Powerpoint Templates and Google slides for Malicious Crypto Mining
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
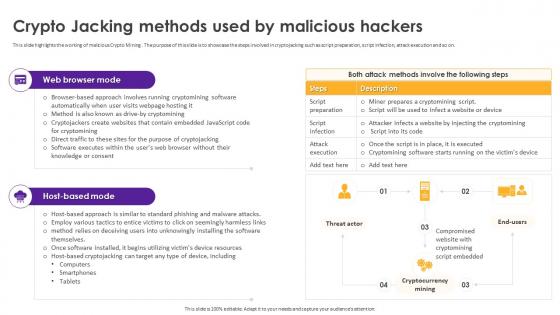 Cryptomining Innovations And Trends Crypto Jacking Methods Used By Malicious Hackers
Cryptomining Innovations And Trends Crypto Jacking Methods Used By Malicious HackersThis slide highlights the working of malicious Crypto Mining . The purpose of this slide is to showcase the steps involved in cryptojacking such as script preparation, script infection, attack execution and so on. Present the topic in a bit more detail with this Cryptomining Innovations And Trends Crypto Jacking Methods Used By Malicious Hackers. Use it as a tool for discussion and navigation on Crypto Jacking Methods, Malicious Hackers, Compromised Website, Cryptomining Script Embedded. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cryptomining Innovations And Trends About Malicious Crypto Mining Overview And Impacts
Cryptomining Innovations And Trends About Malicious Crypto Mining Overview And ImpactsThis slide represents the Crypto Mining malware. The purpose of this slide is to showcase how it affects the victim, such as by gaining unauthorized use of computer power, impact on device owner, exploitation of web browsers and mobile apps, etc. Increase audience engagement and knowledge by dispensing information using Cryptomining Innovations And Trends About Malicious Crypto Mining Overview And Impacts. This template helps you present information on three stages. You can also present information on Unauthorized Use Of Computing Power, Impact On Device Owners, Concealed Nature Of Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cryptomining Innovations And Trends Possible Methods To Detect Malicious Crypto Mining
Cryptomining Innovations And Trends Possible Methods To Detect Malicious Crypto MiningThis slide highlights the symptoms used to detect Cryptojacking. The purpose of this slide is to showcase possible indicators, such as poor system performance, overheating, high electricity costs, sudden Central Processor Unit CPU usage spikes, and more. Deliver an outstanding presentation on the topic using this Cryptomining Innovations And Trends Possible Methods To Detect Malicious Crypto Mining. Dispense information and present a thorough explanation of Poor System Performance, Overheating, High Electricity Costs, Central Processor Unit using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
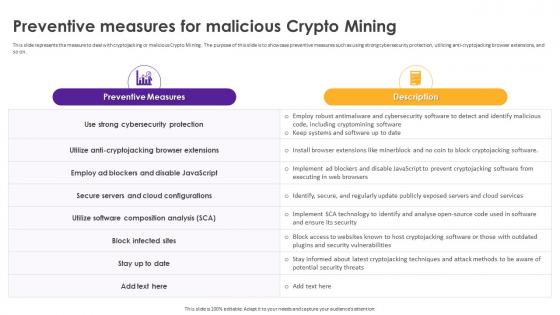 Cryptomining Innovations And Trends Preventive Measures For Malicious Crypto Mining
Cryptomining Innovations And Trends Preventive Measures For Malicious Crypto MiningThis slide represents the measure to deal with cryptojacking or malicious Crypto Mining. The purpose of this slide is to showcase preventive measures such as using strong cybersecurity protection, utilizing anti-cryptojacking browser extensions, and so on. Present the topic in a bit more detail with this Cryptomining Innovations And Trends Possible Methods To Detect Malicious Crypto Mining. Use it as a tool for discussion and navigation on Block Infected Sites, Strong Cybersecurity Protection, Secure Servers And Cloud Configurations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cryptomining Innovations And Trends Real World Examples Of Malicious Crypto Mining
Cryptomining Innovations And Trends Real World Examples Of Malicious Crypto MiningThis slide highlights the different examples of cryptojacking. The purpose of this slide is to showcase cryptojacking examples such as Prometei, PowerGhost, Graboid, MinerGAre malware, and so on. Present the topic in a bit more detail with this Cryptomining Innovations And Trends Real World Examples Of Malicious Crypto Mining. Use it as a tool for discussion and navigation on Minergate Malware, Malicious Crypto Mining, Legitimate Windows Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
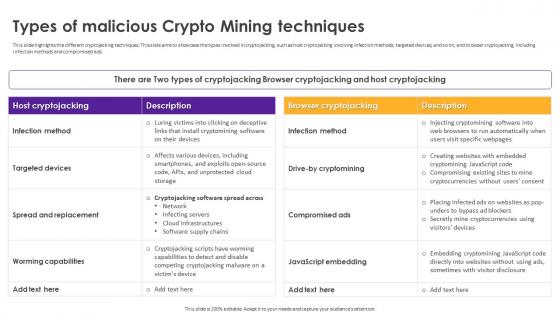 Cryptomining Innovations And Trends Types Of Malicious Crypto Mining Techniques
Cryptomining Innovations And Trends Types Of Malicious Crypto Mining TechniquesThis slide highlights the different cryptojacking techniques. This slide aims to showcase the types involved in cryptojacking, such as host cryptojacking involving infection methods, targeted devices, and so on, and browser cryptojacking, including infection methods and compromised ads. Present the topic in a bit more detail with this Cryptomining Innovations And Trends Types Of Malicious Crypto Mining Techniques. Use it as a tool for discussion and navigation on Spread And Replacement, Compromised Ads, Infection Method, Targeted Devices. This template is free to edit as deemed fit for your organization. Therefore download it now.

