Application Security Implementation Plan Powerpoint Presentation Slides
Explore our Application Security Implementation Plan PowerPoint Presentation, which explains how to implement application security in an organization. It also includes critical challenges, performance analysis, and a project summary of application security. Additionally, this Securing Applications through Encryption PPT demonstrates the various application security approaches, including authorization, authentication, encryption, access control, logging, security testing, etc. This Authentication Template also includes the team structure for implementing application security in IT and the team responsibility assignment matrix for application security. Furthermore, the Implementing Authentication in Application Security Presentation caters to scenarios after implementing application security in organizational networks based on several parameters such as unauthorized access, data breaches, and compliance. Lastly, our Access Control Deck outlines best practices, a checklist, a training budget, a timeline, a roadmap, and the impact of application security. Download our 100 percent editable and customizable template, also compatible with Google Slides.
Explore our Application Security Implementation Plan PowerPoint Presentation, which explains how to implement application s..
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Deliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Application Security Implementation Plan Powerpoint Presentation Slides is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the sixty slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
Slide 1: The slide introduces Application Security Implementation Plan. State Your Company Name and begin.
Slide 2: This is an Agenda slide. State your agendas here.
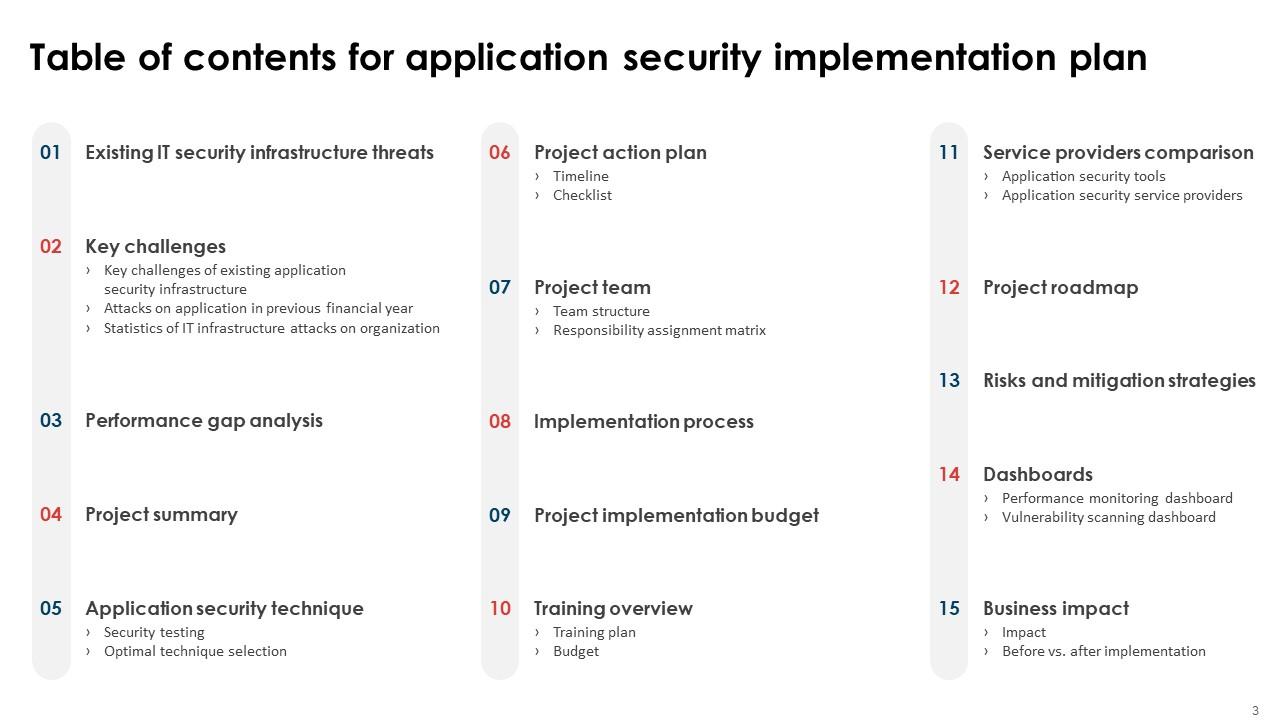
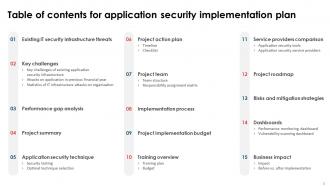
Slide 3: The slide displays Table of contents for the presentation.
Slide 4: The slide continues Table of contents.
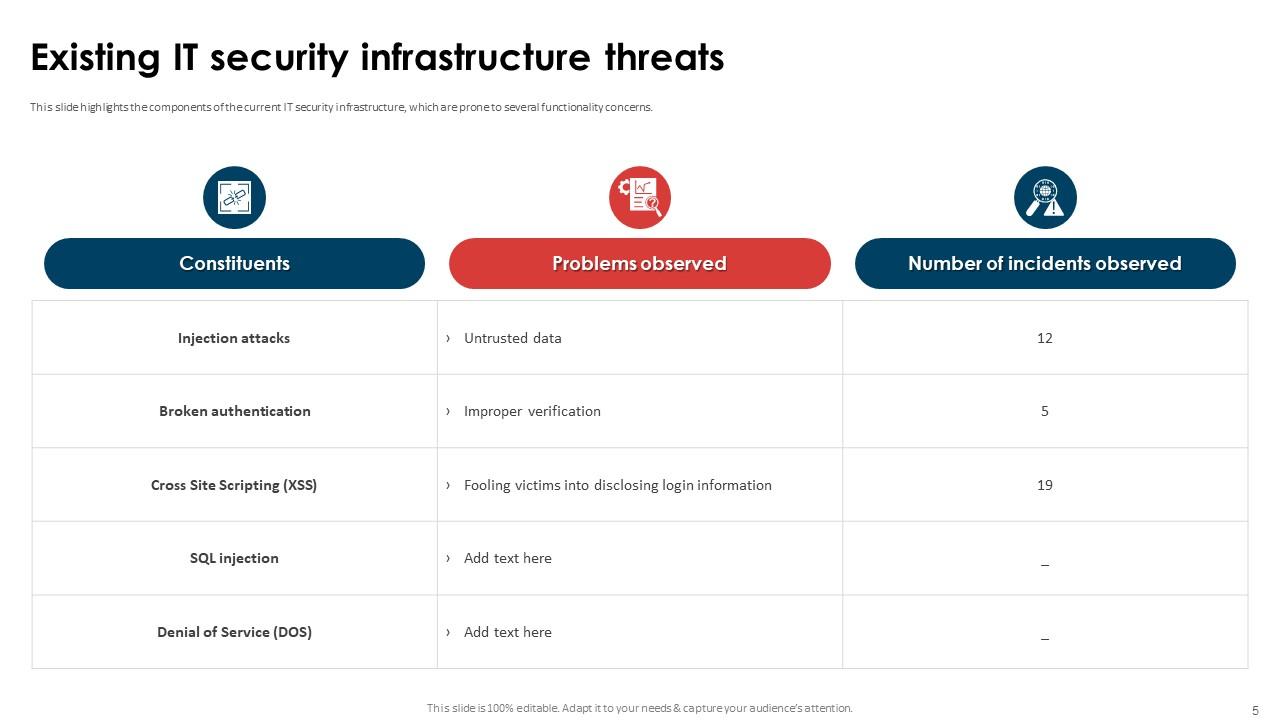
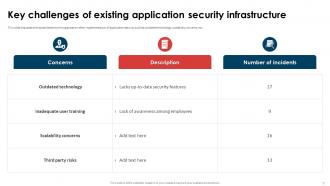
Slide 5: This slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns.
Slide 6: The slide renders Title of contents further.
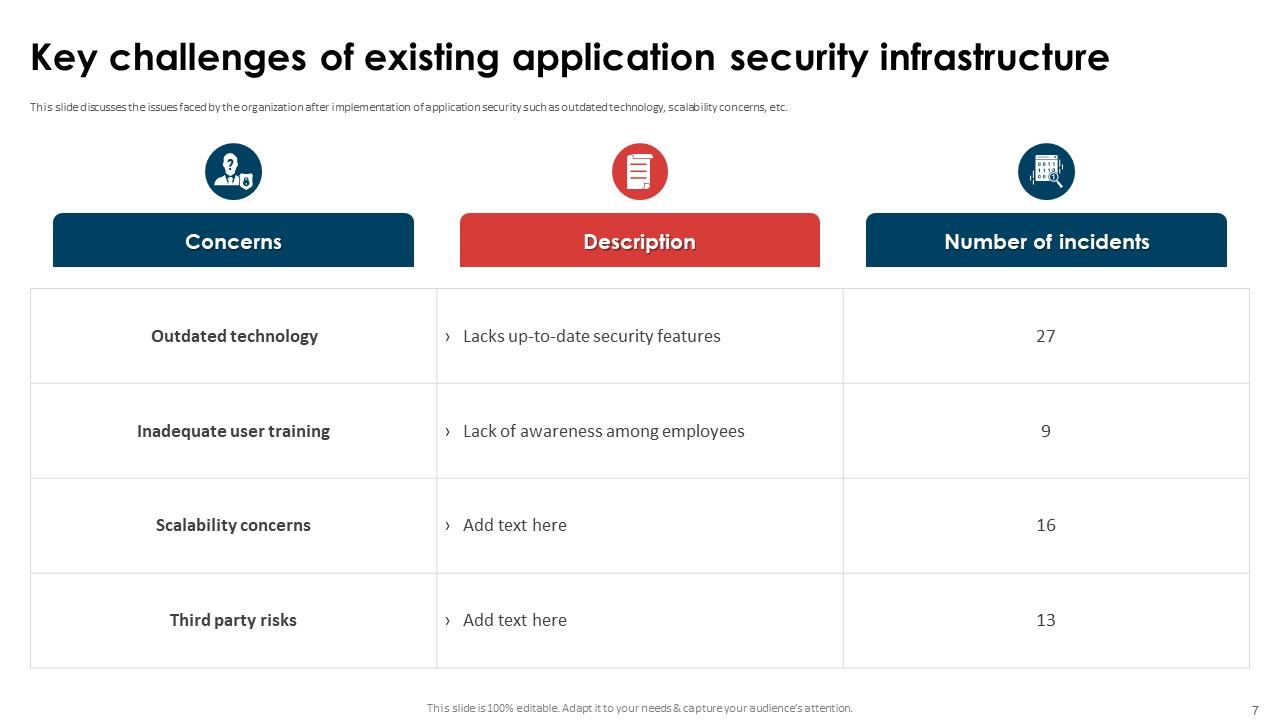
Slide 7: This slide discusses the issues faced by the organization after implementation of application security.
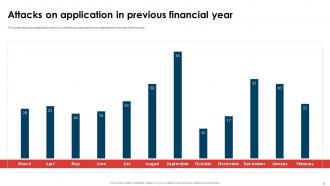
Slide 8: This slide depicts the application security incidents encountered by the organization in the last financial year.
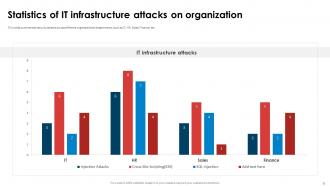
Slide 9: This slide summarizes security attacks across different organizational departments, such as IT, HR, Sales, Finance, etc.
Slide 10: The slide depicts Title of contents which is to be discussed further.
