Powerpoint Templates and Google slides for Encryption And Tokenization
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
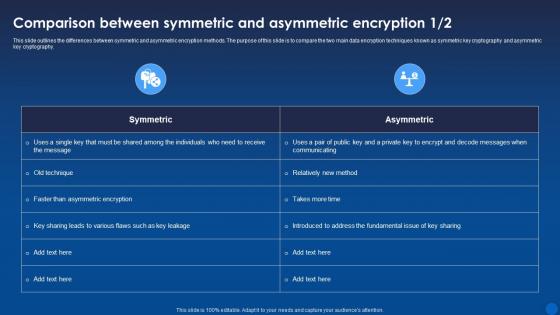 Comparison Symmetric And Asymmetric Encryption Encryption For Data Privacy In Digital Age It
Comparison Symmetric And Asymmetric Encryption Encryption For Data Privacy In Digital Age ItThis slide outlines the differences between symmetric and asymmetric encryption methods. The purpose of this slide is to compare the two main data encryption techniques known as symmetric key cryptography and asymmetric key cryptography. Present the topic in a bit more detail with this Comparison Symmetric And Asymmetric Encryption Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric, Encryption, Comparison. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 WIFI Encryption Security Device Colored Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Encryption Security Device Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis PowerPoint icon features a colourful illustration of a lock, symbolizing the security of a wireless network. It is perfect for presentations on WIFI security, data protection, and cyber safety. Use this icon to emphasize the importance of secure networks and data privacy.
-
 WIFI Encryption Security Device Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Encryption Security Device Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is perfect for any presentation on WIFI security. It features a classic black and white design with a laptop and a router, making it ideal for any modern business presentation. It is easy to use and can be used to illustrate the importance of secure WIFI connections.
-
 File Encryption Sharing Colored Icon In Powerpoint Pptx Png And Editable Eps Format
File Encryption Sharing Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis cheerful coloured powerpoint icon is perfect for illustrating file sharing. It features a cloud with an arrow pointing up and down, representing the transfer of files between two sources.
-
 File Encryption Sharing Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
File Encryption Sharing Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon is perfect for representing File Sharing. It features a folder with an arrow pointing to the right, symbolizing the sharing of files from one device to another. It is simple, yet effective and can be used in any presentation.
-
 Encryption Broken Shield Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Broken Shield Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon features a broken shield with a distressed texture. It is perfect for conveying a sense of vulnerability, fragility, or failure in presentations. It is available in a range of vibrant colours and can be used to highlight key points or draw attention to important concepts.
-
 Encryption Broken Shield Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Broken Shield Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint icon depicts a broken shield, representing a lack of protection or security. It is perfect for conveying a sense of vulnerability, fragility, or danger in presentations. It can also be used to illustrate a lack of trust or loyalty.
-
 Sales force Encrypted Fields Limitations In Powerpoint And Google Slides Cpb
Sales force Encrypted Fields Limitations In Powerpoint And Google Slides CpbPresenting Sales force Encrypted Fields Limitations In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Salesforce Encrypted Fields Limitations. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Shield Encryption Salesforce Limitations In Powerpoint And Google Slides Cpb
Shield Encryption Salesforce Limitations In Powerpoint And Google Slides CpbPresenting Shield Encryption Salesforce Limitations In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Shield Encryption Salesforce Limitations. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 WIFI Off Wireless Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Off Wireless Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis is a coloured powerpoint icon of a WIFI symbol with a red cross over it, indicating the WIFI is off. Ideal for presentations or documents related to technology, networks and internet security.
-
 WIFI Off Wireless Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Off Wireless Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon is perfect for presentations that need to communicate the concept of WIFI Off. It features a simple, minimalistic design that is easy to recognize and eye catching. The icon is available in both vector and raster formats for easy use.
-
 Digital Signature Encryptions Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Signature Encryptions Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is perfect for illustrating the concept of digital signature. It is a high-resolution, vector-based graphic with a vibrant and eye-catching colour palette. It is an ideal choice for presentations, infographics, and other visuals.
-
 Digital Signature Encryptions Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Signature Encryptions Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Digital Signature is a modern and stylish way to represent the concept of digital signature. It is a simple yet powerful graphic that will add a professional touch to any presentation. It is easy to customize and can be used for a variety of purposes.
