Powerpoint Templates and Google slides for Accessibility Of Content
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Network Access Control As An Element Of Network Security Training Ppt
Network Access Control As An Element Of Network Security Training PptPresenting Network Access Control as an Element of Network Security. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
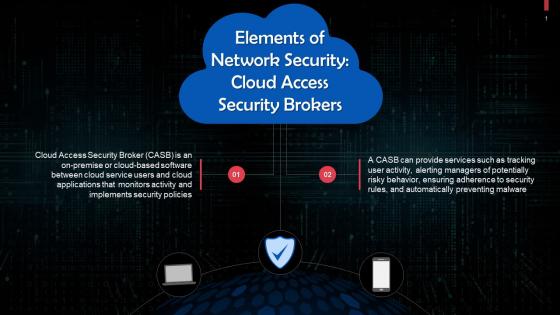 Cloud Access Security Brokers As An Element Of Network Security Training Ppt
Cloud Access Security Brokers As An Element Of Network Security Training PptPresenting Cloud Access Security Brokers as an Element of Network Security. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Overview Of Identity Access Management Policy Training Ppt
Overview Of Identity Access Management Policy Training PptPresenting Overview of Identity Access Management Policy. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
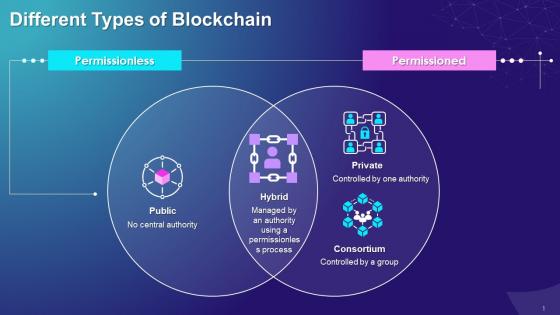 Different Types Of Blockchain Based On Permission To Access Training Ppt
Different Types Of Blockchain Based On Permission To Access Training PptPresenting Different Types of Blockchain based on Permission to Access. This slide is well crafted and designed by our PowerPoint specialists. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. You can add or delete the content as per your need.
-
 Benefit Of Digital Banking For Customers Remote Access Training Ppt
Benefit Of Digital Banking For Customers Remote Access Training PptPresenting Real-time remote access as a Benefit of Digital Banking for Customers. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
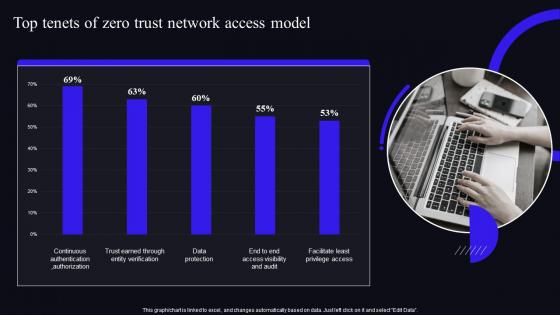 Top Tenets Of Zero Trust Network Access Model Zero Trust Security Model
Top Tenets Of Zero Trust Network Access Model Zero Trust Security ModelDeliver an outstanding presentation on the topic using this Top Tenets Of Zero Trust Network Access Model Zero Trust Security Model. Dispense information and present a thorough explanation of Continuous Authentication, Data Protection, Facilitate Least Privilege Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
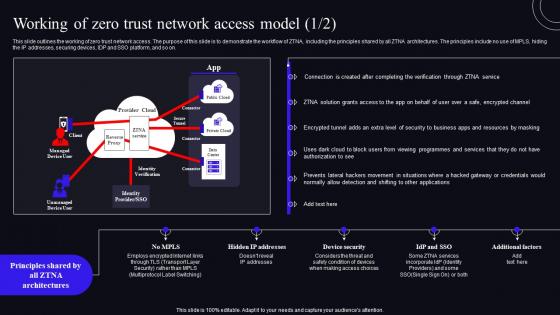 Working Of Zero Trust Network Access Model Zero Trust Security Model
Working Of Zero Trust Network Access Model Zero Trust Security ModelThis slide outlines the working of zero trust network access. The purpose of this slide is to demonstrate the workflow of ZTNA, including the principles shared by all ZTNA architectures. The principles include no use of MPLS, hiding the IP addresses, securing devices, IDP and SSO platform, and so on. Deliver an outstanding presentation on the topic using this Working Of Zero Trust Network Access Model Zero Trust Security Model. Dispense information and present a thorough explanation of Demonstrate, Architectures, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
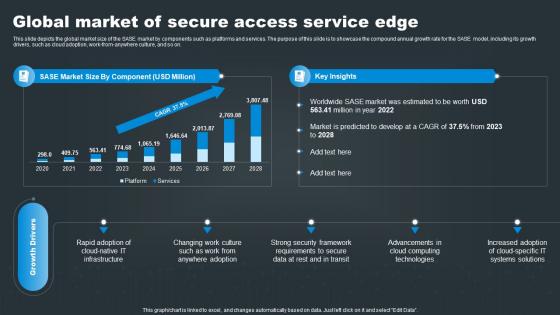 SASE Network Security Global Market Of Secure Access Service Edge
SASE Network Security Global Market Of Secure Access Service EdgeThis slide depicts the global market size of the SASE market by components such as platforms and services. The purpose of this slide is to showcase the compound annual growth rate for the SASE model, including its growth drivers, such as cloud adoption, work from anywhere culture, and so on. Deliver an outstanding presentation on the topic using this SASE Network Security Global Market Of Secure Access Service Edge. Dispense information and present a thorough explanation of Service, Secure, Global using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
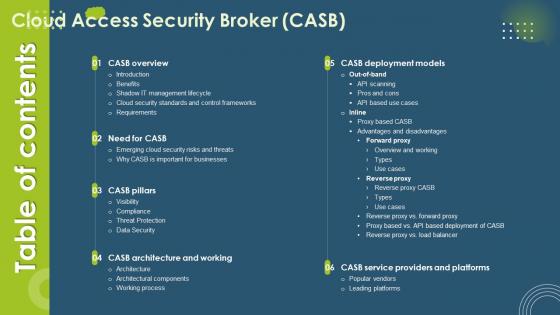 Table Of Contents For Cloud Access Security Broker CASB V2 Ppt Ideas Design Inspiration
Table Of Contents For Cloud Access Security Broker CASB V2 Ppt Ideas Design InspirationIntroducing Table Of Contents For Cloud Access Security Broker CASB V2 Ppt Ideas Design Inspiration to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Shadow IT Management Lifecycle, Threat Protection, Data Security, Emerging Cloud Security Risks And Threats, using this template. Grab it now to reap its full benefits.
