Powerpoint Templates and Google slides for Five Cybersecurity Evolution
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Five Cybersecurity Evolution In Powerpoint And Google Slides Cpb
Five Cybersecurity Evolution In Powerpoint And Google Slides CpbPresenting Five Cybersecurity Evolution In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Five Cybersecurity Evolution. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
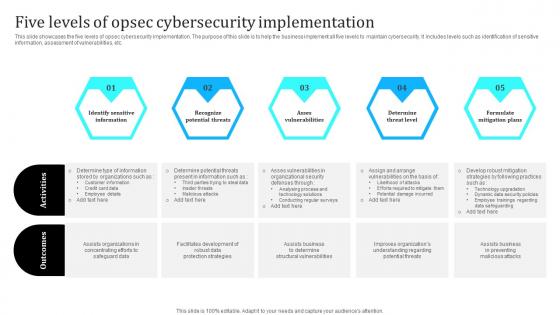 Five Levels Of Opsec Cybersecurity Implementation
Five Levels Of Opsec Cybersecurity ImplementationThis slide showcases the five levels of opsec cybersecurity implementation. The purpose of this slide is to help the business implement all five levels to maintain cybersecurity. It includes levels such as identification of sensitive information, assessment of vulnerabilities, etc. Introducing our premium set of slides with Five Levels Of Opsec Cybersecurity Implementation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Sensitive Information, Recognize Potential Threats, Asses Vulnerabilities . So download instantly and tailor it with your information.
-
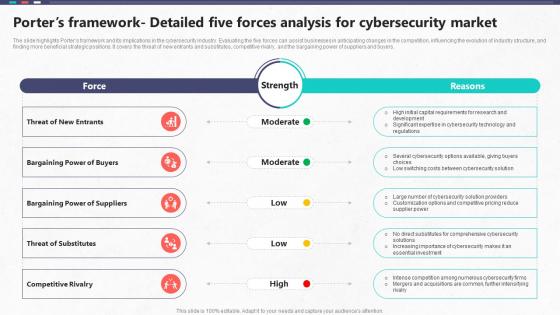 Porters Framework Detailed Five Forces Analysis For Cybersecurity Global Cybersecurity Industry Outlook
Porters Framework Detailed Five Forces Analysis For Cybersecurity Global Cybersecurity Industry OutlookThe slide highlights Porters framework and its implications in the cybersecurity industry. Evaluating the five forces can assist businesses in anticipating changes in the competition, influencing the evolution of industry structure, and finding more beneficial strategic positions. It covers the threat of new entrants and substitutes, competitive rivalry, and the bargaining power of suppliers and buyers. Deliver an outstanding presentation on the topic using this Porters Framework Detailed Five Forces Analysis For Cybersecurity Global Cybersecurity Industry Outlook. Dispense information and present a thorough explanation of Bargaining Power Of Suppliers, Bargaining Power Of Buyers, Threat Of New Entrants using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
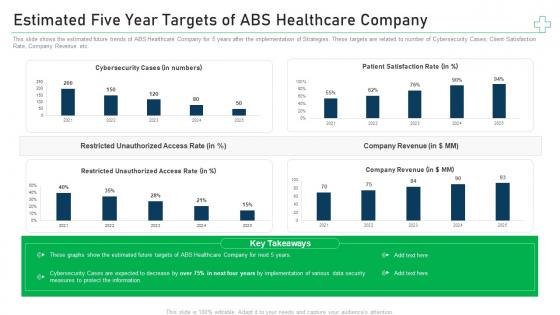 Estimated five year targets of company minimize cybersecurity threats in healthcare company
Estimated five year targets of company minimize cybersecurity threats in healthcare companyThis slide shows the estimated future trends of ABS Healthcare Company for 5 years after the implementation of Strategies. These targets are related to number of Cybersecurity Cases, Client Satisfaction Rate, Company Revenue etc. Present the topic in a bit more detail with this Estimated Five Year Targets Of Company Minimize Cybersecurity Threats In Healthcare Company. Use it as a tool for discussion and navigation on Cybersecurity Cases, Patient Satisfaction Rate, Company Revenue. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
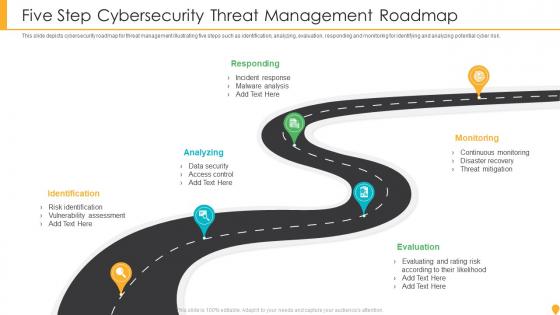 Five Step Cybersecurity Threat Management Roadmap
Five Step Cybersecurity Threat Management RoadmapThis slide depicts cybersecurity roadmap for threat management illustrating five steps such as identification, analyzing, evaluation, responding and monitoring for identifying and analyzing potential cyber risk. Presenting our set of slides with name Five Step Cybersecurity Threat Management Roadmap. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Analyzing, Identification, Responding, Monitoring, Evaluation.
