Powerpoint Templates and Google slides for Cloning Attack
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Clone Phishing As A Type Of Password Attack Training Ppt
Clone Phishing As A Type Of Password Attack Training PptPresenting Clone Phishing as a Type of Password Attack. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Clone Phishing Attacks Preventive Measures
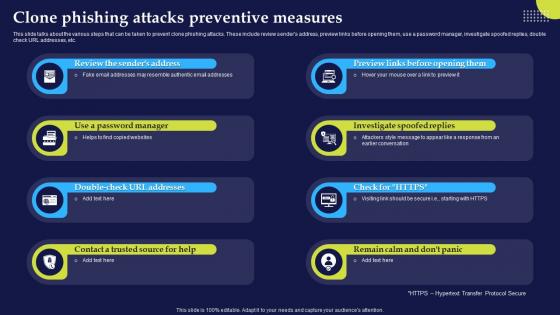
Phishing Attacks And Strategies To Mitigate Them V2 Clone Phishing Attacks Preventive MeasuresThis slide talks about the various steps that can be taken to prevent clone phishing attacks. These include review senders address, preview links before opening them, use a password manager, investigate spoofed replies, double check URL addresses, etc. Increase audience engagement and knowledge by dispensing information using Phishing Attacks And Strategies To Mitigate Them V2 Clone Phishing Attacks Preventive Measures. This template helps you present information on eight stages. You can also present information on Investigate Spoofed Replies, Clone Phishing Attacks Preventive, Resemble Authentic Email Addresses using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Examples Of Clone Phishing Cyber Scams
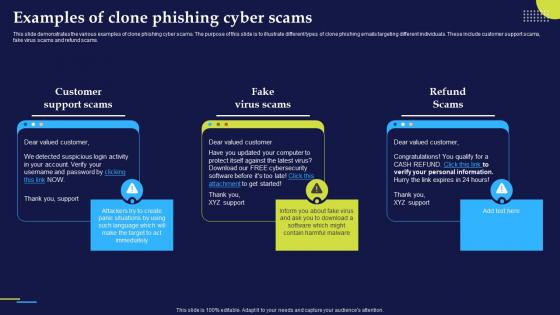
Phishing Attacks And Strategies To Mitigate Them V2 Examples Of Clone Phishing Cyber ScamsThis slide demonstrates the various examples of clone phishing cyber scams. The purpose of this slide is to illustrate different types of clone phishing emails targeting different individuals. These include customer support scams, fake virus scams and refund scams. Increase audience engagement and knowledge by dispensing information using Phishing Attacks And Strategies To Mitigate Them V2 Examples Of Clone Phishing Cyber Scams. This template helps you present information on three stages. You can also present information on Customer Support Scams, Fake Virus Scams, Refund Scams, Clone Phishing Cyber Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 K111 Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies To Mitigate Them V2
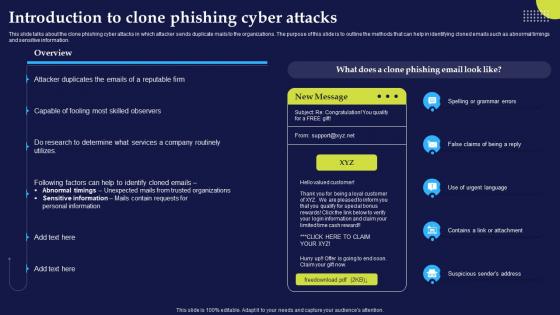
K111 Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies To Mitigate Them V2This slide talks about the clone phishing cyber attacks in which attacker sends duplicate mails to the organizations. The purpose of this slide is to outline the methods that can help in identifying cloned emails such as abnormal timings and sensitive information. Deliver an outstanding presentation on the topic using this K111 Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies To Mitigate Them V2. Dispense information and present a thorough explanation of Spelling Or Grammar Errors, Suspicious Senders Address, Clone Phishing Cyber Attacks, Routinely Utilizes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
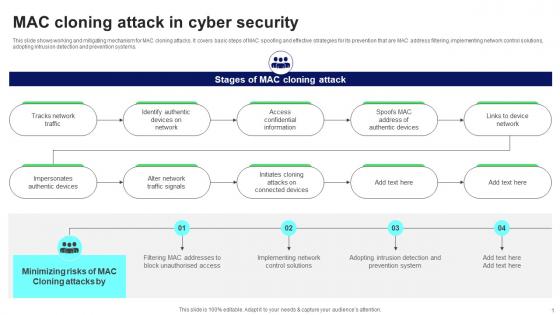 MAC Cloning Attack In Cyber Security
