Powerpoint Templates and Google slides for Effective Cyber Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Information Security Program For Effective Cybersecurity Risk Management Powerpoint Presentation Slides
Information Security Program For Effective Cybersecurity Risk Management Powerpoint Presentation SlidesThis complete presentation has PPT slides on wide range of topics highlighting the core areas of your business needs. It has professionally designed templates with relevant visuals and subject driven content. This presentation deck has total of fifty six slides. Get access to the customizable templates. Our designers have created editable templates for your convenience. You can edit the color, text and font size as per your need. You can add or delete the content if required. You are just a click to away to have this ready-made presentation. Click the download button now.
-
 Effective security monitoring plan to eliminate cyber threats and data breaches complete deck
Effective security monitoring plan to eliminate cyber threats and data breaches complete deckEnthrall your audience with this Effective Security Monitoring Plan To Eliminate Cyber Threats And Data Breaches Complete Deck. Increase your presentation threshold by deploying this well crafted template. It acts as a great communication tool due to its well researched content. It also contains stylized icons, graphics, visuals etc, which make it an immediate attention grabber. Comprising fourty four slides, this complete deck is all you need to get noticed. All the slides and their content can be altered to suit your unique business setting. Not only that, other components and graphics can also be modified to add personal touches to this prefabricated set.
-
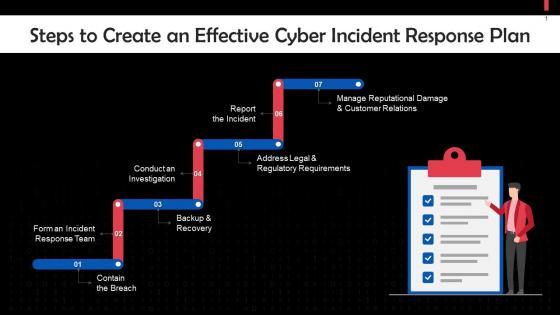 Steps To Create An Effective Cyber Incident Response Plan Training Ppt
Steps To Create An Effective Cyber Incident Response Plan Training PptPresenting Steps to Create an Effective Cyber Incident Response Plan. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
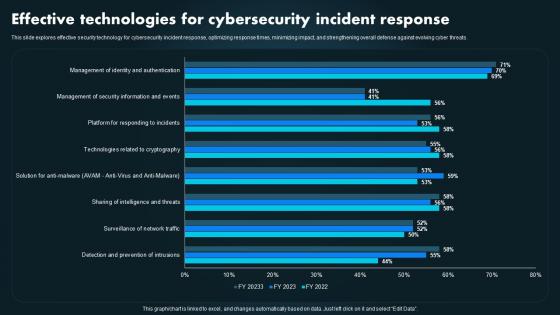 Effective Technologies For Cybersecurity Incident Response
Effective Technologies For Cybersecurity Incident ResponseThis slide explores effective security technology for cybersecurity incident response, optimizing response times, minimizing impact, and strengthening overall defense against evolving cyber threats. Introducing our Effective Technologies For Cybersecurity Incident Response set of slides. The topics discussed in these slides are Effective Technologies, Cybersecurity Incident Response, Minimizing Impact, Strengthening. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cybersecurity Plan With Effective Healthcare Tools
Cybersecurity Plan With Effective Healthcare ToolsThis slide presents healthcare cybersecurity plan, helpful in identifying nature of threats and using tools to protect system from malicious practices. It includes affected components such as patient, privacy protection, healthcare legacy system and tools such as Microsoft EMET and Exact Trak Introducing our Cybersecurity Plan With Effective Healthcare Tools set of slides. The topics discussed in these slides are Cybersecurity Key Components, Cybersecurity Solutions. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
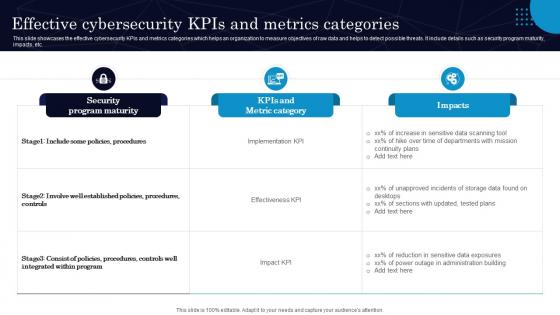 Effective Cybersecurity Kpis And Metrics Categories
Effective Cybersecurity Kpis And Metrics CategoriesThis slide showcases the effective cybersecurity KPIs and metrics categories which helps an organization to measure objectives of raw data and helps to detect possible threats. It include details such as security program maturity, impacts, etc. Introducing our Effective Cybersecurity Kpis And Metrics Categories set of slides. The topics discussed in these slides are Security Program Maturity, Kpis And Metric Category. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
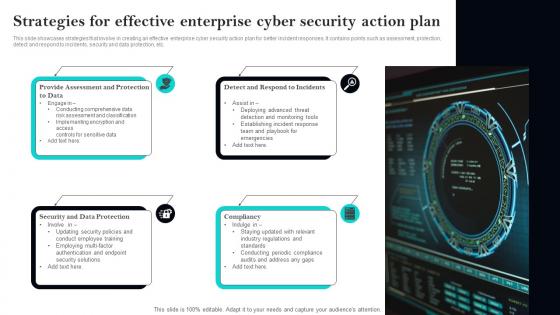 Strategies For Effective Enterprise Cyber Security Action Plan
Strategies For Effective Enterprise Cyber Security Action PlanThis slide showcases strategies that involve in creating an effective enterprise cyber security action plan for better incident responses. It contains points such as assessment, protection, detect and respond to incidents, security and data protection, etc. Presenting our set of slides with Strategies For Effective Enterprise Cyber Security Action Plan. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Protection, Assessment, Respond.
