Powerpoint Templates and Google slides for Confidential Computing For Organizations
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
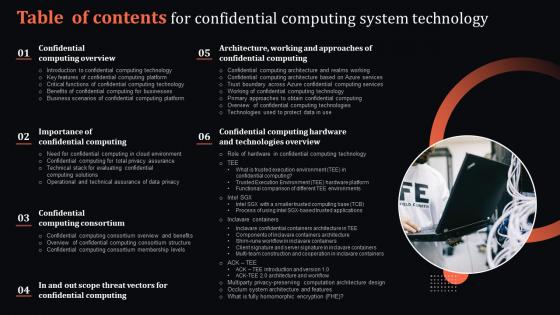 Table Of Contents For Confidential Computing System Technology
Table Of Contents For Confidential Computing System TechnologyIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Confidential Computing System Technology. This template helps you present information on six stages. You can also present information on Confidential Computing Overview, Importance Of Confidential Computing, Confidential Computing Consortium using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
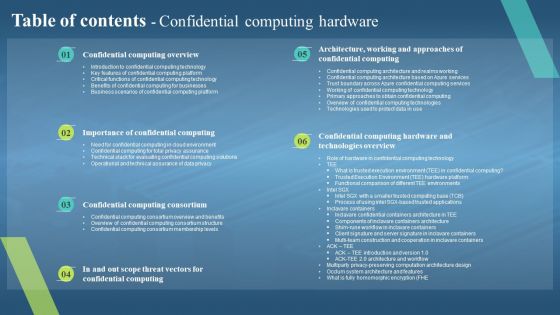 Table Of Contents Confidential Computing Hardware Ppt Icon File Formats
Table Of Contents Confidential Computing Hardware Ppt Icon File FormatsIncrease audience engagement and knowledge by dispensing information using Table Of Contents Confidential Computing Hardware Ppt Icon File Formats. This template helps you present information on six stages. You can also present information on Importance Of Confidential Computing, Confidential Computing Overview, Architecture, Working And Approaches Of Confidential Computing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
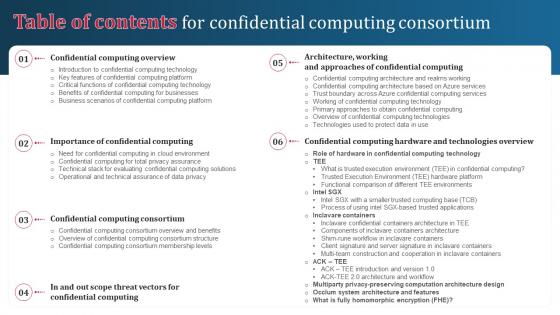 Table Of Contents For Confidential Computing Consortium Ppt Ideas Background Designs
Table Of Contents For Confidential Computing Consortium Ppt Ideas Background DesignsIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Confidential Computing Consortium Ppt Ideas Background Designs. This template helps you present information on six stages. You can also present information on Confidential Computing Overview, Confidential Computing Consortium, Technologies Overview using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
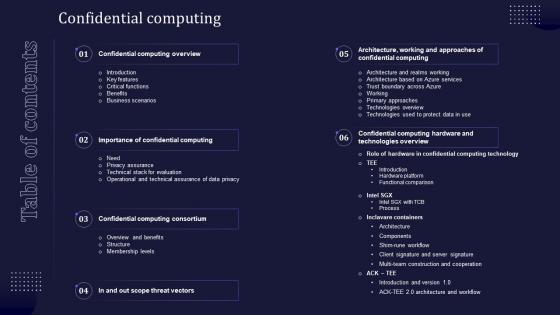 Table Of Contents For Confidential Computing V2 Ppt Infographics Demonstration
Table Of Contents For Confidential Computing V2 Ppt Infographics DemonstrationIntroducing Table Of Contents For Confidential Computing V2 Ppt Infographics Demonstration to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Confidential Computing Overview, Confidential Computing Hardware, Technologies Overview, Confidential Computing Consortium, using this template. Grab it now to reap its full benefits.
-
 Agenda For Confidential Computing System Technology
Agenda For Confidential Computing System TechnologyIntroducing Agenda For Confidential Computing System Technology to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Applications, Environment, using this template. Grab it now to reap its full benefits.
-
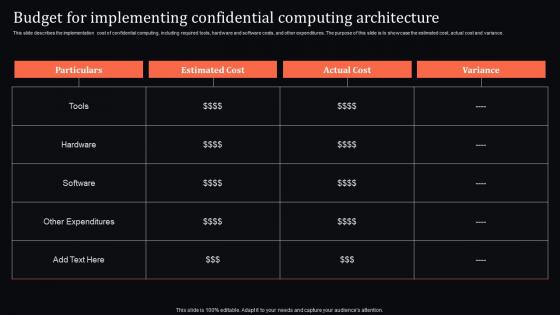 Budget For Implementing Architecture Confidential Computing System Technology
Budget For Implementing Architecture Confidential Computing System TechnologyThis slide describes the implementation cost of confidential computing, including required tools, hardware and software costs, and other expenditures. The purpose of this slide is to showcase the estimated cost, actual cost and variance. Deliver an outstanding presentation on the topic using this Budget For Implementing Architecture Confidential Computing System Technology. Dispense information and present a thorough explanation of Implementing, Confidential, Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
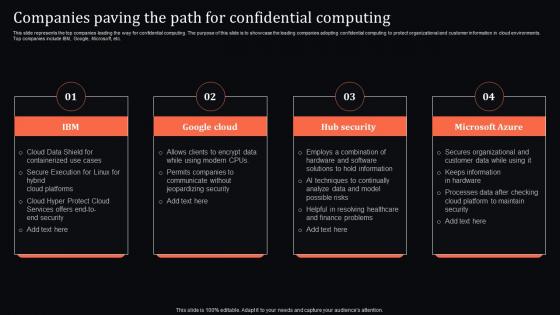 Companies Paving The Path For Confidential Computing System Technology
Companies Paving The Path For Confidential Computing System TechnologyThis slide represents the top companies leading the way for confidential computing. The purpose of this slide is to showcase the leading companies adopting confidential computing to protect organizational and customer information in cloud environments. Top companies include IBM, Google, Microsoft, etc. Introducing Companies Paving The Path For Confidential Computing System Technology to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Containerized, Services, Execution, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing System Technology For Table Of Contents
Confidential Computing System Technology For Table Of ContentsIntroducing Confidential Computing System Technology For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Approaches, Architecture, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Confidential Computing System Technology
Icons Slide For Confidential Computing System TechnologyPresent the topic in a bit more detail with this Icons Slide For Confidential Computing System Technology. Use it as a tool for discussion and navigation on Icons. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
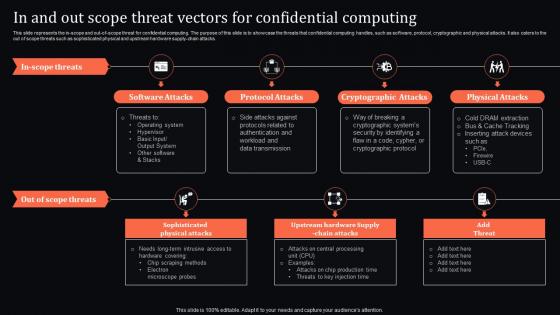 In And Threat Vectors For Confidential Computing Confidential Computing System Technology