MAC Cloning Attack In Cyber SecurityThis slide shows working and mitigating mechanism for MAC cloning attacks. It covers basic steps of MAC spoofing and effective strategies for its prevention that are MAC address filtering, implementing network control solutions, adopting intrusion detection and prevention systems. Presenting our well structured MAC Cloning Attack In Cyber Security. The topics discussed in this slide are Network Traffic, Traffic Signals, Confidential Information. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
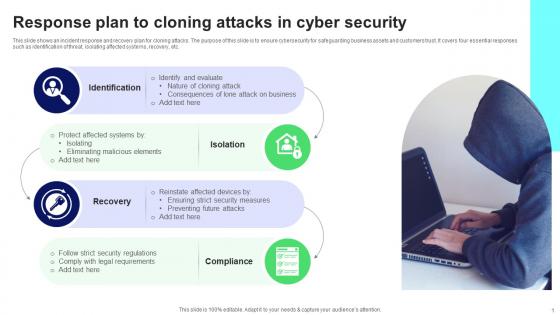 Response Plan To Cloning Attacks In Cyber Security
Response Plan To Cloning Attacks In Cyber SecurityThis slide shows an incident response and recovery plan for cloning attacks. The purpose of this slide is to ensure cybersecurity for safeguarding business assets and customers trust. It covers four essential responses such as identification of threat, isolating affected systems, recovery, etc. Presenting our set of slides with name Response Plan To Cloning Attacks In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloning Attack, Malicious Elements, Security Measures.
-
 Cyber Attacks On Ukraine Website Defacements DDOS Attacks And Website Clones
Cyber Attacks On Ukraine Website Defacements DDOS Attacks And Website ClonesThis slide represents the other attacks carried out by Russia on Ukraine, such as website defacement, distributed denial of service attacks, and website clones. Introducing Cyber Attacks On Ukraine Website Defacements DDOS Attacks And Website Clones to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Website Defacements Ddos Attacks And Website Clones, using this template. Grab it now to reap its full benefits.
-
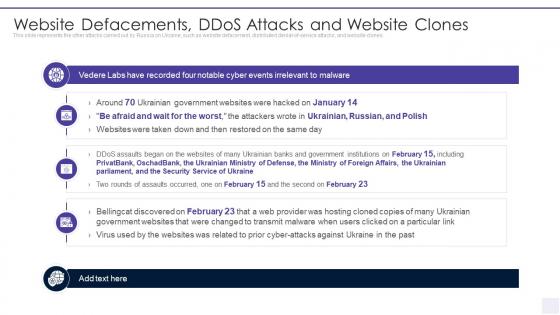 Wiper Malware Attack Website Defacements DDOS Attacks And Website Clones
Wiper Malware Attack Website Defacements DDOS Attacks And Website ClonesThis slide represents the other attacks carried out by Russia on Ukraine, such as website defacement, distributed denial of service attacks, and website clones. Present the topic in a bit more detail with this Wiper Malware Attack Website Defacements DDOS Attacks And Website Clones. Use it as a tool for discussion and navigation on Website Defacements Ddos Attacks And Website Clones. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ukraine and russia cyber warfare it website defacements ddos attacks and website clones
Ukraine and russia cyber warfare it website defacements ddos attacks and website clonesThis slide represents the other attacks carried out by Russia on Ukraine, such as website defacement, distributed denial of service attacks, and website clones. Introducing Ukraine And Russia Cyber Warfare It Website Defacements Ddos Attacks And Website Clones to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Government, Institutions, Defacements, using this template. Grab it now to reap its full benefits.
