Powerpoint Templates and Google slides for Conduct Cybersecurity
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
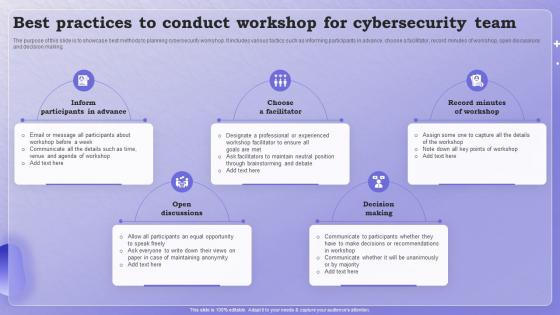 Best Practices To Conduct Workshop For Cybersecurity Team
Best Practices To Conduct Workshop For Cybersecurity TeamThe purpose of this slide is to showcase best methods to planning cybersecurity workshop. It includes various tactics such as informing participants in advance, choose a facilitator, record minutes of workshop, open discussions and decision making. Presenting our set of slides with Best Practices To Conduct Workshop For Cybersecurity Team. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Open Discussions, Decision Making.
-
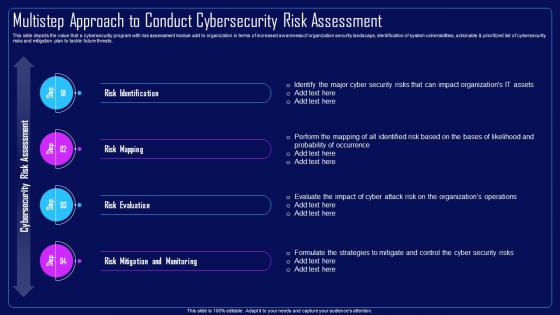 Action Plan To Combat Cyber Crimes Multistep Approach To Conduct Cybersecurity Risk Assessment
Action Plan To Combat Cyber Crimes Multistep Approach To Conduct Cybersecurity Risk AssessmentThis slide depicts the value that a cybersecurity program with risk assessment module add to organization in terms of increased awareness of organization security landscape, identification of system vulnerabilities, actionable and prioritized list of cybersecurity risks and mitigation plan to tackle future threats. Increase audience engagement and knowledge by dispensing information using Action Plan To Combat Cyber Crimes Multistep Approach To Conduct Cybersecurity Risk Assessment. This template helps you present information on four stages. You can also present information on Risk Identification, Risk Mapping, Risk Evaluation, Risk Mitigation And Monitoring using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
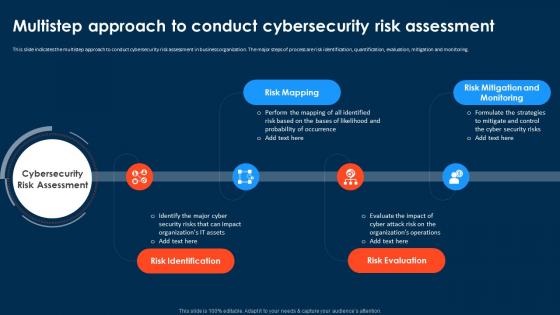 Compressive Planning Guide Multistep Approach To Conduct Cybersecurity Risk Assessment
Compressive Planning Guide Multistep Approach To Conduct Cybersecurity Risk AssessmentThis slide indicates the multistep approach to conduct cybersecurity risk assessment in business organization. The major steps of process are risk identification, quantification, evaluation, mitigation and monitoring. Introducing Compressive Planning Guide Multistep Approach To Conduct Cybersecurity Risk Assessment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Risk Mapping, Risk Mitigation And Monitoring, Risk Evaluation, Risk Identification, using this template. Grab it now to reap its full benefits.
