Powerpoint Templates and Google slides for Protocol For Secure Connections
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
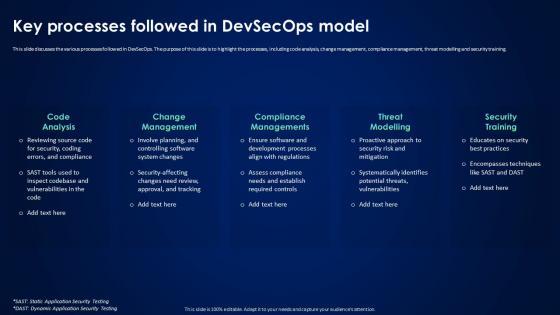 Devsecops Best Practices For Secure Key Processes Followed In Devsecops Model
Devsecops Best Practices For Secure Key Processes Followed In Devsecops ModelThis slide discusses the various processes followed in DevSecOps. The purpose of this slide is to highlight the processes, including code analysis, change management, compliance management, threat modelling and security training. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Key Processes Followed In Devsecops Model. This template helps you present information on five stages. You can also present information on Code Analysis, Change Management, Compliance Managements, Threat Modelling using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
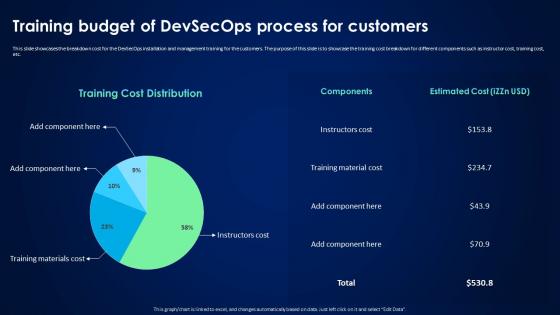 Devsecops Best Practices For Secure Training Budget Of Devsecops Process For Customers
Devsecops Best Practices For Secure Training Budget Of Devsecops Process For CustomersThis slide showcases the breakdown cost for the DevSecOps installation and management training for the customers. The purpose of this slide is to showcase the training cost breakdown for different components such as instructor cost, training cost, etc. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Training Budget Of Devsecops Process For Customers. Use it as a tool for discussion and navigation on Training Budget, Devsecops Process For Customers, Instructor Cost, Training Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
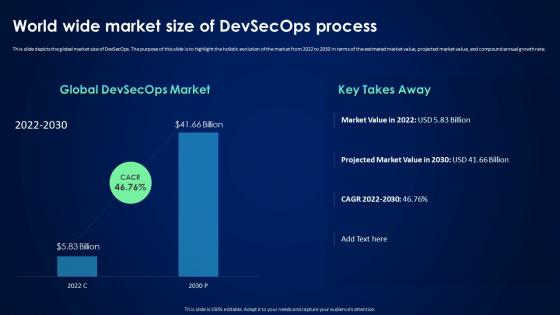 Devsecops Best Practices For Secure World Wide Market Size Of Devsecops Process
Devsecops Best Practices For Secure World Wide Market Size Of Devsecops ProcessThis slide depicts the global market size of DevSecOps. The purpose of this slide is to highlight the holistic evolution of the market from 2022 to 2030 in terms of the estimated market value, projected market value, and compound annual growth rate. Present the topic in a bit more detail with this Devsecops Best Practices For Secure World Wide Market Size Of Devsecops Process. Use it as a tool for discussion and navigation on Global Market Size Devsecops, Holistic Evolution, Projected Market Value, Compound Annual Growth Rate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
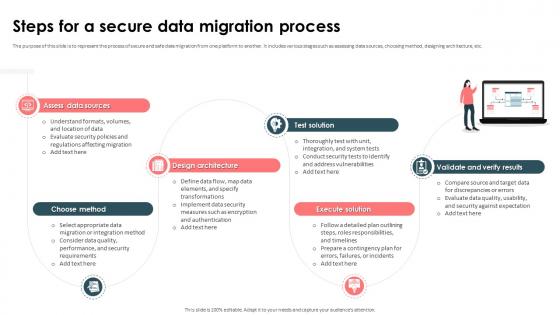 Strategic Approach For Effective Data Migration Steps For A Secure Data Migration Process
Strategic Approach For Effective Data Migration Steps For A Secure Data Migration ProcessThe purpose of this slide is to represent the process of secure and safe data migration from one platform to another. It includes various stages such as assessing data sources, choosing method, designing architecture, etc. Introducing Strategic Approach For Effective Data Migration Steps For A Secure Data Migration Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Design Architecture, Validate And Verify Results, Assess Data Sources, Data Migration Process, using this template. Grab it now to reap its full benefits.
