Powerpoint Templates and Google slides for Data Encryption And Protection
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
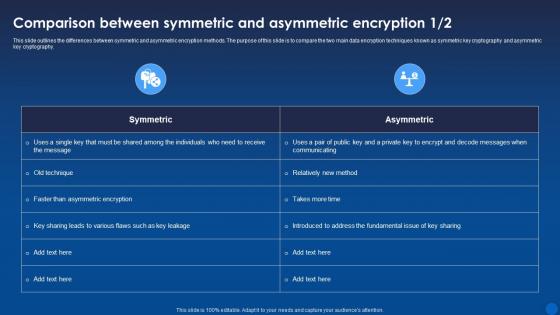 Comparison Symmetric And Asymmetric Encryption Encryption For Data Privacy In Digital Age It
Comparison Symmetric And Asymmetric Encryption Encryption For Data Privacy In Digital Age ItThis slide outlines the differences between symmetric and asymmetric encryption methods. The purpose of this slide is to compare the two main data encryption techniques known as symmetric key cryptography and asymmetric key cryptography. Present the topic in a bit more detail with this Comparison Symmetric And Asymmetric Encryption Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric, Encryption, Comparison. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
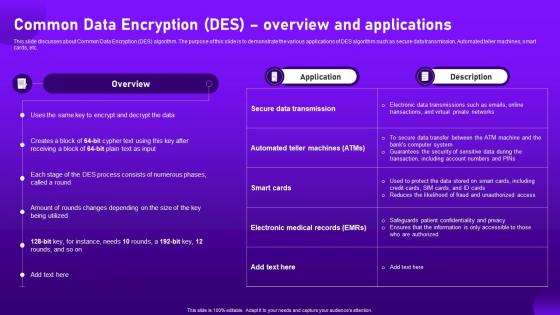 Common Data Encryption Des Overview And Applications Cloud Cryptography
Common Data Encryption Des Overview And Applications Cloud CryptographyThis slide discusses about Common Data Encryption DES algorithm. The purpose of this slide is to demonstrate the various applications of DES algorithm such as secure data transmission, Automated teller machines, smart cards, etc. Deliver an outstanding presentation on the topic using this Common Data Encryption Des Overview And Applications Cloud Cryptography. Dispense information and present a thorough explanation of Overview, Applications, Data Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
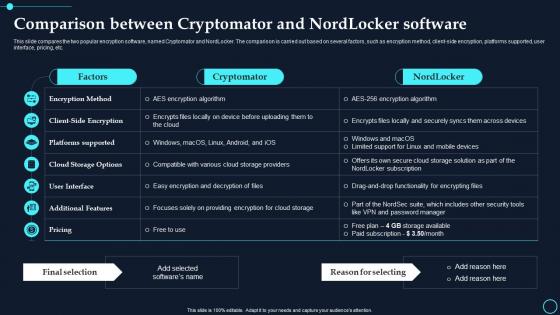 Comparison Between Cryptomator And Nordlocker Software Cloud Data Encryption
Comparison Between Cryptomator And Nordlocker Software Cloud Data EncryptionThis slide compares the two popular encryption software, named Cryptomator and NordLocker. The comparison is carried out based on several factors, such as encryption method, client side encryption, platforms supported, user interface, pricing, etc. Present the topic in a bit more detail with this Comparison Between Cryptomator And Nordlocker Software Cloud Data Encryption. Use it as a tool for discussion and navigation on Cryptomator, Nordlocker. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
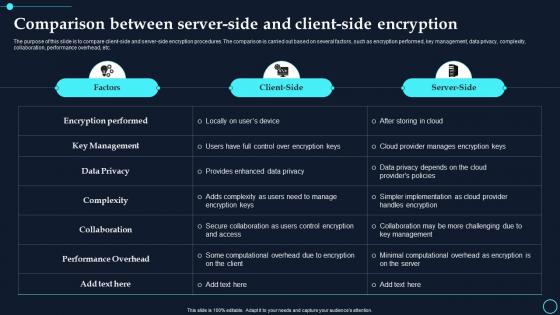 Comparison Between Server-Side And Client Side Encryption Cloud Data Encryption
Comparison Between Server-Side And Client Side Encryption Cloud Data EncryptionThe purpose of this slide is to compare client side and server side encryption procedures. The comparison is carried out based on several factors, such as encryption performed, key management, data privacy, complexity, collaboration, performance overhead, etc. Deliver an outstanding presentation on the topic using this Comparison Between Server Side And Client Side Encryption Cloud Data Encryption. Dispense information and present a thorough explanation of Encryption Performed, Key Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Major Risks And Mitigation Strategies For Cloud Encryption Implementation Cloud Data Encryption
Major Risks And Mitigation Strategies For Cloud Encryption Implementation Cloud Data EncryptionThe purpose of this slide is to discuss the challenges faced while encrypting cloud data. The critical components of this slide are the description of the risk, probability of occurrence, impact on system infrastructure, and possible mitigation strategies. Deliver an outstanding presentation on the topic using this Major Risks And Mitigation Strategies For Cloud Encryption Implementation Cloud Data Encryption. Dispense information and present a thorough explanation of Probability, Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
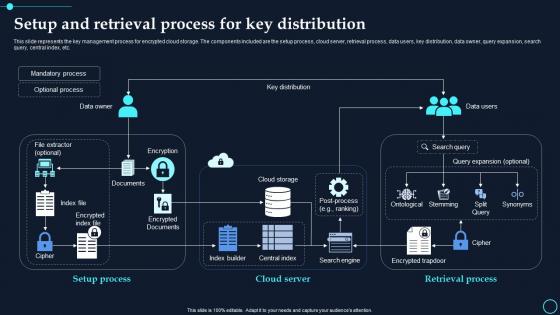 Setup And Retrieval Process For Key Distribution Cloud Data Encryption
Setup And Retrieval Process For Key Distribution Cloud Data EncryptionThis slide represents the key management process for encrypted cloud storage. The components included are the setup process, cloud server, retrieval process, data users, key distribution, data owner, query expansion, search query, central index, etc. Present the topic in a bit more detail with this Setup And Retrieval Process For Key Distribution Cloud Data Encryption. Use it as a tool for discussion and navigation on Mandatory Process, Optional Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Security Encryption Technology Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Security Encryption Technology Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Data Security