-
 Security Plan To Prevent Cyber Multistep Approach To Conduct Cybersecurity Risk Assessment
Security Plan To Prevent Cyber Multistep Approach To Conduct Cybersecurity Risk AssessmentThis slide indicates the multistep approach to conduct cybersecurity risk assessment in business organization. The major steps of process are risk identification, quantification, evaluation, mitigation and monitoring. Increase audience engagement and knowledge by dispensing information using Security Plan To Prevent Cyber Multistep Approach To Conduct Cybersecurity Risk Assessment. This template helps you present information on four stages. You can also present information on Risk Identification, Risk Mapping, Risk Evaluation, Risk Mitigation And Monitoring using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Need To Conduct IoT Security Improving IoT Device Cybersecurity IoT SS
Need To Conduct IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase the major reasons for conducting Internet of Things IoT security awareness training. Information covered in this slide is related to employees familiarity with cybersecurity policies and procedure, updating the software, etc. Increase audience engagement and knowledge by dispensing information using Need To Conduct IoT Security Improving IoT Device Cybersecurity IoT SS. This template helps you present information on five stages. You can also present information on Cybersecurity, Potential, Software using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
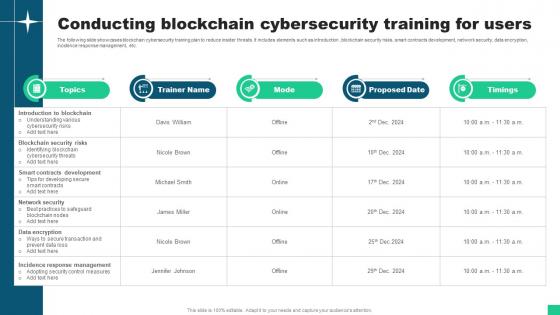
 Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS V
Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction ,blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS V. Dispense information and present a thorough explanation of Trainer Name, Mode, Proposed Date using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Conducting Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V
Conducting Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction ,blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Conducting Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Introduction Blockchain, Blockchain Security Risks, Smart Contracts Development using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Conducting Blockchain Cybersecurity Training For Users Guide For Blockchain BCT SS V
Conducting Blockchain Cybersecurity Training For Users Guide For Blockchain BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction ,blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Conducting Blockchain Cybersecurity Training For Users Guide For Blockchain BCT SS V Dispense information and present a thorough explanation of Blockchain Security Risks, Development, Network Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS V
Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction, blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS V Dispense information and present a thorough explanation of Introduction To Blockchain, Blockchain Security Risks, Smart Contracts Development using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity Risk Assessment Program Multistep Approach To Conduct Cybersecurity Risk Assessment
Cybersecurity Risk Assessment Program Multistep Approach To Conduct Cybersecurity Risk AssessmentThis slide indicates the multistep approach to conduct cybersecurity risk assessment in business organization. The major steps of process are risk identification, quantification, evaluation, mitigation and monitoring. Introducing Cybersecurity Risk Assessment Program Multistep Approach To Conduct Cybersecurity Risk Assessment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Risk Mitigation, Monitoring, Risk Evaluation, Risk Mapping, Risk Identification, using this template. Grab it now to reap its full benefits.
-
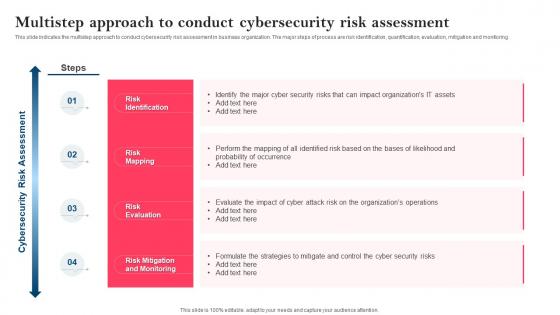 Strategy To Minimize Cyber Attacks Multistep Approach To Conduct Cybersecurity Risk Assessment
Strategy To Minimize Cyber Attacks Multistep Approach To Conduct Cybersecurity Risk AssessmentThis slide indicates the multistep approach to conduct cybersecurity risk assessment in business organization. The major steps of process are risk identification, quantification, evaluation, mitigation and monitoring. Introducing Strategy To Minimize Cyber Attacks Multistep Approach To Conduct Cybersecurity Risk Assessment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Risk Identification, Risk Mapping, Risk Evaluation, Risk Mitigation And Monitoring, using this template. Grab it now to reap its full benefits.
-
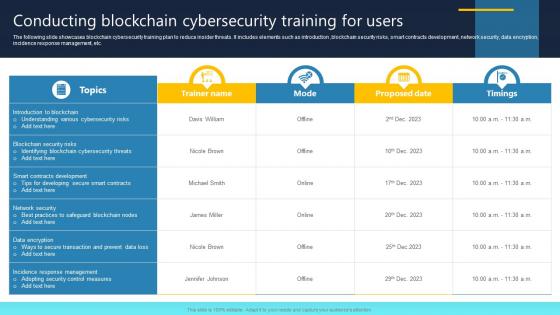 Ultimate Guide For Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS
Ultimate Guide For Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SSThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction ,blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Ultimate Guide For Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS Dispense information and present a thorough explanation of Blockchain Nodes, Control Measures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
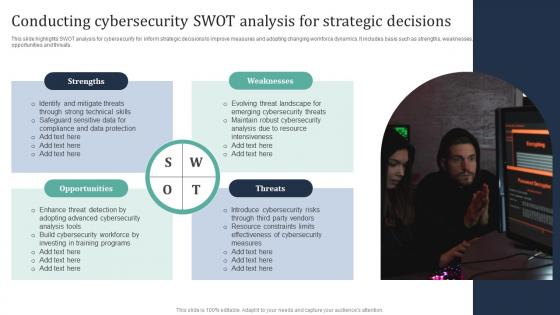 Conducting Cybersecurity SWOT Analysis For Strategic Decisions
Conducting Cybersecurity SWOT Analysis For Strategic DecisionsThis slide highlights SWOT analysis for cybersecurity for inform strategic decisions to improve measures and adopting changing workforce dynamics. It includes basis such as strengths, weaknesses, opportunities and threats. Presenting our set of slides with Conducting Cybersecurity SWOT Analysis For Strategic Decisions. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Technical, Protection, Cybersecurity.

