Information Technology Security Powerpoint Presentation Slides
IT Security protects electronic devices such as computers, servers, mobile gadgets, data, electronic systems, etc., from IT attacks. This PowerPoint presentation illustrates important details about Information Technology security. This IT security PowerPoint presentation will be helpful to throw light on the current scenario of the organization, the requirement of IT security in different sectors, and its work. In addition, computer security PPT contains the critical elements of IT security, IT risk identification and assessment, steps to mitigate those risks, benefits of IT security, and automations role in IT security. Further, this data security presentation comes with a checklist to implement IT security in the organization, a 30-60-90-day plan to manage IT security, and the budget to implement the same. The Information Security deck also showcases a roadmap to monitor IT security and a timeline to implement IT security. Lastly, this electronic information security PPT shows the effects of IT security implementation on the organization and dashboard for threat tracking in Information Technology Security. Customize this 100 Percent editable template now.
IT Security protects electronic devices such as computers, servers, mobile gadgets, data, electronic systems, etc., from IT..
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Deliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts,this Information Technology Security Powerpoint Presentation Slides is the best tool you can utilize. Personalize its content and graphics to make it unique and thought provoking. All the eighty one slides are editable and modifiable,so feel free to adjust them to your business setting. The font,color,and other components also come in an editable format making this PPT design the best choice for your next presentation. So,download now.
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
Slide 1: This slide introduces Information Technology Security. State Your Company Name and begin.
Slide 2: This is an Agenda slide. State your agendas here.
Slide 3: This slide presents Table of Content for the presentation.
Slide 4: This is another slide continuing Table of Content for the presentation.
Slide 5: This slide highlights title for topics that are to be covered next in the template.
Slide 6: This slide defines the meaning of Cyber security and how it helps to prevent data through different methods and techniques.
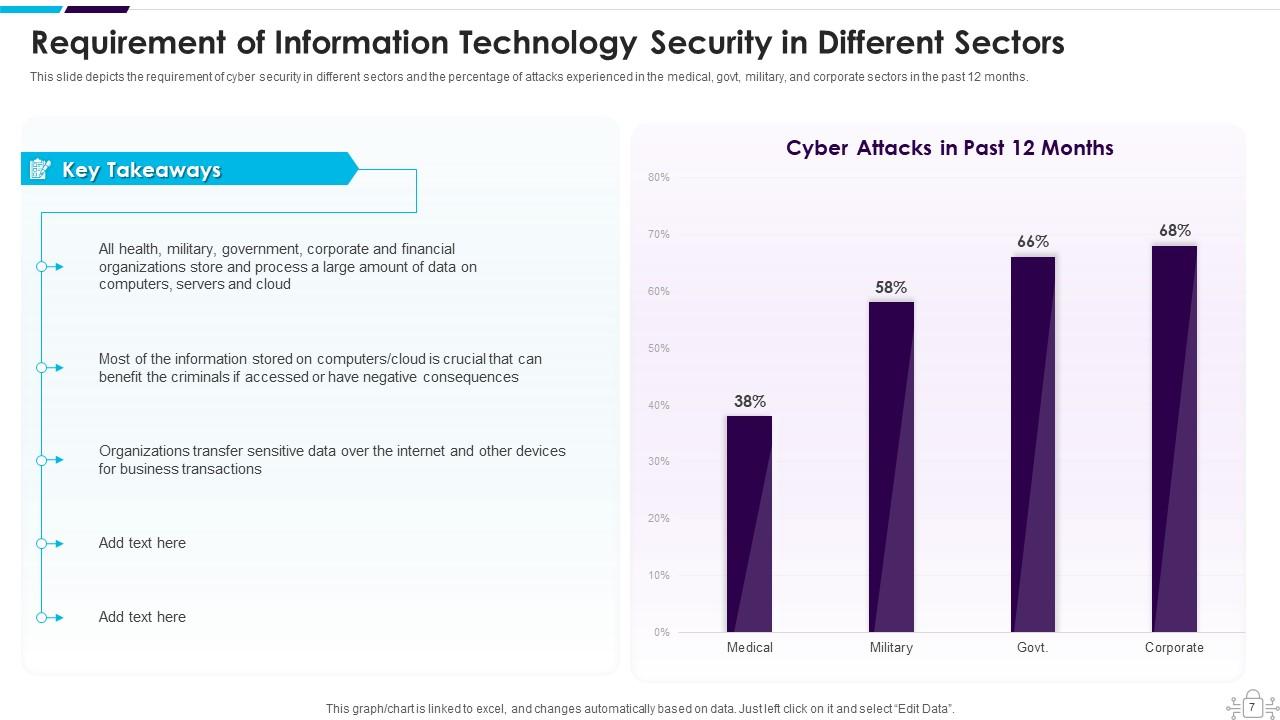
Slide 7: This slide shows Requirement of Cyber Security in Different Sectors.
Slide 8: This slide highlights title for topics that are to be covered next in the template.
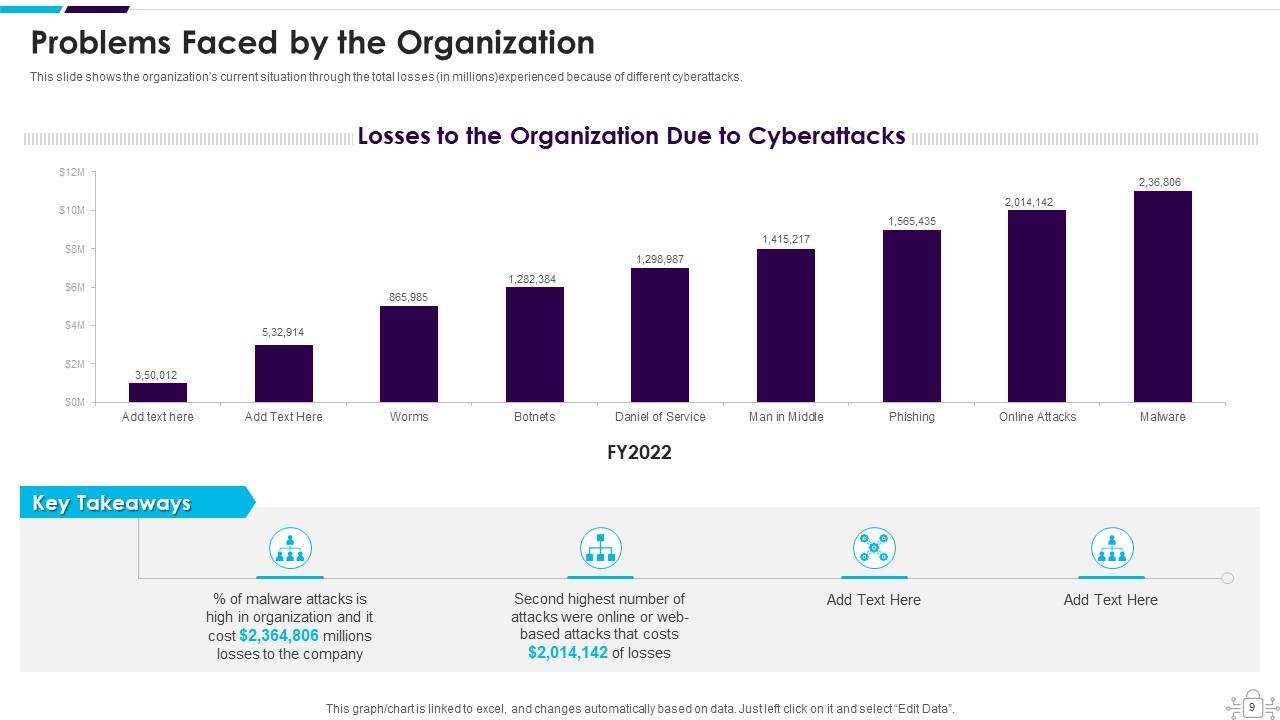
Slide 9: This slide shows the organization's current situation through the total losses experienced because of different cyberattacks.
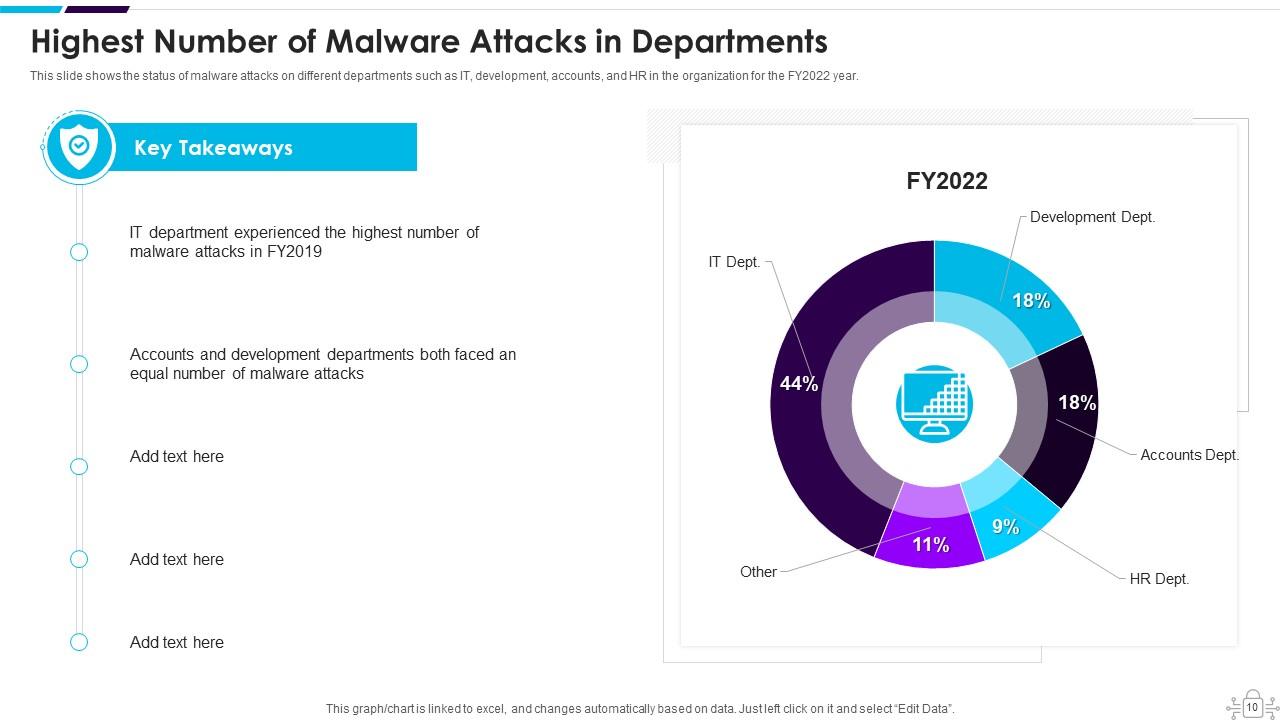
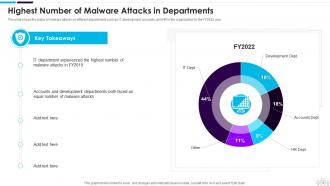
Slide 10: This slide displays Highest Number of Malware Attacks in Departments.
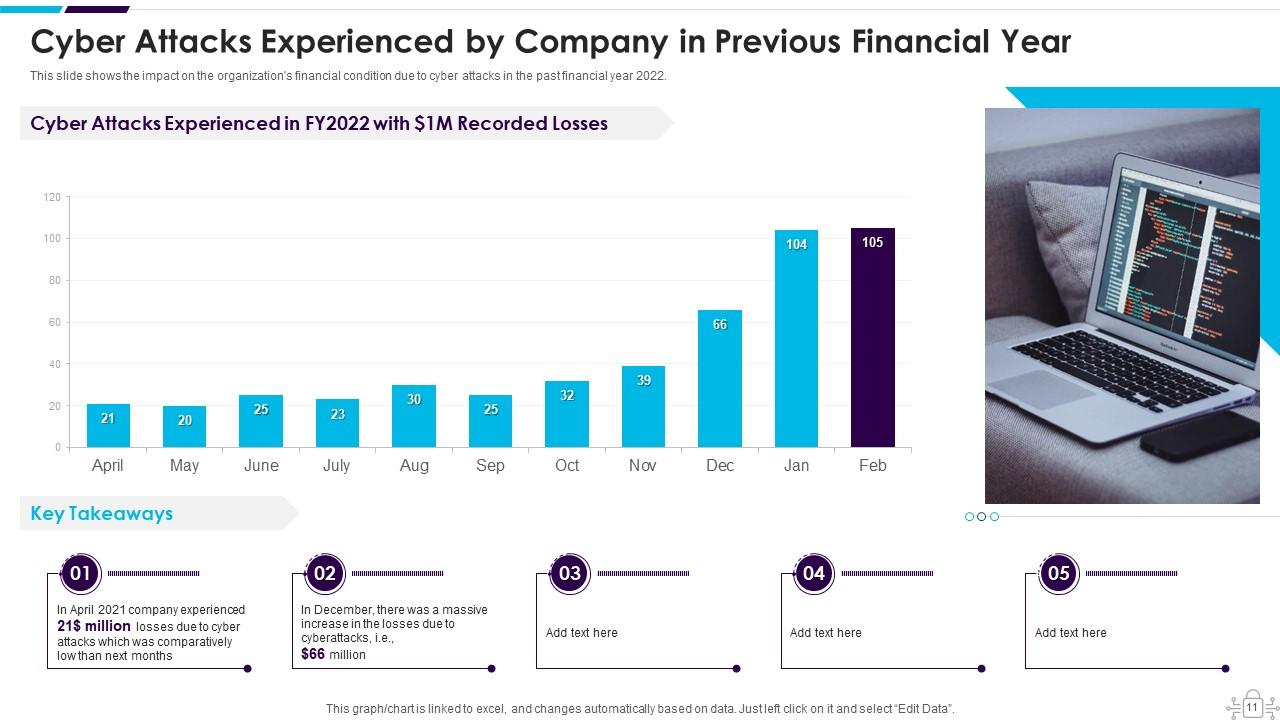
Slide 11: This slide shows Cyber Attacks Experienced by Company in Previous Financial Year.
Slide 12: This slide highlights title for topics that are to be covered next in the template.
Slide 13: This slide represents the different elements of Cyber security such as application security, network security, information security, etc.
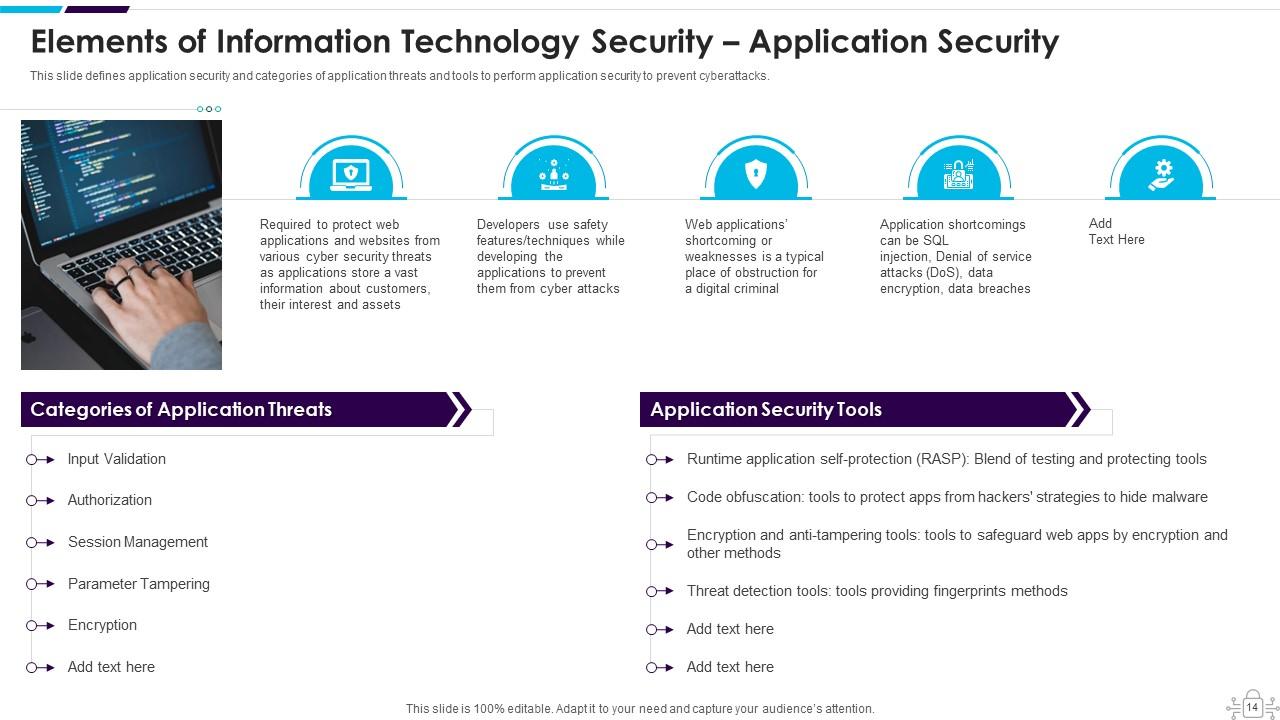
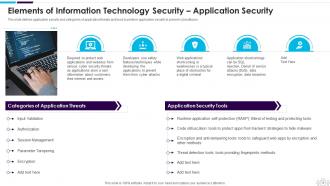
Slide 14: This slide defines application security and categories of application threats and tools to perform application security.