-
 About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It
About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the role and functionality of IPsec Internet Protocol Security in securing connections between devices. This slide also outlines the uses of IPsec such as protecting data during transmission over open networks, use in building VPNs, etc. Deliver an outstanding presentation on the topic using this About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Overview, Protocol Security, Destination using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of utilizing Hypertext Transfer Protocol Secure HTTPS for website encryption. The advantages discussed in this slide are secure interaction, data integrity, privacy and security, better performance, user experience, etc. Introducing Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Interaction, Data Integrity, Better Performance, using this template. Grab it now to reap its full benefits.
-
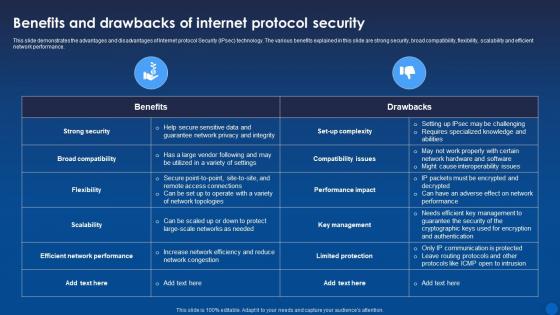 Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages and disadvantages of Internet protocol Security IPsec technology. The various benefits explained in this slide are strong security, broad compatibility, flexibility, scalability and efficient network performance. Deliver an outstanding presentation on the topic using this Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Key Management, Performance Impact, Compatibility Issues using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
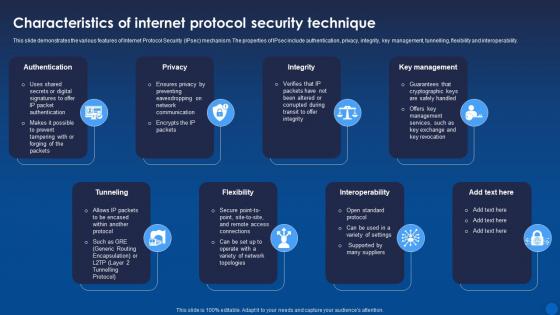 Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It
Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various features of Internet Protocol Security IPsec mechanism. The properties of IPsec include authentication, privacy, integrity, key management, tunnelling, flexibility and interoperability. Introducing Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Interoperability, using this template. Grab it now to reap its full benefits.
-
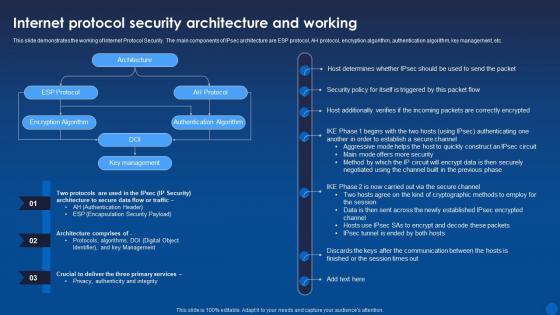 Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age It
Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age ItThis slide demonstrates the working of Internet Protocol Security. The main components of IPsec architecture are ESP protocol, AH protocol, encryption algorithm, authentication algorithm, key management, etc. Present the topic in a bit more detail with this Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Protocol Security, Architecture, Encryption Algorithm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
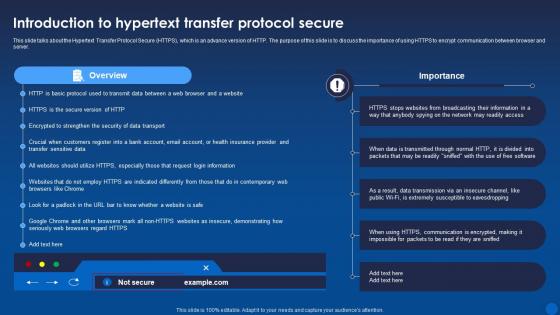 Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide talks about the Hypertext Transfer Protocol Secure HTTPS, which is an advance version of HTTP. The purpose of this slide is to discuss the importance of using HTTPS to encrypt communication between browser and server. Present the topic in a bit more detail with this Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Introduction, Overview, Protocol Secure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
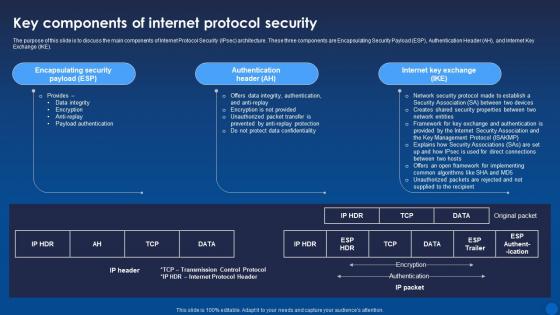 Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss the main components of Internet Protocol Security IPsec architecture. These three components are Encapsulating Security Payload ESP, Authentication Header AH, and Internet Key Exchange IKE. Deliver an outstanding presentation on the topic using this Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Authentication Header, Internet Key Exchange, Encapsulating Security Payload using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age It
Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age ItThis slide talks about the challenges of Hypertext Transfer Protocol Secure HTTPS and their possible solutions. These challenges are lack of end-to-end encryption, certificate authority vulnerabilities, difficulty in detecting malicious content, and complexity and cost of certificate management. Present the topic in a bit more detail with this Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Limitations, Solutions, Description. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
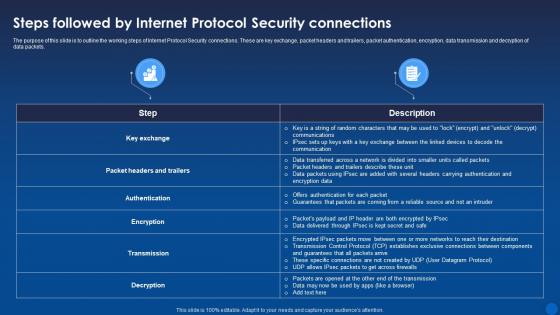 Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age It
Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the working steps of Internet Protocol Security connections. These are key exchange, packet headers and trailers, packet authentication, encryption, data transmission and decryption of data packets. Deliver an outstanding presentation on the topic using this Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Connections, Protocol Security, Data Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
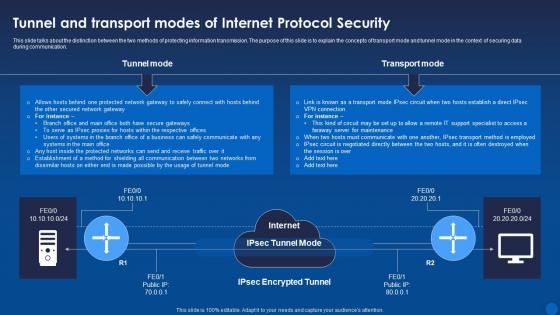 Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThis slide talks about the distinction between the two methods of protecting information transmission. The purpose of this slide is to explain the concepts of transport mode and tunnel mode in the context of securing data during communication. Present the topic in a bit more detail with this Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Transport Mode, Protocol Security, Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
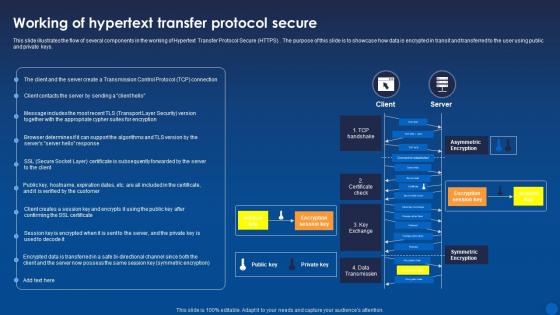 Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide illustrates the flow of several components in the working of Hypertext Transfer Protocol Secure HTTPS. The purpose of this slide is to showcase how data is encrypted in transit and transferred to the user using public and private keys. Present the topic in a bit more detail with this Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric Encryption, Symmetric Encryption, Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
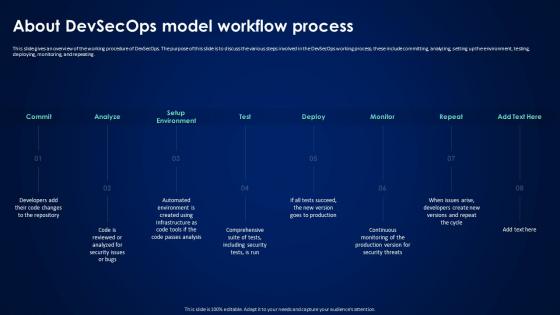 About Devsecops Model Workflow Process Devsecops Best Practices For Secure
About Devsecops Model Workflow Process Devsecops Best Practices For SecureThis slide gives an overview of the working procedure of DevSecOps. The purpose of this slide is to discuss the various steps involved in the DevSecOps working process, these include committing, analyzing, setting up the environment, testing, deploying, monitoring, and repeating. Introducing About Devsecops Model Workflow Process Devsecops Best Practices For Secure to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Devsecops Working Process, Analyzing, Testing, Deploying, Monitoring, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure About Devsecops Introduction And Working Process
Devsecops Best Practices For Secure About Devsecops Introduction And Working ProcessThis slide gives an overview of DevSecOps and its process. The purpose of this slide is to explain DevSecOps, including its process steps, which are release, deploy, operate, monitor, plan, code, build, and test. Present the topic in a bit more detail with this Devsecops Best Practices For Secure About Devsecops Introduction And Working Process. Use it as a tool for discussion and navigation on Development, Security, Operations, Smooth Integration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
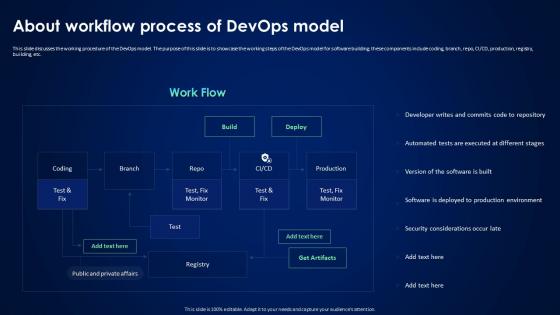 Devsecops Best Practices For Secure About Workflow Process Of Devops Model
Devsecops Best Practices For Secure About Workflow Process Of Devops ModelThis slide discusses the working procedure of the DevOps model. The purpose of this slide is to showcase the working steps of the DevOps model for software building, these components include coding, branch, repo, CI or CD, production, registry, building, etc. Present the topic in a bit more detail with this Devsecops Best Practices For Secure About Workflow Process Of Devops Model. Use it as a tool for discussion and navigation on Software Building, Coding, Production, Registry, Security Considerations Occur Late. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Continuous Integration And Continuous Delivery Process
