Powerpoint Templates and Google slides for Mitigation Cyber Attacks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Implementing Strategies To Mitigate Cyber Security Threats Powerpoint Presentation Slides
Implementing Strategies To Mitigate Cyber Security Threats Powerpoint Presentation SlidesDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Implementing Strategies To Mitigate Cyber Security Threats Powerpoint Presentation Slides is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the sixty slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Cyber Risk Assessment And Mitigation Planning Complete Deck
Cyber Risk Assessment And Mitigation Planning Complete DeckDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Cyber Risk Assessment And Mitigation Planning Complete Deck is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the sixty slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Cyber Attack Risks Mitigation Strategies Powerpoint Ppt Template Bundles DK MD
Cyber Attack Risks Mitigation Strategies Powerpoint Ppt Template Bundles DK MDIf you require a professional template with great design, then this Cyber Attack Risks Mitigation Strategies Powerpoint Ppt Template Bundles DK MD is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using eighteen slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 Blockchain Cyber Security Issues And Risk Mitigation Powerpoint Ppt Template Bundles BCT MM
Blockchain Cyber Security Issues And Risk Mitigation Powerpoint Ppt Template Bundles BCT MMIf you require a professional template with great design, then this Blockchain Cyber Security Issues And Risk Mitigation Powerpoint Ppt Template Bundles BCT MM is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using thirteen slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Cyber Phishing Attacks Tracking Dashboard
Phishing Attacks And Strategies To Mitigate Them V2 Cyber Phishing Attacks Tracking DashboardThis slide represents the dashboard to track cyber phishing attacks. The purpose of this slide is to provide a graphical representation of cyber attacks occurred in a specific time span. It also depicts the organizations health risk. Deliver an outstanding presentation on the topic using this Phishing Attacks And Strategies To Mitigate Them V2 Cyber Phishing Attacks Tracking Dashboard. Dispense information and present a thorough explanation of Dashboard To Track, Cyber Phishing Attacks, Graphical Representation, Specific Time Span, Organizations Health Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Supplier Cybersecurity Risk Mitigation Strategy Supplier Risk Management
Impact Of Supplier Cybersecurity Risk Mitigation Strategy Supplier Risk ManagementThis slide showcase impact of supplier cybersecurity risk mitigation strategy. This template includes elements such as decrease in compliance risk cases and data breaches cases, increase in productivity level etc. Present the topic in a bit more detail with this Impact Of Supplier Cybersecurity Risk Mitigation Strategy Supplier Risk Management. Use it as a tool for discussion and navigation on Data Breaches, Service Disruption, Risk Mitigation Strategy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Impact Of Phishing Cyber Scams On Organizations
Phishing Attacks And Strategies To Mitigate Them V2 Impact Of Phishing Cyber Scams On OrganizationsThis slide talks about the damage caused by phishing attacks. The purpose of this slide is to explain the impact of phishing scams on organizations. The key points included are information loss, damaged credibility, direct financial loss and productivity loss. Increase audience engagement and knowledge by dispensing information using Phishing Attacks And Strategies To Mitigate Them V2 Impact Of Phishing Cyber Scams On Organizations. This template helps you present information on four stages. You can also present information on Direct Financial Loss, Productivity Loss, Damaged Credibility, Phishing Cyber Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
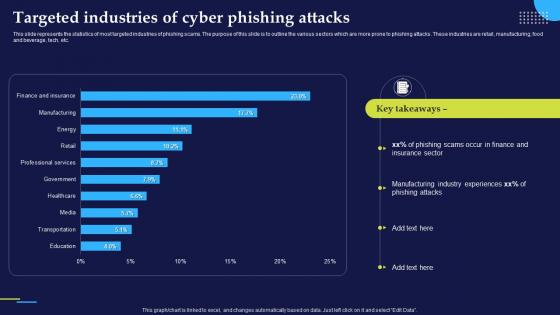 Phishing Attacks And Strategies To Mitigate Them V2 Targeted Industries Of Cyber Phishing Attacks
Phishing Attacks And Strategies To Mitigate Them V2 Targeted Industries Of Cyber Phishing AttacksThis slide represents the statistics of most targeted industries of phishing scams. The purpose of this slide is to outline the various sectors which are more prone to phishing attacks. These industries are retail, manufacturing, food and beverage, tech, etc. Deliver an outstanding presentation on the topic using this Phishing Attacks And Strategies To Mitigate Them V2 Targeted Industries Of Cyber Phishing Attacks. Dispense information and present a thorough explanation of Phishing Scams, Phishing Attacks, Manufacturing, Food And Beverage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Vishing Cyber Scams In Different Businesses
Phishing Attacks And Strategies To Mitigate Them V2 Vishing Cyber Scams In Different BusinessesThis slide demonstrates the various types of vishing scams. The purpose of this slide is to illustrate the ways in which attackers conduct scams in different businesses using vishing technique. These are banking vishing and internal revenue service vishing. Present the topic in a bit more detail with this Phishing Attacks And Strategies To Mitigate Them V2 Vishing Cyber Scams In Different Businesses. Use it as a tool for discussion and navigation on Attackers Conduct Scams, Vishing Technique, Internal Revenue Service Vishing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
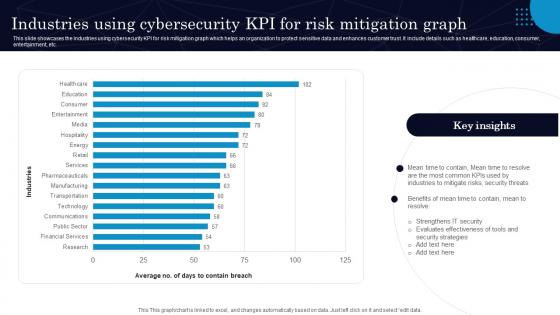 Industries Using Cybersecurity Kpi For Risk Mitigation Graph
Industries Using Cybersecurity Kpi For Risk Mitigation GraphThis slide showcases the industries using cybersecurity KPI for risk mitigation graph which helps an organization to protect sensitive data and enhances customer trust. It include details such as healthcare, education, consumer, entertainment, etc. Presenting our well structured Industries Using Cybersecurity Kpi For Risk Mitigation Graph. The topics discussed in this slide are Mitigate Risks, Security Threats.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
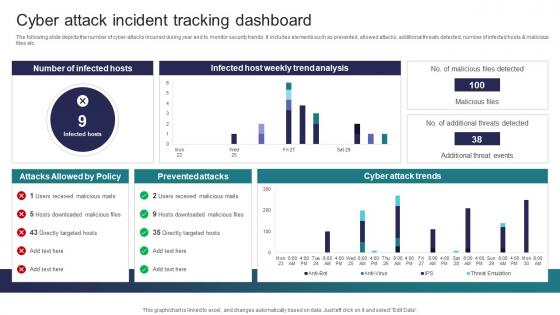 Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security Threats
Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the number of cyber attacks incurred during year end to monitor security trends. It includes elements such as prevented, allowed attacks, additional threats detected, number of infected hosts and malicious files etc. Present the topic in a bit more detail with this Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Prevented Attacks, Cyber Attack Trends This template is free to edit as deemed fit for your organization. Therefore download it now.