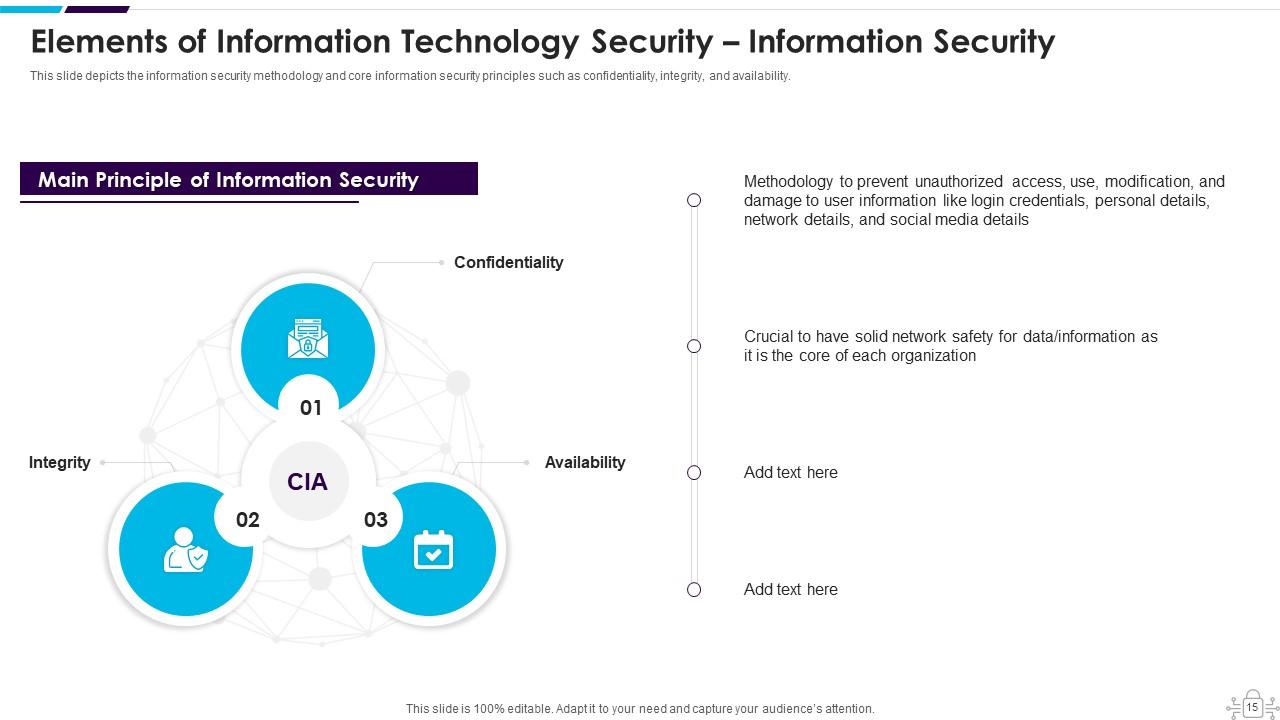
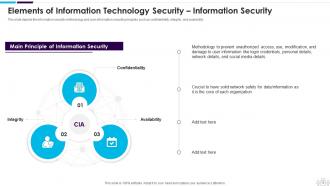
Slide 15: This slide displays Elements of Cyber Security – Information Security.
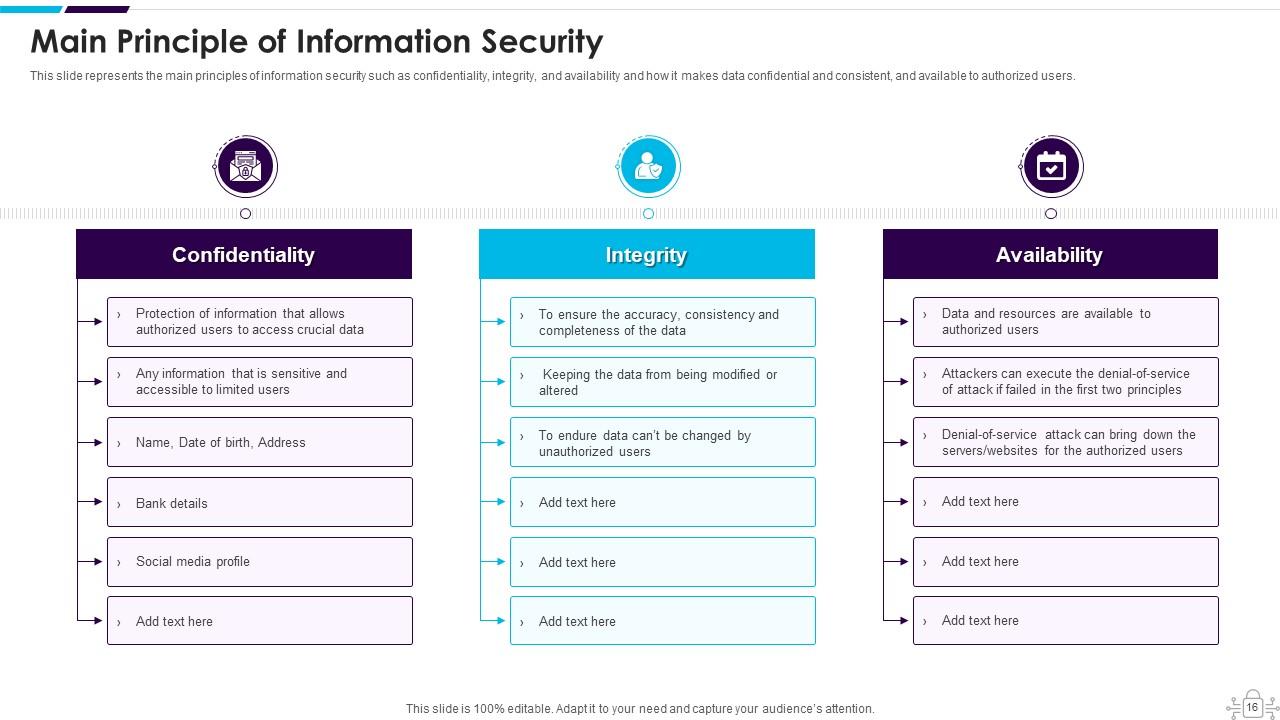
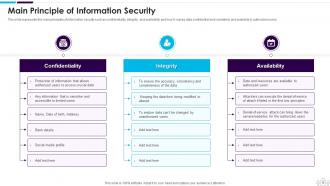
Slide 16: This slide represents the main principles of information security such as confidentiality, integrity, and availability.
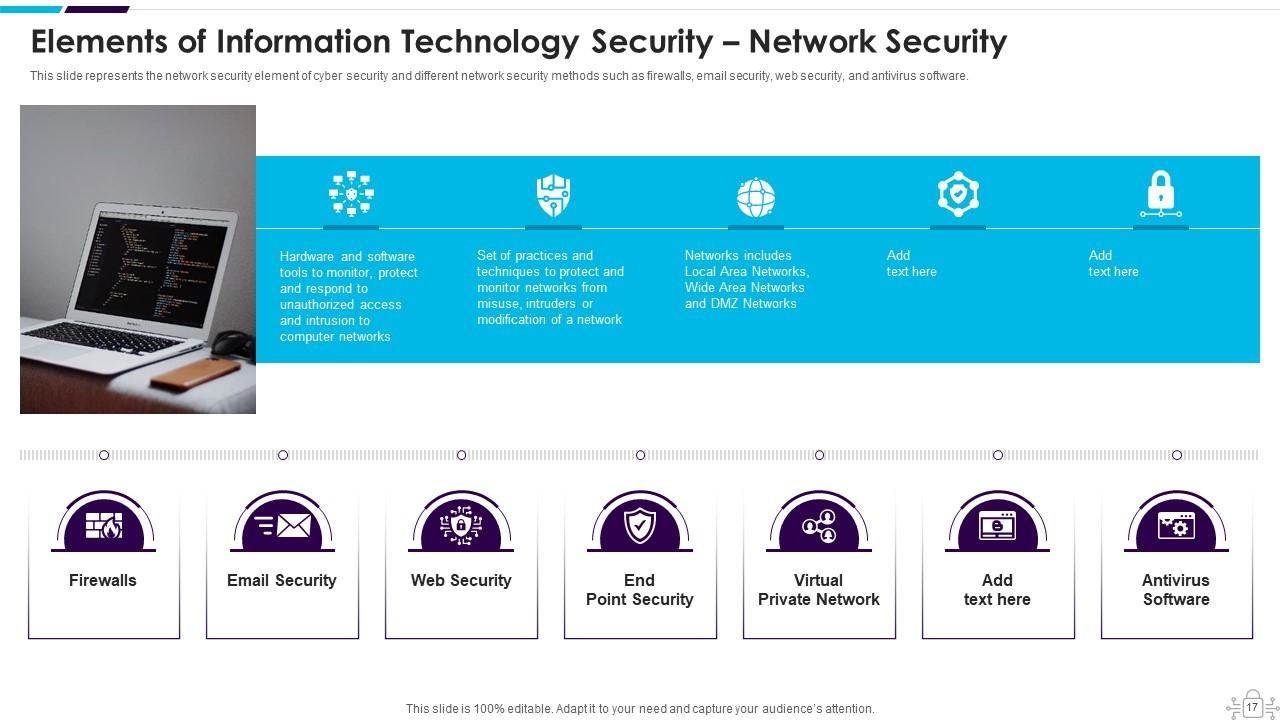
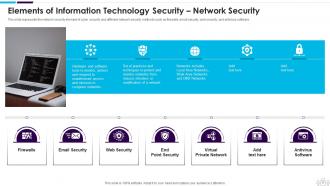
Slide 17: This slide represents the Cyber security element of Network security and different network security methods.
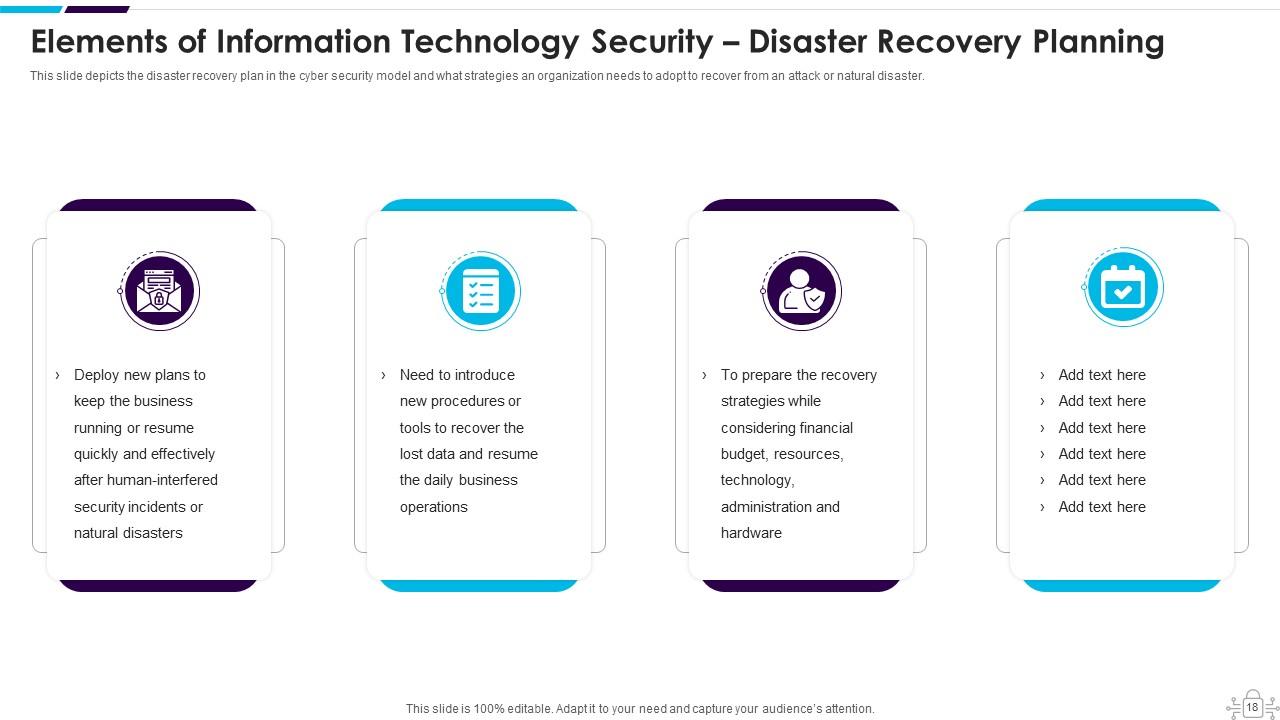
Slide 18: This slide presents Elements of Cyber Security – Disaster Recovery Planning.
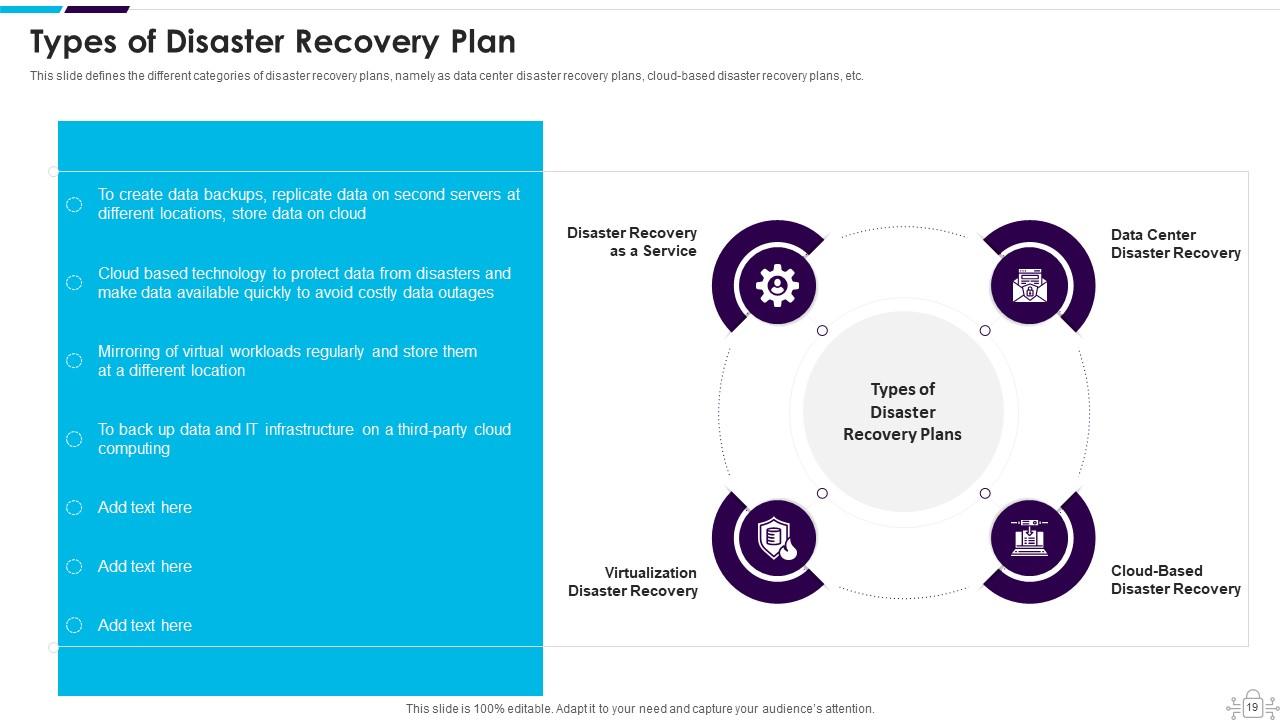
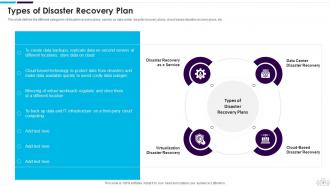
Slide 19: This slide defines the different categories of disaster recovery plans, namely as data center disaster recovery plans, cloud-based disaster recovery plans, etc.
