Powerpoint Templates and Google slides for Secure Log Integrity
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Logging As A Type Of Application Security Training Ppt
Logging As A Type Of Application Security Training PptPresenting Logging as a Type of Application Security. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
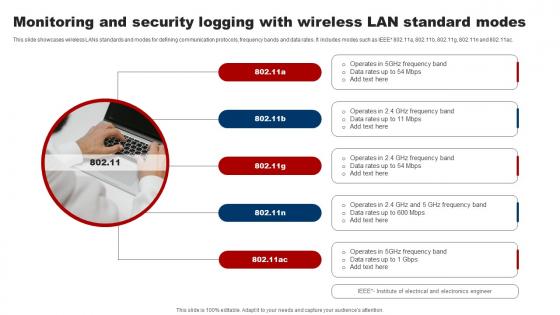 Monitoring And Security Logging With Wireless Lan Standard Modes
Monitoring And Security Logging With Wireless Lan Standard ModesThis slide showcases wireless LANs standards and modes for defining communication protocols, frequency bands and data rates. It includes modes such as IEEE 802.11a, 802.11b, 802.11g, 802.11n and 802.11ac. Introducing our premium set of slides with Monitoring And Security Logging With Wireless Lan Standard Modes. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Monitoring, Security, Standard Modes . So download instantly and tailor it with your information.
-
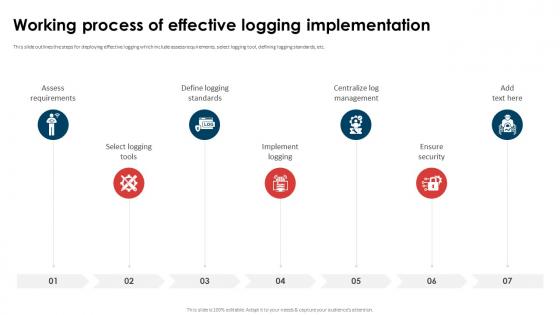 Application Security Implementation Plan Working Process Of Effective Logging Implementation
Application Security Implementation Plan Working Process Of Effective Logging ImplementationThis slide outlines the steps for deploying effective logging which include assess requirements, select logging tool, defining logging standards, etc. Introducing Application Security Implementation Plan Working Process Of Effective Logging Implementation to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Ensure Security, Centralize Log Management, Define Logging Standards, Select Logging Tools, using this template. Grab it now to reap its full benefits.
-
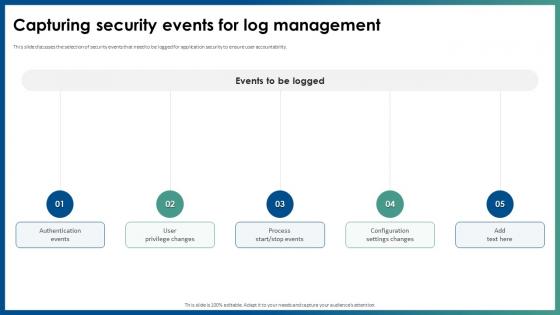 Capturing Security Events For Log Management Application Security
Capturing Security Events For Log Management Application SecurityThis slide discusses the selection of security events that need to be logged for application security to ensure user accountability. Introducing Capturing Security Events For Log Management Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Authentication Events, User Privilege Changes, Configuration Settings Changes, using this template. Grab it now to reap its full benefits.