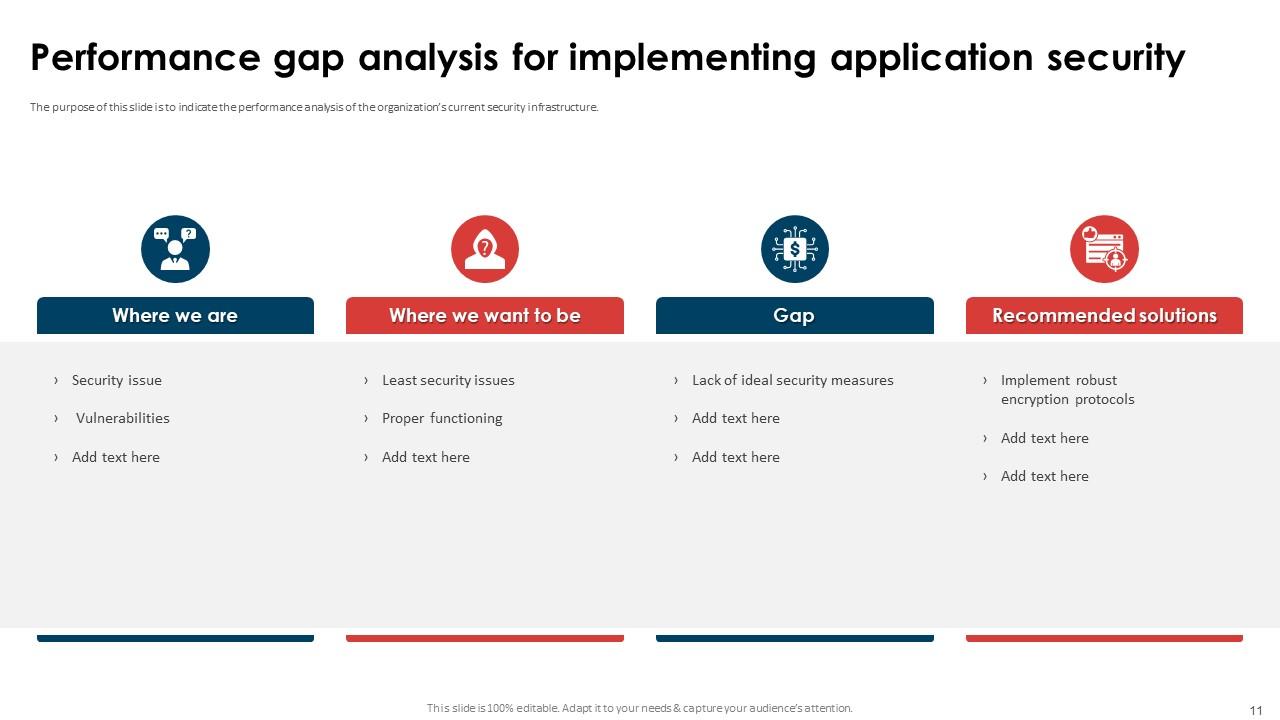
Slide 11: The slide indicates the performance analysis of the organization’s current security infrastructure.
Slide 12: The slide represents Title of contents further.
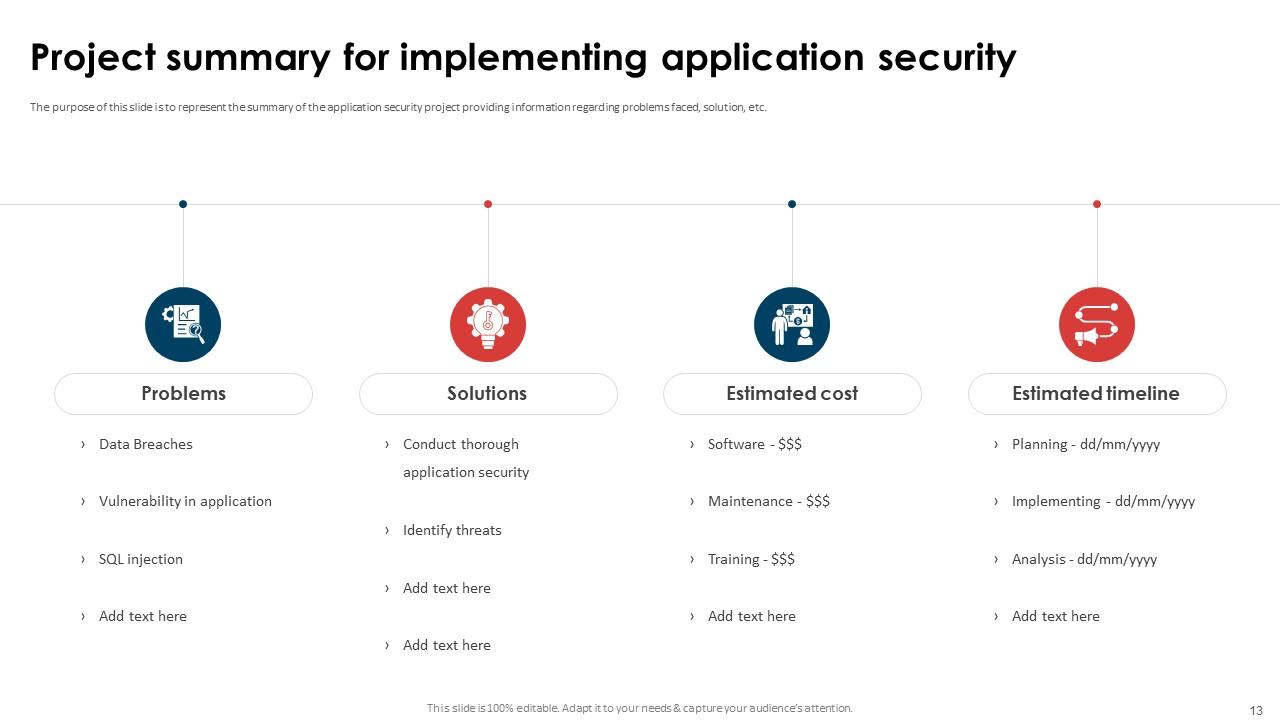
Slide 13: The slide demonstrates the summary of the application security project providing information regarding problems faced, solution, etc.
Slide 14: The slide displays Title of contents further.
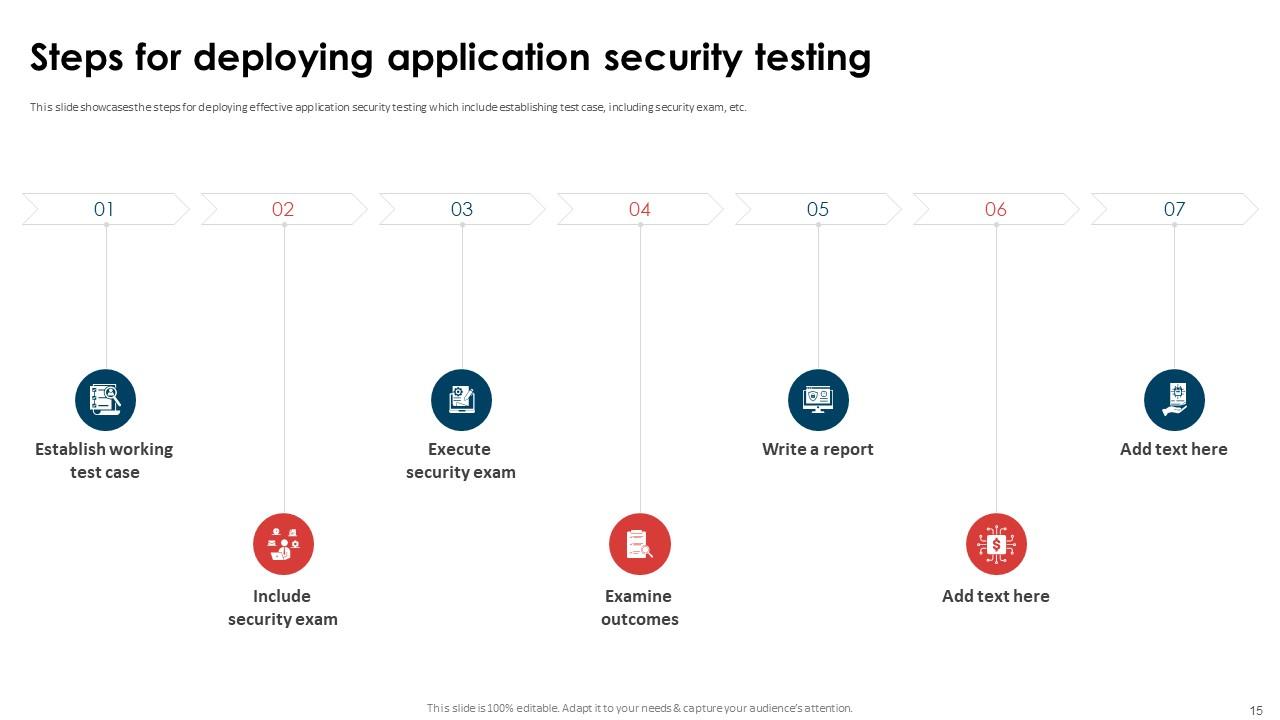
Slide 15: This slide showcases the steps for deploying effective application security testing which include establishing test case, including security exam, etc.
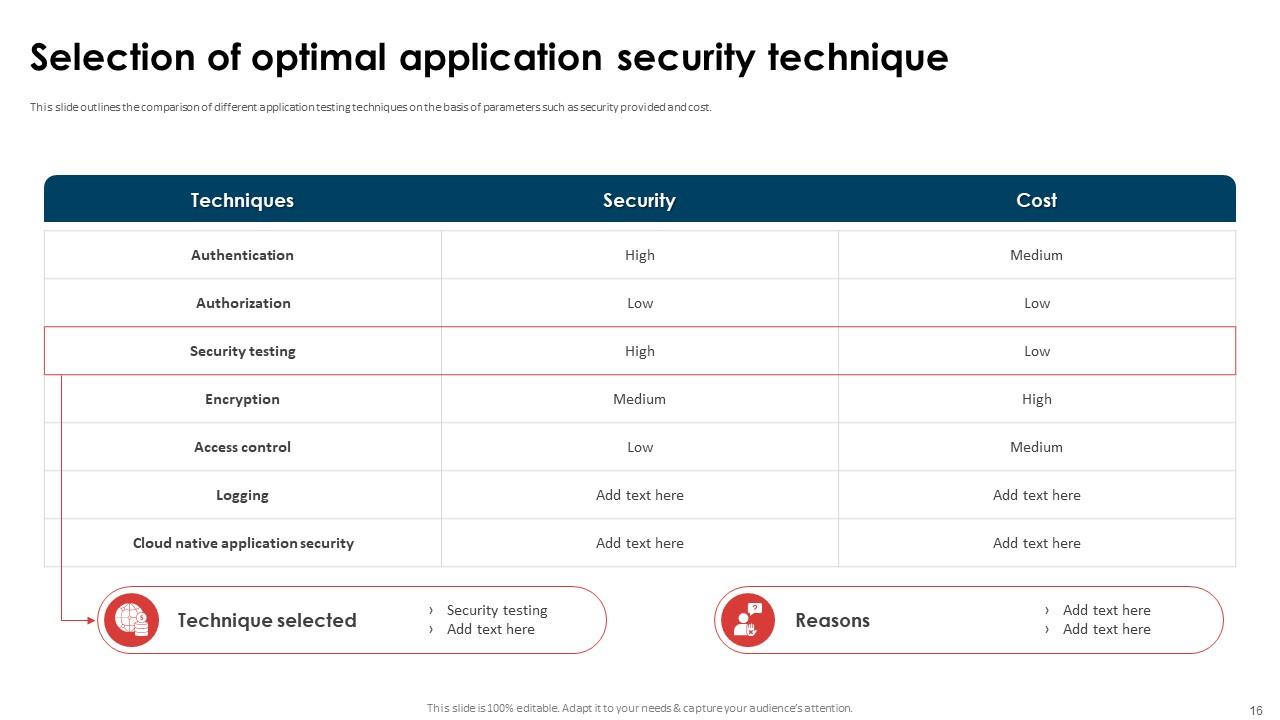
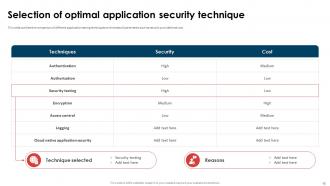
Slide 16: This slide outlines the comparison of different application testing techniques on the basis of parameters such as security provided and cost.