-
 Encryption Scan WIFI Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Scan WIFI Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is perfect for presentations and displays. It features a modern, sleek design and is available in a range of vibrant colours. It is easy to use and adds a professional touch to your work.
-
 Encryption Scan WIFI Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Scan WIFI Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon on Scan WIFI is a simple yet effective way to add a professional look to your presentation. It is easy to customize and can be used to illustrate any concept related to scanning a wireless network. It is an ideal choice for any business or educational presentation.
-
 User Authentication Encryption Login Colored Icon In Powerpoint Pptx Png And Editable Eps Format
User Authentication Encryption Login Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is perfect for making your presentation stand out. It features a login symbol in bright and vivid colours that will draw the attention of your audience. It is easy to use and can be resized to fit your needs. Get creative and make your presentation memorable with this powerpoint icon.
-
 User Authentication Encryption Login Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
User Authentication Encryption Login Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMonotone Powerpoint Icon on Login is a high-quality vector icon designed to be used in presentations, websites, and other digital projects. It features a simple, minimalistic design with a monotone color palette, making it perfect for modern and professional designs.
-
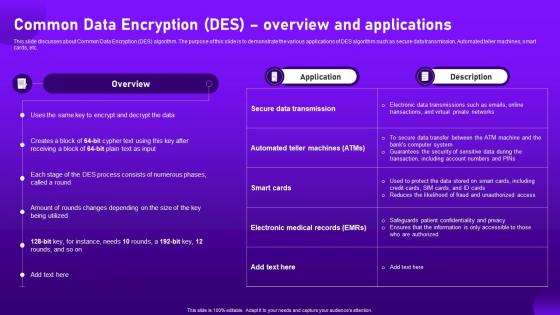 Common Data Encryption Des Overview And Applications Cloud Cryptography
Common Data Encryption Des Overview And Applications Cloud CryptographyThis slide discusses about Common Data Encryption DES algorithm. The purpose of this slide is to demonstrate the various applications of DES algorithm such as secure data transmission, Automated teller machines, smart cards, etc. Deliver an outstanding presentation on the topic using this Common Data Encryption Des Overview And Applications Cloud Cryptography. Dispense information and present a thorough explanation of Overview, Applications, Data Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
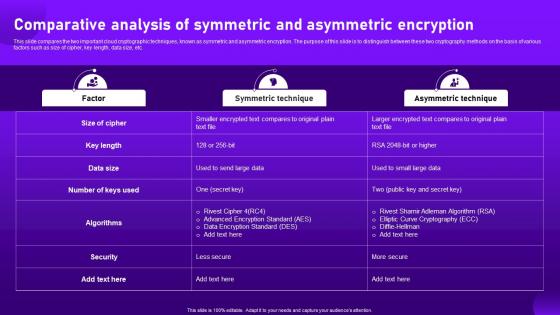 Comparative Analysis Of Symmetric And Asymmetric Encryption Cloud Cryptography
Comparative Analysis Of Symmetric And Asymmetric Encryption Cloud CryptographyThis slide compares the two important cloud cryptographic techniques, known as symmetric and asymmetric encryption. The purpose of this slide is to distinguish between these two cryptography methods on the basis of various factors such as size of cipher, key length, data size, etc. Present the topic in a bit more detail with this Comparative Analysis Of Symmetric And Asymmetric Encryption Cloud Cryptography. Use it as a tool for discussion and navigation on Comparative, Analysis, Asymmetric Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
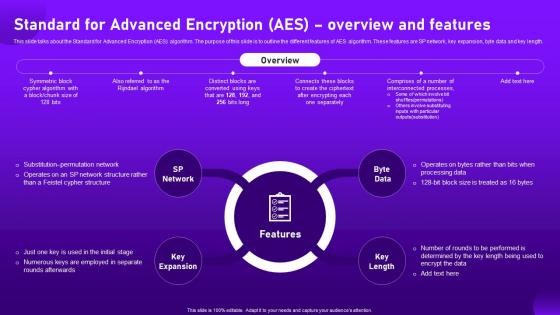 Standard For Advanced Encryption Aes Overview And Features Cloud Cryptography
Standard For Advanced Encryption Aes Overview And Features Cloud CryptographyThis slide talks about the Standard for Advanced Encryption AES algorithm. The purpose of this slide is to outline the different features of AES algorithm. These features are SP network, key expansion, byte data and key length. Introducing Standard For Advanced Encryption Aes Overview And Features Cloud Cryptography to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Key Expansion, Overview, Processing, using this template. Grab it now to reap its full benefits.
