Powerpoint Templates and Google slides for Common Security Framework
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Most Common Information Security Threats Training Ppt
Most Common Information Security Threats Training PptPresenting Most Common Information Security Threats. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
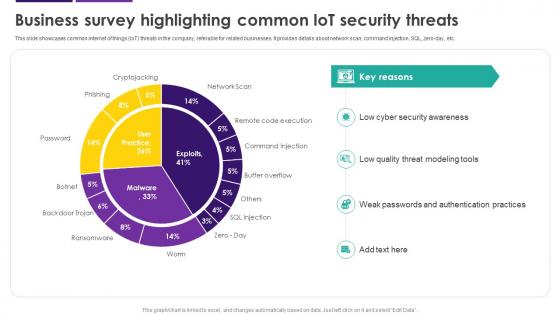 Business Survey Highlighting Common IoT Security Threats Internet Of Things IoT Security Cybersecurity SS
Business Survey Highlighting Common IoT Security Threats Internet Of Things IoT Security Cybersecurity SSThis slide showcases common internet of things IoT threats in the company, referable for related businesses. It provides details about network scan, command injection, SQL, zero-day, etc. Present the topic in a bit more detail with this Business Survey Highlighting Common IoT Security Threats Internet Of Things IoT Security Cybersecurity SS. Use it as a tool for discussion and navigation on Cyber Security Awareness, Quality Threat Modeling Tools, Weak Passwords, Authentication Practices. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
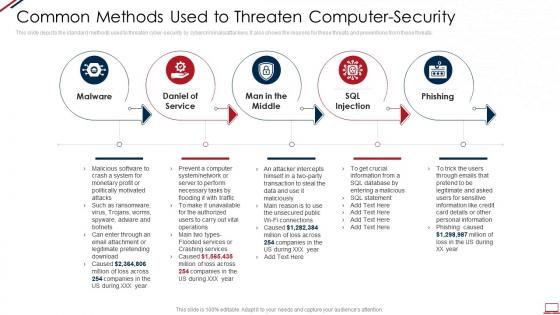 Computer system security common methods used to threaten computer security
Computer system security common methods used to threaten computer securityThis slide depicts the standard methods used to threaten cyber security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Increase audience engagement and knowledge by dispensing information using Computer System Security Common Methods Used To Threaten Computer Security. This template helps you present information on five stages. You can also present information on Malware, Daniel Of Service, Man In The Middle, SQL Injection, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
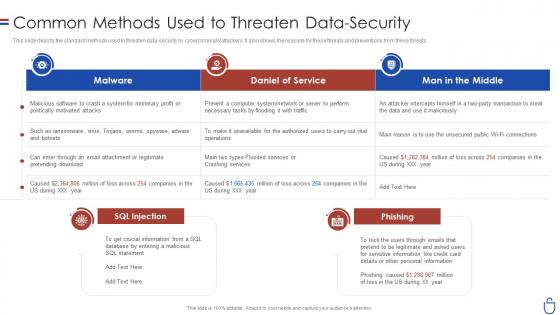 Data security it common methods used to threaten data security
Data security it common methods used to threaten data securityThis slide depicts the standard methods used to threaten data-security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Present the topic in a bit more detail with this Data Security IT Common Methods Used To Threaten Data Security. Use it as a tool for discussion and navigation on Malware, Daniel Service, Man Middle, SQL Injection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Common Issues Addressed By Security Patch Management Process
Common Issues Addressed By Security Patch Management ProcessFollowing slide highlights common problems tackled by security patch management process. The purpose of this slide is to build an organizations overall security position and maintain the integrity of its IT and operational environment. It includes factors such as data breaches, loss of productivity, etc.Presenting our set of slides with Common Issues Addressed By Security Patch Management Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Reputation Damage, Unintended System, Security Incidents.