-
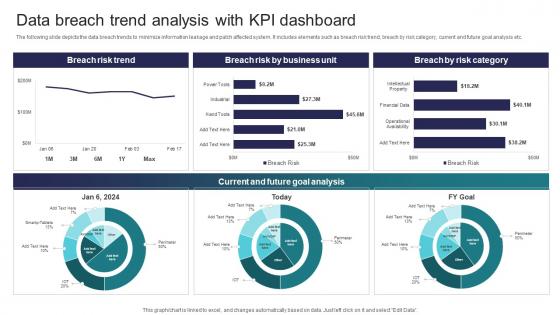 Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security Threats
Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the data breach trends to minimize information leakage and patch affected system. It includes elements such as breach risk trend, breach by risk category, current and future goal analysis etc. Present the topic in a bit more detail with this Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Current And Future Goal Analysis, Breach Risk Trend This template is free to edit as deemed fit for your organization. Therefore download it now.
-
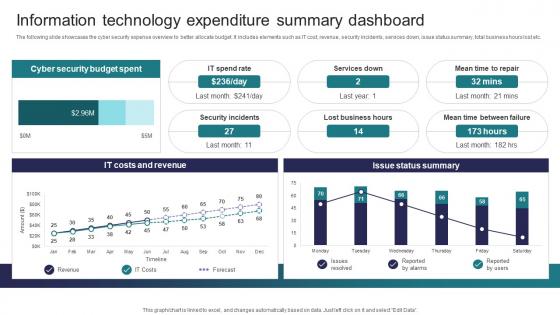 Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security Threats
Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the cyber security expense overview to better allocate budget. It includes elements such as IT cost, revenue, security incidents, services down, issue status summary, total business hours lost etc. Deliver an outstanding presentation on the topic using this Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Cyber Security Budget Spent, It Costs And Revenue, Issue Status Summary using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
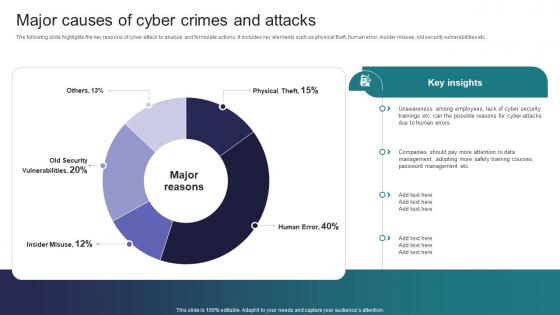 Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security Threats
Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights the key reasons of cyber attack to analyze and formulate actions. It includes key elements such as physical theft, human error, insider misuse, old security vulnerabilities etc. Deliver an outstanding presentation on the topic using this Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Employees, Management, Training Courses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
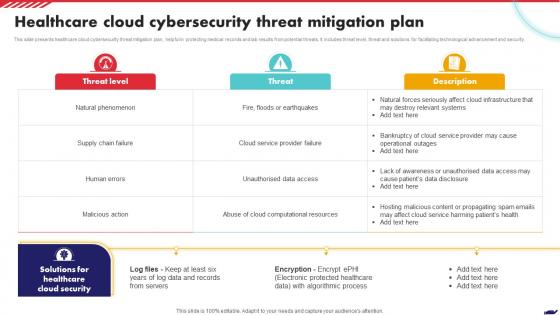 Healthcare Cloud Cybersecurity Threat Mitigation Plan
Healthcare Cloud Cybersecurity Threat Mitigation PlanThis slide presents healthcare cloud cybersecurity threat mitigation plan, helpful in protecting medical records and lab results from potential threats. It includes threat level, threat and solutions for facilitating technological advancement and security. Presenting our well structured Healthcare Cloud Cybersecurity Threat Mitigation Plan. The topics discussed in this slide are Healthcare Cloud Security, Threat Level, Algorithmic Process. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Action Plan To Combat Cyber Crimes Strategic Plan To Mitigate Cyber Attacks
Action Plan To Combat Cyber Crimes Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Deliver an outstanding presentation on the topic using this Action Plan To Combat Cyber Crimes Strategic Plan To Mitigate Cyber Attacks. Dispense information and present a thorough explanation of Risk Mitigation Plan, Multiple Cyber Attacks, Mitigation Approach using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Compressive Planning Guide Strategic Plan To Mitigate Cyber Attacks
Compressive Planning Guide Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Deliver an outstanding presentation on the topic using this Compressive Planning Guide Strategic Plan To Mitigate Cyber Attacks. Dispense information and present a thorough explanation of Strategic Plan, Mitigate Cyber Attacks, Risk Mitigation Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