-
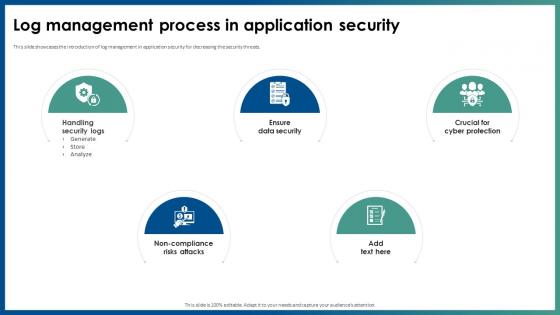 Log Management Process In Application Security
Log Management Process In Application SecurityThis slide showcases the introduction of log management in application security for decreasing the security threats. Increase audience engagement and knowledge by dispensing information using Log Management Process In Application Security. This template helps you present information on five stages. You can also present information on Handling Security Logs, Non Compliance Risks Attacks, Ensure Data Security, Log Management Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Log Management Best Practices Application Security
Security Log Management Best Practices Application SecurityThis slide highlights the best approaches of logging implementation which include preventing inappropriate actions, employ logging tools, etc. Increase audience engagement and knowledge by dispensing information using Security Log Management Best Practices Application Security. This template helps you present information on five stages. You can also present information on Scrutinize Admin And Operators, Prevent Inappropriate Actions, Ensure Authorized Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
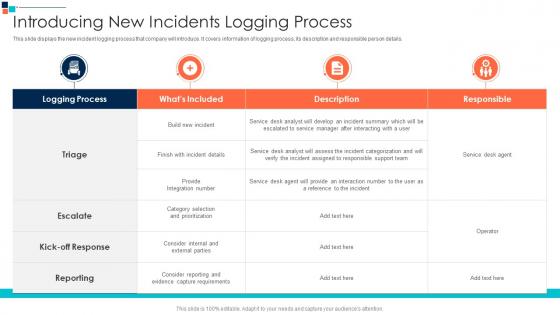 Introducing New Incidents Logging Process Introducing A Risk Based Approach To Cyber Security
Introducing New Incidents Logging Process Introducing A Risk Based Approach To Cyber SecurityThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details.Present the topic in a bit more detail with this Introducing New Incidents Logging Process Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Category Selection, Assigned To Responsible, Provide An Interaction This template is free to edit as deemed fit for your organization. Therefore download it now.
-
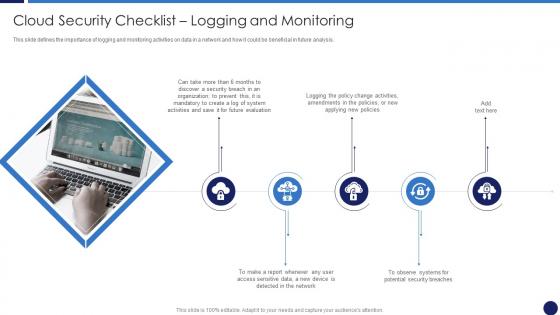 Cloud Security Checklist Logging And Monitoring Cloud Data Protection
Cloud Security Checklist Logging And Monitoring Cloud Data ProtectionThis slide defines the importance of logging and monitoring activities on data in a network and how it could be beneficial in future analysis. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Logging And Monitoring Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organization, Network, Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
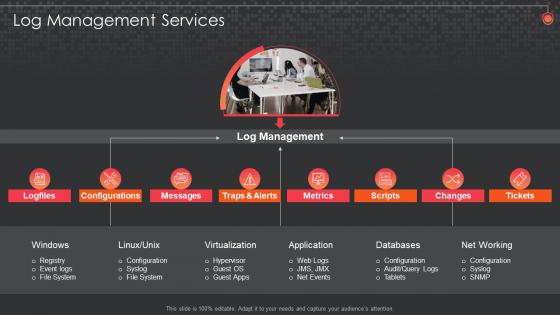 Log Management Services Siem For Security Analysis
Log Management Services Siem For Security AnalysisIntroducing Log Management Services Siem For Security Analysis to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Configurations, Databases, Management, using this template. Grab it now to reap its full benefits.