-
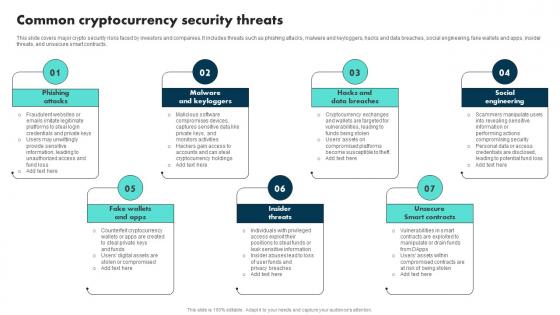 Common Cryptocurrency Security Threats Exploring The Role BCT SS
Common Cryptocurrency Security Threats Exploring The Role BCT SSThis slide covers major crypto security risks faced by investors and companies. It includes threats such as phishing attacks, malware and keyloggers, hacks and data breaches, social engineering, fake wallets and apps, insider threats, and unsecure smart contracts. Introducing Common Cryptocurrency Security Threats Exploring The Role BCT SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attacks, Malware And Keyloggers, Insider Threats, using this template. Grab it now to reap its full benefits.
-
 Common Securities Fund Bond Market In Powerpoint And Google Slides Cpb
Common Securities Fund Bond Market In Powerpoint And Google Slides CpbPresenting Common Securities Fund Bond Market In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Common Securities Fund Bond Market. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
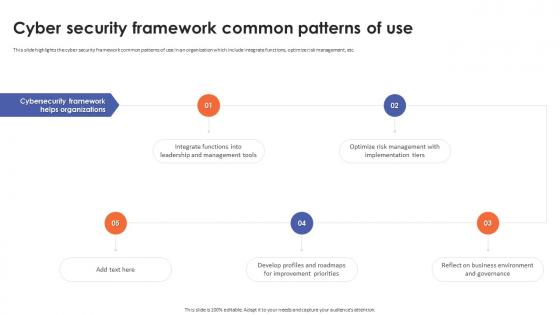 Cyber Security Framework Common Patterns Of Use
Cyber Security Framework Common Patterns Of UseThis slide highlights the cyber security framework common patterns of use in an organization which include integrate functions, optimize risk management, etc. Increase audience engagement and knowledge by dispensing information using Cyber Security Framework Common Patterns Of Use. This template helps you present information on five stages. You can also present information on Cyber Security Framework, Integrate Functions, Optimize Risk Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Devsecops Best Practices For Secure Specific Security Tool Common To All Devsecops Design
Devsecops Best Practices For Secure Specific Security Tool Common To All Devsecops DesignThis slide discusses the specific security tool common to DevSecOps design. The purpose of this slide is to explain the various tools, including runtime defense, vulnerability, CVE service host, artifact repository, and zero trust. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Specific Security Tool Common To All Devsecops Design. Dispense information and present a thorough explanation of Cyber Security Vulnerability, Supplies Common Vulnerabilities, Artifact Repository using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ethical Hacking And Network Security Common Types Of Cyber Crime
Ethical Hacking And Network Security Common Types Of Cyber CrimeThis slide describes the common types of cybercrime such as identity theft, computer fraud, privacy breach, electronic money laundering, electronic funds transfer, and so on. Introducing Ethical Hacking And Network Security Common Types Of Cyber Crime to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Electronic Money Laundering, Electronic Funds Transfer, Denial Of Service Attacks, Sharing Copyrighted Files Or Data, using this template. Grab it now to reap its full benefits.
-
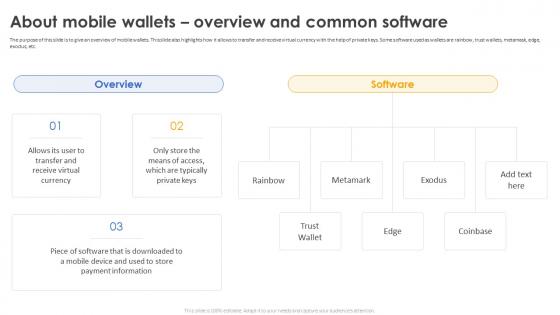 Secure Your Digital Assets About Mobile Wallets Overview And Common Software
Secure Your Digital Assets About Mobile Wallets Overview And Common SoftwareThe purpose of this slide is to give an overview of mobile wallets. This slide also highlights how it allows to transfer and receive virtual currency with the help of private keys. Some software used as wallets are rainbow, trust wallets, metamask, edge, exodus, etc. Introducing Secure Your Digital Assets About Mobile Wallets Overview And Common Software to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Mobile Wallets, Transfer And Receive Virtual Currency, Trust Wallets, Exodus, using this template. Grab it now to reap its full benefits.
