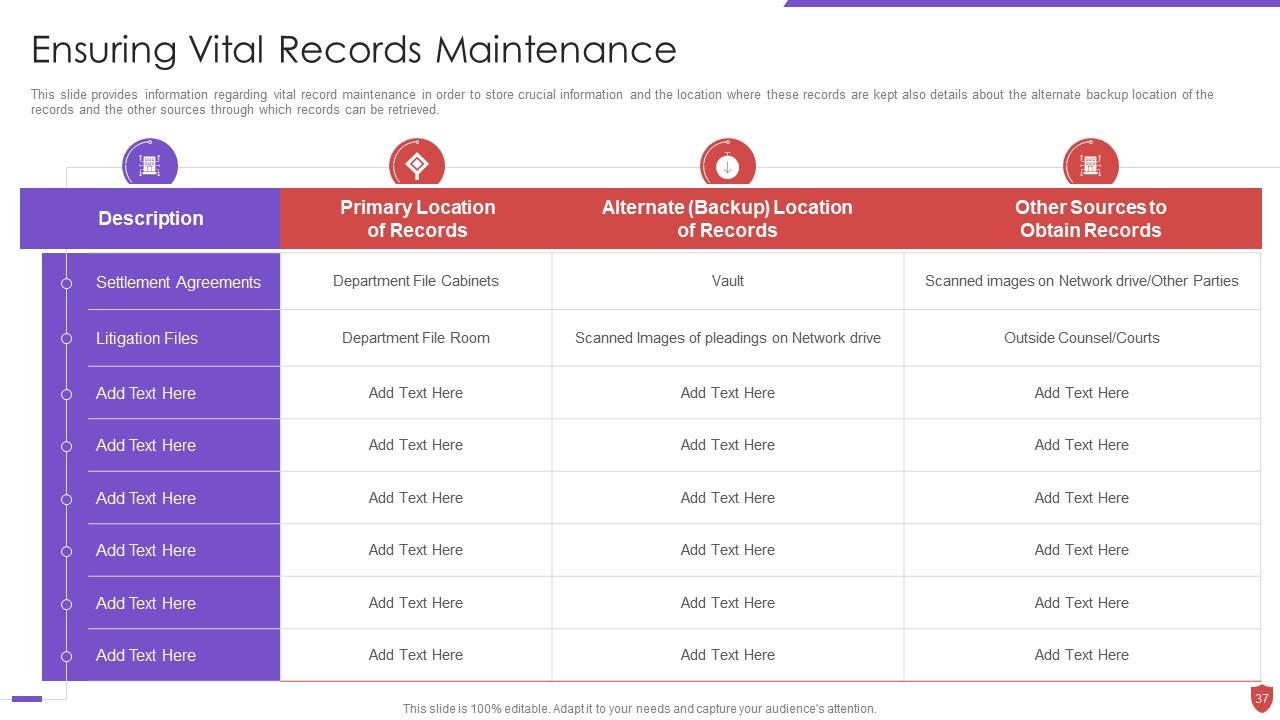
Slide 37: This slide provides information regarding vital record maintenance in order to store crucial information.
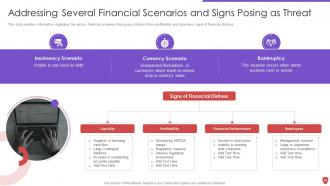
Slide 38: This slide displays title for 'Ensuring financial assets security'.
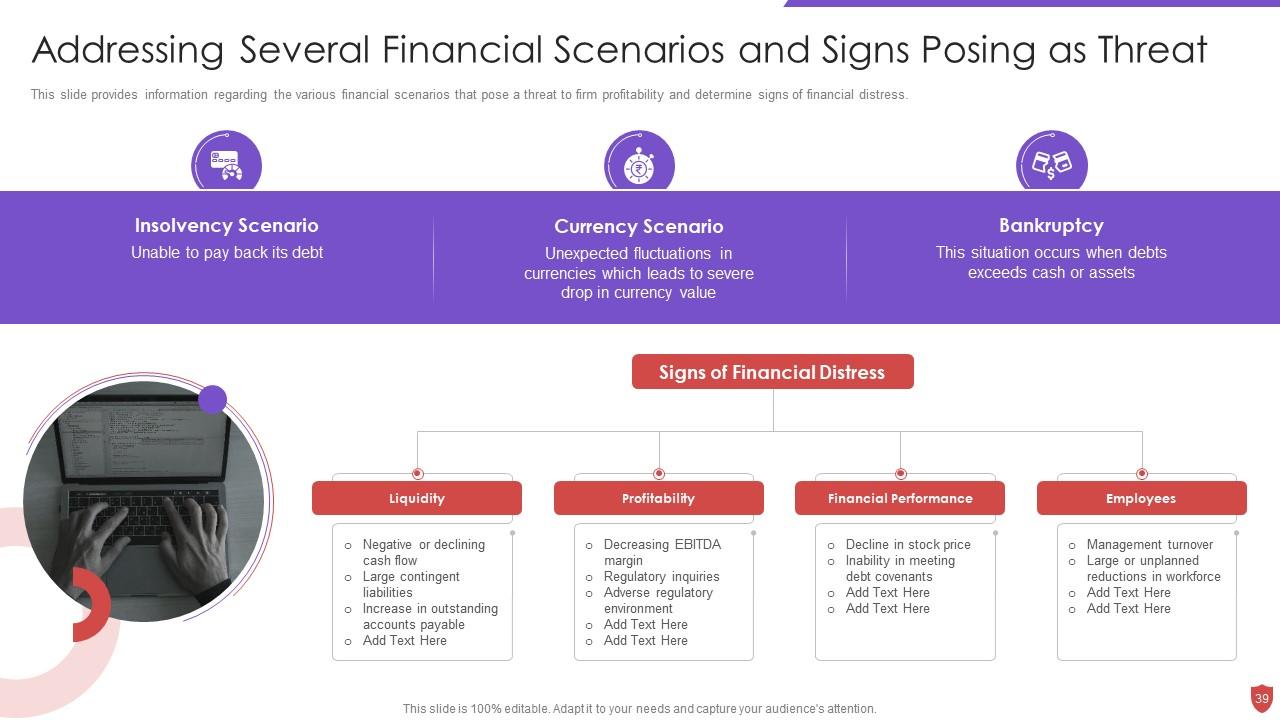
Slide 39: This slide provides information regarding the various financial scenarios that pose a threat to firm.