Encryption Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Security Encryption Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Cryptography Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cryptography Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Cryptography Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cryptography Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Data Encryption Key Management Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Encryption Key Management Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Data Encryption Key Management Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Encryption Key Management Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Digital Signatures Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Signatures Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Digital Signatures Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Signatures Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Encryption Algorithms Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Algorithms Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Encryption Algorithms Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Algorithms Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Identity Management Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Identity Management Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Identity Management Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Identity Management Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
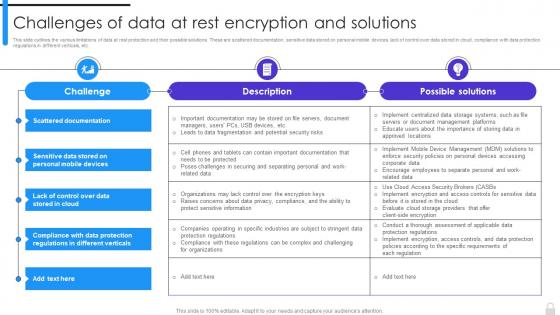 Encryption Implementation Strategies Challenges Of Data At Rest Encryption And Solutions
Encryption Implementation Strategies Challenges Of Data At Rest Encryption And SolutionsThis slide outlines the various limitations of data at rest protection and their possible solutions. These are scattered documentation, sensitive data stored on personal mobile devices, lack of control over data stored in cloud, compliance with data protection regulations in different verticals, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data At Rest Encryption And Solutions. Use it as a tool for discussion and navigation on Data At Rest Protection, Scattered Documentation, Sensitive Data Stored, Personal Mobile Devices, Data Protection Regulations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
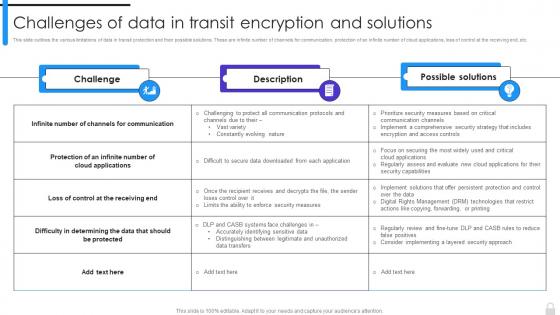 Encryption Implementation Strategies Challenges Of Data In Transit Encryption And Solutions
Encryption Implementation Strategies Challenges Of Data In Transit Encryption And SolutionsThis slide outlines the various limitations of data in transit protection and their possible solutions. These are infinite number of channels for communication, protection of an infinite number of cloud applications, loss of control at the receiving end, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Challenges Of Data In Transit Encryption And Solutions. Dispense information and present a thorough explanation of Data In Transit, Encryption And Solutions, Cloud Applications, Channels For Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
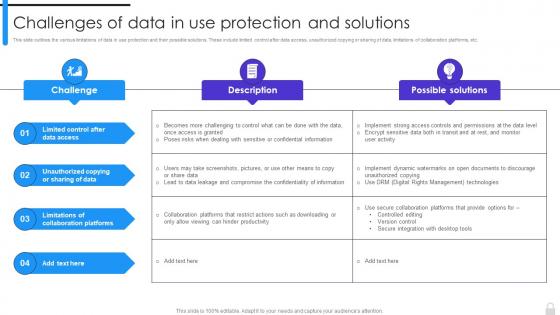 Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions
Encryption Implementation Strategies Challenges Of Data In Use Protection And SolutionsThis slide outlines the various limitations of data in use protection and their possible solutions. These include limited control after data access, unauthorized copying or sharing of data, limitations of collaboration platforms, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions. Use it as a tool for discussion and navigation on Limitations Of Collaboration Platforms, Unauthorized Copying Or Sharing Of Data, Limited Control After Data Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Encryption Secure Computer Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Encryption Secure Computer Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is a visual representation of secure computer. It is a modern, vibrant and eye catching icon that will help to create an impactful presentation. It is a great way to emphasize the importance of data security and safety.
-
 Data Encryption Secure Computer Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Encryption Secure Computer Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for presentations on secure computer systems. It features a black and white design depicting a computer with a padlock, symbolizing the safety of your data. Use this icon to emphasize the importance of secure computing.