-
 Secure Your Digital Assets Introduction And Common Software Of Desktop Wallets
Secure Your Digital Assets Introduction And Common Software Of Desktop WalletsThis slide represents the perception of the desktop wallets and some software. These wallets use the operating systems that are installed on the desktop The purpose of this slide is to outline that desktop wallets are a fine option for cold storage, simple to use, easy to take backups, etc. Introducing Secure Your Digital Assets Introduction And Common Software Of Desktop Wallets to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Electrum Bitcoin Wallet, Desktop Wallets, Operating Systems, Atomic Wallet, using this template. Grab it now to reap its full benefits.
-
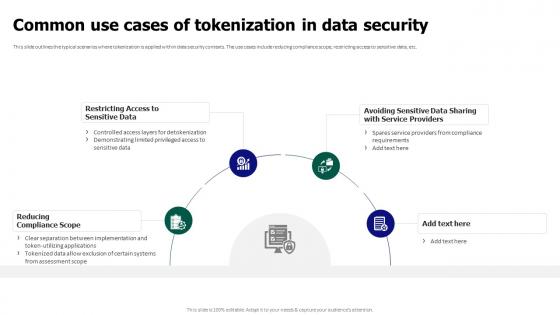 Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data Security
Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data SecurityThis slide outlines the typical scenarios where tokenization is applied within data security contexts. The use cases include reducing compliance scope, restricting access to sensitive data, etc. Introducing Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Restricting Access To Sensitive Data, Reducing Compliance Scope, Tokenization In Data Security, using this template. Grab it now to reap its full benefits.
-
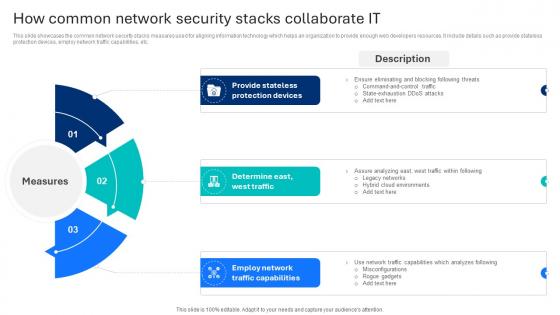 How Common Network Security Stacks Collaborate It
How Common Network Security Stacks Collaborate ItThis slide showcases the common network security stacks measures used for aligning information technology which helps an organization to provide enough web developers resources. It include details such as provide stateless protection devices, employ network traffic capabilities, etc. Introducing our premium set of slides with name How Common Network Security Stacks Collaborate It Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Provide Stateless, Protection Devices, Traffic Capabilities. So download instantly and tailor it with your information.