Devsecops Best Practices For Secure Continuous Integration And Continuous Delivery ProcessThis slide discusses the continuous integration and continuous delivery process security for DevSecOps. The purpose of this slide is to highlight the process, including integrating container security scanners, automating security testing in CI, incorporating security tests in acceptance testing, and so on. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Continuous Integration And Continuous Delivery Process. Use it as a tool for discussion and navigation on Integrate Container Security Scanners, Automate Security Updates, Automate Configuration Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Continuous Process Improvement In Devsecops
Devsecops Best Practices For Secure Continuous Process Improvement In DevsecopsThis slide discusses the DevSecOps program requirement for continuous improvement. The purpose of this slide is to explain the needs of the DevSecOps program for achieving efficiency, these include strategic goals, architecture operation, and program evaluation. Introducing Devsecops Best Practices For Secure Continuous Process Improvement In Devsecops to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Strategic Goals, Architecture And Operations, Program Evaluation, Devops Environment, using this template. Grab it now to reap its full benefits.
-
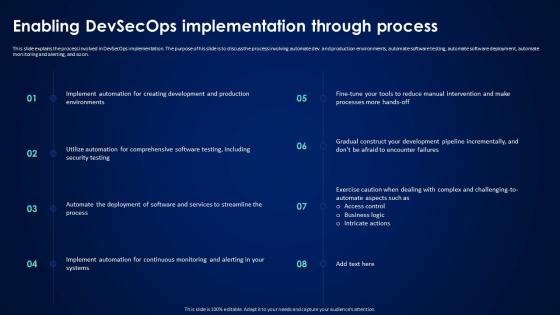 Devsecops Best Practices For Secure Enabling Devsecops Implementation Through Process
Devsecops Best Practices For Secure Enabling Devsecops Implementation Through ProcessThis slide explains the process involved in DevSecOps implementation. The purpose of his slide is to discuss the process involving automate dev. and production environments, automate software testing, automate software deployment, automate monitoring and alerting, and so on. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Enabling Devsecops Implementation Through Process. This template helps you present information on eight stages. You can also present information on Devsecops Implementation, Production Environments, Automate Software Testing, Automate Software Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
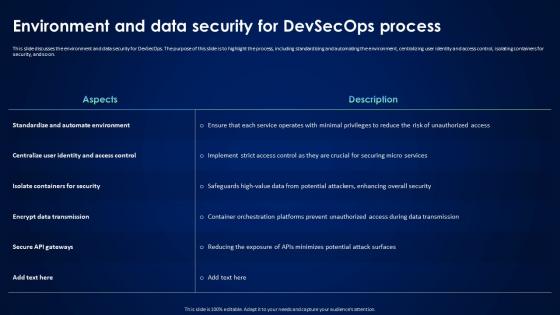 Devsecops Best Practices For Secure Environment And Data Security For Devsecops Process
Devsecops Best Practices For Secure Environment And Data Security For Devsecops ProcessThis slide discusses the environment and data security for DevSecOps. The purpose of this slide is to highlight the process, including standardizing and automating the environment, centralizing user identity and access control, isolating containers for security, and so on. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Environment And Data Security For Devsecops Process. Use it as a tool for discussion and navigation on Standardize And Automate Environment, Isolate Containers For Security, Encrypt Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Overview Of Working Process Of Devsecops Model
Devsecops Best Practices For Secure Overview Of Working Process Of Devsecops ModelThis slide discusses the workflow procedure of DevSecOps model. The purpose of this slide is to showcase the working steps of DevSecOps model for software building and enhancing security at each level these include coding, branch, repo, CI or CD, production, etc. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Overview Of Working Process Of Devsecops Model. Use it as a tool for discussion and navigation on Workflow Procedure Of Devsecops, Software Building, Enhancing Security, Production. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