-
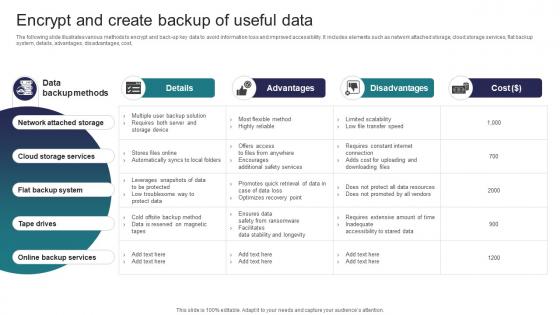 Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats
Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates various methods to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
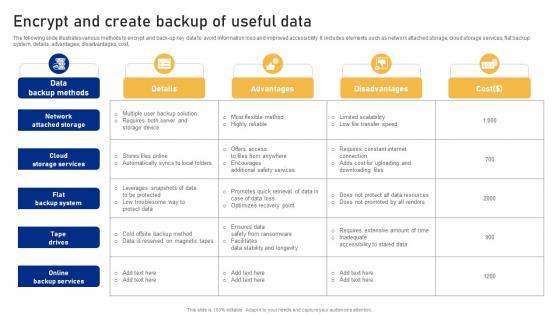 Encrypt And Create Backup Of Useful Data Cyber Risk Assessment
Encrypt And Create Backup Of Useful Data Cyber Risk AssessmentThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Cyber Risk Assessment Dispense information and present a thorough explanation of Network Attached, Backup System, Backup Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 About Bring Your Own Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It
About Bring Your Own Encryption Overview And Benefits Encryption For Data Privacy In Digital Age ItThis slide discusses about widely used encryption method known as Bring Your Own Encryption BYOE. The purpose of this slide is to elaborate the meaning of BYOE. This slide also outlines the benefits of Bring Your Own Keys BYOK method. Present the topic in a bit more detail with this About Bring Your Own Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Overview, Encryption, Technique. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 About Cloud Encryption Tools And Services Encryption For Data Privacy In Digital Age It
About Cloud Encryption Tools And Services Encryption For Data Privacy In Digital Age ItThis slide talks about the cloud encryption methodologies. The purpose of this slide is to outline the encryption tools used in cloud cryptography. It also describes services provided by popular cloud encryption tools such as data encryption, key management, etc. Deliver an outstanding presentation on the topic using this About Cloud Encryption Tools And Services Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Encryption, Services, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
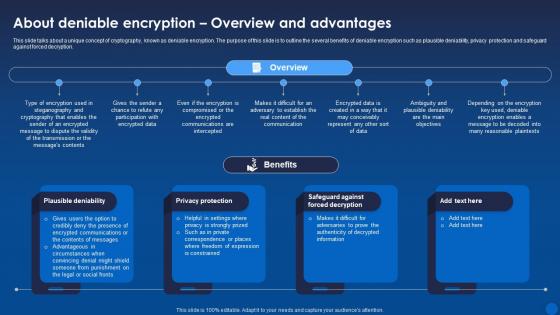 About Deniable Encryption Overview And Advantages Encryption For Data Privacy In Digital Age It
About Deniable Encryption Overview And Advantages Encryption For Data Privacy In Digital Age ItThis slide talks about a unique concept of cryptography, known as deniable encryption. The purpose of this slide is to outline the several benefits of deniable encryption such as plausible deniability, privacy protection and safeguard against forced decryption. Present the topic in a bit more detail with this About Deniable Encryption Overview And Advantages Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Overview, Decryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
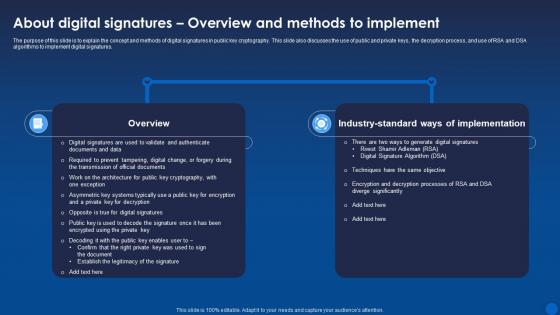 About Digital Signatures Overview And Methods Encryption For Data Privacy In Digital Age It
About Digital Signatures Overview And Methods Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the concept and methods of digital signatures in public key cryptography. This slide also discusses the use of public and private keys, the decryption process, and use of RSA and DSA algorithms to implement digital signatures. Deliver an outstanding presentation on the topic using this About Digital Signatures Overview And Methods Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Implementation, Overview, Significantly using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
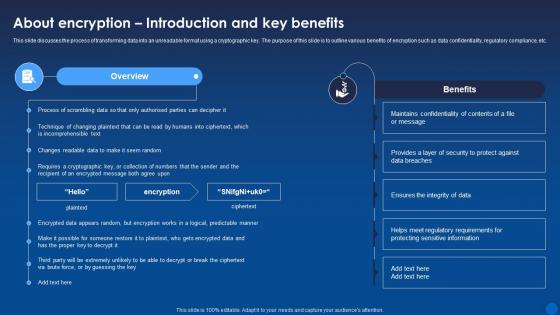 About Encryption Introduction And Key Benefits Encryption For Data Privacy In Digital Age It
About Encryption Introduction And Key Benefits Encryption For Data Privacy In Digital Age ItThis slide discusses the process of transforming data into an unreadable format using a cryptographic key. The purpose of this slide is to outline various benefits of encryption such as data confidentiality, regulatory compliance, etc. Present the topic in a bit more detail with this About Encryption Introduction And Key Benefits Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Introduction, Sensitive, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
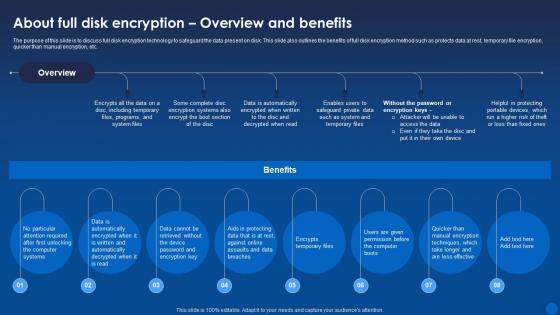 About Full Disk Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It