Slide 17: The slide renders Title of contents which is to be discussed further.
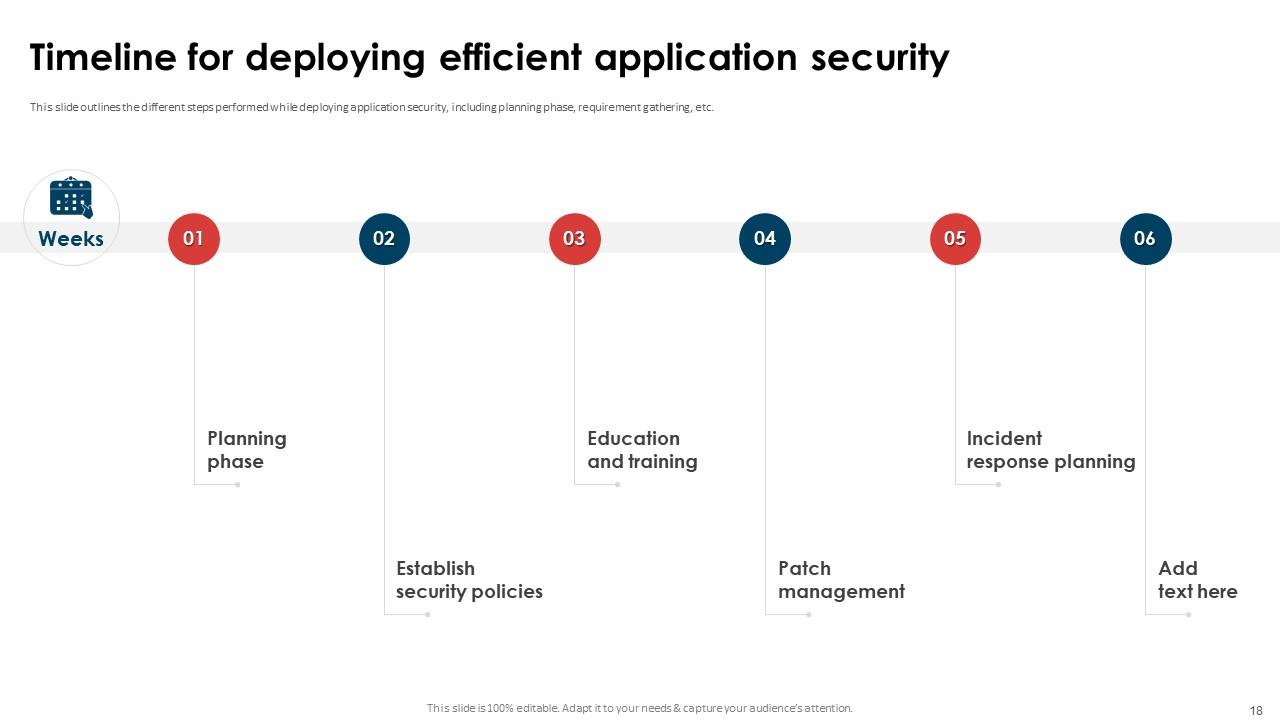
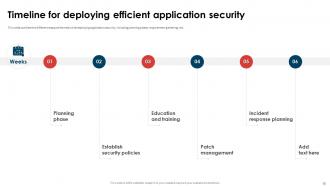
Slide 18: This slide describes the different steps performed while deploying application security, including planning phase, requirement gathering, etc.
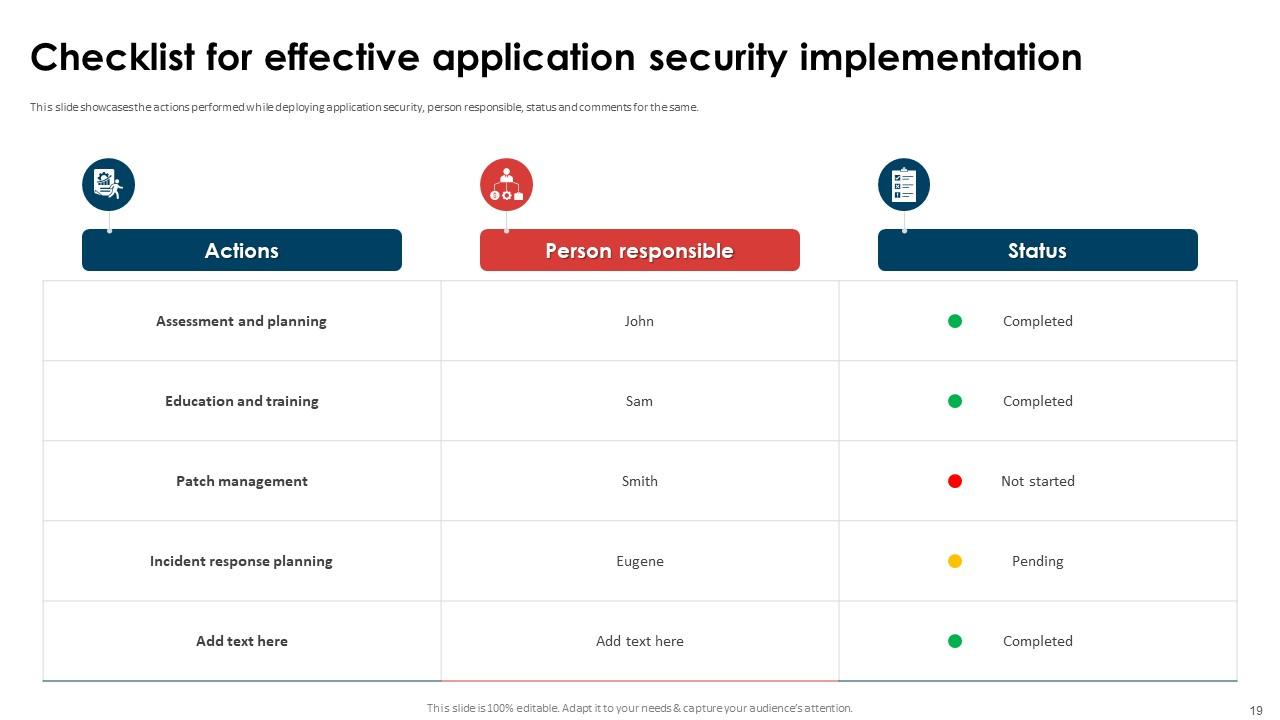
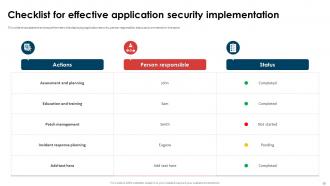
Slide 19: This slide showcases the actions performed while deploying application security, person responsible, status and comments for the same.
Slide 20: The slide renders Title of contents which is to be discussed further.
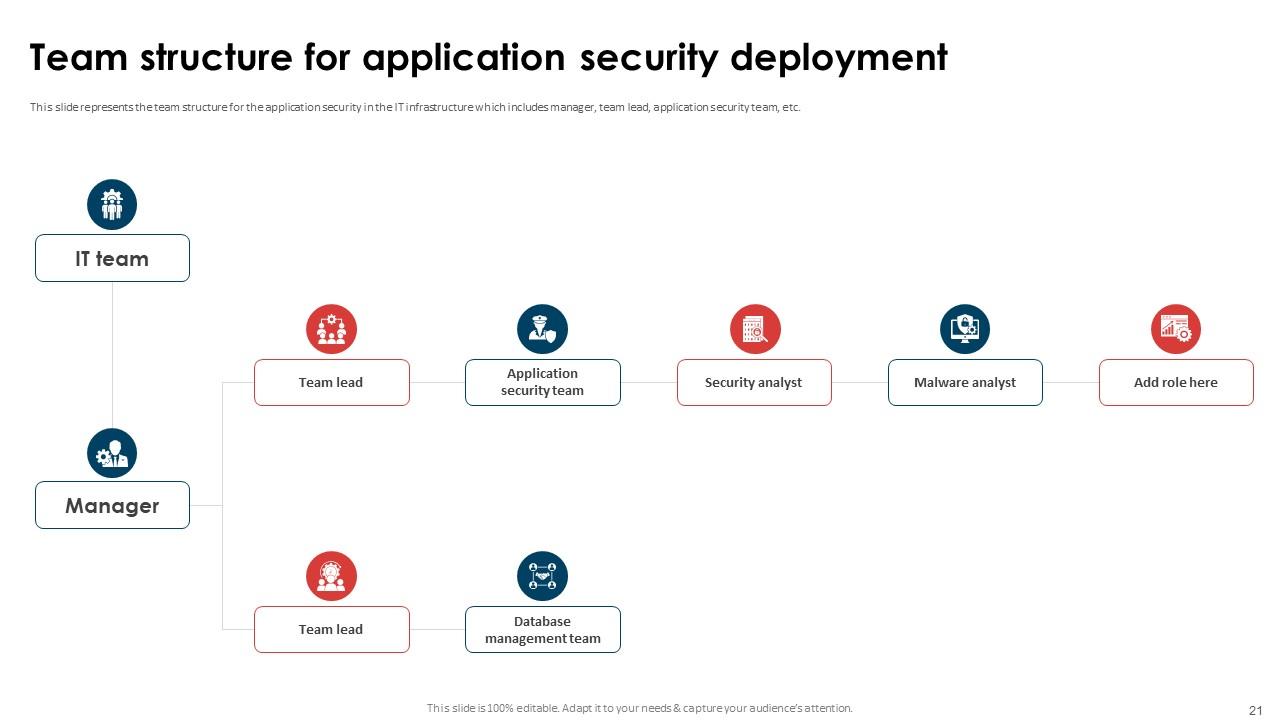
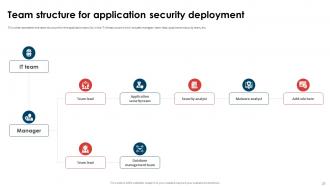
Slide 21: This slide represents the team structure for the application security in the IT infrastructure.
