Powerpoint Templates and Google slides for Guides Vulnerability Reduction
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
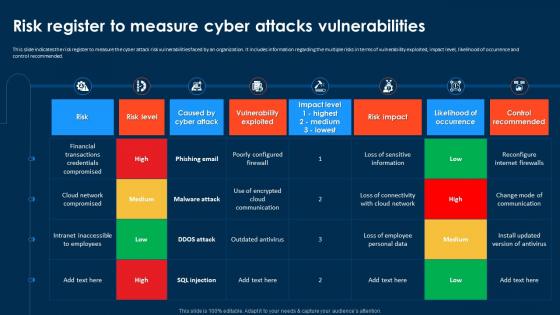 Compressive Planning Guide Risk Register To Measure Cyber Attacks Vulnerabilities
Compressive Planning Guide Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Compressive Planning Guide Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cyber Attack Risk Vulnerabilities, Vulnerability Exploited, Occurrence And Control Recommended. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
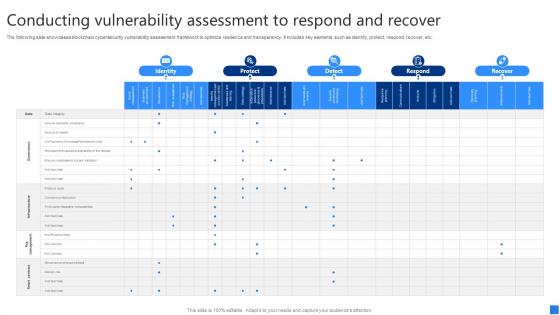 Conducting Vulnerability Assessment Securing Blockchain Transactions A Beginners Guide BCT SS V
Conducting Vulnerability Assessment Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Present the topic in a bit more detail with this Conducting Vulnerability Assessment Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Identity, Protect, Detect. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
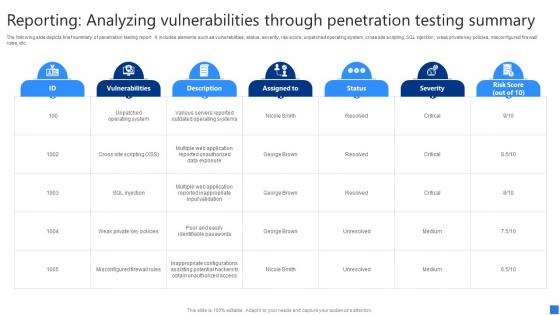 Reporting Analyzing Vulnerabilities Securing Blockchain Transactions A Beginners Guide BCT SS V
Reporting Analyzing Vulnerabilities Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts brief summary of penetration testing report . It includes elements such as vulnerabilities, status, severity, risk score, unpatched operating system, cross site scripting, SQL injection, weak private key policies, misconfigured firewall rules, etc. Present the topic in a bit more detail with this Reporting Analyzing Vulnerabilities Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Vulnerabilities, Status, Severity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
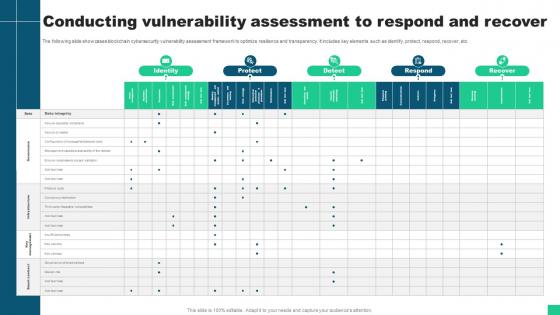 Conducting Vulnerability Assessment To Respond And Recover Guide For Blockchain BCT SS V
Conducting Vulnerability Assessment To Respond And Recover Guide For Blockchain BCT SS VThe following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Present the topic in a bit more detail with this Conducting Vulnerability Assessment To Respond And Recover Guide For Blockchain BCT SS V Use it as a tool for discussion and navigation on Identity, Protect, Respond, Recover This template is free to edit as deemed fit for your organization. Therefore download it now.
