Powerpoint Templates and Google slides for Identify Cybersecurity Risks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Identifying A Cybersecurity Risk Training Ppt
Identifying A Cybersecurity Risk Training PptPresenting Identifying a Cybersecurity Risk. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Identifying Assets As A Step For Cybersecurity Risk Identification Training Ppt
Identifying Assets As A Step For Cybersecurity Risk Identification Training PptPresenting Identifying Assets as a Step for Cybersecurity Risk Identification. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Identifying Threats As A Step For Cybersecurity Risk Identification Training Ppt
Identifying Threats As A Step For Cybersecurity Risk Identification Training PptPresenting Identifying Threats as a Step for Cybersecurity Risk Identification. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Identifying Vulnerabilities As A Step For Cybersecurity Risk Identification Training Ppt
Identifying Vulnerabilities As A Step For Cybersecurity Risk Identification Training PptPresenting Identifying Vulnerabilities as a Step for Cybersecurity Risk Identification. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management
Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks ManagementThe following slide showcases the various types of cyber-attacks faced by employees to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service etc. Introducing Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Spear Phishing, Advanced Persistent Threats, Ransomware, Phishing, using this template. Grab it now to reap its full benefits.
-
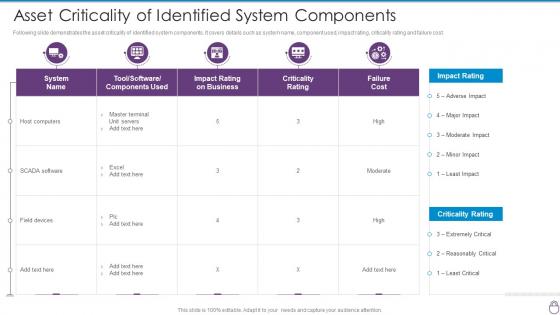 Cybersecurity Risk Management Framework Asset Criticality Of Identified System
Cybersecurity Risk Management Framework Asset Criticality Of Identified SystemFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Cybersecurity Risk Management Framework Asset Criticality Of Identified System. Use it as a tool for discussion and navigation on Criticality Rating, Failure Cost, Moderate, High. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
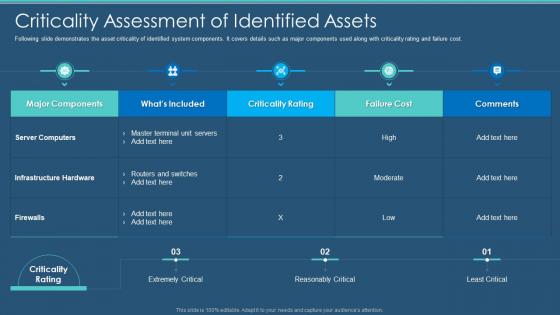 Cybersecurity Criticality Assessment Of Identified Assets Information Security Program
Cybersecurity Criticality Assessment Of Identified Assets Information Security ProgramFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost. Present the topic in a bit more detail with this Cybersecurity Criticality Assessment Of Identified Assets Information Security Program. Use it as a tool for discussion and navigation on Criticality Assessment Of Identified Assets. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity and digital business risk management criticality assessment of identified assets
Cybersecurity and digital business risk management criticality assessment of identified assetsFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost. Present the topic in a bit more detail with this Cybersecurity And Digital Business Risk Management Criticality Assessment Of Identified Assets. Use it as a tool for discussion and navigation on Assessment, Infrastructure, Components. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity Risk Analysis And Management Plan Identifying Employees For Information Security