-
 Siem For Security Analysis Information And Event Management Logging Process
Siem For Security Analysis Information And Event Management Logging ProcessThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Siem For Security Analysis Information And Event Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
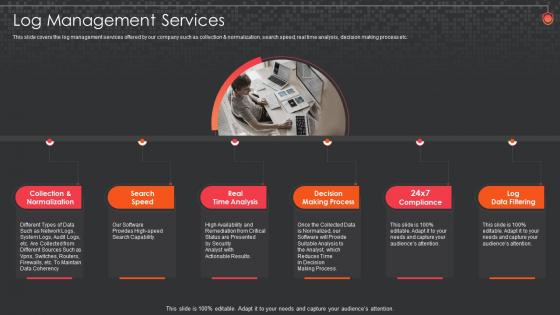 Siem For Security Analysis Log Management Services
Siem For Security Analysis Log Management ServicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Increase audience engagement and knowledge by dispensing information using Siem For Security Analysis Log Management Services. This template helps you present information on six stages. You can also present information on Log Management Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
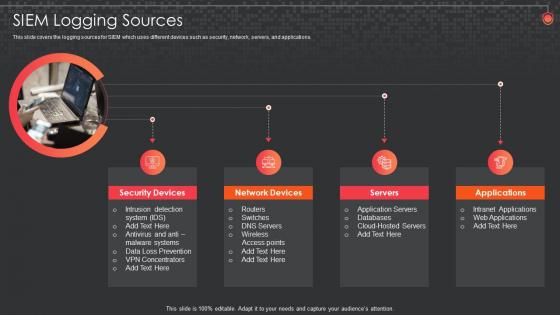 Siem For Security Analysis Logging Sources
Siem For Security Analysis Logging SourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Introducing Siem For Security Analysis Logging Sources to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Siem Logging Sources, using this template. Grab it now to reap its full benefits.
-
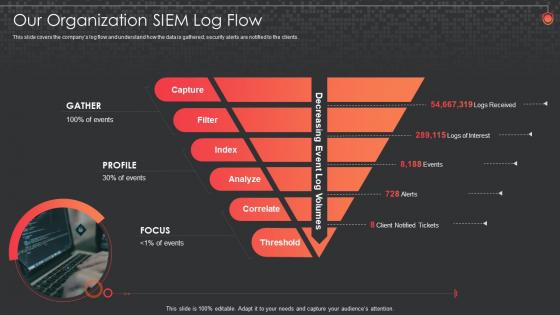 Siem For Security Analysis Organization Siem Log Flow
Siem For Security Analysis Organization Siem Log FlowThis slide covers the companys log flow and understand how the data is gathered, security alerts are notified to the clients. Increase audience engagement and knowledge by dispensing information using Siem For Security Analysis Organization Siem Log Flow. This template helps you present information on five stages. You can also present information on Our Organization Siem Log Flow using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
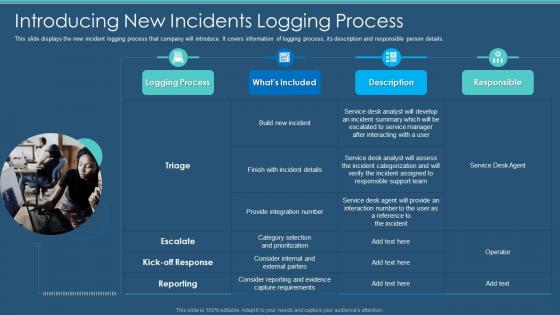 Information Security Program Cybersecurity Introducing New Incidents Logging Process
Information Security Program Cybersecurity Introducing New Incidents Logging ProcessThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details. Present the topic in a bit more detail with this Information Security Program Cybersecurity Introducing New Incidents Logging Process. Use it as a tool for discussion and navigation on Introducing New Incidents Logging Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
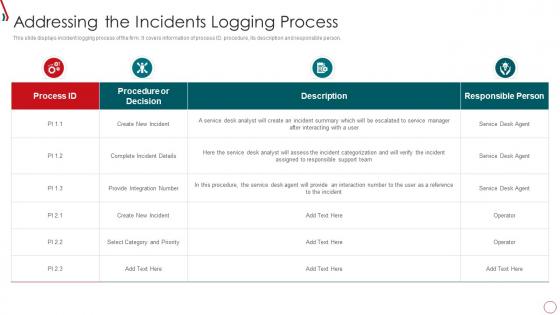 Risk Management Framework For Information Security Addressing The Incidents Logging
Risk Management Framework For Information Security Addressing The Incidents LoggingThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Addressing The Incidents Logging. Dispense information and present a thorough explanation of Create New Incident, Complete Incident Details, Provide Integration Number using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
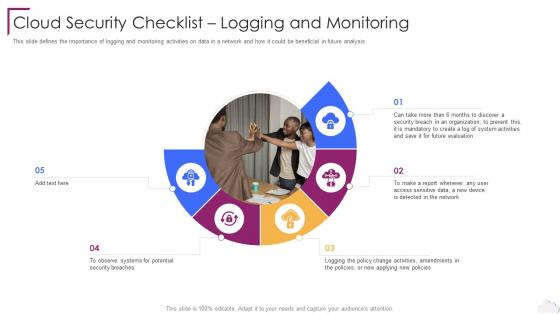 Cloud Security Checklist Logging And Monitoring Cloud Computing Security