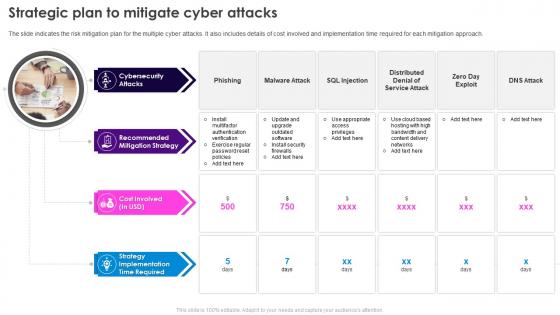 Security Plan To Prevent Cyber Strategic Plan To Mitigate Cyber Attacks
Security Plan To Prevent Cyber Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Increase audience engagement and knowledge by dispensing information using Security Plan To Prevent Cyber Strategic Plan To Mitigate Cyber Attacks. This template helps you present information on four stages. You can also present information on Cybersecurity Attacks, Recommended Mitigation Strategy, Strategy Implementation Time Required using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cybersecurity Risks Mitigation Strategy For Compliance Risk Supplier Risk Management
Cybersecurity Risks Mitigation Strategy For Compliance Risk Supplier Risk ManagementThis slide showcases cybersecurity risks mitigation strategy for compliance risk. This template includes strategies such as perform a risk assessment, develop incident response plan, visualize the attack surface etc. Deliver an outstanding presentation on the topic using this Cybersecurity Risks Mitigation Strategy For Compliance Risk Supplier Risk Management. Dispense information and present a thorough explanation of Mitigation Strategies, Strategy Description, Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
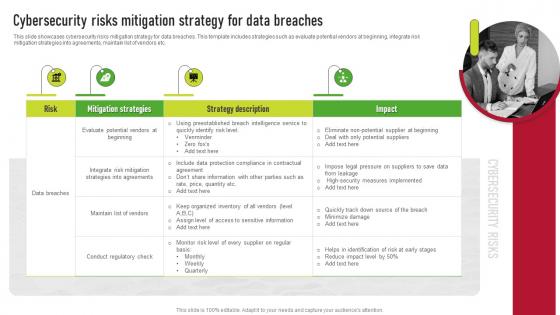 Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk Management
Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk ManagementThis slide showcases cybersecurity risks mitigation strategy for data breaches. This template includes strategies such as evaluate potential vendors at beginning, integrate risk mitigation strategies into agreements, maintain list of vendors etc. Introducing Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Mitigation Strategies, Strategy Description, Risk, using this template. Grab it now to reap its full benefits.
-
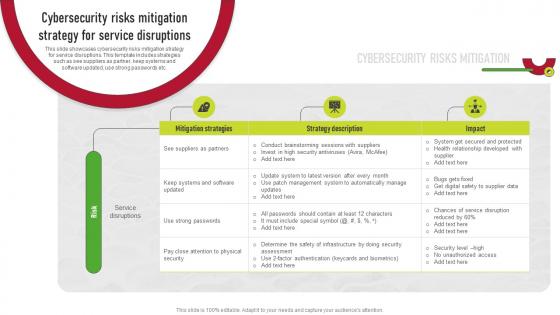 Cybersecurity Risks Mitigation Strategy For Service Disruptions Supplier Risk Management
Cybersecurity Risks Mitigation Strategy For Service Disruptions Supplier Risk ManagementThis slide showcases cybersecurity risks mitigation strategy for service disruptions. This template includes strategies such as see suppliers as partner, keep systems and software updated, use strong passwords etc. Present the topic in a bit more detail with this Cybersecurity Risks Mitigation Strategy For Service Disruptions Supplier Risk Management. Use it as a tool for discussion and navigation on Mitigation Strategies, Strategy Description, Service Disruptions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Different Types Of Smishing Cyber Scams
Phishing Attacks And Strategies To Mitigate Them V2 Different Types Of Smishing Cyber ScamsThis slide talks about the various types of smishing cyber attacks. The purpose of this slide is to briefly explain different techniques of smishing scams used by the attackers to scam users. These are covid-19 smishing, financial services smishing, etc. Introducing Phishing Attacks And Strategies To Mitigate Them V2 Different Types Of Smishing Cyber Scams to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Smishing Scams, Financial Services Smishing, Gift Smishing, Customer Support Smishing, using this template. Grab it now to reap its full benefits.