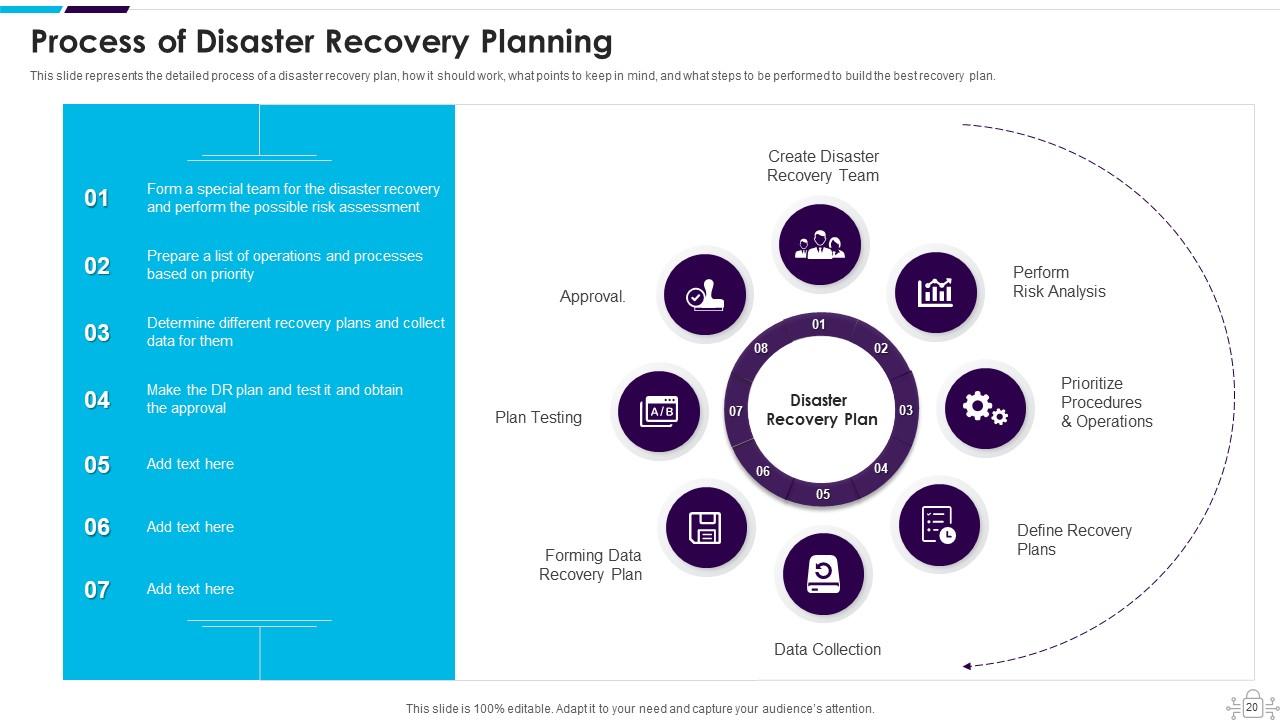
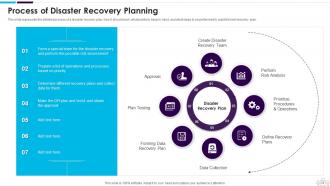
Slide 20: This slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, etc.
Slide 21: This slide defines the operational security element of Network security.
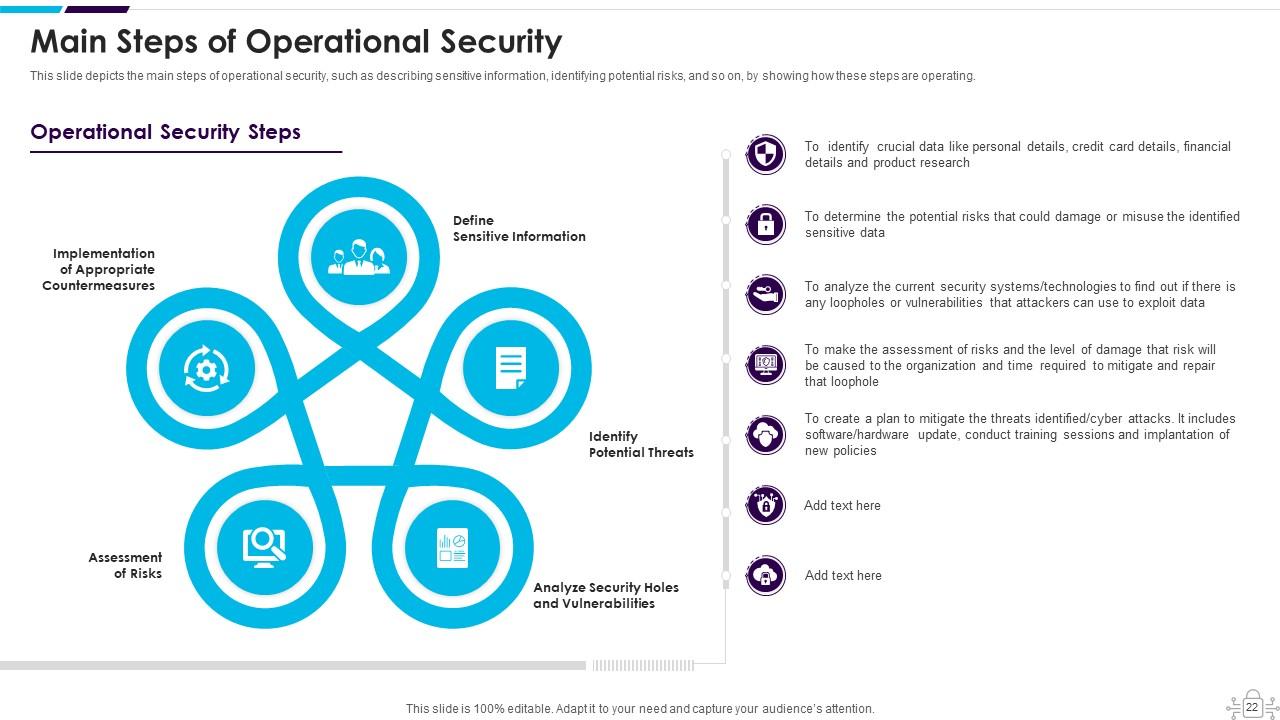
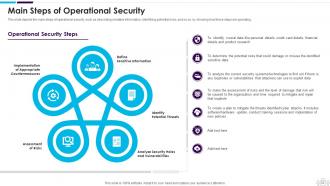
Slide 22: This slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, etc.
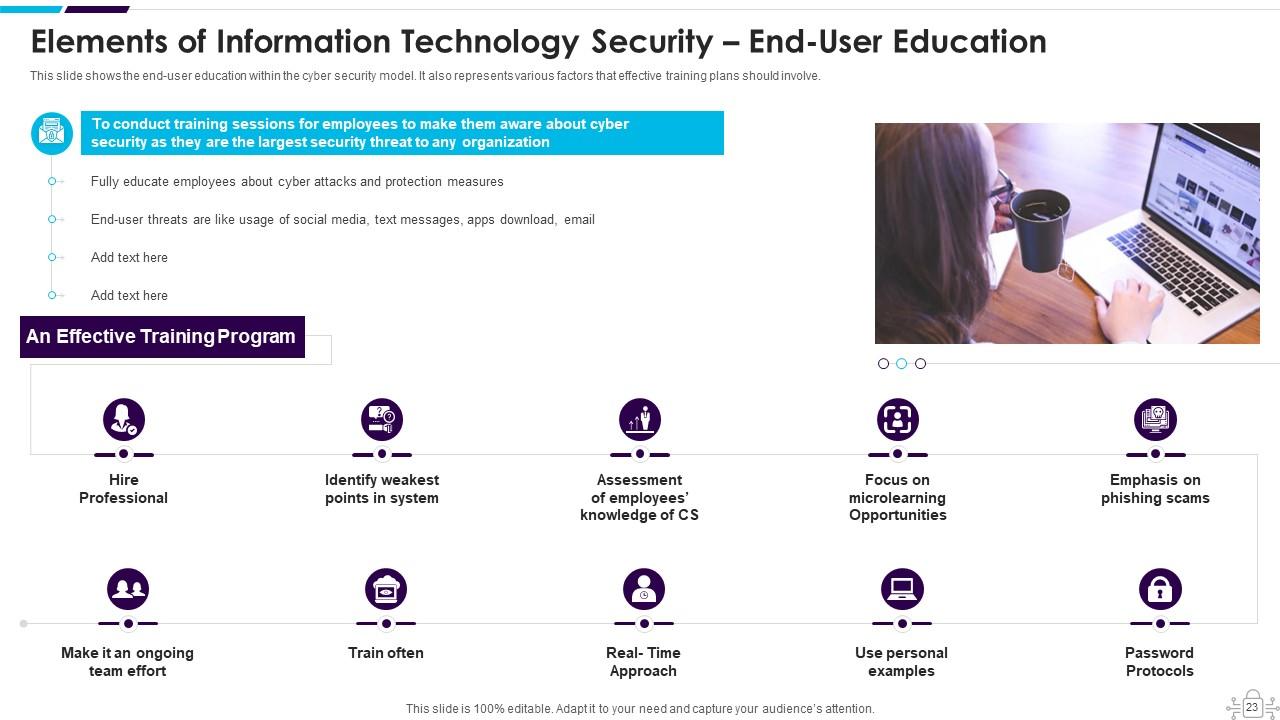
Slide 23: This slide presents the end-user education within the Cyber security model.
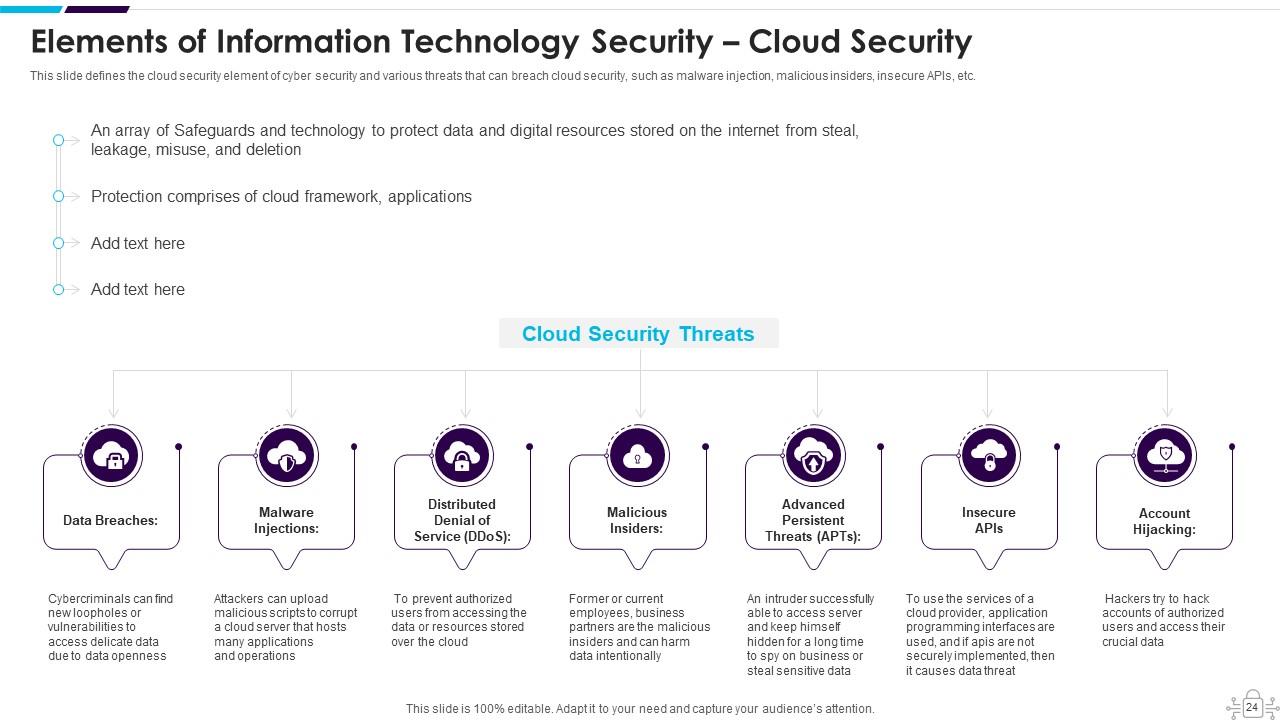
Slide 24: This slide shows Elements of Network Security – Cloud Security.
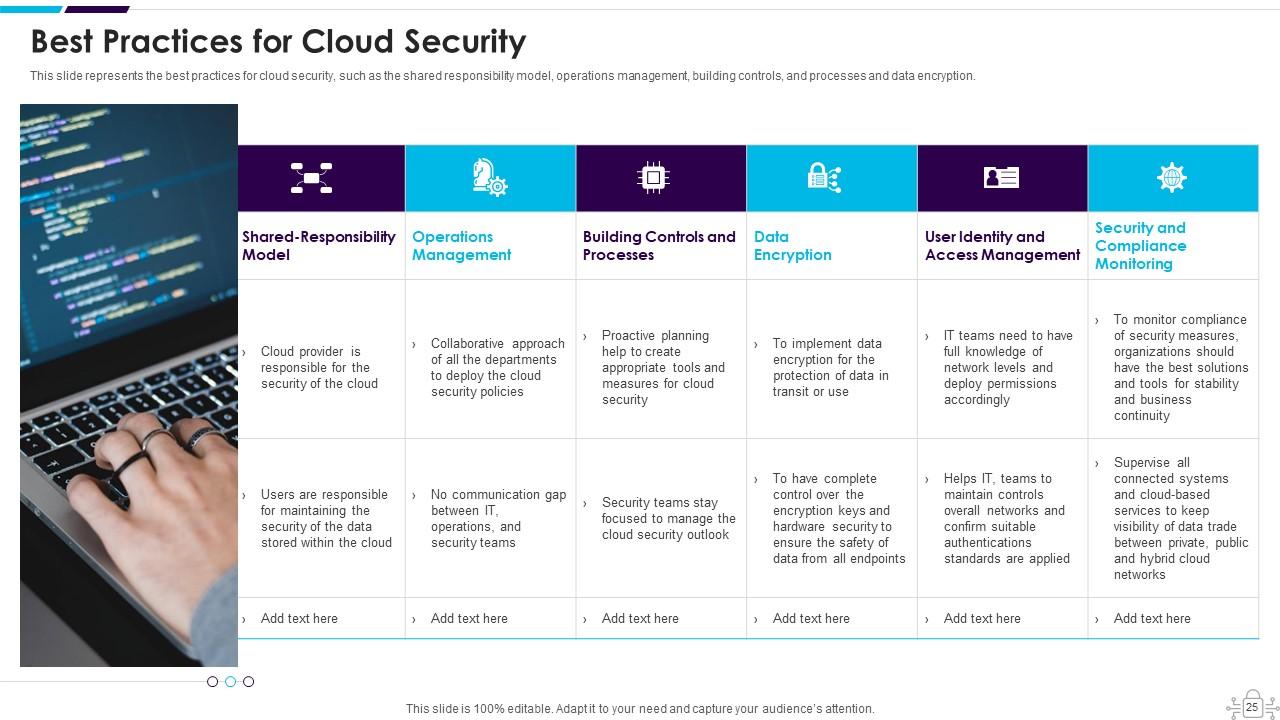
Slide 25: This slide represents the best practices for cloud security, such as the shared responsibility model, operations management, etc.
