Powerpoint Templates and Google slides for Privacy Of Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Working Of Data Privacy Management Tools Training Ppt
Working Of Data Privacy Management Tools Training PptPresenting Working of Data Privacy Management Tools. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
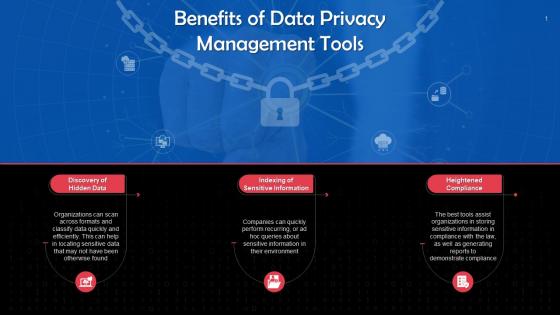 Benefits Of Data Privacy Management Tools Training Ppt
Benefits Of Data Privacy Management Tools Training PptPresenting Benefits of Data Privacy Management Tools. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
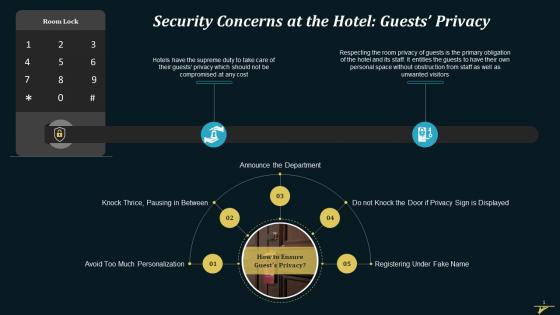 Security Concern Of Guests Privacy At A Hotel Training Ppt
Security Concern Of Guests Privacy At A Hotel Training PptPresenting Security Concern of Guests Privacy at a Hotel . This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizablealter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
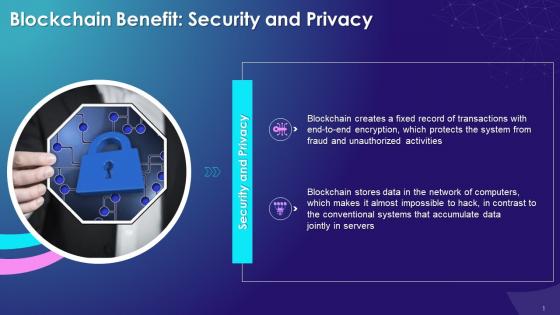 Security And Privacy Benefit Of Blockchain Technology Training Ppt
Security And Privacy Benefit Of Blockchain Technology Training PptPresenting Security and Privacy Benefit of Blockchain Technology. This slide is well crafted and designed by our PowerPoint specialists. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. You can add or delete the content as per your need.
-
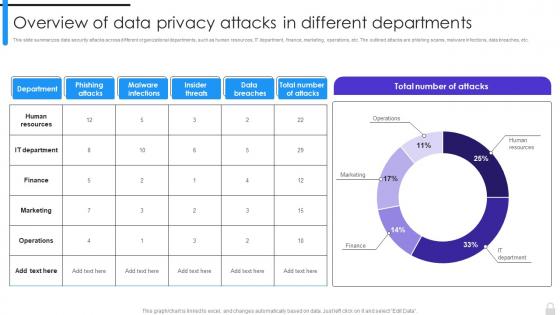 Encryption Implementation Strategies Overview Of Data Privacy Attacks In Different Departments
Encryption Implementation Strategies Overview Of Data Privacy Attacks In Different DepartmentsThis slide summarizes data security attacks across different organizational departments, such as human resources, IT department, finance, marketing, operations, etc. The outlined attacks are phishing scams, malware infections, data breaches, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Overview Of Data Privacy Attacks In Different Departments. Use it as a tool for discussion and navigation on Human Resources, IT Department, Finance, Marketing, Operations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
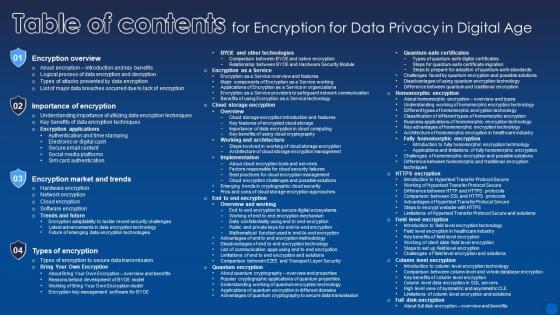 Table Of Contents For Encryption For Data Privacy In Digital Age
Table Of Contents For Encryption For Data Privacy In Digital AgeDeliver an outstanding presentation on the topic using this Table Of Contents For Encryption For Data Privacy In Digital Age. Dispense information and present a thorough explanation of Encryption Overview, Importance Of Encryption, Encryption Market And Trends using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
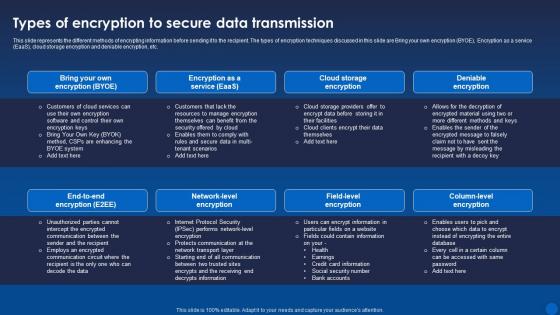 Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age It
Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age ItThis slide represents the different methods of encrypting information before sending it to the recipient. The types of encryption techniques discussed in this slide are Bring your own encryption BYOE, Encryption as a service EaaS, cloud storage encryption and deniable encryption, etc. Present the topic in a bit more detail with this Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Data Transmission, Encryption, Deniable Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
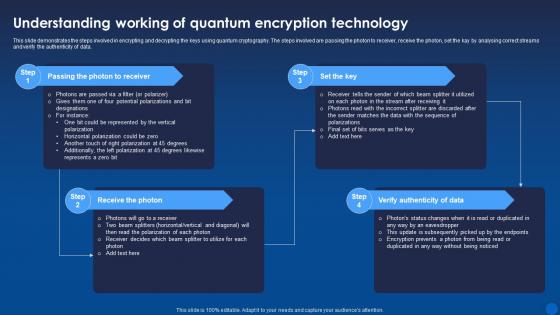 Understanding Working Of Quantum Encryption Technology Encryption For Data Privacy In Digital Age It
Understanding Working Of Quantum Encryption Technology Encryption For Data Privacy In Digital Age ItThis slide demonstrates the steps involved in encrypting and decrypting the keys using quantum cryptography. The steps involved are passing the photon to receiver, receive the photon, set the kay by analysing correct streams and verify the authenticity of data. Increase audience engagement and knowledge by dispensing information using Understanding Working Of Quantum Encryption Technology Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Passing The Photon To Receiver, Receive The Photon, Verify Authenticity Of Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
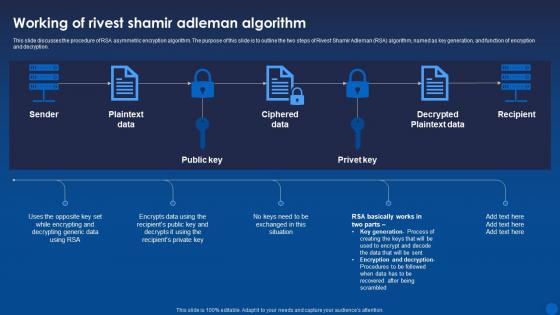 Working Of Rivest Shamir Adleman Algorithm Encryption For Data Privacy In Digital Age It
Working Of Rivest Shamir Adleman Algorithm Encryption For Data Privacy In Digital Age ItThis slide discusses the procedure of RSA asymmetric encryption algorithm. The purpose of this slide is to outline the two steps of Rivest Shamir Adleman RSA algorithm, named as key generation, and function of encryption and decryption. Deliver an outstanding presentation on the topic using this Working Of Rivest Shamir Adleman Algorithm Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Algorithm, Ciphered Data, Decrypted Plaintext Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