-
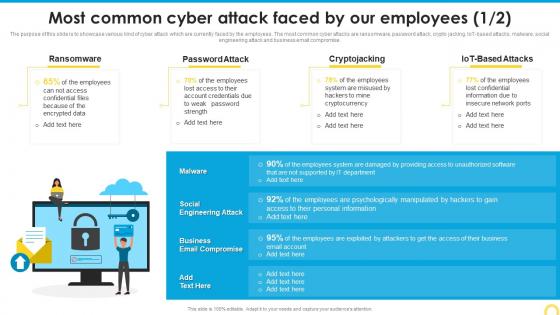 Most Common Cyber Attack Building A Security Awareness Program
Most Common Cyber Attack Building A Security Awareness ProgramThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT based attacks, malware, social engineering attack and business email compromise. Present the topic in a bit more detail with this Most Common Cyber Attack Building A Security Awareness Program. Use it as a tool for discussion and navigation on Ransomware, Password Attack, Cryptojacking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
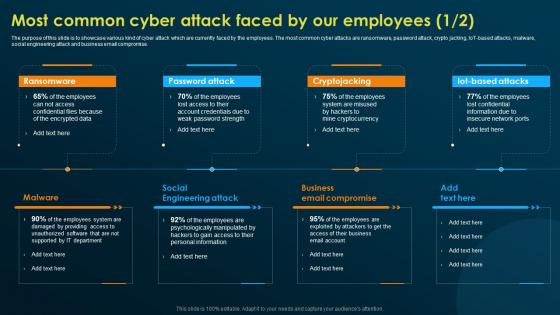 Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness Training
Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness TrainingThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT based attacks, malware, social engineering attack and business email compromise. Introducing Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness Training to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Password Attack, Cryptojacking, Malware, using this template. Grab it now to reap its full benefits.
-
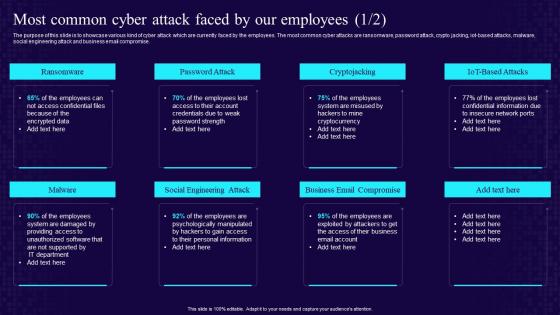 Most Common Cyber Attack Faced By Our Employees Developing Cyber Security Awareness Training Program
Most Common Cyber Attack Faced By Our Employees Developing Cyber Security Awareness Training ProgramThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, iot based attacks, malware, social engineering attack and business email compromise. Increase audience engagement and knowledge by dispensing information using Most Common Cyber Attack Faced By Our Employees Developing Cyber Security Awareness Training Program. This template helps you present information on eight stages. You can also present information on Ransomware, Password Attack, Social Engineering Attack, Business Email Compromise using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Most Common Cyber Attack Faced By Our Employees Conducting Security Awareness
Most Common Cyber Attack Faced By Our Employees Conducting Security AwarenessThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT-based attacks, malware, social engineering attack and business email compromise. Present the topic in a bit more detail with this Most Common Cyber Attack Faced By Our Employees Conducting Security Awareness. Use it as a tool for discussion and navigation on Ransomware, Password Attack, Cryptojacking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
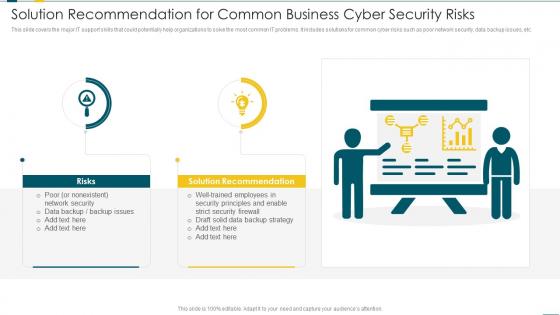 Solution Recommendation For Common Business Cyber Security Risks
Solution Recommendation For Common Business Cyber Security RisksThis slide covers the major IT support skills that could potentially help organizations to solve the most common IT problems. It includes solutions for common cyber risks such as poor network security, data backup issues, etc. Introducing our premium set of slides with Solution Recommendation For Common Business Cyber Security Risks. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risks, Solution Recommendation, Network Security. So download instantly and tailor it with your information.