-
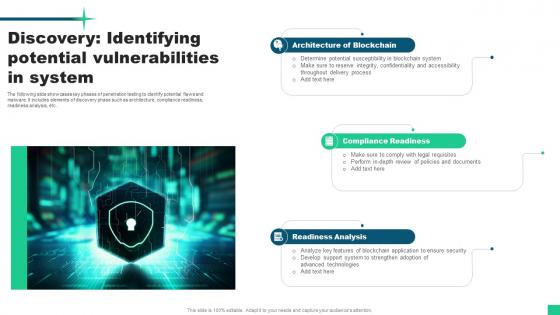 Discovery Identifying Potential Vulnerabilities In System Guide For Blockchain BCT SS V
Discovery Identifying Potential Vulnerabilities In System Guide For Blockchain BCT SS VThe following slide showcases key phases of penetration testing to identify potential flaws and malware. It includes elements of discovery phase such as architecture, compliance readiness, readiness analysis, etc. Increase audience engagement and knowledge by dispensing information using Discovery Identifying Potential Vulnerabilities In System Guide For Blockchain BCT SS V This template helps you present information on three stages. You can also present information on Architecture Of Blockchain, Compliance Readiness, Readiness Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
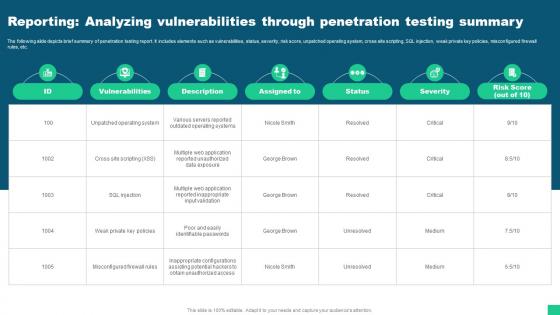 Reporting Analyzing Vulnerabilities Through Penetration Testing Guide For Blockchain BCT SS V
Reporting Analyzing Vulnerabilities Through Penetration Testing Guide For Blockchain BCT SS VThe following slide depicts brief summary of penetration testing report. It includes elements such as vulnerabilities, status, severity, risk score, unpatched operating system, cross site scripting, SQL injection, weak private key policies, misconfigured firewall rules, etc. Deliver an outstanding presentation on the topic using this Reporting Analyzing Vulnerabilities Through Penetration Testing Guide For Blockchain BCT SS V Dispense information and present a thorough explanation of Vulnerabilities, Description, Severity, Risk Score using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
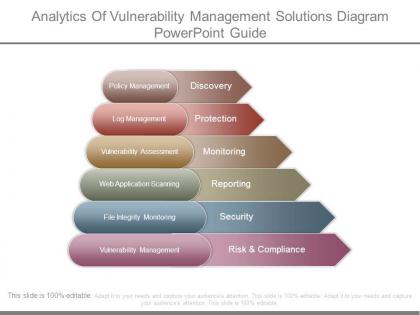 Analytics of vulnerability management solutions diagram powerpoint guide
Analytics of vulnerability management solutions diagram powerpoint guidePresenting analytics of vulnerability management solutions diagram powerpoint guide. This is a analytics of vulnerability management solutions diagram powerpoint guide. This is a six stage process. The stages in this process are discovery, protection, monitoring, reporting, security, risk and compliance.
