Information security governance with stakeholders
Our Information Security Governance With Stakeholders are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Presenting our set of slides with name Information Security Governance With Stakeholders. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Stakeholders Oversee Information Security, Governance Framework, Organizational Security Structure, Management Commitment, Monitoring And Tracking.
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
Description:
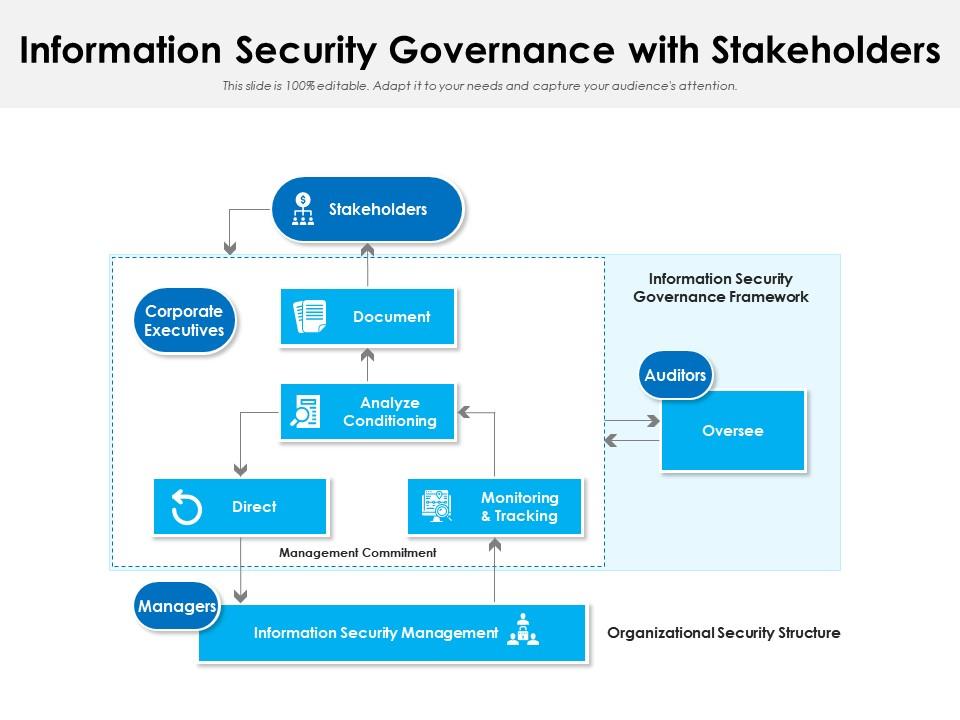
The image depicts a PowerPoint slide titled "Information Security Governance with Stakeholders." It outlines the relationship and roles within an organization's structure for implementing information security governance. The slide shows a flowchart with various interconnected elements:
1. Stakeholders:
This represents individuals or groups with an interest in the company's information security policies.
2. Corporate Executives:
They have responsibilities such as documenting and analyzing conditioning, which suggests they are involved in creating and maintaining security policies and procedures.
3. Information Security Management:
Managers are shown to direct these efforts, indicating their role in executing the security strategies set by executives.
4. Monitoring & Tracking:
This is part of the management's commitment, signifying the ongoing process of ensuring the security measures are effective.
5. Auditors:
Positioned within the Information Security Governance Framework to oversee the processes, auditors likely ensure compliance and effectiveness of the security measures.
Use Cases:
This slide can be used in a variety of industries where information security is critical:
1. Financial Services:
Use: Implementing robust security protocols to protect financial data.
Presenter: Chief Information Security Officer
Audience: Risk management team, IT staff
2. Healthcare:
Use: Ensuring patient data confidentiality and compliance with health data regulations.
Presenter: Compliance Officer
Audience: Healthcare administrators, data protection staff
3. Technology:
Use: Safeguarding intellectual property and customer data.
Presenter: Security Architect
Audience: Software developers, system engineers
4. Retail:
Use: Protecting customer transaction data and preventing data breaches.
Presenter: Data Security Manager
Audience: E-commerce team, customer service managers
5. Education:
Use: Securing student and staff information systems.
Presenter: IT Director
Audience: School administrators, IT department
6. Government:
Use: Managing the security of sensitive government records.
Presenter: Director of Cybersecurity
Audience: Public sector managers, security analysts
7. Telecommunications:
Use: Defending against cyber threats and ensuring the integrity of communication networks.
Presenter: Network Security Manager
Audience: Network operators, policy makers
Information security governance with stakeholders with all 2 slides:
Use our Information Security Governance With Stakeholders to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
Nice and innovative design.