In And Threat Vectors For Confidential Computing Confidential Computing System TechnologyThis slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Increase audience engagement and knowledge by dispensing information using In And Threat Vectors For Confidential Computing Confidential Computing System Technology. This template helps you present information on seven stages. You can also present information on Software Attacks, Protocol Attacks, Cryptographic Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
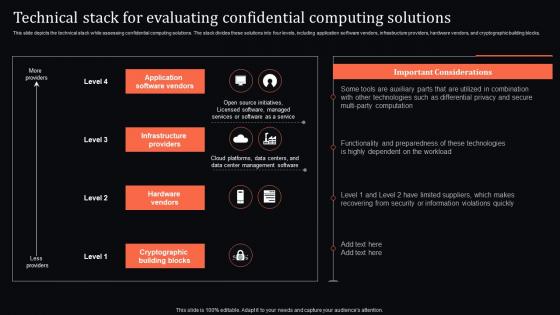 Technical Stack For Confidential Computing Solutions Confidential Computing System Technology
Technical Stack For Confidential Computing Solutions Confidential Computing System TechnologyThis slide depicts the technical stack while assessing confidential computing solutions. The stack divides these solutions into four levels, including application software vendors, infrastructure providers, hardware vendors, and cryptographic building blocks. Present the topic in a bit more detail with this Technical Stack For Confidential Computing Solutions Confidential Computing System Technology. Use it as a tool for discussion and navigation on Application Software Vendors, Infrastructure Providers, Hardware Vendors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
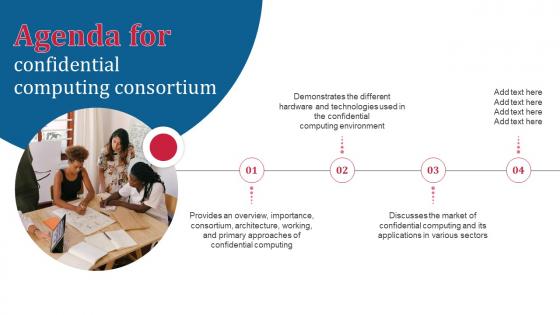 Agenda For Confidential Computing Consortium Ppt Icon Example Introduction
Agenda For Confidential Computing Consortium Ppt Icon Example IntroductionIntroducing Agenda For Confidential Computing Consortium Ppt Icon Example Introduction to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Consortium, Architecture, Working And Primary Approaches, Confidential Computing, using this template. Grab it now to reap its full benefits.
-
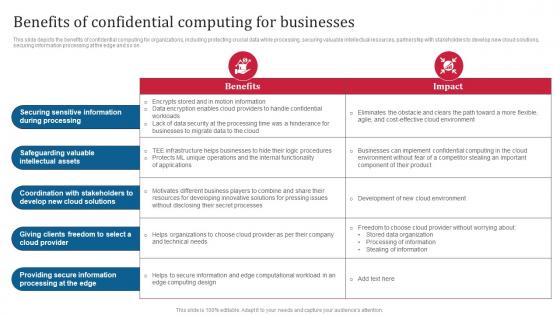 Confidential Computing Consortium Benefits Of Confidential Computing For Businesses
Confidential Computing Consortium Benefits Of Confidential Computing For BusinessesThis slide depicts the benefits of confidential computing for organizations, including protecting crucial data while processing, securing valuable intellectual resources, partnership with stakeholders to develop new cloud solutions, securing information processing at the edge and so on. Present the topic in a bit more detail with this Confidential Computing Consortium Benefits Of Confidential Computing For Businesses. Use it as a tool for discussion and navigation on Securing Sensitive Information, Safeguarding Valuable Intellectual Assets, Coordination With Stakeholders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
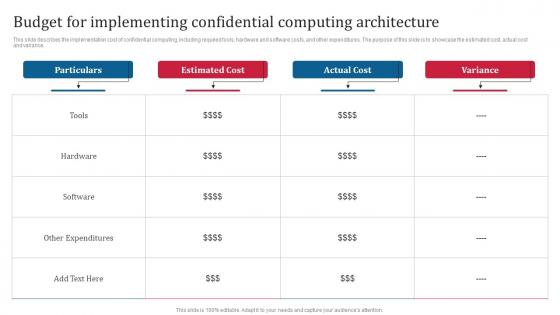 Confidential Computing Consortium Budget For Implementing Confidential Computing Architecture
Confidential Computing Consortium Budget For Implementing Confidential Computing ArchitectureThis slide describes the implementation cost of confidential computing, including required tools, hardware and software costs, and other expenditures. The purpose of this slide is to showcase the estimated cost, actual cost and variance. Deliver an outstanding presentation on the topic using this Confidential Computing Consortium Budget For Implementing Confidential Computing Architecture. Dispense information and present a thorough explanation of Budget For Implementing Confidential, Computing Architecture, Hardware And Software Costs using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
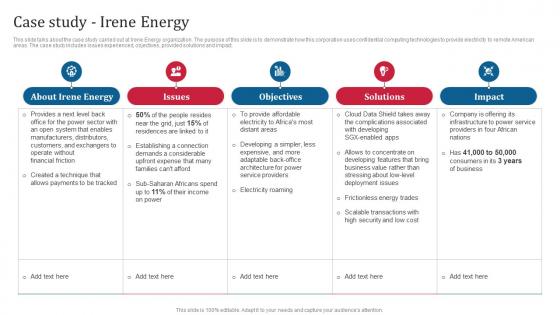 Confidential Computing Consortium Case Study Irene Energy Ppt Icon File Formats
Confidential Computing Consortium Case Study Irene Energy Ppt Icon File FormatsThis slide talks about the case study carried out at Irene Energy organization. The purpose of this slide is to demonstrate how this corporation uses confidential computing technologies to provide electricity to remote American areas. The case study includes issues experienced, objectives, provided solutions and impact. Present the topic in a bit more detail with this Confidential Computing Consortium Case Study Irene Energy Ppt Icon File Formats. Use it as a tool for discussion and navigation on Irene Energy Organization, Demonstrate, Confidential Computing Technologies, Electricity Roaming. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
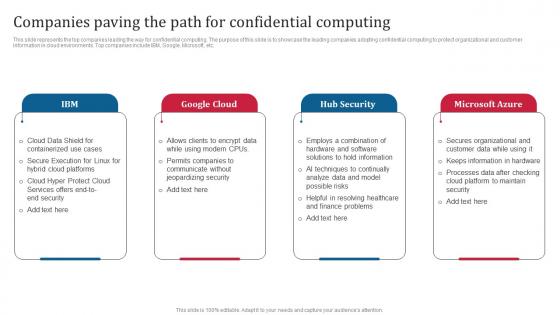 Confidential Computing Consortium Companies Paving The Path For Confidential Computing
Confidential Computing Consortium Companies Paving The Path For Confidential ComputingThis slide represents the top companies leading the way for confidential computing. The purpose of this slide is to showcase the leading companies adopting confidential computing to protect organizational and customer information in cloud environments. Top companies include IBM, Google, Microsoft, etc. Introducing Confidential Computing Consortium Companies Paving The Path For Confidential Computing to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Path For Confidential Computing, Customer Information, Cloud Environments, Protect Organizational, using this template. Grab it now to reap its full benefits.