-
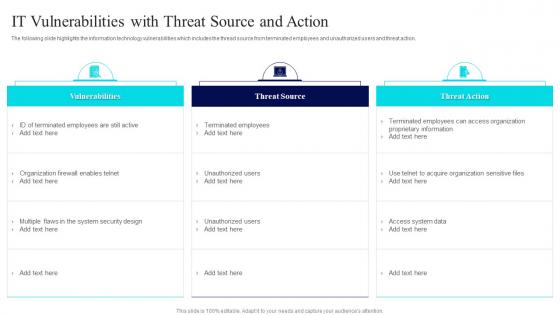 IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology Systems
IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology SystemsThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Vulnerabilities, Threat Source, Threat Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comprehensive Guide For Successful Types Of Website Security Threats And Vulnerabilities
Comprehensive Guide For Successful Types Of Website Security Threats And VulnerabilitiesFollowing slide exhibits types of security threats that negatively affect website operational efficiency and goodwill. It include types such as malware, viruses, spam links, DDoS with examples, impact and mitigation tools. Increase audience engagement and knowledge by dispensing information using Comprehensive Guide For Successful Types Of Website Security Threats And Vulnerabilities. This template helps you present information on three stages. You can also present information on Malware And Viruses, Spam Links, Denial Of Service Attacks, Website Security Threats, Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
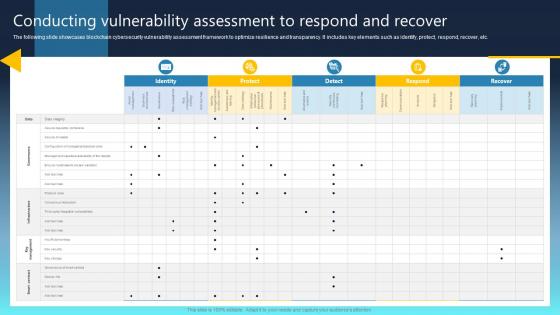 Ultimate Guide For Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS
Ultimate Guide For Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SSPresent the topic in a bit more detail with this Ultimate Guide For Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS Use it as a tool for discussion and navigation on Protect, Detect, Detect This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ultimate Guide For Blockchain Discovery Identifying Potential Vulnerabilities In System BCT SS
Ultimate Guide For Blockchain Discovery Identifying Potential Vulnerabilities In System BCT SSIncrease audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Discovery Identifying Potential Vulnerabilities In System BCT SS This template helps you present information on Three stages. You can also present information on Architecture Of Blockchain, Compliance Readiness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
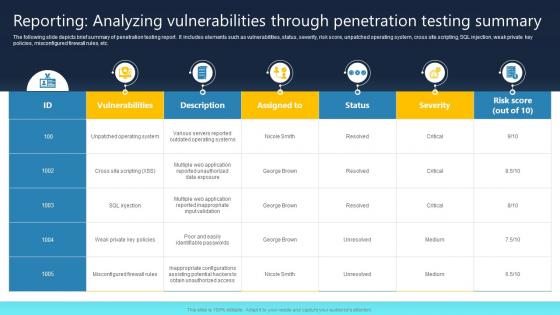 Ultimate Guide For Blockchain Reporting Analyzing Vulnerabilities Through Penetration BCT SS
Ultimate Guide For Blockchain Reporting Analyzing Vulnerabilities Through Penetration BCT SSThe following slide showcases some tips for consensus mechanism to ensure record of legitimate transactions. It includes elements such as proof of work PoW, proof of stake PoS, delegated PoS, resolving complicated puzzles, verifying transactions, sharing monetary risks, etc Increase audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Reporting Analyzing Vulnerabilities Through Penetration BCT SS This template helps you present information on Three stages. You can also present information on Unpatched Operating System, Weak Private Key Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Supply chain vulnerability ppt powerpoint presentation portfolio guide cpb
Supply chain vulnerability ppt powerpoint presentation portfolio guide cpbPresenting this set of slides with name Supply Chain Vulnerability Ppt Powerpoint Presentation Portfolio Guide Cpb. This is an editable Powerpoint one stages graphic that deals with topics like Supply Chain Vulnerability to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security vulnerability testing ppt powerpoint presentation gallery guide cpb
Security vulnerability testing ppt powerpoint presentation gallery guide cpbPresenting this set of slides with name Security Vulnerability Testing Ppt Powerpoint Presentation Gallery Guide Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Security Vulnerability Testing to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Computer vulnerabilities ppt powerpoint presentation file guide cpb
Computer vulnerabilities ppt powerpoint presentation file guide cpbPresenting this set of slides with name Computer Vulnerabilities Ppt Powerpoint Presentation File Guide Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Computer Vulnerabilities to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

