Powerpoint Templates and Google slides for Computer Technology Facts
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
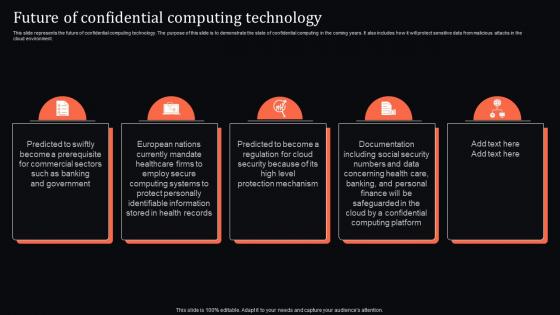 Future Of Confidential Computing Technology Confidential Computing System Technology
Future Of Confidential Computing Technology Confidential Computing System TechnologyThis slide represents the future of confidential computing technology. The purpose of this slide is to demonstrate the state of confidential computing in the coming years. It also includes how it will protect sensitive data from malicious attacks in the cloud environment. Introducing Future Of Confidential Computing Technology Confidential Computing System Technology to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confidential, Computing, Technology, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Confidential Computing System Technology
Icons Slide For Confidential Computing System TechnologyPresent the topic in a bit more detail with this Icons Slide For Confidential Computing System Technology. Use it as a tool for discussion and navigation on Icons. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
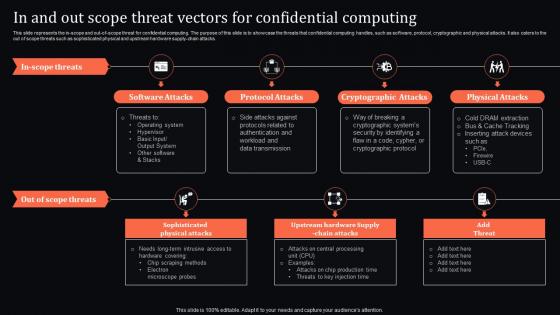 In And Threat Vectors For Confidential Computing Confidential Computing System Technology
In And Threat Vectors For Confidential Computing Confidential Computing System TechnologyThis slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Increase audience engagement and knowledge by dispensing information using In And Threat Vectors For Confidential Computing Confidential Computing System Technology. This template helps you present information on seven stages. You can also present information on Software Attacks, Protocol Attacks, Cryptographic Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
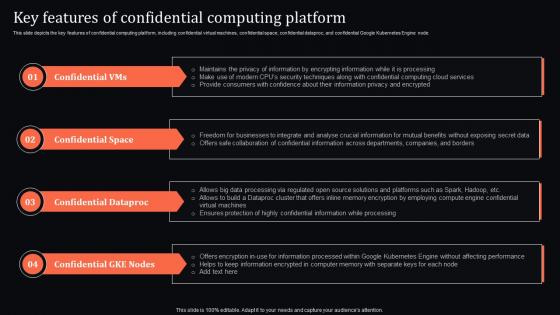 Key Features Of Confidential Computing Platform Confidential Computing System Technology
Key Features Of Confidential Computing Platform Confidential Computing System TechnologyThis slide depicts the key features of confidential computing platform, including confidential virtual machines, confidential space, confidential dataproc, and confidential Google Kubernetes Engine node. Introducing Key Features Of Confidential Computing Platform Confidential Computing System Technology to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Confidential Space, Confidential Dataproc, Confidential Gke Nodes, using this template. Grab it now to reap its full benefits.
-
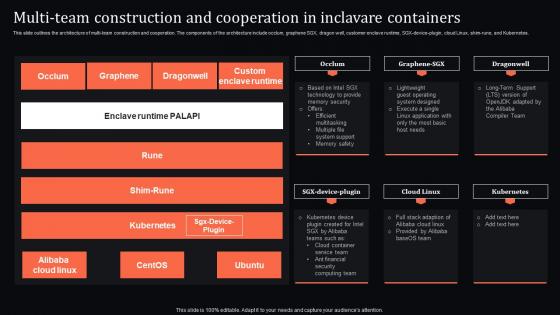 Multi Team And Cooperation In Inclavare Containers Confidential Computing System Technology
Multi Team And Cooperation In Inclavare Containers Confidential Computing System TechnologyThis slide outlines the architecture of multi-team construction and cooperation. The components of the architecture include occlum, graphene SGX, dragon well, customer enclave runtime, SGX-device-plugin, cloud Linux, shim-rune, and Kubernetes. Deliver an outstanding presentation on the topic using this Multi Team And Cooperation In Inclavare Containers Confidential Computing System Technology. Dispense information and present a thorough explanation of Construction, Cooperation, Containers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
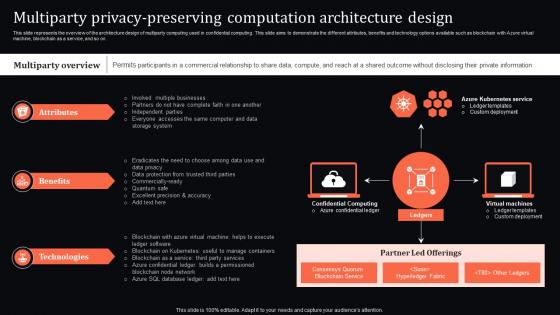 Multiparty Privacy Computation Architecture Design Confidential Computing System Technology
Multiparty Privacy Computation Architecture Design Confidential Computing System TechnologyThis slide represents the overview of the architecture design of multiparty computing used in confidential computing. This slide aims to demonstrate the different attributes, benefits and technology options available such as blockchain with Azure virtual machine, blockchain as a service, and so on. Present the topic in a bit more detail with this Multiparty Privacy Computation Architecture Design Confidential Computing System Technology. Use it as a tool for discussion and navigation on Computation, Architecture, Technologies . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
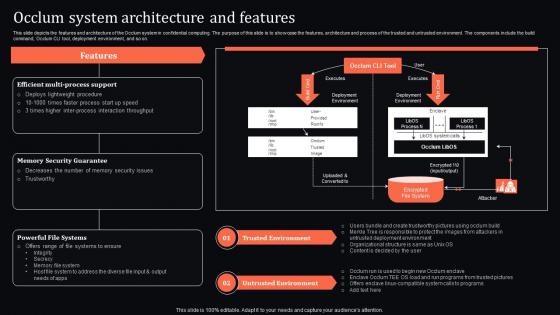 Occlum System Architecture And Features Confidential Computing System Technology
Occlum System Architecture And Features Confidential Computing System TechnologyThis slide depicts the features and architecture of the Occlum system in confidential computing. The purpose of this slide is to showcase the features, architecture and process of the trusted and untrusted environment. The components include the build command, Occlum CLI tool, deployment environment, and so on. Present the topic in a bit more detail with this Occlum System Architecture And Features Confidential Computing System Technology. Use it as a tool for discussion and navigation on Trusted Environment, Untrusted Environment, Memory Security Guarantee. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