-
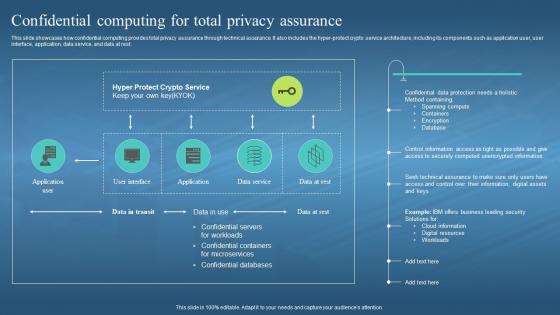 Confidential Computing Hardware Confidential Computing For Total Privacy Assurance
Confidential Computing Hardware Confidential Computing For Total Privacy AssuranceThis slide showcases how confidential computing provides total privacy assurance through technical assurance. It also includes the hyper-protect crypto service architecture, including its components such as application user, user interface, application, data service, and data at rest. Present the topic in a bit more detail with this Confidential Computing Hardware Confidential Computing For Total Privacy Assurance. Use it as a tool for discussion and navigation on Spanning Compute, Containers, Encryption, Cloud Information, Digital Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
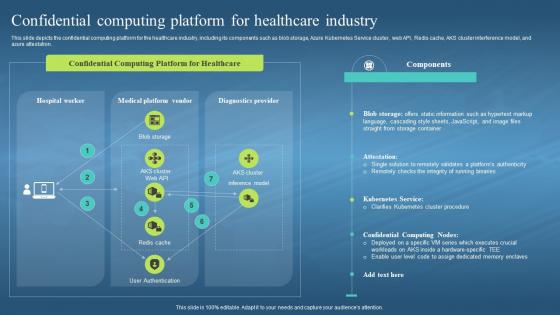 Confidential Computing Hardware Confidential Computing Platform For Healthcare Industry
Confidential Computing Hardware Confidential Computing Platform For Healthcare IndustryThis slide depicts the confidential computing platform for the healthcare industry, including its components such as blob storage, Azure Kubernetes Service cluster, web API, Redis cache, AKS cluster interference model, and azure attestation. Present the topic in a bit more detail with this Confidential Computing Hardware Confidential Computing Platform For Healthcare Industry. Use it as a tool for discussion and navigation on Confidential Computing Platform, Healthcare Industry, Azure Kubernetes Service Cluster, Aks Cluster Interference Model. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
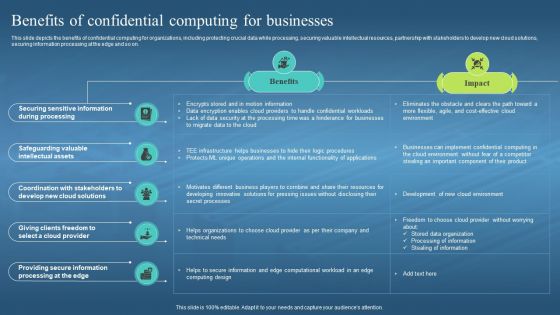 Confidential Computing Hardware Benefits Of Confidential Computing For Businesses
Confidential Computing Hardware Benefits Of Confidential Computing For BusinessesThis slide depicts the benefits of confidential computing for organizations, including protecting crucial data while processing, securing valuable intellectual resources, partnership with stakeholders to develop new cloud solutions, securing information processing at the edge and so on. Deliver an outstanding presentation on the topic using this Confidential Computing Hardware Benefits Of Confidential Computing For Businesses. Dispense information and present a thorough explanation of Confidential Computing For Organizations, Protecting Crucial Data, Securing Valuable Intellectual Resources, New Cloud Solutions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
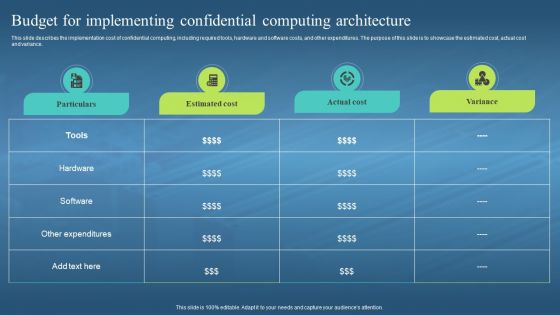 Confidential Computing Hardware Budget For Implementing Confidential Computing
Confidential Computing Hardware Budget For Implementing Confidential ComputingThis slide describes the implementation cost of confidential computing, including required tools, hardware and software costs, and other expenditures. The purpose of this slide is to showcase the estimated cost, actual cost and variance. Present the topic in a bit more detail with this Confidential Computing Hardware Budget For Implementing Confidential Computing. Use it as a tool for discussion and navigation on Cost Of Confidential Computing, Hardware And Software Costs, Estimated Cost, Actual Cost And Variance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing Hardware Companies Paving The Path For Confidential Computing
Confidential Computing Hardware Companies Paving The Path For Confidential ComputingThis slide represents the top companies leading the way for confidential computing. The purpose of this slide is to showcase the leading companies adopting confidential computing to protect organizational and customer information in cloud environments. Top companies include IBM, Google, Microsoft, etc. Introducing Confidential Computing Hardware Companies Paving The Path For Confidential Computing to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Confidential Computing, Cloud Environments, Cloud Platform, Hardware And Software Solutions, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing Hardware For Table Of Contents Ppt Icon Designs Download
Confidential Computing Hardware For Table Of Contents Ppt Icon Designs DownloadPresent the topic in a bit more detail with this Confidential Computing Hardware For Table Of Contents Ppt Icon Designs Download. Use it as a tool for discussion and navigation on Confidential Computing Market, Technology Segment Market Growth, Scenario Case Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing Hardware In And Out Scope Threat Vectors For Confidential Computing
Confidential Computing Hardware In And Out Scope Threat Vectors For Confidential ComputingThis slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Increase audience engagement and knowledge by dispensing information using Confidential Computing Hardware In And Out Scope Threat Vectors For Confidential Computing. This template helps you present information on four stages. You can also present information on Software Attacks, Protocol Attacks, Cryptographic Attacks, Physical Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
