Powerpoint Templates and Google slides for Computing Container Cluster
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Multi Team And Cooperation In Inclavare Containers Confidential Computing System Technology
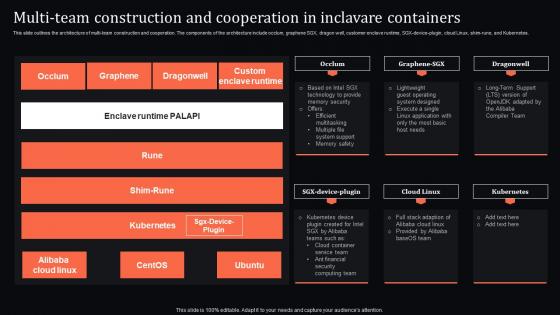
Multi Team And Cooperation In Inclavare Containers Confidential Computing System TechnologyThis slide outlines the architecture of multi-team construction and cooperation. The components of the architecture include occlum, graphene SGX, dragon well, customer enclave runtime, SGX-device-plugin, cloud Linux, shim-rune, and Kubernetes. Deliver an outstanding presentation on the topic using this Multi Team And Cooperation In Inclavare Containers Confidential Computing System Technology. Dispense information and present a thorough explanation of Construction, Cooperation, Containers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Shim Rune Workflow In Inclavare Containers Confidential Computing System Technology
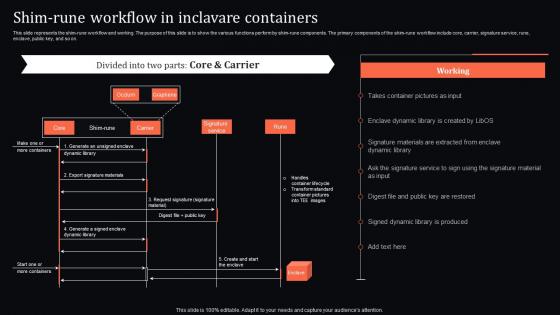
Shim Rune Workflow In Inclavare Containers Confidential Computing System TechnologyThis slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Present the topic in a bit more detail with this Shim Rune Workflow In Inclavare Containers Confidential Computing System Technology. Use it as a tool for discussion and navigation on Component, Workflow, Inclavare Containers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing Consortium Client Signature And Server Signature In Inclavare Containers
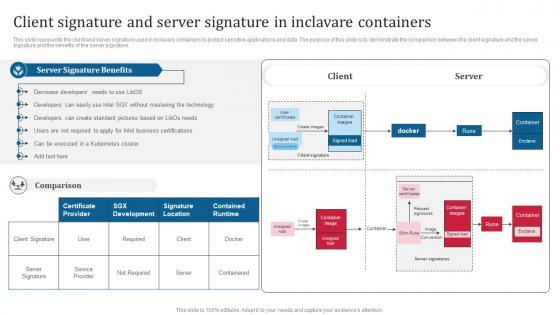
Confidential Computing Consortium Client Signature And Server Signature In Inclavare ContainersThis slide represents the client and server signature used in inclavare containers to protect sensitive applications and data. The purpose of this slide is to demonstrate the comparison between the client signature and the server signature and the benefits of the server signature. Present the topic in a bit more detail with this Confidential Computing Consortium Client Signature And Server Signature In Inclavare Containers. Use it as a tool for discussion and navigation on Client Signature, Server Signature, Inclavare Containers, Protect Sensitive Applications And Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing Hardware Components Of Inclavare Containers Architecture
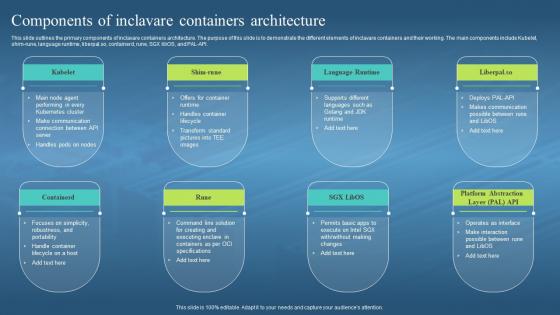
Confidential Computing Hardware Components Of Inclavare Containers ArchitectureThis slide outlines the primary components of inclavare containers architecture. The purpose of this slide is to demonstrate the different elements of inclavare containers and their working. The main components include Kubelet, shim-rune, language runtime, liberpal.so, containerd, rune, SGX libOS, and PAL-API. Increase audience engagement and knowledge by dispensing information using Confidential Computing Hardware Components Of Inclavare Containers Architecture. This template helps you present information on eight stages. You can also present information on Inclavare Containers Architecture, Demonstrate, Language Runtime, Handle Container Lifecycle using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
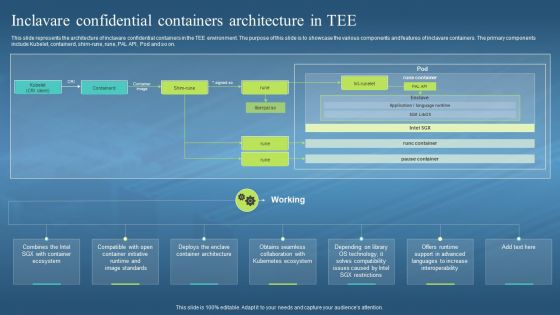 Confidential Computing Hardware Inclavare Confidential Containers Architecture In Tee
Confidential Computing Hardware Inclavare Confidential Containers Architecture In TeeThis slide represents the architecture of inclavare confidential containers in the TEE environment. The purpose of this slide is to showcase the various components and features of inclavare containers. The primary components include Kubelet, containerd, shim-rune, rune, PAL API, Pod and so on. Introducing Confidential Computing Hardware Inclavare Confidential Containers Architecture In Tee to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Architecture Of Inclavare, Confidential Containers, Tee Environment, Kubernetes Ecosystem, using this template. Grab it now to reap its full benefits.