-
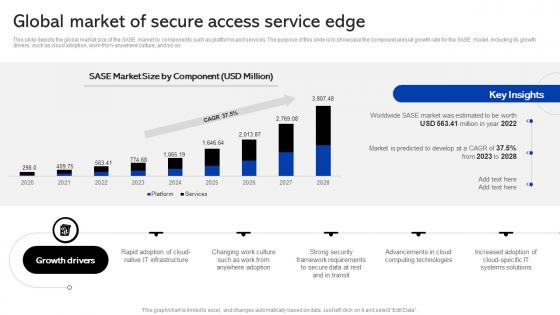 Sase Security Global Market Of Secure Access Service Edge
Sase Security Global Market Of Secure Access Service EdgeThis slide depicts the global market size of the SASE market by components such as platforms and services. The purpose of this slide is to showcase the compound annual growth rate for the SASE model, including its growth drivers, such as cloud adoption, work-from-anywhere culture, and so on. Present the topic in a bit more detail with this Sase Security Global Market Of Secure Access Service Edge. Use it as a tool for discussion and navigation on Service, Technologies, Advancements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
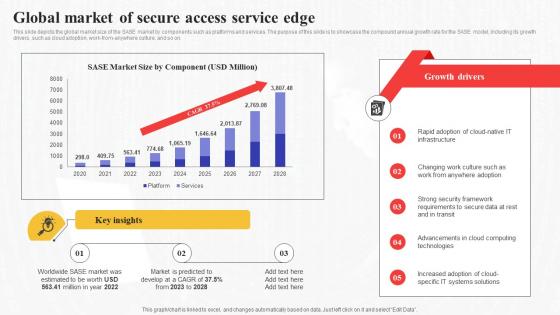 Global Market Of Secure Access Service Edge Secure Access Service Edge Sase
Global Market Of Secure Access Service Edge Secure Access Service Edge SaseThis slide depicts the global market size of the SASE market by components such as platforms and services. The purpose of this slide is to showcase the compound annual growth rate for the SASE model, including its growth drivers, such as cloud adoption, work-from-anywhere culture, and so on. Present the topic in a bit more detail with this Global Market Of Secure Access Service Edge Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Framework, Requirements, Advancements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents For Secure Access Service Edge Sase
Table Of Contents For Secure Access Service Edge SaseDeliver an outstanding presentation on the topic using this Table Of Contents For Secure Access Service Edge Sase. Dispense information and present a thorough explanation of Traditional Network Security Problems, SASE Architecture And Working, Importance Of SASE Model using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
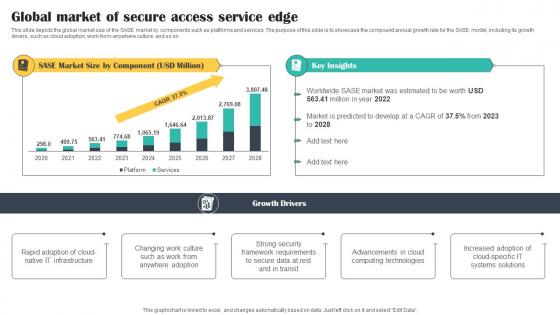 Global Market Of Secure Access Service Edge Cloud Security Model
Global Market Of Secure Access Service Edge Cloud Security ModelThis slide depicts the global market size of the SASE market by components such as platforms and services. The purpose of this slide is to showcase the compound annual growth rate for the SASE model, including its growth drivers, such as cloud adoption, work from anywhere culture, and so on. Deliver an outstanding presentation on the topic using this Global Market Of Secure Access Service Edge Cloud Security Model. Dispense information and present a thorough explanation of Global, Market, Secure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
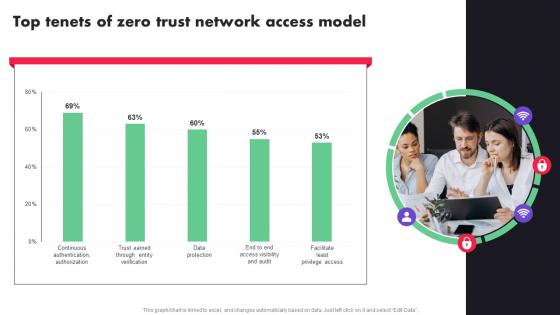 Top Tenets Of Zero Trust Network Access Model Ppt File Example
Top Tenets Of Zero Trust Network Access Model Ppt File ExampleDeliver an outstanding presentation on the topic using this Top Tenets Of Zero Trust Network Access Model Ppt File Example. Dispense information and present a thorough explanation of Top Tenets, Zero Trust Network, Access Model using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
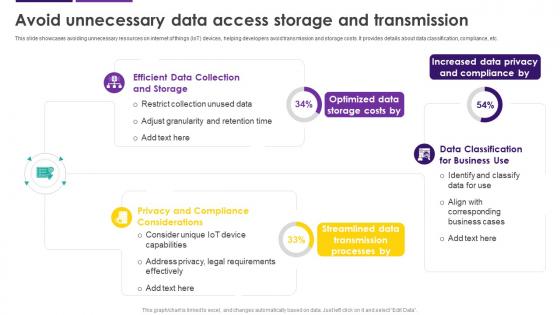 Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SS
Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SSThis slide showcases avoiding unnecessary resources on internet of things IoT devices, helping developers avoid transmission and storage costs. It provides details about data classification, compliance, etc. Deliver an outstanding presentation on the topic using this Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of Privacy And Compliance Considerations, Data Privacy And Compliance, Data Access Storage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
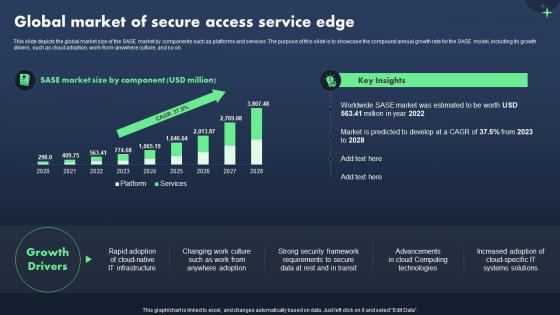 Sase Model Global Market Of Secure Access Service Edge
Sase Model Global Market Of Secure Access Service EdgeThis slide depicts the global market size of the SASE market by components such as platforms and services. The purpose of this slide is to showcase the compound annual growth rate for the SASE model, including its growth drivers, such as cloud adoption, work-from-anywhere culture, and so on. Present the topic in a bit more detail with this Sase Model Global Market Of Secure Access Service Edge. Use it as a tool for discussion and navigation on Secure Access Service Edge. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
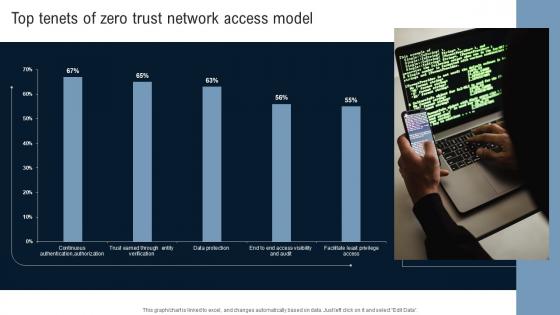 Top Tenets Of Zero Trust Network Access Model Identity Defined Networking
Top Tenets Of Zero Trust Network Access Model Identity Defined NetworkingPresent the topic in a bit more detail with this Top Tenets Of Zero Trust Network Access Model Identity Defined Networking Use it as a tool for discussion and navigation on Top Tenets, Trust Network, Access Model This template is free to edit as deemed fit for your organization. Therefore download it now.