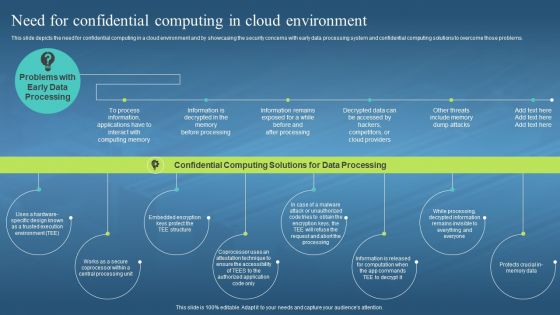 Confidential Computing Hardware Need For Confidential Computing In Cloud Environment
Confidential Computing Hardware Need For Confidential Computing In Cloud EnvironmentThis slide depicts the need for confidential computing in a cloud environment and by showcasing the security concerns with early data processing system and confidential computing solutions to overcome those problems. Increase audience engagement and knowledge by dispensing information using Confidential Computing Hardware Need For Confidential Computing In Cloud Environment. This template helps you present information on six stages. You can also present information on Computing Memory, Competitors Or Cloud Providers, Memory Dump Attacks, Cloud Environment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
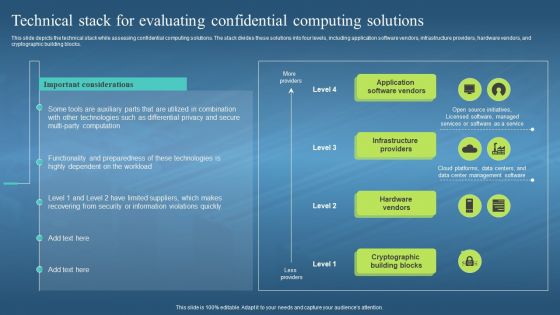 Confidential Computing Hardware Technical Stack For Evaluating Confidential Computing
Confidential Computing Hardware Technical Stack For Evaluating Confidential ComputingThis slide depicts the technical stack while assessing confidential computing solutions. The stack divides these solutions into four levels, including application software vendors, infrastructure providers, hardware vendors, and cryptographic building blocks. Deliver an outstanding presentation on the topic using this Confidential Computing Hardware Technical Stack For Evaluating Confidential Computing. Dispense information and present a thorough explanation of Application Software Vendors, Infrastructure Providers, Hardware Vendors, Cryptographic Building Blocks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icons Slide For Confidential Computing Hardware Ppt Icon Example Introduction
Icons Slide For Confidential Computing Hardware Ppt Icon Example IntroductionIntroducing our well researched set of slides titled Icons Slide For Confidential Computing Hardware Ppt Icon Example Introduction. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Agenda For Confidential Computing Market
Agenda For Confidential Computing MarketIntroducing Agenda For Confidential Computing Market to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confidential, Architecture, Computing Environment, using this template. Grab it now to reap its full benefits.
-
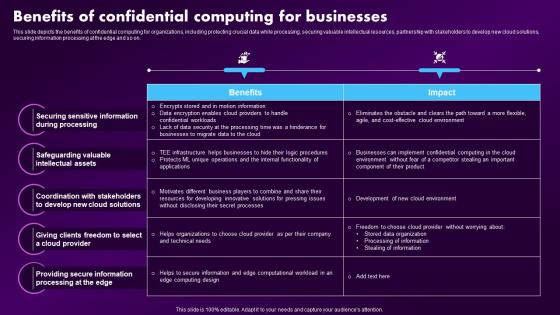 Confidential Computing Market Benefits Of Confidential Computing For Businesses
Confidential Computing Market Benefits Of Confidential Computing For BusinessesThis slide depicts the benefits of confidential computing for organizations, including protecting crucial data while processing, securing valuable intellectual resources, partnership with stakeholders to develop new cloud solutions, securing information processing at the edge and so on. Present the topic in a bit more detail with this Confidential Computing Market Benefits Of Confidential Computing For Businesses. Use it as a tool for discussion and navigation on Businesses, Solutions, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
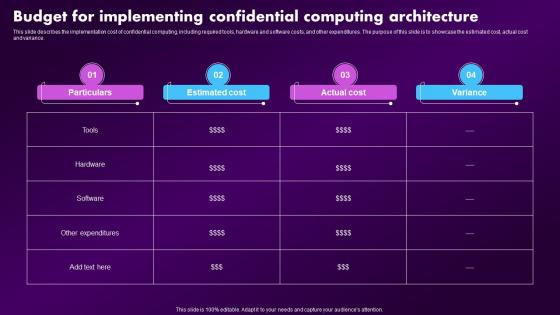 Confidential Computing Market Budget For Implementing Confidential Computing Architecture
Confidential Computing Market Budget For Implementing Confidential Computing ArchitectureThis slide describes the implementation cost of confidential computing, including required tools, hardware and software costs, and other expenditures. The purpose of this slide is to showcase the estimated cost, actual cost and variance. Deliver an outstanding presentation on the topic using this Confidential Computing Market Budget For Implementing Confidential Computing Architecture. Dispense information and present a thorough explanation of Implementing, Confidential, Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
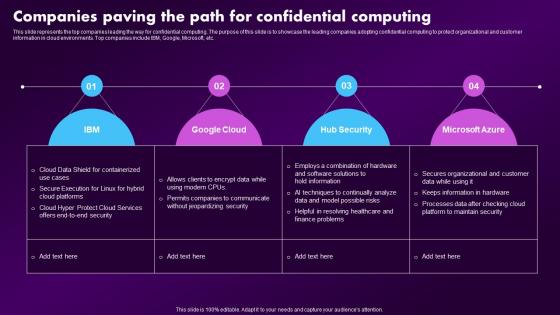 Confidential Computing Market Companies Paving The Path For Confidential Computing
Confidential Computing Market Companies Paving The Path For Confidential ComputingThis slide represents the top companies leading the way for confidential computing. The purpose of this slide is to showcase the leading companies adopting confidential computing to protect organizational and customer information in cloud environments. Top companies include IBM, Google, Microsoft, etc. Introducing Confidential Computing Market Companies Paving The Path For Confidential Computing to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Hub Security, Microsoft Azure, Google Cloud, using this template. Grab it now to reap its full benefits.