-
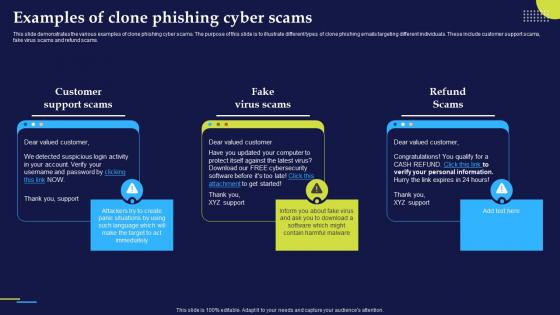 Phishing Attacks And Strategies To Mitigate Them V2 Examples Of Clone Phishing Cyber Scams
Phishing Attacks And Strategies To Mitigate Them V2 Examples Of Clone Phishing Cyber ScamsThis slide demonstrates the various examples of clone phishing cyber scams. The purpose of this slide is to illustrate different types of clone phishing emails targeting different individuals. These include customer support scams, fake virus scams and refund scams. Increase audience engagement and knowledge by dispensing information using Phishing Attacks And Strategies To Mitigate Them V2 Examples Of Clone Phishing Cyber Scams. This template helps you present information on three stages. You can also present information on Customer Support Scams, Fake Virus Scams, Refund Scams, Clone Phishing Cyber Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Execution Of Man In The Middle Cyber Attacks
Phishing Attacks And Strategies To Mitigate Them V2 Execution Of Man In The Middle Cyber AttacksThis slide illustrates the process of executing man-in-the-middle cyber attacks. The purpose of this slide is to outline the two stages of execution of MITM scams. These stages are interception and decryption. Present the topic in a bit more detail with this Phishing Attacks And Strategies To Mitigate Them V2 Execution Of Man In The Middle Cyber Attacks. Use it as a tool for discussion and navigation on Cyber Attacks, Interception And Decryption, Online Data Transfer, Intercepting User Traffic. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
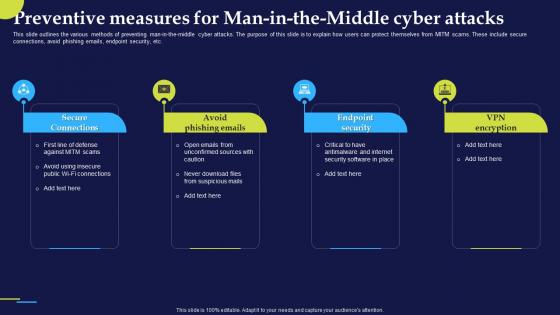 Phishing Attacks And Strategies To Mitigate Them V2 Preventive Measures For Man In The Middle Cyber
Phishing Attacks And Strategies To Mitigate Them V2 Preventive Measures For Man In The Middle CyberThis slide outlines the various methods of preventing man-in-the-middle cyber attacks. The purpose of this slide is to explain how users can protect themselves from MITM scams. These include secure connections, avoid phishing emails, endpoint security, etc. Introducing Phishing Attacks And Strategies To Mitigate Them V2 Preventive Measures For Man In The Middle Cyber to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Secure Connections, Avoid Phishing Emails, Endpoint Security, Cyber Attacks, using this template. Grab it now to reap its full benefits.
-
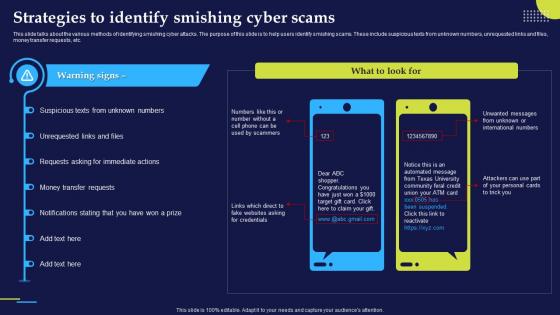 Phishing Attacks And Strategies To Mitigate Them V2 Strategies To Identify Smishing Cyber Scams
Phishing Attacks And Strategies To Mitigate Them V2 Strategies To Identify Smishing Cyber ScamsThis slide talks about the various methods of identifying smishing cyber attacks. The purpose of this slide is to help users identify smishing scams. These include suspicious texts from unknown numbers, unrequested links and files, money transfer requests, etc. Present the topic in a bit more detail with this Phishing Attacks And Strategies To Mitigate Them V2 Strategies To Identify Smishing Cyber Scams. Use it as a tool for discussion and navigation on Smishing Cyber Attacks, Smishing Scams, Unrequested Links And Files, Money Transfer Requests. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 K101 Different Types Of Vishing Cyber Attacks Phishing Attacks And Strategies To Mitigate Them V2
K101 Different Types Of Vishing Cyber Attacks Phishing Attacks And Strategies To Mitigate Them V2This slide talks about the various types of vishing cyber attacks. The purpose of this slide is to briefly explain different techniques of vishing scams used by the attackers to scam users. These are caller ID spoofing, dumpster diving, wardialing, etc. Increase audience engagement and knowledge by dispensing information using K101 Different Types Of Vishing Cyber Attacks Phishing Attacks And Strategies To Mitigate Them V2. This template helps you present information on four stages. You can also present information on Security And It Infrastructure, Voice Over Internet Protocol, Transmission Of Voice, Phishing Attack Victims using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 K107 Working Process Of Cyber Phishing Attacks Phishing Attacks And Strategies To Mitigate Them V2
K107 Working Process Of Cyber Phishing Attacks Phishing Attacks And Strategies To Mitigate Them V2This slide talks about the implementation and working of phishing attacks. The purpose of this slide is to explain how are cyber phishing scams conducted. The components include hacker, phishing mail, target, phishing website and original website. Introducing K107 Working Process Of Cyber Phishing Attacks Phishing Attacks And Strategies To Mitigate Them V2 to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Working Process, Cyber Phishing Attacks, Phishing Website, Cyber Phishing Scams Conducted, using this template. Grab it now to reap its full benefits.