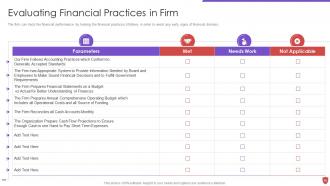
Slide 40: This slide presents Evaluating Financial Practices in Firm.
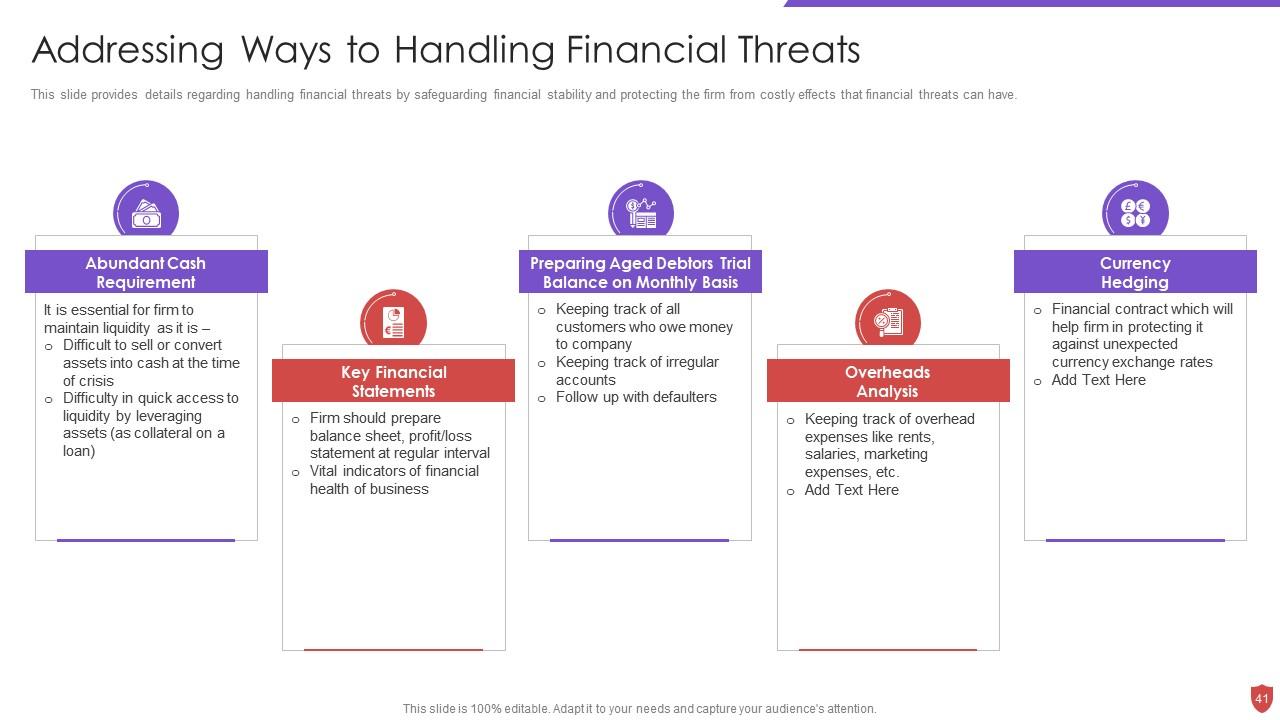
Slide 41: This slide provides details regarding handling financial threats by safeguarding financial stability.
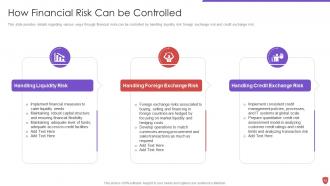
Slide 42: This slide provides details regarding various ways through financial risks can be controlled.
Slide 43: This slide presents title for 'Leveraging workforce'.