-
 Prerequisites For Establishing Effective Cyber Security Tabletop Exercise
Prerequisites For Establishing Effective Cyber Security Tabletop ExerciseThis slide shows factors for creating an effective cyber tabletop exercise. The purpose of this slide is to provide support for development by ensuring enhanced experience of running tabletop exercises. It covers factors such as clear objectives, stakeholders involvement, realism and improvements. Presenting our set of slides with Prerequisites For Establishing Effective Cyber Security Tabletop Exercise. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Clear Objectives, Stakeholders Involvement, Realism And Relevance.
-
 Core Elements Of Effective Cyber Audit
Core Elements Of Effective Cyber AuditThis slide covers key elements in cyber audit and provides details about core departments that help to optimize efficiency in a company. It includes elements such as operations, data, etc. Introducing our premium set of slides with Core Elements Of Effective Cyber Audit. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Operations, Network Security, System . So download instantly and tailor it with your information.
-
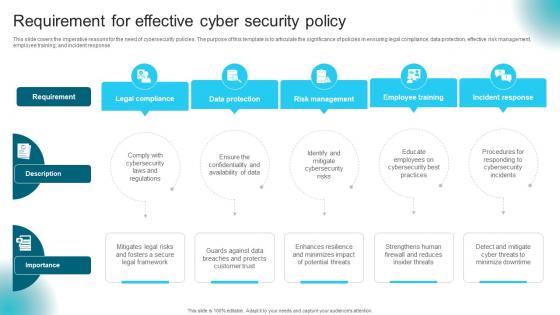 Requirement For Effective Cyber Security Policy
Requirement For Effective Cyber Security PolicyThis slide covers the imperative reasons for the need of cybersecurity policies. The purpose of this template is to articulate the significance of policies in ensuring legal compliance, data protection, effective risk management, employee training, and incident response. Presenting our set of slides with Requirement For Effective Cyber Security Policy This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Legal Compliance, Data Protection, Risk Management
-
 Effective Blackberry Cybersecurity Solutions For Enhanced Protection
Effective Blackberry Cybersecurity Solutions For Enhanced ProtectionThis slide showcases blackberry cybersecurity solutions for better safety. The purpose of this template is to provide businesses with solutions for enhancing protection against digital threats and vulnerabilities. It includes elements such as incident response, unified endpoint management, etc. Introducing our premium set of slides with Effective Blackberry Cybersecurity Solutions For Enhanced Protection. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Management, Protect, Response. So download instantly and tailor it with your information.
-
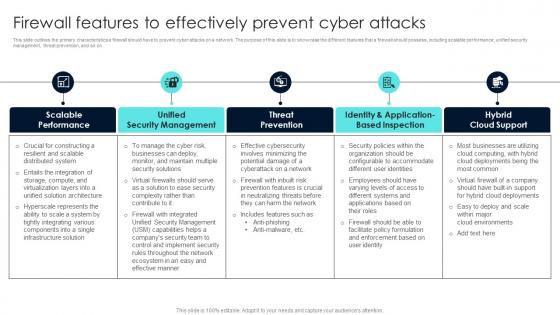 Firewall Network Security Firewall Features To Effectively Prevent Cyber Attacks
Firewall Network Security Firewall Features To Effectively Prevent Cyber AttacksThis slide outlines the primary characteristics a firewall should have to prevent cyber attacks on a network. The purpose of this slide is to showcase the different features that a firewall should possess, including scalable performance, unified security management, threat prevention, and so on. Introducing Firewall Network Security Firewall Features To Effectively Prevent Cyber Attacks to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on URL Categories By Traffic, Traffic Source IP, Traffic Desintation IP using this template. Grab it now to reap its full benefits.