-
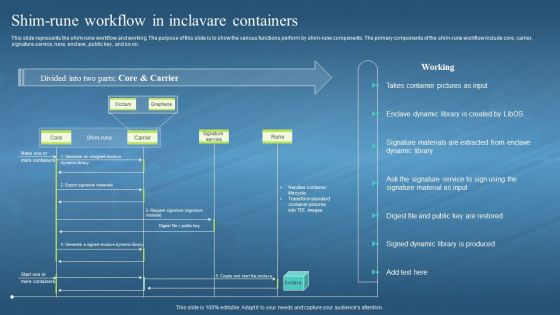 Confidential Computing Hardware Shim Rune Workflow In Inclavare Containers
Confidential Computing Hardware Shim Rune Workflow In Inclavare ContainersThis slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Present the topic in a bit more detail with this Confidential Computing Hardware Shim Rune Workflow In Inclavare Containers. Use it as a tool for discussion and navigation on Shim Rune Workflow And Working, Shim Rune Components, Signature Service, Enclave Dynamic Library. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
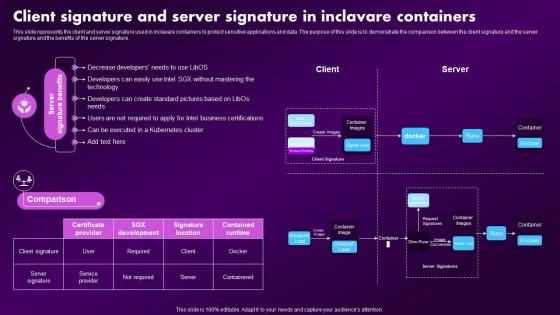 Confidential Computing Market Client Signature And Server Signature In Inclavare Containers
Confidential Computing Market Client Signature And Server Signature In Inclavare ContainersThis slide represents the client and server signature used in inclavare containers to protect sensitive applications and data. The purpose of this slide is to demonstrate the comparison between the client signature and the server signature and the benefits of the server signature. Present the topic in a bit more detail with this Confidential Computing Market Client Signature And Server Signature In Inclavare Containers. Use it as a tool for discussion and navigation on Business, Certifications, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
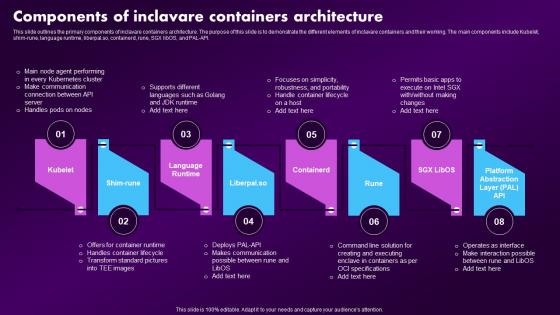 Confidential Computing Market Components Of Inclavare Containers Architecture
Confidential Computing Market Components Of Inclavare Containers ArchitectureThis slide outlines the primary components of inclavare containers architecture. The purpose of this slide is to demonstrate the different elements of inclavare containers and their working. The main components include Kubelet, shim-rune, language runtime, liberpal.so, containerd, rune, SGX libOS, and PAL-API. Increase audience engagement and knowledge by dispensing information using Confidential Computing Market Components Of Inclavare Containers Architecture. This template helps you present information on eight stages. You can also present information on Language Runtime, Containerd, Containers Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
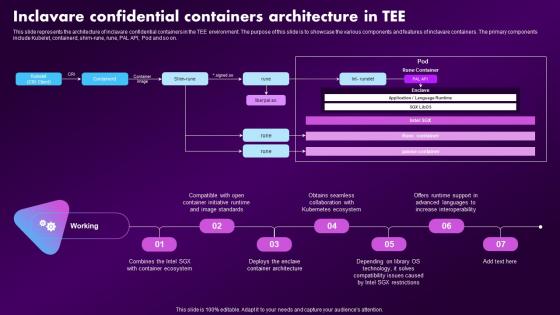 Confidential Computing Market Inclavare Confidential Containers Architecture In Tee
Confidential Computing Market Inclavare Confidential Containers Architecture In TeeThis slide represents the architecture of inclavare confidential containers in the TEE environment. The purpose of this slide is to showcase the various components and features of inclavare containers. The primary components include Kubelet, containerd, shim-rune, rune, PAL API, Pod and so on. Present the topic in a bit more detail with this Confidential Computing Market Inclavare Confidential Containers Architecture In Tee. Use it as a tool for discussion and navigation on Confidential, Containers, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
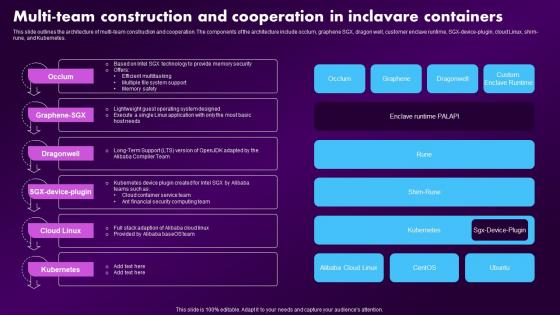 Confidential Computing Market Multi Team Construction And Cooperation In Inclavare Containers
Confidential Computing Market Multi Team Construction And Cooperation In Inclavare ContainersThis slide outlines the architecture of multi-team construction and cooperation. The components of the architecture include occlum, graphene SGX, dragon well, customer enclave runtime, SGX-device-plugin, cloud Linux, shim-rune, and Kubernetes. Present the topic in a bit more detail with this Confidential Computing Market Multi Team Construction And Cooperation In Inclavare Containers. Use it as a tool for discussion and navigation on Cooperation, Construction, Inclavare Containers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
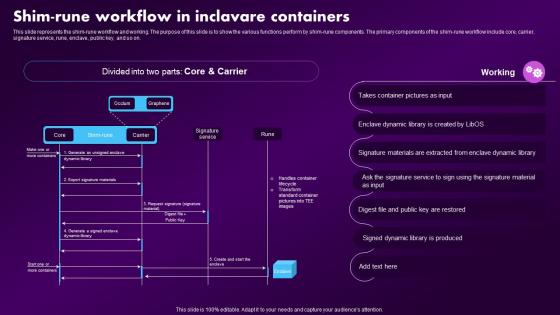 Confidential Computing Market Shim Rune Workflow In Inclavare Containers