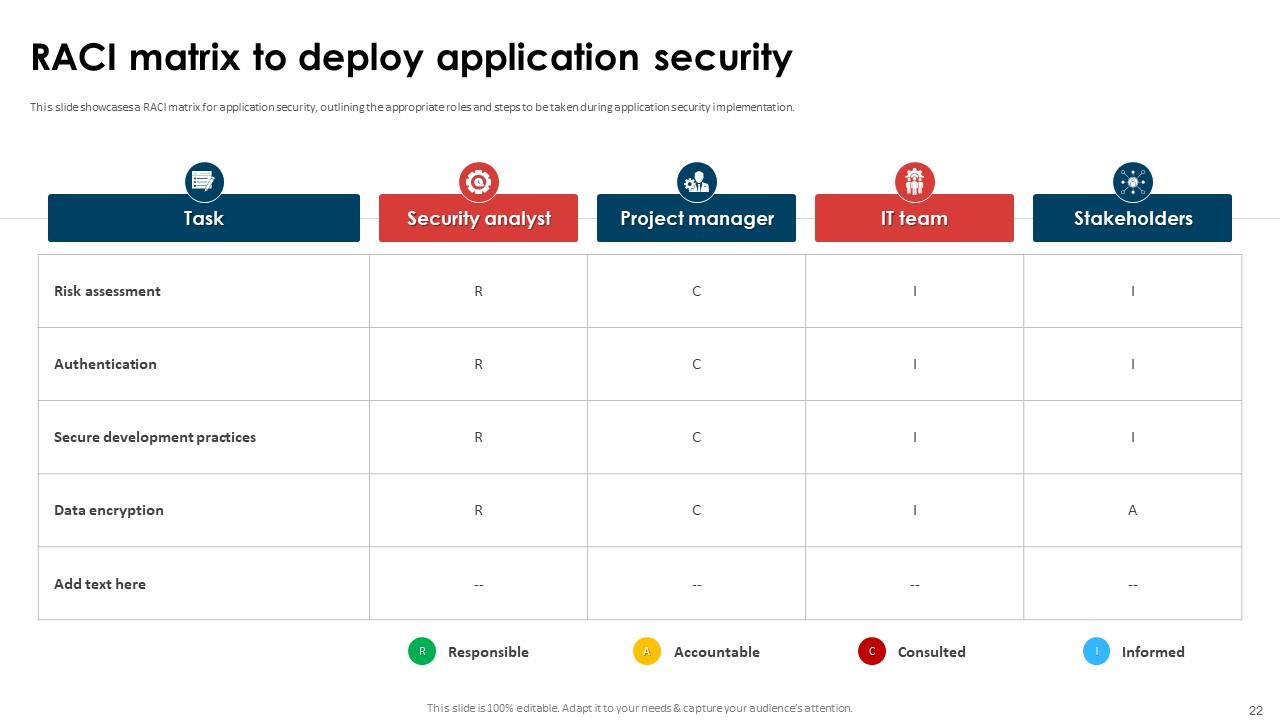
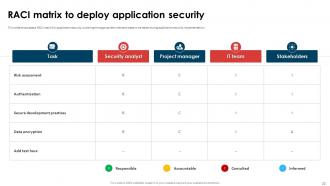
Slide 22: This slide shows a RACI matrix for application security, outlining the appropriate roles and steps to be taken during application security implementation.
Slide 23: The slide again presents Title of contents.
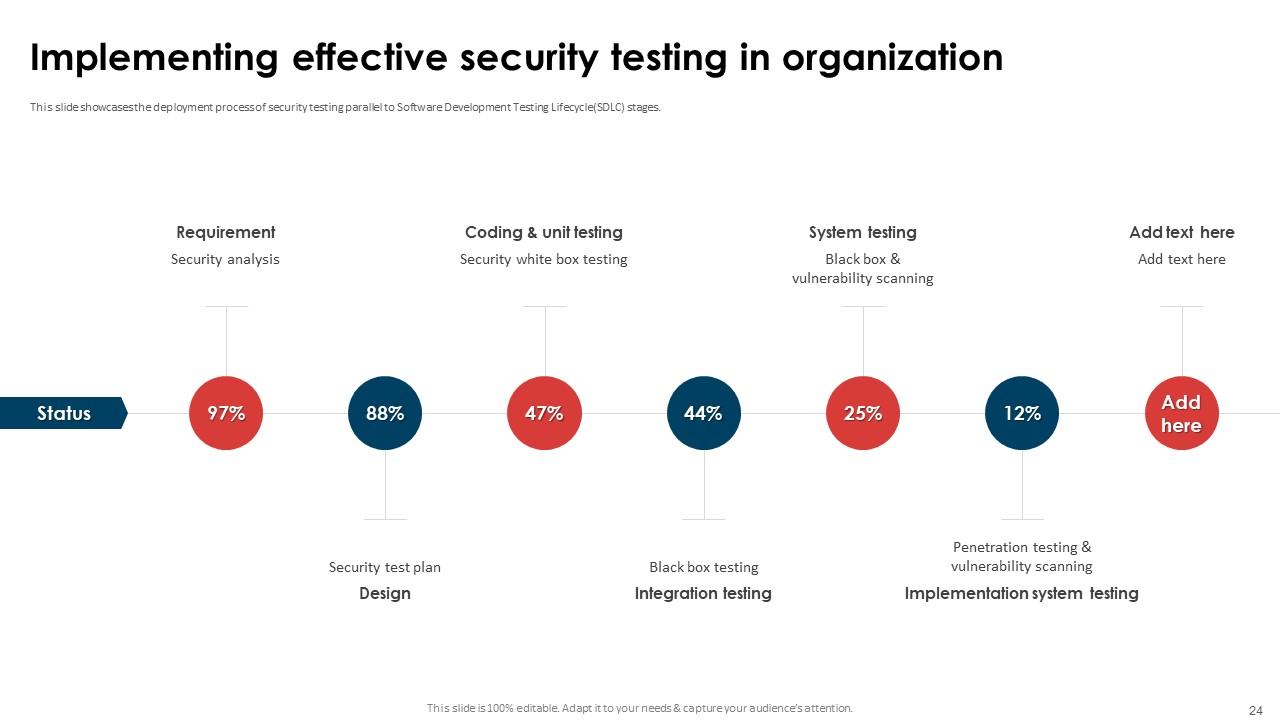
Slide 24: This slide showcases the deployment process of security testing parallel to Software Development Testing Lifecycle(SDLC) stages.
Slide 25: The slide displays Title of contents which is to be discussed further.
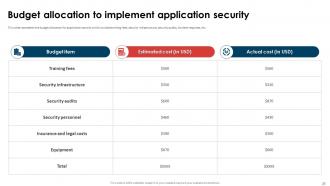
Slide 26: This slide represents the budget allocation for application security which includes training fees, security infrastructure, etc.
Slide 27: The slide displays Title of contents further.
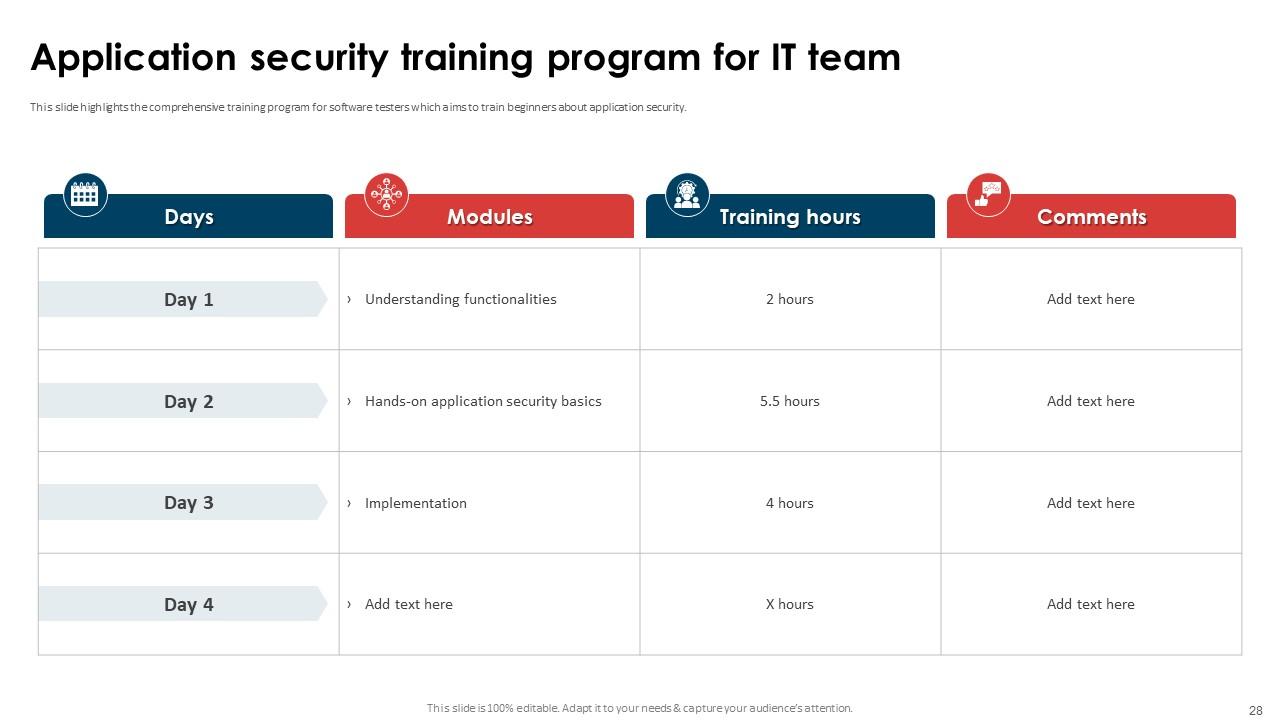
Slide 28: This slide highlights the comprehensive training program for software testers which aims to train beginners about application security.
Slide 29: This slide showcases the training cost breakdown for different components such as instructor, training cost, etc.
Slide 30: The slide renders Title of contents further.
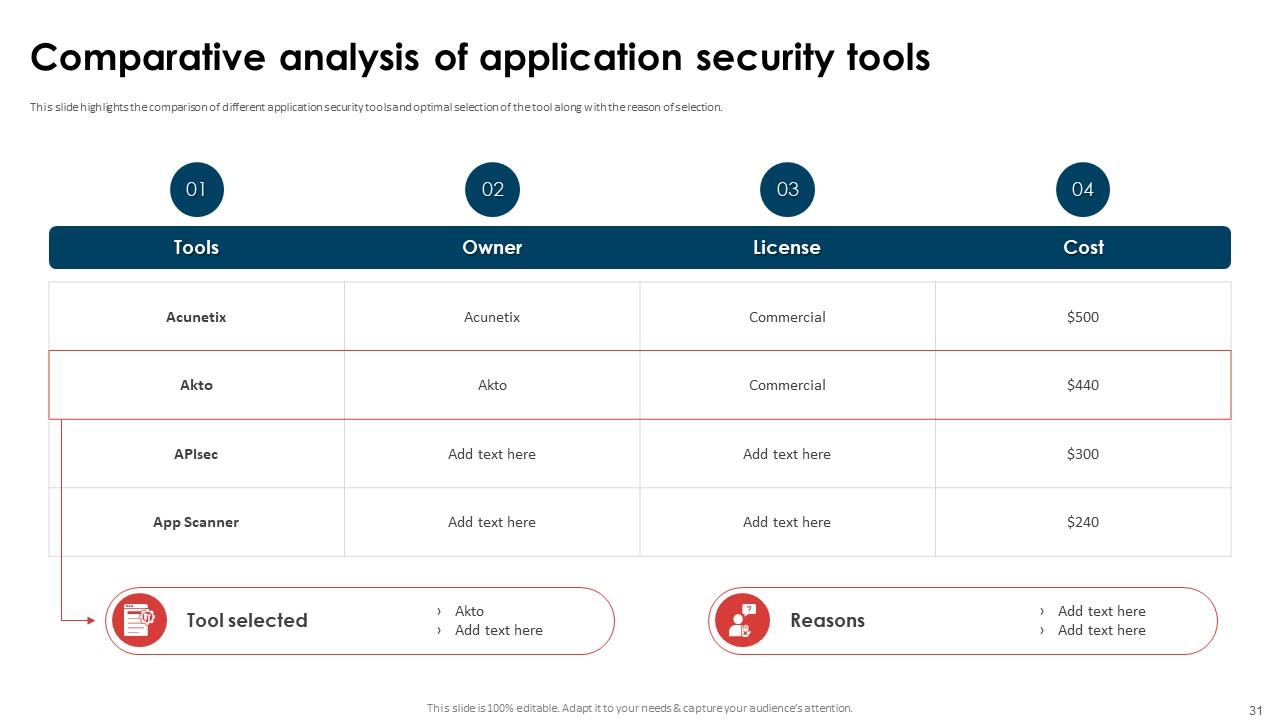
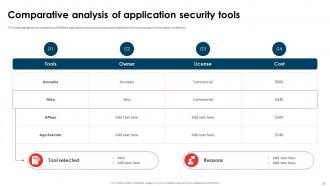
Slide 31: This slide highlights the comparison of different application security tools and optimal selection of the tool along with the reason of selection.