-
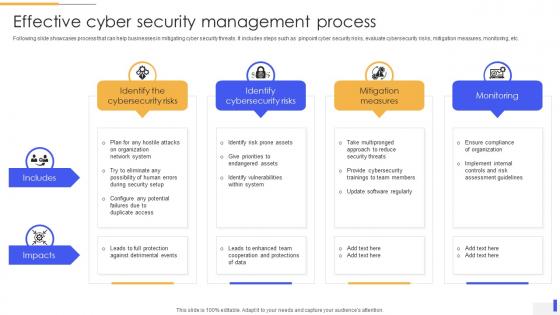 Effective Cyber Security Management Process
Effective Cyber Security Management ProcessFollowing slide showcases process that can help businesses in mitigating cyber security threats. It includes steps such as pinpoint cyber security risks, evaluate cybersecurity risks, mitigation measures, monitoring, etc. Presenting our well structured Effective Cyber Security Management Process. The topics discussed in this slide are Identify The Cybersecurity Risks, Identify Cybersecurity Risks, Mitigation Measures. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
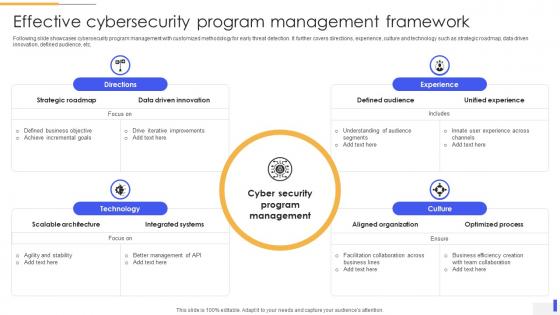 Effective Cybersecurity Program Management Framework
Effective Cybersecurity Program Management FrameworkFollowing slide showcases cybersecurity program management with customized methodology for early threat detection. It further covers directions, experience, culture and technology such as strategic roadmap, data driven innovation, defined audience, etc. Introducing our Effective Cybersecurity Program Management Framework set of slides. The topics discussed in these slides are Scalable Architecture, Integrated Systems, Data Driven Innovation. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
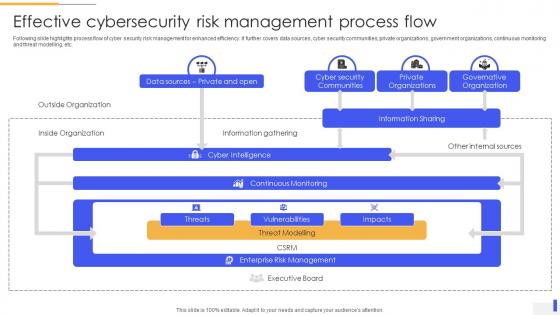 Effective Cybersecurity Risk Management Process Flow
Effective Cybersecurity Risk Management Process FlowFollowing slide highlights process flow of cyber security risk management for enhanced efficiency. It further covers data sources, cyber security communities, private organizations, government organizations, continuous monitoring and threat modelling, etc. Presenting our well structured Effective Cybersecurity Risk Management Process Flow. The topics discussed in this slide are Cyber Security Communities, Private Organizations, Governative Organization. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
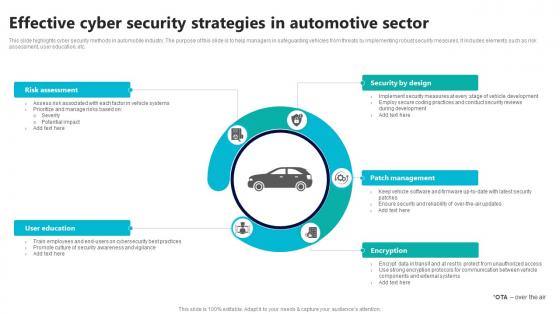 Effective Cyber Security Strategies In Automotive Sector
Effective Cyber Security Strategies In Automotive SectorThis slide highlights cyber security methods in automobile industry. The purpose of this slide is to help managers in safeguarding vehicles from threats by implementing robust security measures. It includes elements such as risk assessment, user education, etc. Introducing our premium set of slides with Effective Cyber Security Strategies In Automotive Sector Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk Assessment, Security By Design, Patch Management So download instantly and tailor it with your information.
-
 Effective Cybersecurity Measures In Retail Sector
Effective Cybersecurity Measures In Retail SectorThis slide highlights best practices for ensuring retail cyber security. The purpose of this template is to assist security teams in developing and implementing techniques for protecting enterprises from digital attacks. It includes elements such as employee training, recovery plan, etc. Presenting our set of slides with Effective Cybersecurity Measures In Retail Sector This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Employee Training, Adherence, Regular Audits, Recovery Plan
-
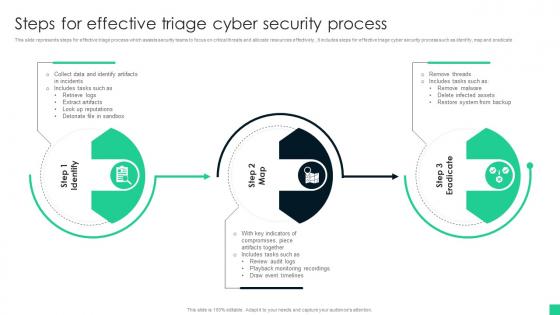 Steps For Effective Triage Cyber Security Process
Steps For Effective Triage Cyber Security ProcessThis slide represents steps for effective triage process which assists security teams to focus on critical threats and allocate resources effectively., It includes steps for effective triage cyber security process such as identify, map and eradicate Introducing our premium set of slides with name Steps For Effective Triage Cyber Security Process Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Artifacts, Draw Event Timelines, System From Backup. So download instantly and tailor it with your information.
-
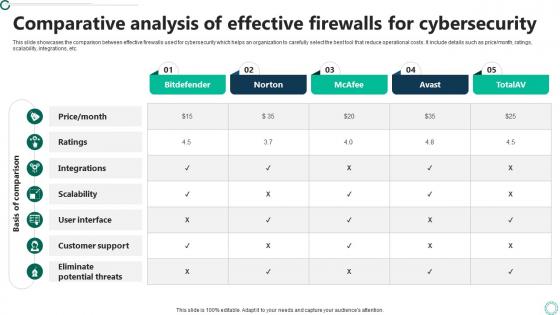 Comparative Analysis Of Effective Firewalls For Cybersecurity
Comparative Analysis Of Effective Firewalls For CybersecurityThis slide showcases the comparison between effective firewalls used for cybersecurity which helps an organization to carefully select the best tool that reduce operational costs. It include details such as price or month, ratings, scalability, integrations, etc. Presenting our well structured Comparative Analysis Of Effective Firewalls For Cybersecurity. The topics discussed in this slide are Comparative, Analysis, Cybersecurity. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Effective Future Trends Of Cybersecurity Firewall
Effective Future Trends Of Cybersecurity FirewallThis slide showcases the major future trends of cybersecurity firewall which helps an organization to secure computer network from malicious traffic and unauthorized access. It include details such as cloud based, zero trust and artificial intelligence firewall. Presenting our set of slides with Effective Future Trends Of Cybersecurity Firewall. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Based Firewalls, Zero Trust Firewalls, AI Powered Firewalls .