-
 File Encryption Download Folder Colored Icon In Powerpoint Pptx Png And Editable Eps Format
File Encryption Download Folder Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful PowerPoint icon is perfect for adding a touch of vibrancy to your presentations. It comes in a range of colours and is easy to download and use. Ideal for making your slides stand out and engaging your audience.
-
 File Encryption Download Folder Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
File Encryption Download Folder Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for presentations. It is a high quality vector image that can be scaled to any size without losing its quality. It is easy to customize and can be used in any project.
-
 Encryption Safety Information Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Safety Information Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is perfect for conveying safety information in a visually appealing way. It features a bright yellow background with a black image of a safety helmet, clearly indicating the importance of safety. It is sure to draw attention and help your audience understand the importance of safety in any situation.
-
 Encryption Safety Information Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Safety Information Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is perfect for highlighting safety information in presentations. It features a figure in a safety vest and hardhat, with a warning sign in the background. The icon is a great visual aid to emphasize the importance of safety in the workplace.
-
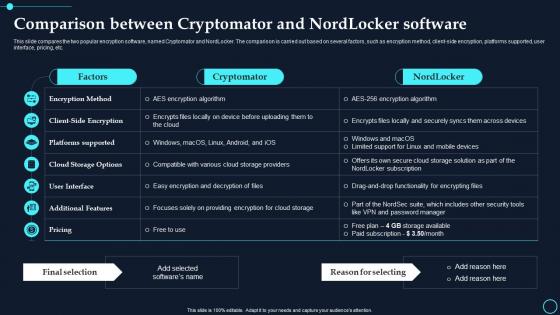 Comparison Between Cryptomator And Nordlocker Software Cloud Data Encryption
Comparison Between Cryptomator And Nordlocker Software Cloud Data EncryptionThis slide compares the two popular encryption software, named Cryptomator and NordLocker. The comparison is carried out based on several factors, such as encryption method, client side encryption, platforms supported, user interface, pricing, etc. Present the topic in a bit more detail with this Comparison Between Cryptomator And Nordlocker Software Cloud Data Encryption. Use it as a tool for discussion and navigation on Cryptomator, Nordlocker. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
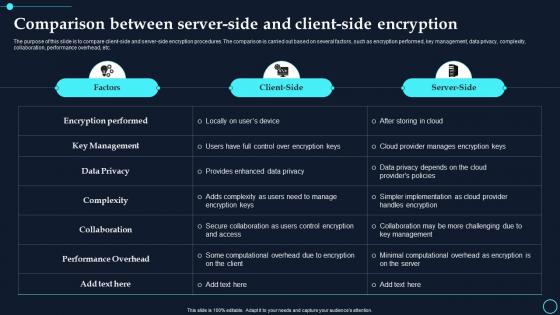 Comparison Between Server-Side And Client Side Encryption Cloud Data Encryption
Comparison Between Server-Side And Client Side Encryption Cloud Data EncryptionThe purpose of this slide is to compare client side and server side encryption procedures. The comparison is carried out based on several factors, such as encryption performed, key management, data privacy, complexity, collaboration, performance overhead, etc. Deliver an outstanding presentation on the topic using this Comparison Between Server Side And Client Side Encryption Cloud Data Encryption. Dispense information and present a thorough explanation of Encryption Performed, Key Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Major Risks And Mitigation Strategies For Cloud Encryption Implementation Cloud Data Encryption
Major Risks And Mitigation Strategies For Cloud Encryption Implementation Cloud Data EncryptionThe purpose of this slide is to discuss the challenges faced while encrypting cloud data. The critical components of this slide are the description of the risk, probability of occurrence, impact on system infrastructure, and possible mitigation strategies. Deliver an outstanding presentation on the topic using this Major Risks And Mitigation Strategies For Cloud Encryption Implementation Cloud Data Encryption. Dispense information and present a thorough explanation of Probability, Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