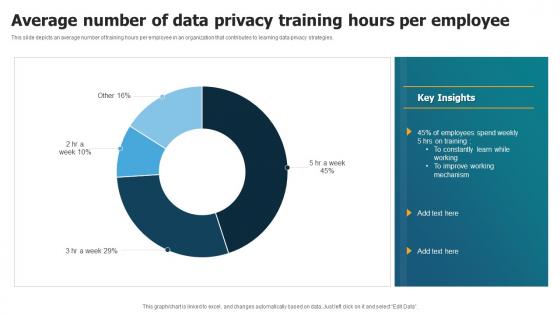 Average Number Of Data Privacy Training Hours Per Employee
Average Number Of Data Privacy Training Hours Per EmployeeThis slide depicts an average number of training hours per employee in an organization that contributes to learning data privacy strategies. Introducing our Average Number Of Data Privacy Training Hours Per Employee set of slides. The topics discussed in these slides are Average Number, Training Hours Per Employee. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Risks Associated With Lack Of Data Privacy Training
Risks Associated With Lack Of Data Privacy TrainingThis slide covers the consequences of not providing data security training to employees that may lead to business losses. Introducing our Risks Associated With Lack Of Data Privacy Training set of slides. The topics discussed in these slides are Data Breaches, Financial Consequences, Reputational Damage. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
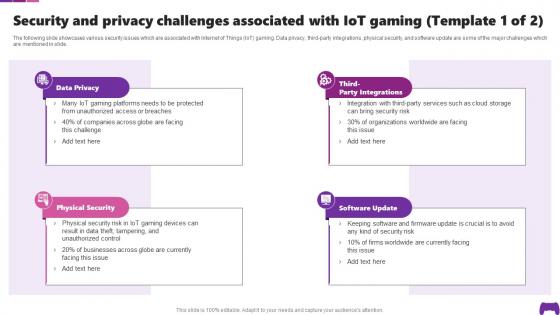 Security And Privacy Challenges Associated With IoT Transforming Future Of Gaming IoT SS
Security And Privacy Challenges Associated With IoT Transforming Future Of Gaming IoT SSThe following slide showcases various security issues which are associated with Internet of Things IoT gaming. Data privacy, third-party integrations, physical security, and software update are some of the major challenges which are mentioned in slide. Introducing Security And Privacy Challenges Associated With IoT Transforming Future Of Gaming IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Privacy, Physical Security, Software Update, using this template. Grab it now to reap its full benefits.
-
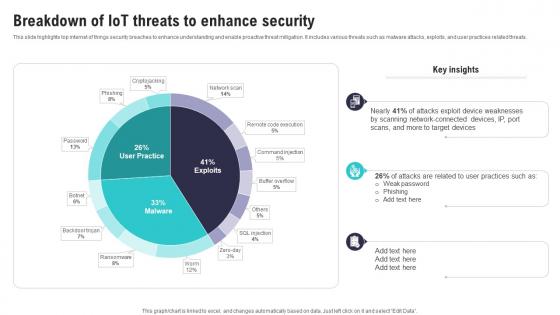 Breakdown Of IoT Threats To Enhance Security IoT Security And Privacy Safeguarding IoT SS
Breakdown Of IoT Threats To Enhance Security IoT Security And Privacy Safeguarding IoT SSThis slide highlights top internet of things security breaches to enhance understanding and enable proactive threat mitigation. It includes various threats such as malware attacks, exploits, and user practices related threats. Present the topic in a bit more detail with this Breakdown Of IoT Threats To Enhance Security IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Scanning Network Connected, Attacks Exploit, Device Weaknesses. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
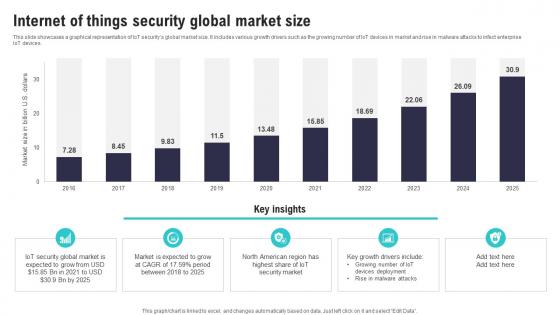 Internet Of Things Security Global Market Size IoT Security And Privacy Safeguarding IoT SS
Internet Of Things Security Global Market Size IoT Security And Privacy Safeguarding IoT SSThis slide showcases a graphical representation of IoT securitys global market size. It includes various growth drivers such as the growing number of IoT devices in market and rise in malware attacks to infect enterprise IoT devices.Deliver an outstanding presentation on the topic using this Internet Of Things Security Global Market Size IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Security Global Market, American Region, Rise Malware Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS
Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS. This template helps you present information on five stages. You can also present information on Introduction Iot Security, Need Iot, Security Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
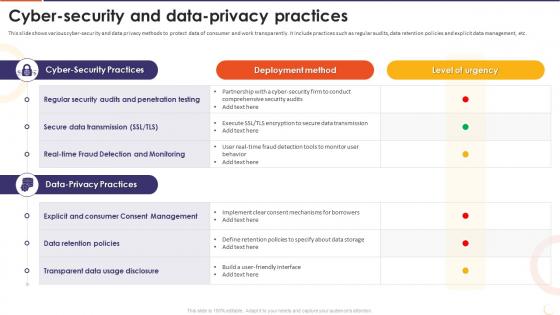 The Future Of Financing Digital Cyber Security And Data Privacy Practices
The Future Of Financing Digital Cyber Security And Data Privacy PracticesThis slide shows various cyber-security and data privacy methods to protect data of consumer and work transparently. It include practices such as regular audits, data retention policies and explicit data management, etc. Present the topic in a bit more detail with this The Future Of Financing Digital Cyber Security And Data Privacy Practices. Use it as a tool for discussion and navigation on Regular Security Audits, Penetration Testing, Secure Data Transmission, Data Retention Policies, Transparent Data Usage Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 The Future Of Financing Digital Key Data Privacy Risks In Digital Lending
The Future Of Financing Digital Key Data Privacy Risks In Digital LendingThis slide shows major risks related to digital lending for borrower and lenders. It include key risks such as consumer data sharing, customer and transparency, data leakage, etc. Deliver an outstanding presentation on the topic using this The Future Of Financing Digital Key Data Privacy Risks In Digital Lending. Dispense information and present a thorough explanation of Consumer Data Sharing, Customer Concern And Transparency, Data Retention And Leakage, Data Minimization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