Confidential Computing Market Shim Rune Workflow In Inclavare ContainersThis slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Deliver an outstanding presentation on the topic using this Confidential Computing Market Shim Rune Workflow In Inclavare Containers. Dispense information and present a thorough explanation of Components, Workflow, Service using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
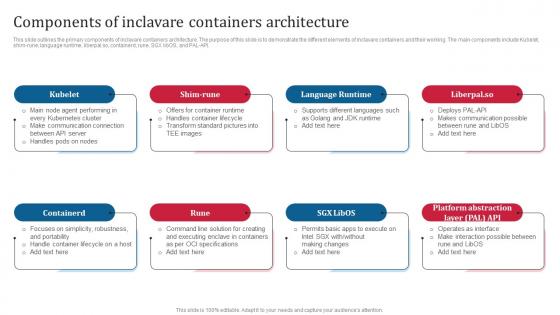 Confidential Computing Consortium Components Of Inclavare Containers Architecture
Confidential Computing Consortium Components Of Inclavare Containers ArchitectureThis slide outlines the primary components of inclavare containers architecture. The purpose of this slide is to demonstrate the different elements of inclavare containers and their working. The main components include Kubelet, shim-rune, language runtime, liberpal.so, containerd, rune, SGX libOS, and PAL-API. Increase audience engagement and knowledge by dispensing information using Confidential Computing Consortium Components Of Inclavare Containers Architecture. This template helps you present information on eight stages. You can also present information on Inclavare Containers Architecture, Shim Rune, Demonstrate, Handles Container Lifecycle using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
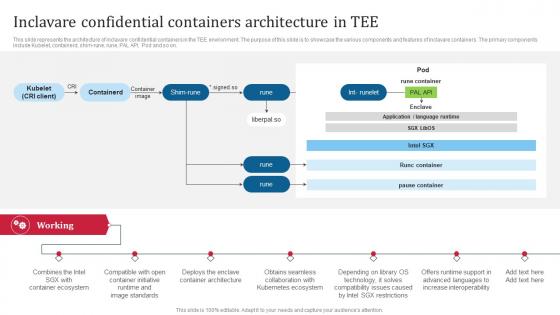 Confidential Computing Consortium Inclavare Confidential Containers Architecture In TEE
Confidential Computing Consortium Inclavare Confidential Containers Architecture In TEEThis slide represents the architecture of inclavare confidential containers in the TEE environment. The purpose of this slide is to showcase the various components and features of inclavare containers. The primary components include Kubelet, containerd, shim-rune, rune, PAL API, Pod and so on. Present the topic in a bit more detail with this Confidential Computing Consortium Inclavare Confidential Containers Architecture In TEE. Use it as a tool for discussion and navigation on Container Ecosystem, Container Initiative, Enclave Container Architecture, Kubernetes Ecosystem. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
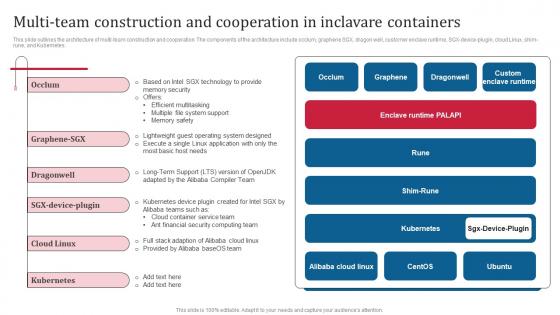 Confidential Computing Consortium Multi Team Construction And Cooperation In Inclavare Containers
Confidential Computing Consortium Multi Team Construction And Cooperation In Inclavare ContainersThis slide outlines the architecture of multi-team construction and cooperation. The components of the architecture include occlum, graphene SGX, dragon well, customer enclave runtime, SGX-device-plugin, cloud Linux, shim-rune, and Kubernetes. Deliver an outstanding presentation on the topic using this Confidential Computing Consortium Multi Team Construction And Cooperation In Inclavare Containers. Dispense information and present a thorough explanation of Efficient Multitasking, Multiple File System Support, Memory Safety, Financial Security Computing Team using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
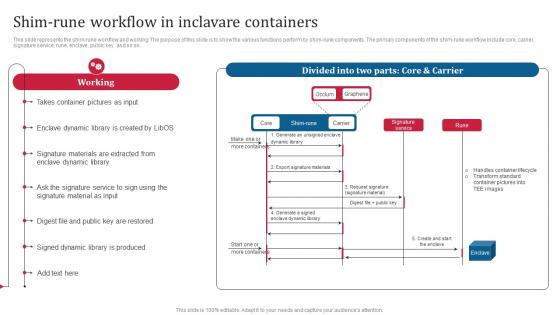 Confidential Computing Consortium Shim Rune Workflow In Inclavare Containers
Confidential Computing Consortium Shim Rune Workflow In Inclavare ContainersThis slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Deliver an outstanding presentation on the topic using this Confidential Computing Consortium Shim Rune Workflow In Inclavare Containers. Dispense information and present a thorough explanation of Handles Container Lifecycle, Transform Standard Container, Shim Rune Workflow, Shim Rune Components using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
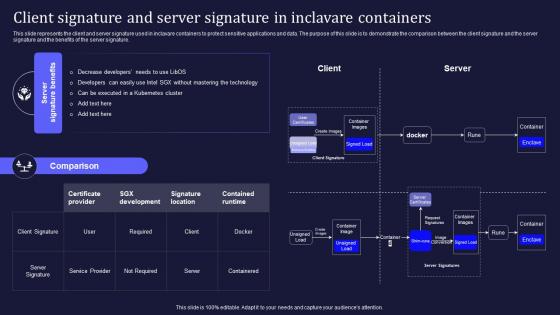 Confidential Computing V2 Client Signature And Server Signature In Inclavare Containers
Confidential Computing V2 Client Signature And Server Signature In Inclavare ContainersThis slide represents the client and server signature used in inclavare containers to protect sensitive applications and data. The purpose of this slide is to demonstrate the comparison between the client signature and the server signature and the benefits of the server signature. Present the topic in a bit more detail with this Confidential Computing V2 Client Signature And Server Signature In Inclavare Containers. Use it as a tool for discussion and navigation on Client Signature, Server Signature, Inclavare Containers, Sensitive Applications And Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Components Of Inclavare Containers Architecture