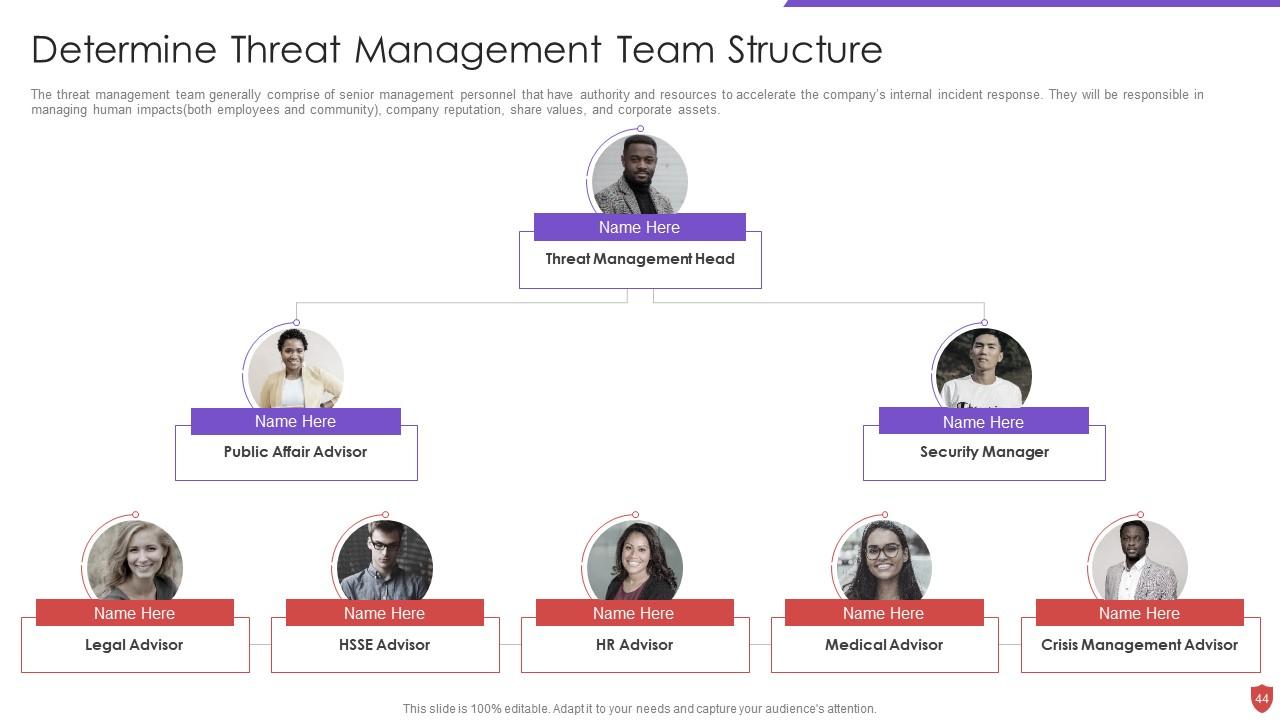
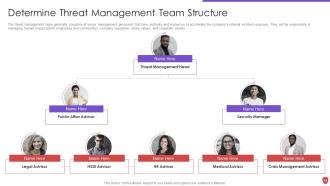
Slide 44: This slide exhibits 'Determine Threat Management Team Structure'.
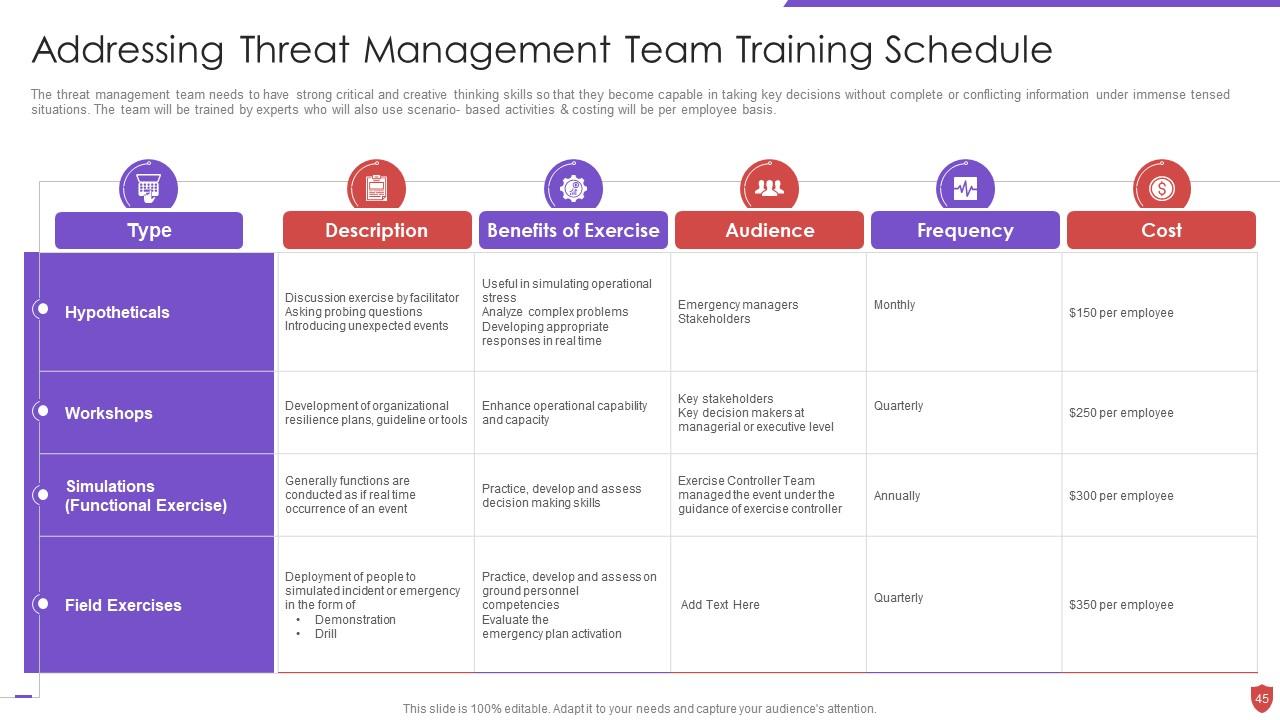
Slide 45: This slide addresses Threat Management Team Training Schedule.