-
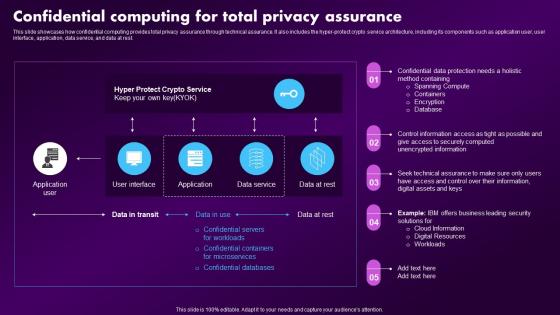 Confidential Computing Market Confidential Computing For Total Privacy Assurance
Confidential Computing Market Confidential Computing For Total Privacy AssuranceThis slide showcases how confidential computing provides total privacy assurance through technical assurance. It also includes the hyper-protect crypto service architecture, including its components such as application user, user interface, application, data service, and data at rest. Present the topic in a bit more detail with this Confidential Computing Market Confidential Computing For Total Privacy Assurance. Use it as a tool for discussion and navigation on Confidential, Servers, Microservices. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
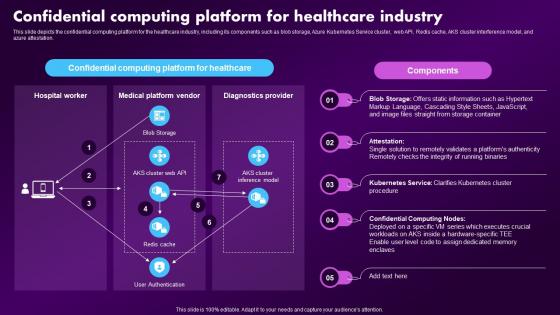 Confidential Computing Market Confidential Computing Platform For Healthcare Industry
Confidential Computing Market Confidential Computing Platform For Healthcare IndustryThis slide depicts the confidential computing platform for the healthcare industry, including its components such as blob storage, Azure Kubernetes Service cluster, web API, Redis cache, AKS cluster interference model, and azure attestation. Deliver an outstanding presentation on the topic using this Confidential Computing Market Confidential Computing Platform For Healthcare Industry. Dispense information and present a thorough explanation of Authenticity, Confidential, Computing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
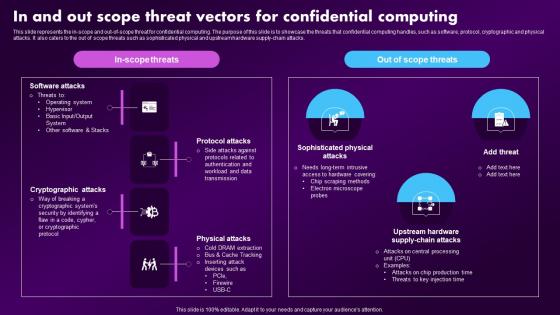 Confidential Computing Market In And Out Scope Threat Vectors For Confidential Computing
Confidential Computing Market In And Out Scope Threat Vectors For Confidential ComputingThis slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Deliver an outstanding presentation on the topic using this Confidential Computing Market In And Out Scope Threat Vectors For Confidential Computing. Dispense information and present a thorough explanation of Confidential, Computing, Production using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
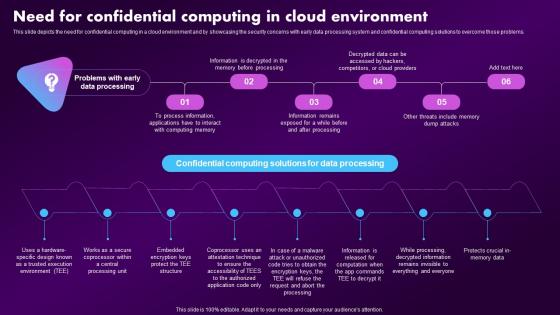 Confidential Computing Market Need For Confidential Computing In Cloud Environment
Confidential Computing Market Need For Confidential Computing In Cloud EnvironmentThis slide depicts the need for confidential computing in a cloud environment and by showcasing the security concerns with early data processing system and confidential computing solutions to overcome those problems. Present the topic in a bit more detail with this Confidential Computing Market Need For Confidential Computing In Cloud Environment. Use it as a tool for discussion and navigation on Confidential, Computing, Environment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
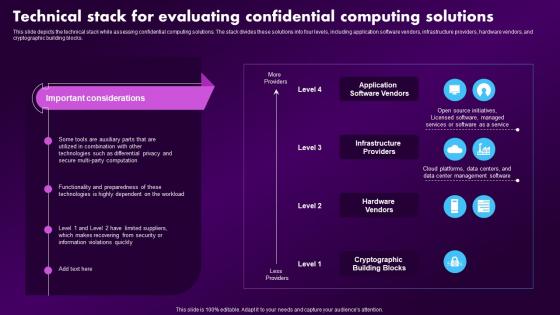 Confidential Computing Market Technical Stack For Evaluating Confidential Computing Solutions
Confidential Computing Market Technical Stack For Evaluating Confidential Computing SolutionsThis slide depicts the technical stack while assessing confidential computing solutions. The stack divides these solutions into four levels, including application software vendors, infrastructure providers, hardware vendors, and cryptographic building blocks. Deliver an outstanding presentation on the topic using this Confidential Computing Market Technical Stack For Evaluating Confidential Computing Solutions. Dispense information and present a thorough explanation of Evaluating, Solutions, Technical using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 F1606 Table Of Contents For Confidential Computing Market
F1606 Table Of Contents For Confidential Computing MarketIntroducing F1606 Table Of Contents For Confidential Computing Market to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Architecture, Approaches, Confidential Computing, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Confidential Computing Market
Icons Slide For Confidential Computing MarketPresent the topic in a bit more detail with this Icons Slide For Confidential Computing Market. Use it as a tool for discussion and navigation on Icons. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing Consortium For Table Of Contents Ppt Icon Graphics Pictures
Confidential Computing Consortium For Table Of Contents Ppt Icon Graphics PicturesIntroducing Confidential Computing Consortium For Table Of Contents Ppt Icon Graphics Pictures to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Confidential Computing Technologies, Trust Boundary, Architecture And Realms Working, using this template. Grab it now to reap its full benefits.