-
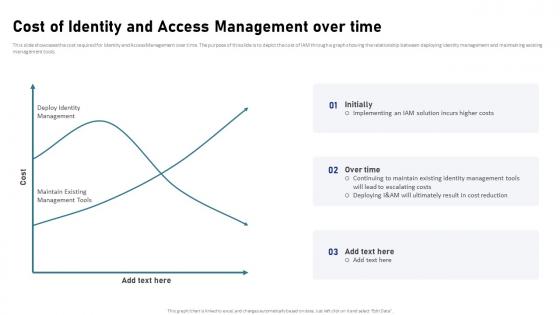 IAM Process For Effective Access Cost Of Identity And Access Management Over Time
IAM Process For Effective Access Cost Of Identity And Access Management Over TimeThis slide showcases the cost required for Identity and Access Management over time. The purpose of this slide is to depict the cost of IAM through a graph showing the relationship between deploying identity management and maintaining existing management tools. Deliver an outstanding presentation on the topic using this IAM Process For Effective Access Cost Of Identity And Access Management Over Time. Dispense information and present a thorough explanation of Cost Of Identity And Access, Management Over Time, Existing Management Tools using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
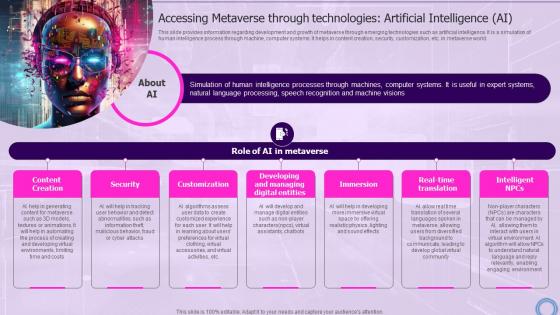 Accessing Artificial Intelligence Ai Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Artificial Intelligence Ai Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as artificial intelligence. It is a simulation of human intelligence process through machine, computer systems. It helps in content creation, security, customization, etc. in metaverse world. Introducing Accessing Artificial Intelligence Ai Decoding Digital Reality Of Physical World With Megaverse AI SS V to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Customization, Developing And Managing Digital Entities, Technologies, using this template. Grab it now to reap its full benefits.
-
 Accessing Extended Reality Xr Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Extended Reality Xr Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as extended reality. It is combination of AR, VR and MR for users to interact with each other in metaverse space. Increase audience engagement and knowledge by dispensing information using Accessing Extended Reality Xr Decoding Digital Reality Of Physical World With Megaverse AI SS V. This template helps you present information on seven stages. You can also present information on Technologies, Development, Growth using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
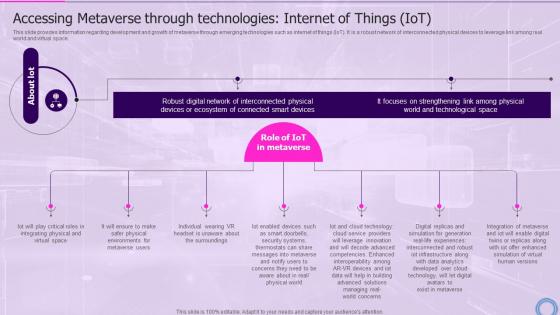 Accessing Internet Of Things Iot Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Internet Of Things Iot Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as internet of things IoT. It is a robust network of interconnected physical devices to leverage link among real world and virtual space. Introducing Accessing Internet Of Things Iot Decoding Digital Reality Of Physical World With Megaverse AI SS V to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Technologies, Competencies, Environments, using this template. Grab it now to reap its full benefits.
-
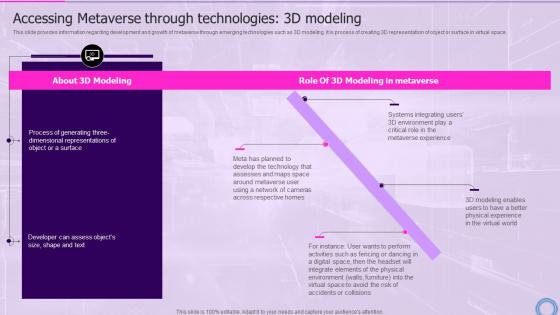 Accessing Metaverse 3d Modeling Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Metaverse 3d Modeling Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as 3D modeling. It is process of creating 3D representation of object or surface in virtual space. Present the topic in a bit more detail with this Accessing Metaverse 3d Modeling Decoding Digital Reality Of Physical World With Megaverse AI SS V. Use it as a tool for discussion and navigation on Technologies, Environment, Experience. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
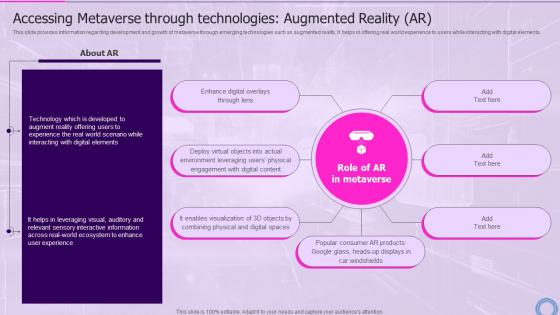 Accessing Metaverse Augmented Ar Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Metaverse Augmented Ar Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as augmented reality. It helps in offering real world experience to users while interacting with digital elements. Introducing Accessing Metaverse Augmented Ar Decoding Digital Reality Of Physical World With Megaverse AI SS V to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Technologies, Environment, Visualization, using this template. Grab it now to reap its full benefits.