-
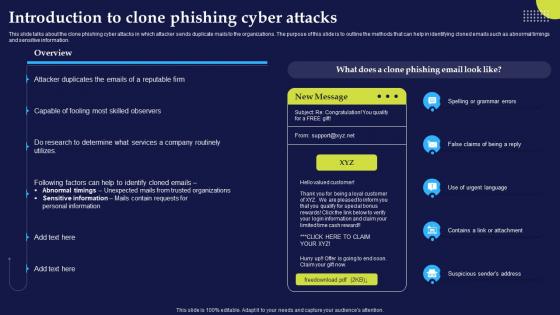 K111 Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies To Mitigate Them V2
K111 Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies To Mitigate Them V2This slide talks about the clone phishing cyber attacks in which attacker sends duplicate mails to the organizations. The purpose of this slide is to outline the methods that can help in identifying cloned emails such as abnormal timings and sensitive information. Deliver an outstanding presentation on the topic using this K111 Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies To Mitigate Them V2. Dispense information and present a thorough explanation of Spelling Or Grammar Errors, Suspicious Senders Address, Clone Phishing Cyber Attacks, Routinely Utilizes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Financial Cyber Threat Mitigation AI Image PowerPoint Presentation PPT ECS
Financial Cyber Threat Mitigation AI Image PowerPoint Presentation PPT ECSIntroducing a Visual PPT on Financial Cyber Threat Mitigation. Each PowerPoint Slide has been thoughtfully designed by our team of Presentation Specialists. Adjusting the content is simple, whether you want to add or eliminate details. Plus, this PPT Template can be used on any screen size and is even Google Slides friendly. Grab the PPT, customize to your preference, and present with self assurance.
-
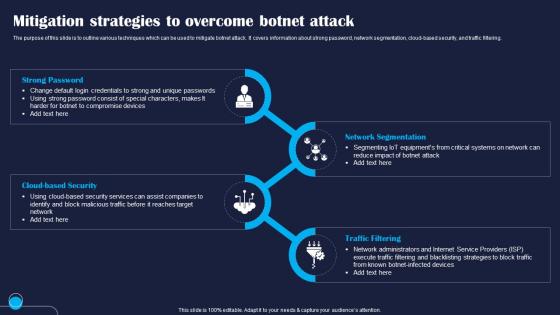 Mitigation Strategies To Overcome Improving IoT Device Cybersecurity IoT SS
Mitigation Strategies To Overcome Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline various techniques which can be used to mitigate botnet attack. It covers information about strong password, network segmentation, cloud based security, and traffic filtering. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Overcome Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Strong, Security, Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigation Strategies To Overcome IoT Improving IoT Device Cybersecurity IoT SS
Mitigation Strategies To Overcome IoT Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase multiple techniques which can be used to overcome security breach caused by Verkada hack. The strategies mentioned in slide are regular security audit, secure authentication, firmware update, and encryption. Introducing Mitigation Strategies To Overcome IoT Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Continuous, Authentication, Encryption, using this template. Grab it now to reap its full benefits.
-
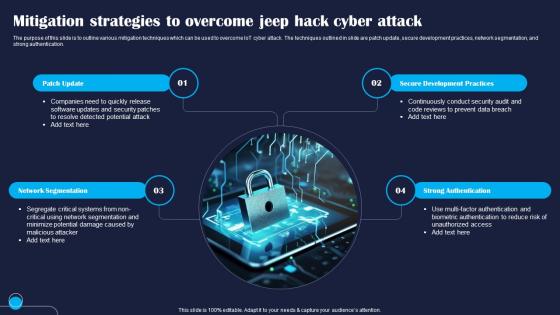 Mitigation Strategies To Overcome Jeep Hack Improving IoT Device Cybersecurity IoT SS
Mitigation Strategies To Overcome Jeep Hack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline various mitigation techniques which can be used to overcome IoT cyber attack. The techniques outlined in slide are patch update, secure development practices, network segmentation, and strong authentication. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Overcome Jeep Hack Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Patch, Segmentation, Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigation Strategies To Overcome Stuxnet Improving IoT Device Cybersecurity IoT SS
Mitigation Strategies To Overcome Stuxnet Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight different mitigation techniques which can be used by companies to Internet of Things IoT security vulnerability. It covers information about strong access controls, security testing, user training, and robust security response plan. Introducing Mitigation Strategies To Overcome Stuxnet Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strong, Security, Incident, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Risks Mitigation With Serverless Computing V2
Cybersecurity Risks Mitigation With Serverless Computing V2This slide talks about some ways that a serverless system can help reduce the attack surface by minimizing the number of attack vectors. These include reduced infrastructure, access control restrictions, stateless computing, and auto-scaling. Increase audience engagement and knowledge by dispensing information using Cybersecurity Risks Mitigation With Serverless Computing V2. This template helps you present information on four stages. You can also present information on Reduced Infrastructure, Access Control Restrictions, Stateless Computing, Serverless Computing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Risk Mitigation Strategy Action Plan Icon
Cyber Security Risk Mitigation Strategy Action Plan IconIntroducing our premium set of slides with Cyber Security Risk Mitigation Strategy Action Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Mitigation, Strategy, Action. So download instantly and tailor it with your information.