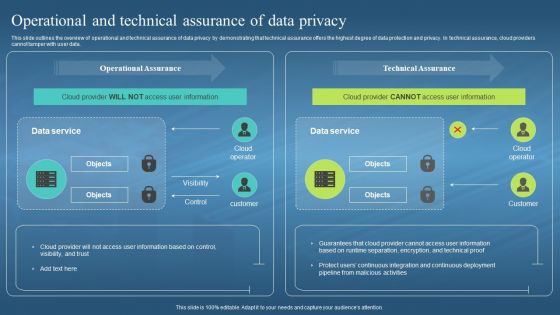 Confidential Computing Hardware Operational And Technical Assurance Of Data Privacy
Confidential Computing Hardware Operational And Technical Assurance Of Data PrivacyThis slide outlines the overview of operational and technical assurance of data privacy by demonstrating that technical assurance offers the highest degree of data protection and privacy. In technical assurance, cloud providers cannot tamper with user data. Present the topic in a bit more detail with this Confidential Computing Hardware Operational And Technical Assurance Of Data Privacy. Use it as a tool for discussion and navigation on Operational Assurance, Technical Assurance, Data Privacy, Integration And Continuous Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
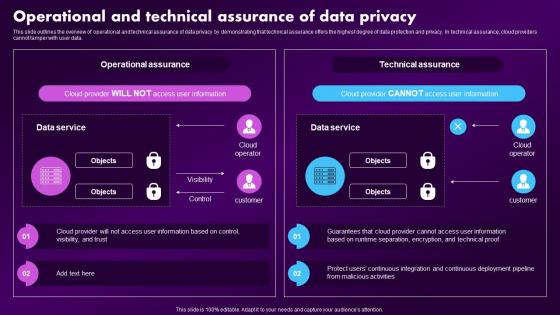 Confidential Computing Market Operational And Technical Assurance Of Data Privacy
Confidential Computing Market Operational And Technical Assurance Of Data PrivacyThis slide outlines the overview of operational and technical assurance of data privacy by demonstrating that technical assurance offers the highest degree of data protection and privacy. In technical assurance, cloud providers cannot tamper with user data. Present the topic in a bit more detail with this Confidential Computing Market Operational And Technical Assurance Of Data Privacy. Use it as a tool for discussion and navigation on Operational Assurance, Technical Assurance, Operational. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
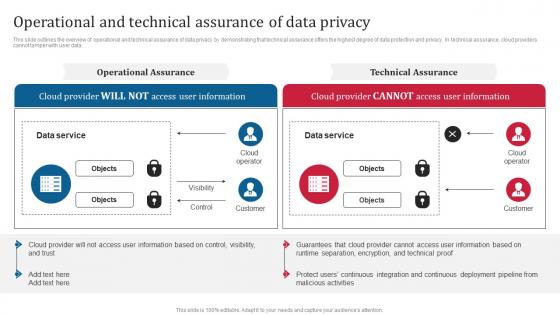 Confidential Computing Consortium Operational And Technical Assurance Of Data Privacy
Confidential Computing Consortium Operational And Technical Assurance Of Data PrivacyThis slide outlines the overview of operational and technical assurance of data privacy by demonstrating that technical assurance offers the highest degree of data protection and privacy. In technical assurance, cloud providers cannot tamper with user data. Present the topic in a bit more detail with this Confidential Computing Consortium Operational And Technical Assurance Of Data Privacy. Use it as a tool for discussion and navigation on Operational And Technical, Assurance Of Data Privacy, Data Protection And Privacy, Demonstrating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
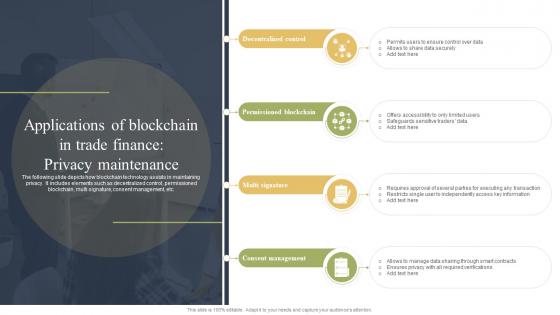 Applications Of Blockchain In Trade Finance Privacy How Blockchain Is Reforming Trade BCT SS
Applications Of Blockchain In Trade Finance Privacy How Blockchain Is Reforming Trade BCT SSThe following slide depicts how blockchain technology assists in maintaining privacy. It includes elements such as decentralized control, permissioned blockchain, multi signature, consent management, etc. Introducing Applications Of Blockchain In Trade Finance Privacy How Blockchain Is Reforming Trade BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Control, Permissioned Blockchain, Multi Signature, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 Operational And Technical Assurance Of Data Privacy
Confidential Computing V2 Operational And Technical Assurance Of Data PrivacyThis slide outlines the overview of operational and technical assurance of data privacy by demonstrating that technical assurance offers the highest degree of data protection and privacy. In technical assurance, cloud providers cannot tamper with user data. Present the topic in a bit more detail with this Confidential Computing V2 Operational And Technical Assurance Of Data Privacy. Use it as a tool for discussion and navigation on Operational And Technical Assurance, Data Protection And Privacy, Technical Assurance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
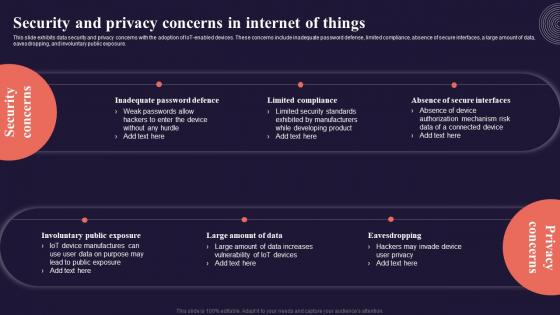 Security And Privacy Concerns In Internet Of Things Introduction To Internet Of Things IoT SS
Security And Privacy Concerns In Internet Of Things Introduction To Internet Of Things IoT SSThis slide exhibits data security and privacy concerns with the adoption of IoT enabled devices. These concerns include inadequate password defense, limited compliance, absence of secure interfaces, a large amount of data, eavesdropping, and involuntary public exposure. Introducing Security And Privacy Concerns In Internet Of Things Introduction To Internet Of Things IoT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Inadequate Password Defence, Limited Compliance, using this template. Grab it now to reap its full benefits.
