Powerpoint Templates and Google slides for Accessible Approachable
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Approaches To Implement Zero Trust Network Access Cloud Security Model
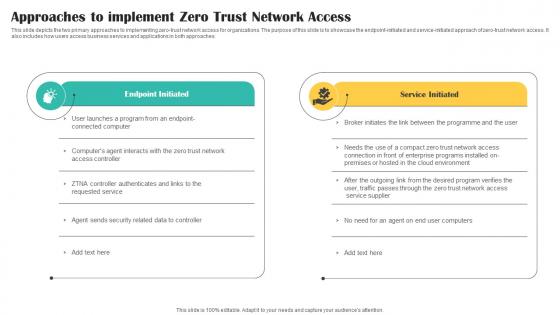
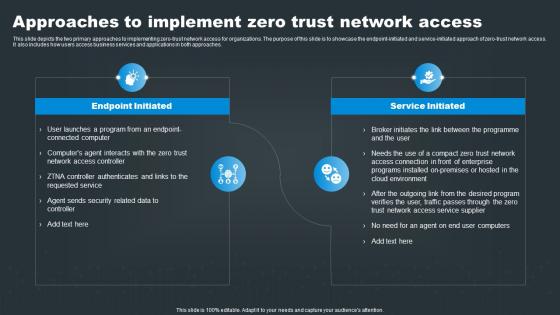
Approaches To Implement Zero Trust Network Access Cloud Security ModelThis slide depicts the two primary approaches to implementing zero trust network access for organizations. The purpose of this slide is to showcase the endpoint initiated and service initiated approach of zero-trust network access. It also includes how users access business services and applications in both approaches. Deliver an outstanding presentation on the topic using this Approaches To Implement Zero Trust Network Access Cloud Security Model. Dispense information and present a thorough explanation of Network, Access, Implement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SASE Network Security Approaches To Implement Zero Trust Network Access
SASE Network Security Approaches To Implement Zero Trust Network AccessThis slide depicts the two primary approaches to implementing zero trust network access for organizations. The purpose of this slide is to showcase the endpoint initiated and service initiated approach of zero trust network access. It also includes how users access business services and applications in both approaches. Increase audience engagement and knowledge by dispensing information using SASE Network Security Approaches To Implement Zero Trust Network Access. This template helps you present information on two stages. You can also present information on Program, Environment, Service using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Sase Security Approaches To Implement Zero Trust Network Access
Sase Security Approaches To Implement Zero Trust Network AccessThis slide depicts the two primary approaches to implementing zero-trust network access for organizations. The purpose of this slide is to showcase the endpoint-initiated and service-initiated approach of zero-trust network access. It also includes how users access business services and applications in both approaches. Deliver an outstanding presentation on the topic using this Sase Security Approaches To Implement Zero Trust Network Access. Dispense information and present a thorough explanation of Approaches, Organizations, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Approaches To Implement Zero Trust Network Access Secure Access Service Edge Sase
Approaches To Implement Zero Trust Network Access Secure Access Service Edge SaseThis slide depicts the two primary approaches to implementing zero-trust network access for organizations. The purpose of this slide is to showcase the endpoint-initiated and service-initiated approach of zero-trust network access. It also includes how users access business services and applications in both approaches. Deliver an outstanding presentation on the topic using this Approaches To Implement Zero Trust Network Access Secure Access Service Edge Sase. Dispense information and present a thorough explanation of Approaches, Endpoint Initiated, Service Initiated using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
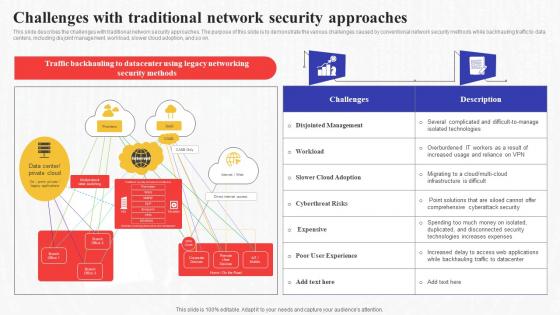 Challenges With Traditional Network Security Approaches Secure Access Service Edge Sase
Challenges With Traditional Network Security Approaches Secure Access Service Edge SaseThis slide describes the challenges with traditional network security approaches. The purpose of this slide is to demonstrate the various challenges caused by conventional network security methods while backhauling traffic to data centers, including disjoint management, workload, slower cloud adoption, and so on. Present the topic in a bit more detail with this Challenges With Traditional Network Security Approaches Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Approaches, Demonstrate, Conventional. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Sase Model Approaches To Implement Zero Trust Network Access
Sase Model Approaches To Implement Zero Trust Network AccessThis slide depicts the two primary approaches to implementing zero-trust network access for organizations. The purpose of this slide is to showcase the endpoint-initiated and service-initiated approach of zero-trust network access. It also includes how users access business services and applications in both approaches. Introducing Sase Model Approaches To Implement Zero Trust Network Access to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Service Initiated, Endpoint Initiated, using this template. Grab it now to reap its full benefits.