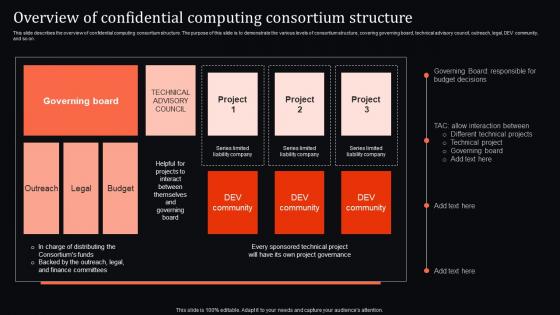 Overview Of Computing Consortium Structure Confidential Computing System Technology
Overview Of Computing Consortium Structure Confidential Computing System TechnologyThis slide describes the overview of confidential computing consortium structure. The purpose of this slide is to demonstrate the various levels of consortium structure, covering governing board, technical advisory council, outreach, legal, DEV community, and so on. Present the topic in a bit more detail with this Overview Of Computing Consortium Structure Confidential Computing System Technology. Use it as a tool for discussion and navigation on Computing, Consortium, Structure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
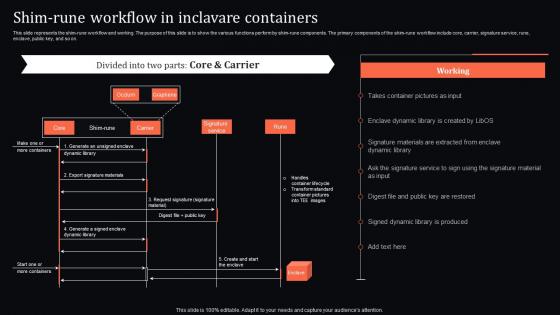 Shim Rune Workflow In Inclavare Containers Confidential Computing System Technology
Shim Rune Workflow In Inclavare Containers Confidential Computing System TechnologyThis slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Present the topic in a bit more detail with this Shim Rune Workflow In Inclavare Containers Confidential Computing System Technology. Use it as a tool for discussion and navigation on Component, Workflow, Inclavare Containers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
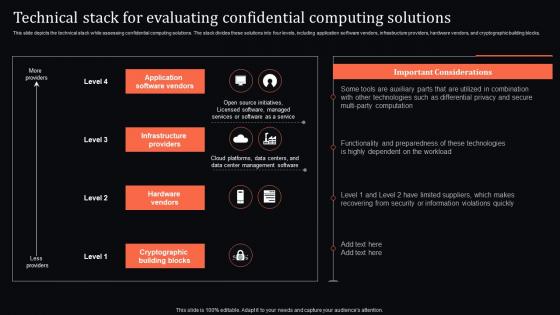 Technical Stack For Confidential Computing Solutions Confidential Computing System Technology
Technical Stack For Confidential Computing Solutions Confidential Computing System TechnologyThis slide depicts the technical stack while assessing confidential computing solutions. The stack divides these solutions into four levels, including application software vendors, infrastructure providers, hardware vendors, and cryptographic building blocks. Present the topic in a bit more detail with this Technical Stack For Confidential Computing Solutions Confidential Computing System Technology. Use it as a tool for discussion and navigation on Application Software Vendors, Infrastructure Providers, Hardware Vendors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
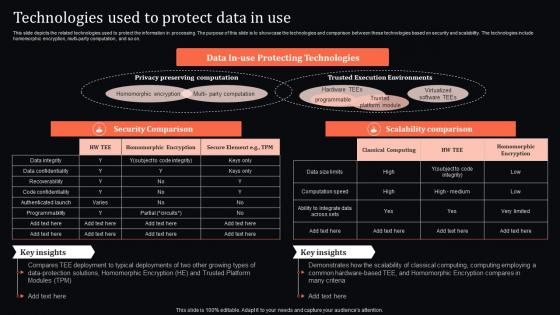 Technologies Used To Protect Data In Use Confidential Computing System Technology
Technologies Used To Protect Data In Use Confidential Computing System TechnologyThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Deliver an outstanding presentation on the topic using this Technologies Used To Protect Data In Use Confidential Computing System Technology. Dispense information and present a thorough explanation of Technologies, Security Comparison, Scalability Comparison using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
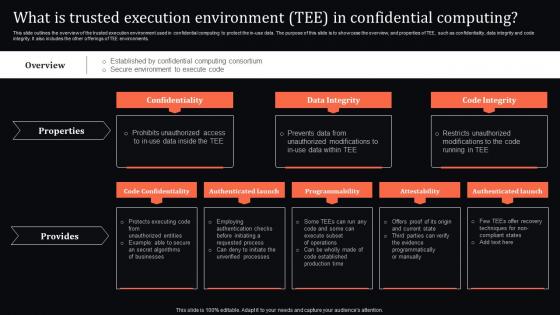 What Is Environment Tee In Confidential Computing Confidential Computing System Technology
What Is Environment Tee In Confidential Computing Confidential Computing System TechnologyThis slide outlines the overview of the trusted execution environment used in confidential computing to protect the in-use data. The purpose of this slide is to showcase the overview, and properties of TEE, such as confidentiality, data integrity and code integrity. It also includes the other offerings of TEE environments. Present the topic in a bit more detail with this What Is Environment Tee In Confidential Computing Confidential Computing System Technology. Use it as a tool for discussion and navigation on Confidentiality, Data Integrity, Code Integrity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
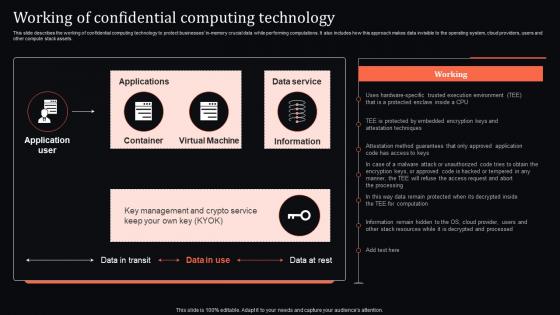 Working Of Confidential Computing Technology Confidential Computing System Technology
Working Of Confidential Computing Technology Confidential Computing System TechnologyThis slide describes the working of confidential computing technology to protect businesses in-memory crucial data while performing computations. It also includes how this approach makes data invisible to the operating system, cloud providers, users and other compute stack assets. Present the topic in a bit more detail with this Working Of Confidential Computing Technology Confidential Computing System Technology. Use it as a tool for discussion and navigation on Confidential, Computing, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Green Technology Icon With Computer Chipset
Green Technology Icon With Computer ChipsetPresenting our well structured Green Technology Icon With Computer Chipset. The topics discussed in this slide are Computer, Technology, Green. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cognitive Computing Technology Brain Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cognitive Computing Technology Brain Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon on Technology Brain is a great way to illustrate your presentations. It is eye-catching and modern, and will help to make your slides stand out. It is easy to use and customize, and can be used in any presentation.