About Full Disk Encryption Overview And Benefits Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss full disk encryption technology to safeguard the data present on disk. This slide also outlines the benefits of full disk encryption method such as protects data at rest, temporary file encryption, quicker than manual encryption, etc. Deliver an outstanding presentation on the topic using this About Full Disk Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Encryption, Overview, Automatically using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 About Homomorphic Encryption Overview And Types Encryption For Data Privacy In Digital Age It
About Homomorphic Encryption Overview And Types Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the concept of homomorphic encryption. The benefits of this technique are privacy preservation, data security, secure outsourcing, trust in untrusted environments, enhanced data exchange, etc. Present the topic in a bit more detail with this About Homomorphic Encryption Overview And Types Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Homomorphic, Encryption, Overview. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It
About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the role and functionality of IPsec Internet Protocol Security in securing connections between devices. This slide also outlines the uses of IPsec such as protecting data during transmission over open networks, use in building VPNs, etc. Deliver an outstanding presentation on the topic using this About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Overview, Protocol Security, Destination using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
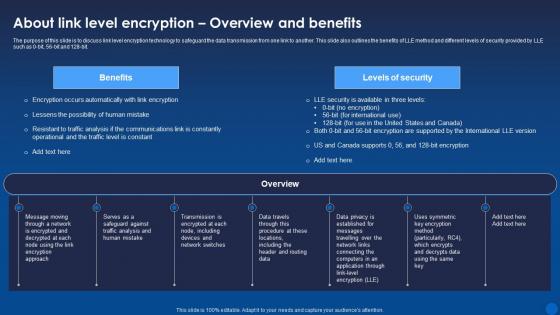 About Link Level Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It
About Link Level Encryption Overview And Benefits Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss link level encryption technology to safeguard the data transmission from one link to another. This slide also outlines the benefits of LLE method and different levels of security provided by LLE such as 0-bit, 56-bit and 128-bit. Present the topic in a bit more detail with this About Link Level Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Overview, Application. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 About Quantum Cryptography Overview And Properties Encryption For Data Privacy In Digital Age It
About Quantum Cryptography Overview And Properties Encryption For Data Privacy In Digital Age ItThis slide discusses the emerging cryptographic technology known as quantum encryption. The purpose of this slide is to discuss the meaning of quantum cryptography. This slide also outlines the properties such as Quantum-safe cryptography and Quantum key distribution. Deliver an outstanding presentation on the topic using this About Quantum Cryptography Overview And Properties Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Quantum, Cryptography, Properties using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
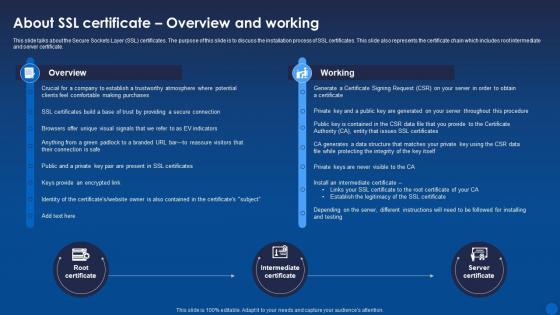 About Ssl Certificate Overview And Working Encryption For Data Privacy In Digital Age It
About Ssl Certificate Overview And Working Encryption For Data Privacy In Digital Age ItThis slide talks about the Secure Sockets Layer SSL certificates. The purpose of this slide is to discuss the installation process of SSL certificates. This slide also represents the certificate chain which includes root intermediate and server certificate. Present the topic in a bit more detail with this About Ssl Certificate Overview And Working Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Certificate, Overview, Intermediate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
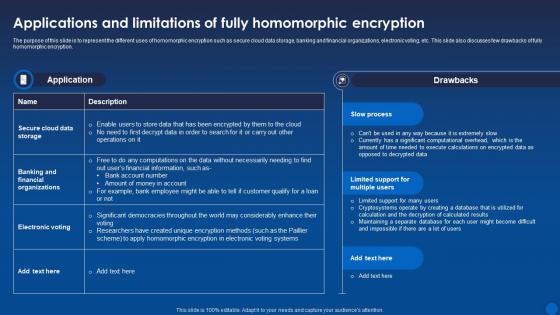 Applications And Limitations Of Fully Homomorphic Encryption For Data Privacy In Digital Age It