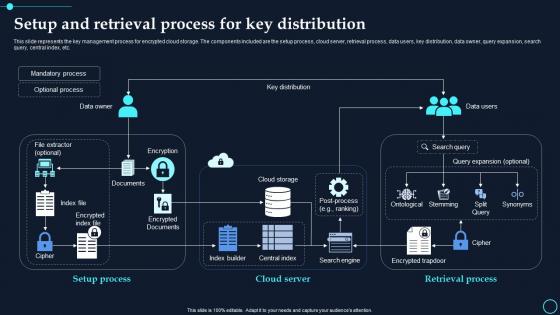 Setup And Retrieval Process For Key Distribution Cloud Data Encryption
Setup And Retrieval Process For Key Distribution Cloud Data EncryptionThis slide represents the key management process for encrypted cloud storage. The components included are the setup process, cloud server, retrieval process, data users, key distribution, data owner, query expansion, search query, central index, etc. Present the topic in a bit more detail with this Setup And Retrieval Process For Key Distribution Cloud Data Encryption. Use it as a tool for discussion and navigation on Mandatory Process, Optional Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Security Encryption Technology Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Security Encryption Technology Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Data Security Encryption Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Security Encryption Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Cryptography Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cryptography Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Cryptography Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cryptography Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Data Encryption Key Management Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Encryption Key Management Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Data Encryption Key Management Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Encryption Key Management Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Digital Signatures Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Signatures Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Digital Signatures Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Signatures Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Encryption Algorithms Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Algorithms Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Encryption Algorithms Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Algorithms Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Identity Management Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Identity Management Data Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis high quality coloured PowerPoint icon depicts Data Encryption Technology, with a bright and vibrant design. Perfect for presentations, brochures, and other digital projects. Easily add to your project to illustrate the importance of data security.
-
 Identity Management Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Identity Management Data Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great visual representation of Data Encryption Technology. It is a simple and modern design that easily conveys the concept of secure data transmission. It is perfect for presentations on data security and encryption technology.
-
 Encryption Code Decoder Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Code Decoder Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis powerpoint icon is a vibrant, multi coloured symbol that conveys the idea of decoding and problem solving. It is perfect for presentations, websites and other digital projects that require a modern, eye catching icon. The icon is available in a variety of colours and sizes, making it easy to customise to your projects needs.