-
 Cognitive Computing Technology Brain Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cognitive Computing Technology Brain Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMonotone PowerPoint icon on Technology Brain is a modern and stylish icon perfect for presentations and other digital projects. It features a sleek design with a black and white color scheme that adds a professional touch to any project. It is sure to make your presentation stand out and leave a lasting impression.
-
 Computer Technology Brain Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Computer Technology Brain Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon on Technology Brain is a great way to illustrate your presentations. It is eye-catching and modern, and will help to make your slides stand out. It is easy to use and customize, and can be used in any presentation.
-
 Computer Technology Brain Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Computer Technology Brain Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMonotone PowerPoint icon on Technology Brain is a modern and stylish icon perfect for presentations and other digital projects. It features a sleek design with a black and white color scheme that adds a professional touch to any project. It is sure to make your presentation stand out and leave a lasting impression.
-
 Computer Tower Technology Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Computer Tower Technology Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful PowerPoint icon features a computer tower with a bright, modern design. It is perfect for presentations on technology, computing, or any other related topic. Add some colour to your slides with this eye-catching icon.
-
 Computer Tower Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Computer Tower Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a vector illustration of a computer tower. It is perfect for presentations, websites, and other digital projects. The icon is simple and modern, and will add a professional touch to any project.
-
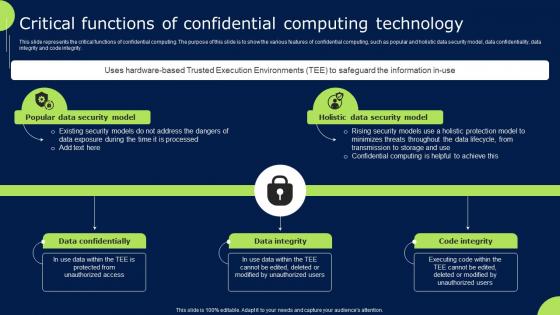 Confidential Cloud Computing Critical Functions Of Confidential Computing Technology
Confidential Cloud Computing Critical Functions Of Confidential Computing TechnologyThis slide represents the critical functions of confidential computing. The purpose of this slide is to show the various features of confidential computing, such as popular and holistic data security model, data confidentiality, data integrity and code integrity. Present the topic in a bit more detail with this Confidential Cloud Computing Critical Functions Of Confidential Computing Technology. Use it as a tool for discussion and navigation on Confidential, Computing, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
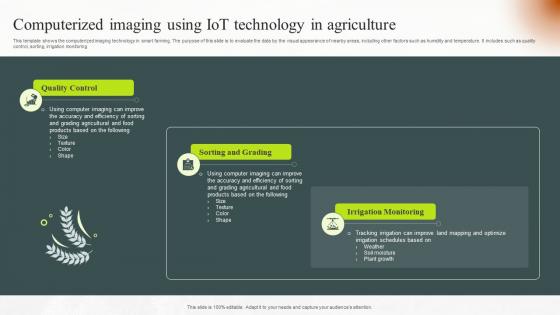 Computerized Imaging Using IoT Technology In Agriculture
Computerized Imaging Using IoT Technology In AgricultureThis template shows the computerized imaging technology in smart farming. The purpose of this slide is to evaluate the data by the visual appearance of nearby areas, including other factors such as humidity and temperature. It includes such as quality control, sorting, irrigation monitoring.Presenting our set of slides with Computerized Imaging Using IoT Technology In Agriculture. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Quality Control, Sorting Grading, Irrigation Monitoring.
-
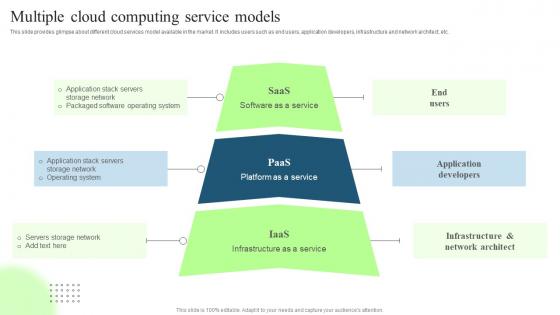 Technological Digital Transformation Multiple Cloud Computing Service Models
Technological Digital Transformation Multiple Cloud Computing Service ModelsThis slide provides glimpse about different cloud services model available in the market. It includes users such as end users, application developers, infrastructure and network architect, etc. Present the topic in a bit more detail with this Technological Digital Transformation Multiple Cloud Computing Service Models. Use it as a tool for discussion and navigation on Saas Software As A Service, Paas Platform As A Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
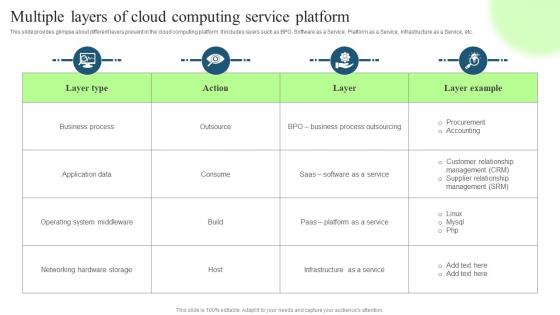 Technological Digital Transformation Multiple Layers Of Cloud Computing Service Platform
Technological Digital Transformation Multiple Layers Of Cloud Computing Service PlatformThis slide provides glimpse about different layers present in the cloud computing platform. It includes layers such as BPO, Software as a Service, Platform as a Service, Infrastructure as a Service, etc. Deliver an outstanding presentation on the topic using this Technological Digital Transformation Multiple Layers Of Cloud Computing Service Platform. Dispense information and present a thorough explanation of Business Process, Application Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
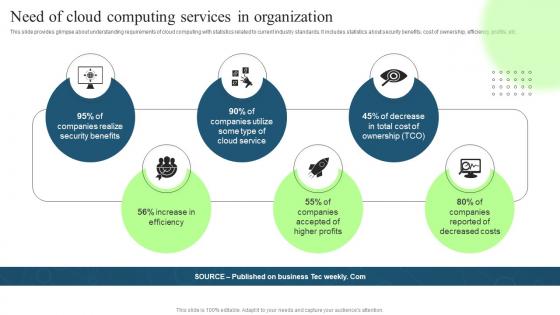 Technological Digital Transformation Need Of Cloud Computing Services In Organization
Technological Digital Transformation Need Of Cloud Computing Services In OrganizationThis slide provides glimpse about understanding requirements of cloud computing with statistics related to current industry standards. It includes statistics about security benefits, cost of ownership, efficiency, profits, etc. Introducing Technological Digital Transformation Need Of Cloud Computing Services In Organization to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Companies Utilize, Companies Realize, using this template. Grab it now to reap its full benefits.