-
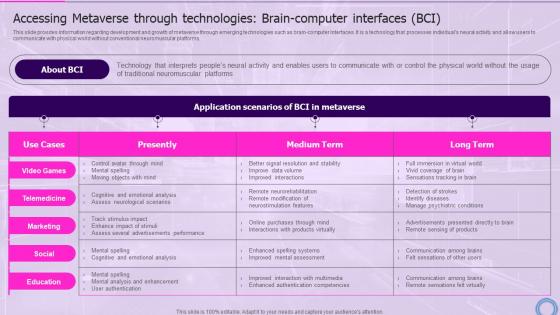 Accessing Metaverse Interfaces Bci Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Metaverse Interfaces Bci Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as brain-computer interfaces. It is a technology that processes individuals neural activity and allow users to communicate with physical world without conventional neuromuscular platforms. Deliver an outstanding presentation on the topic using this Accessing Metaverse Interfaces Bci Decoding Digital Reality Of Physical World With Megaverse AI SS V. Dispense information and present a thorough explanation of Technologies, Conventional, Neuromuscular using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
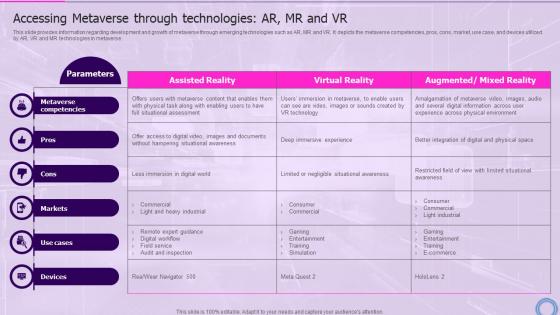 Accessing Technologies Ar Mr And Vr Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Technologies Ar Mr And Vr Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as AR, MR and VR. It depicts the metaverse competencies, pros, cons, market, use case, and devices utilized by AR, VR and MR technologies in metaverse. Present the topic in a bit more detail with this Accessing Technologies Ar Mr And Vr Decoding Digital Reality Of Physical World With Megaverse AI SS V. Use it as a tool for discussion and navigation on Technologies, Competencies, Development. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
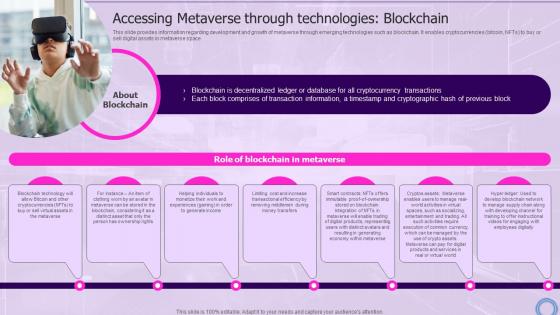 Accessing Technologies Blockchain Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Technologies Blockchain Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as blockchain. It enables cryptocurrencies bitcoin, NFTs to buy or sell digital assets in metaverse space. Increase audience engagement and knowledge by dispensing information using Accessing Technologies Blockchain Decoding Digital Reality Of Physical World With Megaverse AI SS V. This template helps you present information on seven stages. You can also present information on Technologies, Cryptocurrency, Transactions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
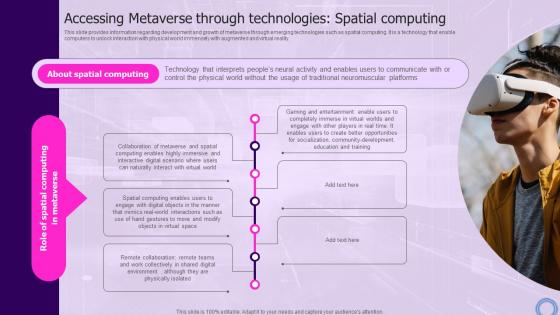 Accessing Technologies Computing Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Technologies Computing Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as spatial computing. It is a technology that enable computers to unlock interaction with physical world immensely with augmented and virtual reality. Introducing Accessing Technologies Computing Decoding Digital Reality Of Physical World With Megaverse AI SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Technologies, Communicate, Development, using this template. Grab it now to reap its full benefits.
-
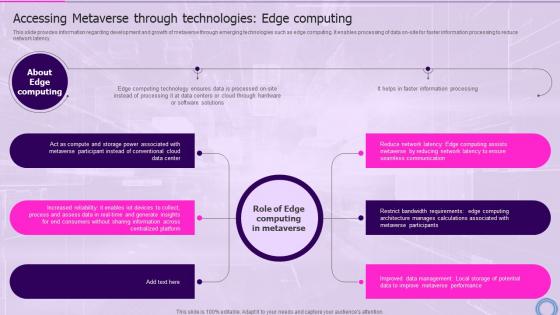 Accessing Technologies Edge Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Technologies Edge Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as edge computing. It enables processing of data on-site for faster information processing to reduce network latency. Increase audience engagement and knowledge by dispensing information using Accessing Technologies Edge Decoding Digital Reality Of Physical World With Megaverse AI SS V. This template helps you present information on six stages. You can also present information on Technologies, Information, Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
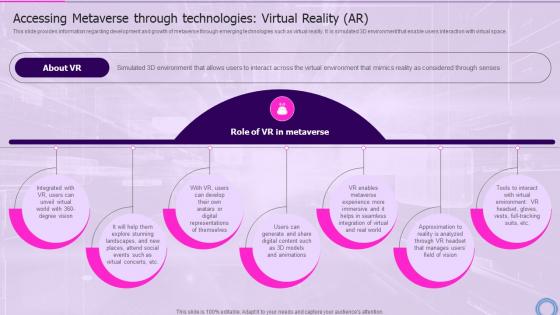 Accessing Technologies Virtual Reality Decoding Digital Reality Of Physical World With Megaverse AI SS V
Accessing Technologies Virtual Reality Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as virtual reality. It is simulated 3D environment that enable users interaction with virtual space. Introducing Accessing Technologies Virtual Reality Decoding Digital Reality Of Physical World With Megaverse AI SS V to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Representation, Approximation, Environment, using this template. Grab it now to reap its full benefits.
-
 How Metaverse Can Be Accessed By Decoding Digital Reality Of Physical World With Megaverse AI SS V
How Metaverse Can Be Accessed By Decoding Digital Reality Of Physical World With Megaverse AI SS VThis slide provides information regarding different ways through metaverse can be executed by connecting with VR interface such as headset, game console, to gain immersive metaverse experience. Present the topic in a bit more detail with this How Metaverse Can Be Accessed By Decoding Digital Reality Of Physical World With Megaverse AI SS V. Use it as a tool for discussion and navigation on Metaverse, Development, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
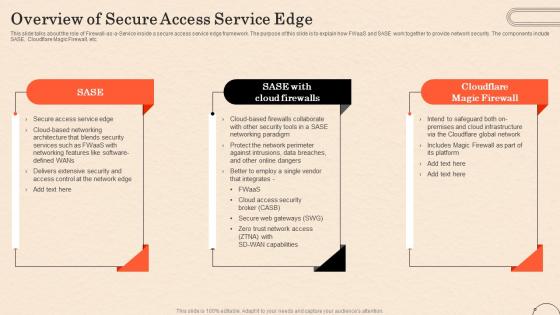 Firewall As A Service Fwaas Overview Of Secure Access Service Edge
Firewall As A Service Fwaas Overview Of Secure Access Service EdgeThis slide talks about the role of Firewall-as-a-Service inside a secure access service edge framework. The purpose of this slide is to explain how FWaaS and SASE work together to provide network security. The components include SASE, Cloudflare Magic Firewall, etc. Increase audience engagement and knowledge by dispensing information using Firewall As A Service Fwaas Overview Of Secure Access Service Edge. This template helps you present information on three stages. You can also present information on Cloudflare Global Network, Cloud Infrastructure, Cloud Access Security Broker, Secure Web Gateways, Zero Trust Network Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Media In Customer Service Models Of Access To Information And Communication Technology
Social Media In Customer Service Models Of Access To Information And Communication TechnologyThis slide describes the models of access described by scholar Mark Warschauer as a framework for examining information and communication technology accessibility. The models include devices, conduits, and literacy. Increase audience engagement and knowledge by dispensing information using Social Media In Customer Service Models Of Access To Information And Communication Technology. This template helps you present information on three stages. You can also present information on Scholar Mark Warschauer, Framework For Examining Information, Communication Technology Accessibility using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