Cybersecurity Risk Analysis And Management Plan Identifying Employees For Information SecurityThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner Deliver an outstanding presentation on the topic using this Cybersecurity Risk Analysis And Management Plan Identifying Employees For Information Security. Dispense information and present a thorough explanation of Identifying, Information, Training Programme using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identifying Information Security Threats And Impact Cybersecurity Risk Analysis And Management Plan
Identifying Information Security Threats And Impact Cybersecurity Risk Analysis And Management PlanThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization Present the topic in a bit more detail with this Identifying Information Security Threats And Impact Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Identifying, Information, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
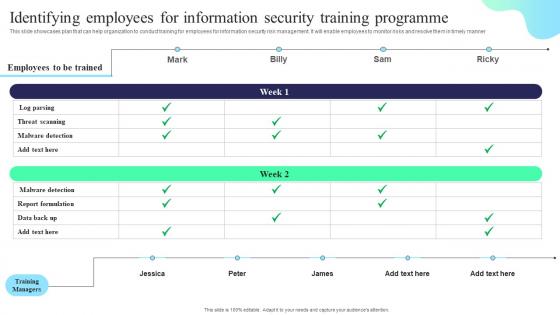 Identifying Employees For Information Security Training Formulating Cybersecurity Plan
Identifying Employees For Information Security Training Formulating Cybersecurity PlanThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner. Deliver an outstanding presentation on the topic using this Identifying Employees For Information Security Training Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Threat Scanning, Report Formulation, Training Programme using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identifying Information Security Threats And Impact Formulating Cybersecurity Plan
Identifying Information Security Threats And Impact Formulating Cybersecurity PlanThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Introducing Identifying Information Security Threats And Impact Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Errors And Omissions, Fraud And Theft, Employee Sabotage, using this template. Grab it now to reap its full benefits.
-
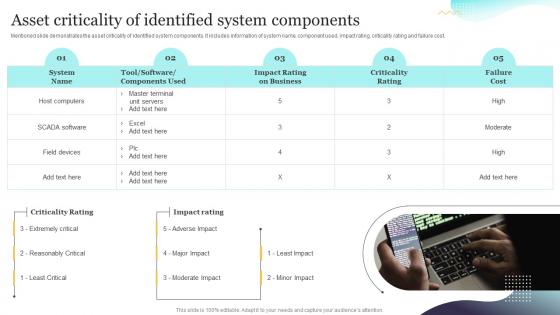 Asset Criticality Of Identified System Components Upgrading Cybersecurity With Incident Response Playbook
Asset Criticality Of Identified System Components Upgrading Cybersecurity With Incident Response PlaybookMentioned slide demonstrates the asset criticality of identified system components. It includes information of system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Asset Criticality Of Identified System Components Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Criticality, Information, Demonstrates. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
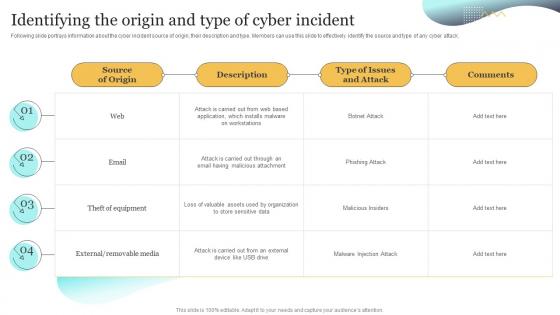 Identifying The Origin And Type Of Cyber Incident Upgrading Cybersecurity With Incident Response Playbook
Identifying The Origin And Type Of Cyber Incident Upgrading Cybersecurity With Incident Response PlaybookFollowing slide portrays information about the cyber incident source of origin, their description and type. Members can use this slide to effectively identify the source and type of any cyber attack. Present the topic in a bit more detail with this Identifying The Origin And Type Of Cyber Incident Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Effectively, Information, Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