-
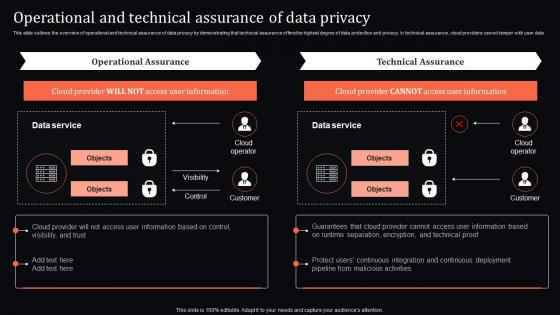 Confidential Computing System Technology Operational And Technical Assurance Of Data Privacy
Confidential Computing System Technology Operational And Technical Assurance Of Data PrivacyThis slide outlines the overview of operational and technical assurance of data privacy by demonstrating that technical assurance offers the highest degree of data protection and privacy. In technical assurance, cloud providers cannot tamper with user data. Deliver an outstanding presentation on the topic using this Confidential Computing System Technology Operational And Technical Assurance Of Data Privacy. Dispense information and present a thorough explanation of Operational, Deployment, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
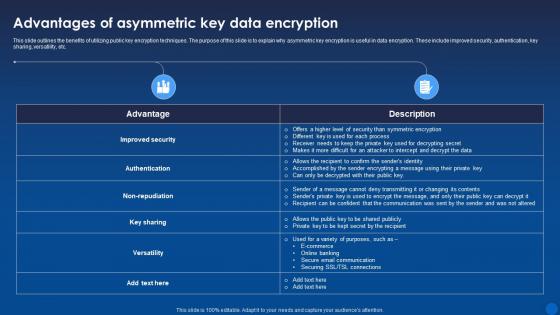 Advantages Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age It
Advantages Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of utilizing public key encryption techniques. The purpose of this slide is to explain why asymmetric key encryption is useful in data encryption. These include improved security, authentication, key sharing, versatility, etc. Deliver an outstanding presentation on the topic using this Advantages Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Accomplished, Communication, Asymmetric using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
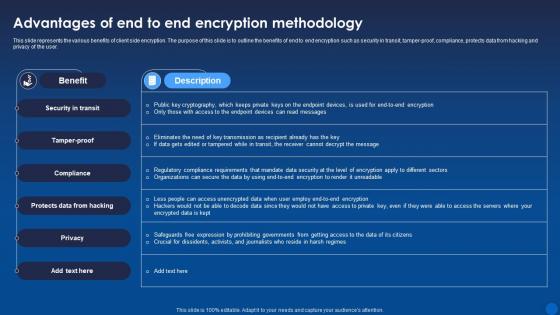 Advantages Of End To End Encryption Methodology Encryption For Data Privacy In Digital Age It
Advantages Of End To End Encryption Methodology Encryption For Data Privacy In Digital Age ItThis slide represents the various benefits of client side encryption. The purpose of this slide is to outline the benefits of end to end encryption such as security in transit, tamper-proof, compliance, protects data from hacking and privacy of the user. Present the topic in a bit more detail with this Advantages Of End To End Encryption Methodology Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Protects Data From Hacking, Security In Transit, Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of utilizing Hypertext Transfer Protocol Secure HTTPS for website encryption. The advantages discussed in this slide are secure interaction, data integrity, privacy and security, better performance, user experience, etc. Introducing Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Interaction, Data Integrity, Better Performance, using this template. Grab it now to reap its full benefits.
-
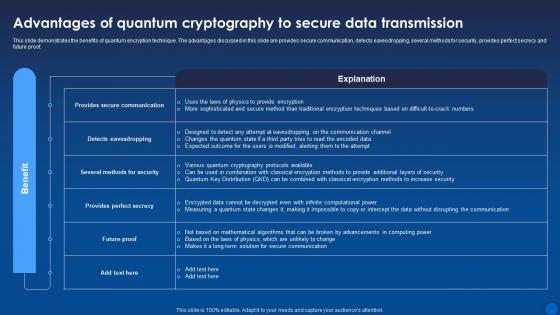 Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It
Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age ItThis slide demonstrates the benefits of quantum encryption technique. The advantages discussed in this slide are provides secure communication, detects eavesdropping, several methods for security, provides perfect secrecy and future proof. Present the topic in a bit more detail with this Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Quantum, Cryptography, Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Advantages Of Rivest Shamir Adleman Encryption Algorithm Encryption For Data Privacy In Digital Age It
Advantages Of Rivest Shamir Adleman Encryption Algorithm Encryption For Data Privacy In Digital Age ItThis slide demonstrates the benefits of utilizing Rivest Shamir Adleman technique for data encryption. The advantages outlines in this slide are no key sharing, proof of authenticity, faster encryption, and no data modification. Increase audience engagement and knowledge by dispensing information using Advantages Of Rivest Shamir Adleman Encryption Algorithm Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Proof Of Authenticity, Faster Encryption, Data Modification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
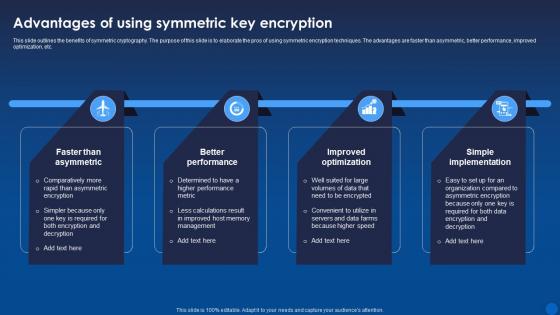 Advantages Of Using Symmetric Key Encryption Encryption For Data Privacy In Digital Age It
Advantages Of Using Symmetric Key Encryption Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of symmetric cryptography. The purpose of this slide is to elaborate the pros of using symmetric encryption techniques. The advantages are faster than asymmetric, better performance, improved optimization, etc. Introducing Advantages Of Using Symmetric Key Encryption Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Faster Than Asymmetric, Better Performance, Improved Optimization, using this template. Grab it now to reap its full benefits.
-
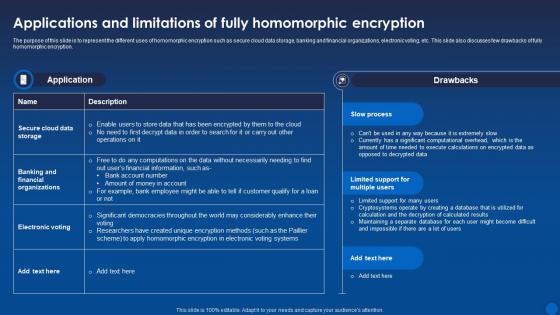 Applications And Limitations Of Fully Homomorphic Encryption For Data Privacy In Digital Age It
Applications And Limitations Of Fully Homomorphic Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to represent the different uses of homomorphic encryption such as secure cloud data storage, banking and financial organizations, electronic voting, etc. This slide also discusses few drawbacks of fully homomorphic encryption. Deliver an outstanding presentation on the topic using this Applications And Limitations Of Fully Homomorphic Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Homomorphic, Encryption, Applications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
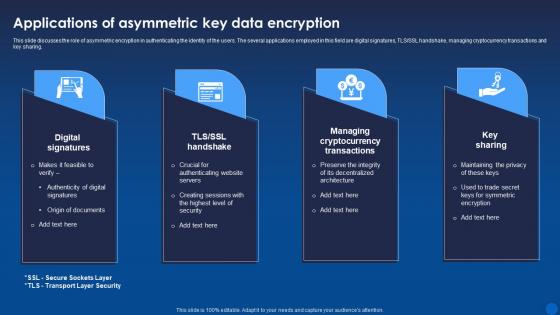 Applications Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age It
Applications Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age ItThis slide discusses the role of asymmetric encryption in authenticating the identity of the users. The several applications employed in this field are digital signatures, TLS or SSL handshake, managing cryptocurrency transactions and key sharing. Introducing Applications Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Digital Signatures, Managing Cryptocurrency Transactions, Data Encryption, using this template. Grab it now to reap its full benefits.