Cloud Security Checklist Logging And Monitoring Cloud Computing SecurityThis slide defines the importance of logging and monitoring activities on data in a network and how it could be beneficial in future analysis. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Logging And Monitoring Cloud Computing Security. This template helps you present information on five stages. You can also present information on Future Evaluation, Organization, Policy Change Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Checklist Logging And Monitoring Cloud Information Security
Cloud Security Checklist Logging And Monitoring Cloud Information SecurityThis slide defines the importance of logging and monitoring activities on data in a network and how it could be beneficial in future analysis.Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Logging And Monitoring Cloud Information Security This template helps you present information on five stages. You can also present information on Data Supposed, Malware Mechanisms, Security Precautions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
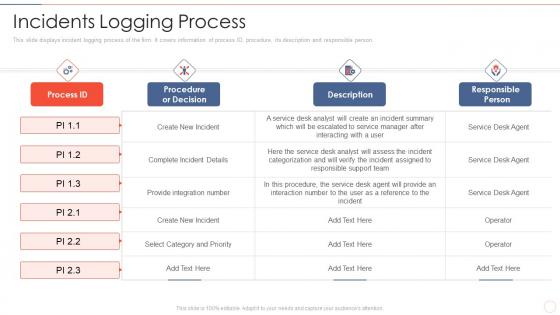 Effective information security incidents logging process
Effective information security incidents logging processThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person. Present the topic in a bit more detail with this Effective Information Security Incidents Logging Process. Use it as a tool for discussion and navigation on Complete Incident Details, Select Category And Priority, Provide Integration Number. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
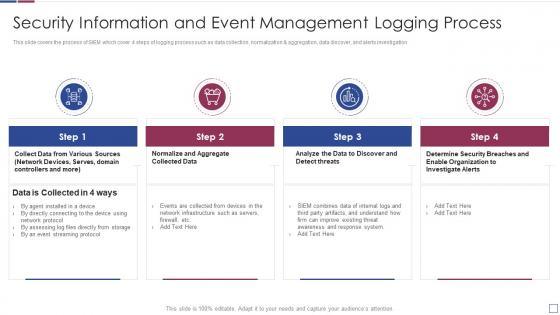 Information and event management logging process real time analysis of security alerts
Information and event management logging process real time analysis of security alertsThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Present the topic in a bit more detail with this Information And Event Management Logging Process Real Time Analysis Of Security Alerts. Use it as a tool for discussion and navigation on Information, Management, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
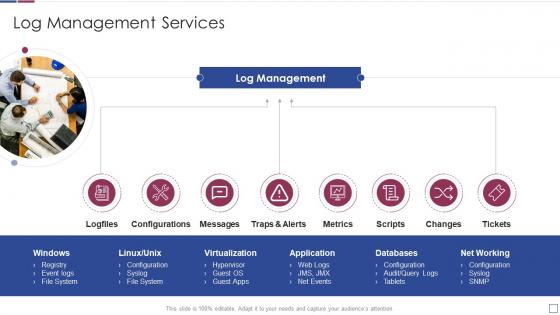 Log management services real time analysis of security alerts
Log management services real time analysis of security alertsIncrease audience engagement and knowledge by dispensing information using Log Management Services Real Time Analysis Of Security Alerts. This template helps you present information on eight stages. You can also present information on Configurations, Application, Virtualization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
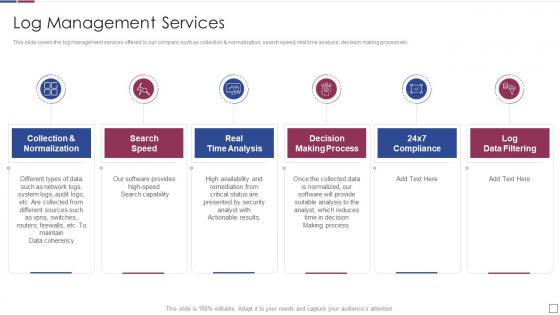 Real time analysis of security alerts log management services
Real time analysis of security alerts log management servicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Introducing Real Time Analysis Of Security Alerts Log Management Services to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Normalization, Analysis, Process, using this template. Grab it now to reap its full benefits.
-
 Real time analysis of security alerts logging sources