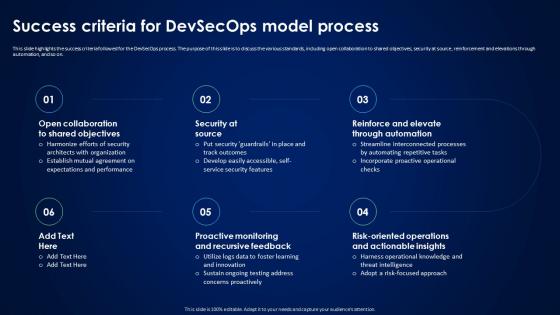 Devsecops Best Practices For Secure Success Criteria For Devsecops Model Process
Devsecops Best Practices For Secure Success Criteria For Devsecops Model ProcessThis slide highlights the success criteria followed for the DevSecOps process. The purpose of this slide is to discuss the various standards, including open collaboration to shared objectives, security at source, reinforcement and elevations through automation, and so on. Introducing Devsecops Best Practices For Secure Success Criteria For Devsecops Model Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Proactive Monitoring And Recursive, Reinforce And Elevate Through Automation, Security At Source, using this template. Grab it now to reap its full benefits.
-
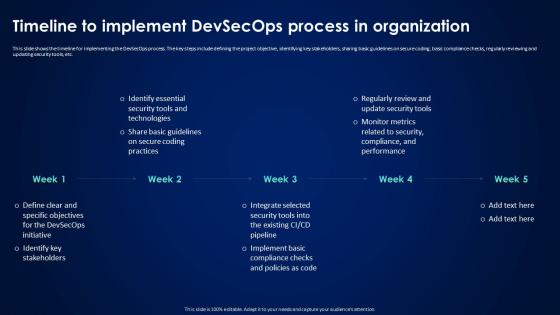 Devsecops Best Practices For Secure Timeline To Implement Devsecops Process In Organization
Devsecops Best Practices For Secure Timeline To Implement Devsecops Process In OrganizationThis slide shows the timeline for implementing the DevSecOps process. The key steps include defining the project objective, identifying key stakeholders, sharing basic guidelines on secure coding, basic compliance checks, regularly reviewing and updating security tools, etc. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Timeline To Implement Devsecops Process In Organization. This template helps you present information on five stages. You can also present information on Timeline To Implement Devsecops, Regularly Reviewing, Updating Security Tools, Sharing Basic Guidelines using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Devsecops Best Practices For Secure Various Impact Of Devsecops Process In Organization
Devsecops Best Practices For Secure Various Impact Of Devsecops Process In OrganizationThis slide discusses the various impacts of the DevSecOps process in an organization. The purpose of this slide is to explain the impact of DevSecOps in terms of security, development, operations, compliance, customer trust, and resilience. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Various Impact Of Devsecops Process In Organization. Use it as a tool for discussion and navigation on Automated Infrastructure Management, Vulnerability Management, Resilient Application Design. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IP Security For Cyber Protocol Icon
IP Security For Cyber Protocol IconPresenting our set of slides with name IP Security For Cyber Protocol Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on IP Security, Cyber Protocol Icon.
-
 Environments best suited for efficient and secure supply chains ppt rules
Environments best suited for efficient and secure supply chains ppt rulesThis slide shows the environment best suited for efficient and secure supply chain which includes various factors such as operations strategy, investment lead time, etc. Present the topic in a bit more detail with this Environments Best Suited For Efficient And Secure Supply Chains Ppt Rules. Use it as a tool for discussion and navigation on Supply Chains, Operations Strategy, Inventory Investment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Practices For Secure Online Payment Processing
Practices For Secure Online Payment ProcessingThis slide mentions practices for online payment processing to ensure secure checkout process. It includes matching IP and billing address, Encrypt data and use payment tokenization method. Introducing our premium set of slides with Practices For Secure Online Payment Processing. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Match The Ip And Billing Address, Encrypt Data, Use Payment Tokenization. So download instantly and tailor it with your information.