-
 Encryption Code Decoder Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Code Decoder Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMonotone Powerpoint Icon is a perfect choice for presentations. It is a professional looking icon that is easy to use and customize. It can be used to create a modern and stylish look for any presentation. It is also available in different sizes and colors to suit your needs.
-
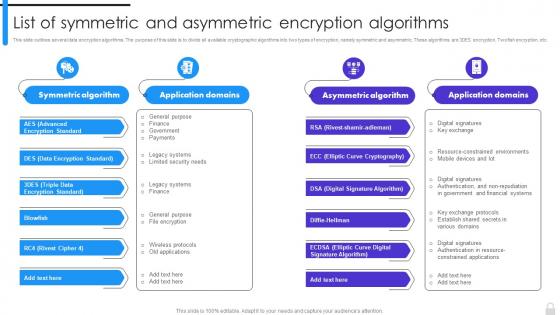 Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption Algorithms
Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption AlgorithmsThis slide outlines several data encryption algorithms. The purpose of this slide is to divide all available cryptographic algorithms into two types of encryption, namely symmetric and asymmetric. These algorithms are 3DES encryption, Twofish encryption, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption Algorithms. Dispense information and present a thorough explanation of Data Encryption Standard, Triple Data Encryption Standard, Digital Signature Algorithm, Elliptic Curve Cryptography using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
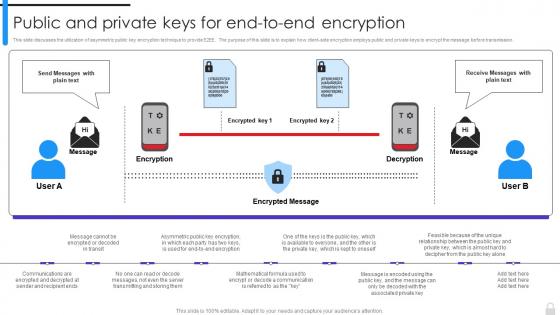 Encryption Implementation Strategies Public And Private Keys For End To End Encryption
Encryption Implementation Strategies Public And Private Keys For End To End EncryptionThis slide discusses the utilization of asymmetric public key encryption technique to provide E2EE. The purpose of this slide is to explain how client-side encryption employs public and private keys to encrypt the message before transmission. Present the topic in a bit more detail with this Encryption Implementation Strategies Public And Private Keys For End To End Encryption. Use it as a tool for discussion and navigation on Public And Private Keys, Encryption Employs, Encryption Technique, Server Transmitting And Storing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
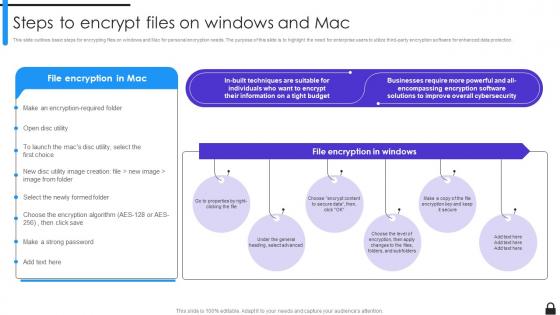 Encryption Implementation Strategies Steps To Encrypt Files On Windows And Mac
Encryption Implementation Strategies Steps To Encrypt Files On Windows And MacThis slide outlines basic steps for encrypting files on windows and Mac for personal encryption needs. The purpose of this slide is to highlight the need for enterprise users to utilize third-party encryption software for enhanced data protection. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Steps To Encrypt Files On Windows And Mac. This template helps you present information on six stages. You can also present information on Encrypting Files On Windows, Mac For Personal Encryption Needs, Encryption Software, Enhanced Data Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
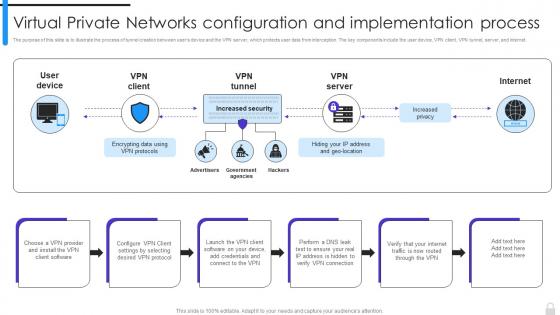 Encryption Implementation Strategies Virtual Private Networks Configuration And Implementation
Encryption Implementation Strategies Virtual Private Networks Configuration And ImplementationThe purpose of this slide is to illustrate the process of tunnel creation between users device and the VPN server, which protects user data from interception. The key components include the user device, VPN client, VPN tunnel, server, and internet. Introducing Encryption Implementation Strategies Virtual Private Networks Configuration And Implementation to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Advertisers, Government Agencies, Virtual Private Networks, Configuration And Implementation Process, using this template. Grab it now to reap its full benefits.