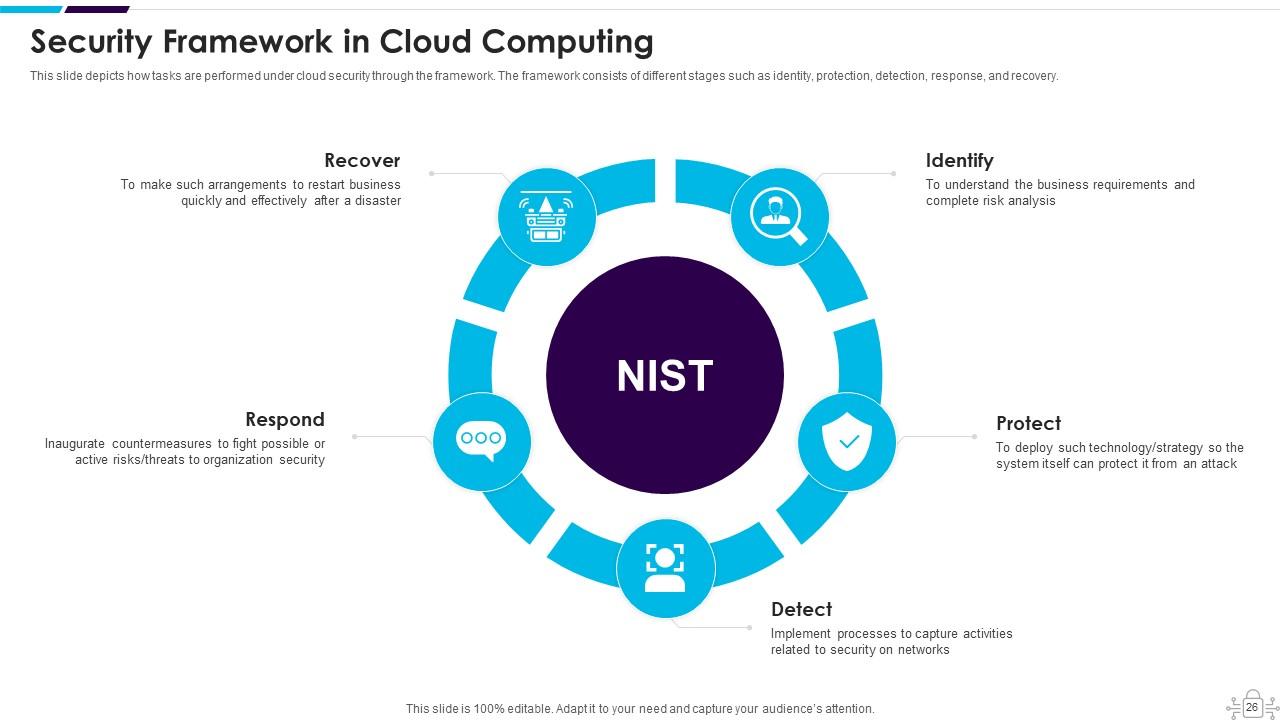
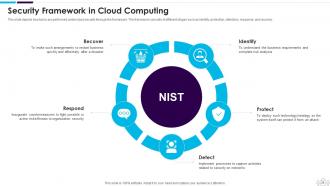
Slide 26: This slide shows Security Framework in Cloud Computing.
Slide 27: This slide highlights title for topics that are to be covered next in the template.
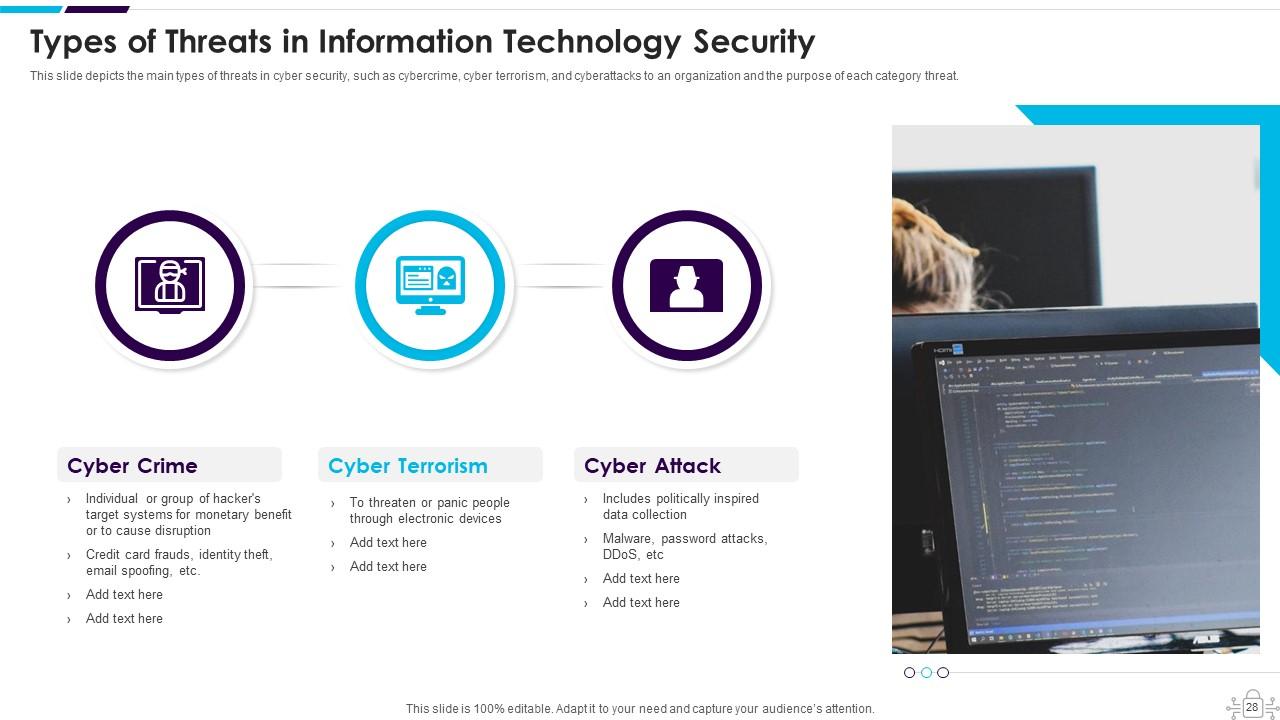
Slide 28: This slide presents the main types of threats in Cyber security, such as cybercrime, cyber terrorism, etc.
Slide 29: This slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, etc.
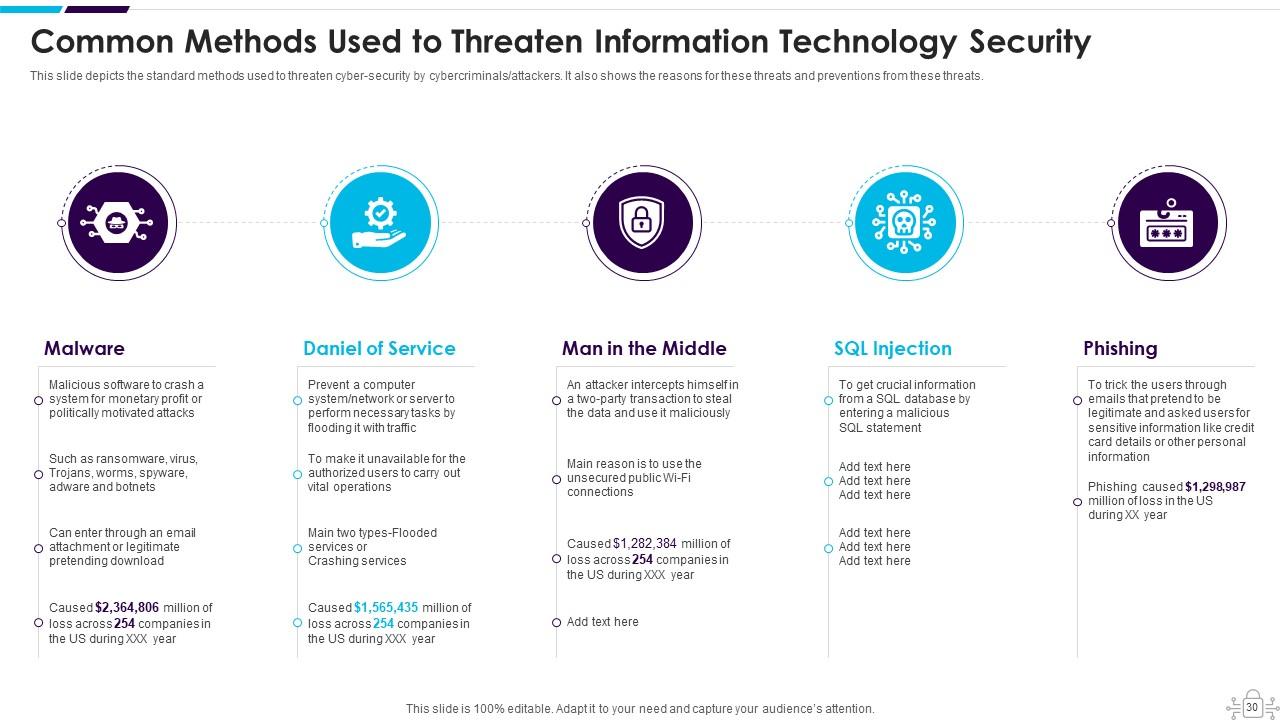
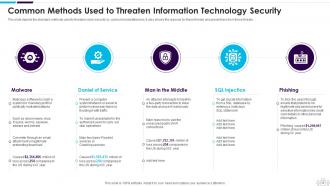
Slide 30: This slide displays Common Methods Used to Threaten Network-Security.
Slide 31: This slide highlights title for topics that are to be covered next in the template.
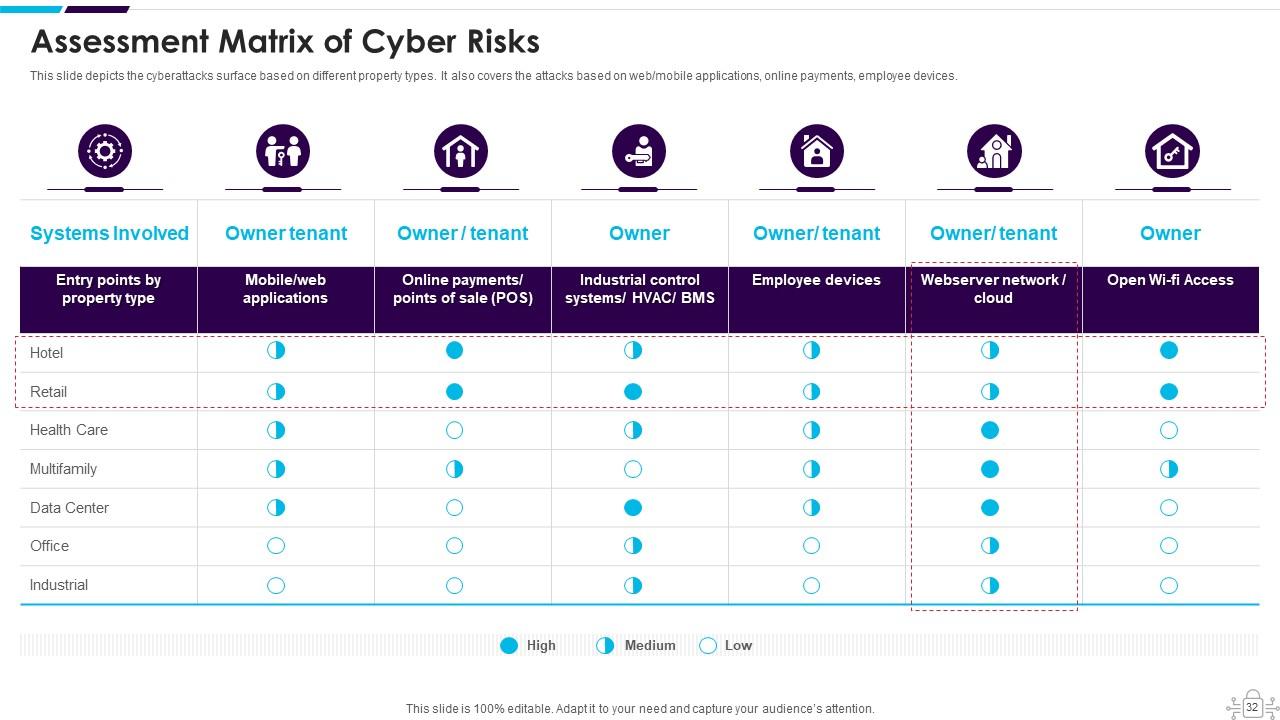
Slide 32: This slide depicts the cyberattacks surface based on different property types.
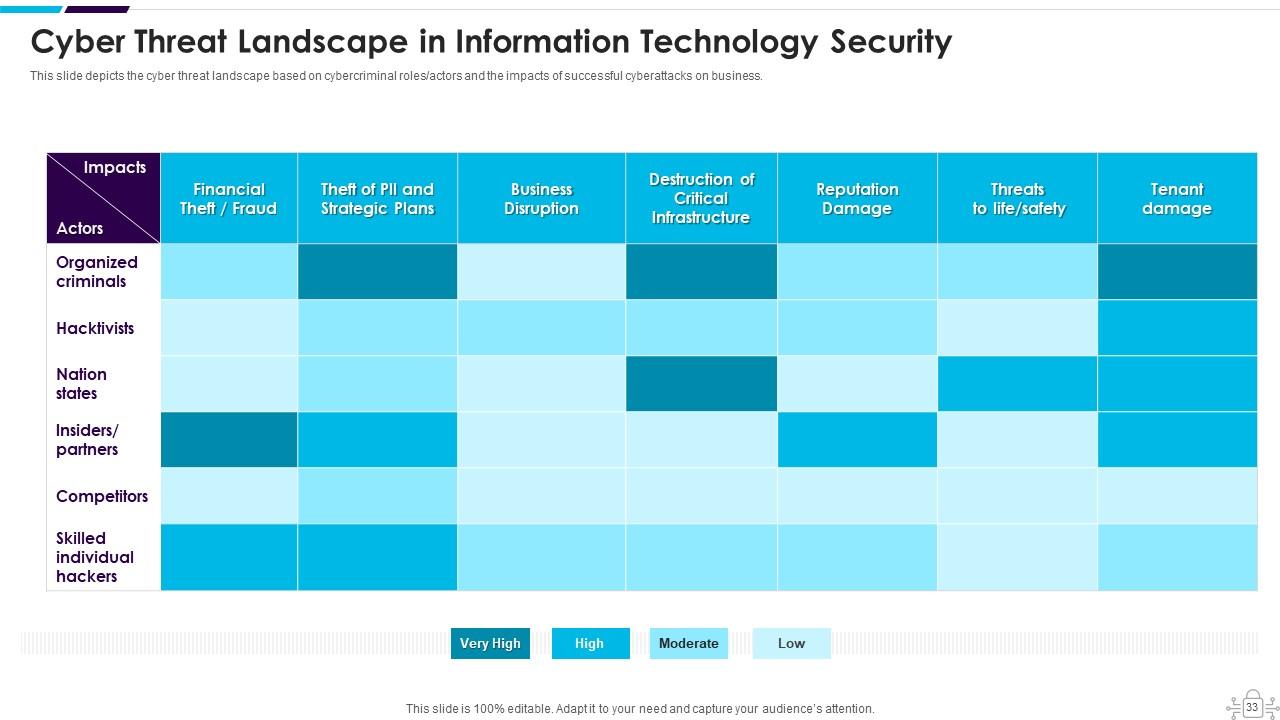
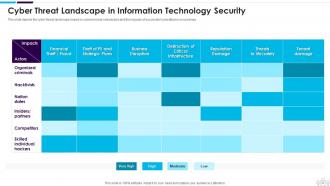
Slide 33: This slide presents Cyber Threat Landscape in Data Security.
Slide 34: This slide highlights title for topics that are to be covered next in the template.