Applications And Limitations Of Fully Homomorphic Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to represent the different uses of homomorphic encryption such as secure cloud data storage, banking and financial organizations, electronic voting, etc. This slide also discusses few drawbacks of fully homomorphic encryption. Deliver an outstanding presentation on the topic using this Applications And Limitations Of Fully Homomorphic Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Homomorphic, Encryption, Applications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
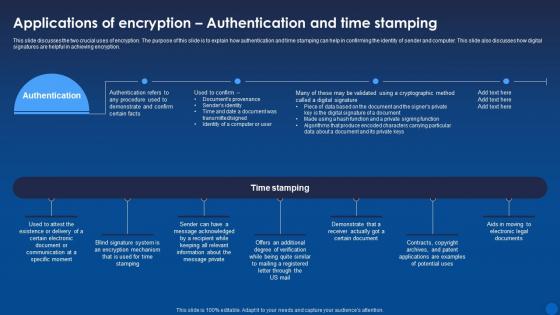 Applications Of Authentication And Time Stamping Encryption For Data Privacy In Digital Age It
Applications Of Authentication And Time Stamping Encryption For Data Privacy In Digital Age ItThis slide discusses the two crucial uses of encryption. The purpose of this slide is to explain how authentication and time stamping can help in confirming the identity of sender and computer. This slide also discusses how digital signatures are helpful in achieving encryption. Present the topic in a bit more detail with this Applications Of Authentication And Time Stamping Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Authentication, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
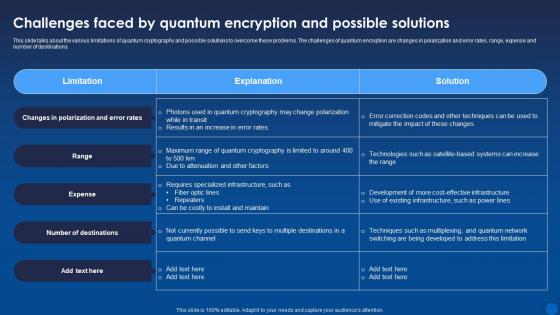 Challenges Faced By Quantum Encryption And Possible Encryption For Data Privacy In Digital Age It
Challenges Faced By Quantum Encryption And Possible Encryption For Data Privacy In Digital Age ItThis slide talks about the various limitations of quantum cryptography and possible solutions to overcome these problems. The challenges of quantum encryption are changes in polarization and error rates, range, expense and number of destinations. Present the topic in a bit more detail with this Challenges Faced By Quantum Encryption And Possible Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Solutions, Destinations, Cryptography. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
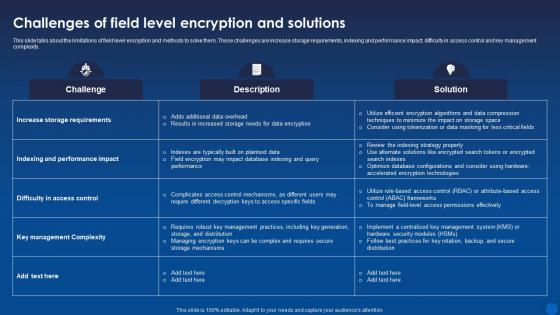 Challenges Of Field Level Encryption And Solutions Encryption For Data Privacy In Digital Age It
Challenges Of Field Level Encryption And Solutions Encryption For Data Privacy In Digital Age ItThis slide talks about the limitations of field level encryption and methods to solve them. These challenges are increase storage requirements, indexing and performance impact, difficulty in access control and key management complexity. Deliver an outstanding presentation on the topic using this Challenges Of Field Level Encryption And Solutions Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Description, Solution, Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
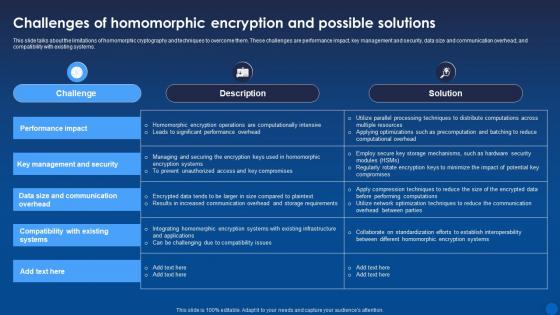 Challenges Of Homomorphic Encryption And Possible Encryption For Data Privacy In Digital Age It
Challenges Of Homomorphic Encryption And Possible Encryption For Data Privacy In Digital Age ItThis slide talks about the limitations of homomorphic cryptography and techniques to overcome them. These challenges are performance impact, key management and security, data size and communication overhead, and compatibility with existing systems. Present the topic in a bit more detail with this Challenges Of Homomorphic Encryption And Possible Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Key Management And Security, Performance Impact, Compatibility With Existing Systems. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
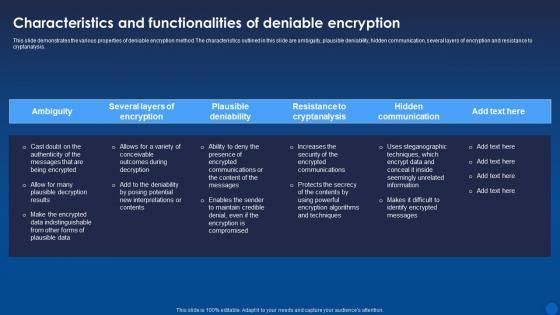 Characteristics And Functionalities Of Deniable Encryption Encryption For Data Privacy In Digital Age It
Characteristics And Functionalities Of Deniable Encryption Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various properties of deniable encryption method. The characteristics outlined in this slide are ambiguity, plausible deniability, hidden communication, several layers of encryption and resistance to cryptanalysis. Deliver an outstanding presentation on the topic using this Characteristics And Functionalities Of Deniable Encryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Ambiguity, Plausible Deniability, Hidden Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
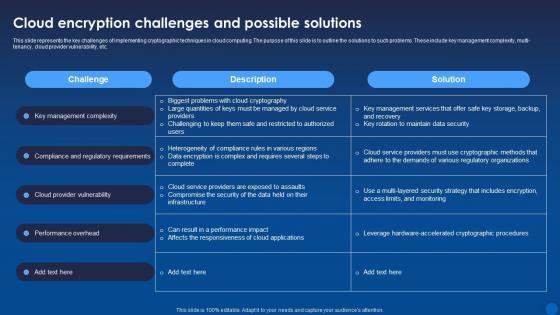 Cloud Encryption Challenges And Possible Solutions Encryption For Data Privacy In Digital Age It