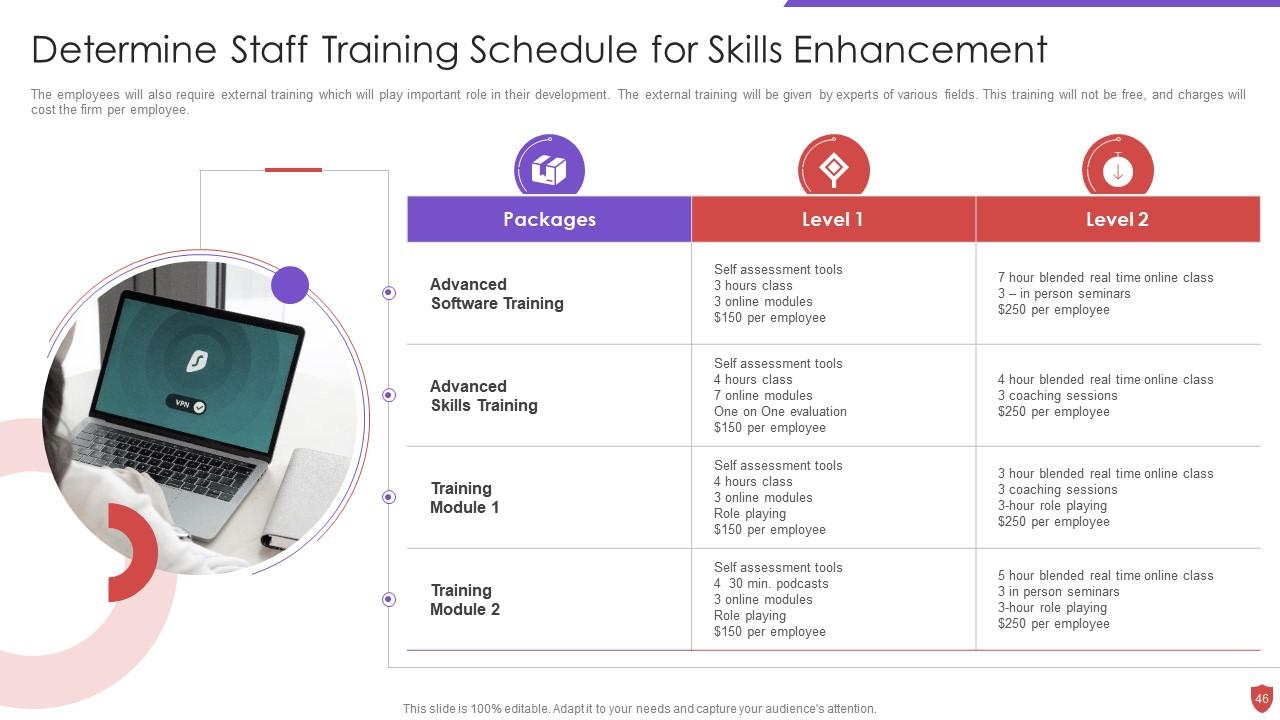
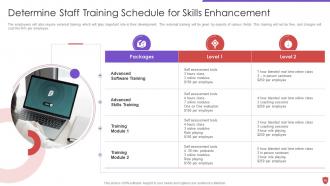
Slide 46: This slide shows 'Determine Staff Training Schedule for Skills Enhancement'.
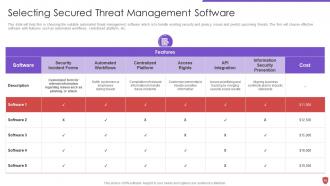
Slide 47: This slide depicts title for 'Budget assessment'.
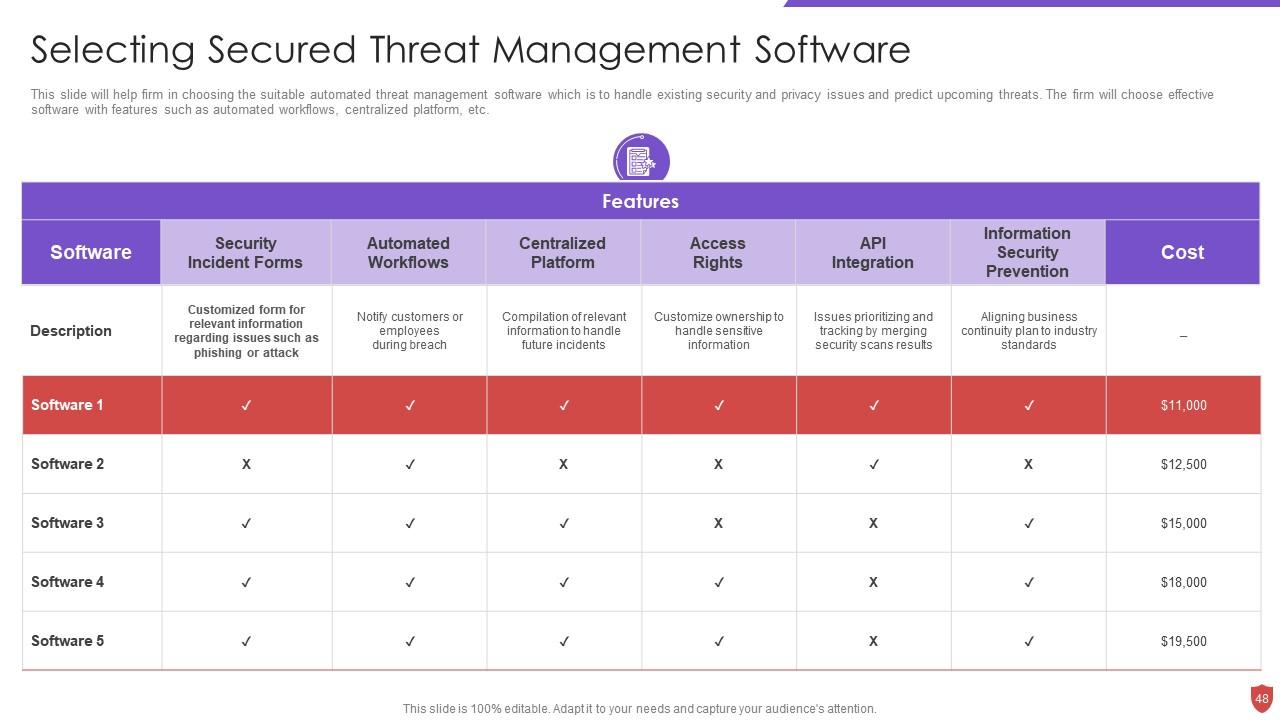
Slide 48: This slide highlights 'Selecting Secured Threat Management Software'.