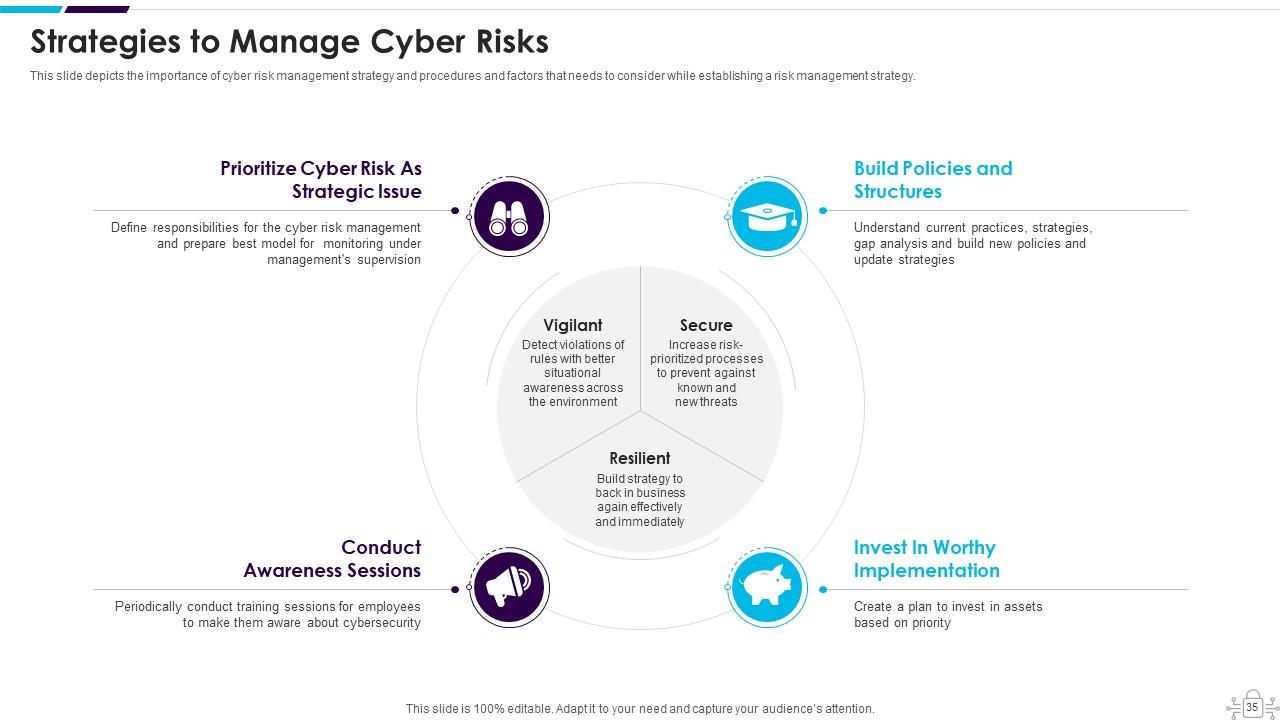
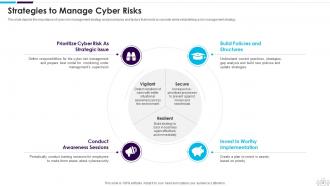
Slide 35: This slide depicts the importance of cyber risk management strategy and procedures.
Slide 36: This slide shows Cyber Safety Tips - Protection Against Cyberattacks.
Slide 37: This slide highlights title for topics that are to be covered next in the template.
Slide 38: This slide presents the different benefits of deploying a Network security model in an organization.
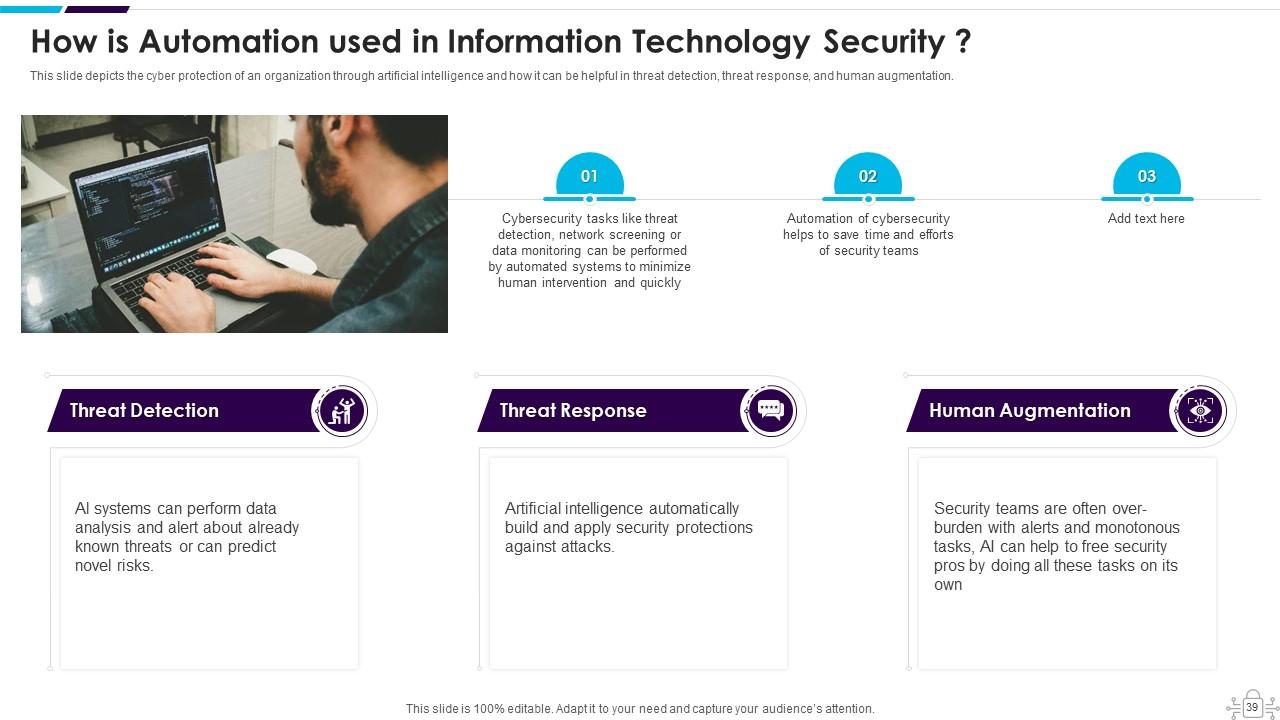
Slide 39: This slide depicts the cyber protection of an organization through artificial intelligence.
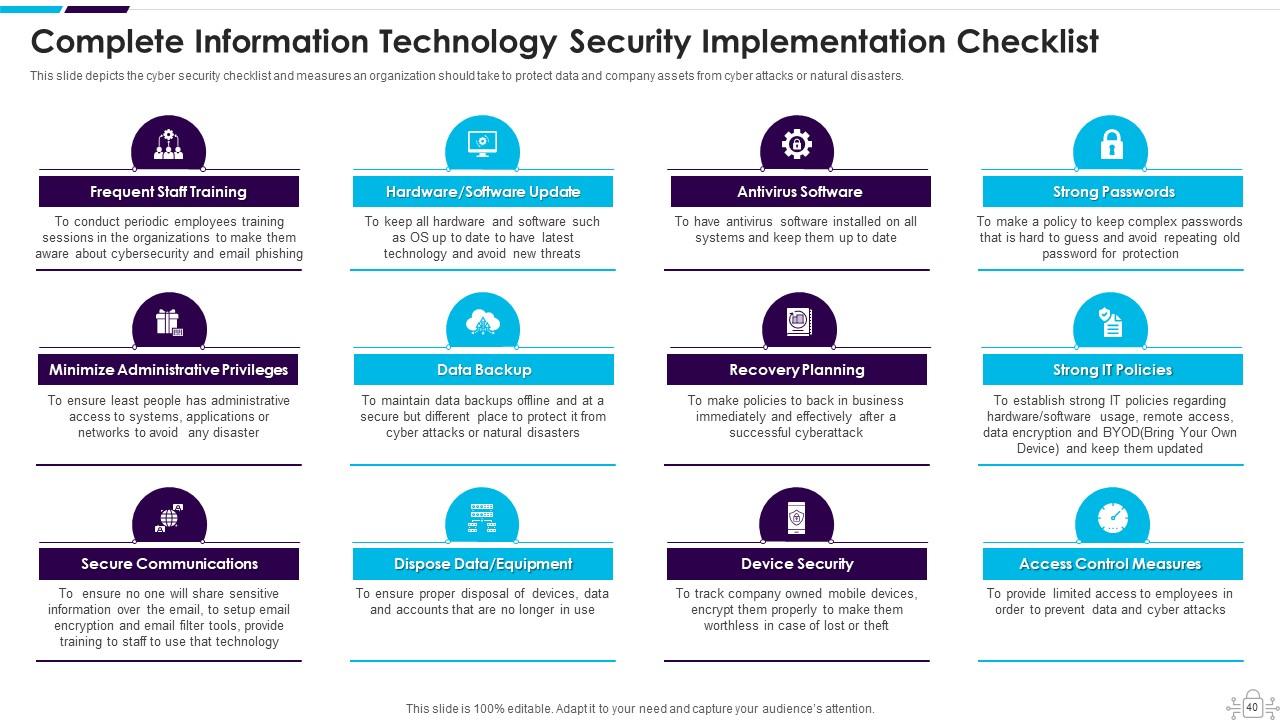
Slide 40: This slide displays Complete Cyber Security Implementation Checklist.
Slide 41: This slide highlights title for topics that are to be covered next in the template.
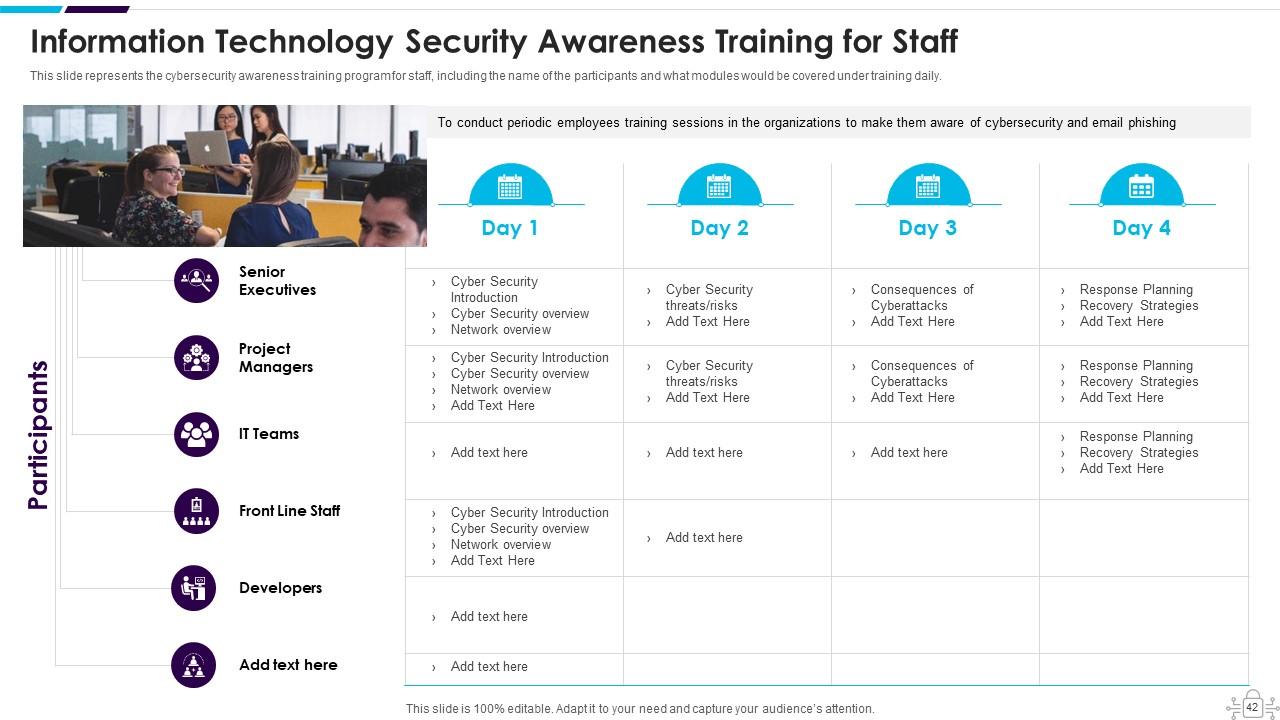
Slide 42: This slide represents the Cyber security awareness training program for staff, including the name of the participants.
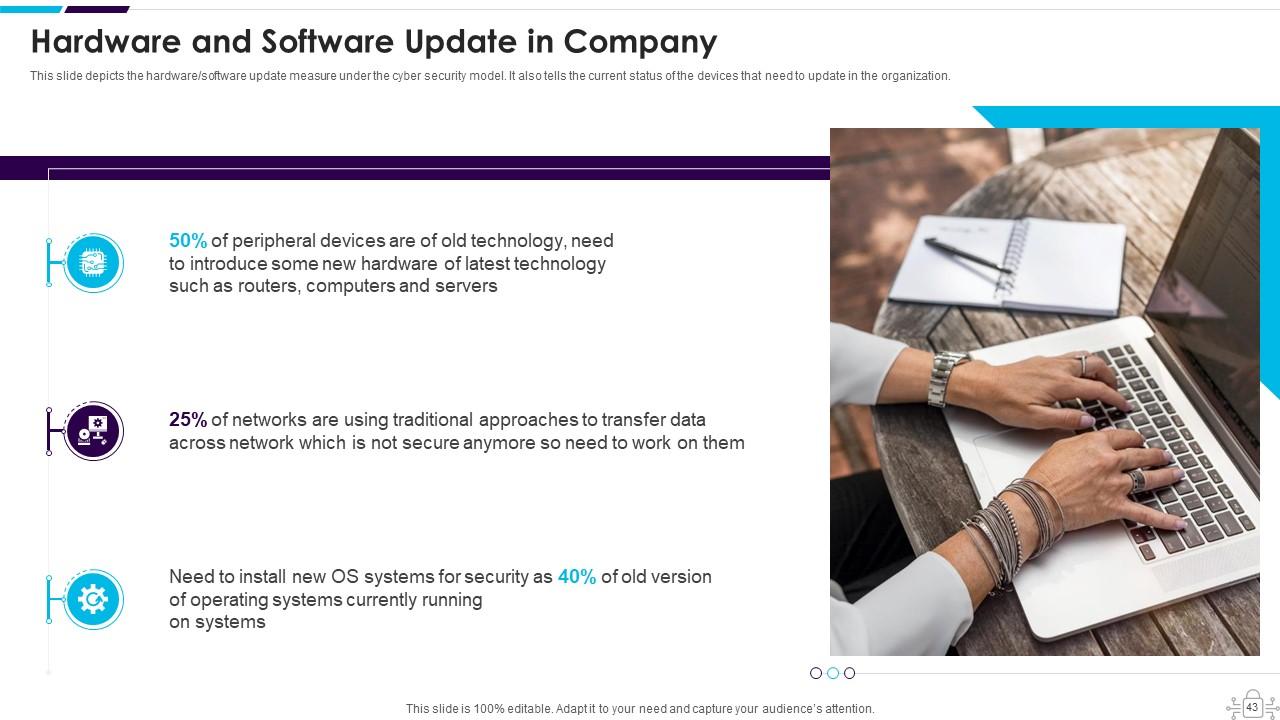
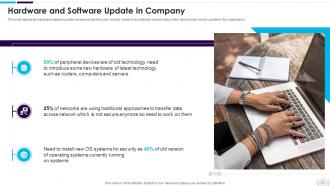
Slide 43: This slide presents Hardware and Software Update in Company.