Real time analysis of security alerts logging sourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Increase audience engagement and knowledge by dispensing information using Real Time Analysis Of Security Alerts Logging Sources. This template helps you present information on four stages. You can also present information on Siem Logging Sources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
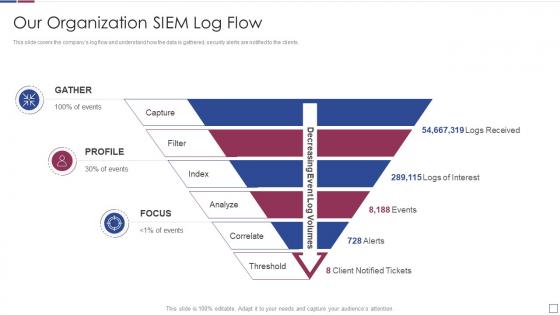 Real time analysis of security alerts organization siem log flow
Real time analysis of security alerts organization siem log flowThis slide covers the companys log flow and understand how the data is gathered, security alerts are notified to the clients. Deliver an outstanding presentation on the topic using this Real Time Analysis Of Security Alerts Organization Siem Log Flow. Dispense information and present a thorough explanation of Our Organization Siem Log Flow using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
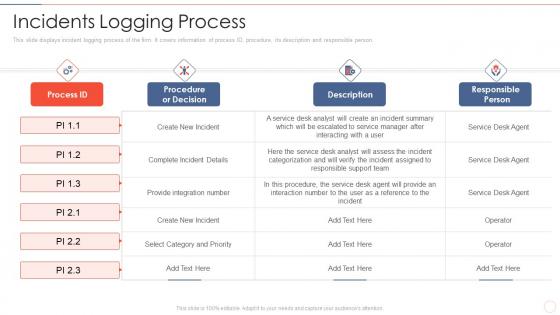 Incidents logging process effective information security risk management process
Incidents logging process effective information security risk management processThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person.Deliver an outstanding presentation on the topic using this Incidents Logging Process Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Select Category And Priority, Procedure, The Service, Responsible Person using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
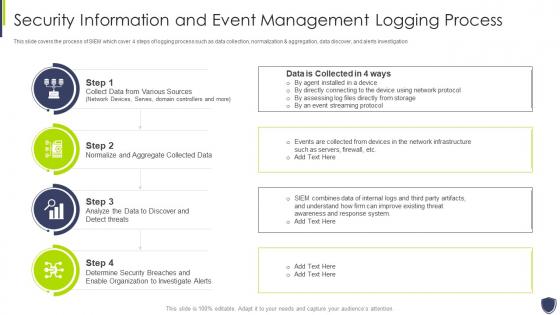 Improve it security with vulnerability information and event management logging process
Improve it security with vulnerability information and event management logging processThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Improve It Security With Vulnerability Information And Event Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management log management services
Improve it security with vulnerability management log management servicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Introducing Improve It Security With Vulnerability Management Log Management Services to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Collection And Normalization, Search Speed, Real Time Analysis, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management logging sources
Improve it security with vulnerability management logging sourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Logging Sources. This template helps you present information on four stages. You can also present information on Security Devices, Network Devices, Servers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
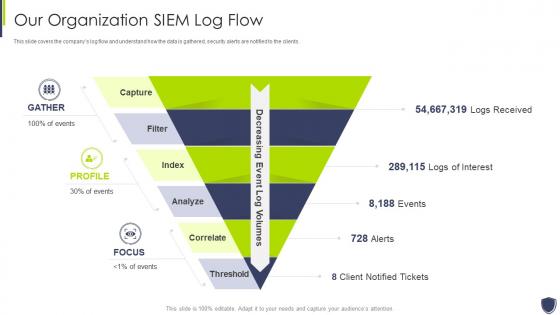 Improve it security with vulnerability management organization siem log flow
Improve it security with vulnerability management organization siem log flowThis slide covers the companys log flow and understand how the data is gathered, security alerts are notified to the clients. Introducing Improve It Security With Vulnerability Management Organization Siem Log Flow to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Our Organization Siem Log Flow, using this template. Grab it now to reap its full benefits.