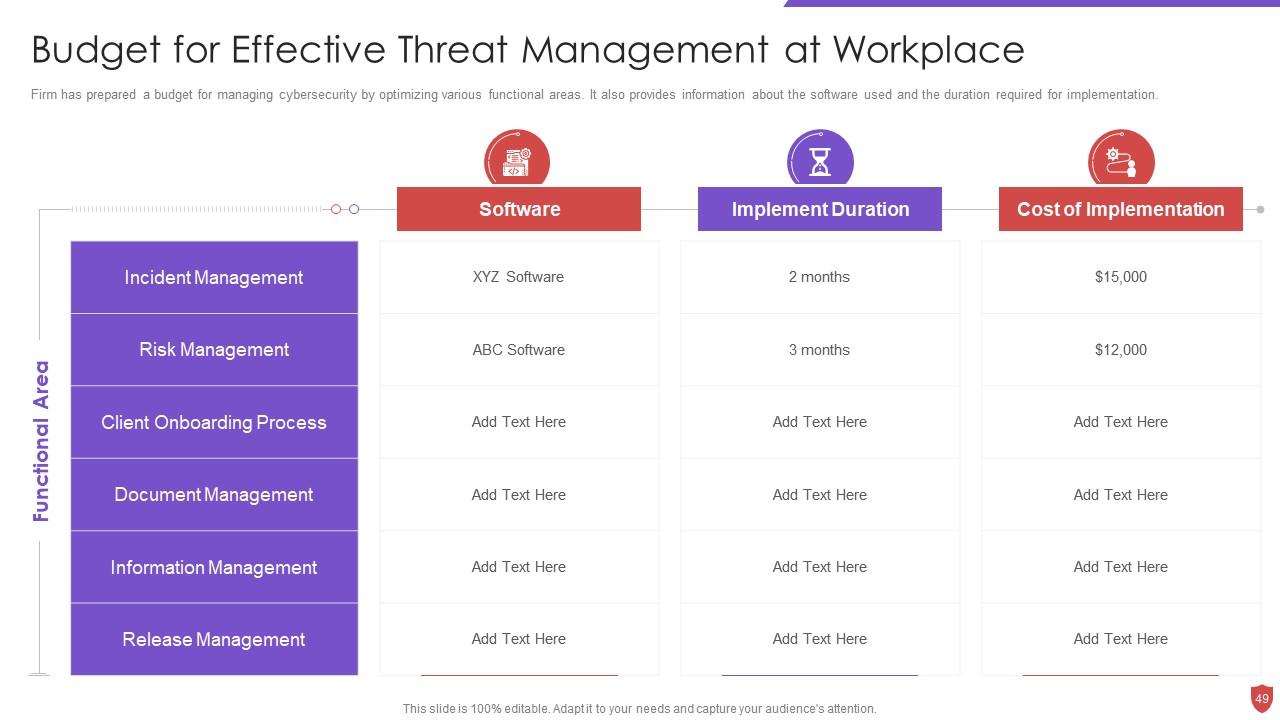
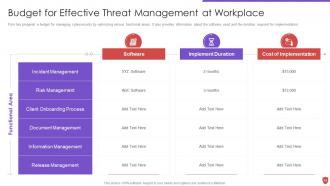
Slide 49: This slide illustrates Budget for Effective Threat Management at Workplace.
Slide 50: This slide presents title for 'Impact assessment'.
Slide 51: This slide portrays information regarding how firm is successful in handling security threats.