-
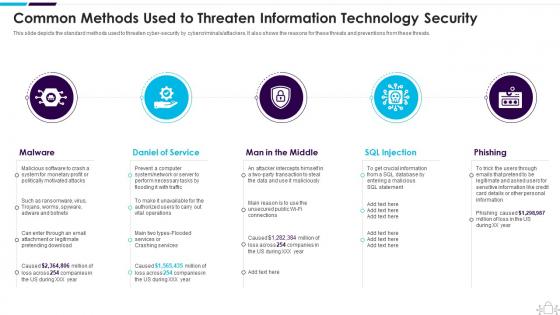 Information Technology Security Common Methods Used Threaten Information Security
Information Technology Security Common Methods Used Threaten Information SecurityThis slide depicts the standard methods used to threaten cyber security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Introducing Information Technology Security Common Methods Used Threaten Information Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Daniel Of Service, Man In The Middle, SQL Injection , using this template. Grab it now to reap its full benefits.
-
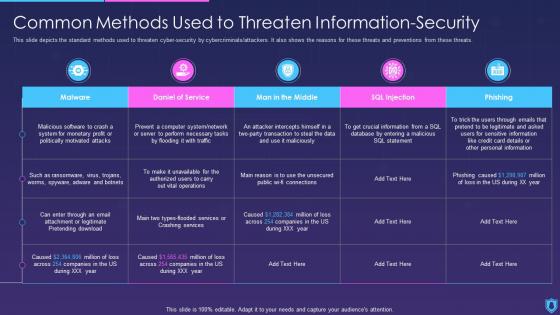 Information Security Common Methods Used To Threaten Information Security
Information Security Common Methods Used To Threaten Information SecurityThis slide depicts the standard methods used to threaten cyber-security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Deliver an outstanding presentation on the topic using this Information Security Common Methods Used To Threaten Information Security. Dispense information and present a thorough explanation of Information, Security, Common using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
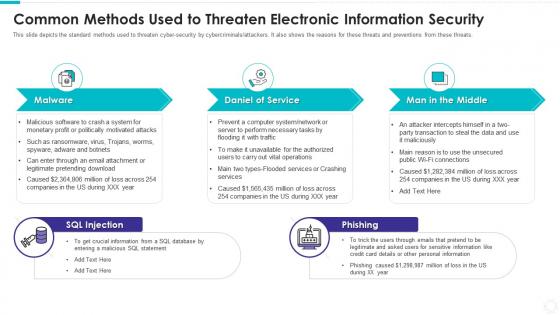 Common methods used to threaten electronic information security
Common methods used to threaten electronic information securityIntroducing Common Methods Used To Threaten Electronic Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Daniel Service, Man Middle, SQL Injection, Phishing , using this template. Grab it now to reap its full benefits.
-
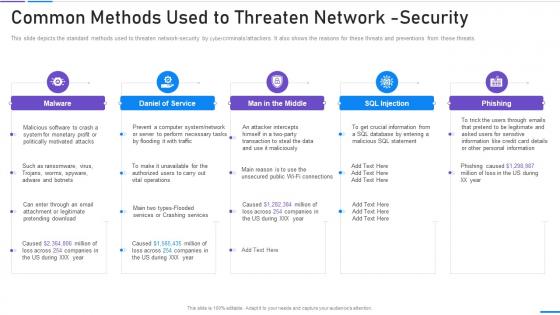 Network Security Common Methods Used To Threaten Network Security
Network Security Common Methods Used To Threaten Network SecurityThis slide depicts the standard methods used to threaten network security by cybercriminals attackers. It also shows the reasons for these threats and preventions from these threats. Increase audience engagement and knowledge by dispensing information using Network Security Common Methods Used To Threaten Network Security. This template helps you present information on five stages. You can also present information on Malicious, Necessary, Perform, Unavailable, Operations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
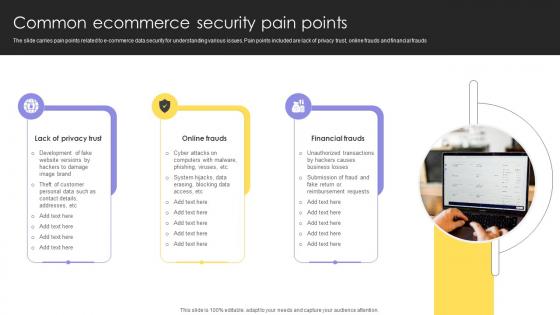 Common Ecommerce Security Pain Points
Common Ecommerce Security Pain PointsThe slide carries pain points related to ecommerce data security for understanding various issues. Pain points included are lack of privacy trust, online frauds and financial frauds. Presenting our set of slides with Common Ecommerce Security Pain Points. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Lack Of Privacy Trust, Online Frauds, Financial Fraud.