-
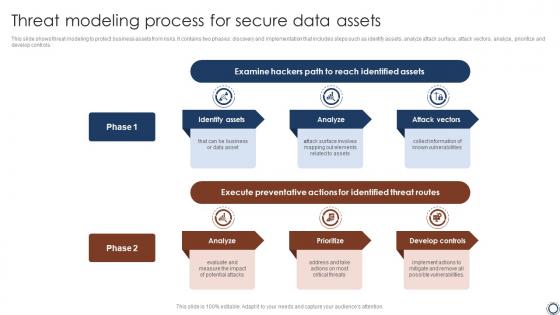 Threat Modeling Process For Secure Data Assets
Threat Modeling Process For Secure Data AssetsThis slide shows threat modeling to protect business assets from risks. It contains two phases discovery and implementation that includes steps such as identify assets, analyze attack surface, attack vectors, analyze, prioritize and develop controls. Introducing our premium set of slides with name Threat Modeling Process For Secure Data Assets. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Hackers Path, Identified Assets, Threat Routes. So download instantly and tailor it with your information.
-
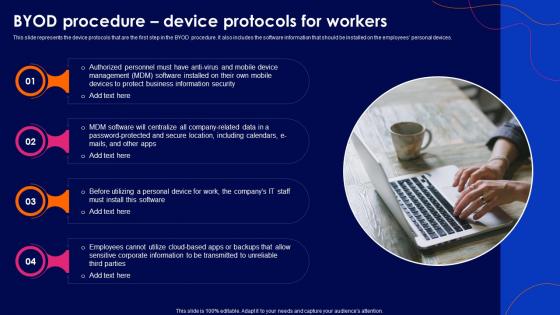 Cyber Security Policy Byod Procedure Device Protocols For Workers
Cyber Security Policy Byod Procedure Device Protocols For WorkersThis slide represents the device protocols that are the first step in the BYOD procedure. It also includes the software information that should be installed on the employees personal devices. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Byod Procedure Device Protocols For Workers. This template helps you present information on four stages. You can also present information on Software, Business, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
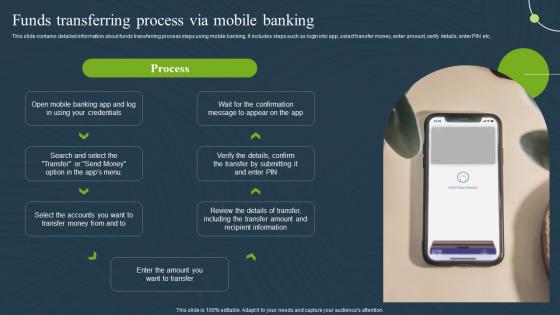 Funds Transferring Process Mobile Banking For Convenient And Secure Online Payments Fin SS
Funds Transferring Process Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide contains detailed information about funds transferring process steps using mobile banking. It includes steps such as login into app, select transfer money, enter amount, verify details, enter PIN etc. Present the topic in a bit more detail with this Funds Transferring Process Mobile Banking For Convenient And Secure Online Payments Fin SS. Use it as a tool for discussion and navigation on Transferring, Process, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
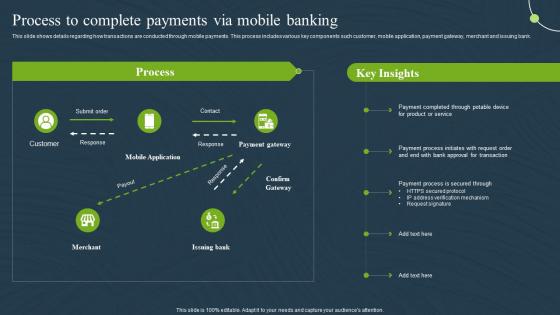 Process To Complete Banking Mobile Banking For Convenient And Secure Online Payments Fin SS
Process To Complete Banking Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide shows details regarding how transactions are conducted through mobile payments. This process includes various key components such customer, mobile application, payment gateway, merchant and issuing bank. Deliver an outstanding presentation on the topic using this Process To Complete Banking Mobile Banking For Convenient And Secure Online Payments Fin SS. Dispense information and present a thorough explanation of Process, Verification, Mechanism using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
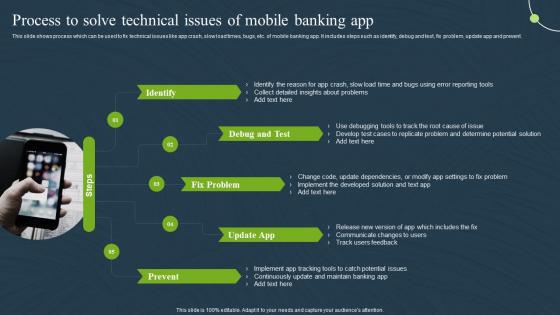 Process To Solve Technical Issues App Mobile Banking For Convenient And Secure Online Payments Fin SS
Process To Solve Technical Issues App Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide shows process which can be used to fix technical issues like app crash, slow load times, bugs, etc. of mobile banking app. It includes steps such as identify, debug and test, fix problem, update app and prevent. Introducing Process To Solve Technical Issues App Mobile Banking For Convenient And Secure Online Payments Fin SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Identify, Debug And Test, Fix Problem, using this template. Grab it now to reap its full benefits.