-
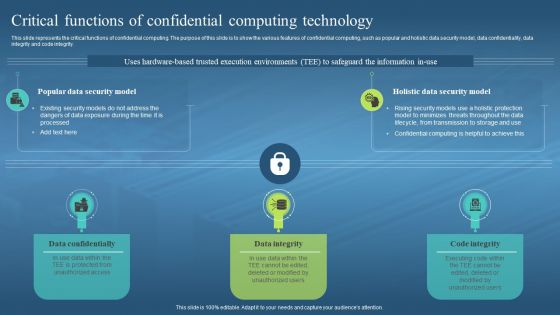 Confidential Computing Hardware Critical Functions Of Confidential Computing Technology
Confidential Computing Hardware Critical Functions Of Confidential Computing TechnologyThis slide represents the critical functions of confidential computing. The purpose of this slide is to show the various features of confidential computing, such as popular and holistic data security model, data confidentiality, data integrity and code integrity. Increase audience engagement and knowledge by dispensing information using Confidential Computing Hardware Critical Functions Of Confidential Computing Technology. This template helps you present information on three stages. You can also present information on Data Confidentially, Data Integrity, Code Integrity, Confidential Computing Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
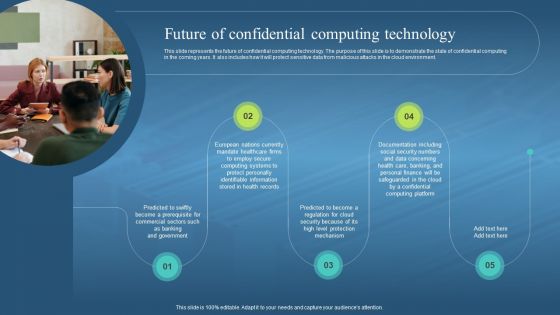 Confidential Computing Hardware Future Of Confidential Computing Technology
Confidential Computing Hardware Future Of Confidential Computing TechnologyThis slide represents the future of confidential computing technology. The purpose of this slide is to demonstrate the state of confidential computing in the coming years. It also includes how it will protect sensitive data from malicious attacks in the cloud environment. Increase audience engagement and knowledge by dispensing information using Confidential Computing Hardware Future Of Confidential Computing Technology. This template helps you present information on five stages. You can also present information on Confidential Computing Technology, Demonstrate, Cloud Environment, Prerequisite For Commercial Sectors using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
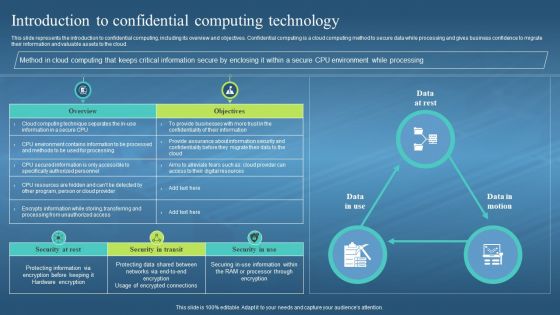 Confidential Computing Hardware Introduction To Confidential Computing Technology
Confidential Computing Hardware Introduction To Confidential Computing TechnologyThis slide represents the introduction to confidential computing, including its overview and objectives. Confidential computing is a cloud computing method to secure data while processing and gives business confidence to migrate their information and valuable assets to the cloud. Present the topic in a bit more detail with this Confidential Computing Hardware Introduction To Confidential Computing Technology. Use it as a tool for discussion and navigation on Confidential Computing, Cloud Computing Method, CPU Environment While Processing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
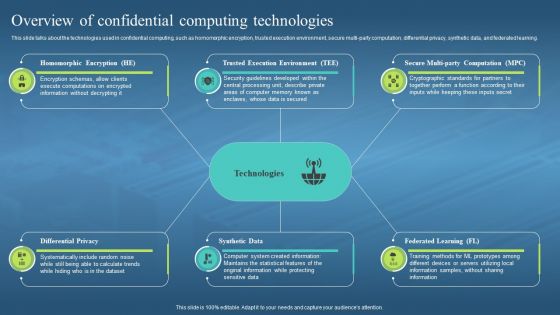 Confidential Computing Hardware Overview Of Confidential Computing Technologies
Confidential Computing Hardware Overview Of Confidential Computing TechnologiesThis slide talks about the technologies used in confidential computing, such as homomorphic encryption, trusted execution environment, secure multi-party computation, differential privacy, synthetic data, and federated learning. Increase audience engagement and knowledge by dispensing information using Confidential Computing Hardware Overview Of Confidential Computing Technologies. This template helps you present information on six stages. You can also present information on Homomorphic Encryption, Trusted Execution Environment, Federated Learning, Synthetic Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
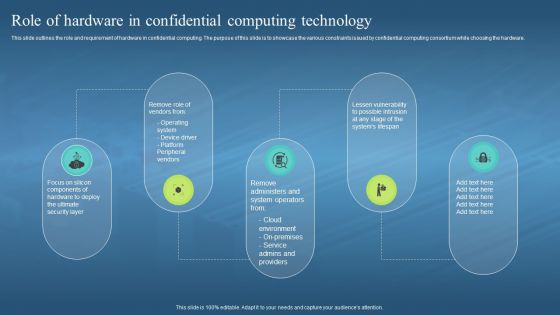 Confidential Computing Hardware Role Of Hardware In Confidential Computing Technology
Confidential Computing Hardware Role Of Hardware In Confidential Computing TechnologyThis slide outlines the role and requirement of hardware in confidential computing. The purpose of this slide is to showcase the various constraints issued by confidential computing consortium while choosing the hardware. Introducing Confidential Computing Hardware Role Of Hardware In Confidential Computing Technology to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Environment, Service Admins And Providers, Operating System, Device Driver, Peripheral Vendors, using this template. Grab it now to reap its full benefits.
-
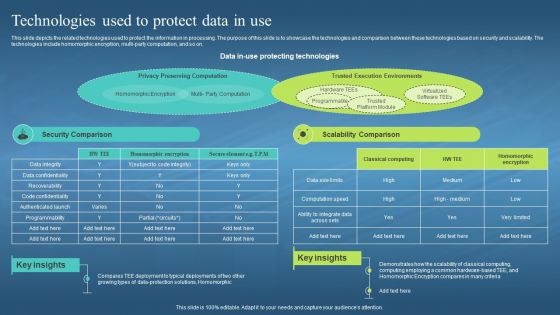 Confidential Computing Hardware Technologies Used To Protect Data In Use
Confidential Computing Hardware Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Present the topic in a bit more detail with this Confidential Computing Hardware Technologies Used To Protect Data In Use. Use it as a tool for discussion and navigation on Protect The Information In Processing, Security And Scalability, Homomorphic Encryption, Multi Party Computation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
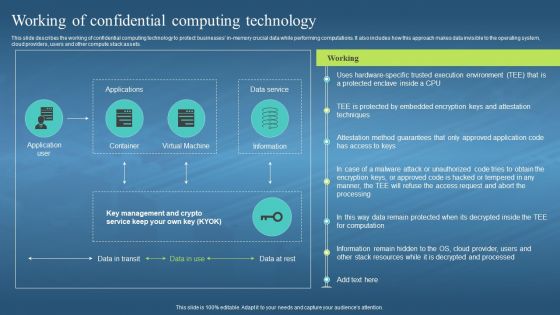 Confidential Computing Hardware Working Of Confidential Computing Technology
Confidential Computing Hardware Working Of Confidential Computing TechnologyThis slide describes the working of confidential computing technology to protect businesses in-memory crucial data while performing computations. It also includes how this approach makes data invisible to the operating system, cloud providers, users and other compute stack assets. Present the topic in a bit more detail with this Confidential Computing Hardware Working Of Confidential Computing Technology. Use it as a tool for discussion and navigation on Confidential Computing Technology, Protect Businesses, Performing Computations, Operating System, Cloud Providers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Computing Fintech Technology Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Computing Fintech Technology Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis PowerPoint icon features a vibrant blue and green colour scheme, perfect for presentations on Fintech. It is a great visual aid to help explain the concept of financial technology and its impact on the industry.