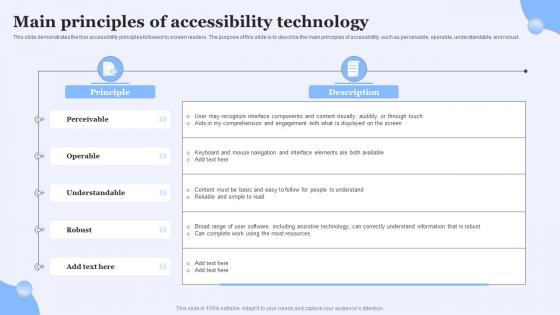 Screen Reader Friendly Website Main Principles Of Accessibility Technology
Screen Reader Friendly Website Main Principles Of Accessibility TechnologyThis slide demonstrates the four accessibility principles followed by screen readers. The purpose of this slide is to describe the main principles of accessibility, such as perceivable, operable, understandable, and robust. Deliver an outstanding presentation on the topic using this Screen Reader Friendly Website Main Principles Of Accessibility Technology. Dispense information and present a thorough explanation of Demonstrates, Accessibility Principles, Such As Perceivable, Understandable And Robust, Accessibility Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
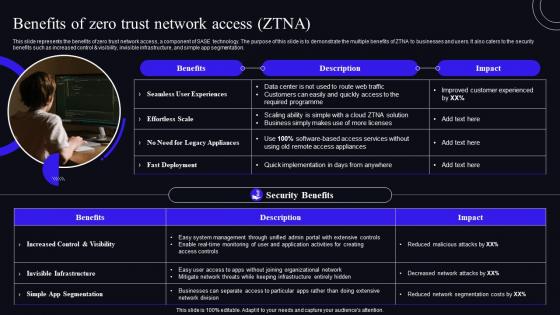 Benefits Of Zero Trust Network Access ZTNA Zero Trust Security Model
Benefits Of Zero Trust Network Access ZTNA Zero Trust Security ModelThis Slide Represents The Benefits Of Zero Trust Network Access, A Component Of SASE Technology. The Purpose Of This Slide Is To Demonstrate The Multiple Benefits Of ZTNA To Businesses And Users. It Also Caters To The Security Benefits Such As Increased Control And Visibility, Invisible Infrastructure, And Simple App Segmentation. Present The Topic In A Bit More Detail With This Benefits Of Zero Trust Network Access ZTNA Zero Trust Security Model. Use It As A Tool For Discussion And Navigation On Deployment, Experiences, Appliances. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
 Challenges Of VPN Based Remote Access Solutions Zero Trust Security Model
Challenges Of VPN Based Remote Access Solutions Zero Trust Security ModelThis slide outlines the limitations of virtual private network-based remote access services. The purpose of this slide is to showcase the various challenges of the VPN network system and how the zero trust network model can overcome those issues. Present the topic in a bit more detail with this Challenges Of VPN Based Remote Access Solutions Zero Trust Security Model. Use it as a tool for discussion and navigation on Extreme Implicit Trust, Performance Problems, Insufficient Granular. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Critical Principles Of Zero Trust Network Access Model Zero Trust Security Model
Critical Principles Of Zero Trust Network Access Model Zero Trust Security ModelThis slide illustrates the key principles of zero trust network access model, including their impact. The purpose of this slide is to highlight the primary principles of the ZTNA model, including least privilege access, micro-segmentation, MFA, device validation, and monitoring everything. Present the topic in a bit more detail with this Critical Principles Of Zero Trust Network Access Model Zero Trust Security Model. Use it as a tool for discussion and navigation on Description, Segmentation, Validation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
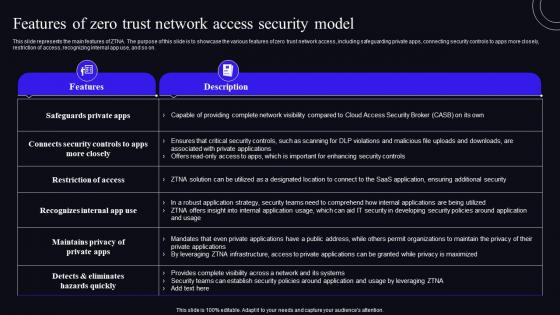 Features Of Zero Trust Network Access Security Model Zero Trust Security Model
Features Of Zero Trust Network Access Security Model Zero Trust Security ModelThis slide represents the main features of ZTNA. The purpose of this slide is to showcase the various features of zero trust network access, including safeguarding private apps, connecting security controls to apps more closely, restriction of access, recognizing internal app use, and so on. Present the topic in a bit more detail with this Features Of Zero Trust Network Access Security Model Zero Trust Security Model. Use it as a tool for discussion and navigation on Organizations, Applications, Infrastructure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
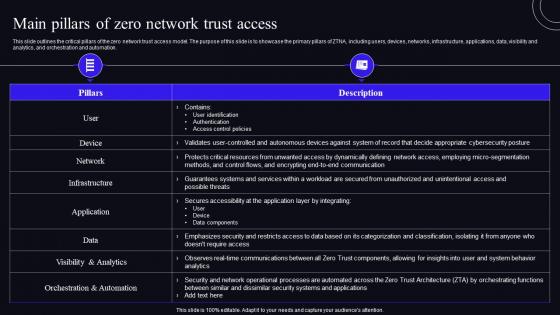 Main Pillars Of Zero Network Trust Access Zero Trust Security Model
Main Pillars Of Zero Network Trust Access Zero Trust Security ModelThis slide outlines the critical pillars of the zero network trust access model. The purpose of this slide is to showcase the primary pillars of ZTNA, including users, devices, networks, infrastructure, applications, data, visibility and analytics, and orchestration and automation. Present the topic in a bit more detail with this Main Pillars Of Zero Network Trust Access Zero Trust Security Model. Use it as a tool for discussion and navigation on Application, Infrastructure, Orchestration Automation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
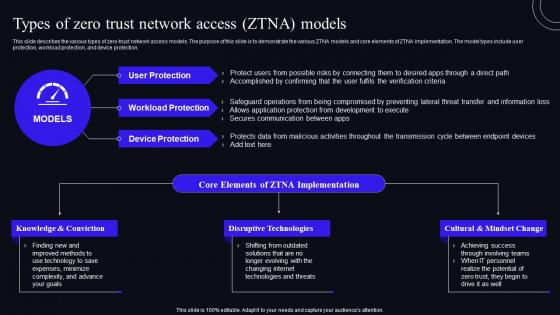 Types Of Zero Trust Network Access ZTNA Models Zero Trust Security Model
Types Of Zero Trust Network Access ZTNA Models Zero Trust Security ModelThis Slide Describes The Various Types Of Zero-Trust Network Access Models. The Purpose Of This Slide Is To Demonstrate The Various ZTNA Models And Core Elements Of ZTNA Implementation. The Model Types Include User Protection, Workload Protection, And Device Protection. Present The Topic In A Bit More Detail With This Types Of Zero Trust Network Access ZTNA Models Zero Trust Security Model. Use It As A Tool For Discussion And Navigation On Knowledge Conviction, Disruptive Technologies, Cultural Mindset Change. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
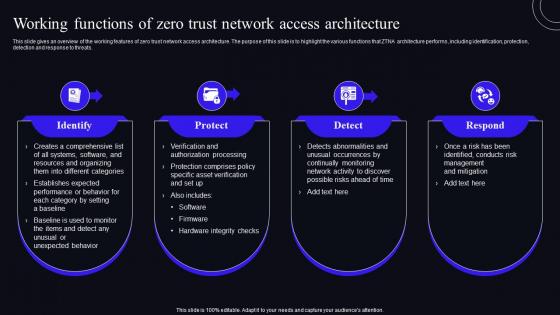 Working Functions Of Zero Trust Network Access Architecture Zero Trust Security Model
Working Functions Of Zero Trust Network Access Architecture Zero Trust Security ModelThis slide gives an overview of the working features of zero trust network access architecture. The purpose of this slide is to highlight the various functions that ZTNA architecture performs, including identification, protection, detection and response to threats. Introducing Working Functions Of Zero Trust Network Access Architecture Zero Trust Security Model to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Architecture, Abnormalities, Processing, using this template. Grab it now to reap its full benefits.