-
 Cybercrimes Types For Privacy Safeguarding Through Effective Monitoring
Cybercrimes Types For Privacy Safeguarding Through Effective MonitoringFollowing slide showcases types of cyber crimes for effective monitoring to safeguard privacy. It further covers types such as computer hacking, copyright infringement and cyber stalking, etc. Introducing our premium set of slides with Cybercrimes Types For Privacy Safeguarding Through Effective Monitoring Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Stalking, Computer Hacking, Copyright Infringement. So download instantly and tailor it with your information.
-
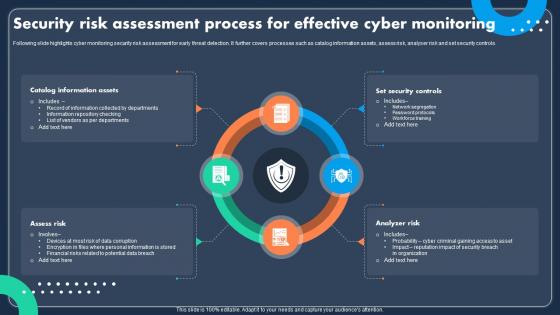 Security Risk Assessment Process For Effective Cyber Monitoring
Security Risk Assessment Process For Effective Cyber MonitoringFollowing slide highlights cyber monitoring security risk assessment for early threat detection. It further covers processes such as catalog information assets, assess risk, analyser risk and set security controls. Introducing our premium set of slides with Security Risk Assessment Process For Effective Cyber Monitoring Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Assets, Security Controls, Analyzer Risk. So download instantly and tailor it with your information.
-
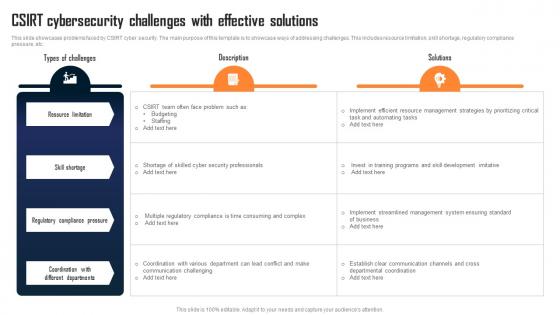 Csirt Cybersecurity Challenges With Effective Solutions
Csirt Cybersecurity Challenges With Effective SolutionsThis slide showcases problems faced by CSIRT cyber security. The main purpose of this template is to showcase ways of addressing challenges. This includes resource limitation, skill shortage, regulatory compliance pressure, etc. Presenting our well structured Csirt Cybersecurity Challenges With Effective Solutions. The topics discussed in this slide are Resource Limitation, Skill Shortage, Regulatory Compliance Pressure. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
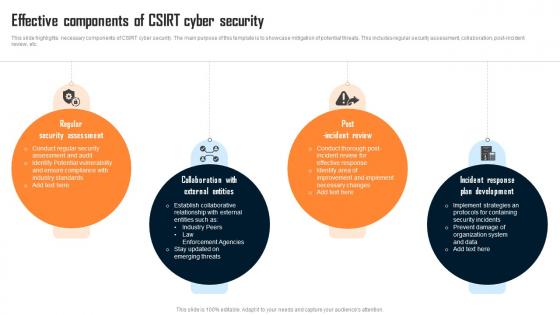 Effective Components Of Csirt Cyber Security
Effective Components Of Csirt Cyber SecurityThis slide highlights necessary components of CSIRT cyber security. The main purpose of this template is to showcase mitigation of potential threats. This includes regular security assessment, collaboration, post incident review, etc. Presenting our set of slides with Effective Components Of Csirt Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Assessment, External Entities, Incident Review.
-
 Effective Role Of Csirt Cybersecurity Team
Effective Role Of Csirt Cybersecurity TeamThis slide provides different roles of CSIRT cyber security. The main purpose of this template is to showcase comprehensive approach for effective management. This includes incident responder, forensics report , legal advisor, etc. Introducing our premium set of slides with Effective Role Of Csirt Cybersecurity Team. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Threat Intelligence Analyst, Incident Responder, Forensics Analyst. So download instantly and tailor it with your information.
-
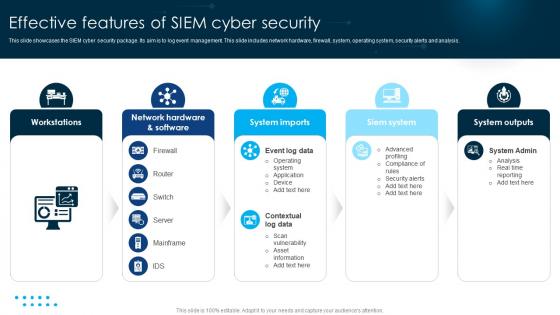 Effective Features Of SIEM Cyber Security
Effective Features Of SIEM Cyber SecurityThis slide showcases the SIEM cyber security package. Its aim is to log event management. This slide includes network hardware, firewall, system, operating system, security alerts and analysis. Introducing our premium set of slides with name Effective Features Of SIEM Cyber Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Workstations, System Imports, Siem System. So download instantly and tailor it with your information.