-
 Cloud Computing Fintech Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Computing Fintech Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for presentations on Fintech. It features a modern, sleek design with a white background and a black and white icon of a computer and a dollar sign. It is a great visual representation of the concept of Fintech.
-
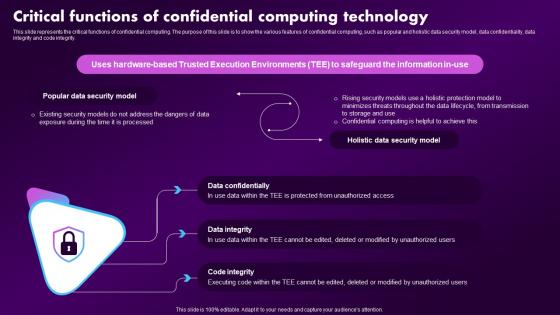 Confidential Computing Market Critical Functions Of Confidential Computing Technology
Confidential Computing Market Critical Functions Of Confidential Computing TechnologyThis slide represents the critical functions of confidential computing. The purpose of this slide is to show the various features of confidential computing, such as popular and holistic data security model, data confidentiality, data integrity and code integrity. Deliver an outstanding presentation on the topic using this Confidential Computing Market Critical Functions Of Confidential Computing Technology. Dispense information and present a thorough explanation of Technology, Information, Environments using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
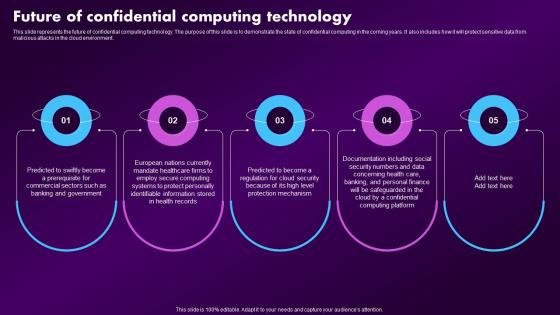 Confidential Computing Market Future Of Confidential Computing Technology
Confidential Computing Market Future Of Confidential Computing TechnologyThis slide represents the future of confidential computing technology. The purpose of this slide is to demonstrate the state of confidential computing in the coming years. It also includes how it will protect sensitive data from malicious attacks in the cloud environment. Increase audience engagement and knowledge by dispensing information using Confidential Computing Market Future Of Confidential Computing Technology. This template helps you present information on five stages. You can also present information on Confidential, Computing, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
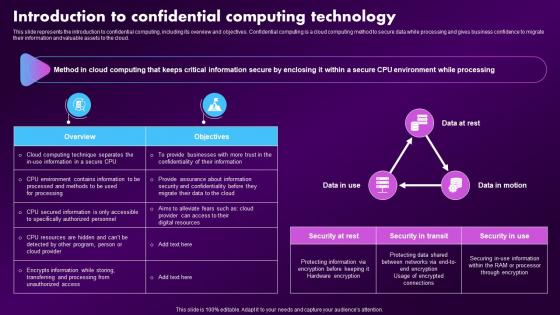 Confidential Computing Market Introduction To Confidential Computing Technology
Confidential Computing Market Introduction To Confidential Computing TechnologyThis slide represents the introduction to confidential computing, including its overview and objectives. Confidential computing is a cloud computing method to secure data while processing and gives business confidence to migrate their information and valuable assets to the cloud. Present the topic in a bit more detail with this Confidential Computing Market Introduction To Confidential Computing Technology. Use it as a tool for discussion and navigation on Introduction, Computing, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
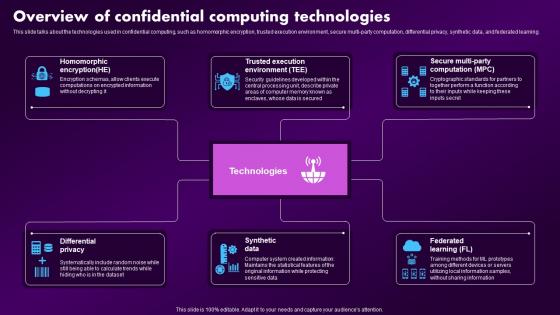 Confidential Computing Market Overview Of Confidential Computing Technologies
Confidential Computing Market Overview Of Confidential Computing TechnologiesThis slide talks about the technologies used in confidential computing, such as homomorphic encryption, trusted execution environment, secure multi-party computation, differential privacy, synthetic data, and federated learning. Deliver an outstanding presentation on the topic using this Confidential Computing Market Overview Of Confidential Computing Technologies. Dispense information and present a thorough explanation of Homomorphic Encryption, Trusted Execution Environment, Secure Multi Party Computation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
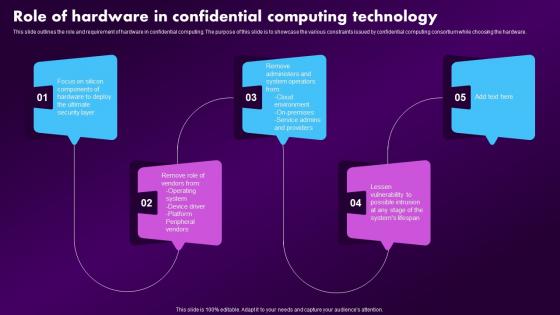 Confidential Computing Market Role Of Hardware In Confidential Computing Technology
Confidential Computing Market Role Of Hardware In Confidential Computing TechnologyThis slide outlines the role and requirement of hardware in confidential computing. The purpose of this slide is to showcase the various constraints issued by confidential computing consortium while choosing the hardware. Increase audience engagement and knowledge by dispensing information using Confidential Computing Market Role Of Hardware In Confidential Computing Technology. This template helps you present information on five stages. You can also present information on Confidential, Computing, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
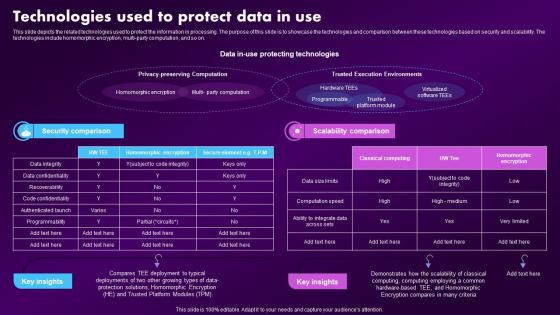 Confidential Computing Market Technologies Used To Protect Data In Use
Confidential Computing Market Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Present the topic in a bit more detail with this Confidential Computing Market Technologies Used To Protect Data In Use. Use it as a tool for discussion and navigation on Technologies, Demonstrates, Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
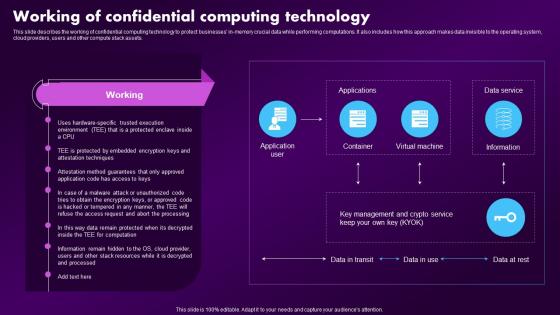 Confidential Computing Market Working Of Confidential Computing Technology