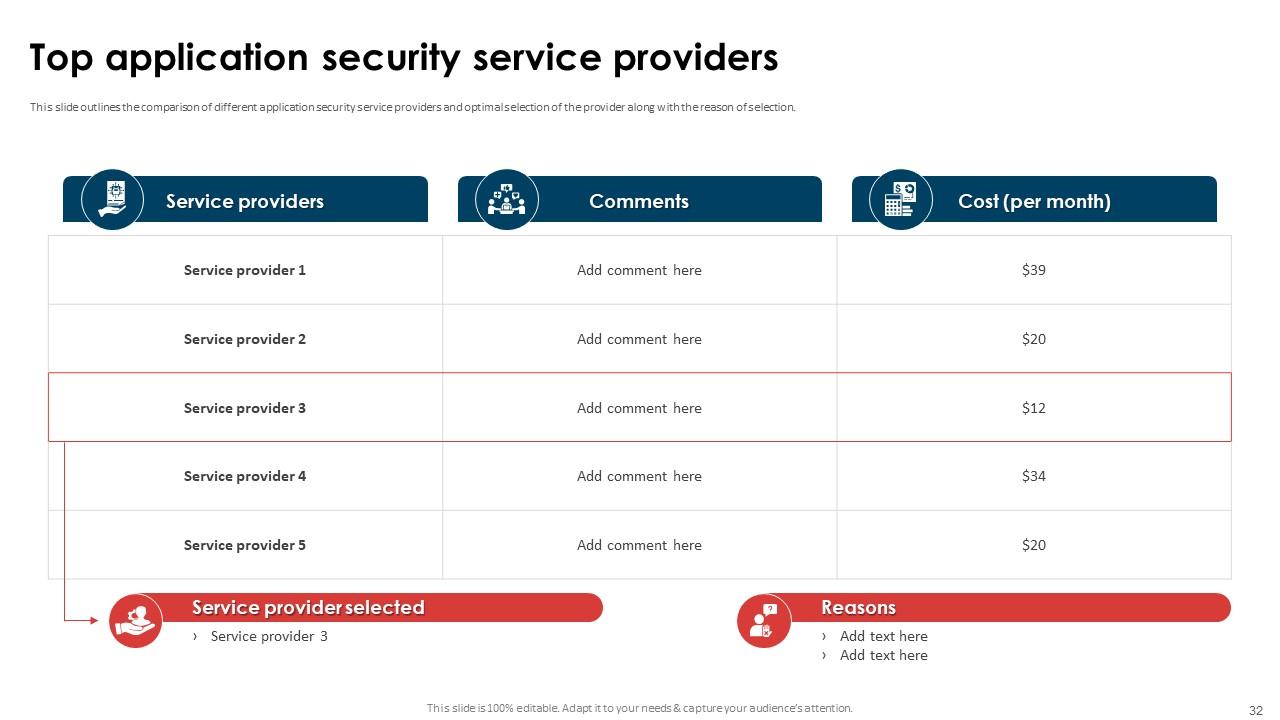
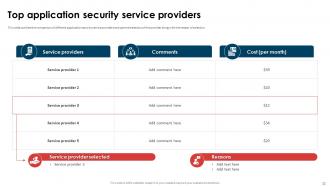
Slide 32: This slide outlines the comparison of different application security service providers and optimal selection of the provider.
Slide 33: The slide represents Title of contents.
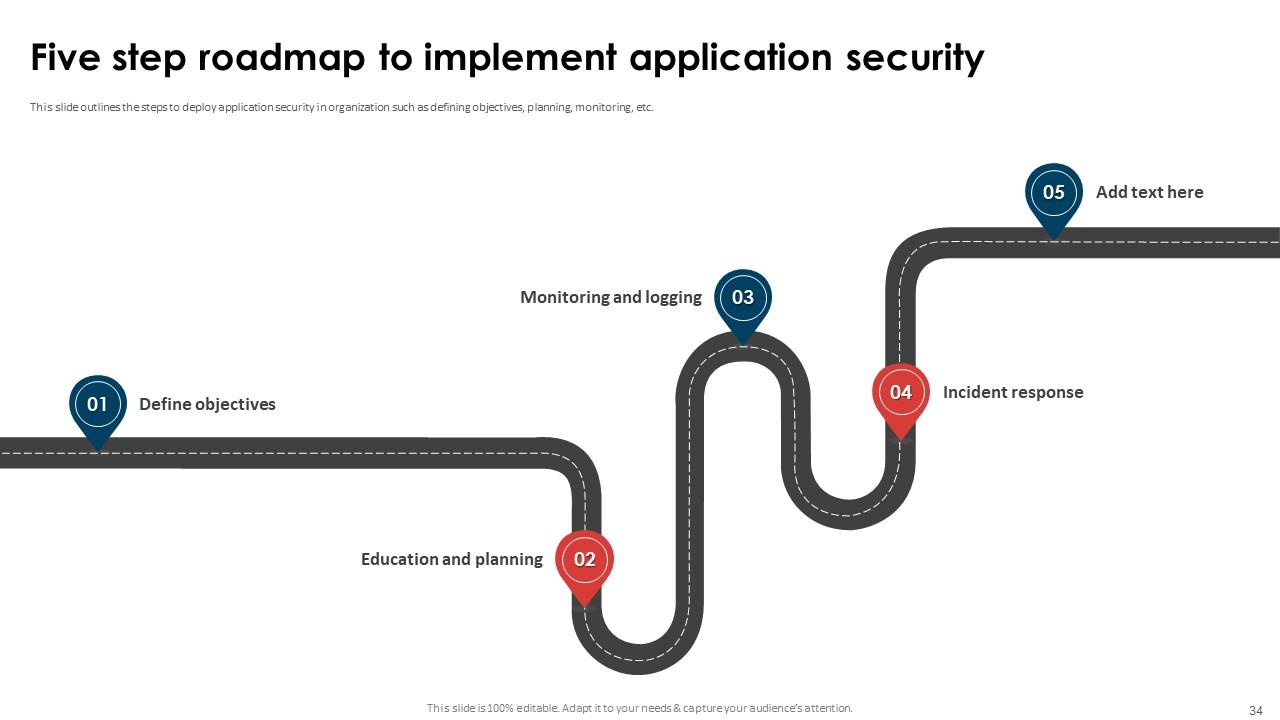
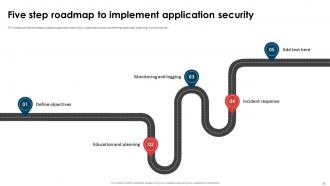
Slide 34: This slide outlines the steps to deploy application security in organization such as defining objectives, planning, monitoring, etc.
Slide 35: The slide displays Title of contents which is to be discussed further.
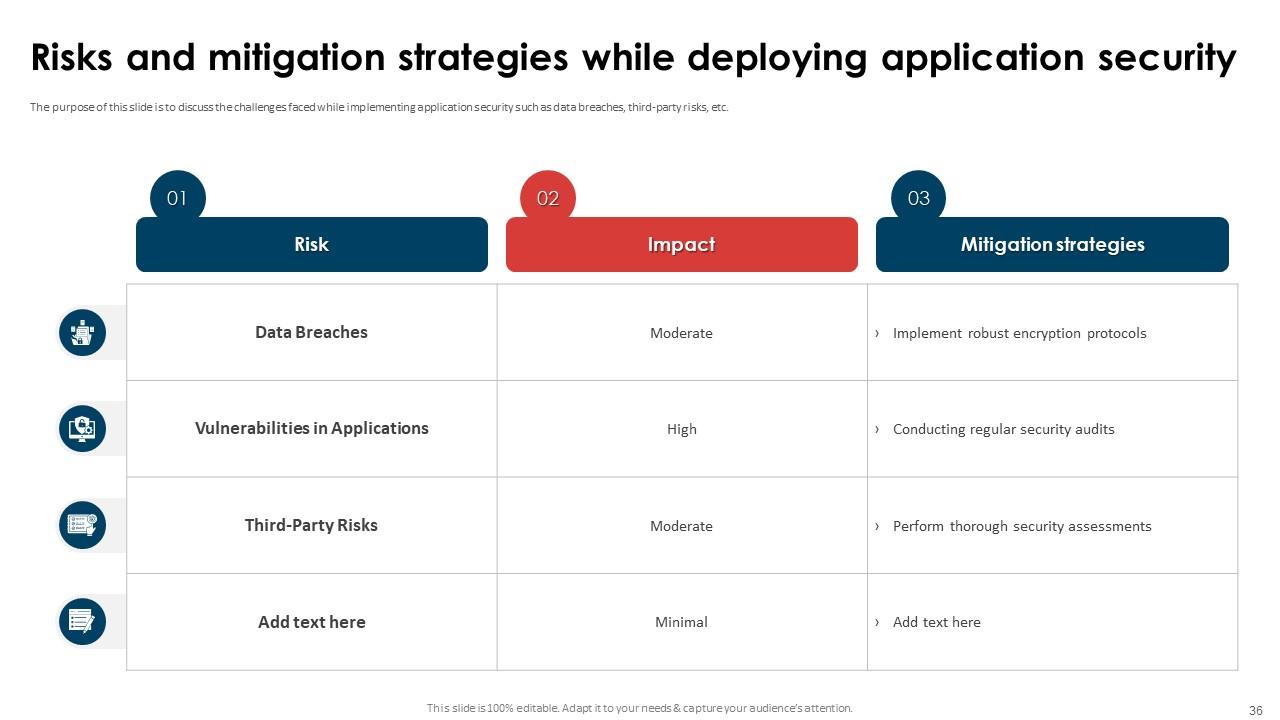
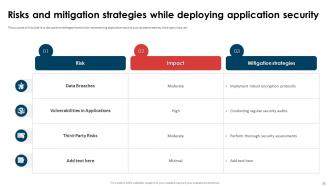
Slide 36: The slide discusses the challenges faced while implementing application security such as data breaches, third-party risks, etc.
Slide 37: The slide again renders Title of contents.