Confidential Computing V2 Components Of Inclavare Containers ArchitectureThis slide outlines the primary components of inclavare containers architecture. The purpose of this slide is to demonstrate the different elements of inclavare containers and their working. The main components include Kubelet, shim-rune, language runtime, liberpal.so, containerd, rune, SGX libOS, and PAL-API. Increase audience engagement and knowledge by dispensing information using Confidential Computing V2 Components Of Inclavare Containers Architecture. This template helps you present information on eight stages. You can also present information on Language Runtime, Platform Abstraction Layer, Robustness And Portability, Communication Connection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
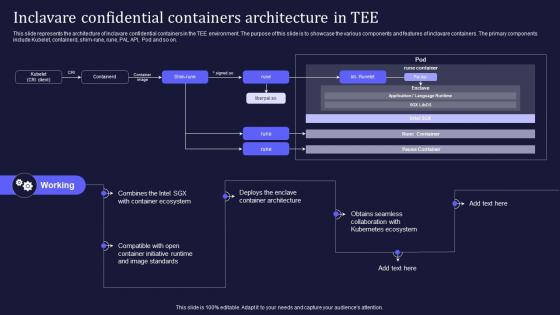 Confidential Computing V2 Inclavare Confidential Containers Architecture In TEE
Confidential Computing V2 Inclavare Confidential Containers Architecture In TEEThis slide represents the architecture of inclavare confidential containers in the TEE environment. The purpose of this slide is to showcase the various components and features of inclavare containers. The primary components include Kubelet, containerd, shim-rune, rune, PAL API, Pod and so on. Present the topic in a bit more detail with this Confidential Computing V2 Inclavare Confidential Containers Architecture In TEE. Use it as a tool for discussion and navigation on Obtains Seamless Collaboration, Kubernetes Ecosystem, Container Initiative Runtime, Enclave Container Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
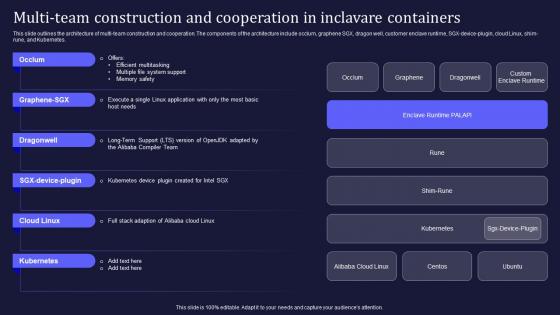 Confidential Computing V2 Multi Team Construction And Cooperation In Inclavare Containers
Confidential Computing V2 Multi Team Construction And Cooperation In Inclavare ContainersThis slide outlines the architecture of multi-team construction and cooperation. The components of the architecture include occlum, graphene SGX, dragon well, customer enclave runtime, SGX-device-plugin, cloud Linux, shim-rune, and Kubernetes. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Multi Team Construction And Cooperation In Inclavare Containers. Dispense information and present a thorough explanation of Efficient Multitasking, Multiple File System Support, Memory Safety, Multi Team Construction using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing V2 Shim Rune Workflow In Inclavare Containers
Confidential Computing V2 Shim Rune Workflow In Inclavare ContainersThis slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Present the topic in a bit more detail with this Confidential Computing V2 Shim Rune Workflow In Inclavare Containers. Use it as a tool for discussion and navigation on Shim Rune Workflow, Shim Rune Components, Enclave Dynamic Library, Handles Container Lifecycle. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
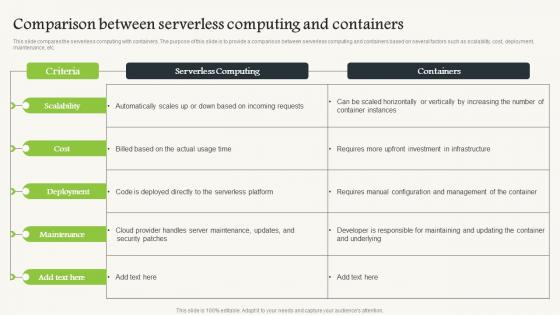 Comparison Between Serverless Computing V2 And Containers
Comparison Between Serverless Computing V2 And ContainersThis slide compares the serverless computing with containers. The purpose of this slide is to provide a comparison between serverless computing and containers based on several factors such as scalability, cost, deployment, maintenance, etc. Deliver an outstanding presentation on the topic using this Comparison Between Serverless Computing V2 And Containers. Dispense information and present a thorough explanation of Serverless Computing And Containers, Deployment, Serverless Platform, Requires Manual Configuration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