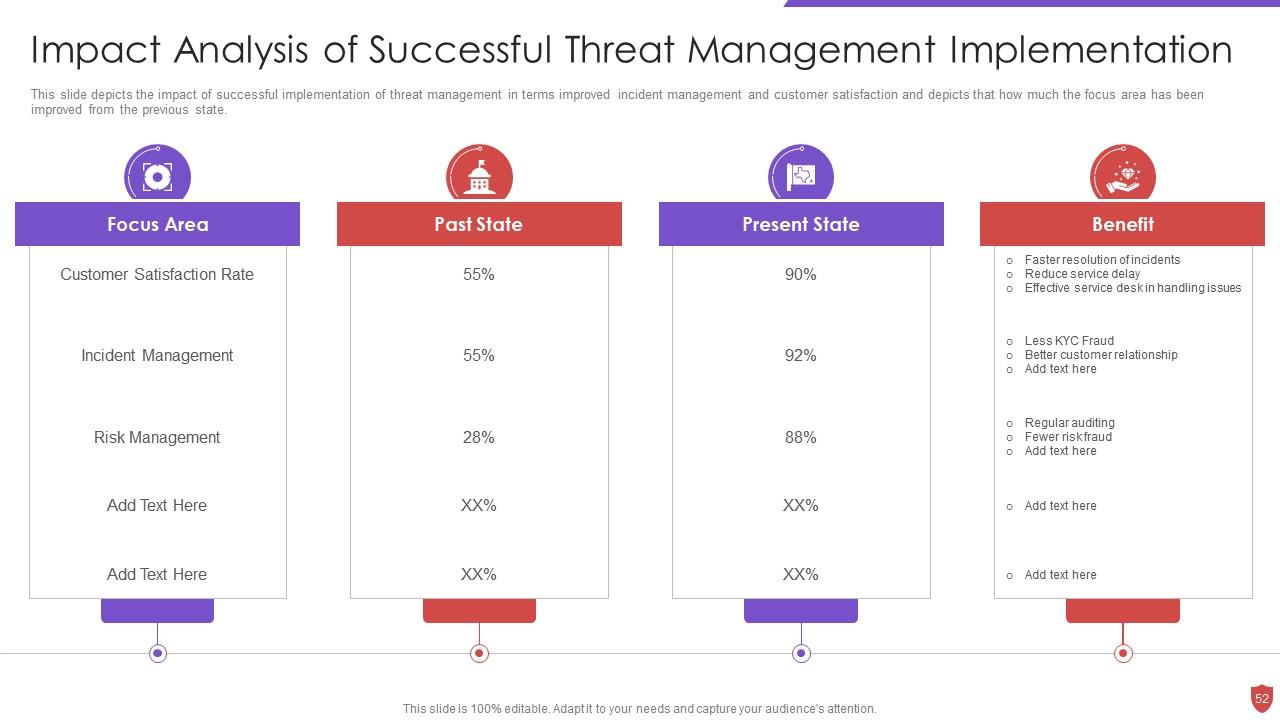
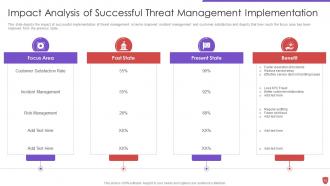
Slide 52: This slide depicts the impact of successful implementation of threat management.
Slide 53: This slide exhibits title for 'Dashboard'.
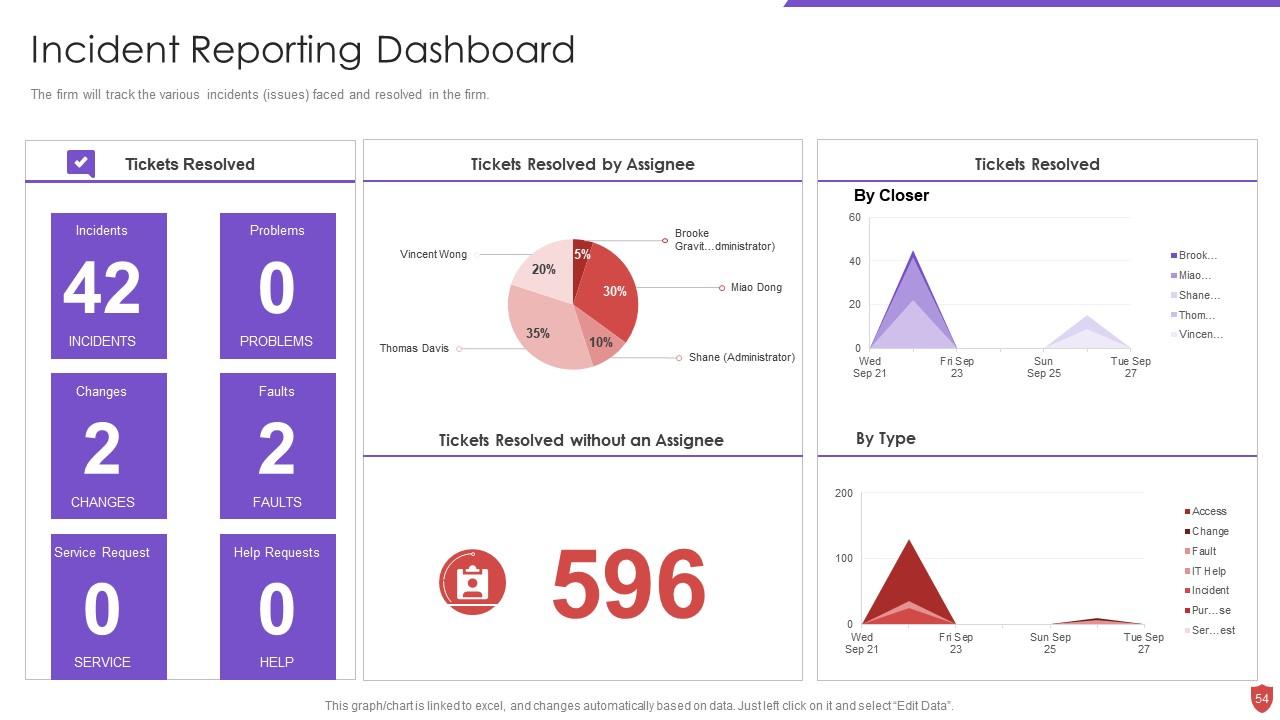
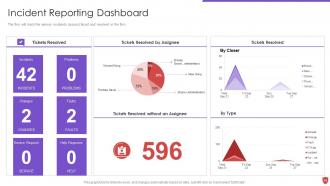
Slide 54: This slide shows Incident Reporting Dashboard.