-
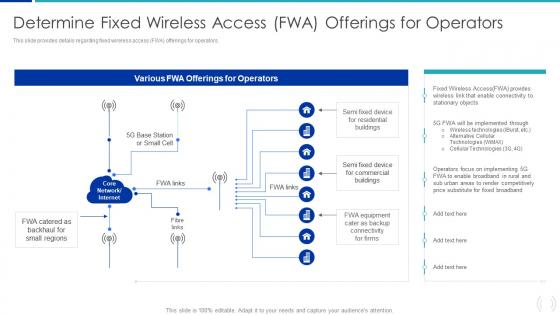 Determine Fixed Wireless Access FWA Offerings For Proactive Approach For 5G Deployment
Determine Fixed Wireless Access FWA Offerings For Proactive Approach For 5G DeploymentThis slide provides details regarding fixed wireless access FWA offerings for operators. Present the topic in a bit more detail with this Determine Fixed Wireless Access FWA Offerings For Proactive Approach For 5G Deployment. Use it as a tool for discussion and navigation on Wireless Technologies, Cellular Technologies, Fixed Broadband. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
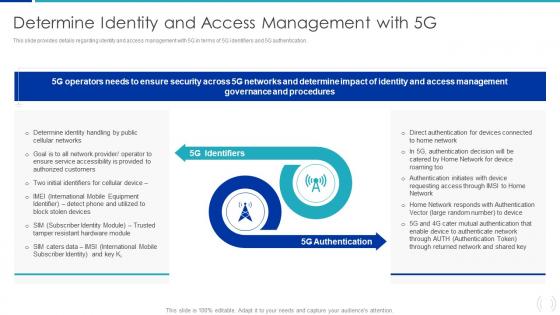 Determine Identity And Access Management With 5G Proactive Approach For 5G Deployment
Determine Identity And Access Management With 5G Proactive Approach For 5G DeploymentThis slide provides details regarding identity and access management with 5G in terms of 5G identifiers and 5G authentication. Introducing Determine Identity And Access Management With 5G Proactive Approach For 5G Deployment to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on 5G Identifiers, 5G Authentication, Governance, using this template. Grab it now to reap its full benefits.
-
 Components Of Brand Portfolio Strategy For Better Access Strategic Approach Toward Optimizing
Components Of Brand Portfolio Strategy For Better Access Strategic Approach Toward OptimizingThis slide covers the fundamental principles of creating an effective brand communication strategy. It includes guidelines such as building and leveraging strong corporate bonds, defining strategic objectives for brands, employing simple and clear brand architecture, etc. Introducing Components Of Brand Portfolio Strategy For Better Access Strategic Approach Toward Optimizing to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Value Relationship, Brand Positioning, Consumers, using this template. Grab it now to reap its full benefits.
-
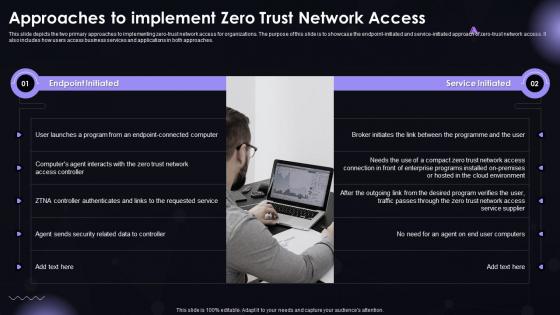 SASE IT Approaches To Implement Zero Trust Network Access Ppt Demonstration
SASE IT Approaches To Implement Zero Trust Network Access Ppt DemonstrationThis slide depicts the two primary approaches to implementing zero-trust network access for organizations. The purpose of this slide is to showcase the endpoint-initiated and service-initiated approach of zero-trust network access. It also includes how users access business services and applications in both approaches. Introducing SASE IT Approaches To Implement Zero Trust Network Access Ppt Demonstration to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Endpoint Initiated, Service Initiated, using this template. Grab it now to reap its full benefits.
-
 Plan business analysis approach define requirement architecture access risks
Plan business analysis approach define requirement architecture access risksPresenting this set of slides with name - Plan Business Analysis Approach Define Requirement Architecture Access Risks. This is an editable five stages graphic that deals with topics like Plan Business Analysis Approach, Define Requirement Architecture, Access Risks to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.