-
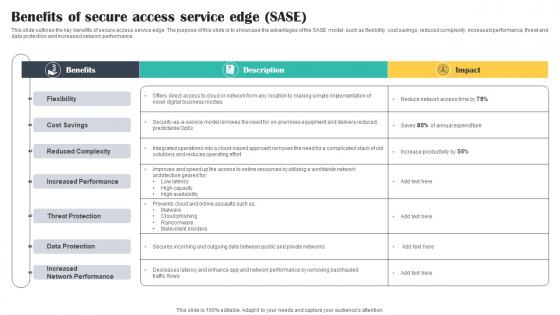 Benefits Of Secure Access Service Edge SASE Cloud Security Model
Benefits Of Secure Access Service Edge SASE Cloud Security ModelThis slide outlines the key benefits of secure access service edge. The purpose of this slide is to showcase the advantages of the SASE model, such as flexibility, cost savings, reduced complexity, increased performance, threat and data protection and increased network performance. Present the topic in a bit more detail with this Benefits Of Secure Access Service Edge SASE Cloud Security Model. Use it as a tool for discussion and navigation on Secure, Benefits, Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
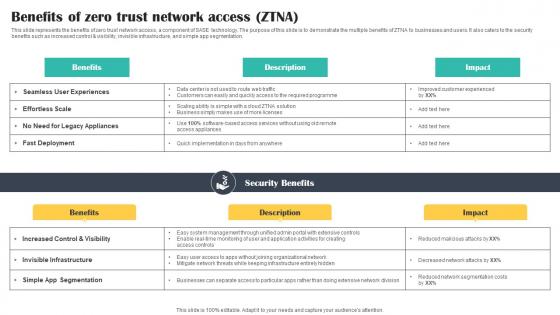 Benefits Of Zero Trust Network Access ZTNA Cloud Security Model
Benefits Of Zero Trust Network Access ZTNA Cloud Security ModelThis slide represents the benefits of zero trust network access, a component of SASE technology. The purpose of this slide is to demonstrate the multiple benefits of ZTNA to businesses and users. It also caters to the security benefits such as increased control and visibility, invisible infrastructure, and simple app segmentation. Deliver an outstanding presentation on the topic using this Benefits Of Zero Trust Network Access ZTNA Cloud Security Model. Dispense information and present a thorough explanation of Benefits, Description, Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
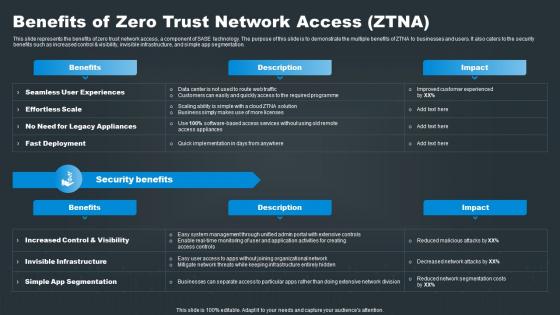 Benefits Of Zero Trust Network Access ZTNA SASE Network Security
Benefits Of Zero Trust Network Access ZTNA SASE Network SecurityThis slide represents the benefits of zero trust network access, a component of SASE technology. The purpose of this slide is to demonstrate the multiple benefits of ZTNA to businesses and users. It also caters to the security benefits such as increased control and visibility, invisible infrastructure, and simple app segmentation. Present the topic in a bit more detail with this Benefits Of Zero Trust Network Access ZTNA SASE Network Security. Use it as a tool for discussion and navigation on Benefits, Description, Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
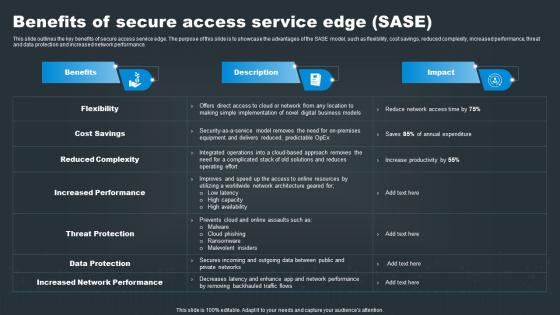 SASE Network Security Benefits Of Secure Access Service Edge SASE
SASE Network Security Benefits Of Secure Access Service Edge SASEThis slide outlines the key benefits of secure access service edge. The purpose of this slide is to showcase the advantages of the SASE model, such as flexibility, cost savings, reduced complexity, increased performance, threat and data protection and increased network performance. Deliver an outstanding presentation on the topic using this SASE Network Security Benefits Of Secure Access Service Edge SASE. Dispense information and present a thorough explanation of Service, Secure, Benefits using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SASE Network Security Pillars Of Cloud Access Security Broker
SASE Network Security Pillars Of Cloud Access Security BrokerThis slide represents the four major pillars of cloud access security broker. The purpose of this slide is to showcase the main pillars of implementing a cloud access security broker. The pillars include compliance, visibility, threat protection, and data security. Increase audience engagement and knowledge by dispensing information using SASE Network Security Pillars Of Cloud Access Security Broker. This template helps you present information on four stages. You can also present information on Security, Prevention, Visibility using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
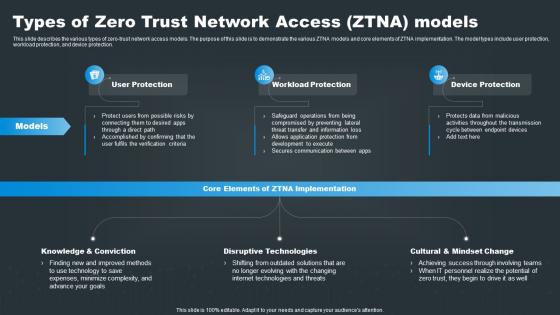 SASE Network Security Types Of Zero Trust Network Access ZTNA Models
SASE Network Security Types Of Zero Trust Network Access ZTNA ModelsThis slide describes the various types of zero trust network access models. The purpose of this slide is to demonstrate the various ZTNA models and core elements of ZTNA implementation. The model types include user protection, workload protection, and device protection. Introducing SASE Network Security Types Of Zero Trust Network Access ZTNA Models to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Protection, Workload, Device, using this template. Grab it now to reap its full benefits.