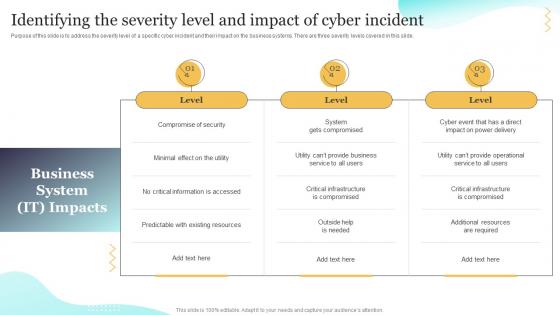 Identifying The Severity Level And Impact Upgrading Cybersecurity With Incident Response Playbook
Identifying The Severity Level And Impact Upgrading Cybersecurity With Incident Response PlaybookPurpose of this slide is to address the severity level of a specific cyber incident and their impact on the business systems. There are three severity levels covered in this slide. Deliver an outstanding presentation on the topic using this Identifying The Severity Level And Impact Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Identifying, Business, Severity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
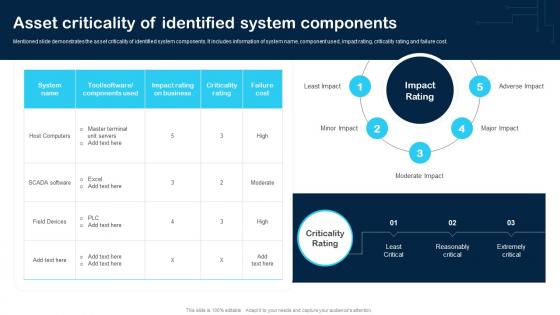 Asset Criticality Of Identified System Components Cybersecurity Incident And Vulnerability
Asset Criticality Of Identified System Components Cybersecurity Incident And VulnerabilityMentioned slide demonstrates the asset criticality of identified system components. It includes information of system name, component used, impact rating, criticality rating and failure cost. Deliver an outstanding presentation on the topic using this Asset Criticality Of Identified System Components Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Host Computers, SCADA Software, Field Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
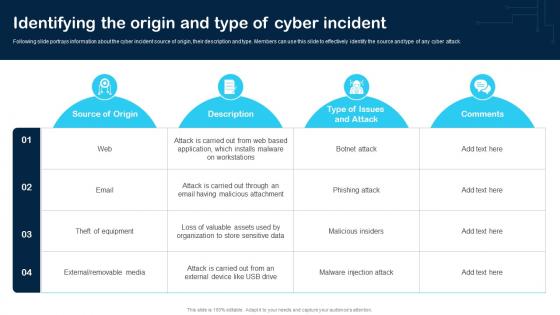 Identifying The Origin And Type Of Cyber Incident Cybersecurity Incident And Vulnerability
Identifying The Origin And Type Of Cyber Incident Cybersecurity Incident And VulnerabilityFollowing slide portrays information about the cyber incident source of origin, their description and type. Members can use this slide to effectively identify the source and type of any cyber attack. Deliver an outstanding presentation on the topic using this Identifying The Origin And Type Of Cyber Incident Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Web, Email, Removable Media using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
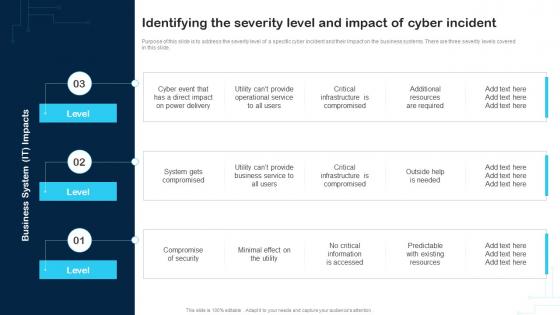 Identifying The Severity Level And Impact Of Cyber Incident Cybersecurity Incident And Vulnerability
Identifying The Severity Level And Impact Of Cyber Incident Cybersecurity Incident And VulnerabilityPurpose of this slide is to address the severity level of a specific cyber incident and their impact on the business systems. There are three severity levels covered in this slide. Introducing Identifying The Severity Level And Impact Of Cyber Incident Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Compromise Of Security, Service, Business System, using this template. Grab it now to reap its full benefits.
-
 Coder checking cybersecurity module to identify potential system risk
Coder checking cybersecurity module to identify potential system riskPresenting our set of slides with Coder Checking Cybersecurity Module To Identify Potential System Risk. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Coder Checking Cybersecurity Module To Identify Potential System Risk.

