Powerpoint Templates and Google slides for Cyber Security Asset Risk Assessment
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber
Checklist For Effectively Managing Asset Security Risk Based Methodology To CyberFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Increase audience engagement and knowledge by dispensing information using Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber This template helps you present information on one stage. You can also present information on System Monitoring, Data Backup, Security Patches using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber Security
Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber SecurityFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost.Deliver an outstanding presentation on the topic using this Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Infrastructure Hardware, Routers And Switches, Server Computers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
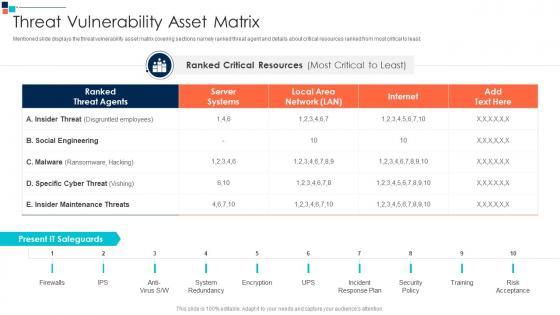 Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security
Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber SecurityMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on System Redundancy, Incident Response Plan, Security Policy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber security risk management addressing asset security categorization
Cyber security risk management addressing asset security categorizationThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Introducing Cyber Security Risk Management Addressing Asset Security Categorization to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Position, Ownership, Location, Security Categorization, Integrity, Confidentiality, Availability, Value , using this template. Grab it now to reap its full benefits.
-
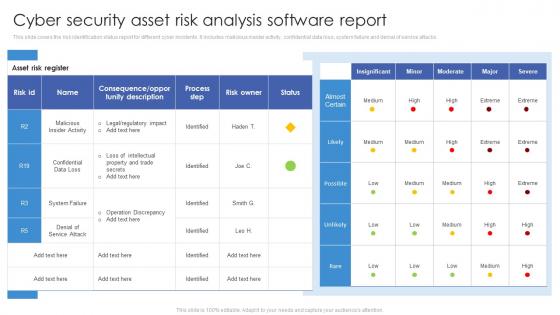 Cyber Security Asset Risk Analysis Software Report
Cyber Security Asset Risk Analysis Software ReportThis slide covers the risk identification status report for different cyber incidents. It includes malicious insider activity, confidential data loss, system failure and denial of service attacks.Presenting our well structured Cyber Security Asset Risk Analysis Software Report. The topics discussed in this slide are Confidential Data, Operation Discrepancy, Process Step. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
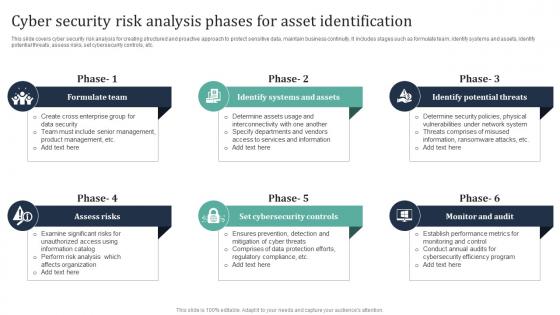 Cyber Security Risk Analysis Phases For Asset Identification
Cyber Security Risk Analysis Phases For Asset IdentificationThis slide covers cyber security risk analysis for creating structured and proactive approach to protect sensitive data, maintain business continuity. It includes stages such as formulate team, identify systems and assets, identify potential threats, assess risks, set cybersecurity controls, etc. Introducing our premium set of slides with Cyber Security Risk Analysis Phases For Asset Identification. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Team, Assess, Cybersecurity. So download instantly and tailor it with your information.