-
 Common Sources Of Precursors And Indicators Implementing Cyber Security Ppt Inspiration
Common Sources Of Precursors And Indicators Implementing Cyber Security Ppt InspirationThis slide represents the common sources of signs which indicates that an incident may occur in the future. It includes details related to common sources of precursors and indicators such as IDPSs, SIEMs, network device logs etc. Deliver an outstanding presentation on the topic using this Common Sources Of Precursors And Indicators Implementing Cyber Security Ppt Inspiration. Dispense information and present a thorough explanation of Common Sources, Precursors And Indicators, Analytics using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
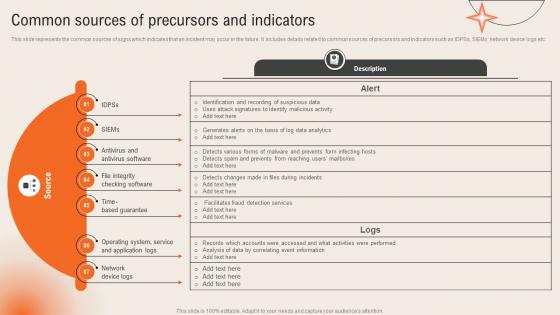 Common Sources Of Precursors And Indicators Deploying Computer Security Incident Management
Common Sources Of Precursors And Indicators Deploying Computer Security Incident ManagementThis slide represents the common sources of signs which indicates that an incident may occur in the future. It includes details related to common sources of precursors and indicators such as IDPSs, SIEMs, network device logs etc.Present the topic in a bit more detail with this Common Sources Of Precursors And Indicators Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Antivirus Software, Based Guarantee, Operating System. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Common Sources Of Precursors And Indicators Development And Implementation Of Security
Common Sources Of Precursors And Indicators Development And Implementation Of SecurityThis slide represents the common sources of signs which indicates that an incident may occur in the future. It includes details related to common sources of precursors and indicators such as IDPSs, SIEMs, network device logs etc. Present the topic in a bit more detail with this Common Sources Of Precursors And Indicators Development And Implementation Of Security. Use it as a tool for discussion and navigation on Identification And Recording, Suspicious Data, Uses Attack Signatures, Identify Malicious Activity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
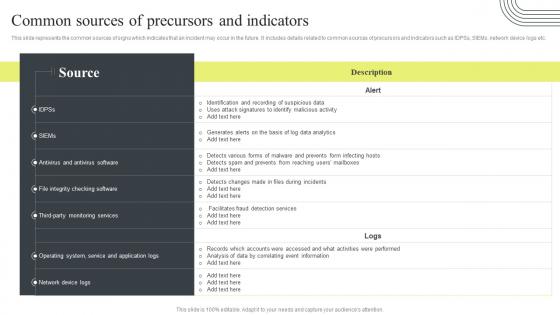 Cyber Security Attacks Response Plan Common Sources Of Precursors And Indicators
Cyber Security Attacks Response Plan Common Sources Of Precursors And IndicatorsThis slide represents the common sources of signs which indicates that an incident may occur in the future. It includes details related to common sources of precursors and indicators such as IDPSs, SIEMs, network device logs etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Common Sources Of Precursors And Indicators. Use it as a tool for discussion and navigation on Precursors And Indicators, Suspicious Data, Identify Malicious Activity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Common Mitigation Methods Cyber Security In Powerpoint And Google Slides Cpb
Common Mitigation Methods Cyber Security In Powerpoint And Google Slides CpbPresenting Common Mitigation Methods Cyber Security In Powerpoint And Google Slides Cpb. slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Common Mitigation Methods Cyber Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