Confidential Computing Market Working Of Confidential Computing TechnologyThis slide describes the working of confidential computing technology to protect businesses in-memory crucial data while performing computations. It also includes how this approach makes data invisible to the operating system, cloud providers, users and other compute stack assets. Deliver an outstanding presentation on the topic using this Confidential Computing Market Working Of Confidential Computing Technology. Dispense information and present a thorough explanation of Confidential, Computing, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Technologies Data Intensive Computing In Powerpoint And Google Slides Cpb
Technologies Data Intensive Computing In Powerpoint And Google Slides CpbPresenting our Technologies Data Intensive Computing In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Treasury Bond Stock. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
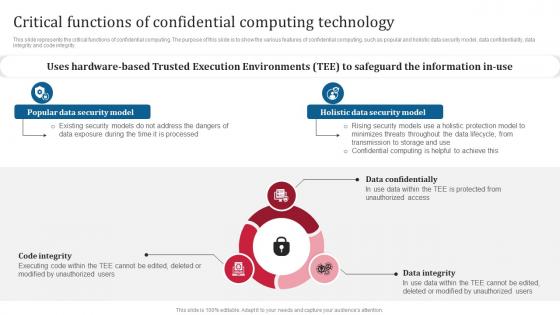 Confidential Computing Consortium Critical Functions Of Confidential Computing Technology
Confidential Computing Consortium Critical Functions Of Confidential Computing TechnologyThis slide represents the critical functions of confidential computing. The purpose of this slide is to show the various features of confidential computing, such as popular and holistic data security model, data confidentiality, data integrity and code integrity. Introducing Confidential Computing Consortium Critical Functions Of Confidential Computing Technology to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Confidentially, Data Integrity, Code Integrity, Trusted Execution Environments, using this template. Grab it now to reap its full benefits.
-
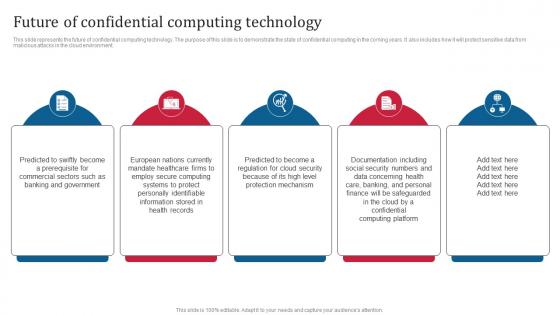 Confidential Computing Consortium Future Of Confidential Computing Technology
Confidential Computing Consortium Future Of Confidential Computing TechnologyThis slide represents the future of confidential computing technology. The purpose of this slide is to demonstrate the state of confidential computing in the coming years. It also includes how it will protect sensitive data from malicious attacks in the cloud environment. Introducing Confidential Computing Consortium Future Of Confidential Computing Technology to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Future Of Confidential, Computing Technology, Cloud Environment, using this template. Grab it now to reap its full benefits.
-
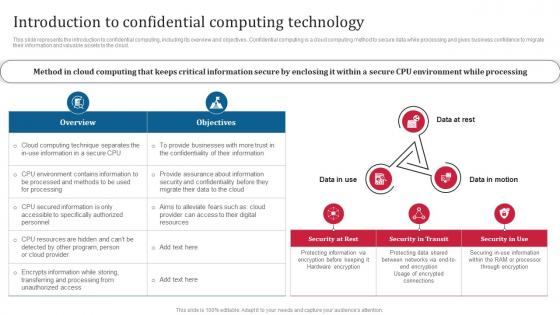 Confidential Computing Consortium Introduction To Confidential Computing Technology
Confidential Computing Consortium Introduction To Confidential Computing TechnologyThis slide represents the introduction to confidential computing, including its overview and objectives. Confidential computing is a cloud computing method to secure data while processing and gives business confidence to migrate their information and valuable assets to the cloud. Present the topic in a bit more detail with this Confidential Computing Consortium Introduction To Confidential Computing Technology. Use it as a tool for discussion and navigation on Confidential Computing Technology, Cloud Computing, Business Confidence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview Of Confidential Computing Technologies Confidential Computing Consortium
Overview Of Confidential Computing Technologies Confidential Computing ConsortiumThis slide talks about the technologies used in confidential computing, such as homomorphic encryption, trusted execution environment, secure multi-party computation, differential privacy, synthetic data, and federated learning. Increase audience engagement and knowledge by dispensing information using Overview Of Confidential Computing Technologies Confidential Computing Consortium. This template helps you present information on six stages. You can also present information on Federated Learning, Homomorphic Encryption, Trusted Execution Environment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
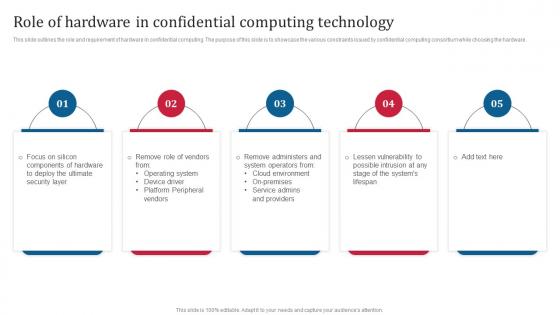 Confidential Computing Consortium Role Of Hardware In Confidential Computing Technology
Confidential Computing Consortium Role Of Hardware In Confidential Computing TechnologyThis slide outlines the role and requirement of hardware in confidential computing. The purpose of this slide is to showcase the various constraints issued by confidential computing consortium while choosing the hardware. Introducing Confidential Computing Consortium Role Of Hardware In Confidential Computing Technology to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Role Of Hardware In Confidential, Computing Technology, Cloud Environment, Platform Peripheral Vendors, using this template. Grab it now to reap its full benefits.