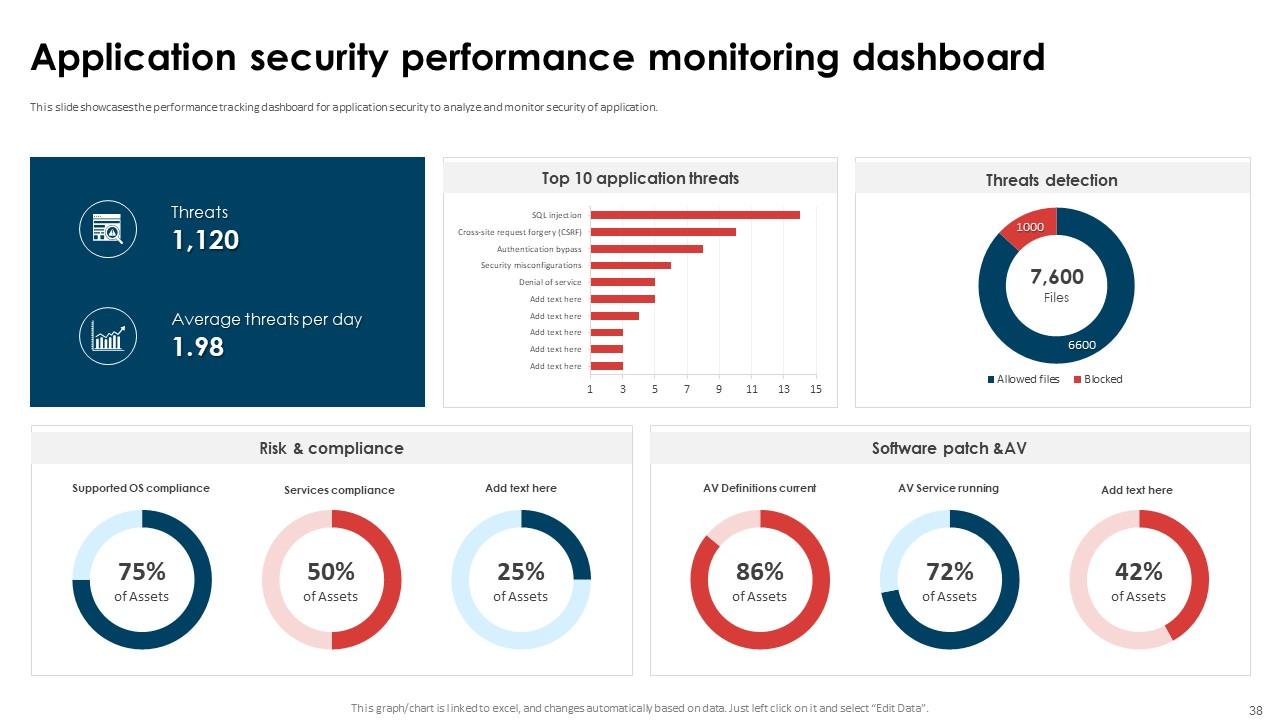
Slide 38: This slide showcases the performance tracking dashboard for application security to analyze and monitor security of application.
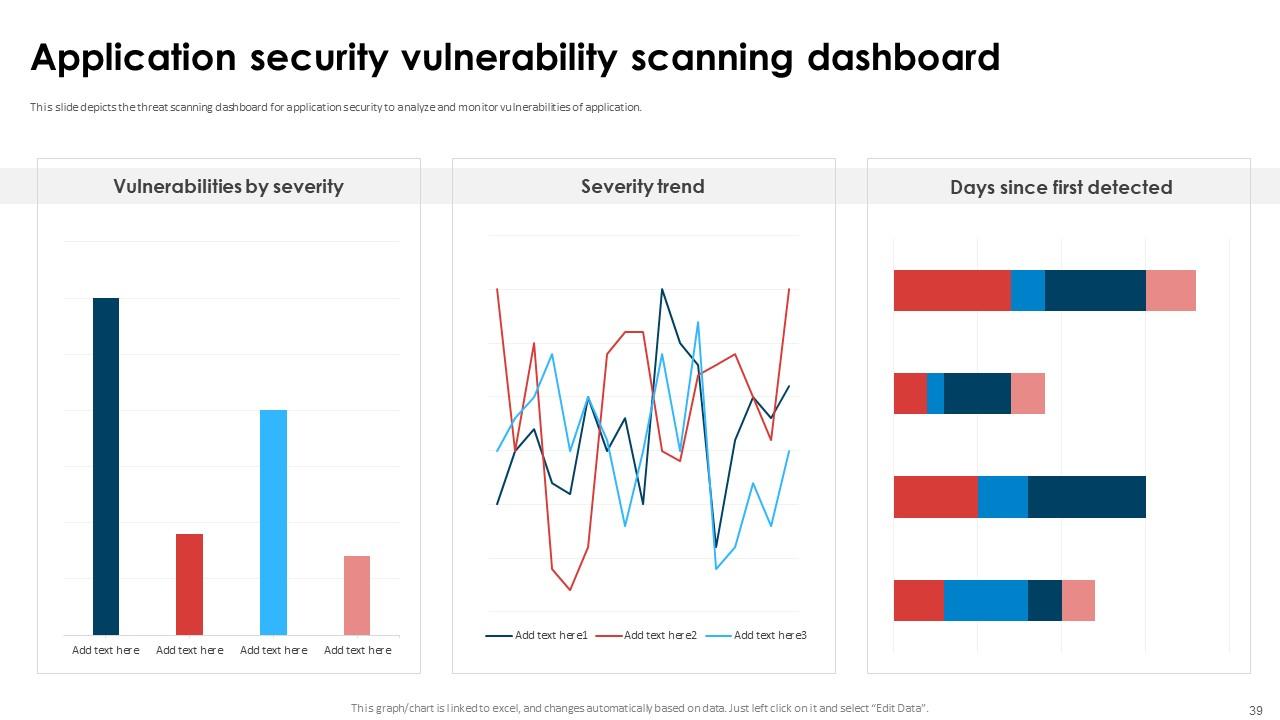
Slide 39: This slide shows the threat scanning dashboard for application security to analyze and monitor vulnerabilities of application.
Slide 40: The slide depicts Title of contents further.
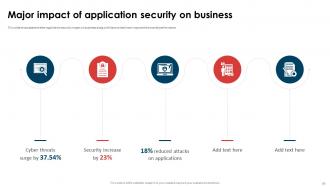
Slide 41: This slide highlights the after application security impact on business along with factors that have improved the overall performance.
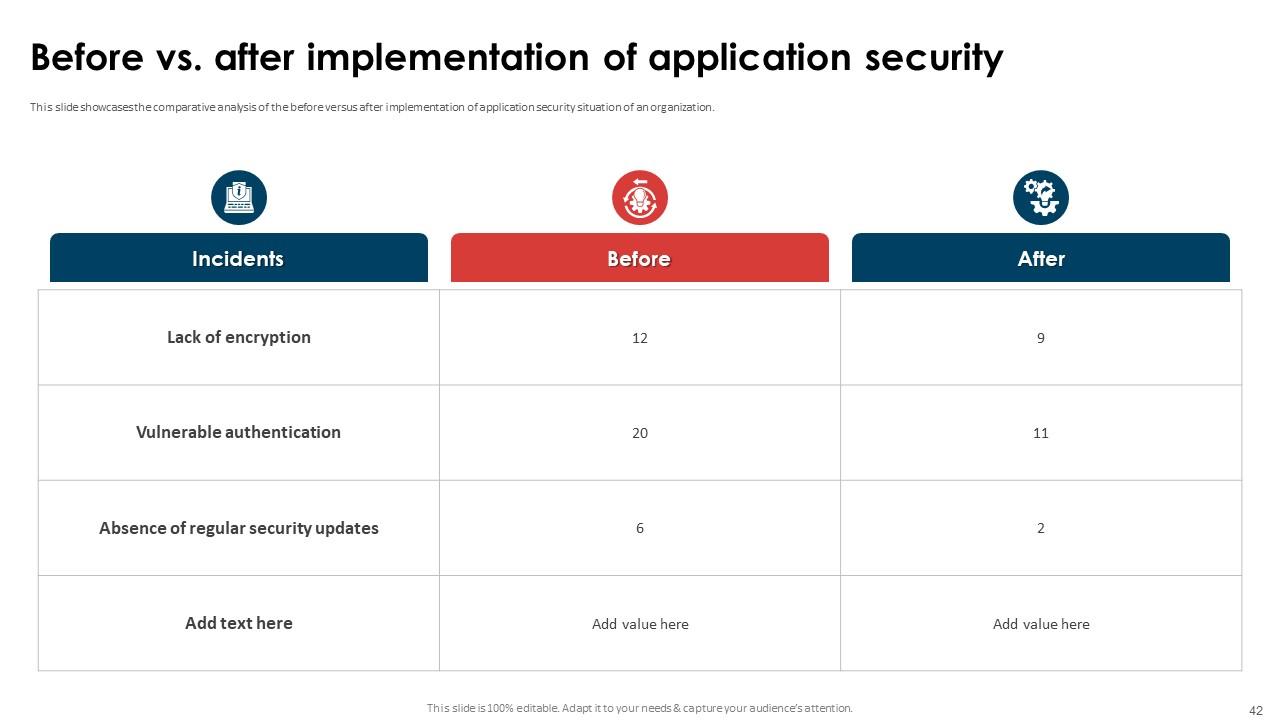
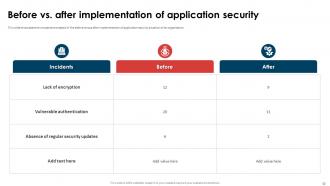
Slide 42: This slide showcases the comparative analysis of the before versus after implementation of application security situation of an organization.
Slide 43: This slide shows all the icons included in the presentation.
Slide 44: This slide is titled as Additional Slides for moving forward.
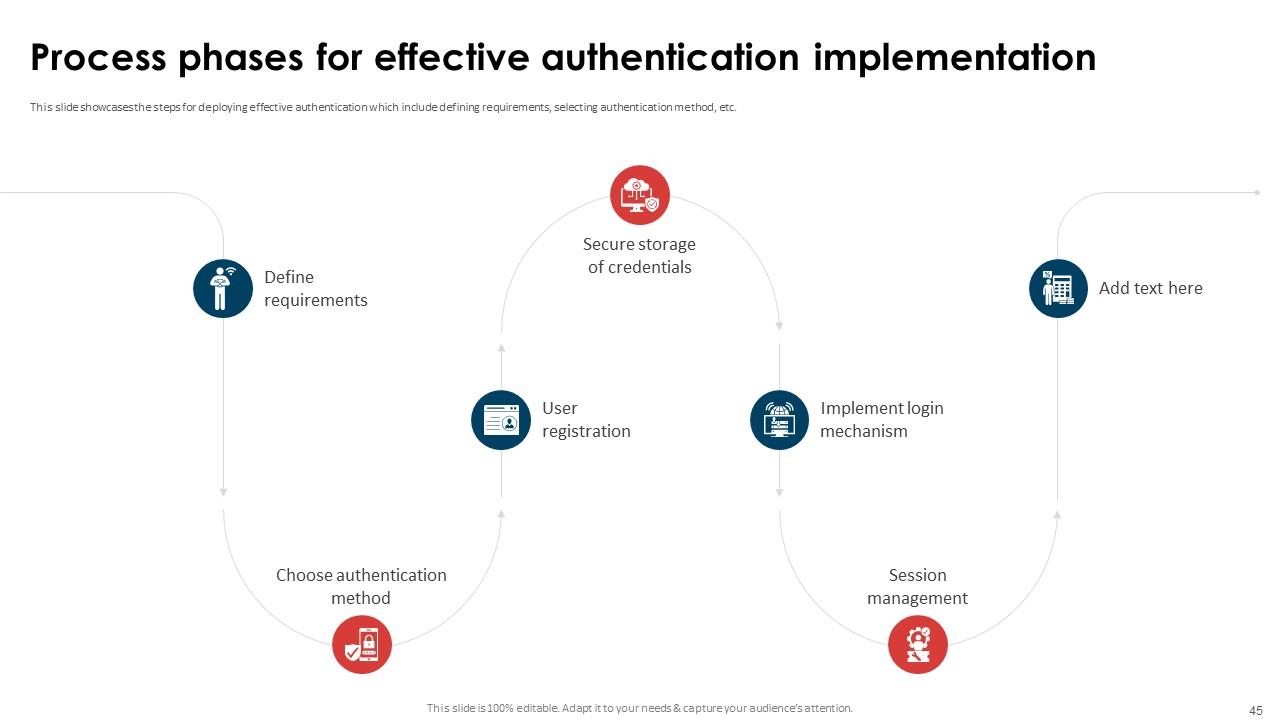
Slide 45: This slide showcases the steps for deploying effective authentication which include defining requirements, selecting authentication method, etc.