-
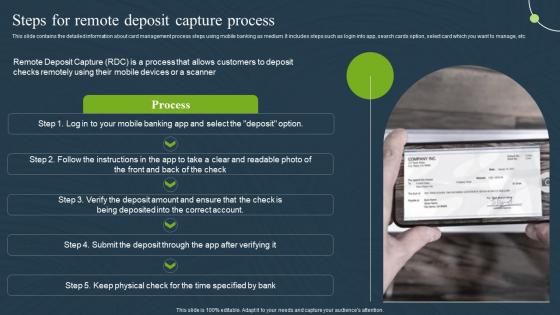 Steps For Remote Deposit Capture Process Mobile Banking For Convenient And Secure Online Payments Fin SS
Steps For Remote Deposit Capture Process Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide contains the detailed information about card management process steps using mobile banking as medium. It includes steps such as login into app, search cards option, select card which you want to manage, etc. Present the topic in a bit more detail with this Steps For Remote Deposit Capture Process Mobile Banking For Convenient And Secure Online Payments Fin SS. Use it as a tool for discussion and navigation on Process, Management, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
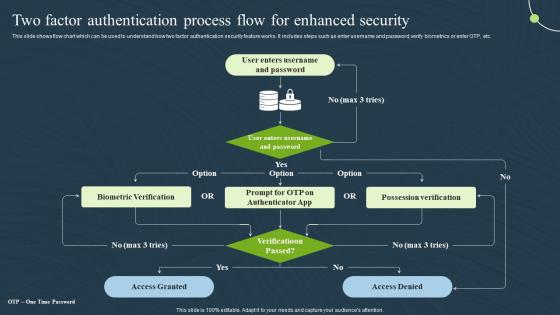 Two Factor Authentication Process Security Mobile Banking For Convenient And Secure Online Payments Fin SS
Two Factor Authentication Process Security Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide shows flow chart which can be used to understand how two factor authentication security feature works. It includes steps such as enter username and password, verify biometrics or enter OTP, etc. Present the topic in a bit more detail with this Two Factor Authentication Process Security Mobile Banking For Convenient And Secure Online Payments Fin SS. Use it as a tool for discussion and navigation on Authentication, Process, Possession Verification . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
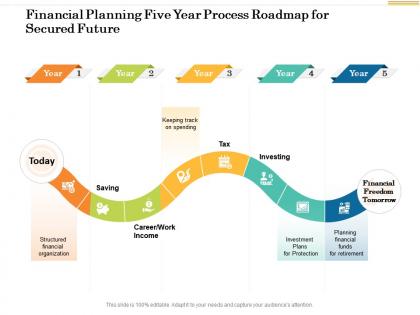 Financial planning five year process roadmap for secured future
Financial planning five year process roadmap for secured futurePresenting Financial Planning Five Year Process Roadmap For Secured Future PowerPoint Template. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements.