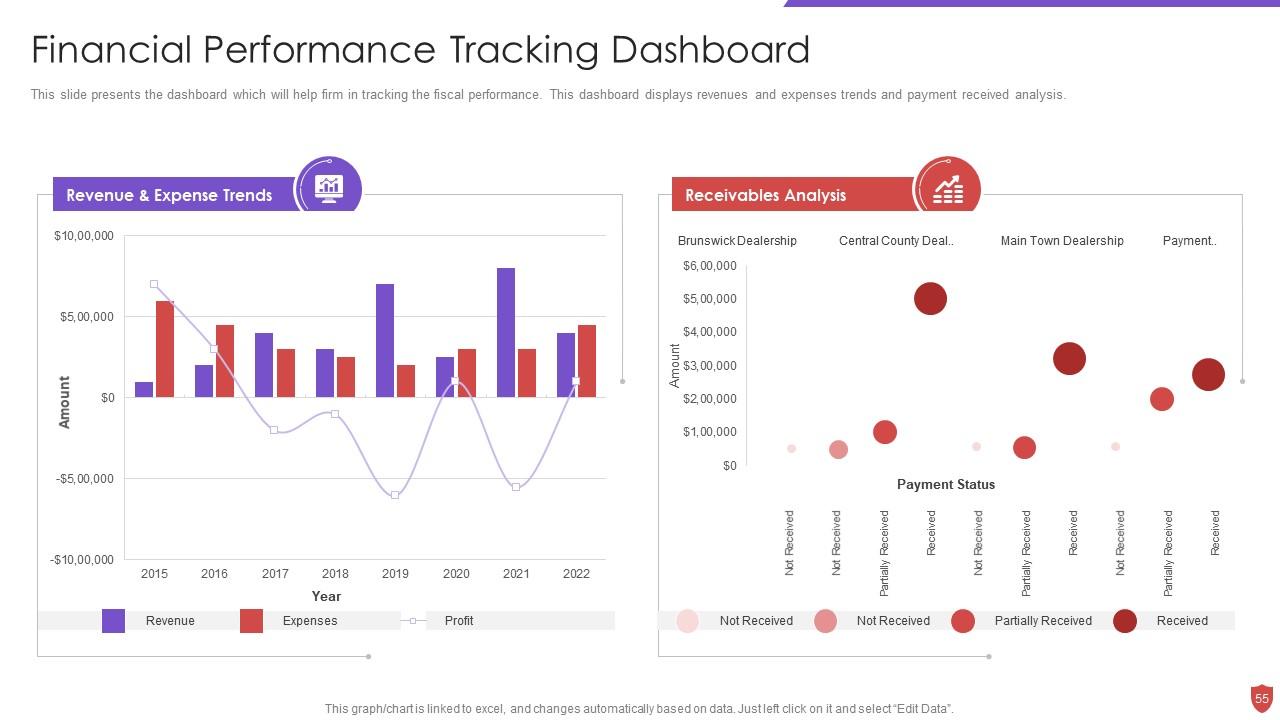
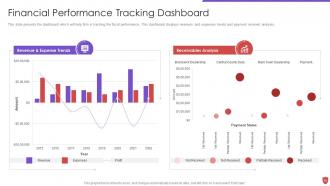
Slide 55: This slide presents the dashboard which will help firm in tracking the fiscal performance.
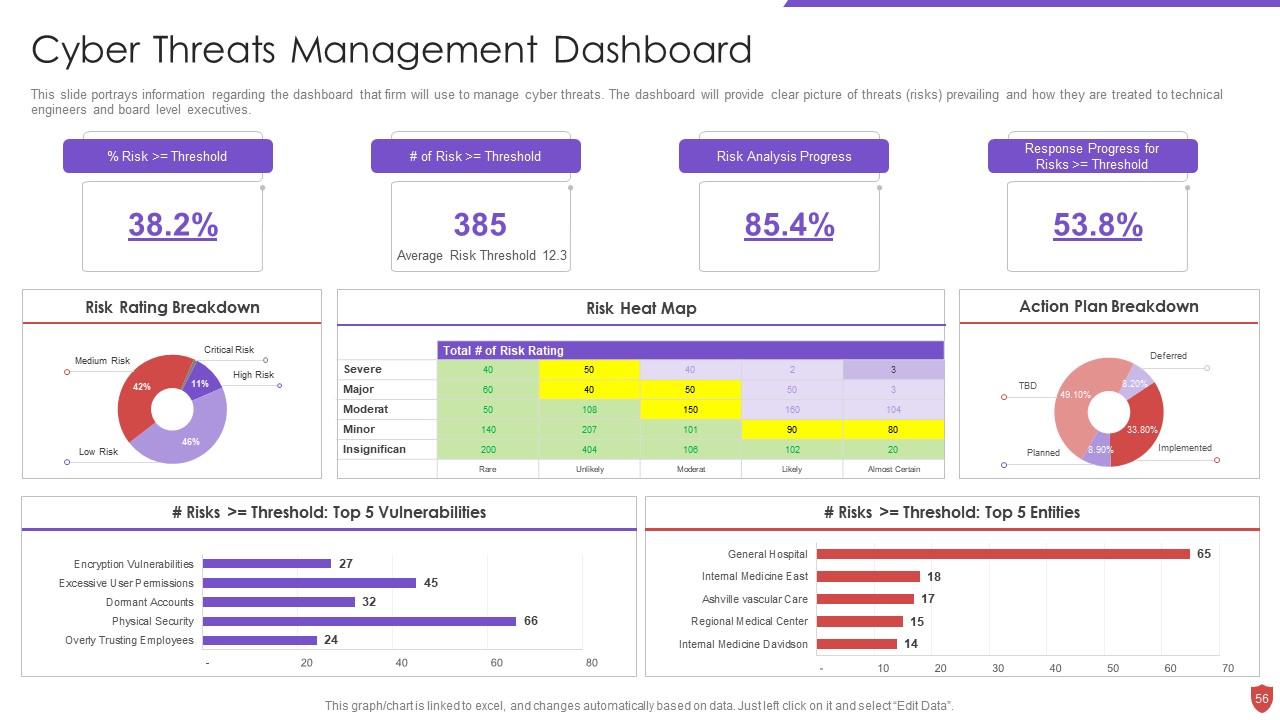
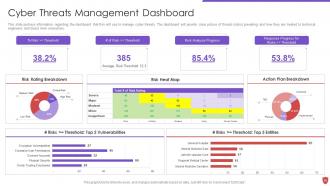
Slide 56: This slide portrays information regarding the dashboard that firm will use to manage cyber threats.