-
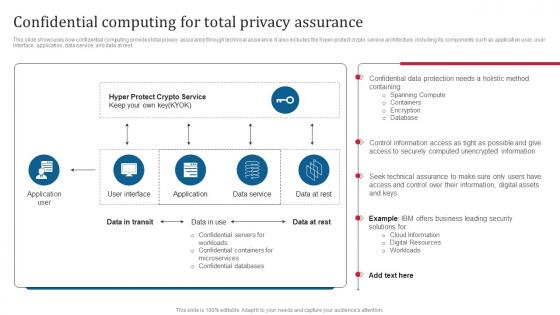 Confidential Computing Consortium Confidential Computing For Total Privacy Assurance
Confidential Computing Consortium Confidential Computing For Total Privacy AssuranceThis slide showcases how confidential computing provides total privacy assurance through technical assurance. It also includes the hyper-protect crypto service architecture, including its components such as application user, user interface, application, data service, and data at rest. Deliver an outstanding presentation on the topic using this Confidential Computing Consortium Confidential Computing For Total Privacy Assurance. Dispense information and present a thorough explanation of Cloud Information, Digital Resources, Spanning Compute, Hyper Protect Crypto Service using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
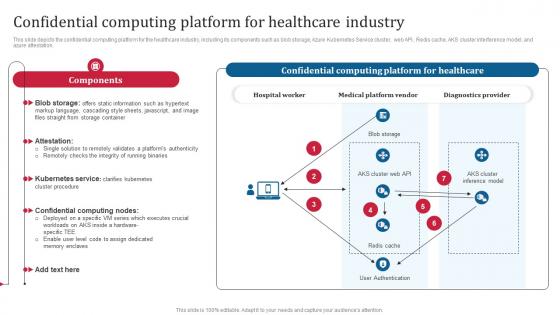 Confidential Computing Consortium Confidential Computing Platform For Healthcare Industry
Confidential Computing Consortium Confidential Computing Platform For Healthcare IndustryThis slide depicts the confidential computing platform for the healthcare industry, including its components such as blob storage, Azure Kubernetes Service cluster, web API, Redis cache, AKS cluster interference model. Deliver an outstanding presentation on the topic using this Confidential Computing Consortium Confidential Computing Platform For Healthcare Industry. Dispense information and present a thorough explanation of Hospital Worker, Medical Platform Vendor, Diagnostics Provider, Confidential Computing Nodes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icons Slide For Confidential Computing Consortium Ppt Ideas Infographic Template
Icons Slide For Confidential Computing Consortium Ppt Ideas Infographic TemplatePresenting our well crafted Icons Slide For Confidential Computing Consortium Ppt Ideas Infographic Template set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
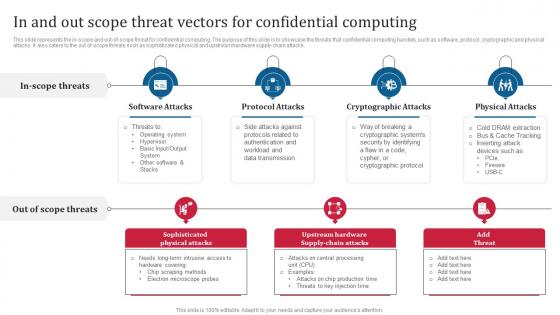 Confidential Computing Consortium In And Out Scope Threat Vectors For Confidential Computing
Confidential Computing Consortium In And Out Scope Threat Vectors For Confidential ComputingThis slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Introducing Confidential Computing Consortium In And Out Scope Threat Vectors For Confidential Computingm to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Sophisticated Physical Attacks, Cryptographic Attacks, Protocol Attacks, Physical Attacks, using this template. Grab it now to reap its full benefits.
-
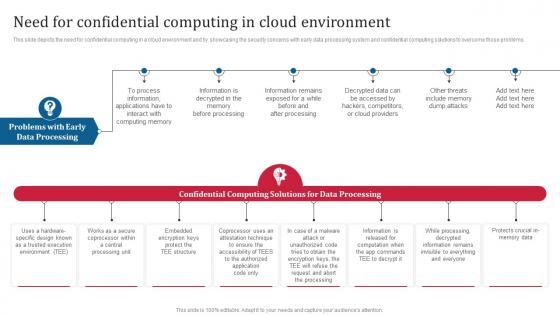 Confidential Computing Consortium Need For Confidential Computing In Cloud Environment
Confidential Computing Consortium Need For Confidential Computing In Cloud EnvironmentThis slide depicts the need for confidential computing in a cloud environment and by showcasing the security concerns with early data processing system and confidential computing solutions to overcome those problems. Increase audience engagement and knowledge by dispensing information using Confidential Computing Consortium Need For Confidential Computing In Cloud Environment. This template helps you present information on five stages. You can also present information on Confidential Computing, Cloud Environment, Overcome Those Problems, Data Processing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
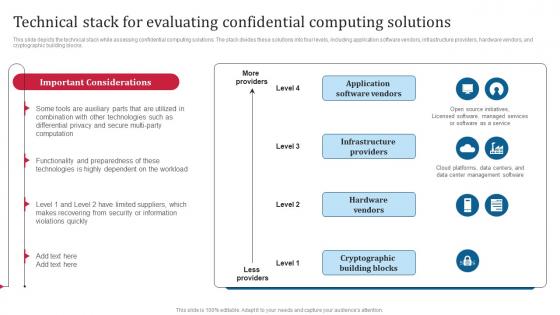 Confidential Computing Consortium Technical Stack For Evaluating Confidential Computing Solutions
Confidential Computing Consortium Technical Stack For Evaluating Confidential Computing SolutionsThis slide depicts the technical stack while assessing confidential computing solutions. The stack divides these solutions into four levels, including application software vendors, infrastructure providers, hardware vendors, and cryptographic building blocks. Present the topic in a bit more detail with this Confidential Computing Consortium Technical Stack For Evaluating Confidential Computing Solutions. Use it as a tool for discussion and navigation on Application Software Vendors, Infrastructure Providers, Hardware Vendors, Cryptographic Building Blocks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
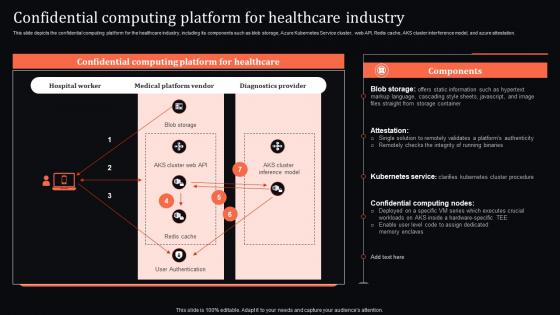 Confidential Computing System Technology Platform For Healthcare Industry
Confidential Computing System Technology Platform For Healthcare IndustryThis slide depicts the confidential computing platform for the healthcare industry, including its components such as blob storage, Azure Kubernetes Service cluster, web API, Redis cache, AKS cluster interference model, and azure attestation. Present the topic in a bit more detail with this Confidential Computing System Technology Platform For Healthcare Industry. Use it as a tool for discussion and navigation on Confidential, Healthcare Industry, Components. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Agenda For Confidential Computing Ppt Inspiration Sample