-
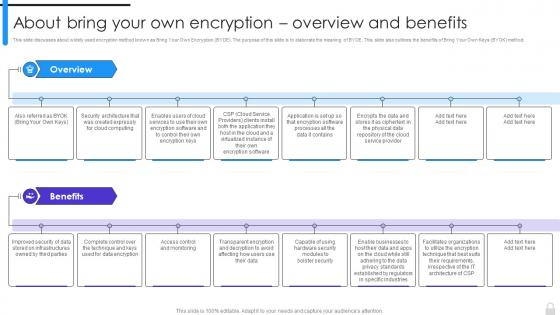 Encryption Implementation Strategies About Bring Your Own Encryption Overview And Benefits
Encryption Implementation Strategies About Bring Your Own Encryption Overview And BenefitsThis slide discusses about widely used encryption method known as Bring Your Own Encryption BYOE. The purpose of this slide is to elaborate the meaning of BYOE. This slide also outlines the benefits of Bring Your Own Keys BYOK method. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies About Bring Your Own Encryption Overview And Benefits. This template helps you present information on eight stages. You can also present information on Bring Your Own Encryption, Bring Your Own Keys, Control And Monitoring using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
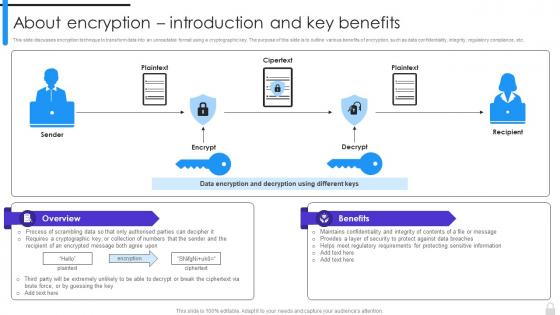 Encryption Implementation Strategies About Encryption Introduction And Key Benefits
Encryption Implementation Strategies About Encryption Introduction And Key BenefitsThis slide discusses encryption technique to transform data into an unreadable format using a cryptographic key. The purpose of this slide is to outline various benefits of encryption, such as data confidentiality, integrity, regulatory compliance, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies About Encryption Introduction And Key Benefits. Use it as a tool for discussion and navigation on Encryption Technique, Cryptographic Key, Data Confidentiality, Integrity, Regulatory Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
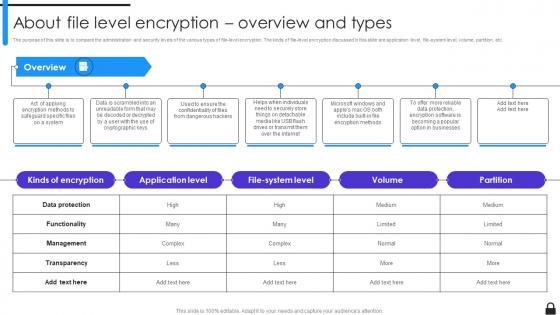 Encryption Implementation Strategies About File Level Encryption Overview And Types
Encryption Implementation Strategies About File Level Encryption Overview And TypesThe purpose of this slide is to compare the administration and security levels of the various types of file-level encryption. The kinds of file-level encryption discussed in this slide are application level, file-system level, volume, partition, etc. Introducing Encryption Implementation Strategies About File Level Encryption Overview And Types to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Administration And Security Levels, File Level Encryption, Application Level, File System Level, using this template. Grab it now to reap its full benefits.
-
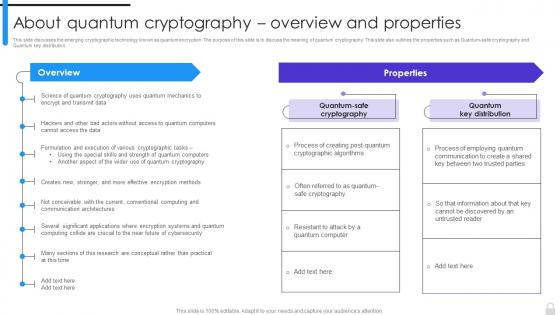 Encryption Implementation Strategies About Quantum Cryptography Overview And Properties
Encryption Implementation Strategies About Quantum Cryptography Overview And PropertiesThis slide discusses the emerging cryptographic technology known as quantum encryption. The purpose of this slide is to discuss the meaning of quantum cryptography. This slide also outlines the properties such as Quantum-safe cryptography and Quantum key distribution. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies About Quantum Cryptography Overview And Properties. Dispense information and present a thorough explanation of Quantum Safe Cryptography, Quantum Key Distribution, Quantum Cryptography using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
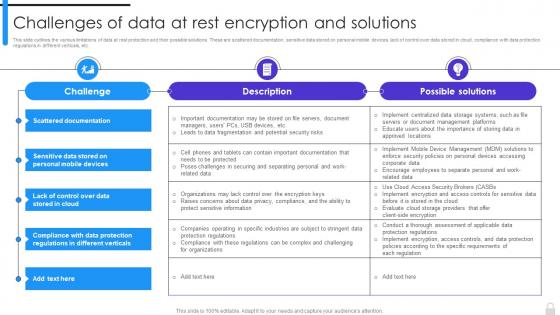 Encryption Implementation Strategies Challenges Of Data At Rest Encryption And Solutions