-
 Top Cyber Risks Faced By The Real Estate Company Effective Risk Management Strategies
Top Cyber Risks Faced By The Real Estate Company Effective Risk Management StrategiesThe following slide exhibits four cyber risks which are faced by the real estate organization. It provides key information about the ransomware, phishing, web based attack and email fraud attack. Present the topic in a bit more detail with this Top Cyber Risks Faced By The Real Estate Company Effective Risk Management Strategies. Use it as a tool for discussion and navigation on Ransomware, Phishing, Business Email Compromise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
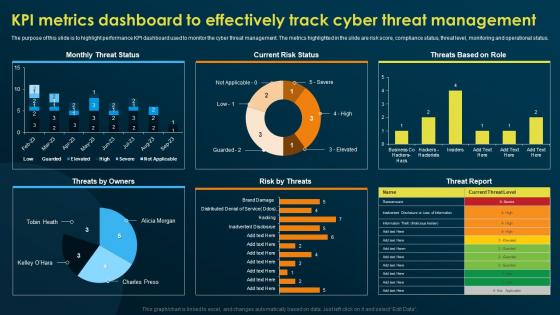 KPI Metrics Dashboard To Effectively Track Cyber Threat Implementing Security Awareness Training
KPI Metrics Dashboard To Effectively Track Cyber Threat Implementing Security Awareness TrainingThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this KPI Metrics Dashboard To Effectively Track Cyber Threat Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Current Risk Status, Threats By Owners, Risk By Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
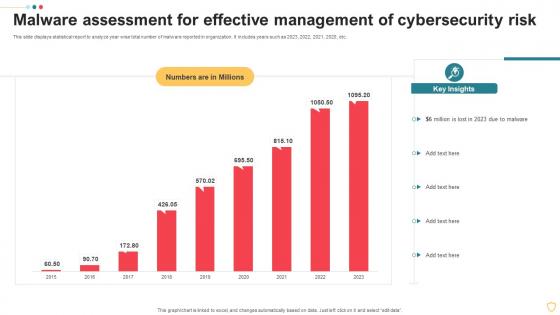 Malware Assessment For Effective Management Of Cybersecurity Risk
Malware Assessment For Effective Management Of Cybersecurity RiskThis slide displays statistical report to analyze year wise total number of malware reported in organization. It includes years such as 2023, 2022, 2021, 2020, etc. Introducing our Malware Assessment For Effective Management Of Cybersecurity Risk set of slides. The topics discussed in these slides are Assessment, Management, Cybersecurity. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber Security
Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Risk By Threats, Threat Report, Current Risk Status. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
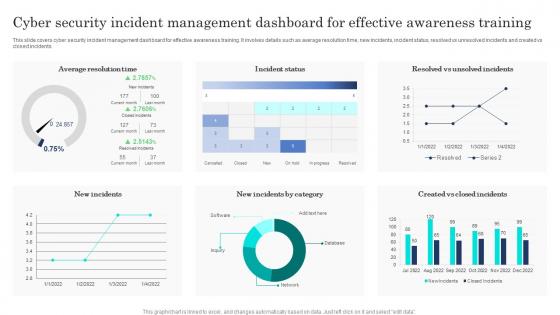 Cyber Security Incident Management Dashboard For Effective Awareness Training
Cyber Security Incident Management Dashboard For Effective Awareness TrainingThis slide covers cyber security incident management dashboard for effective awareness training. It involves details such as average resolution time, new incidents, incident status, resolved vs unresolved incidents and created vs closed incidents. Presenting our well-structured Cyber Security Incident Management Dashboard For Effective Awareness Training. The topics discussed in this slide are Cyber Security, Incident Management Dashboard, Effective Awareness Training. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 KPI Metrics Dashboard To Effectively Track Cyber Threat Management Conducting Security Awareness
KPI Metrics Dashboard To Effectively Track Cyber Threat Management Conducting Security AwarenessThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Deliver an outstanding presentation on the topic using this KPI Metrics Dashboard To Effectively Track Cyber Threat Management Conducting Security Awareness. Dispense information and present a thorough explanation of Monthly Threat Status, Current Risk Status, Threats Based Role using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Developing Cyber Security Awareness KPI Metrics Dashboard To Effectively Track Cyber Threat Management
Developing Cyber Security Awareness KPI Metrics Dashboard To Effectively Track Cyber Threat ManagementThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this Developing Cyber Security Awareness KPI Metrics Dashboard To Effectively Track Cyber Threat Management. Use it as a tool for discussion and navigation on KPI Metrics Dashboard, Effectively Track Cyber, Threat Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
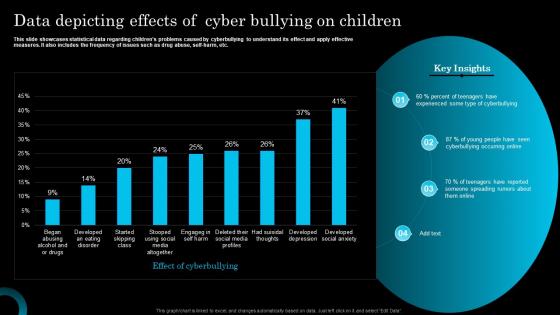 Data Depicting Effects Of Cyber Bullying On Children
Data Depicting Effects Of Cyber Bullying On ChildrenThis slide showcases statistical data regarding childrens problems caused by cyberbullying to understand its effect and apply effective measures. It also includes the frequency of issues such as drug abuse, self harm, etc. Introducing our Data Depicting Effects Of Cyber Bullying On Children set of slides. The topics discussed in these slides are Experienced, Cyberbullying, Spreading. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
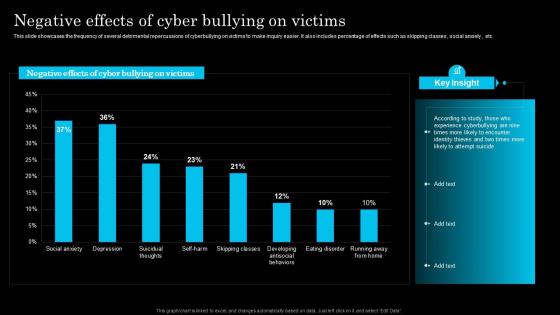 Negative Effects Of Cyber Bullying On Victims
Negative Effects Of Cyber Bullying On VictimsThis slide showcases the frequency of several detrimental repercussions of cyberbullying on victims to make inquiry easier. It also includes percentage of effects such as skipping classes, social anxiety, etc. Presenting our well structured Negative Effects Of Cyber Bullying On Victims. The topics discussed in this slide are According, Encounter, Attempt. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Checklist for effectively managing asset managing cyber risk in a digital age
Checklist for effectively managing asset managing cyber risk in a digital ageFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Checklist For Effectively Managing Asset Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Checklist For Effectively Managing Asset Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
