Steps For Cyber Threat Intelligence Lifecycles
This slide depicts the steps for cyber threat intelligence lifecycles. The purpose of this slide is to help the business successfully implement cyber threat intelligence practices. It includes steps such as requirements, collection, processing, etc.
This slide depicts the steps for cyber threat intelligence lifecycles. The purpose of this slide is to help the business su..
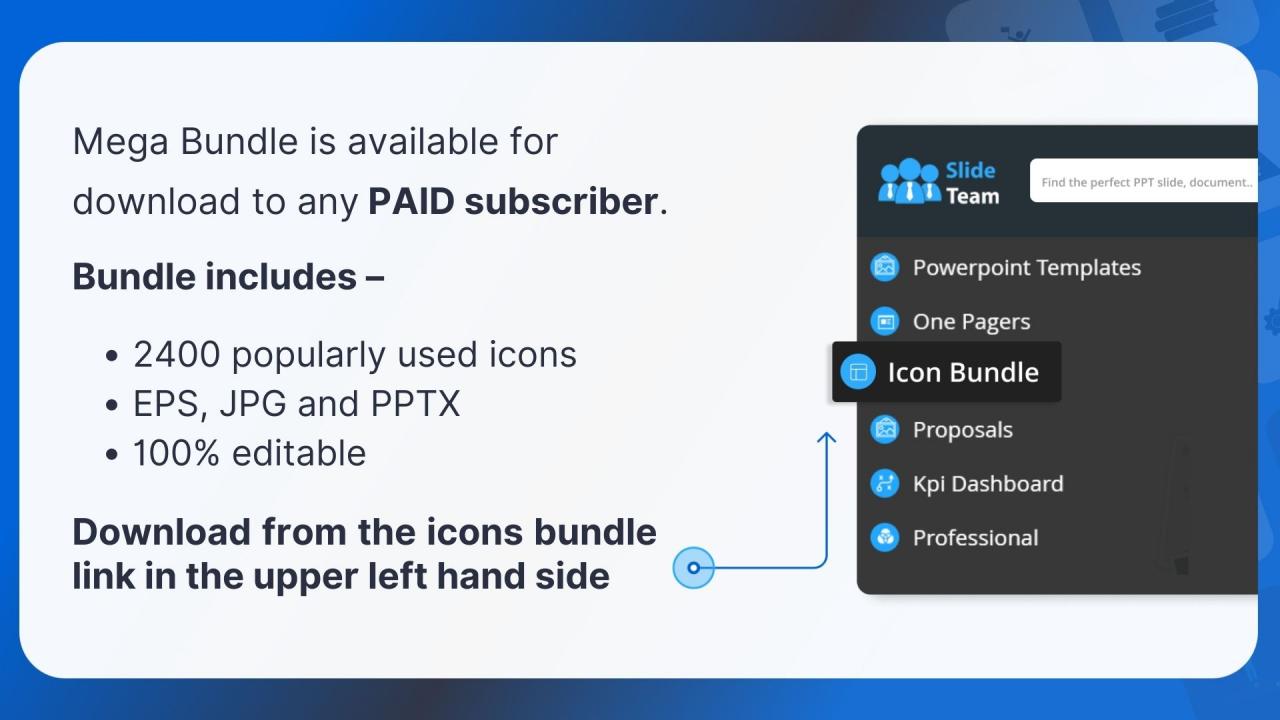
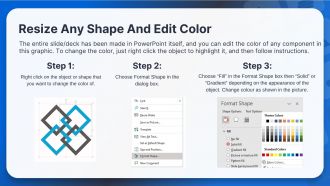
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
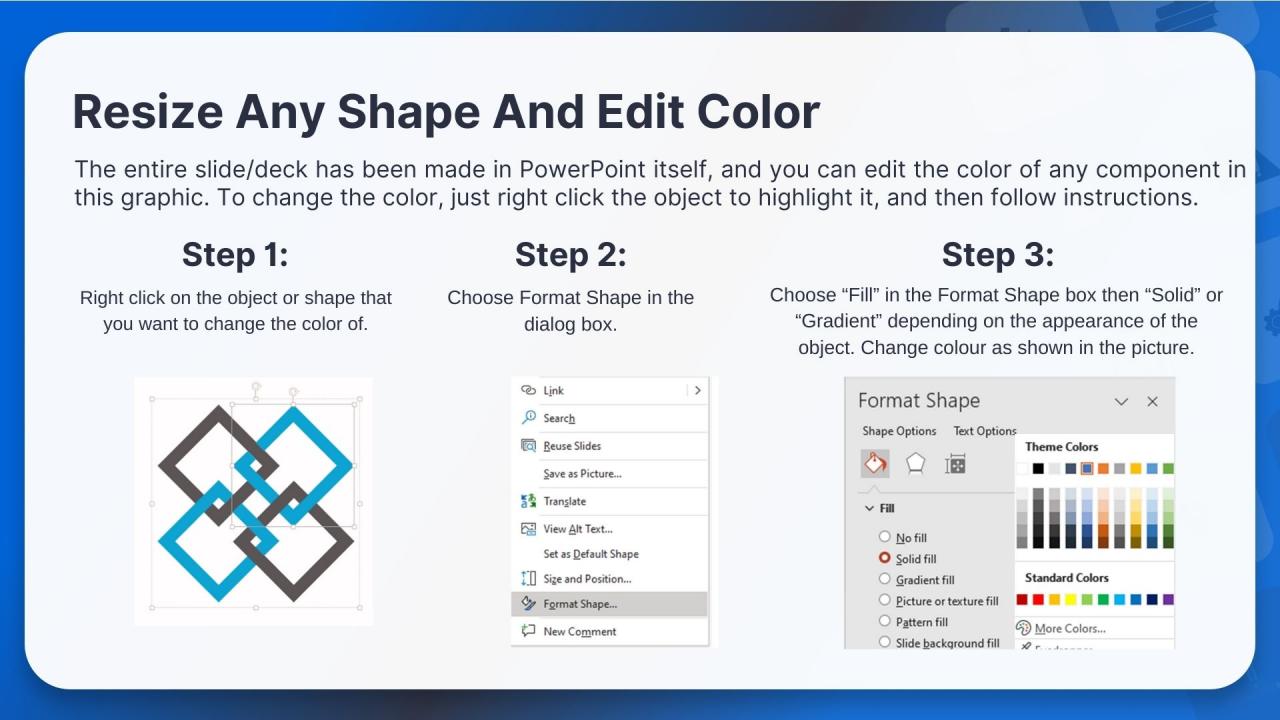
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
This slide depicts the steps for cyber threat intelligence lifecycles. The purpose of this slide is to help the business successfully implement cyber threat