-
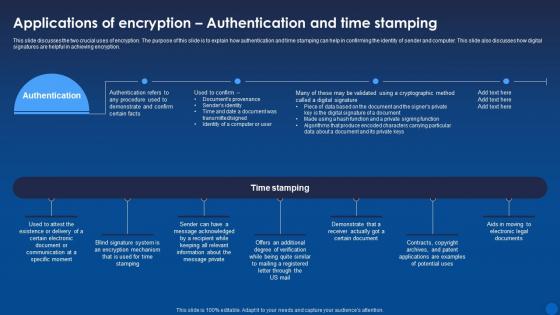 Applications Of Authentication And Time Stamping Encryption For Data Privacy In Digital Age It
Applications Of Authentication And Time Stamping Encryption For Data Privacy In Digital Age ItThis slide discusses the two crucial uses of encryption. The purpose of this slide is to explain how authentication and time stamping can help in confirming the identity of sender and computer. This slide also discusses how digital signatures are helpful in achieving encryption. Present the topic in a bit more detail with this Applications Of Authentication And Time Stamping Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Authentication, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
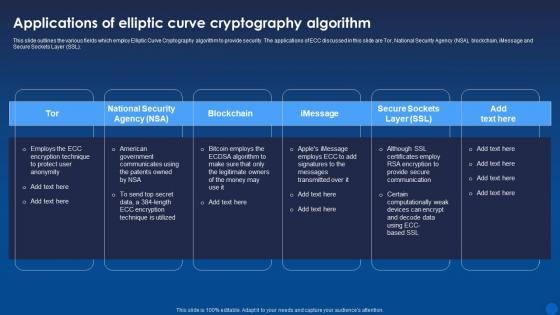 Applications Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It
Applications Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age ItThis slide outlines the various fields which employ Elliptic Curve Cryptography algorithm to provide security. The applications of ECC discussed in this slide are Tor, National Security Agency NSA, blockchain, iMessage and Secure Sockets Layer SSL. Introducing Applications Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Blockchain, Cryptography Algorithm, Applications, using this template. Grab it now to reap its full benefits.
-
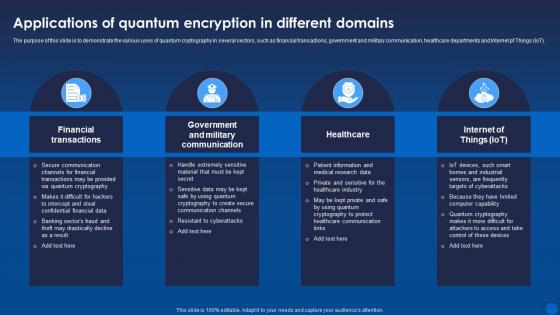 Applications Of Quantum Encryption In Different Domains Encryption For Data Privacy In Digital Age It
Applications Of Quantum Encryption In Different Domains Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to demonstrate the various uses of quantum cryptography in several sectors, such as financial transactions, government and military communication, healthcare departments and Internet pf Things IoT. Increase audience engagement and knowledge by dispensing information using Applications Of Quantum Encryption In Different Domains Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Healthcare, Financial Transactions, Government And Military Communication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
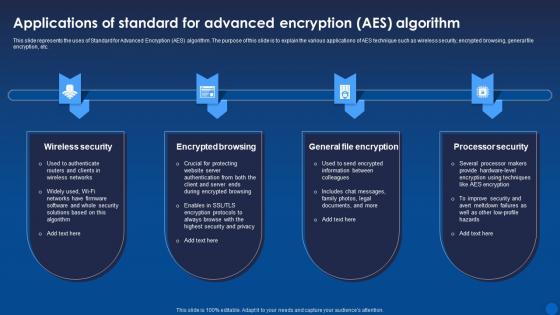 Applications Of Standard For Advanced Encryption Aes Encryption For Data Privacy In Digital Age It
Applications Of Standard For Advanced Encryption Aes Encryption For Data Privacy In Digital Age ItThis slide represents the uses of Standard for Advanced Encryption AES algorithm. The purpose of this slide is to explain the various applications of AES technique such as wireless security, encrypted browsing, general file encryption, etc. Introducing Applications Of Standard For Advanced Encryption Aes Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Wireless Security, Encrypted Browsing, General File Encryption , using this template. Grab it now to reap its full benefits.
-
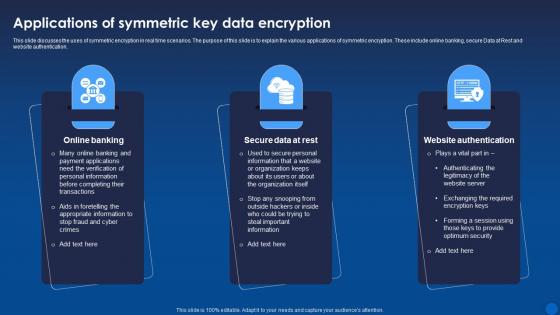 Applications Of Symmetric Key Data Encryption Encryption For Data Privacy In Digital Age It
Applications Of Symmetric Key Data Encryption Encryption For Data Privacy In Digital Age ItThis slide discusses the uses of symmetric encryption in real time scenarios. The purpose of this slide is to explain the various applications of symmetric encryption. These include online banking, secure Data at Rest and website authentication. Increase audience engagement and knowledge by dispensing information using Applications Of Symmetric Key Data Encryption Encryption For Data Privacy In Digital Age It. This template helps you present information on three stages. You can also present information on Online Banking, Secure Data At Rest, Website Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
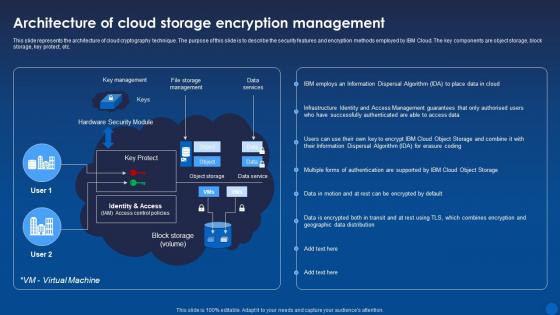 Architecture Of Cloud Storage Encryption Management Encryption For Data Privacy In Digital Age It
Architecture Of Cloud Storage Encryption Management Encryption For Data Privacy In Digital Age ItThis slide represents the architecture of cloud cryptography technique. The purpose of this slide is to describe the security features and encryption methods employed by IBM Cloud. The key components are object storage, block storage, key protect, etc. Deliver an outstanding presentation on the topic using this Architecture Of Cloud Storage Encryption Management Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Architecture, Encryption, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