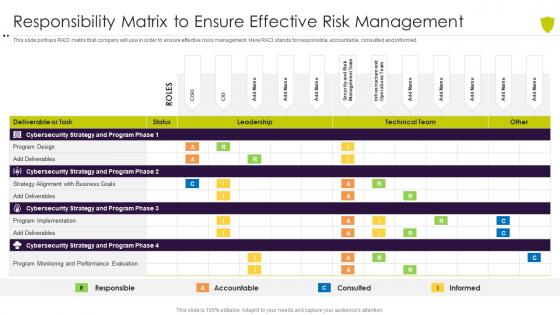 Responsibility matrix to ensure effective risk managing cyber risk in a digital age
Responsibility matrix to ensure effective risk managing cyber risk in a digital ageThis slide portrays RACI matrix that company will use in order to ensure effective risks management. Here RACI stands for responsible, accountable, consulted and informed. Deliver an outstanding presentation on the topic using this Responsibility Matrix To Ensure Effective Risk Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Responsibility Matrix To Ensure Effective Risk Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icons Slide Information Security Program For Effective Cybersecurity Risk Management
Icons Slide Information Security Program For Effective Cybersecurity Risk ManagementIntroducing our well researched set of slides titled Icons Slide Information Security Program For Effective Cybersecurity Risk Management. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber
Checklist For Effectively Managing Asset Security Risk Based Methodology To CyberFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Increase audience engagement and knowledge by dispensing information using Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber This template helps you present information on one stage. You can also present information on System Monitoring, Data Backup, Security Patches using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
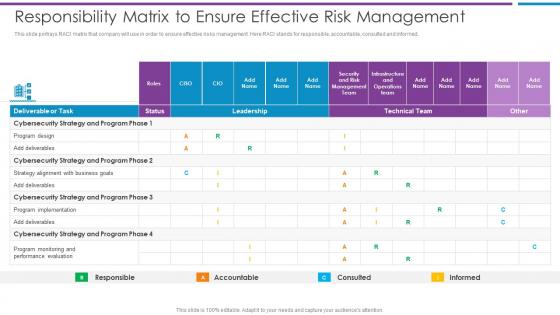 Responsibility Matrix To Ensure Effective Risk Management Risk Based Methodology To Cyber
Responsibility Matrix To Ensure Effective Risk Management Risk Based Methodology To CyberThis slide portrays RACI matrix that company will use in order to ensure effective risks management. Here RACI stands for responsible, accountable, consulted and informed.Present the topic in a bit more detail with this Responsibility Matrix To Ensure Effective Risk Management Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Cybersecurity Strategy, Program Implementation, Program Monitoring This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda Security Program For Effective Cybersecurity Risk Management
Agenda Security Program For Effective Cybersecurity Risk ManagementIntroducing Agenda Security Program For Effective Cybersecurity Risk Management to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Digitalization, Cybersecurity, Business, using this template. Grab it now to reap its full benefits.
-
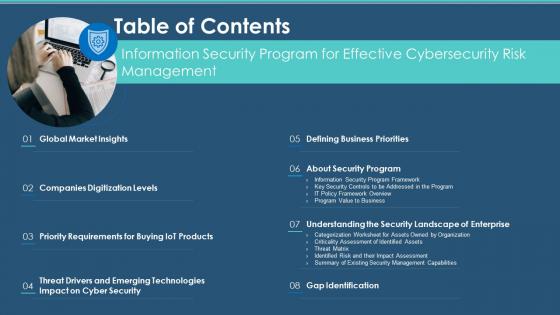 Table Of Contents Information Security Program For Effective Cybersecurity Risk Management
Table Of Contents Information Security Program For Effective Cybersecurity Risk ManagementIncrease audience engagement and knowledge by dispensing information using Table Of Contents Information Security Program For Effective Cybersecurity Risk Management. This template helps you present information on eight stages. You can also present information on Requirements, Technologies, Gap Identification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
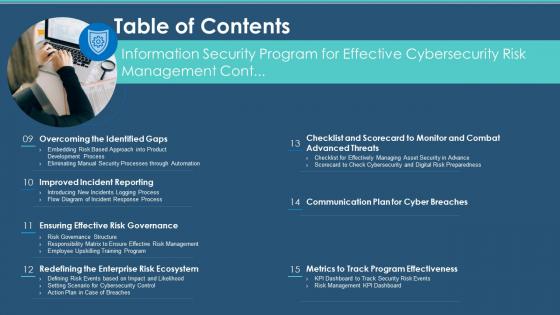 Security Program Effective Cybersecurity Risk Management Table Of Contents
Security Program Effective Cybersecurity Risk Management Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Security Program Effective Cybersecurity Risk Management Table Of Contents. This template helps you present information on seven stages. You can also present information on Risk Governance, Enterprise Risk Ecosystem, Program Effectiveness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents
Incident Response Playbook Impact Categories For Effectively Handling Cyber Security IncidentsMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Increase audience engagement and knowledge by dispensing information using Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents. This template helps you present information on three stages. You can also present information on Functional Impact, Information Impact, Recoverability Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Budget for effective threat management workplace cyber security risk management
Budget for effective threat management workplace cyber security risk managementFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Present the topic in a bit more detail with this Budget For Effective Threat Management Workplace Cyber Security Risk Management. Use it as a tool for discussion and navigation on Incident Management, Risk Management, Client Onboarding Process, Document Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact analysis for effective threat management in cyber security risk management
Impact analysis for effective threat management in cyber security risk managementThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Introducing Impact Analysis For Effective Threat Management In Cyber Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Focus Areas, Actual Access Violations, Access Rights Authorized, using this template. Grab it now to reap its full benefits.