-
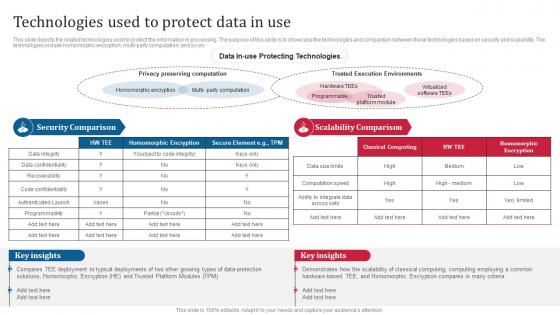 Confidential Computing Consortium Technologies Used To Protect Data In Use
Confidential Computing Consortium Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Deliver an outstanding presentation on the topic using this Confidential Computing Consortium Technologies Used To Protect Data In Use. Dispense information and present a thorough explanation of Protecting Technologies, Security And Scalability, Technologies Homomorphic Encryption, Multi Party Computation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
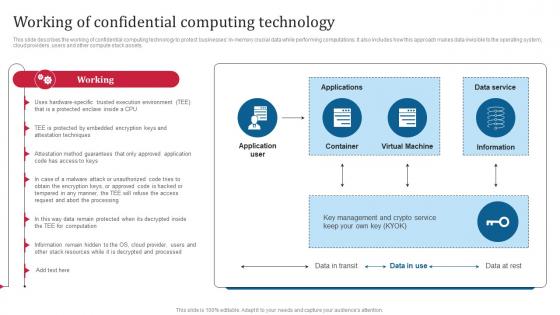 Confidential Computing Consortium Working Of Confidential Computing Technology
Confidential Computing Consortium Working Of Confidential Computing TechnologyThis slide describes the working of confidential computing technology to protect businesses in-memory crucial data while performing computations. It also includes how this approach makes data invisible to the operating system, cloud providers, users and other compute stack assets. Present the topic in a bit more detail with this Confidential Computing Consortium Working Of Confidential Computing Technology. Use it as a tool for discussion and navigation on Working Of Confidential, Computing Technology, Performing Computations, Operating System. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
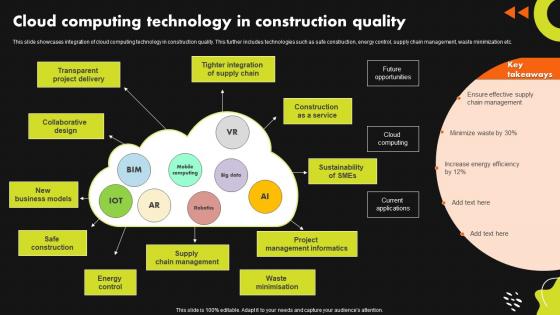 Cloud Computing Technology In Construction Quality
Cloud Computing Technology In Construction QualityThis slide showcases integration of cloud computing technology in construction quality. This further includes technologies such as safe construction, energy control, supply chain management, waste minimization etc. Introducing our Cloud Computing Technology In Construction Quality set of slides. The topics discussed in these slides are Transparent Project Delivery, Collaborative Design. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
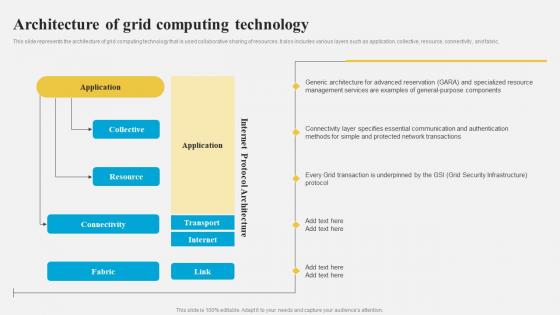 Architecture Of Grid Computing Technology Grid Computing Architecture
Architecture Of Grid Computing Technology Grid Computing ArchitectureThis slide represents the architecture of grid computing technology that is used collaborative sharing of resources. It also includes various layers such as application, collective, resource, connectivity, and fabric. Present the topic in a bit more detail with this Architecture Of Grid Computing Technology Grid Computing Architecture. Use it as a tool for discussion and navigation on Protected Network Transactions, Grid Security Infrastructure, General Purpose Components, Generic Architecture For Advanced Reservation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
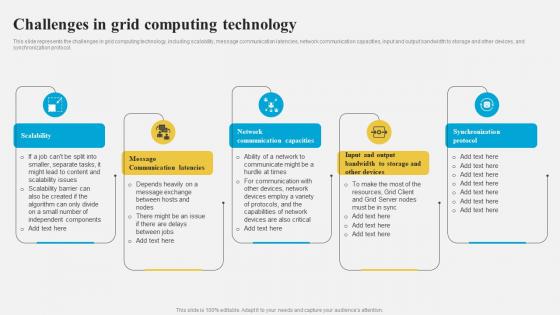 Grid Computing Architecture Challenges In Grid Computing Technology
Grid Computing Architecture Challenges In Grid Computing TechnologyThis slide represents the challenges in grid computing technology, including scalability, message communication latencies, network communication capacities, input and output bandwidth to storage and other devices, and synchronization protocol. Increase audience engagement and knowledge by dispensing information using Grid Computing Architecture Challenges In Grid Computing Technology. This template helps you present information on five stages. You can also present information on Network Communication Capacities, Message Communication Latencies, Scalability, Synchronization Protocol using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
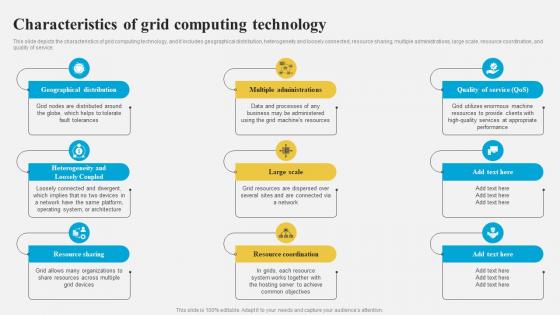 Grid Computing Architecture Characteristics Of Grid Computing Technology
Grid Computing Architecture Characteristics Of Grid Computing TechnologyThis slide depicts the characteristics of grid computing technology, and it includes geographical distribution, heterogeneity and loosely connected, resource sharing, multiple administrations, large scale, resource coordination, and quality of service. Introducing Grid Computing Architecture Characteristics Of Grid Computing Technology to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Multiple Administrations, Geographical Distribution, Resource Sharing, Resource Coordination, Heterogeneity And Loosely Coupled, using this template. Grab it now to reap its full benefits.