-
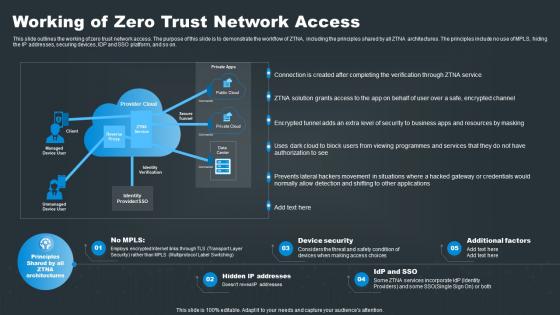 SASE Network Security Working Of Zero Trust Network Access
SASE Network Security Working Of Zero Trust Network AccessThis slide outlines the working of zero trust network access. The purpose of this slide is to demonstrate the workflow of ZTNA, including the principles shared by all ZTNA architectures. The principles include no use of MPLS, hiding the IP addresses, securing devices, IDP and SSO platform, and so on. Increase audience engagement and knowledge by dispensing information using SASE Network Security Working Of Zero Trust Network Access. This template helps you present information on five stages. You can also present information on Access, Connection, Resources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
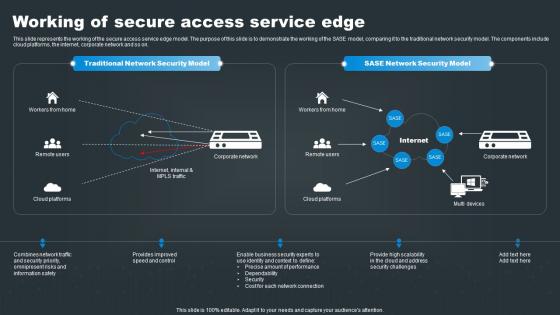 Working Of Secure Access Service Edge SASE Network Security
Working Of Secure Access Service Edge SASE Network SecurityThis slide represents the working of the secure access service edge model. The purpose of this slide is to demonstrate the working of the SASE model, comparing it to the traditional network security model. The components include cloud platforms, the internet, corporate network and so on. Deliver an outstanding presentation on the topic using this Working Of Secure Access Service Edge SASE Network Security. Dispense information and present a thorough explanation of Security, Network, Challenges using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
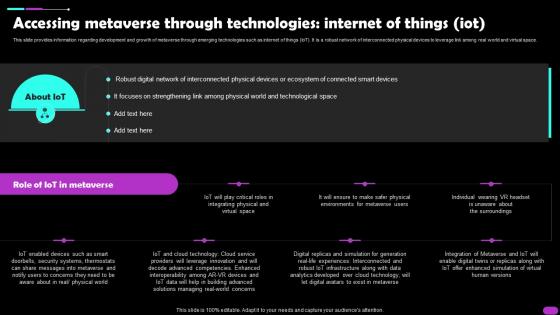 Accessing Metaverse Through Technologies Internet Of Things IOT Metaverse Everything AI SS V
Accessing Metaverse Through Technologies Internet Of Things IOT Metaverse Everything AI SS VThis slide provides information regarding development and growth of metaverse through emerging technologies such as internet of things IoT. It is a robust network of interconnected physical devices to leverage link among real world and virtual space. Present the topic in a bit more detail with this Accessing Metaverse Through Technologies Internet Of Things IOT Metaverse Everything AI SS V. Use it as a tool for discussion and navigation on Digital Network, Technological Space, Smart Devices This template is free to edit as deemed fit for your organization. Therefore download it now.
-
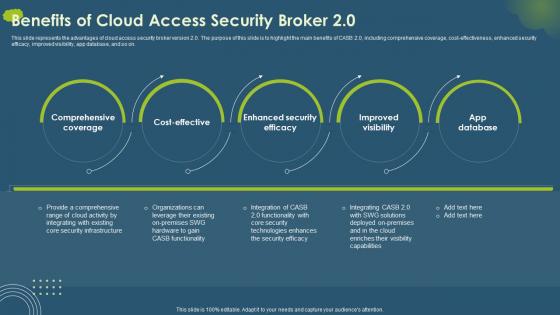 Benefits Of Cloud Access Security Broker 2 0 Cloud Access Security Broker CASB V2
Benefits Of Cloud Access Security Broker 2 0 Cloud Access Security Broker CASB V2This slide represents the advantages of cloud access security broker version 2.0. The purpose of this slide is to highlight the main benefits of CASB 2.0, including comprehensive coverage, cost-effectiveness, enhanced security efficacy, improved visibility, app database, and so on. Increase audience engagement and knowledge by dispensing information using Benefits Of Cloud Access Security Broker 2 0 Cloud Access Security Broker CASB V2. This template helps you present information on five stages. You can also present information on Cloud Access Security Broker, Comprehensive Coverage, Enhanced Security Efficacy, Cost Effectiveness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based Deployment
Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based DeploymentThis slide represents the benefits and drawbacks of proxy-based CASB deployment. The purpose of this slide is to showcase the various pros and cons of proxy-based cloud access security brokers and the advantages cover flexibility, secure SaaS applications, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based Deployment. This template helps you present information on two stages. You can also present information on Cloud Access Security Brokers, Cover Flexibility, Secure SaaS Applications, Enforcement Of Security Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
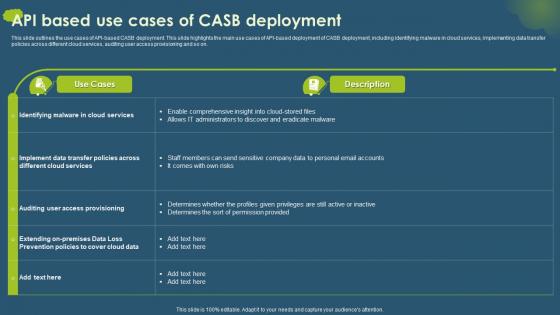 Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB Deployment
Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB DeploymentThis slide outlines the use cases of API-based CASB deployment. This slide highlights the main use cases of API-based deployment of CASB deployment, including identifying malware in cloud services, implementing data transfer policies across different cloud services, auditing user access provisioning and so on. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB Deployment. Dispense information and present a thorough explanation of Malware In Cloud Services, Data Transfer Policies, Cloud Services, Auditing User Access Provisioning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 Benefits Of Cloud Access Security Broker
Cloud Access Security Broker CASB V2 Benefits Of Cloud Access Security BrokerThis slide outlines the different advantages of Cloud Access Security Broker technology. This slide highlights the pros of CASB technology, including risk visibility, cyber threat prevention, granular cloud usage control, shadow IT assessment and management, DLP, managing privileged accounts and admin and controlled data sharing. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Benefits Of Cloud Access Security Broker. Use it as a tool for discussion and navigation on Cyber Threat Prevention, Granular Cloud Usage Control, Data Loss Prevention, Controlled External File Sharing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 For Table Of Contents Ppt Ideas Designs Download