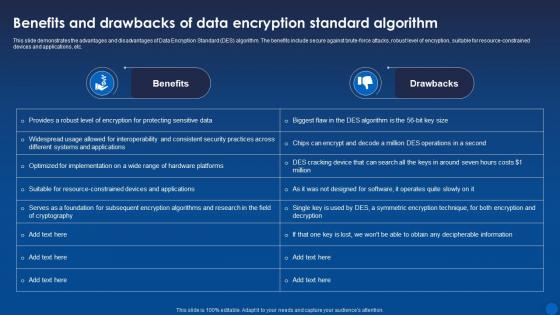 Benefits Of Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age It
Benefits Of Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages and disadvantages of Data Encryption Standard DES algorithm. The benefits include secure against brute-force attacks, robust level of encryption, suitable for resource-constrained devices and applications, etc. Present the topic in a bit more detail with this Benefits Of Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Data Encryption, Demonstrates, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
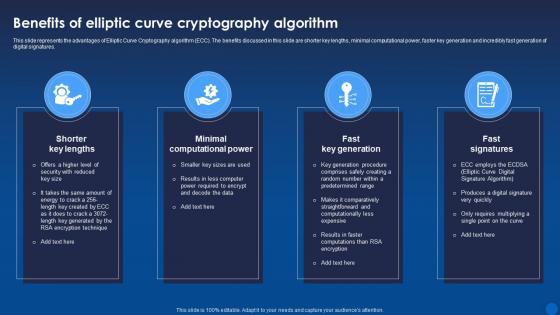 Benefits Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It
Benefits Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the advantages of Elliptic Curve Cryptography algorithm ECC. The benefits discussed in this slide are shorter key lengths, minimal computational power, faster key generation and incredibly fast generation of digital signatures. Increase audience engagement and knowledge by dispensing information using Benefits Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Shorter Key Lengths, Minimal Computational Power, Fast Key Generation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
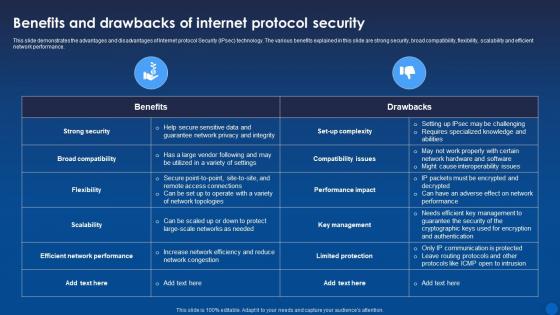 Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages and disadvantages of Internet protocol Security IPsec technology. The various benefits explained in this slide are strong security, broad compatibility, flexibility, scalability and efficient network performance. Deliver an outstanding presentation on the topic using this Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Key Management, Performance Impact, Compatibility Issues using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Benefits Of Standard For Advanced Encryption Algorithm Encryption For Data Privacy In Digital Age It
Benefits Of Standard For Advanced Encryption Algorithm Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages and disadvantages of Standard for Advanced Encryption AES algorithm. The benefits include most reliable security protocol, longer key sizes, used for commercial and open-source solutions for many businesses, etc. Present the topic in a bit more detail with this Benefits Of Standard For Advanced Encryption Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Algorithm, Commercial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
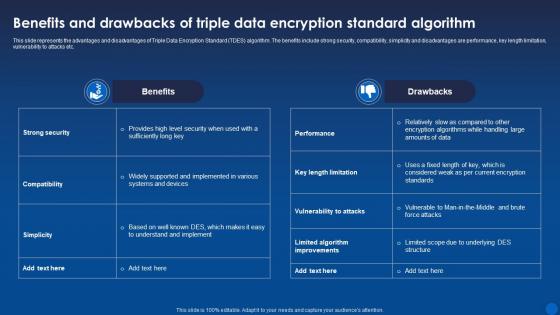 Benefits Of Triple Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age It
Benefits Of Triple Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the advantages and disadvantages of Triple Data Encryption Standard TDES algorithm. The benefits include strong security, compatibility, simplicity and disadvantages are performance, key length limitation, vulnerability to attacks etc. Deliver an outstanding presentation on the topic using this Benefits Of Triple Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Data Encryption, Compatibility, Performance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
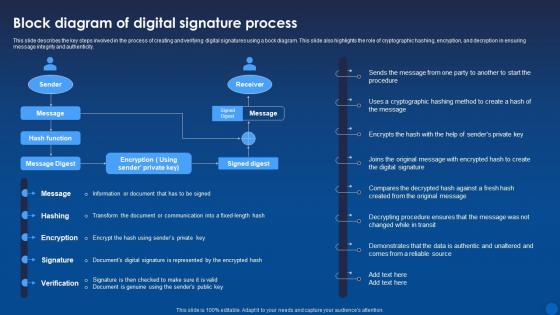 Block Diagram Of Digital Signature Process Encryption For Data Privacy In Digital Age It
Block Diagram Of Digital Signature Process Encryption For Data Privacy In Digital Age ItThis slide describes the key steps involved in the process of creating and verifying digital signatures using a bock diagram. This slide also highlights the role of cryptographic hashing, encryption, and decryption in ensuring message integrity and authenticity. Deliver an outstanding presentation on the topic using this Block Diagram Of Digital Signature Process Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Process, Source, Demonstrates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
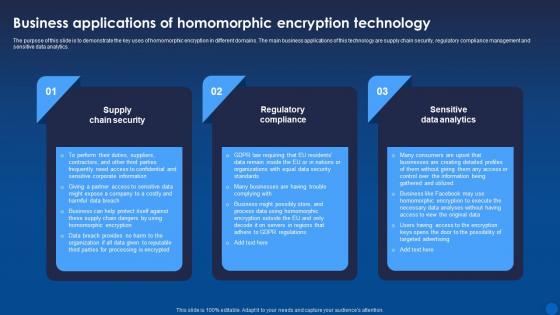 Business Of Homomorphic Encryption Technology Encryption For Data Privacy In Digital Age It
Business Of Homomorphic Encryption Technology Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to demonstrate the key uses of homomorphic encryption in different domains. The main business applications of this technology are supply chain security, regulatory compliance management and sensitive data analytics. Introducing Business Of Homomorphic Encryption Technology Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Supply Chain Security, Regulatory Compliance, Sensitive Data Analytics, using this template. Grab it now to reap its full benefits.