-
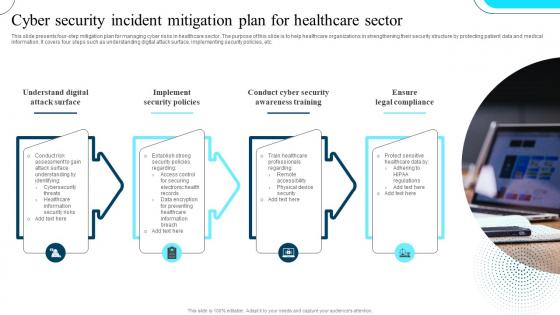 Cyber Security Incident Mitigation Plan For Healthcare Sector
Cyber Security Incident Mitigation Plan For Healthcare SectorThis slide presents four-step mitigation plan for managing cyber risks in healthcare sector. The purpose of this slide is to help healthcare organizations in strengthening their security structure by protecting patient data and medical information. It covers four steps such as understanding digital attack surface, implementing security policies, etc. Introducing our premium set of slides with Cyber Security Incident Mitigation Plan For Healthcare Sector Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Attack Surface,Security Policies,Awareness Training. So download instantly and tailor it with your information.
-
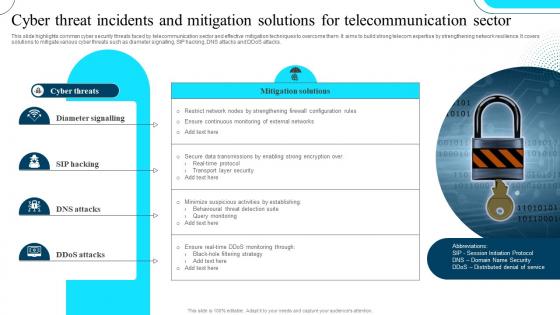 Cyber Threat Incidents And Mitigation Solutions For Telecommunication Sector
Cyber Threat Incidents And Mitigation Solutions For Telecommunication SectorThis slide highlights common cyber security threats faced by telecommunication sector and effective mitigation techniques to overcome them. It aims to build strong telecom expertise by strengthening network resilience. It covers solutions to mitigate various cyber threats such as diameter signalling, SIP hacking, DNS attacks and DDoS attacks. Presenting our set of slides with Cyber Threat Incidents And Mitigation Solutions For Telecommunication Sector This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Diameter Signalling, SIP Hacking, DNS Attacks
-
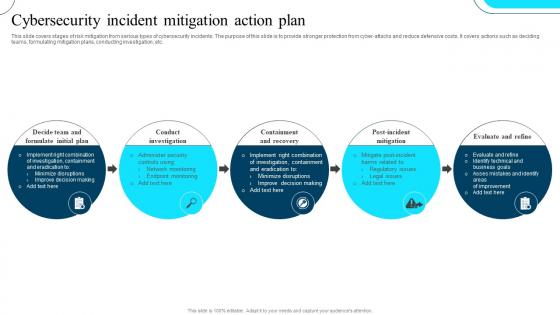 Cybersecurity Incident Mitigation Action Plan
Cybersecurity Incident Mitigation Action PlanThis slide covers stages of risk mitigation from serious types of cybersecurity incidents. The purpose of this slide is to provide stronger protection from cyber-attacks and reduce defensive costs. It covers actions such as deciding teams, formulating mitigation plans, conducting investigation, etc. Introducing our premium set of slides with Cybersecurity Incident Mitigation Action Plan Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Formulate Initial Plan, Conduct Investigation, Containment And Recovery. So download instantly and tailor it with your information.
-
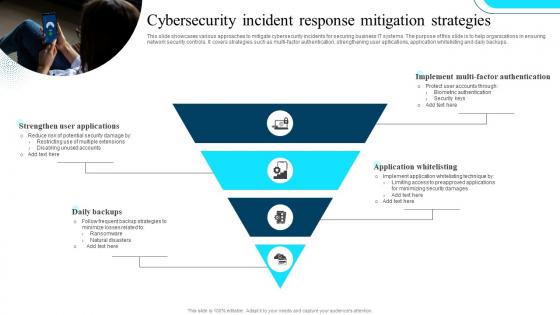 Cybersecurity Incident Response Mitigation Strategies
Cybersecurity Incident Response Mitigation StrategiesThis slide showcases various approaches to mitigate cybersecurity incidents for securing business IT systems. The purpose of this slide is to help organizations in ensuring network security controls. It covers strategies such as multi-factor authentication, strengthening user apllications, application whitelisting and daily backups. Presenting our set of slides with Cybersecurity Incident Response Mitigation Strategies This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strengthen User Applications, Daily Backups, Application Whitelisting.
-
 Icon For Cyber Security Incident Mitigation
Icon For Cyber Security Incident MitigationPresenting our set of slides with Icon For Cyber Security Incident Mitigation This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon For Cyber Security Incident Mitigation.
-
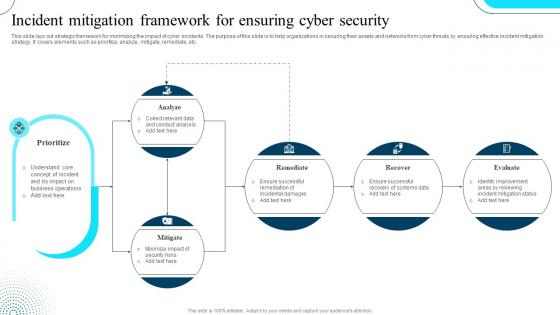 Incident Mitigation Framework For Ensuring Cyber Security
Incident Mitigation Framework For Ensuring Cyber SecurityThis slide lays out strategic framework for minimizing the impact of cyber incidents. The purpose of this slide is to help organizations in securing their assets and networks from cyber threats by ensuring effective incident mitigation strategy. It covers elements such as prioritize, analyze, mitigate, remediate, etc. Introducing our Incident Mitigation Framework For Ensuring Cyber Security set of slides. The topics discussed in these slides are Assess, Manage, Record. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Incident Mitigation Strategies For Cyber Risks In Finance Industry
Incident Mitigation Strategies For Cyber Risks In Finance IndustryThis slide shows strategic techniques to mitigate cyber security risks in finance industry. The purpose of this slide is to strengthen security of financial sector by protecting its complex IT infrastructure and digital assets. It covers strategies such as threat intelligence, external asset protection, brand abuse scanning and dark web monitoring. Presenting our set of slides with Incident Mitigation Strategies For Cyber Risks In Finance Industry This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Mean Time To Detect, Mean Time To Resolve, Incident Escalation Rate.