Encryption Implementation Strategies Challenges Of Data At Rest Encryption And SolutionsThis slide outlines the various limitations of data at rest protection and their possible solutions. These are scattered documentation, sensitive data stored on personal mobile devices, lack of control over data stored in cloud, compliance with data protection regulations in different verticals, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data At Rest Encryption And Solutions. Use it as a tool for discussion and navigation on Data At Rest Protection, Scattered Documentation, Sensitive Data Stored, Personal Mobile Devices, Data Protection Regulations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
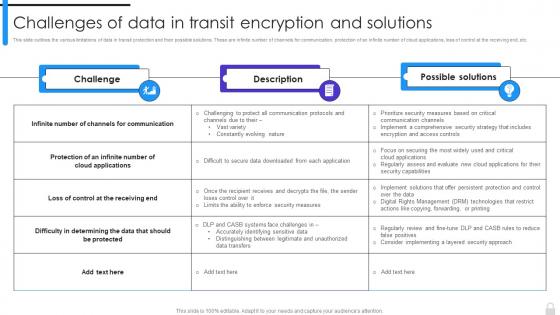 Encryption Implementation Strategies Challenges Of Data In Transit Encryption And Solutions
Encryption Implementation Strategies Challenges Of Data In Transit Encryption And SolutionsThis slide outlines the various limitations of data in transit protection and their possible solutions. These are infinite number of channels for communication, protection of an infinite number of cloud applications, loss of control at the receiving end, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Challenges Of Data In Transit Encryption And Solutions. Dispense information and present a thorough explanation of Data In Transit, Encryption And Solutions, Cloud Applications, Channels For Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
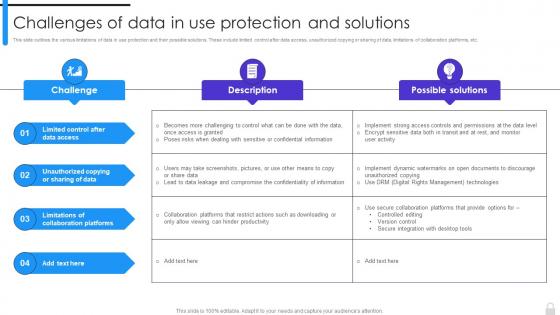 Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions
Encryption Implementation Strategies Challenges Of Data In Use Protection And SolutionsThis slide outlines the various limitations of data in use protection and their possible solutions. These include limited control after data access, unauthorized copying or sharing of data, limitations of collaboration platforms, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions. Use it as a tool for discussion and navigation on Limitations Of Collaboration Platforms, Unauthorized Copying Or Sharing Of Data, Limited Control After Data Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
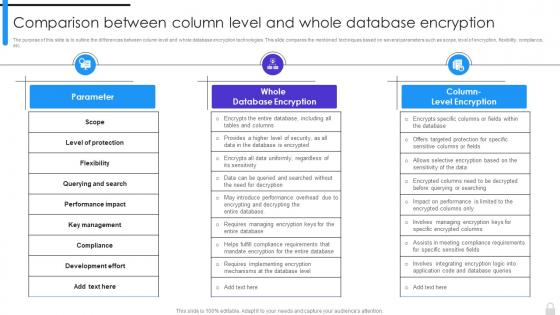 Encryption Implementation Strategies Comparison Between Column Level And Whole Database Encryption
Encryption Implementation Strategies Comparison Between Column Level And Whole Database EncryptionThe purpose of this slide is to outline the differences between column level and whole database encryption technologies. This slide compares the mentioned techniques based on several parameters such as scope, level of encryption, flexibility, compliance, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Comparison Between Column Level And Whole Database Encryption. Dispense information and present a thorough explanation of Whole Database Encryption, Flexibility, Compliance, Mentioned Techniques, Encryption Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
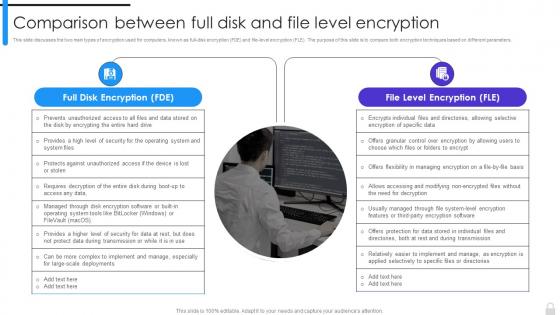 Encryption Implementation Strategies Comparison Between Full Disk And File Level Encryption
Encryption Implementation Strategies Comparison Between Full Disk And File Level EncryptionThis slide discusses the two main types of encryption used for computers, known as full-disk encryption FDE and file-level encryption FLE. The purpose of this slide is to compare both encryption techniques based on different parameters. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Comparison Between Full Disk And File Level Encryption. This template helps you present information on two stages. You can also present information on Full Disk Encryption, File Level Encryption, Operating System And System Files using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