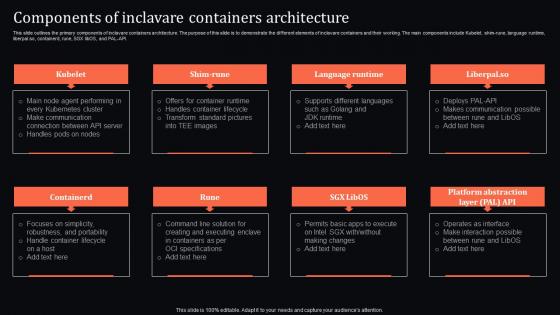 Confidential Computing System Technology Components Of Inclavare Containers Architecture
Confidential Computing System Technology Components Of Inclavare Containers ArchitectureThis slide outlines the primary components of inclavare containers architecture. The purpose of this slide is to demonstrate the different elements of inclavare containers and their working. The main components include Kubelet, shim-rune, language runtime, liberpal.so, containerd, rune, SGX libOS, and PAL-API. Increase audience engagement and knowledge by dispensing information using Confidential Computing System Technology Components Of Inclavare Containers Architecture. This template helps you present information on eight stages. You can also present information on Language Runtime, Containers Architecture, Components using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
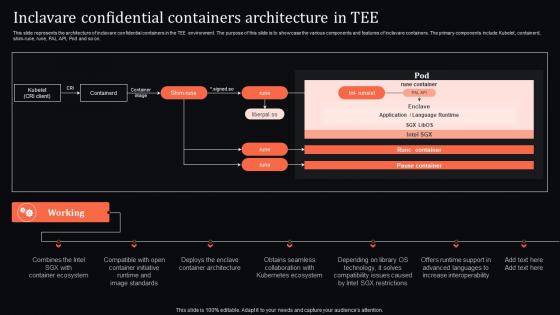 Confidential Computing System Technology Inclavare Confidential Containers Architecture In Tee
Confidential Computing System Technology Inclavare Confidential Containers Architecture In TeeThis slide represents the architecture of inclavare confidential containers in the TEE environment. The purpose of this slide is to showcase the various components and features of inclavare containers. The primary components include Kubelet, containerd, shim-rune, rune, PAL API, Pod and so on. Deliver an outstanding presentation on the topic using this Confidential Computing System Technology Inclavare Confidential Containers Architecture In Tee. Dispense information and present a thorough explanation of Collaboration, Technology, Compatibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Containerization Technology Comparative Analysis Of Containers And Serverless Computing
Containerization Technology Comparative Analysis Of Containers And Serverless ComputingThis slide showcases the difference between containers and serverless computing technology. This slide highlights the key differences between containerization and serverless computing based on physical machines, scalability, cost, maintenance, and so on. Deliver an outstanding presentation on the topic using this Containerization Technology Comparative Analysis Of Containers And Serverless Computing. Dispense information and present a thorough explanation of Comparative Analysis Of Containers, Serverless Computing, Physical Machines, Scalability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Client Signature And Server Signature In Inclavare Containers Confidential Computing It
Client Signature And Server Signature In Inclavare Containers Confidential Computing ItThis slide represents the client and server signature used in inclavare containers to protect sensitive applications and data. The purpose of this slide is to demonstrate the comparison between the client signature and the server signature and the benefits of the server signature. Present the topic in a bit more detail with this Client Signature And Server Signature In Inclavare Containers Confidential Computing It. Use it as a tool for discussion and navigation on Server Signature Benefits, Technology, Business Certifications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
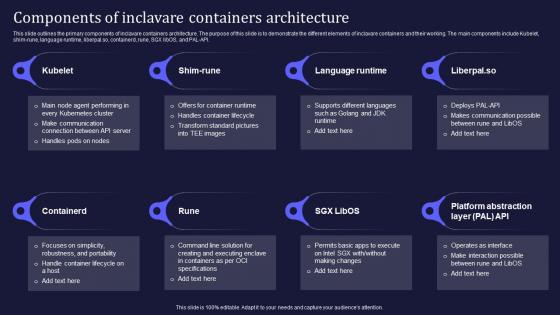 Components Of Inclavare Containers Architecture Confidential Computing It
Components Of Inclavare Containers Architecture Confidential Computing ItThis slide outlines the primary components of inclavare containers architecture. The purpose of this slide is to demonstrate the different elements of inclavare containers and their working. The main components include Kubelet, shim rune, language runtime, liberpal.so, containerd, rune, SGX libOS, and PAL API. Introducing Components Of Inclavare Containers Architecture Confidential Computing It to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Agent Performing, Communication Connection, TEE Images, using this template. Grab it now to reap its full benefits.