-
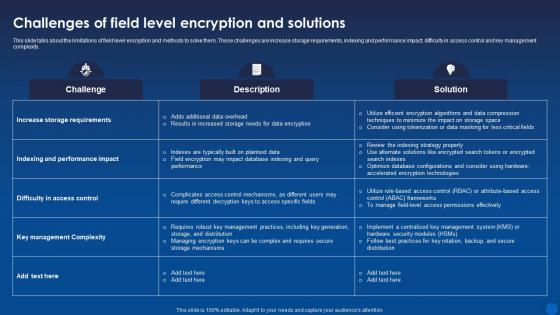 Challenges Of Field Level Encryption And Solutions Encryption For Data Privacy In Digital Age It
Challenges Of Field Level Encryption And Solutions Encryption For Data Privacy In Digital Age ItThis slide talks about the limitations of field level encryption and methods to solve them. These challenges are increase storage requirements, indexing and performance impact, difficulty in access control and key management complexity. Deliver an outstanding presentation on the topic using this Challenges Of Field Level Encryption And Solutions Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Description, Solution, Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
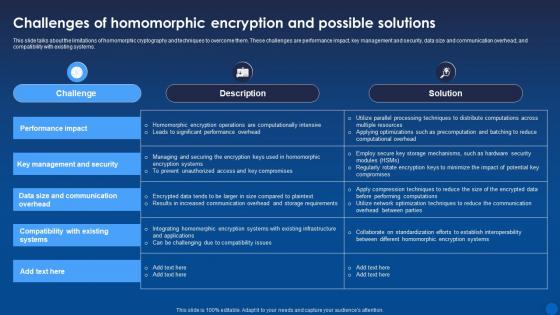 Challenges Of Homomorphic Encryption And Possible Encryption For Data Privacy In Digital Age It
Challenges Of Homomorphic Encryption And Possible Encryption For Data Privacy In Digital Age ItThis slide talks about the limitations of homomorphic cryptography and techniques to overcome them. These challenges are performance impact, key management and security, data size and communication overhead, and compatibility with existing systems. Present the topic in a bit more detail with this Challenges Of Homomorphic Encryption And Possible Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Key Management And Security, Performance Impact, Compatibility With Existing Systems. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
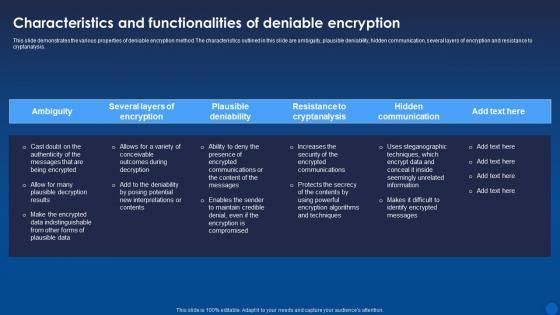 Characteristics And Functionalities Of Deniable Encryption Encryption For Data Privacy In Digital Age It
Characteristics And Functionalities Of Deniable Encryption Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various properties of deniable encryption method. The characteristics outlined in this slide are ambiguity, plausible deniability, hidden communication, several layers of encryption and resistance to cryptanalysis. Deliver an outstanding presentation on the topic using this Characteristics And Functionalities Of Deniable Encryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Ambiguity, Plausible Deniability, Hidden Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
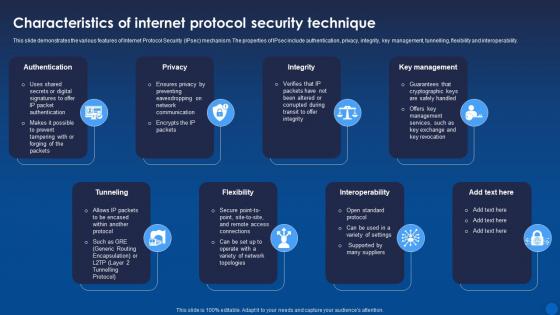 Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It
Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various features of Internet Protocol Security IPsec mechanism. The properties of IPsec include authentication, privacy, integrity, key management, tunnelling, flexibility and interoperability. Introducing Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Interoperability, using this template. Grab it now to reap its full benefits.
-
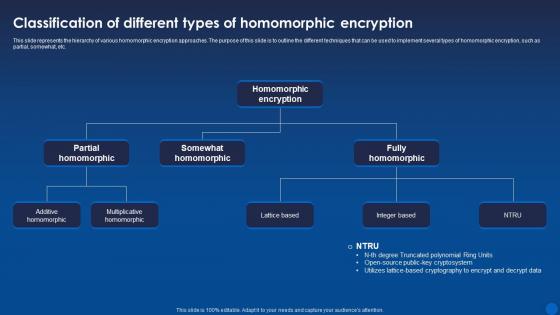 Classification Of Different Types Of Homomorphic Encryption Encryption For Data Privacy In Digital Age It
Classification Of Different Types Of Homomorphic Encryption Encryption For Data Privacy In Digital Age ItThis slide represents the hierarchy of various homomorphic encryption approaches. The purpose of this slide is to outline the different techniques that can be used to implement several types of homomorphic encryption, such as partial, somewhat, etc. Deliver an outstanding presentation on the topic using this Classification Of Different Types Of Homomorphic Encryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Homomorphic Encryption, Somewhat Homomorphic, Partial Homomorphic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
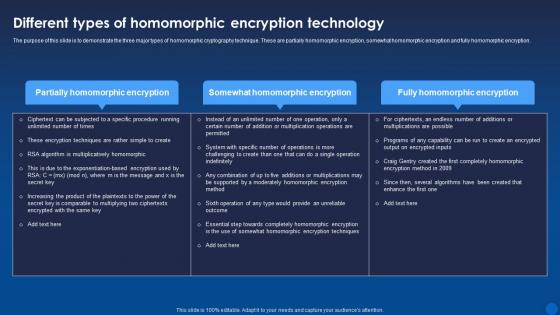 Different Types Of Homomorphic Encryption Technology Encryption For Data Privacy In Digital Age It
Different Types Of Homomorphic Encryption Technology Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to demonstrate the three major types of homomorphic cryptography technique. These are partially homomorphic encryption, somewhat homomorphic encryption and fully homomorphic encryption. Present the topic in a bit more detail with this Different Types Of Homomorphic Encryption Technology Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Homomorphic, Encryption, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
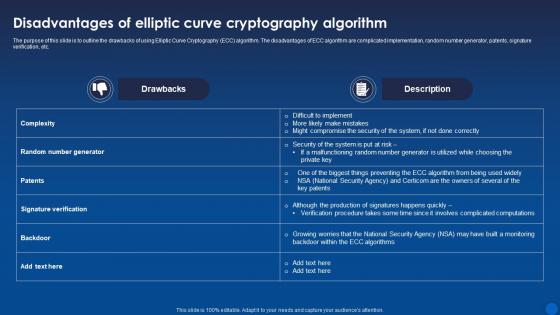 Disadvantages Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It
Disadvantages Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the drawbacks of using Elliptic Curve Cryptography ECC algorithm. The disadvantages of ECC algorithm are complicated implementation, random number generator, patents, signature verification, etc. Deliver an outstanding presentation on the topic using this Disadvantages Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Cryptography, Algorithm, Disadvantages using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
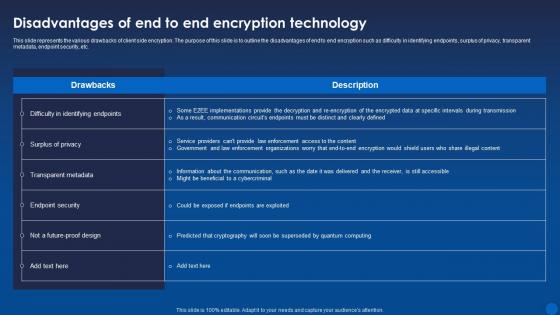 Disadvantages Of End To End Encryption Technology Encryption For Data Privacy In Digital Age It
Disadvantages Of End To End Encryption Technology Encryption For Data Privacy In Digital Age ItThis slide represents the various drawbacks of client side encryption. The purpose of this slide is to outline the disadvantages of end to end encryption such as difficulty in identifying endpoints, surplus of privacy, transparent metadata, endpoint security, etc. Present the topic in a bit more detail with this Disadvantages Of End To End Encryption Technology Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Disadvantages, Encryption, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
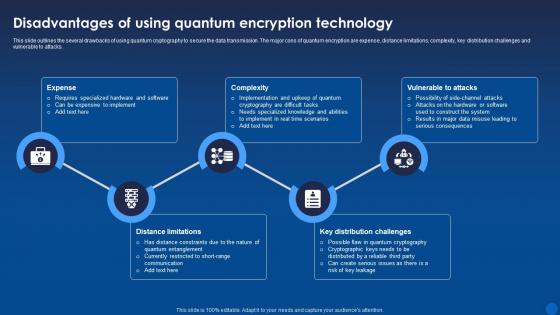 Disadvantages Of Using Quantum Encryption Technology Encryption For Data Privacy In Digital Age It
Disadvantages Of Using Quantum Encryption Technology Encryption For Data Privacy In Digital Age ItThis slide outlines the several drawbacks of using quantum cryptography to secure the data transmission. The major cons of quantum encryption are expense, distance limitations, complexity, key distribution challenges and vulnerable to attacks. Introducing Disadvantages Of Using Quantum Encryption Technology Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Complexity, Vulnerable To Attacks, Distance Limitations, using this template. Grab it now to reap its full benefits.