Confidential Computing V2 Agenda For Confidential Computing Ppt Inspiration SampleIntroducing Confidential Computing V2 Agenda For Confidential Computing Ppt Inspiration Sample to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confidential Computing, Consortium, Architecture, Confidential Computing Environment, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 Benefits Of Confidential Computing For Businesses
Confidential Computing V2 Benefits Of Confidential Computing For BusinessesThis slide depicts the benefits of confidential computing for organizations, including protecting crucial data while processing, securing valuable intellectual resources, partnership with stakeholders to develop new cloud solutions, securing information processing at the edge and so on. Present the topic in a bit more detail with this Confidential Computing V2 Benefits Of Confidential Computing For Businesses. Use it as a tool for discussion and navigation on Confidential Computing For Organizations, Protecting Crucial Data, Securing Valuable Intellectual Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
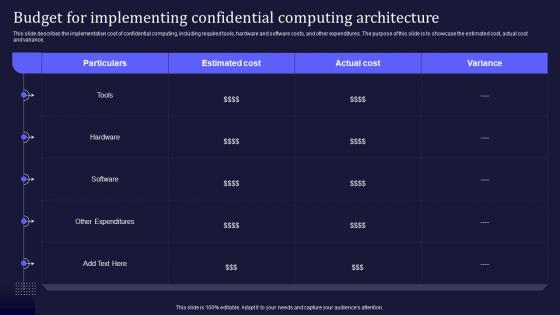 Confidential Computing V2 Budget For Implementing Confidential Computing Architecture
Confidential Computing V2 Budget For Implementing Confidential Computing ArchitectureThis slide describes the implementation cost of confidential computing, including required tools, hardware and software costs, and other expenditures. The purpose of this slide is to showcase the estimated cost, actual cost and variance. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Budget For Implementing Confidential Computing Architecture. Dispense information and present a thorough explanation of Confidential Computing Architecture, Cost Of Confidential Computing, Hardware And Software Costs using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
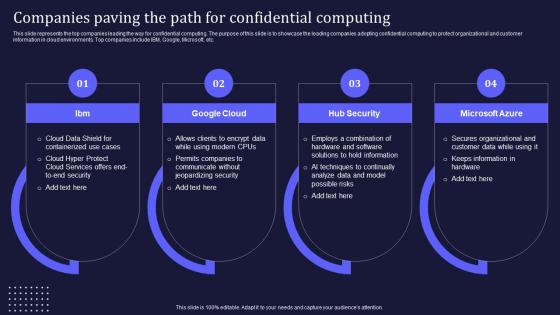 Confidential Computing V2 Companies Paving The Path For Confidential Computing
Confidential Computing V2 Companies Paving The Path For Confidential ComputingThis slide represents the top companies leading the way for confidential computing. The purpose of this slide is to showcase the leading companies adopting confidential computing to protect organizational and customer information in cloud environments. Top companies include IBM, Google, Microsoft, etc. Introducing Confidential Computing V2 Companies Paving The Path For Confidential Computing to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Hub Security, Microsoft Azure, Confidential Computing, Companies Paving The Path, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 For Table Of Contents Ppt Infographics Graphics Download
Confidential Computing V2 For Table Of Contents Ppt Infographics Graphics DownloadIntroducing Confidential Computing V2 For Table Of Contents Ppt Infographics Graphics Download to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Architecture And Realms Working, Trust Boundary Across Azure, Primary Approaches, Technologies Overview, using this template. Grab it now to reap its full benefits.
-
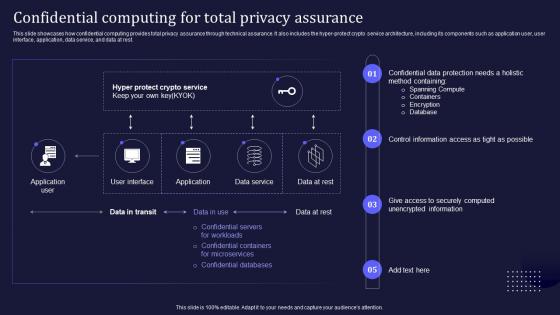 Confidential Computing V2 For Total Privacy Assurance Ppt Infographics Show
Confidential Computing V2 For Total Privacy Assurance Ppt Infographics ShowThis slide showcases how confidential computing provides total privacy assurance through technical assurance. It also includes the hyper-protect crypto service architecture, including its components such as application user, user interface, application, data service, and data at rest. Present the topic in a bit more detail with this Confidential Computing V2 For Total Privacy Assurance Ppt Infographics Show. Use it as a tool for discussion and navigation on Confidential Servers For Workloads, Confidential Containers For Microservices, Confidential Databases. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons Slide For Confidential Computing V2 Ppt infographic template professional
Icons Slide For Confidential Computing V2 Ppt infographic template professionalIntroducing our well researched set of slides titled Icons Slide For Confidential Computing V2 Ppt infographic template professional. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
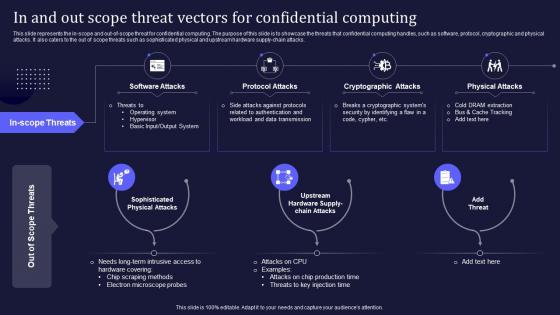 Confidential Computing V2 In And Out Scope Threat Vectors For Confidential Computing
Confidential Computing V2 In And Out Scope Threat Vectors For Confidential ComputingThis slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Introducing Confidential Computing V2 In And Out Scope Threat Vectors For Confidential Computing to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Software Attacks, Sophisticated Physical Attacks, Protocol Attacks, Cryptographic Attacks, Physical Attacks, using this template. Grab it now to reap its full benefits.