-
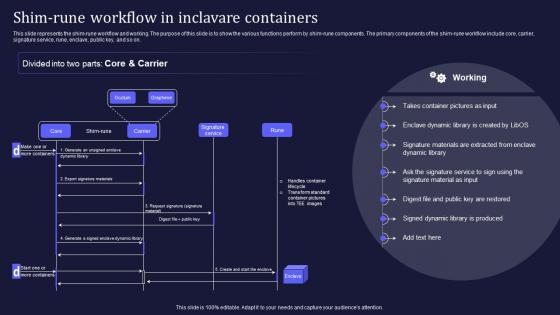 Confidential Computing It Shim Rune Workflow In Inclavare Containers
Confidential Computing It Shim Rune Workflow In Inclavare ContainersThis slide represents the shim rune workflow and working. The purpose of this slide is to show the various functions perform by shim rune components. The primary components of the shim rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Present the topic in a bit more detail with this Confidential Computing It Shim Rune Workflow In Inclavare Containers. Use it as a tool for discussion and navigation on Working, Dynamic Library, Signature Materials. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
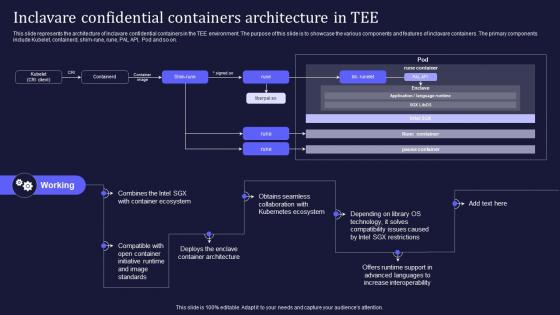 Inclavare Confidential Containers Architecture In Tee Confidential Computing IT
Inclavare Confidential Containers Architecture In Tee Confidential Computing ITThis slide represents the architecture of inclavare confidential containers in the TEE environment. The purpose of this slide is to showcase the various components and features of inclavare containers. The primary components include Kubelet, containerd, shim rune, rune, PAL API, Pod and so on. Increase audience engagement and knowledge by dispensing information using Inclavare Confidential Containers Architecture In Tee Confidential Computing IT. This template helps you present information on seven stages. You can also present information on Working, Container Ecosystem, Kubernetes Ecosystem using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
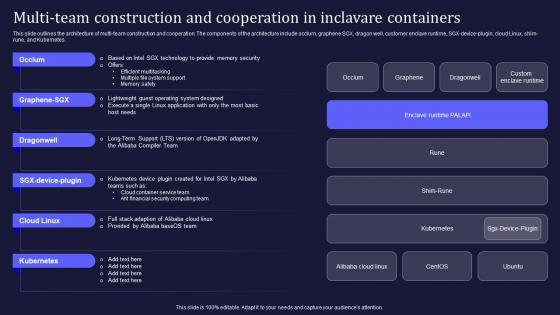 Multi Team Construction And Cooperation In Inclavare Containers Confidential Computing IT
Multi Team Construction And Cooperation In Inclavare Containers Confidential Computing ITThis slide outlines the architecture of multi team construction and cooperation. The components of the architecture include occlum, graphene SGX, dragon well, customer enclave runtime, SGX device plugin, cloud Linux, shim rune, and Kubernetes. Deliver an outstanding presentation on the topic using this Multi Team Construction And Cooperation In Inclavare Containers Confidential Computing IT. Dispense information and present a thorough explanation of SGX Technology, System Support, Memory Safety using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Parameters To Select Cyber Security Containment Strategy Deploying Computer Security Incident
Key Parameters To Select Cyber Security Containment Strategy Deploying Computer Security IncidentThis slide represents the various parameters to look for before choosing an effective and efficient cyber security containment strategy. It includes key parameters such as higher potential damages and theft of organizational resources etc.Introducing Key Parameters To Select Cyber Security Containment Strategy Deploying Computer Security Incident to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Potential Damages, Organizational Resources, Containment Strategy, using this template. Grab it now to reap its full benefits.
-
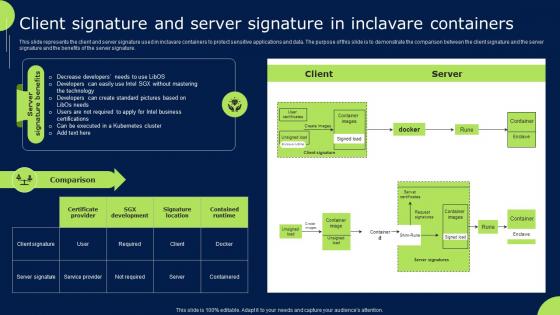 Confidential Cloud Computing Client Signature And Server Signature In Inclavare Containers
Confidential Cloud Computing Client Signature And Server Signature In Inclavare ContainersThis slide represents the client and server signature used in inclavare containers to protect sensitive applications and data. The purpose of this slide is to demonstrate the comparison between the client signature and the server signature and the benefits of the server signature. Present the topic in a bit more detail with this Confidential Cloud Computing Client Signature And Server Signature In Inclavare Containers. Use it as a tool for discussion and navigation on Containers, Server, Signature. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
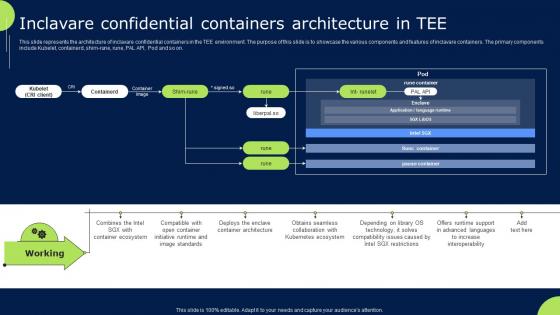 Confidential Cloud Computing Inclavare Confidential Containers Architecture In Tee
Confidential Cloud Computing Inclavare Confidential Containers Architecture In Teeslide represents the architecture of inclavare confidential containers in the TEE environment. The purpose of this slide is to showcase the various components and features of inclavare containers. The primary components include Kubelet, containerd, shim-rune, rune, PAL API, Pod and so on. Present the topic in a bit more detail with this Confidential Cloud Computing Inclavare Confidential Containers Architecture In Tee. Use it as a tool for discussion and navigation on Confidential, Containers, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