-
 Ransomware Incident Mitigation Icon For Ensuring Cyber Security
Ransomware Incident Mitigation Icon For Ensuring Cyber SecurityIntroducing our premium set of slides with Ransomware Incident Mitigation Icon For Ensuring Cyber Security Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ransomware Incident Mitigation, Icon For Ensuring Cyber Security. So download instantly and tailor it with your information.
-
 Saas Cyber Security Icon For Threat Mitigation
Saas Cyber Security Icon For Threat MitigationIntroducing our premium set of slides with Saas Cyber Security Icon For Threat Mitigation Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Saas Cyber Security Icon, Threat Mitigation. So download instantly and tailor it with your information.
-
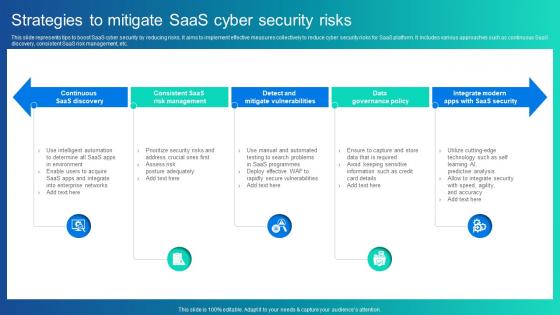 Strategies To Mitigate Saas Cyber Security Risks
Strategies To Mitigate Saas Cyber Security RisksThis slide represents tips to boost SaaS cyber security by reducing risks. It aims to implement effective measures collectively to reduce cyber security risks for SaaS platform. It includes various approaches such as continuous SaaS discovery, consistent SaaS risk management, etc. Introducing our premium set of slides with Strategies To Mitigate Saas Cyber Security Risks Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Continuous Saas Discovery, Risk Management, Mitigate Vulnerabilities. So download instantly and tailor it with your information.
-
 Agenda Implementing Strategies To Mitigate Cyber Security Threats
Agenda Implementing Strategies To Mitigate Cyber Security ThreatsIntroducing Agenda Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Security Awareness, Risk Management Process, Cyber Risk using this template. Grab it now to reap its full benefits.
-
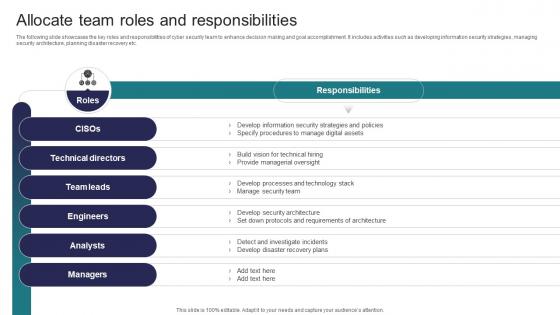 Allocate Team Roles And Responsibilities Implementing Strategies To Mitigate Cyber Security Threats
Allocate Team Roles And Responsibilities Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the key roles and responsibilities of cyber security team to enhance decision making and goal accomplishment. It includes activities such as developing information security strategies, managing security architecture, planning disaster recovery etc. Deliver an outstanding presentation on the topic using this Allocate Team Roles And Responsibilities Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Technical Directors, Team Leads, Engineers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Analyse And Rank Impact Of Cyber Threat Implementing Strategies To Mitigate Cyber Security Threats
Analyse And Rank Impact Of Cyber Threat Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights the prioritization of cyber security threats to minimize possibility of likelihood and severity. It mainly includes elements such as vulnerability, threat, source, likelihood, impact and ranking etc. Present the topic in a bit more detail with this Analyse And Rank Impact Of Cyber Threat Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Vulnerability, Threat, Threat Source This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Analyse Impact Of Cyber Attack On Valuable Implementing Strategies To Mitigate Cyber Security Threats
Analyse Impact Of Cyber Attack On Valuable Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the consequences of data breach threats to prevent information leakage. It mainly includes elements such as impact on revenue, protection cost, liability if lost, weightage criteria, asset importance etc. Deliver an outstanding presentation on the topic using this Analyse Impact Of Cyber Attack On Valuable Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Criteria, Impact On Revenue, Protection Cost using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security Threats
Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti virus, preventing to open suspicious emails, keeping systems up to date etc. Introducing Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Leverage Firewalls, Prevent Opening Suspicious Emails using this template. Grab it now to reap its full benefits.