Cloud Encryption Challenges And Possible Solutions Encryption For Data Privacy In Digital Age ItThis slide represents the key challenges of implementing cryptographic techniques in cloud computing. The purpose of this slide is to outline the solutions to such problems. These include key management complexity, multi-tenancy, cloud provider vulnerability, etc. Present the topic in a bit more detail with this Cloud Encryption Challenges And Possible Solutions Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Cloud Encryption, Description, Solution. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Storage Encryption Introduction And Features Encryption For Data Privacy In Digital Age It
Cloud Storage Encryption Introduction And Features Encryption For Data Privacy In Digital Age ItThis slide demonstrates the importance of encrypting data before storing or sending it to the cloud. This slide also outlines the features and benefits of cloud encryption such as collaboration, security, scalability, access control, confidentiality, etc. Deliver an outstanding presentation on the topic using this Cloud Storage Encryption Introduction And Features Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Encryption, Introduction, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
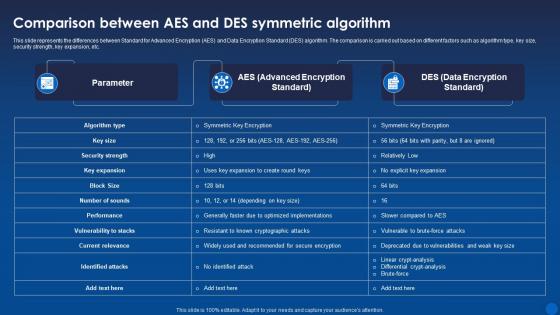 Comparison Aes And Des Symmetric Algorithm Encryption For Data Privacy In Digital Age It
Comparison Aes And Des Symmetric Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the differences between Standard for Advanced Encryption AES and Data Encryption Standard DES algorithm. The comparison is carried out based on different factors such as algorithm type, key size, security strength, key expansion, etc. Deliver an outstanding presentation on the topic using this Comparison Aes And Des Symmetric Algorithm Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Comparison, Key Expansion, Symmetric Algorithm using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
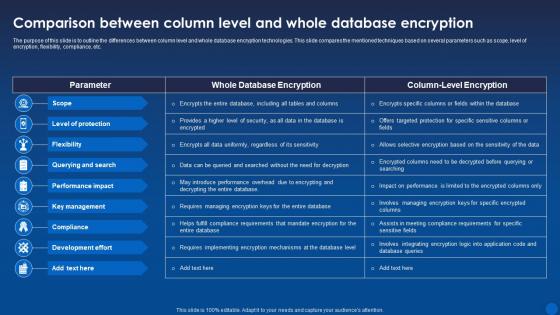 Comparison Between Column Level And Whole Database Encryption For Data Privacy In Digital Age It
Comparison Between Column Level And Whole Database Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the differences between column level and whole database encryption technologies. This slide compares the mentioned techniques based on several parameters such as scope, level of encryption, flexibility, compliance, etc. Present the topic in a bit more detail with this Comparison Between Column Level And Whole Database Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Comparison, Database, Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
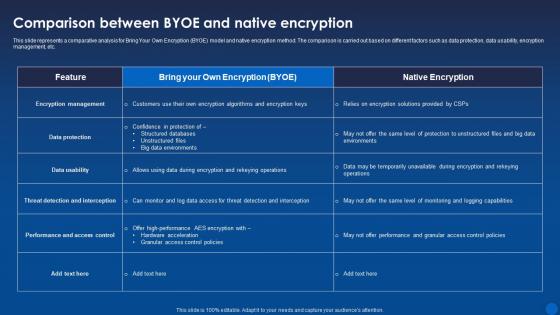 Comparison Byoe And Native Encryption Encryption For Data Privacy In Digital Age It
Comparison Byoe And Native Encryption Encryption For Data Privacy In Digital Age ItThis slide represents a comparative analysis for Bring Your Own Encryption BYOE model and native encryption method. The comparison is carried out based on different factors such as data protection, data usability, encryption management, etc. Deliver an outstanding presentation on the topic using this Comparison Byoe And Native Encryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Comparison, Comparative, Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
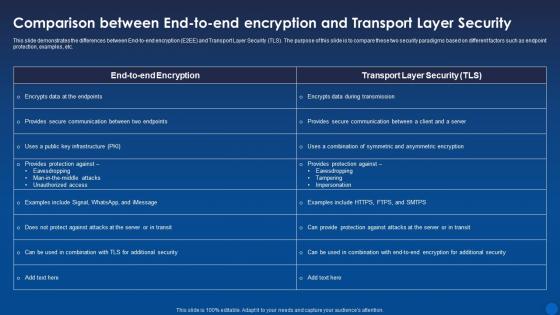 Comparison End To End Encryption And Transport Layer Encryption For Data Privacy In Digital Age It
Comparison End To End Encryption And Transport Layer Encryption For Data Privacy In Digital Age ItThis slide demonstrates the differences between End-to-end encryption E2EE and Transport Layer Security TLS. The purpose of this slide is to compare these two security paradigms based on different factors such as endpoint protection, examples, etc. Present the topic in a bit more detail with this Comparison End To End Encryption And Transport Layer Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Comparison, Protection, Demonstrates. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