-
 Log management services improve it security with vulnerability management
Log management services improve it security with vulnerability managementIncrease audience engagement and knowledge by dispensing information using Log Management Services Improve It Security With Vulnerability Management. This template helps you present information on eight stages. You can also present information on Virtualization, Application, Databases using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Log management services security information and event management
Log management services security information and event managementThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Increase audience engagement and knowledge by dispensing information using Log Management Services Security Information And Event Management. This template helps you present information on six stages. You can also present information on Log Management Services Security Information And Event Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
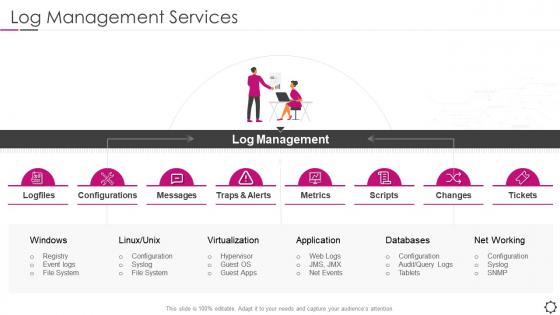 Security information and event management log management metrics
Security information and event management log management metricsIncrease audience engagement and knowledge by dispensing information using Security Information And Event Management Log Management Metrics. This template helps you present information on eight stages. You can also present information on Configurations, Virtualization, Application using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
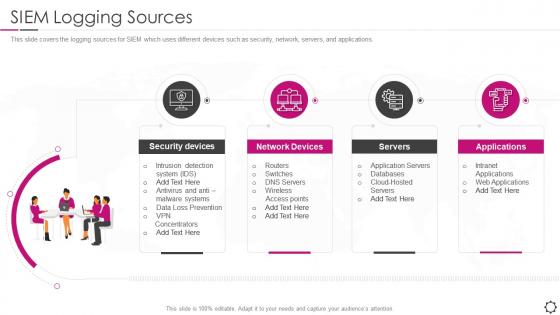 Security information and event management siem logging sources
Security information and event management siem logging sourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Increase audience engagement and knowledge by dispensing information using Security Information And Event Management SIEM Logging Sources. This template helps you present information on four stages. You can also present information on Security Devices, Network Devices, Servers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Incident Response Playbook Addressing The Cyber Incident Logging Process
Security Incident Response Playbook Addressing The Cyber Incident Logging ProcessThis slide displays logging process for a cyber incident logging. It covers information about process ID, procedure, its description and owner details. Deliver an outstanding presentation on the topic using this Security Incident Response Playbook Addressing The Cyber Incident Logging Process. Dispense information and present a thorough explanation of Process, Information, Procedure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure Logistics Packaging Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Secure Logistics Packaging Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful PowerPoint icon is perfect for representing secure delivery. It features a shield with a checkmark inside, signifying the safe and secure delivery of goods or services. It is sure to add a professional touch to any presentation.