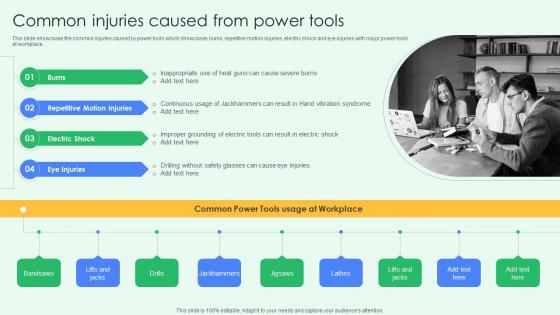 Common Injuries Caused From Power Tools Best Practices For Workplace Security
Common Injuries Caused From Power Tools Best Practices For Workplace SecurityThis slide showcases the common injuries caused by power tools which showcases burns, repetitive motion injuries, electric shock and eye injuries with major power tools at workplace.Increase audience engagement and knowledge by dispensing information using Common Injuries Caused From Power Tools Best Practices For Workplace Security. This template helps you present information on four stages. You can also present information on Inappropriate Heat , Continuous Jackhammers, Improper Grounding using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
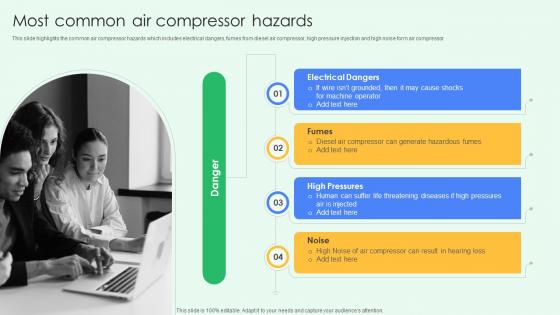 Most Common Air Compressor Hazards Best Practices For Workplace Security
Most Common Air Compressor Hazards Best Practices For Workplace SecurityThis slide highlights the common air compressor hazards which includes electrical dangers, fumes from diesel air compressor, high pressure injection and high noise form air compressor.Introducing Most Common Air Compressor Hazards Best Practices For Workplace Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Electrical Dangers, High Pressures, Compressor Can Result, using this template. Grab it now to reap its full benefits.
-
 Common Stock Money Market Security In Powerpoint And Google Slides Cpb
Common Stock Money Market Security In Powerpoint And Google Slides CpbPresenting Common Stock Money Market Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Common Stock Money Market Security This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Secure network it infrastructure identity management common methodology
Secure network it infrastructure identity management common methodologyPresenting this set of slides with name - Secure Network It Infrastructure Identity Management Common Methodology. This is an editable two stages graphic that deals with topics like Secure Network It Infrastructure, Identity Management, Common Methodology to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Ensure security and access controls establish a common vocabulary
Ensure security and access controls establish a common vocabularyPresenting this set of slides with name - Ensure Security And Access Controls Establish A Common Vocabulary. This is a two stage process. The stages in this process are Icons, Strategy, Business, Management, Marketing.
-
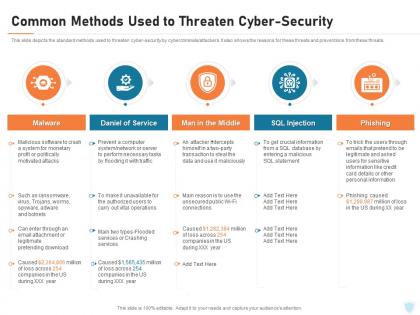 Cyber security it common methods used to threaten cyber security ppt powerpoint model
Cyber security it common methods used to threaten cyber security ppt powerpoint modelThis slide depicts the standard methods used to threaten cyber-security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Increase audience engagement and knowledge by dispensing information using Cyber Security IT Common Methods Used To Threaten Cyber Security Ppt Powerpoint Model. This template helps you present information on five stages. You can also present information on Malware, Daniel Of Service, Man In The Middle, Sql Injection, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