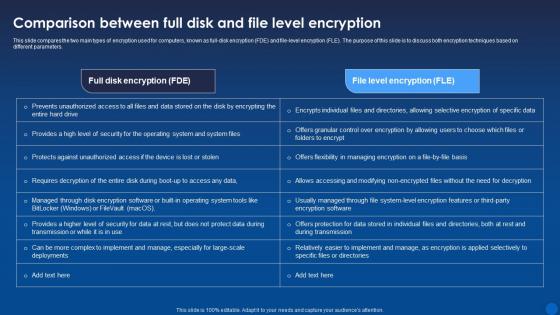 Comparison Full Disk And File Level Encryption Encryption For Data Privacy In Digital Age It
Comparison Full Disk And File Level Encryption Encryption For Data Privacy In Digital Age ItThis slide compares the two main types of encryption used for computers, known as full-disk encryption FDE and file-level encryption FLE. The purpose of this slide is to discuss both encryption techniques based on different parameters. Present the topic in a bit more detail with this Comparison Full Disk And File Level Encryption Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Comparison, Encryption, Techniques. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
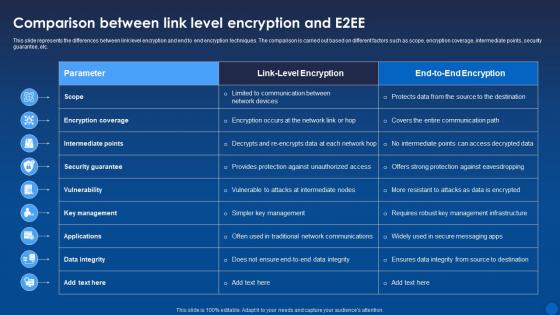 Comparison Link Level Encryption And E2ee Encryption For Data Privacy In Digital Age It
Comparison Link Level Encryption And E2ee Encryption For Data Privacy In Digital Age ItThis slide represents the differences between link level encryption and end to end encryption techniques. The comparison is carried out based on different factors such as scope, encryption coverage, intermediate points, security guarantee, etc. Deliver an outstanding presentation on the topic using this Comparison Link Level Encryption And E2ee Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Comparison, Encryption, Intermediate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
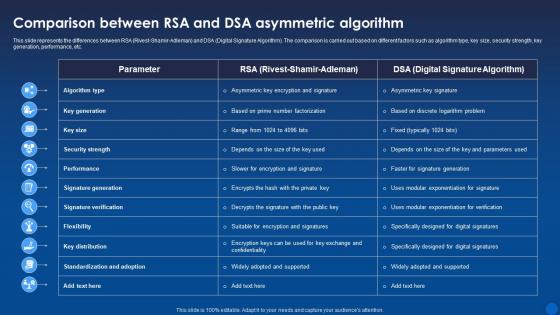 Comparison Rsa And Dsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age It
Comparison Rsa And Dsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the differences between RSA Rivest-Shamir-Adleman and DSA Digital Signature Algorithm. The comparison is carried out based on different factors such as algorithm type, key size, security strength, key generation, performance, etc. Present the topic in a bit more detail with this Comparison Rsa And Dsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric Algorithm, Comparison, Performance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
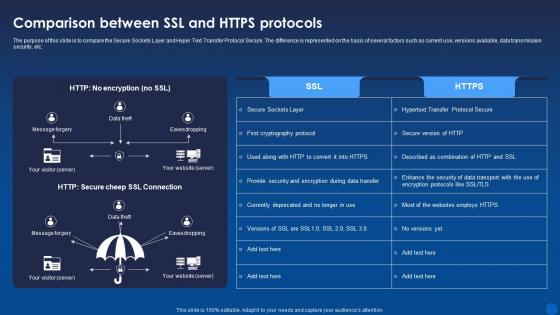 Comparison Ssl And Https Protocols Encryption For Data Privacy In Digital Age It
Comparison Ssl And Https Protocols Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to compare the Secure Sockets Layer and Hyper Text Transfer Protocol Secure. The difference is represented on the basis of several factors such as current use, versions available, data transmission security, etc. Deliver an outstanding presentation on the topic using this Comparison Ssl And Https Protocols Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Comparison, Encryption, Data Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
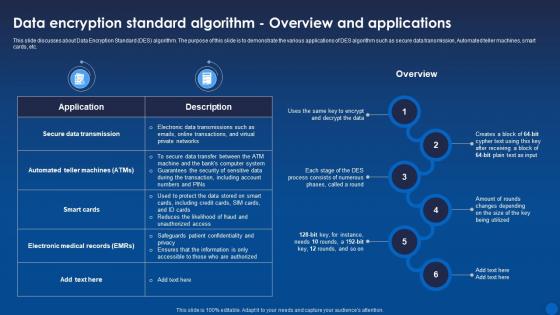 Data Standard Algorithm Overview And Applications Encryption For Data Privacy In Digital Age It
Data Standard Algorithm Overview And Applications Encryption For Data Privacy In Digital Age ItThis slide discusses about Data Encryption Standard DES algorithm. The purpose of this slide is to demonstrate the various applications of DES algorithm such as secure data transmission, Automated teller machines, smart cards, etc. Present the topic in a bit more detail with this Data Standard Algorithm Overview And Applications Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Overview, Applications, Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
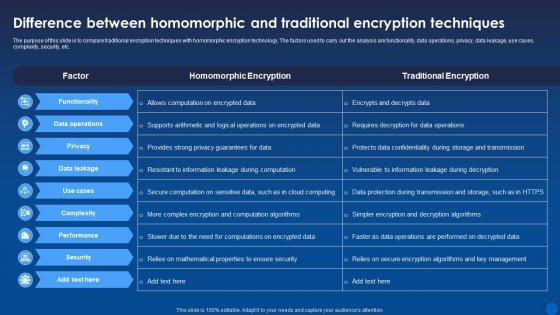 Difference And Traditional Encryption Techniques Encryption For Data Privacy In Digital Age It
Difference And Traditional Encryption Techniques Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to compare traditional encryption techniques with homomorphic encryption technology. The factors used to carry out the analysis are functionality, data operations, privacy, data leakage, use cases, complexity, security, etc. Deliver an outstanding presentation on the topic using this Difference And Traditional Encryption Techniques Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Homomorphic, Encryption, Techniques using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
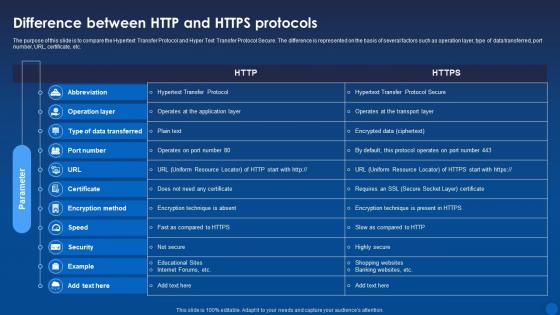 Difference Between Http And Https Protocols Encryption For Data Privacy In Digital Age It