-
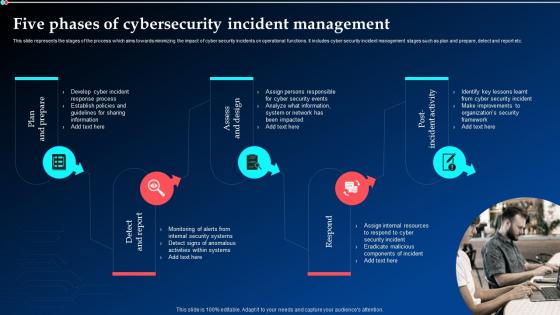 Five Phases Of Cybersecurity Incident Management Ppt Powerpoint Presentation Infographic
Five Phases Of Cybersecurity Incident Management Ppt Powerpoint Presentation InfographicThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Introducing Five Phases Of Cybersecurity Incident Management Ppt Powerpoint Presentation Infographic to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Detect And Report, Assess And Design, Post Incident Activity, using this template. Grab it now to reap its full benefits.
-
 Five Phases Of Cybersecurity Incident Management Deploying Computer Security Incident Management
Five Phases Of Cybersecurity Incident Management Deploying Computer Security Incident ManagementThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc.Introducing Five Phases Of Cybersecurity Incident Management Deploying Computer Security Incident Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Sharing Information, Establish Policies, Response Process, using this template. Grab it now to reap its full benefits.
-
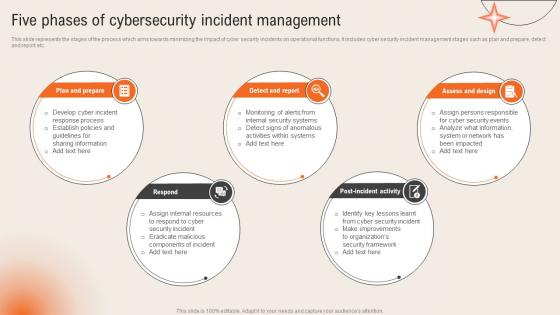
 Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security Incident
Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security IncidentThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Introducing Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security Incident to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assess And Design, Detect And Report, Plan And Prepare, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Attacks Response Plan Five Phases Of Cybersecurity Incident Management
Cyber Security Attacks Response Plan Five Phases Of Cybersecurity Incident ManagementThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Introducing Cyber Security Attacks Response Plan Five Phases Of Cybersecurity Incident Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Plan And Prepare, Post Incident Activity, Assess And Design, Incident Management, using this template. Grab it now to reap its full benefits.
-
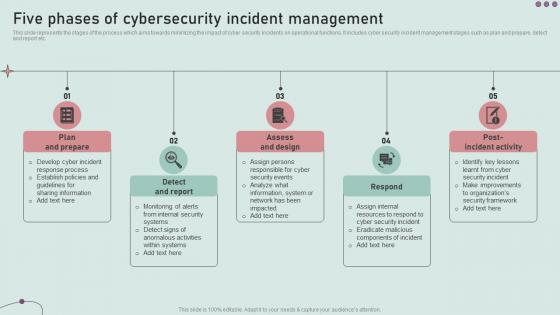
 Five Phases Of Cybersecurity Incident Management Incident Response Strategies Deployment
Five Phases Of Cybersecurity Incident Management Incident Response Strategies DeploymentThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Increase audience engagement and knowledge by dispensing information using Five Phases Of Cybersecurity Incident Management Incident Response Strategies Deployment. This template helps you present information on five stages. You can also present information on Plan, Respond, Report using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