intelligence practices. It includes steps such as requirements, collection, processing, etc. Introducing our premium set of slides with Steps For Cyber Threat Intelligence Lifecycles Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Requirements, Collection, Processing So download instantly and tailor it with your information.
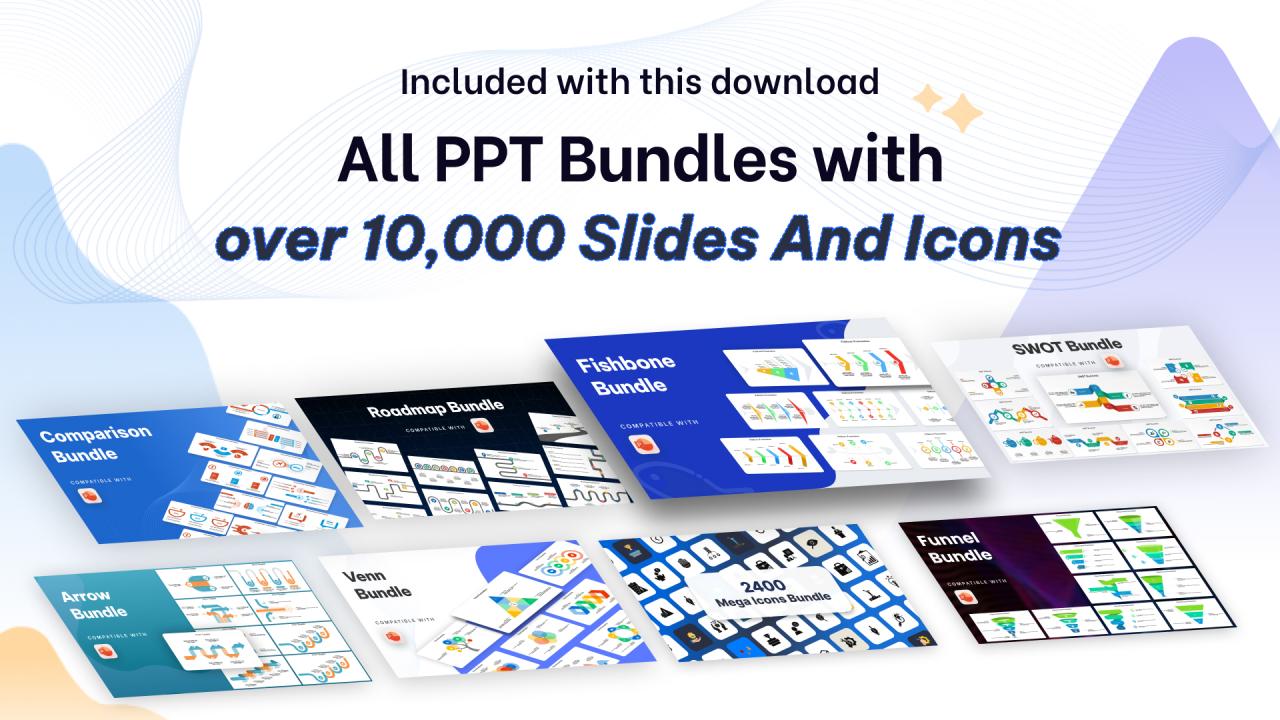
Steps For Cyber Threat Intelligence Lifecycles with all 10 slides:
Use our Steps For Cyber Threat Intelligence Lifecycles to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
Great product with effective design. Helped a lot in our corporate presentations. Easy to edit and stunning visuals.
-
Stunning collection! With a wide variety of options available, I was able to find a perfect slide for my presentation. Thank you, SlideTeam!