-
 Impact analysis for effective cyber threat management workplace
Impact analysis for effective cyber threat management workplaceThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Deliver an outstanding presentation on the topic using this Impact Analysis For Effective Cyber Threat Management Workplace. Dispense information and present a thorough explanation of Focus Areas, Actual Access Violations, Access Rights Authorized using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Approaches To Overcome Cybersecurity Risk Faced Effective Risk Management Strategies
Approaches To Overcome Cybersecurity Risk Faced Effective Risk Management StrategiesThe following slide exhibits various approaches which can be used to prevent cybersecurity risk faced by the real estate enterprise. The key approaches highlighted in the slide are updating the security system, installing anti-phishing add ons, using a customized web application firewall etc. Present the topic in a bit more detail with this Approaches To Overcome Cybersecurity Risk Faced Effective Risk Management Strategies. Use it as a tool for discussion and navigation on Ransomware, Phishing, Business Email Compromise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
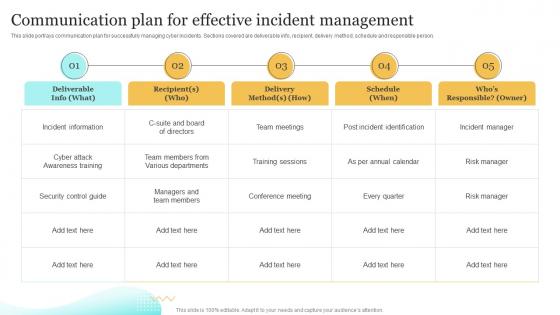 Communication Plan For Effective Incident Upgrading Cybersecurity With Incident Response Playbook
Communication Plan For Effective Incident Upgrading Cybersecurity With Incident Response PlaybookThis slide portrays communication plan for successfully managing cyber incidents. Sections covered are deliverable info, recipient, delivery method, schedule and responsible person. Present the topic in a bit more detail with this Communication Plan For Effective Incident Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Communication, Management, Deliverable. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
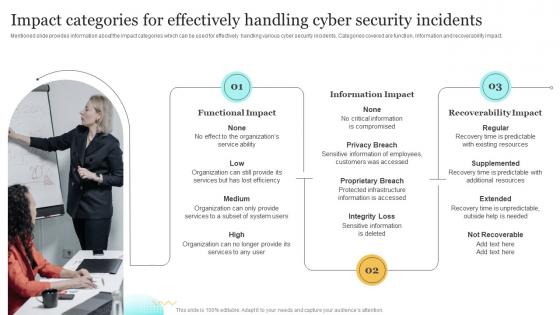 Impact Categories For Effectively Handling Cyber Upgrading Cybersecurity With Incident Response Playbook
Impact Categories For Effectively Handling Cyber Upgrading Cybersecurity With Incident Response PlaybookMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Present the topic in a bit more detail with this Impact Categories For Effectively Handling Cyber Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Functional Impact, Information Impact, Recoverability Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategic Plan Timeline To Develop Effective Cyber Security Strategy
Strategic Plan Timeline To Develop Effective Cyber Security StrategyThis slide signifies the strategic plan timeline to create effective cyber security project. It covers information about steps like identify, analyse, evaluate, prioritise, treat and monitor Presenting our set of slides with name Strategic Plan Timeline To Develop Effective Cyber Security Strategy. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Evaluate, Prioritise.
-
 Communication Plan For Effective Incident Management Cybersecurity Incident And Vulnerability
Communication Plan For Effective Incident Management Cybersecurity Incident And VulnerabilityThis slide portrays communication plan for successfully managing cyber incidents. Sections covered are deliverable info, recipient, delivery method, schedule and responsible person. Introducing Communication Plan For Effective Incident Management Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Delivery Method, Incident Information, Team Meetings, using this template. Grab it now to reap its full benefits.