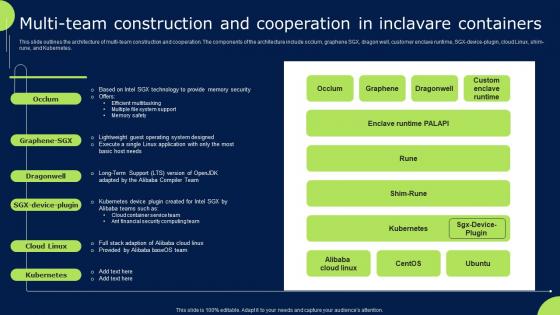 Confidential Cloud Computing Multi Team Construction And Cooperation In Inclavare Containers
Confidential Cloud Computing Multi Team Construction And Cooperation In Inclavare ContainersThis slide outlines the architecture of multi-team construction and cooperation. The components of the architecture include occlum, graphene SGX, dragon well, customer enclave runtime, SGX-device-plugin, cloud Linux, shim-rune, and Kubernetes. Deliver an outstanding presentation on the topic using this Confidential Cloud Computing Multi Team Construction And Cooperation In Inclavare Containers. Dispense information and present a thorough explanation of Construction, Cooperation, Containers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
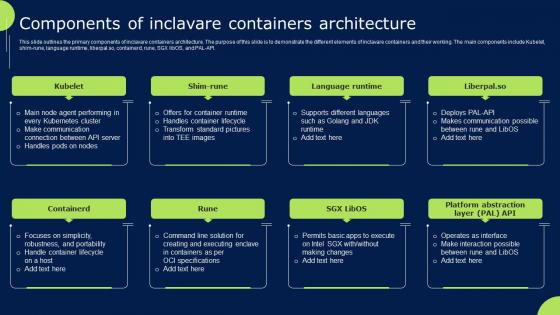 Components Of Inclavare Containers Architecture Confidential Cloud Computing
Components Of Inclavare Containers Architecture Confidential Cloud ComputingThis slide outlines the primary components of inclavare containers architecture. The purpose of this slide is to demonstrate the different elements of inclavare containers and their working. The main components include Kubelet, shim-rune, language runtime, liberpal.so, containerd, rune, SGX libOS, and PAL-API. Increase audience engagement and knowledge by dispensing information using Components Of Inclavare Containers Architecture Confidential Cloud Computing. This template helps you present information on eight stages. You can also present information on Language Runtime, Containers, Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
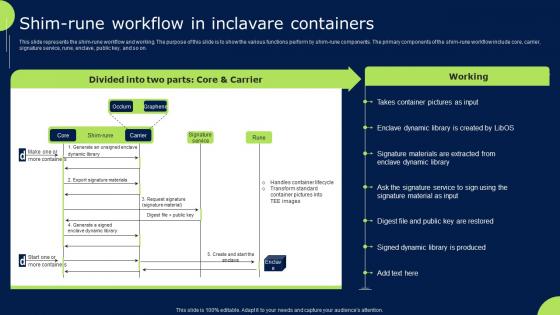 Shim Rune Workflow In Inclavare Containers Confidential Cloud Computing
Shim Rune Workflow In Inclavare Containers Confidential Cloud ComputingThis slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Present the topic in a bit more detail with this Shim Rune Workflow In Inclavare Containers Confidential Cloud Computing. Use it as a tool for discussion and navigation on Containers, Workflow, Components.. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparison Between Serverless Computing And Containers Serverless Computing
Comparison Between Serverless Computing And Containers Serverless ComputingThis slide compares the serverless computing with containers. The purpose of this slide is to provide a comparison between serverless computing and containers based on several factors such as definition, scalability, cost, deployment, use cases, etc. Deliver an outstanding presentation on the topic using this Comparison Between Serverless Computing And Containers Serverless Computing. Dispense information and present a thorough explanation of Serverless Computing, Maintenance, Underlying Infrastructure, Container And Underlying using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Powerpoint template contains graphics of computer and mobile with 100 percent satisfies text
Powerpoint template contains graphics of computer and mobile with 100 percent satisfies textAre you looking for inspirational design ideas or a fully equipped template for your next presentation Then this Powerpoint Template Contains Graphics Of Computer And Mobile With 100 Percent Satisfies Text is an ideal fit for your next delivery. Portray your principal ideas and make your presentation stand out with this design. Make your audience fully aware of the concept by presenting information in an accessible way. The streamlined layout of this design will help your audience understand and retain the complicated idea thereby making it an impactful delivery. It can be used in businesses and organizations such as corporal presentations case studies reports marketing or any other academic presentation to make your message clear and distinctive. This PPT is designed as per the emerging trends in the marketplace and therefore you will face no difficulty in adapting it to your setting. The high resolution graphics and images make it free from any form of pixelation thus making your presentation delivery an absolute success.