Cloud Access Security Broker CASB V2 For Table Of Contents Ppt Ideas Designs DownloadIntroducing Cloud Access Security Broker CASB V2 For Table Of Contents Ppt Ideas Designs Download to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Shadow IT Management Lifecycle, Cloud Security Standards, Control Frameworks, Requirements, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Future Of Cloud Access Security Broker CASB 2 0
Cloud Access Security Broker CASB V2 Future Of Cloud Access Security Broker CASB 2 0This slide outlines the overview of Cloud Access Security Broker 2.0. The purpose of this slide is to showcase the various limitations of CASB version 1.0 and the emerging need for CASB 2.0. The components of CASB 2.0 include user authentication, web security, data loss prevention, advanced malware protection, etc. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Future Of Cloud Access Security Broker CASB 2 0. This template helps you present information on seven stages. You can also present information on Data Loss Prevention, Advanced Malware Protection, Managed Security Service, Endpoint Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
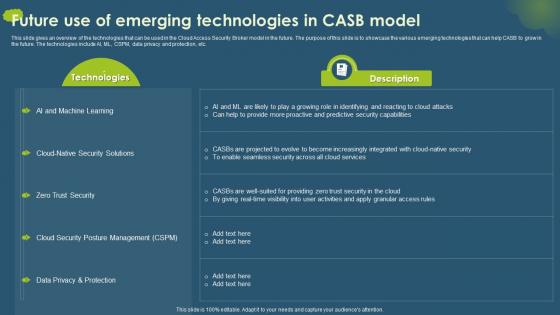 Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB Model
Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB ModelThis slide gives an overview of the technologies that can be used in the Cloud Access Security Broker model in the future. The purpose of this slide is to showcase the various emerging technologies that can help CASB to grow in the future. The technologies include AI, ML, CSPM, data privacy and protection, etc. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB Model. Dispense information and present a thorough explanation of Cloud Security Posture Management, Data Privacy And Protection, Zero Trust Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
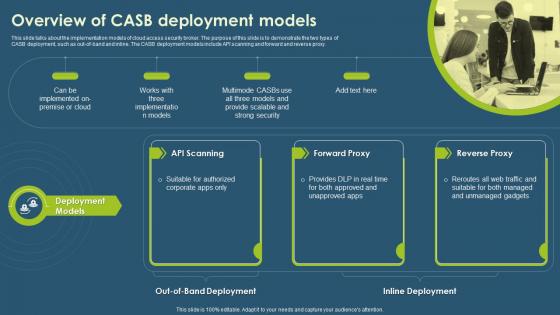 Cloud Access Security Broker CASB V2 Overview Of CASB Deployment Models
Cloud Access Security Broker CASB V2 Overview Of CASB Deployment ModelsThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Overview Of CASB Deployment Models. This template helps you present information on four stages. You can also present information on Cloud Access Security Broker, Unmanaged Gadgets, Inline Deployment, Scalable And Strong Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
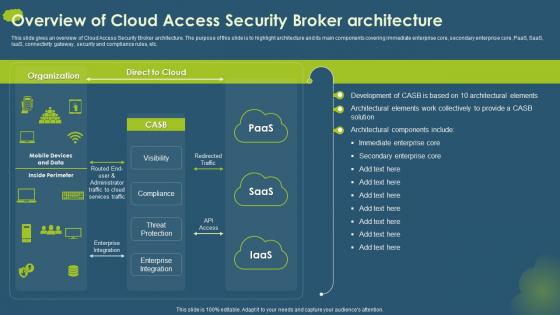 Cloud Access Security Broker CASB V2 Overview Of Cloud Access Security Broker Architecture
Cloud Access Security Broker CASB V2 Overview Of Cloud Access Security Broker ArchitectureThis slide gives an overview of Cloud Access Security Broker architecture. The purpose of this slide is to highlight architecture and its main components covering immediate enterprise core, secondary enterprise core, PaaS, SaaS, IaaS, connectivity gateway, security and compliance rules, etc. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Overview Of Cloud Access Security Broker Architecture. Dispense information and present a thorough explanation of Visibility, Compliance, Threat Protection, Enterprise Integration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
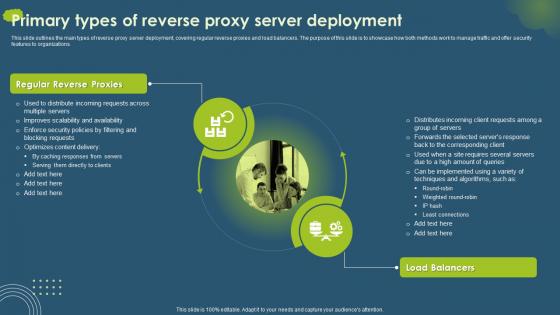 Cloud Access Security Broker CASB V2 Primary Types Of Reverse Proxy Server Deployment
Cloud Access Security Broker CASB V2 Primary Types Of Reverse Proxy Server DeploymentThis slide outlines the main types of reverse proxy server deployment, covering regular reverse proxies and load balancers. The purpose of this slide is to showcase how both methods work to manage traffic and offer security features to organizations. Introducing Cloud Access Security Broker CASB V2 Primary Types Of Reverse Proxy Server Deployment to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Regular Reverse Proxies, Load Balancers, Proxy Server Deployment, using this template. Grab it now to reap its full benefits.
-
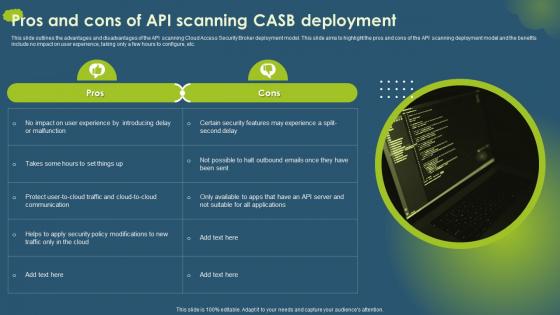 Cloud Access Security Broker CASB V2 Pros And Cons Of API Scanning CASB Deployment
Cloud Access Security Broker CASB V2 Pros And Cons Of API Scanning CASB DeploymentThis slide outlines the advantages and disadvantages of the API scanning Cloud Access Security Broker deployment model. This slide aims to highlight the pros and cons of the API scanning deployment model and the benefits include no impact on user experience, taking only a few hours to configure, etc. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Pros And Cons Of API Scanning CASB Deployment. This template helps you present information on one stages. You can also present information on Cloud Access Security, Broker Deployment Model, Scanning Deployment Model, Security Policy Modifications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