-
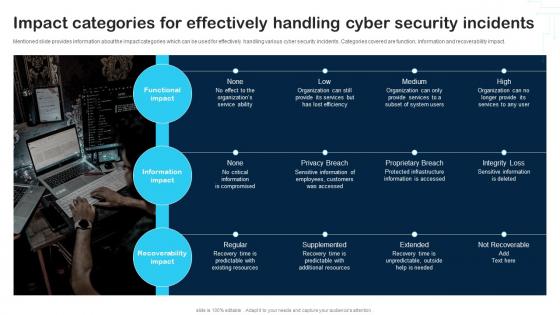 Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability
Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And VulnerabilityMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Increase audience engagement and knowledge by dispensing information using Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability. This template helps you present information on three stages. You can also present information on Functional Impact, Information Impact, Recoverability Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
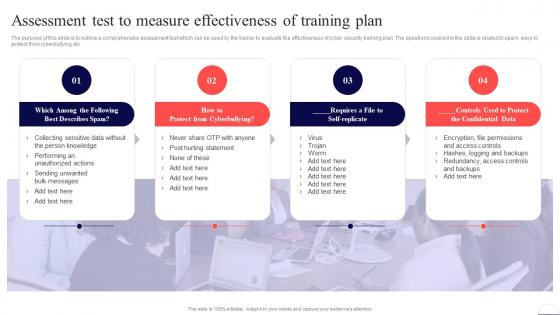 Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber Security
Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Cyberbullying, Confidential Data, Training Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
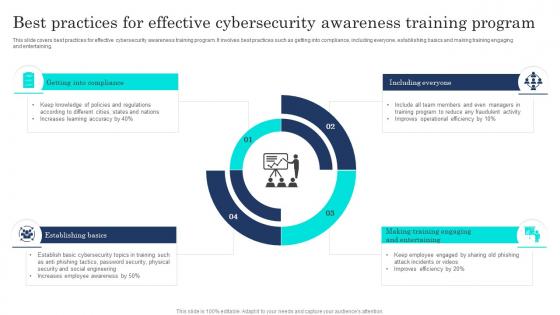 Best Practices For Effective Cybersecurity Awareness Training Program
Best Practices For Effective Cybersecurity Awareness Training ProgramThis slide covers best practices for effective cybersecurity awareness training program. It involves best practices such as getting into compliance, including everyone, establishing basics and making training engaging and entertaining. Presenting our set of slides with name Best Practices For Effective Cybersecurity Awareness Training Program. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Getting Into Compliance, Establishing Basics, Including Everyone.
-
 Cybersecurity Attack Vector Analysis For Effective Awareness Training
Cybersecurity Attack Vector Analysis For Effective Awareness TrainingThis slide covers cybersecurity attack vector analysis for effective awareness training. It involves malware, phishing, denial of service, poor encryption, device misconfiguration and cross site scripting. Introducing our premium set of slides with Cybersecurity Attack Vector Analysis For Effective Awareness Training. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Attack Vector, Examples, Objective, Problem Identifier. So download instantly and tailor it with your information.
-
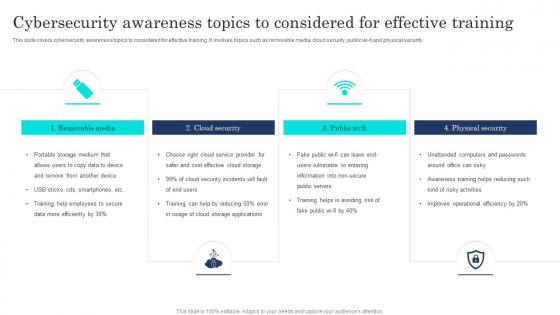 Cybersecurity Awareness Topics To Considered For Effective Training
Cybersecurity Awareness Topics To Considered For Effective TrainingThis slide covers cybersecurity awareness topics to considered for effective training. It involves topics such as removable media, cloud security, public wi fi and physical security. Presenting our set of slides with name Cybersecurity Awareness Topics To Considered For Effective Training. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Removable Media, Cloud Security, Physical Security, Public Wi Fi.
-
 Cybersecurity Awareness Training Methods For Effective Results
Cybersecurity Awareness Training Methods For Effective ResultsThis slide covers cybersecurity awareness training methods for effective results. It involves methods such as involve games, engage friendly competition, include rewards and turn into team effort. Introducing our premium set of slides with Cybersecurity Awareness Training Methods For Effective Results. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cybersecurity Awareness Training, Methods, Effective Results. So download instantly and tailor it with your information.
-
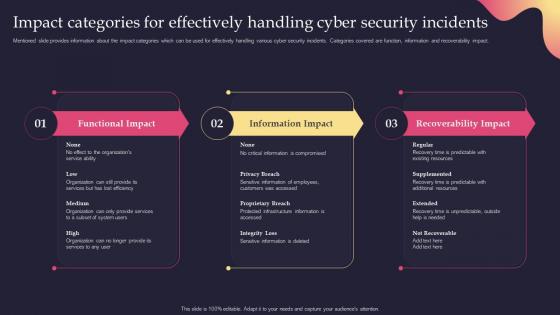 Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents
Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security IncidentsMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Present the topic in a bit more detail with this Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents. Use it as a tool for discussion and navigation on Categories, Effectively, Information Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
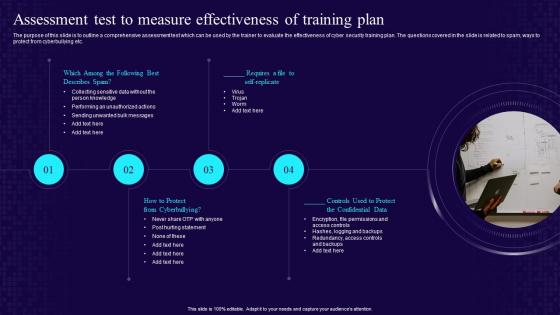 Assessment Test To Measure Effectiveness Of Training Plan Developing Cyber Security Awareness
Assessment Test To Measure Effectiveness Of Training Plan Developing Cyber Security AwarenessThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Plan Developing Cyber Security Awareness. This template helps you present information on four stages. You can also present information on Self Replicate, Confidential Data, Cyberbullying, Training Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