Slide 57: This slide displays Icons for Cyber Security Risk Management.
Slide 58: This slide is titled as Additional Slides for moving forward.
Slide 59: This slide provides 30 60 90 Days Plan with text boxes.
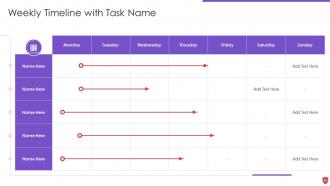
Slide 60: This slide shows Weekly Timeline with Task Name.
Slide 61: This slide displays Roadmap for Process Flow.
Slide 62: This slide shows Post It Notes. Post your important notes here.
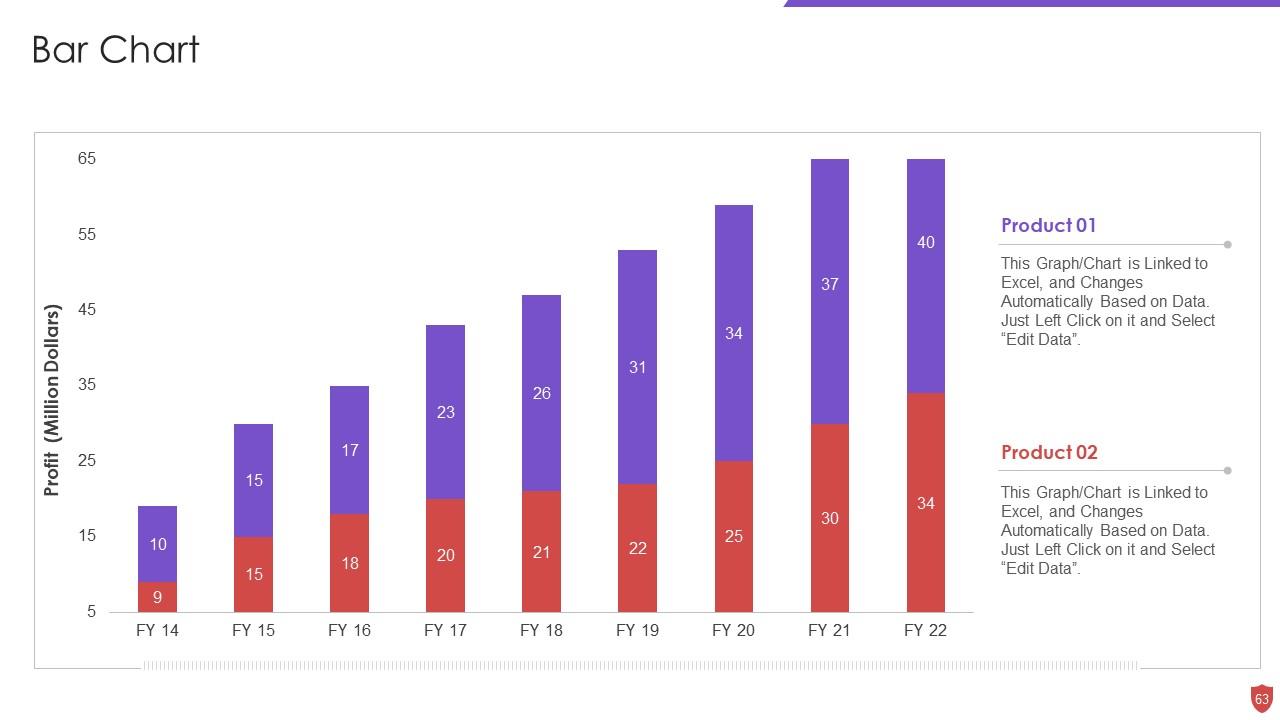
Slide 63: This slide presents Bar chart with two products comparison.
Slide 64: This is a Comparison slide to state comparison between commodities, entities etc.
Slide 65: This slide showcases Magnifying Glass to highlight information, specifications etc
Slide 66: This is Our Target slide. State your targets here.
Slide 67: This is a Thank You slide with address, contact numbers and email address.
Cyber security risk management powerpoint presentation slides with all 72 slides:
Use our Cyber Security Risk Management Powerpoint Presentation Slides to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
Enough space for editing and adding your own content.
-
Best Representation of topics, really appreciable.