Powerpoint Templates and Google slides for Online Authentication Icon
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
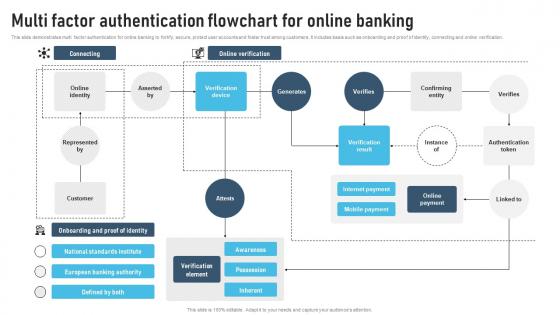 Multi Factor Authentication Flowchart For Online Banking
Multi Factor Authentication Flowchart For Online BankingThis slide demonstrates multi factor authentication for online banking to fortify, secure, protect user accounts and foster trust among customers. It includes basis such as onboarding and proof of identity, connecting and online verification. Presenting our well structured Multi Factor Authentication Flowchart For Online Banking. The topics discussed in this slide are Connecting, Verification, Result. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
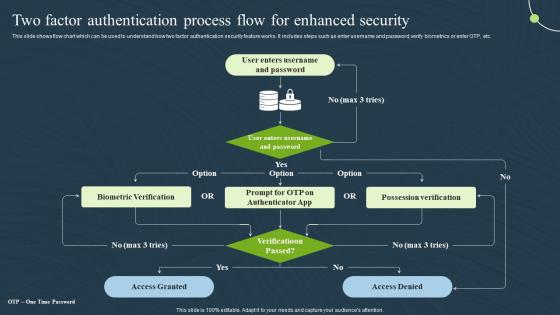 Two Factor Authentication Process Security Mobile Banking For Convenient And Secure Online Payments Fin SS
Two Factor Authentication Process Security Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide shows flow chart which can be used to understand how two factor authentication security feature works. It includes steps such as enter username and password, verify biometrics or enter OTP, etc. Present the topic in a bit more detail with this Two Factor Authentication Process Security Mobile Banking For Convenient And Secure Online Payments Fin SS. Use it as a tool for discussion and navigation on Authentication, Process, Possession Verification . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Online SMS Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Online SMS Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon is perfect for illustrating data tampering. It features a laptop with a red warning sign, conveying the message of caution and security. Use this icon to highlight the importance of data integrity in your presentation.
-
 Online SMS Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Online SMS Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone PowerPoint icon is perfect for visually representing data tampering. It features a laptop with a red line through it, symbolizing the disruption of data integrity. Use it to illustrate the dangers of data tampering and the importance of data security.