-
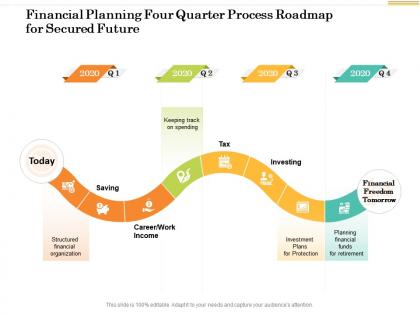 Financial planning four quarter process roadmap for secured future
Financial planning four quarter process roadmap for secured futurePresenting Financial Planning Four Quarter Process Roadmap For Secured Future PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
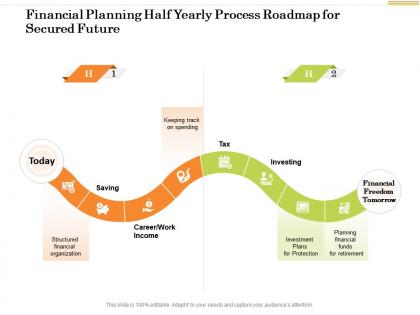 Financial planning half yearly process roadmap for secured future
Financial planning half yearly process roadmap for secured futurePresenting Financial Planning Half Yearly Process Roadmap For Secured Future PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
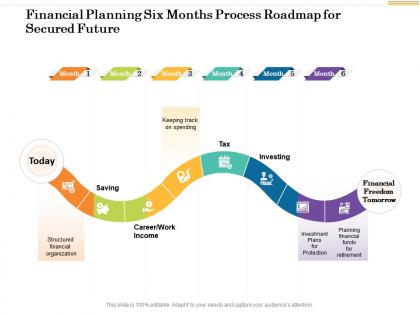 Financial planning six months process roadmap for secured future
Financial planning six months process roadmap for secured futurePresenting Financial Planning Six Months Process Roadmap For Secured Future PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
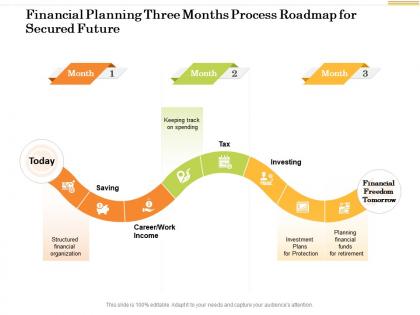 Financial planning three months process roadmap for secured future
Financial planning three months process roadmap for secured futurePresenting Financial Planning Three Months Process Roadmap For Secured Future PowerPoint slide. This PPT slide is available at 4,3 and 16,9 aspect ratios. You can download this PPT theme in various formats like PDF, PNG, and JPG. This PowerPoint template is completely editable and you can modify the font size, font type, and shapes as per your requirements. Our PPT layout is compatible with Google Slides.
-
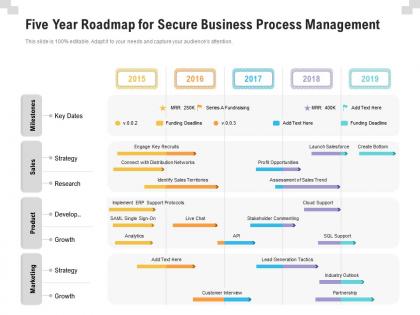 Five year roadmap for secure business process management
Five year roadmap for secure business process managementPresenting Five Year Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
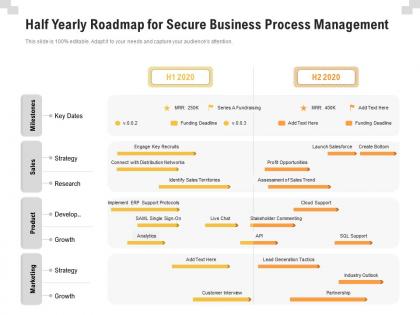 Half yearly roadmap for secure business process management
Half yearly roadmap for secure business process managementPresenting Half Yearly Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
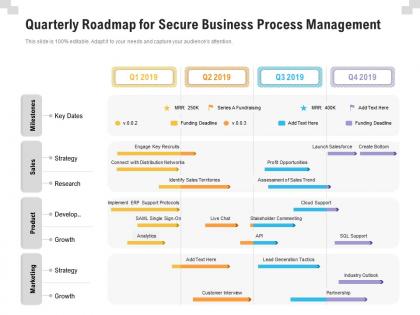 Quarterly roadmap for secure business process management
Quarterly roadmap for secure business process managementPresenting Quarterly Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
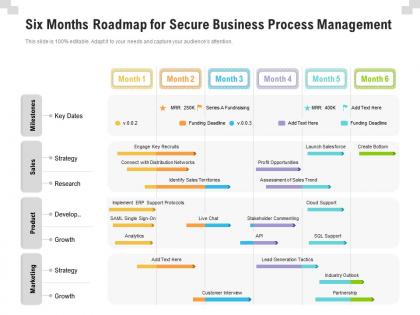 Six months roadmap for secure business process management
Six months roadmap for secure business process managementPresenting Six Months Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
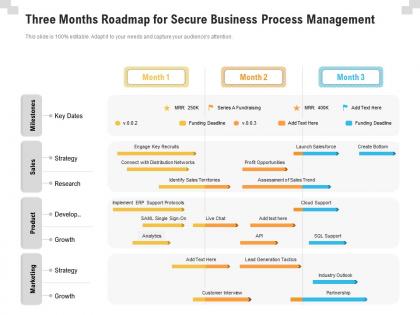 Three months roadmap for secure business process management
Three months roadmap for secure business process managementPresenting Three Months Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Proven process for secure operations icon
Proven process for secure operations iconPresenting our set of slides with name Proven Process For Secure Operations Icon. This exhibits information on one stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Process, Secure, Operations.