-
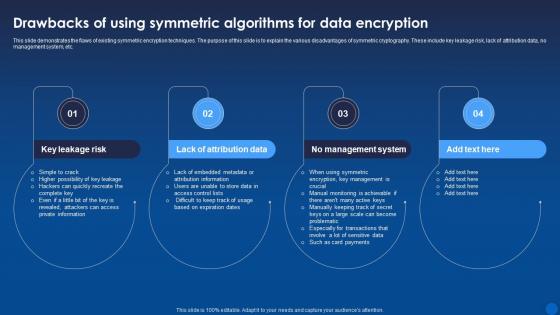 Drawbacks Of Using Symmetric Algorithms For Data Encryption For Data Privacy In Digital Age It
Drawbacks Of Using Symmetric Algorithms For Data Encryption For Data Privacy In Digital Age ItThis slide demonstrates the flaws of existing symmetric encryption techniques. The purpose of this slide is to explain the various disadvantages of symmetric cryptography. These include key leakage risk, lack of attribution data, no management system, etc. Increase audience engagement and knowledge by dispensing information using Drawbacks Of Using Symmetric Algorithms For Data Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Key Leakage Risk, Lack Of Attribution Data, No Management System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
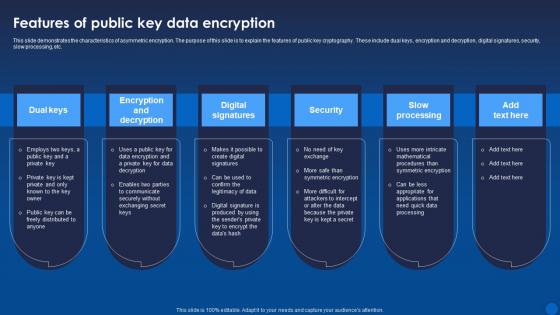 Features Of Public Key Data Encryption Encryption For Data Privacy In Digital Age It
Features Of Public Key Data Encryption Encryption For Data Privacy In Digital Age ItThis slide demonstrates the characteristics of asymmetric encryption. The purpose of this slide is to explain the features of public key cryptography. These include dual keys, encryption and decryption, digital signatures, security, slow processing, etc. Increase audience engagement and knowledge by dispensing information using Features Of Public Key Data Encryption Encryption For Data Privacy In Digital Age It. This template helps you present information on six stages. You can also present information on Security, Slow Processing, Digital Signatures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
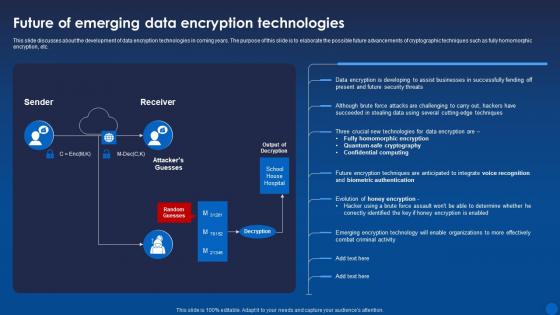 Future Of Emerging Data Encryption Technologies Encryption For Data Privacy In Digital Age It
Future Of Emerging Data Encryption Technologies Encryption For Data Privacy In Digital Age ItThis slide discusses about the development of data encryption technologies in coming years. The purpose of this slide is to elaborate the possible future advancements of cryptographic techniques such as fully homomorphic encryption, etc. Deliver an outstanding presentation on the topic using this Future Of Emerging Data Encryption Technologies Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Encryption, Technologies, Organizations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
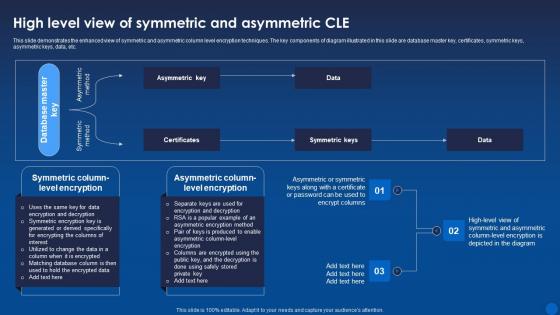 High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age It
High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age ItThis slide demonstrates the enhanced view of symmetric and asymmetric column level encryption techniques. The key components of diagram illustrated in this slide are database master key, certificates, symmetric keys, asymmetric keys, data, etc. Deliver an outstanding presentation on the topic using this High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Symmetric, Asymmetric, Certificates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
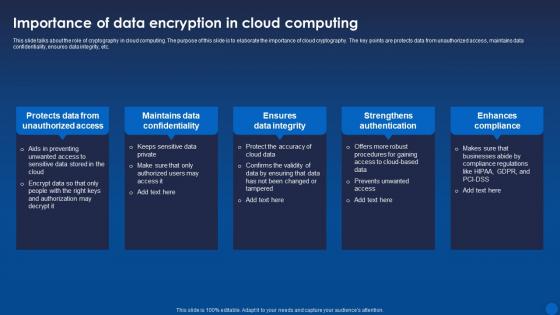 Importance Of Data Encryption In Cloud Computing Encryption For Data Privacy In Digital Age It
Importance Of Data Encryption In Cloud Computing Encryption For Data Privacy In Digital Age ItThis slide talks about the role of cryptography in cloud computing. The purpose of this slide is to elaborate the importance of cloud cryptography. The key points are protects data from unauthorized access, maintains data confidentiality, ensures data integrity, etc. Introducing Importance Of Data Encryption In Cloud Computing Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Protects Data From Unauthorized Access, Maintains Data Confidentiality, Ensures Data Integrity, using this template. Grab it now to reap its full benefits.
-
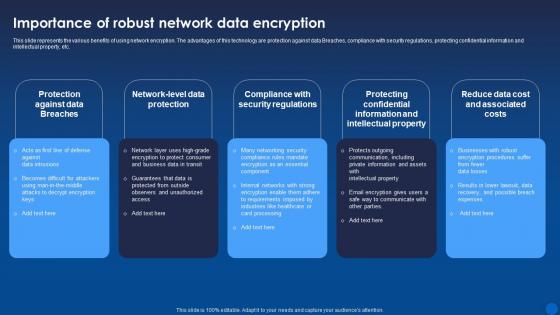 Importance Of Robust Network Data Encryption Encryption For Data Privacy In Digital Age It
Importance Of Robust Network Data Encryption Encryption For Data Privacy In Digital Age ItThis slide represents the various benefits of using network encryption. The advantages of this technology are protection against data Breaches, compliance with security regulations, protecting confidential information and intellectual property, etc. Increase audience engagement and knowledge by dispensing information using Importance Of Robust Network Data Encryption Encryption For Data Privacy In Digital Age It. This template helps you present information on five stages. You can also present information on Protection Against Data Breaches, Data Encryption, Compliance With Security Regulations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