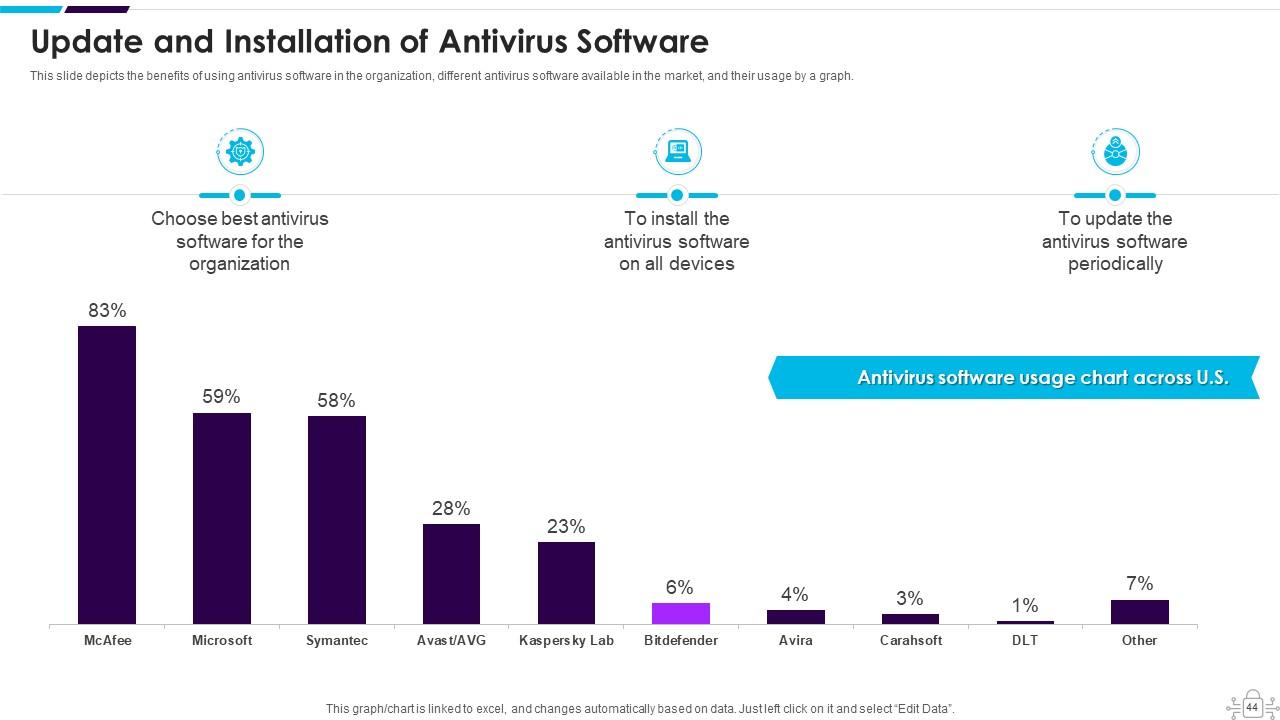
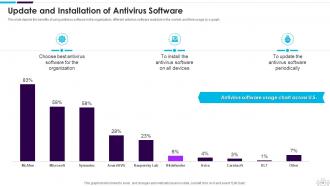
Slide 44: This slide depicts the benefits of using antivirus software in the organization.
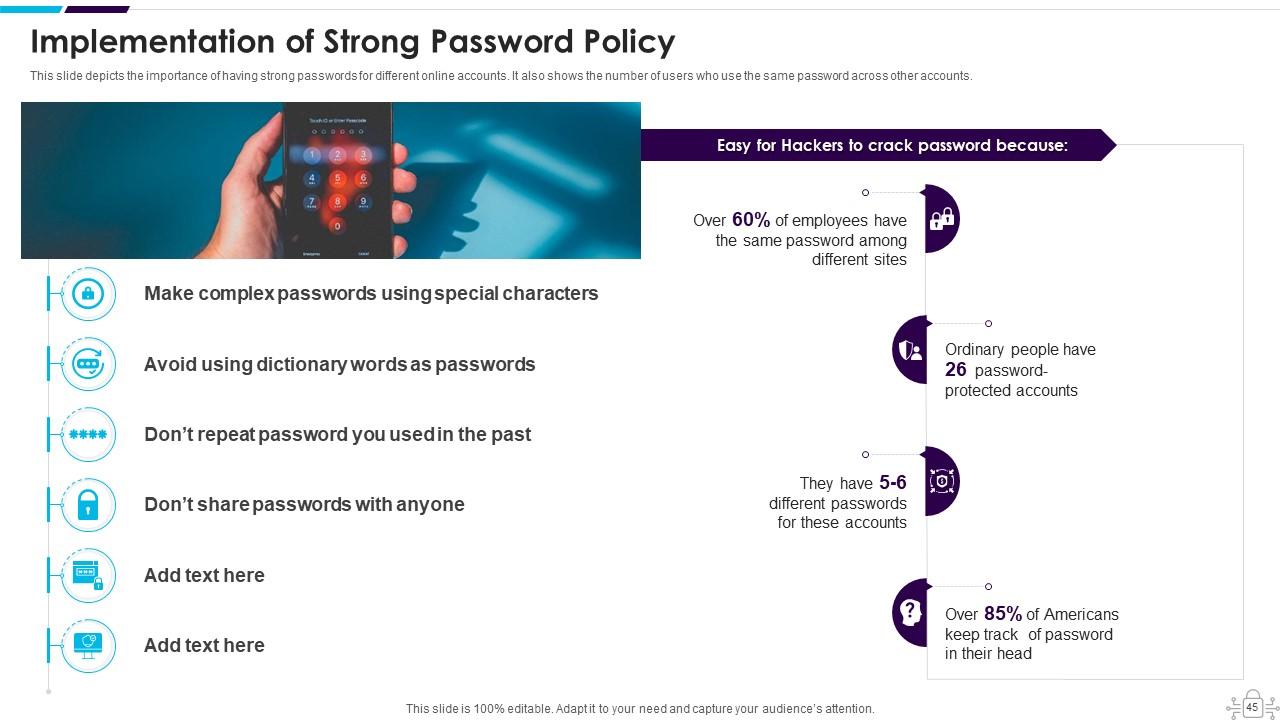
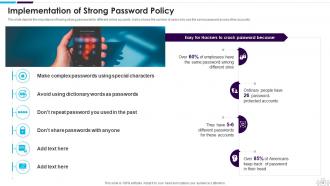
Slide 45: This slide displays the importance of having strong passwords for different online accounts.
Slide 46: This slide shows the importance of minimizing the administrative and staff privilege by showing its benefits for the company.
Slide 47: This slide displays Prepare Data Backup for Sensitive Information.
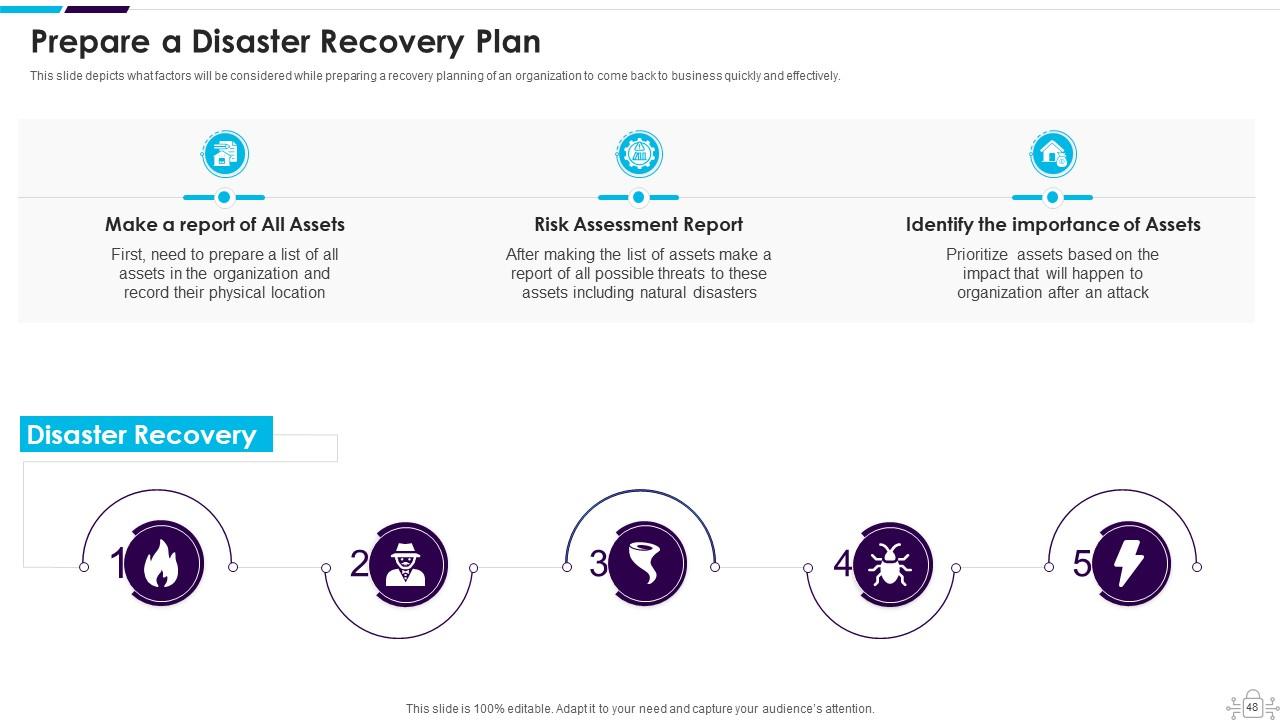
Slide 48: This slide depicts what factors will be considered while preparing a recovery planning of an organization.
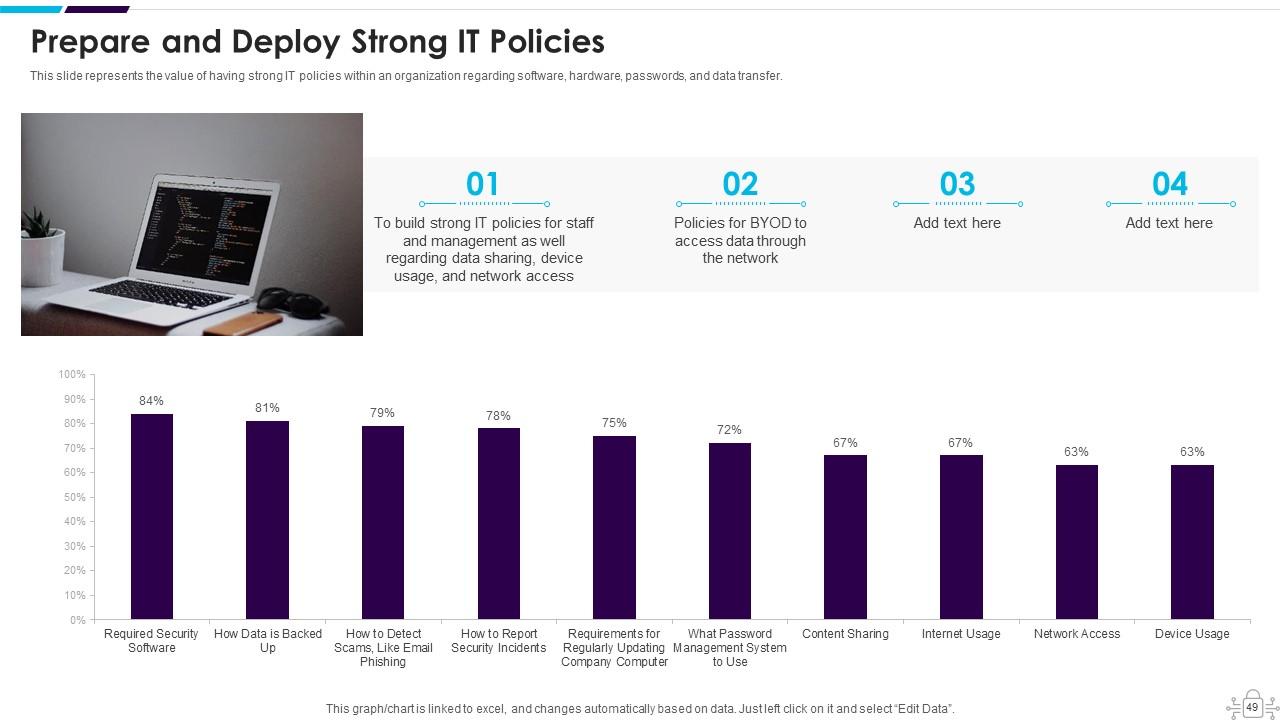
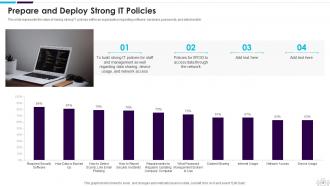
Slide 49: This slide represents the value of having strong IT policies within an organization.
Slide 50: This slide depicts secure communication within an organization and the technology to encrypt emails.
Slide 51: This slide displays the importance of disposal of the data and equipment that is not in use anymore.
Slide 52: This slide depicts that the security of employees’ hardware or devices is also essential while applying the cyber security model.
Slide 53: This slide presents Define Access Control Measures for Employees.
Slide 54: This slide highlights title for topics that are to be covered next in the template.
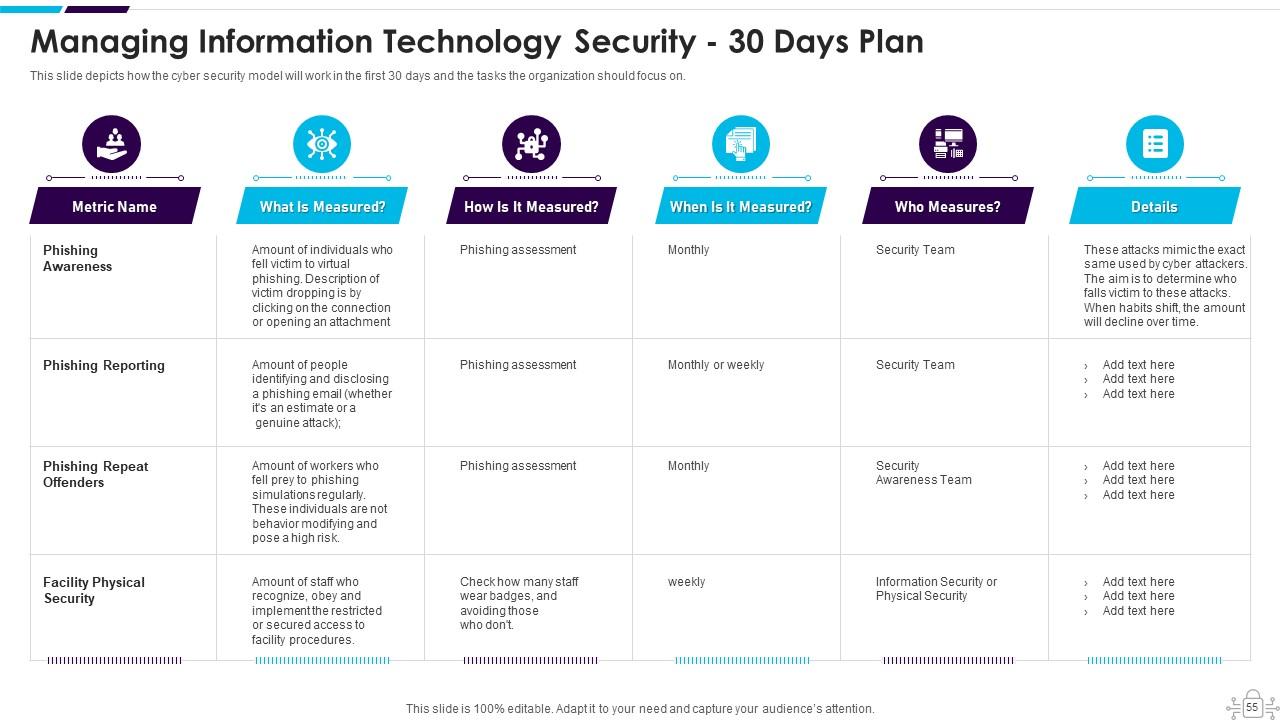
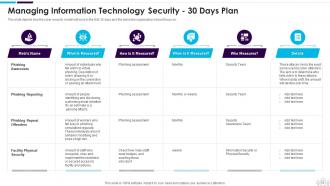
Slide 55: This slide depicts how the Cyber security model will work in the first 30 days and the tasks the organization should focus on.