-
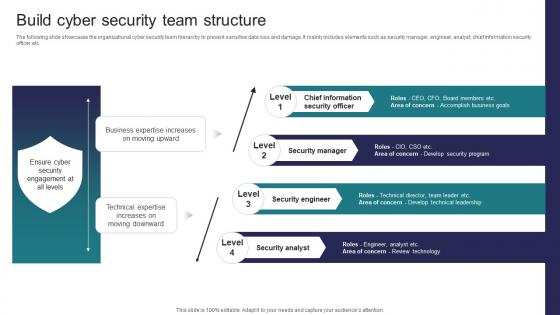 Build Cyber Security Team Structure Implementing Strategies To Mitigate Cyber Security Threats
Build Cyber Security Team Structure Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the organizational cyber security team hierarchy to prevent sensitive data loss and damage. It mainly includes elements such as security manager, engineer, analyst, chief information security officer etc Increase audience engagement and knowledge by dispensing information using Build Cyber Security Team Structure Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on four stages. You can also present information on Security Manager, Security Engineer, Security Analyst using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security Threats
Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts some major assets that are more prone to cyber attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Present the topic in a bit more detail with this Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Sales Record, Customer Database, Product Database This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Conduct Third Party Risk Assessment Implementing Strategies To Mitigate Cyber Security Threats
Conduct Third Party Risk Assessment Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates checklist to evaluate third party risk assessment to eliminate unnecessary threats. It includes elements such as cyber security policies, patch management process, physical security guidelines, information safety etc. Deliver an outstanding presentation on the topic using this Conduct Third Party Risk Assessment Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Parameters, Response, Status using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
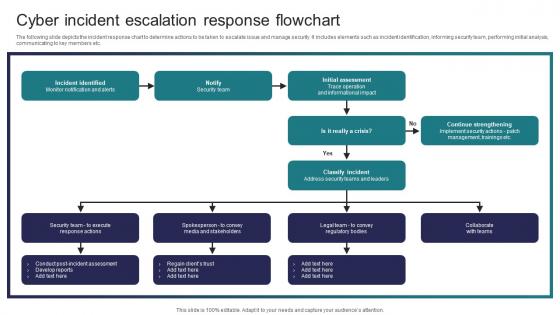 Cyber Incident Escalation Response Flowchart Implementing Strategies To Mitigate Cyber Security Threats
Cyber Incident Escalation Response Flowchart Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the incident response chart to determine actions to be taken to escalate issue and manage security. It includes elements such as incident identification, informing security team, performing initial analysis, communicating to key members etc. Deliver an outstanding presentation on the topic using this Cyber Incident Escalation Response Flowchart Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Incident Identified, Initial Assessment, Classify Incident using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Awareness Facts And Statistics Implementing Strategies To Mitigate Cyber Security Threats
Cyber Security Awareness Facts And Statistics Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases some facts and figures to generate awareness about cyber crimes. It includes elements such as hike in ransomware attacks, more employees are expected to be target of malware attacks, increasing cost of data breaches etc Introducing Cyber Security Awareness Facts And Statistics Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Malware Attacks, Employees, Social Engineering Attacks using this template. Grab it now to reap its full benefits.
-
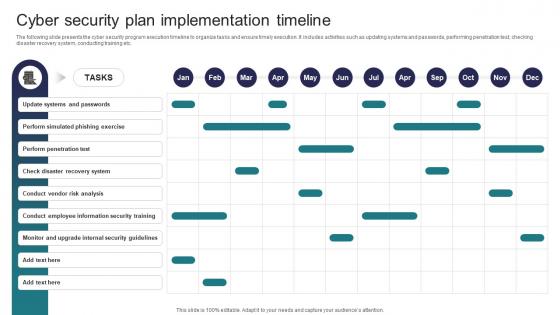 Cyber Security Plan Implementation Timeline Implementing Strategies To Mitigate Cyber Security Threats
Cyber Security Plan Implementation Timeline Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide presents the cyber security program execution timeline to organize tasks and ensure timely execution. It includes activities such as updating systems and passwords, performing penetration test, checking disaster recovery system, conducting training etc. Increase audience engagement and knowledge by dispensing information using Cyber Security Plan Implementation Timeline Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on one stages. You can also present information on Update Systems And Passwords, Perform Simulated Phishing Exercise, Perform Penetration Test using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine Cyber Security Risks And Threats Implementing Strategies To Mitigate Cyber Security Threats
Determine Cyber Security Risks And Threats Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Deliver an outstanding presentation on the topic using this Determine Cyber Security Risks And Threats Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Malware, Phishing, Ransomware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
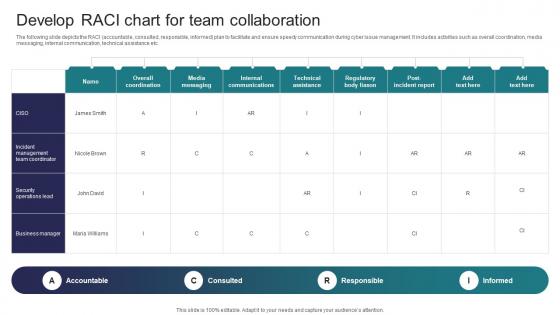 Develop RACI Chart For Team Collaboration Implementing Strategies To Mitigate Cyber Security Threats
Develop RACI Chart For Team Collaboration Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the RACI accountable, consulted, responsible, informed plan to facilitate and ensure speedy communication during cyber issue management. It includes activities such as overall coordination, media messaging, internal communication, technical assistance etc. Present the topic in a bit more detail with this Develop RACI Chart For Team Collaboration Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Accountable, Consulted, Responsible This template is free to edit as deemed fit for your organization. Therefore download it now.
-
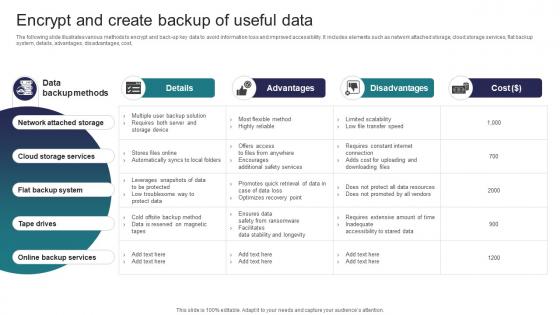 Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats
Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates various methods to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.