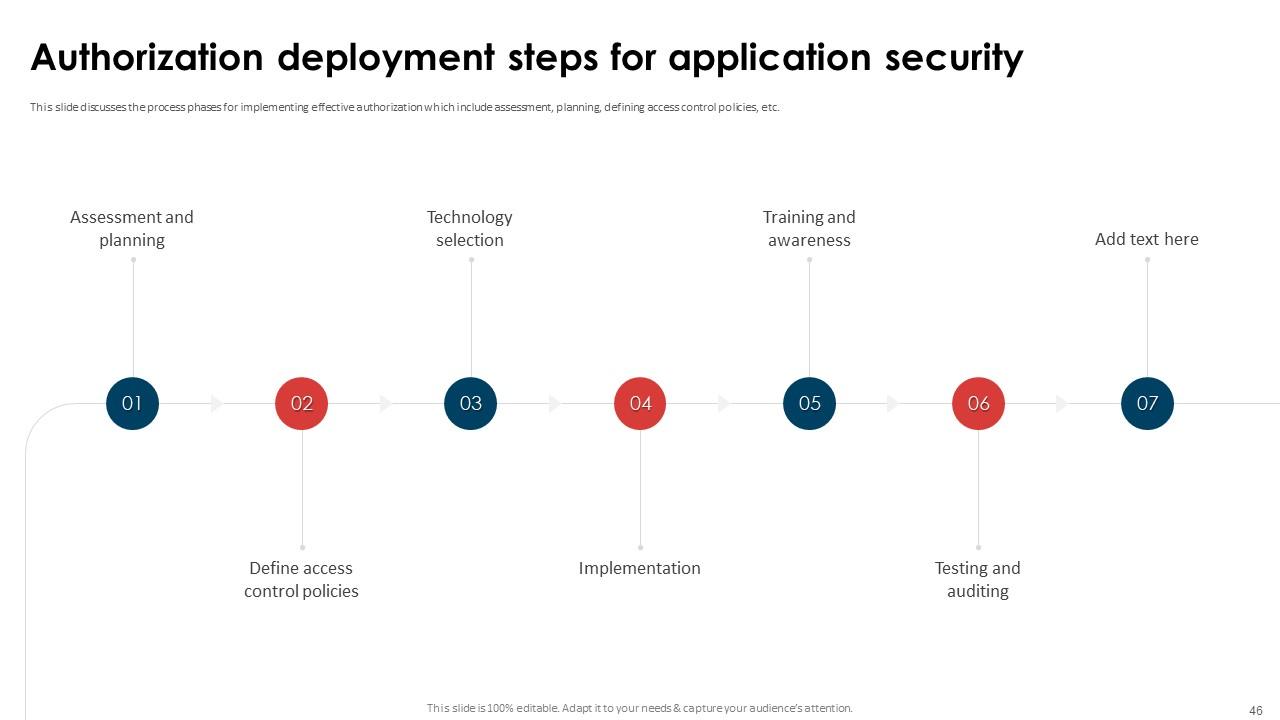
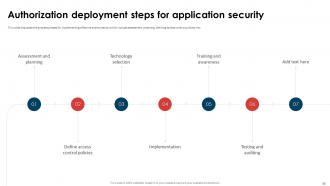
Slide 46: This slide discusses the process phases for implementing effective authorization which include assessment, planning, defining access control policies, etc.
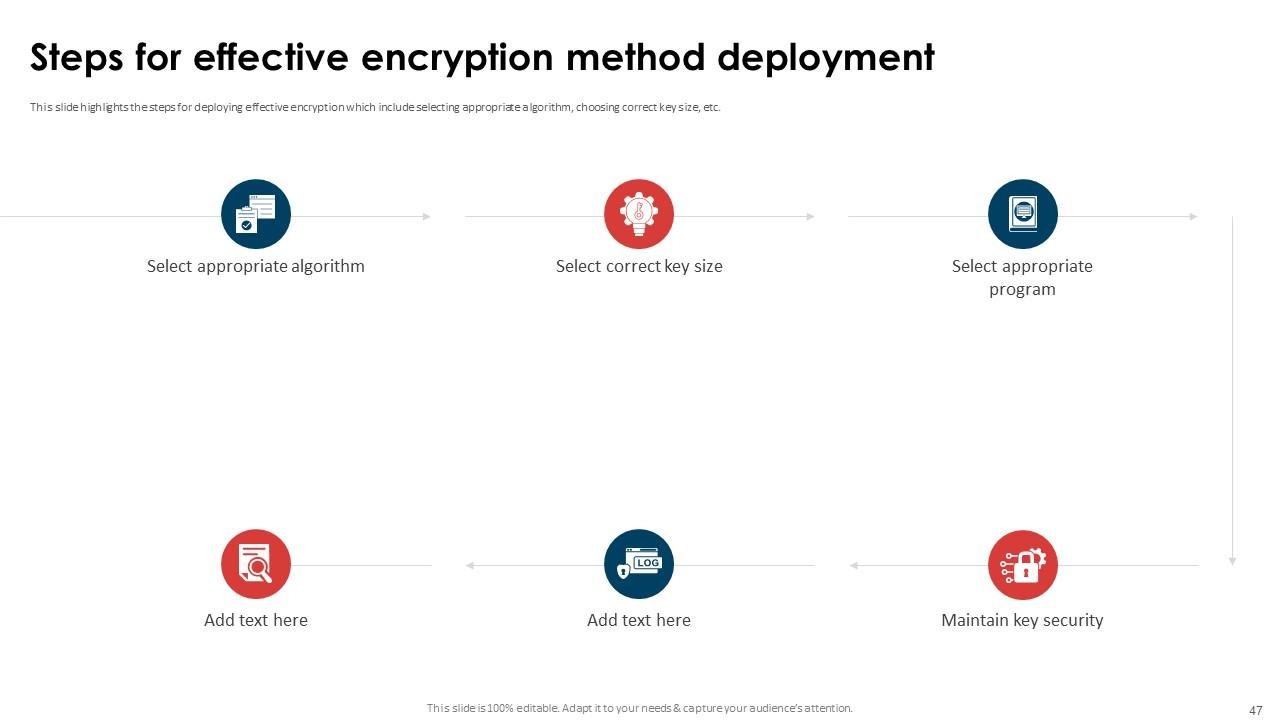
Slide 47: This slide highlights the steps for deploying effective encryption which include selecting appropriate algorithm, choosing correct key size, etc.
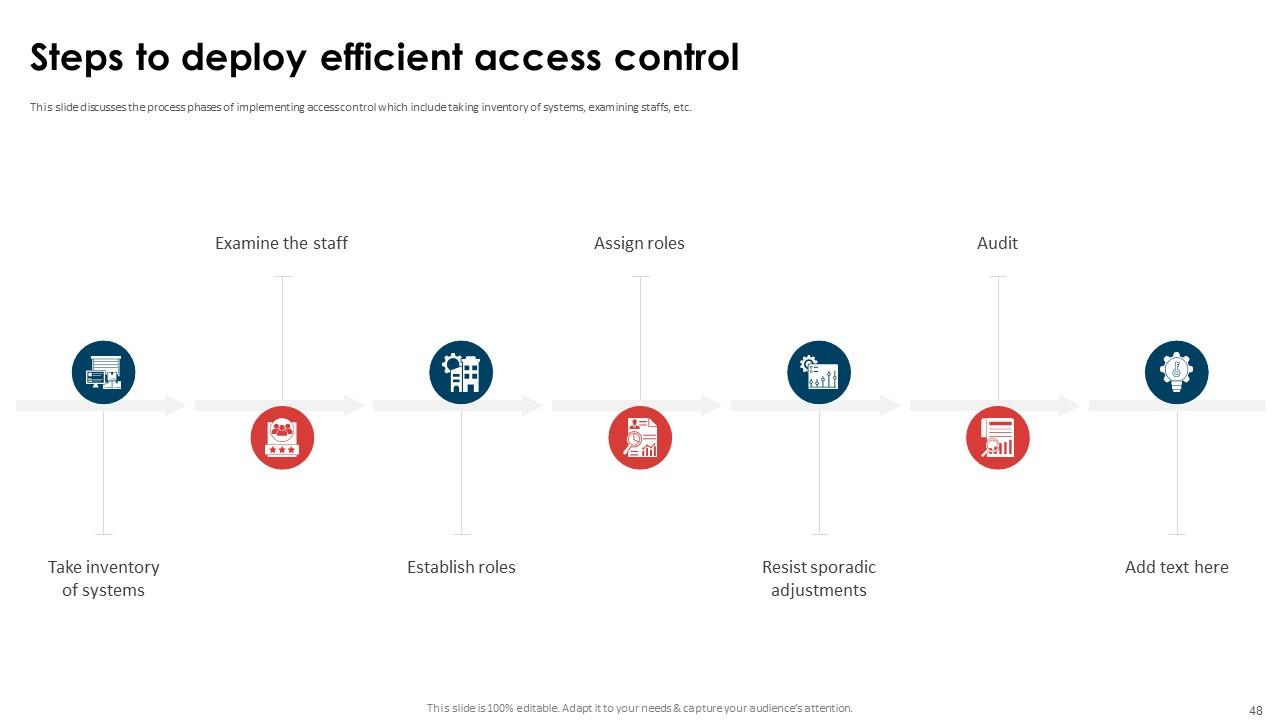
Slide 48: This slide renders the process phases of implementing access control which include taking inventory of systems, examining staffs, etc.