-
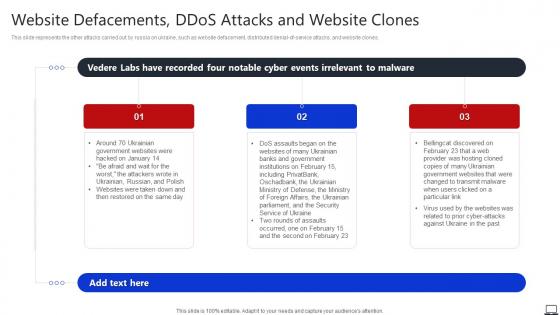 Website Defacements DDOS Attacks And Website Clones String Of Cyber Attacks Against
Website Defacements DDOS Attacks And Website Clones String Of Cyber Attacks AgainstThis slide represents the other attacks carried out by russia on ukraine, such as website defacement, distributed denial of service attacks, and website clones. Introducing Website Defacements DDOS Attacks And Website Clones String Of Cyber Attacks Against to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Government Websites, Attackers, Banks And Government, using this template. Grab it now to reap its full benefits.
-
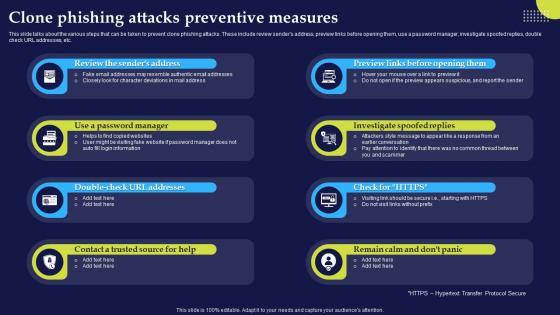 Clone Phishing Attacks Preventive Measures Phishing Attacks And Strategies
Clone Phishing Attacks Preventive Measures Phishing Attacks And StrategiesThis slide talks about the various steps that can be taken to prevent clone phishing attacks. These include review senders address, preview links before opening them, use a password manager, investigate spoofed replies, double check URL addresses, etc.Introducing Clone Phishing Attacks Preventive Measures Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Investigate Spoofed, Password Manager, Contact Trusted, using this template. Grab it now to reap its full benefits.
-
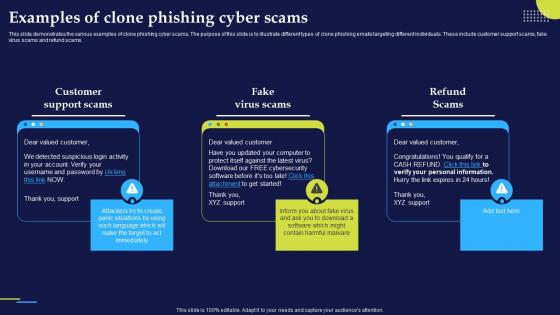 Examples Of Clone Phishing Cyber Scams Phishing Attacks And Strategies
Examples Of Clone Phishing Cyber Scams Phishing Attacks And StrategiesThis slide demonstrates the various examples of clone phishing cyber scams. The purpose of this slide is to illustrate different types of clone phishing emails targeting different individuals. These include customer support scams, fake virus scams and refund scams.Increase audience engagement and knowledge by dispensing information using Examples Of Clone Phishing Cyber Scams Phishing Attacks And Strategies. This template helps you present information on three stages. You can also present information on Detected Suspicious, Support Scams, Virus Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
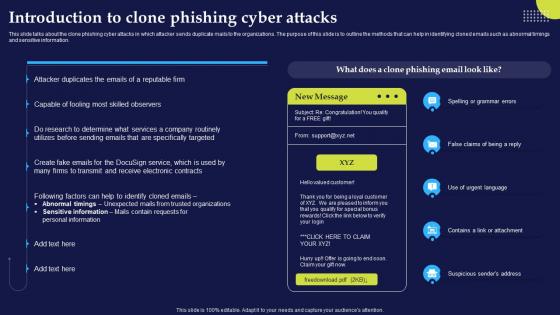 Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies
Introduction To Clone Phishing Cyber Attacks Phishing Attacks And StrategiesThis slide talks about the clone phishing cyber attacks in which attacker sends duplicate mails to the organizations. The purpose of this slide is to outline the methods that can help in identifying cloned emails such as abnormal timings and sensitive information.Present the topic in a bit more detail with this Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Personal Information, Sensitive Information, Abnormal Timings Unexpected. This template is free to edit as deemed fit for your organization. Therefore download it now.