-
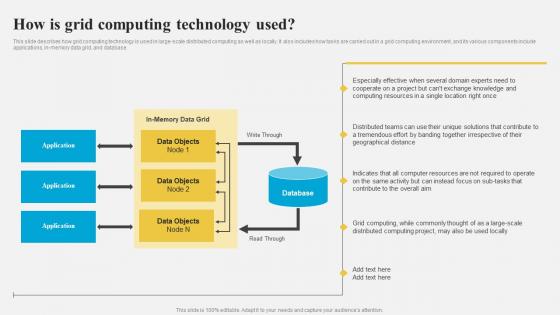 Grid Computing Architecture How Is Grid Computing Technology Used
Grid Computing Architecture How Is Grid Computing Technology UsedThis slide describes how grid computing technology is used in large-scale distributed computing as well as locally. It also includes how tasks are carried out in a grid computing environment, and its various components include applications, in-memory data grid, and database. Present the topic in a bit more detail with this Grid Computing Architecture How Is Grid Computing Technology Used. Use it as a tool for discussion and navigation on Grid Computing Technology, Large Scale Distributed Computing, Grid Computing Environment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
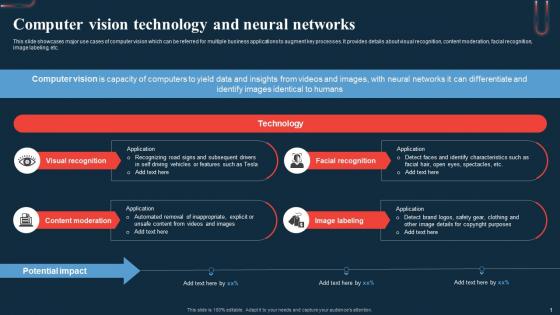 Computer Vision Technology And Neural A Beginners Guide To Neural AI SS
Computer Vision Technology And Neural A Beginners Guide To Neural AI SSThis slide showcases major use cases of computer vision which can be referred for multiple business applications to augment key processes. It provides details about visual recognition, content moderation, facial recognition, image labeling, etc. Introducing Computer Vision Technology And Neural A Beginners Guide To Neural AI SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Recognition, Moderation, Visual, using this template. Grab it now to reap its full benefits.
-
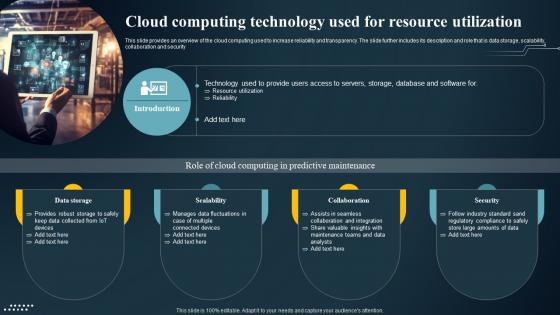 Cloud Computing Technology Used For Resource IoT Predictive Maintenance Guide IoT SS
Cloud Computing Technology Used For Resource IoT Predictive Maintenance Guide IoT SSThis slide provides an overview of the cloud computing used to increase reliability and transparency. The slide further includes its description and role that is data storage, scalability, collaboration and security.Increase audience engagement and knowledge by dispensing information using Cloud Computing Technology Used For Resource IoT Predictive Maintenance Guide IoT SS. This template helps you present information on one stage. You can also present information on Assists Seamless, Data Storage, Industry Standard using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
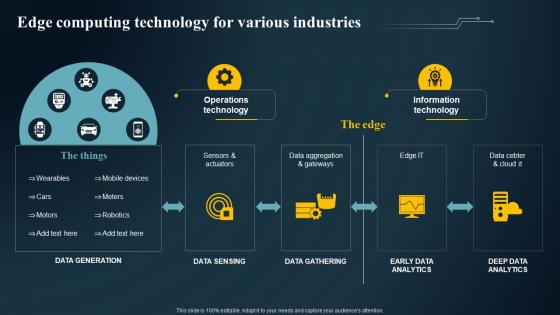 Edge Computing Technology For Various IoT Predictive Maintenance Guide IoT SS
Edge Computing Technology For Various IoT Predictive Maintenance Guide IoT SSPresent the topic in a bit more detail with this Edge Computing Technology For Various IoT Predictive Maintenance Guide IoT SS. Use it as a tool for discussion and navigation on Data Aggregation Gateways, Sensors Actuators, Information Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
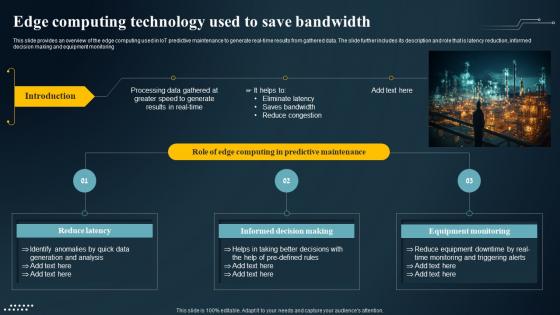 Edge Computing Technology Used To Save IoT Predictive Maintenance Guide IoT SS
Edge Computing Technology Used To Save IoT Predictive Maintenance Guide IoT SSThis slide provides an overview of the edge computing used in IoT predictive maintenance to generate real time results from gathered data. The slide further includes its description and role that is latency reduction, informed decision making and equipment monitoring.Deliver an outstanding presentation on the topic using this Edge Computing Technology Used To Save IoT Predictive Maintenance Guide IoT SS. Dispense information and present a thorough explanation of Informed Decision Making, Equipment Monitoring, Generation Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
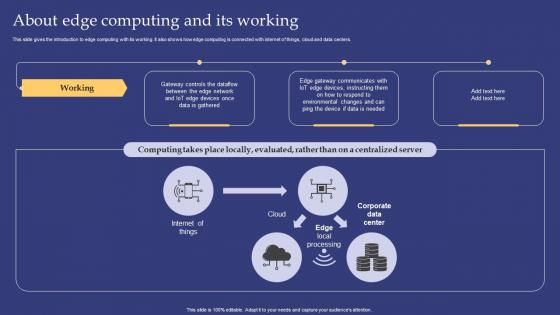 Emerging Technologies About Edge Computing And Its Working
Emerging Technologies About Edge Computing And Its WorkingThis slide gives the introduction to edge computing with its working. It also shows how edge computing is connected with internet of things, cloud and data centers. Present the topic in a bit more detail with this Emerging Technologies About Edge Computing And Its Working. Use it as a tool for discussion and navigation on Working, Internet Of Things. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
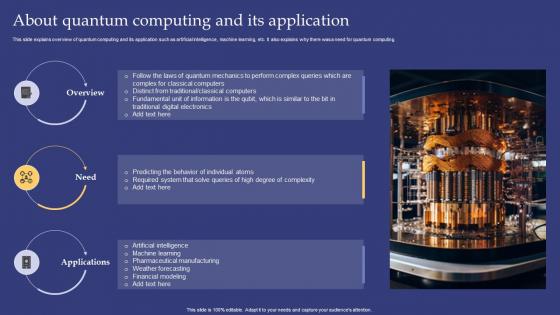 Emerging Technologies About Quantum Computing And Its Application
Emerging Technologies About Quantum Computing And Its ApplicationThis slide explains overview of quantum computing and its application such as artificial intelligence, machine learning, etc. It also explains why there was a need for quantum computing. Deliver an outstanding presentation on the topic using this Emerging Technologies About Quantum Computing And Its Application. Dispense information and present a thorough explanation of Overview, Need using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