Difference Between Http And Https Protocols Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to compare the Hypertext Transfer Protocol and Hyper Text Transfer Protocol Secure. The difference is represented on the basis of several factors such as operation layer, type of data transferred, port number, URL, certificate, etc. Present the topic in a bit more detail with this Difference Between Http And Https Protocols Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Transfer Protocol, Operation, Data Transferred. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
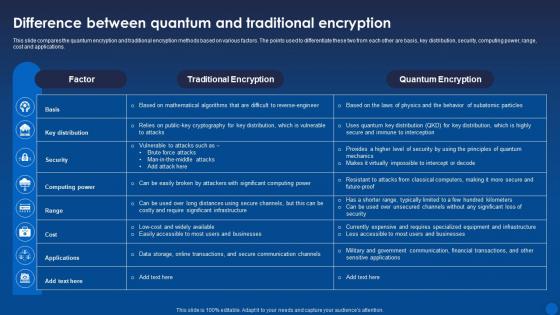 Difference Quantum And Traditional Encryption Encryption For Data Privacy In Digital Age It
Difference Quantum And Traditional Encryption Encryption For Data Privacy In Digital Age ItThis slide compares the quantum encryption and traditional encryption methods based on various factors. The points used to differentiate these two from each other are basis, key distribution, security, computing power, range, cost and applications. Deliver an outstanding presentation on the topic using this Difference Quantum And Traditional Encryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Traditional Encryption, Quantum Encryption, Applications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
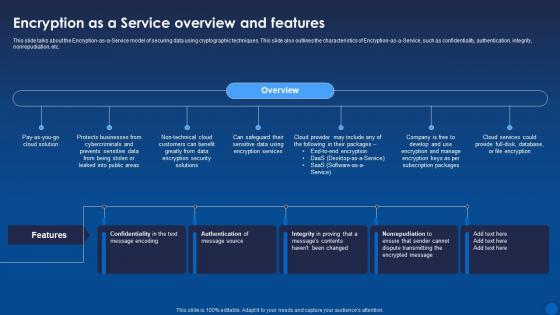 Encryption As A Service Overview And Features Encryption For Data Privacy In Digital Age It
Encryption As A Service Overview And Features Encryption For Data Privacy In Digital Age ItThis slide talks about the Encryption-as-a-Service model of securing data using cryptographic techniques. This slide also outlines the characteristics of Encryption-as-a-Service, such as confidentiality, authentication, integrity, nonrepudiation, etc. Deliver an outstanding presentation on the topic using this Encryption As A Service Overview And Features Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Service, Overview, Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
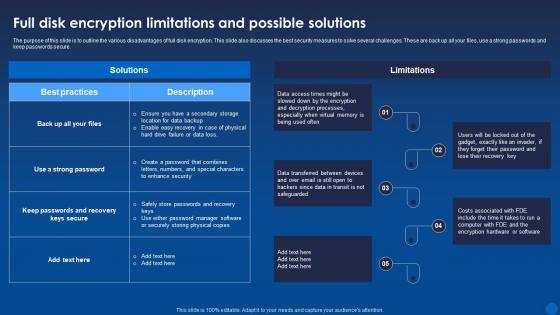 Full Disk Encryption Limitations And Possible Solutions Encryption For Data Privacy In Digital Age It
Full Disk Encryption Limitations And Possible Solutions Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the various disadvantages of full disk encryption. This slide also discusses the best security measures to solve several challenges. These are back up all your files, use a strong passwords and keep passwords secure. Present the topic in a bit more detail with this Full Disk Encryption Limitations And Possible Solutions Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Limitations, Safeguarded. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
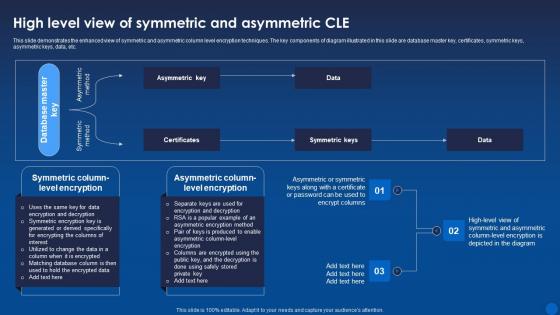 High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age It
High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age ItThis slide demonstrates the enhanced view of symmetric and asymmetric column level encryption techniques. The key components of diagram illustrated in this slide are database master key, certificates, symmetric keys, asymmetric keys, data, etc. Deliver an outstanding presentation on the topic using this High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Symmetric, Asymmetric, Certificates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
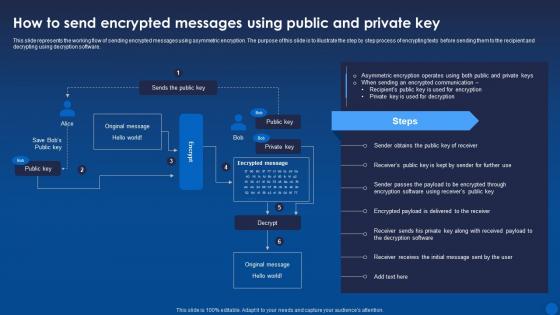 How To Messages Using Public And Private Key Encryption For Data Privacy In Digital Age It
How To Messages Using Public And Private Key Encryption For Data Privacy In Digital Age ItThis slide represents the working flow of sending encrypted messages using asymmetric encryption. The purpose of this slide is to illustrate the step by step process of encrypting texts before sending them to the recipient and decrypting using decryption software. Present the topic in a bit more detail with this How To Messages Using Public And Private Key Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric, ncryption, Communication. This template is free to edit as deemed fit for your organization. Therefore download it now.