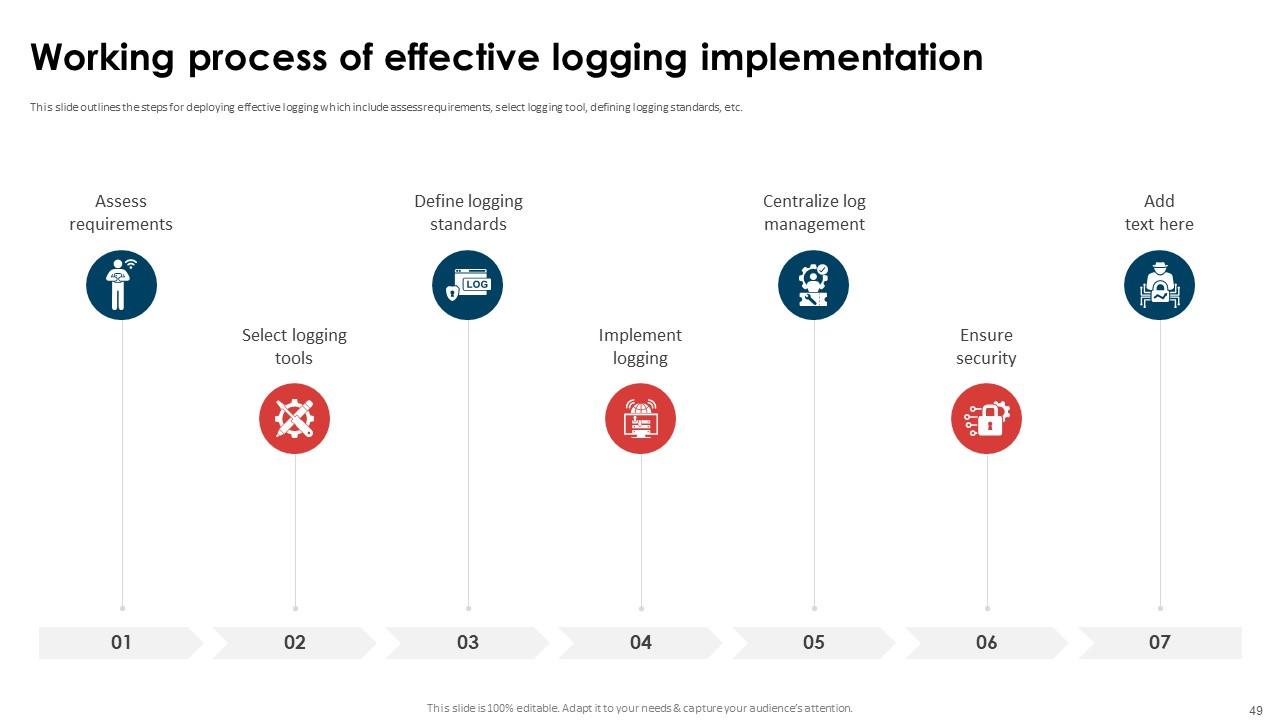
Slide 49: This slide outlines the steps for deploying effective logging which include assess requirements, select logging tool, defining logging standards, etc.
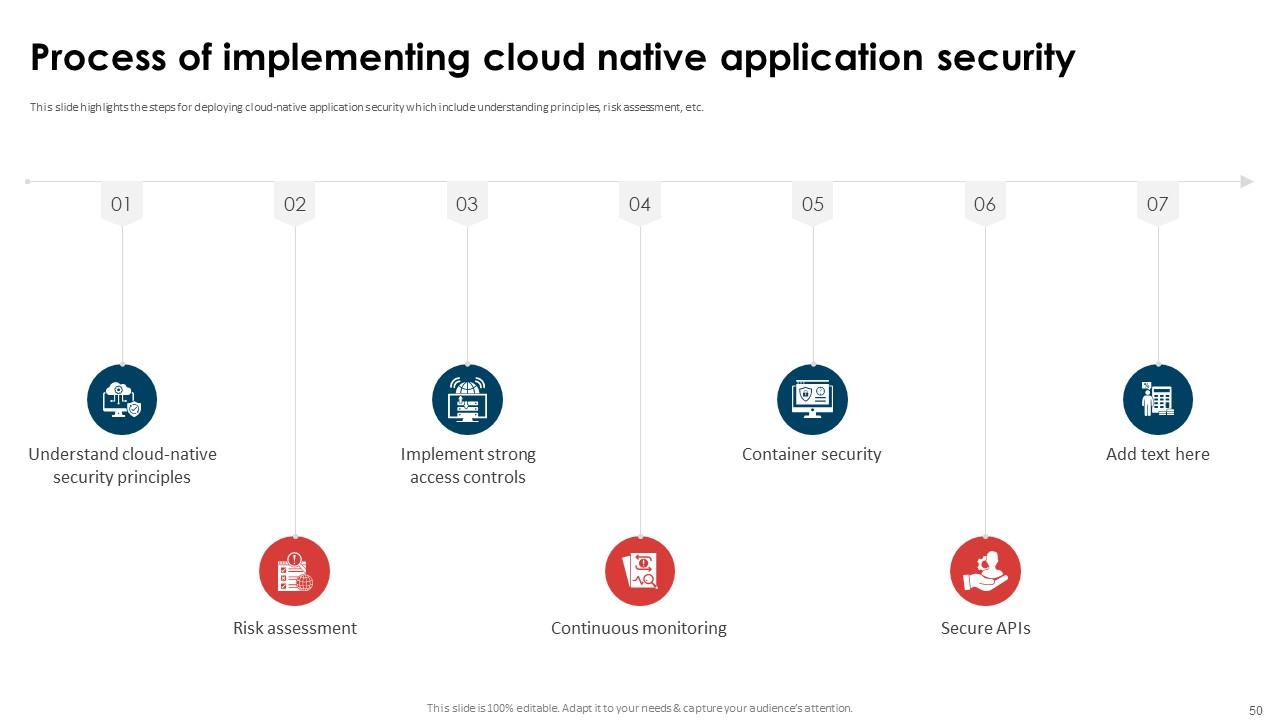
Slide 50: This slide highlights the steps for deploying cloud-native application security which include understanding principles, risk assessment, etc.
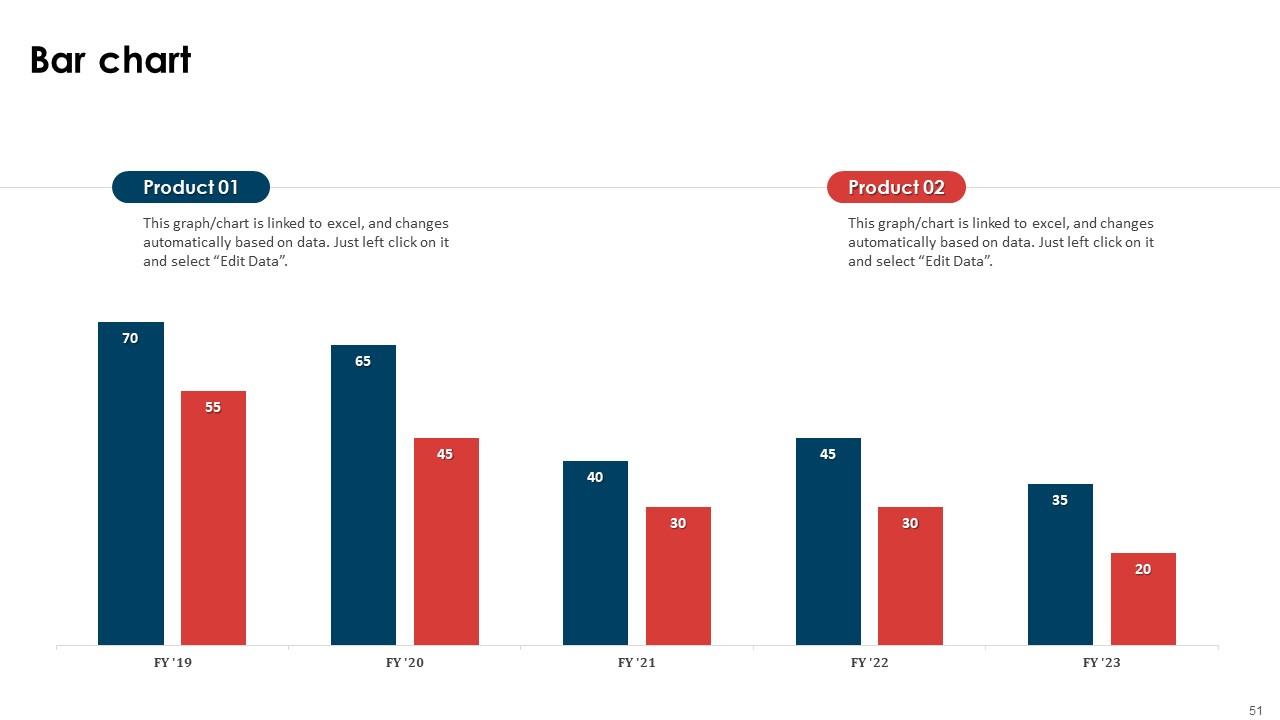
Slide 51: This slide presents Bar chart with two products comparison.
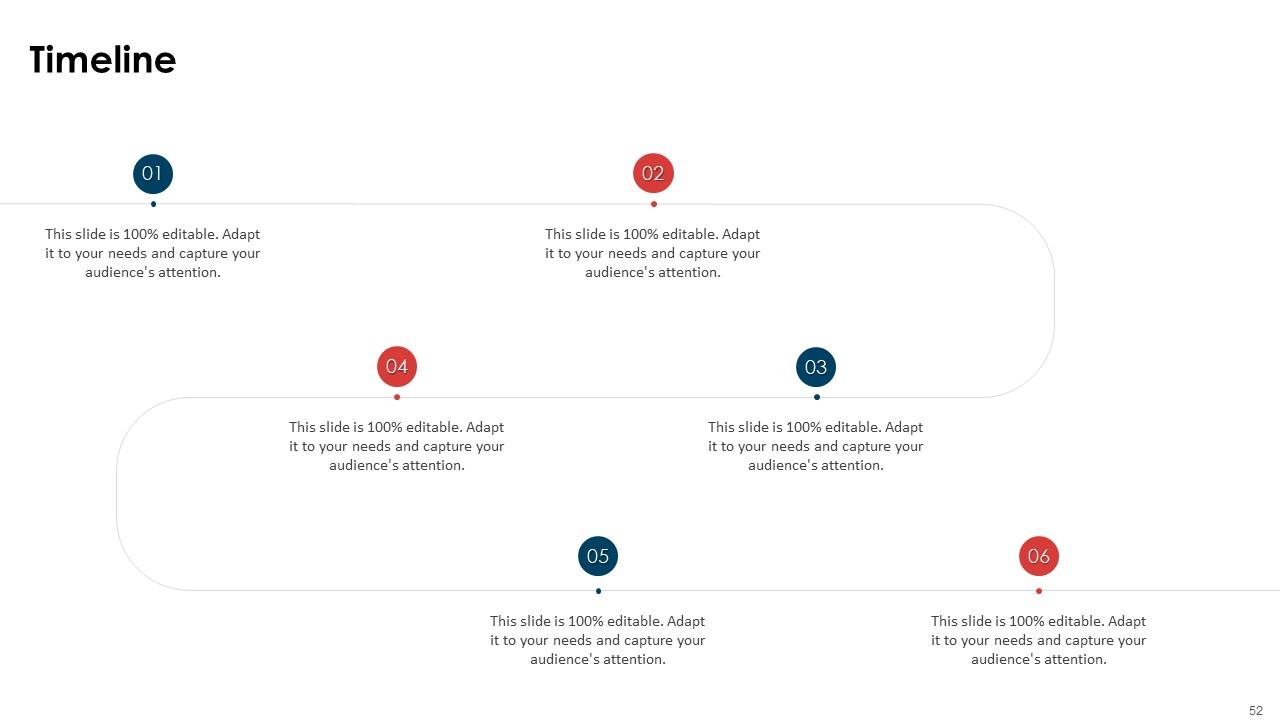
Slide 52: This is a Timeline slide. Show data related to time intervals here.
Slide 53: This slide depicts Venn diagram with text boxes.
Slide 54: This is a Financial slide. Show your finance related stuff here.
Slide 55: This slide contains Puzzle with related icons and text.
Slide 56: This is Our Goal slide. State your firm's goals here.
Slide 57: This is an Idea Generation slide to state a new idea or highlight information, specifications etc.
Slide 58: This slide provides 30 60 90 Days Plan with text boxes.
Slide 59: This slide shows Post It Notes. Post your important notes here.
Slide 60: This is a Thank You slide with address, contact numbers and email address.
Application Security Implementation Plan Powerpoint Presentation Slides with all 69 slides:
Use our Application Security Implementation Plan Powerpoint Presentation Slides to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
“Ample and amazing variety of templates available, really helpful for making professional PPT for day to day workings.”
-
The presentations are very helpful. I am always able to get appropriate templates for the different topics related to my profession.