-
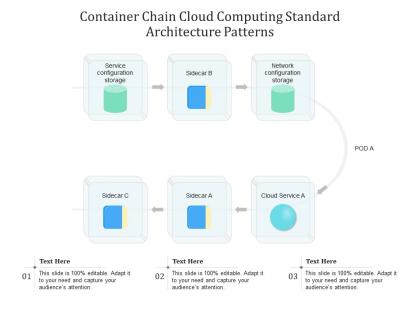 Container chain cloud computing standard architecture patterns ppt presentation diagram
Container chain cloud computing standard architecture patterns ppt presentation diagramHere is a slide titled Container Chain Cloud Computing Standard Architecture Patterns Ppt Presentation Diagram. Describe cloud computing patterns and their applications using this contemporary presentation template available in standard and widescreen sizes. Topics such as Service Configuration Storage, Network Configuration Storage, Cloud Service can be discussed with the help of this PowerPoint theme. Hit the download button and instantly elevate your presentation with our customizable PPT template.
-
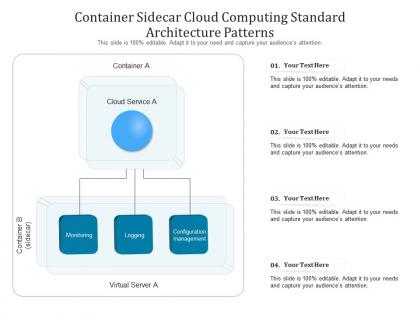 Container sidecar cloud computing standard architecture patterns ppt powerpoint slide
Container sidecar cloud computing standard architecture patterns ppt powerpoint slideUtilize this visually appealing slide titled Container Sidecar Cloud Computing Standard Architecture Patterns Ppt Powerpoint Slide. Elucidate the concept of cloud computing patterns using this editable PowerPoint presentation. Explain Monitoring, Logging, Configuration Management using this PPT theme. Instantly grab the attention of your audience by downloading this professionally designed PPT template.
-
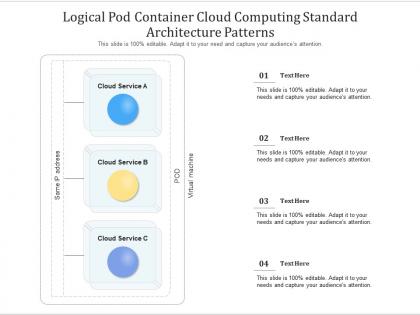 Logical pod container cloud computing standard architecture patterns ppt powerpoint slide
Logical pod container cloud computing standard architecture patterns ppt powerpoint slideHere is a slide titled Logical Pod Container Cloud Computing Standard Architecture Patterns Ppt Powerpoint Slide. Describe cloud computing patterns and their applications using this contemporary presentation template available in standard and widescreen sizes. Topics such as Logical Pod Container, Cloud Computing, Standard Architecture Patterns can be discussed with the help of this PowerPoint theme. Hit the download button and instantly elevate your presentation with our customizable PPT template.
-
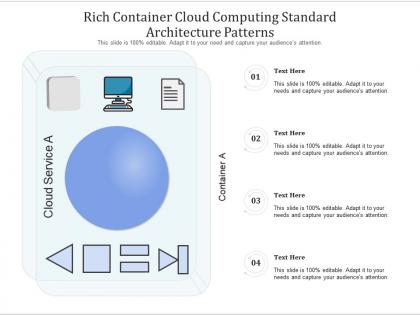 Rich container cloud computing standard architecture patterns ppt presentation diagram
Rich container cloud computing standard architecture patterns ppt presentation diagramHere is a slide titled Rich Container Cloud Computing Standard Architecture Patterns Ppt Presentation Diagram. Describe cloud computing patterns and their applications using this contemporary presentation template available in standard and widescreen sizes. Topics such as Rich Container, Cloud Computing, Standard Architecture Patterns can be discussed with the help of this PowerPoint theme. Hit the download button and instantly elevate your presentation with our customizable PPT template.
-
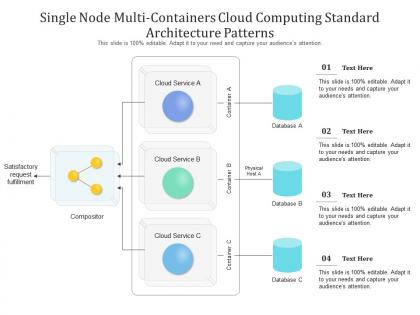 Single node multi containers cloud computing standard architecture patterns ppt presentation diagram
Single node multi containers cloud computing standard architecture patterns ppt presentation diagramShowcase your expertise on cloud computing patterns by introducing this slide titled Single Node Multi Containers Cloud Computing Standard Architecture Patterns Ppt Presentation Diagram. This PowerPoint template is compatible with both the standard and widescreen sizes. Give insights into the concepts such as Satisfactory Request Fulfillment, Compositor, Cloud Service with our pre-designed PPT theme. Download this information technology PowerPoint template now.
-
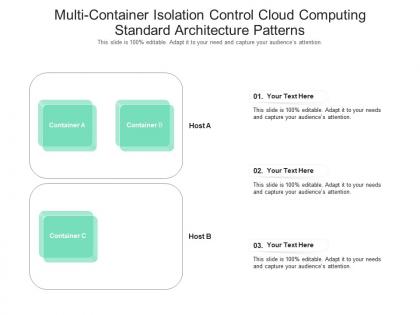 Multi container isolation control cloud computing standard architecture patterns ppt presentation diagram
Multi container isolation control cloud computing standard architecture patterns ppt presentation diagramShowcase your expertise on cloud computing patterns by introducing this slide titled Multi Container Isolation Control Cloud Computing Standard Architecture Patterns Ppt Presentation Diagram. This PowerPoint template is compatible with both the standard and widescreen sizes. Give insights into the concepts such as Multi Container Isolation, Control Cloud Computing, Standard Architecture Patterns with our pre-designed PPT theme. Download this information technology PowerPoint template now.