-
 Secure Logistics Packaging Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Secure Logistics Packaging Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone powerpoint icon is perfect for illustrating secure delivery of documents or packages. It features a truck with a padlock on the back, symbolizing a safe and secure delivery process. Its a great way to show the importance of secure delivery in any presentation.
-
 Mobile location call center logs weather data advance security
Mobile location call center logs weather data advance securityPresenting this set of slides with name - Mobile Location Call Center Logs Weather Data Advance Security. This is an editable six stages graphic that deals with topics like Mobile Location, Call Center Logs, Weather Data, Advance Security to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security log management process ppt powerpoint presentation professional graphics cpb
Security log management process ppt powerpoint presentation professional graphics cpbPresenting this set of slides with name Security Log Management Process Ppt Powerpoint Presentation Professional Graphics Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Security Log Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security introduction log analytics ppt powerpoint presentation file introduction cpb
Security introduction log analytics ppt powerpoint presentation file introduction cpbPresenting this set of slides with name Security Introduction Log Analytics Ppt Powerpoint Presentation File Introduction Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Security Introduction Log Analytics to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
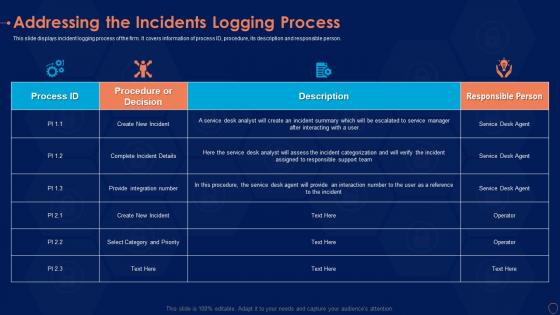 Addressing incidents logging information security risk management program
Addressing incidents logging information security risk management programThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person. Present the topic in a bit more detail with this Addressing Incidents Logging Information Security Risk Management Program. Use it as a tool for discussion and navigation on Procedure, Decision, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
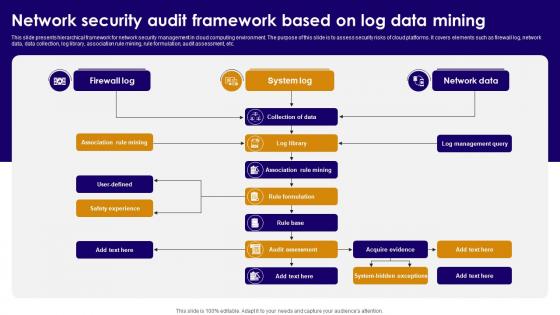 Network Security Audit Framework Based On Log Data Mining
Network Security Audit Framework Based On Log Data MiningThis slide presents hierarchical framework for network security management in cloud computing environment. The purpose of this slide is to assess security risks of cloud platforms. It covers elements such as firewall log, network data, data collection, log library, association rule mining, rule formulation, audit assessment, etc. Introducing our Network Security Audit Framework Based On Log Data Mining set of slides. The topics discussed in these slides are Firewall Log, System Log, Association Rule Mining. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.