-
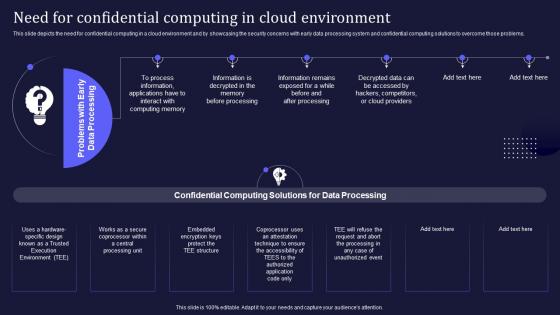 Confidential Computing V2 Need For Confidential Computing In Cloud Environment
Confidential Computing V2 Need For Confidential Computing In Cloud EnvironmentThis slide depicts the need for confidential computing in a cloud environment and by showcasing the security concerns with early data processing system and confidential computing solutions to overcome those problems. Introducing Confidential Computing V2 Need For Confidential Computing In Cloud Environment to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Environment, Data Processing System, Confidential Computing Solutions, Early Data Processing, using this template. Grab it now to reap its full benefits.
-
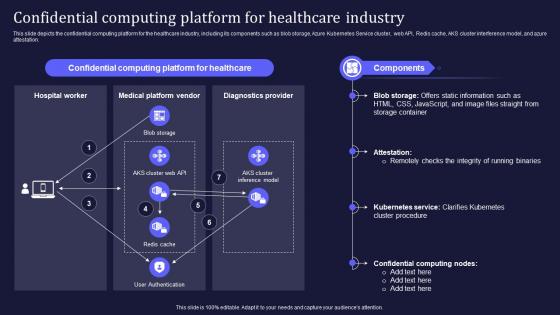 Confidential Computing V2 Platform For Healthcare Industry Ppt Infographics Grid
Confidential Computing V2 Platform For Healthcare Industry Ppt Infographics GridThis slide depicts the confidential computing platform for the healthcare industry, including its components such as blob storage, Azure Kubernetes Service cluster, web API, Redis cache, AKS cluster interference model, and azure attestation. Present the topic in a bit more detail with this Confidential Computing V2 Platform For Healthcare Industry Ppt Infographics Grid. Use it as a tool for discussion and navigation on Kubernetes Service, Integrity Of Running Binaries, Confidential Computing Platform, Healthcare Industry. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
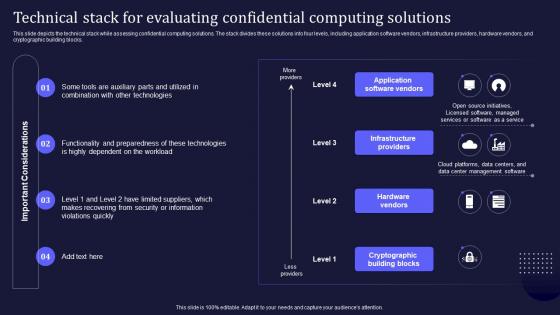 Confidential Computing V2 Technical Stack For Evaluating Confidential Computing Solutions
Confidential Computing V2 Technical Stack For Evaluating Confidential Computing SolutionsThis slide depicts the technical stack while assessing confidential computing solutions. The stack divides these solutions into four levels, including application software vendors, infrastructure providers, hardware vendors, and cryptographic building blocks. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Technical Stack For Evaluating Confidential Computing Solutions. Dispense information and present a thorough explanation of Application Software Vendors, Infrastructure Providers, Hardware Vendors, Cryptographic Building Blocks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
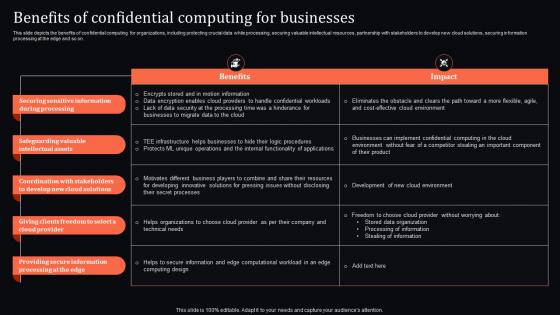 Confidential Computing System Technology Benefits Of Confidential Computing For Businesses
Confidential Computing System Technology Benefits Of Confidential Computing For BusinessesThis slide depicts the benefits of confidential computing for organizations, including protecting crucial data while processing, securing valuable intellectual resources, partnership with stakeholders to develop new cloud solutions, securing information processing at the edge and so on. Present the topic in a bit more detail with this Confidential Computing System Technology Benefits Of Confidential Computing For Businesses. Use it as a tool for discussion and navigation on Stakeholders, Intellectual, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
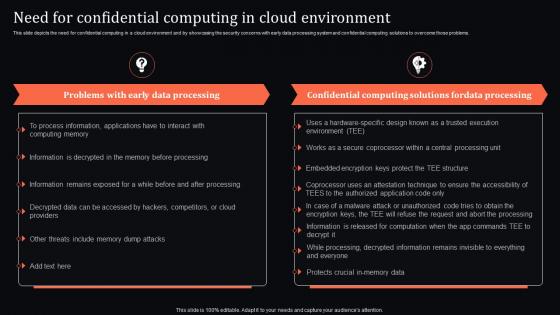 Confidential Computing System Technology Need For Confidential Computing In Cloud Environment
Confidential Computing System Technology Need For Confidential Computing In Cloud EnvironmentThis slide depicts the need for confidential computing in a cloud environment and by showcasing the security concerns with early data processing system and confidential computing solutions to overcome those problems. Deliver an outstanding presentation on the topic using this Confidential Computing System Technology Need For Confidential Computing In Cloud Environment. Dispense information and present a thorough explanation of Confidential, Environment, Solutions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
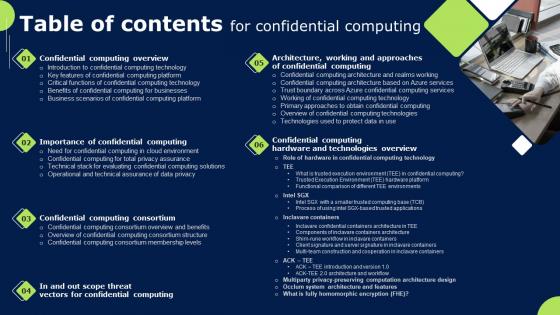 Table Of Contents For Confidential Computing Ppt Show Example Introduction
Table Of Contents For Confidential Computing Ppt Show Example IntroductionIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Confidential Computing Ppt Show Example Introduction. This template helps you present information on six stages. You can also present information on Confidential Computing Overview, Confidential Computing Consortium, Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda For Confidential Computing Ppt Powerpoint Presentation File Files
Agenda For Confidential Computing Ppt Powerpoint Presentation File FilesIntroducing Agenda For Confidential Computing Ppt Powerpoint Presentation File Files to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confidential Computing, Computing Environment, Market Of Confidential Computing, using this template. Grab it now to reap its full benefits.