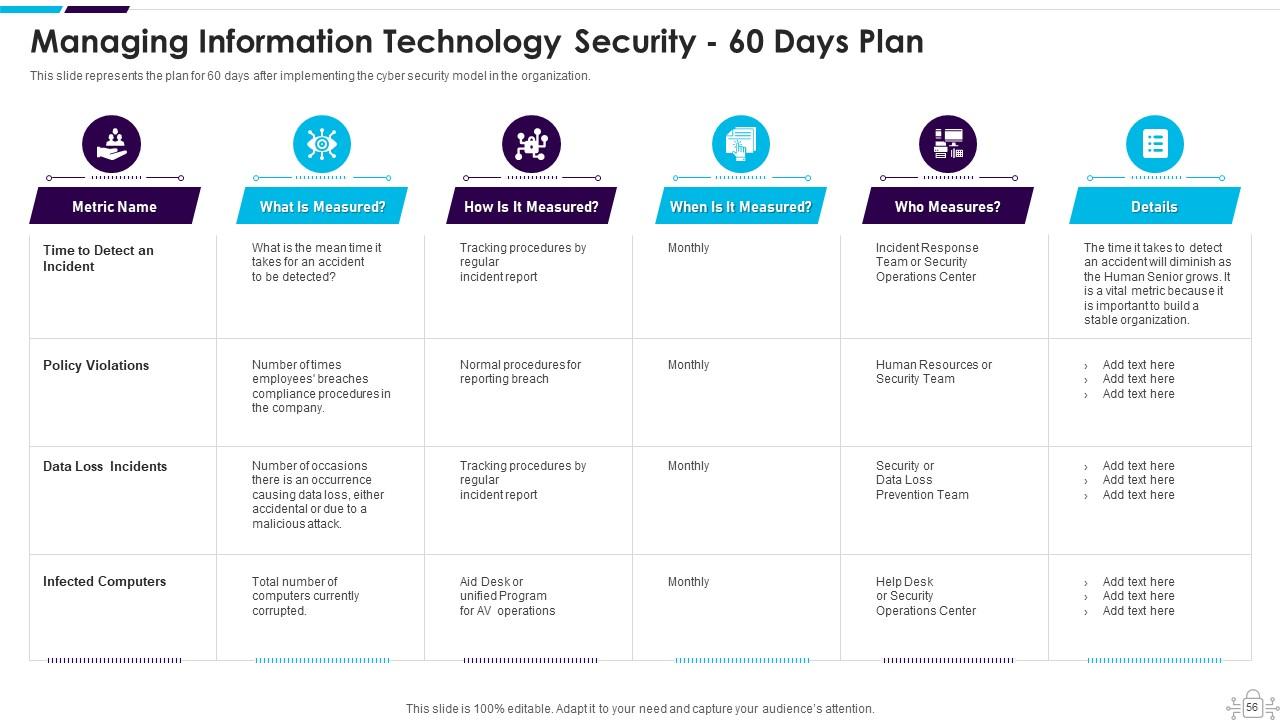
Slide 56: This slide represents the plan for 60 days after implementing the Network security model in the organization.
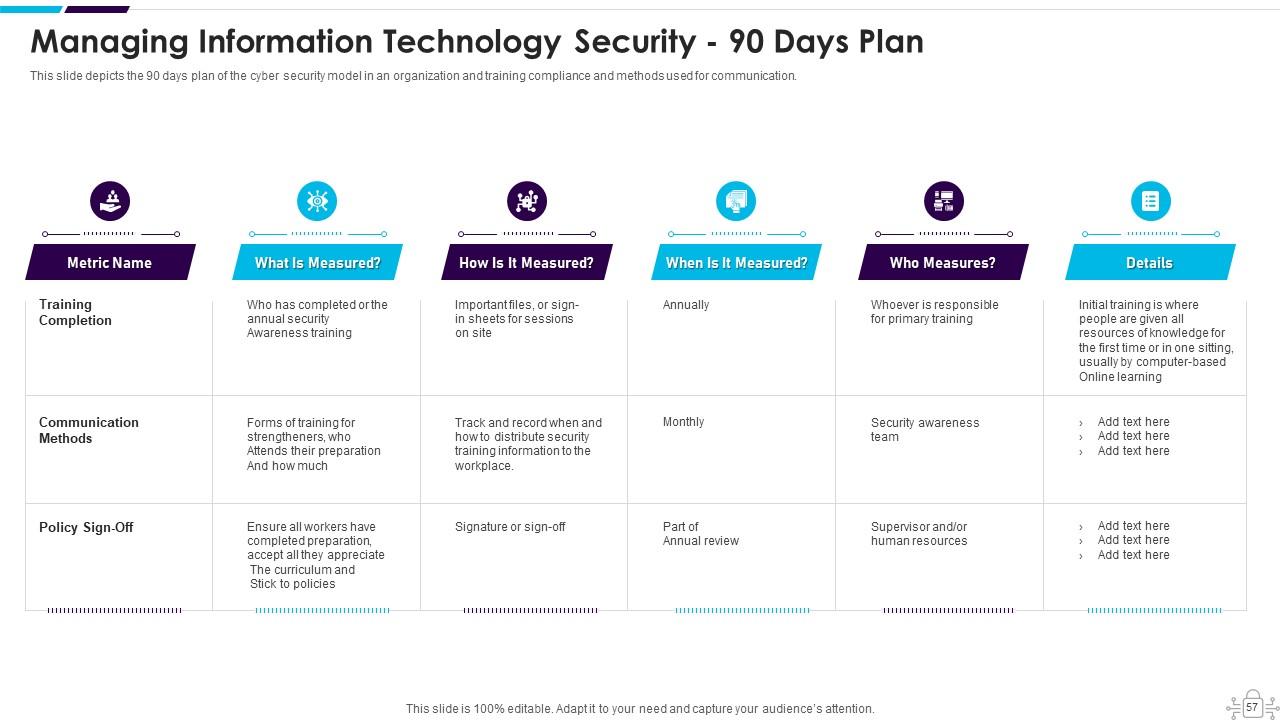
Slide 57: This slide depicts the 90 days plan of the Network security model in an organization and training compliance.
Slide 58: This slide highlights title for topics that are to be covered next in the template.
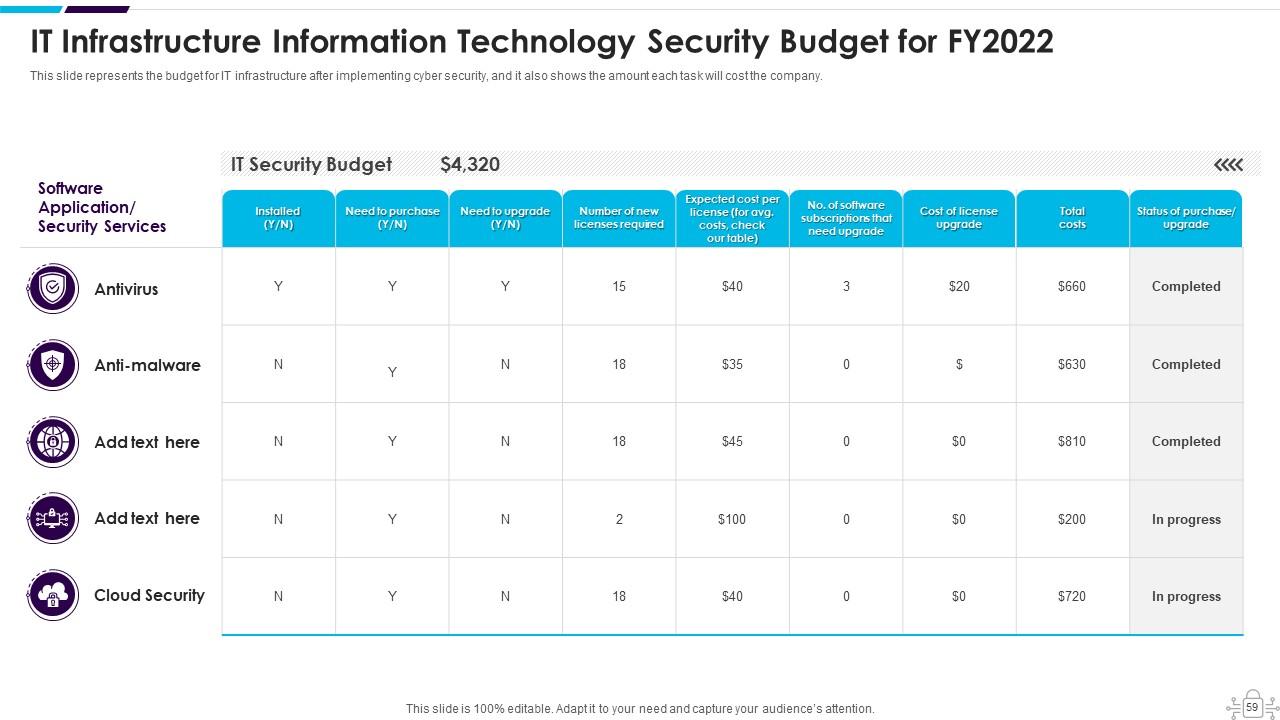
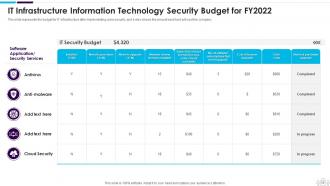
Slide 59: This slide represents the budget for IT infrastructure after implementing data security.
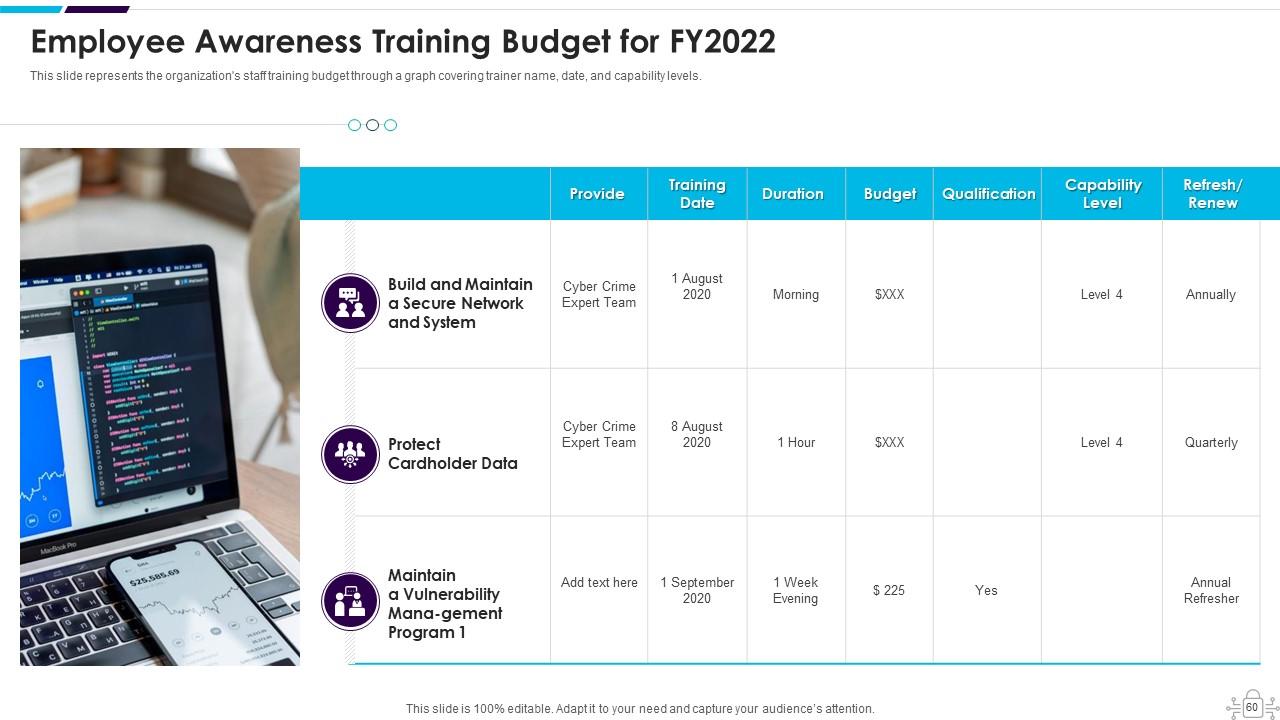
Slide 60: This slide displays the organization's staff training budget through a graph covering trainer name, date, and capability levels.
Slide 61: This slide highlights title for topics that are to be covered next in the template.
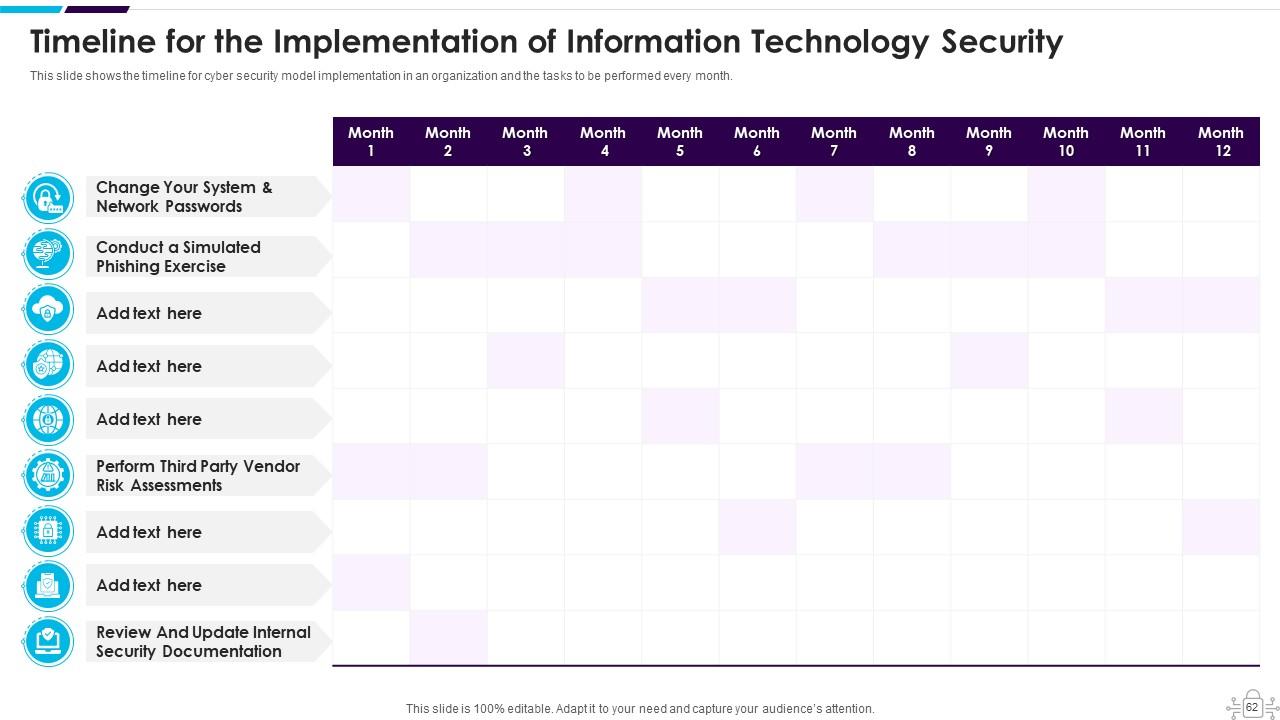
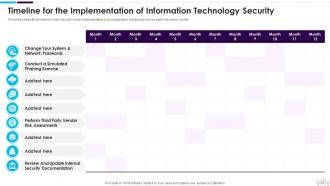
Slide 62: This slide displays Timeline for the Implementation of Network Security.
Slide 63: This slide depicts the Cyber security training roadmap.
Slide 64: This slide highlights title for topics that are to be covered next in the template.
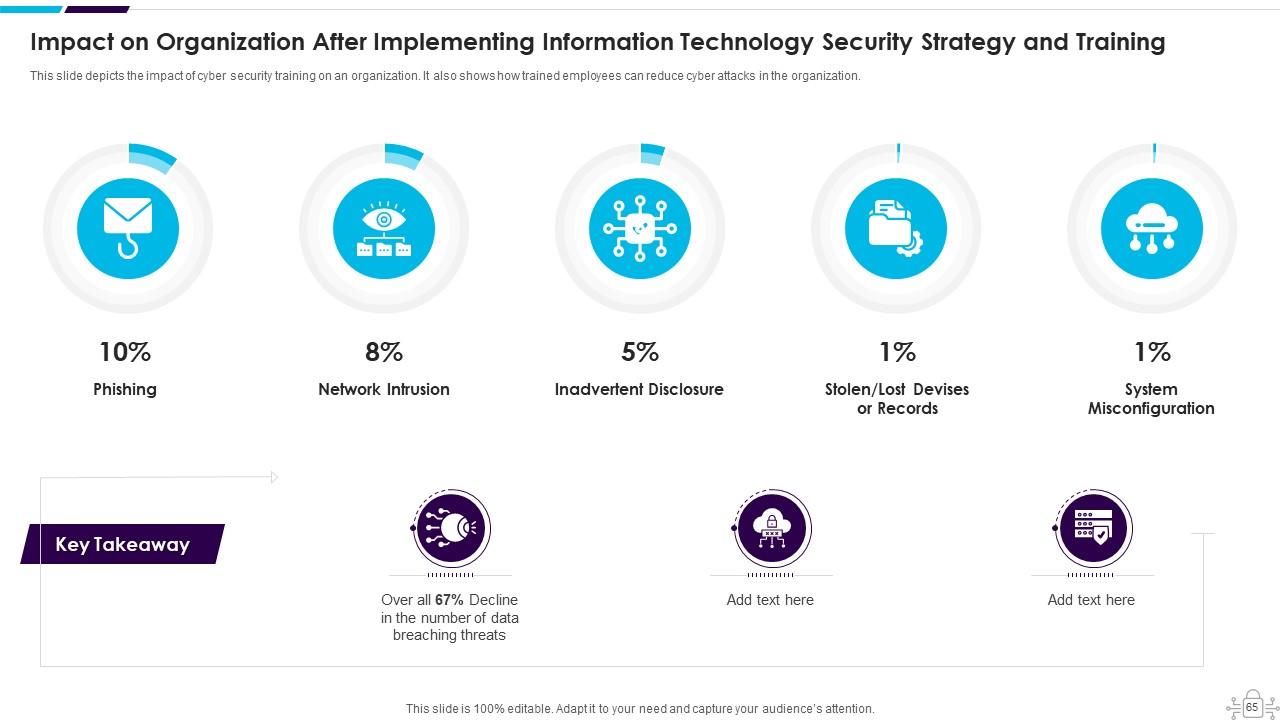
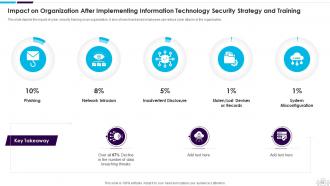
Slide 65: This slide displays Impact on Organization After Implementing Cyber Security Strategy and Training.