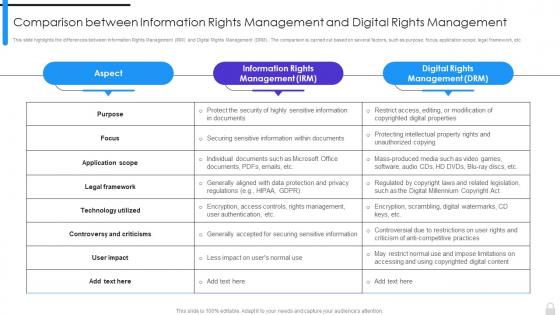 Encryption Implementation Strategies Comparison Between Information Rights Management And Digital
Encryption Implementation Strategies Comparison Between Information Rights Management And DigitalThis slide highlights the differences between Information Rights Management IRM and Digital Rights Management DRM. The comparison is carried out based on several factors, such as purpose, focus, application scope, legal framework, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Comparison Between Information Rights Management And Digital. Dispense information and present a thorough explanation of Information Rights Management, Digital Rights Management, Controversy And Criticisms using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
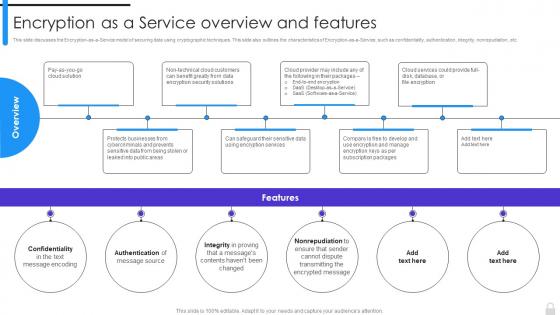 Encryption Implementation Strategies Encryption As A Service Overview And Features
Encryption Implementation Strategies Encryption As A Service Overview And FeaturesThis slide discusses the Encryption-as-a-Service model of securing data using cryptographic techniques. This slide also outlines the characteristics of Encryption-as-a-Service, such as confidentiality, authentication, integrity, nonrepudiation, etc. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Encryption As A Service Overview And Features. This template helps you present information on six stages. You can also present information on Text Message Encoding, Encryption Services, Subscription Packages, Data Encryption Security Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
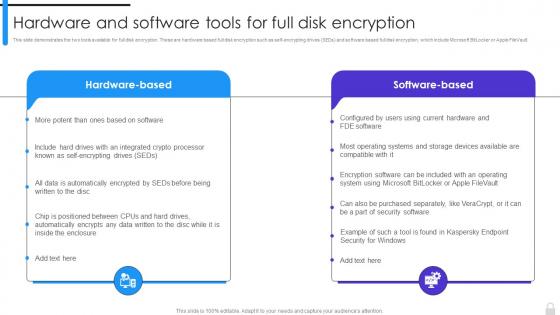 Encryption Implementation Strategies Hardware And Software Tools For Full Disk Encryption
Encryption Implementation Strategies Hardware And Software Tools For Full Disk EncryptionThis slide demonstrates the two tools available for full disk encryption. These are hardware based full disk encryption such as self-encrypting drives SEDs and software based full disk encryption, which include Microsoft BitLocker or Apple FileVault. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Hardware And Software Tools For Full Disk Encryption. This template helps you present information on two stages. You can also present information on Hardware And Software Tools, Full Disk Encryption, Microsoft Bitlocker, Apple Filevault using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
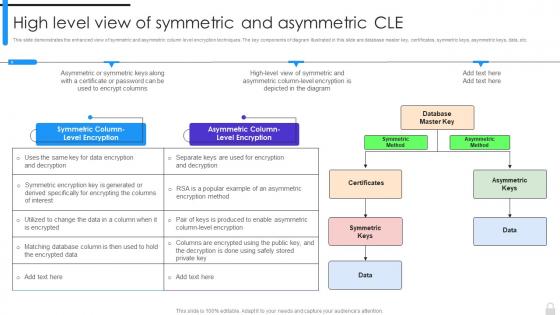 Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric Cle
Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric CleThis slide demonstrates the enhanced view of symmetric and asymmetric column level encryption techniques. The key components of diagram illustrated in this slide are database master key, certificates, symmetric keys, asymmetric keys, data, etc. Introducing Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric Cle to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Symmetric Method, Asymmetric Method, Asymmetric Column Level Encryption, Symmetric Column Level Encryption, using this template. Grab it now to reap its full benefits.
-
 Encrypted Google DOCS In Powerpoint And Google Slides Cpb
Encrypted Google DOCS In Powerpoint And Google Slides CpbPresenting our Encrypted Google DOCS In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Encrypted Google DOCS This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.