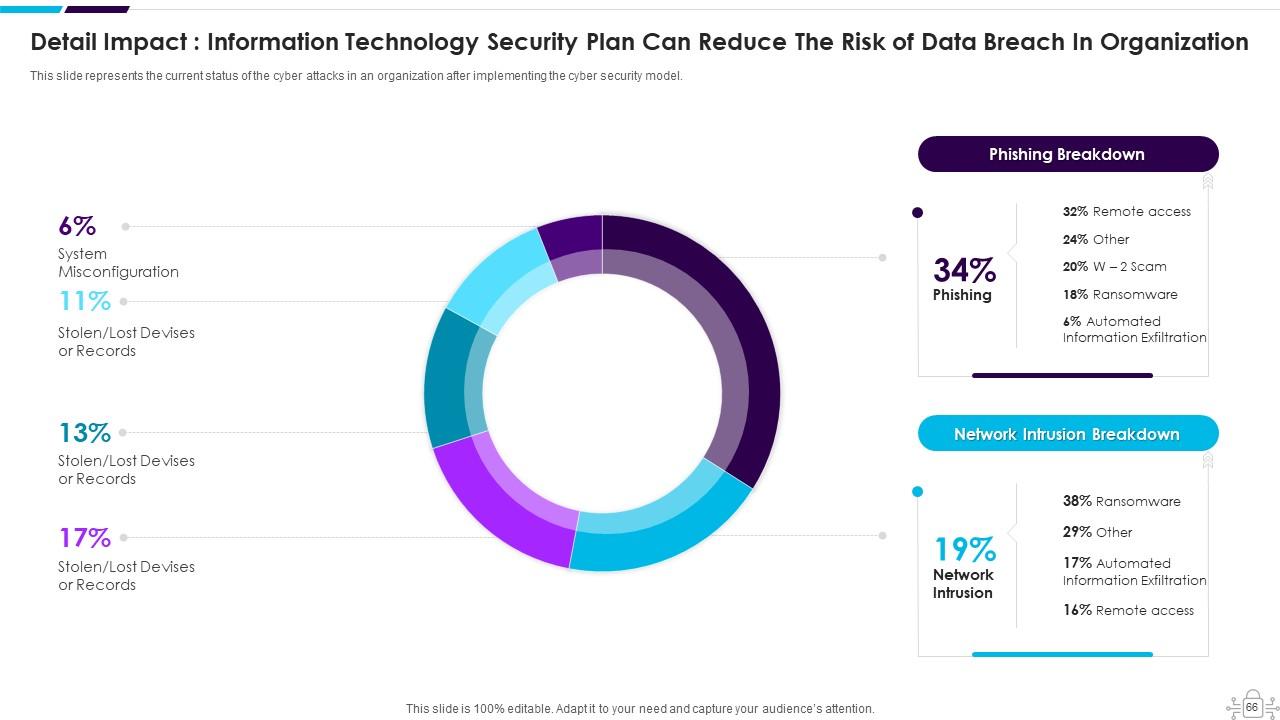
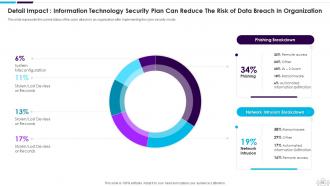
Slide 66: This slide represents the current status of the cyber attacks in an organization after implementing the cyber security model.
Slide 67: This slide highlights title for topics that are to be covered next in the template.
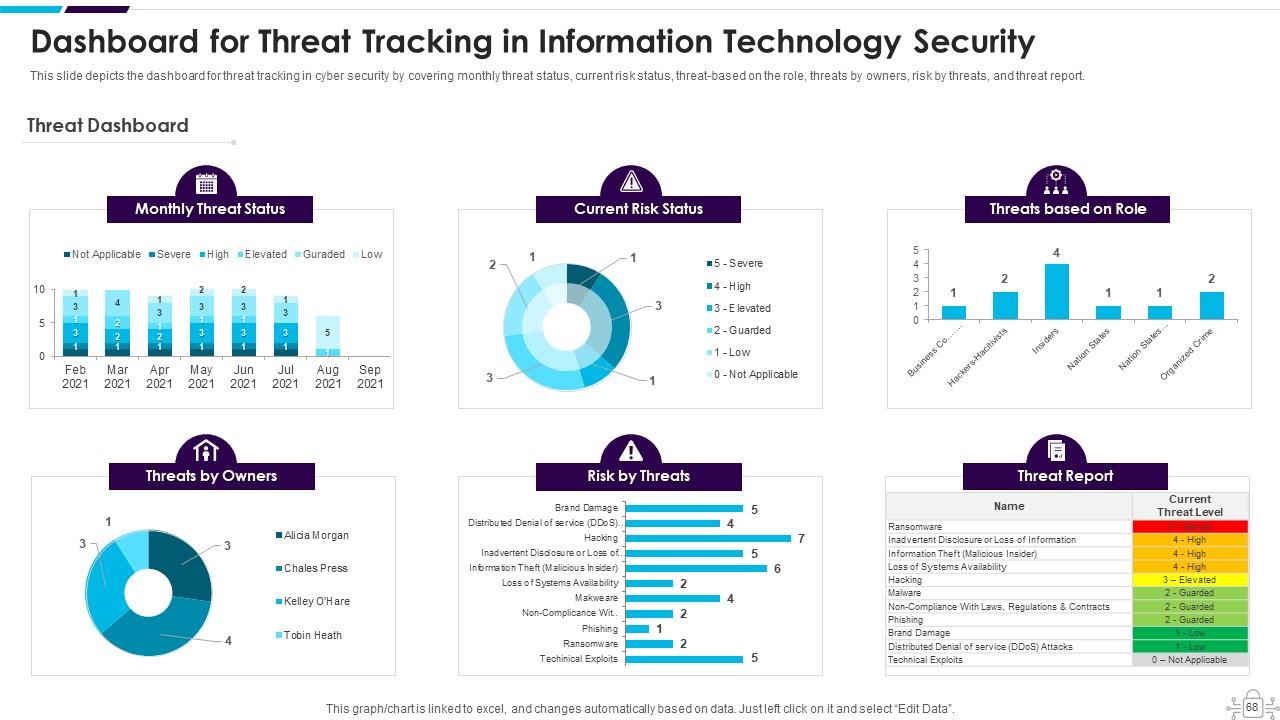
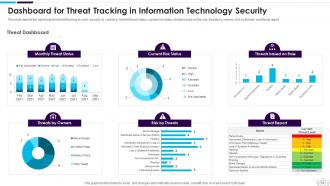
Slide 68: This slide presents Dashboard for Threat Tracking in Network Security.
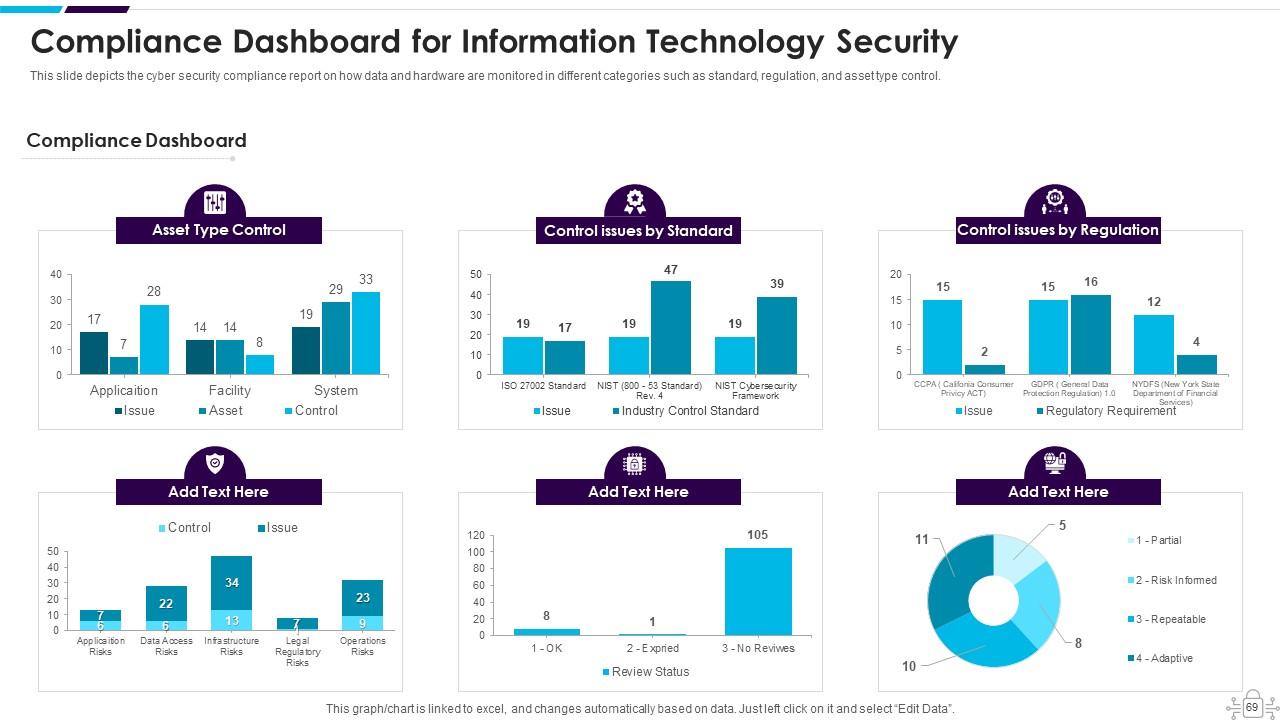
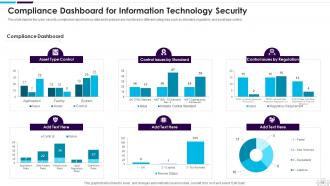
Slide 69: This slide depicts the Cyber security compliance report on how data and hardware are monitored in different categories.
Slide 70: This slide displays Icons for Information Technology Security.
Slide 71: This slide is titled as Additional Slides for moving forward.
Slide 72: This is About Us slide to show company specifications etc.
Slide 73: This is Our Team slide with names and designation.
Slide 74: This is Our Mission slide with related imagery and text.
Slide 75: This slide shows Post It Notes. Post your important notes here.
Slide 76: This slide presents Roadmap with additional textboxes.
Slide 77: This slide provides 30 60 90 Days Plan with text boxes.
Slide 78: This slide shows Circular Diagram with additional textboxes.
Slide 79: This is Our Goal slide. State your firm's goals here.
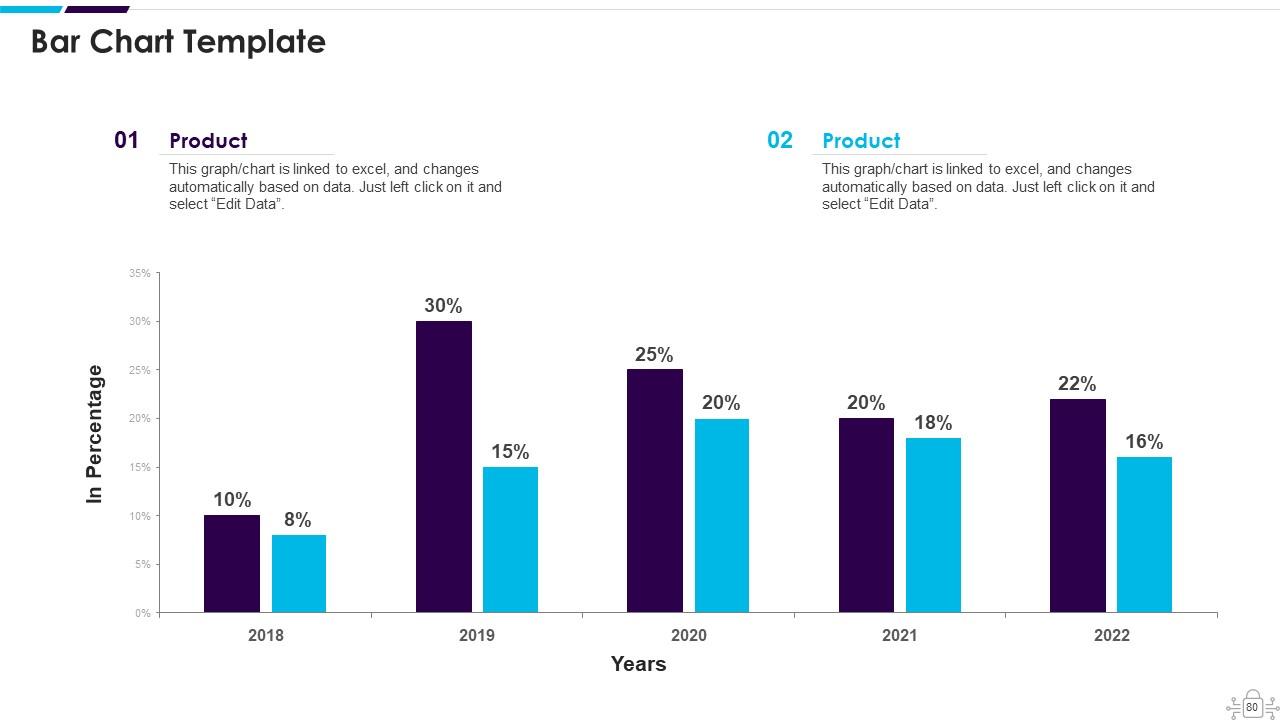
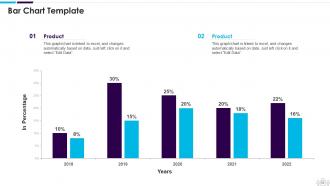
Slide 80: This slide presents Bar chart with two products comparison.
Slide 81: This is a Thank You slide with address, contact numbers and email address.
Information Technology Security Powerpoint Presentation Slides with all 86 slides:
Use our Information Technology Security Powerpoint Presentation Slides to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
FAQs
Cybersecurity refers to the practice of protecting computer systems, networks, and sensitive information from unauthorized access, use, theft, damage, or disruption. It helps prevent data breaches by using various methods and techniques, including encryption, firewalls, antivirus software, and intrusion detection systems.
Cyber security is important in different sectors because it helps protect sensitive information, prevent data breaches, ensure business continuity, avoid financial losses, maintain customer trust, and comply with legal regulations and industry standards.
The different elements of cyber security include application security, network security, information security, disaster recovery planning, operational security, cloud security, and end-user education.
Disaster recovery planning is important in cyber security because it helps organizations prepare for and respond to unexpected events that could disrupt their operations, damage their reputation, or cause financial losses. It involves creating a plan to recover critical systems, applications, and data in the event of a disaster or cyber attack.
Some common methods used to threaten network security include phishing, malware attacks, denial-of-service attacks, social engineering, and ransomware attacks. Organizations can prevent these threats by implementing strong security policies, conducting regular employee training, and deploying advanced security solutions.
-
Excellent Designs.
-
Easily Understandable slides.