Powerpoint Templates and Google slides for Secure On Boarding
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Mobile Banking For Convenient And Secure Online Payments Fin CD
Mobile Banking For Convenient And Secure Online Payments Fin CDDeliver an informational PPT on various topics by using this Mobile Banking For Convenient And Secure Online Payments Fin CD. This deck focuses and implements best industry practices, thus providing a birds-eye view of the topic. Encompassed with ninty nine slides, designed using high-quality visuals and graphics, this deck is a complete package to use and download. All the slides offered in this deck are subjective to innumerable alterations, thus making you a pro at delivering and educating. You can modify the color of the graphics, background, or anything else as per your needs and requirements. It suits every business vertical because of its adaptable layout.
-
 Hands On Blockchain Security Risk Management And Best Practices BCT CD V
Hands On Blockchain Security Risk Management And Best Practices BCT CD VDeliver an informational PPT on various topics by using this Hands On Blockchain Security Risk Management And Best Practices BCT CD V. This deck focuses and implements best industry practices, thus providing a birds-eye view of the topic. Encompassed with seventy seven slides, designed using high-quality visuals and graphics, this deck is a complete package to use and download. All the slides offered in this deck are subjective to innumerable alterations, thus making you a pro at delivering and educating. You can modify the color of the graphics, background, or anything else as per your needs and requirements. It suits every business vertical because of its adaptable layout.
-
 Enterprise Mobile Security For On Device Threat Detection Powerpoint Presentation Slides
Enterprise Mobile Security For On Device Threat Detection Powerpoint Presentation SlidesThis complete deck covers various topics and highlights important concepts. It has PPT slides which cater to your business needs. This complete deck presentation emphasizes Enterprise Mobile Security For On Device Threat Detection Powerpoint Presentation Slides and has templates with professional background images and relevant content. This deck consists of total of sixty three slides. Our designers have created customizable templates, keeping your convenience in mind. You can edit the color, text and font size with ease. Not just this, you can also add or delete the content if needed. Get access to this fully editable complete presentation by clicking the download button below.
-
 One pager security project proposal template
One pager security project proposal templateThis is One Pager Security Project Proposal Template featuring A4 size content and graphics. It is designed in PowerPoint using various tools. However, you can also access it with Google Slides.
-
 One pager security system proposal template
One pager security system proposal templateGet your hands on this One Pager Security System Proposal Template PowerPoint proposal Security system is a crucial aspect of modern businesses as it helps organizations to secure multiple assets such as people and other important data. Realizing the importance of safeguarding the important data we have come up with this professionally designed deck. This proposal will arm you to introduce your team of professionals who can help secure other businesses from threats. It includes various slides that showcase project overview and goals. Additionally, it also depicts multiple services that the organization provides which includes Email marketing, cyber security, etc. You can also grab the proposal to depict the action plan timeline for a security system that incorporates various phases like evaluation and assessment, research, development, etc. Displaying the company information, its background and its mission and vision has now become easy with this proposal at your disposal. Furthermore, you can provide a glimpse to the terms and conditions of the contract in a clear and concise manner. Bag this One Pager Security System Proposal Template proposal now.
-
 Malware On Endpoints As An Information Security Threat Training Ppt
Malware On Endpoints As An Information Security Threat Training PptPresenting Malware on Endpoints as an Information Security Threat. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Securing Your Accounts As One Of The Tips For Investing In Cryptocurrency Training Ppt
Securing Your Accounts As One Of The Tips For Investing In Cryptocurrency Training PptPresenting Securing your accounts as one of the tips for Investing in Cryptocurrency. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
 Blockchain Impact On Education Industry By Providing Enhanced Security System Training Ppt
Blockchain Impact On Education Industry By Providing Enhanced Security System Training PptPresenting Blockchain Impact on Education Industry by Providing Enhanced Security System. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
 Blockchain Impact On Education Industry With Secure Cloud Storage Training Ppt
Blockchain Impact On Education Industry With Secure Cloud Storage Training PptPresenting Blockchain Impact on Education Industry with Secure Cloud Storage. These slides are 100 percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
 Discussion Question On Blockchain Security Training Ppt
Discussion Question On Blockchain Security Training PptPresenting Discussion Question on Blockchain Security. Our PowerPoint experts have included all the necessary templates, designs, icons, graphs, and other essential material. This deck is well crafted by extensive research. Slides consist of amazing visuals and appropriate content. These PPT slides can be instantly downloaded with just a click. Compatible with all screen types and monitors. Supports Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
 Blockchain Impact On Drugs Supply Chain With Enhanced Security Training Ppt
Blockchain Impact On Drugs Supply Chain With Enhanced Security Training PptPresenting Blockchain Impact on Drugs Supply Chain with Enhanced Security. These slides are 100 percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
 Data security it impact on organization after implementing data security strategy
Data security it impact on organization after implementing data security strategyThis slide depicts the impact of data security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Deliver an outstanding presentation on the topic using this Data Security IT Impact On Organization After Implementing Data Security Strategy. Dispense information and present a thorough explanation of Phishing, Network Intrusion, Inadvertent Disclosure, System Misconfiguration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
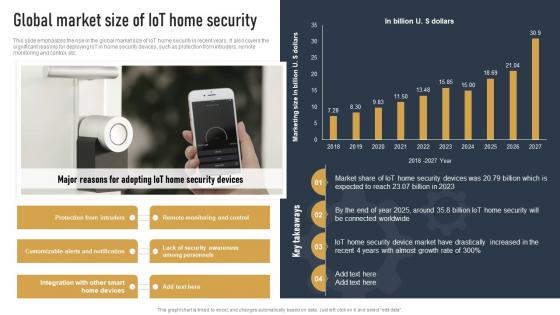 Global Market Size Of IOT Home Security Impact Of IOT On Various Industries IOT SS
Global Market Size Of IOT Home Security Impact Of IOT On Various Industries IOT SSThis slide emphasizes the rise in the global market size of IoT home security in recent years. It also covers the significant reasons for deploying IoT in home security devices, such as protection from intruders, remote monitoring and control, etc. Deliver an outstanding presentation on the topic using this Global Market Size Of IOT Home Security Impact Of IOT On Various Industries IOT SS. Dispense information and present a thorough explanation of Protection From Intruders, Major Reasons, Security Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
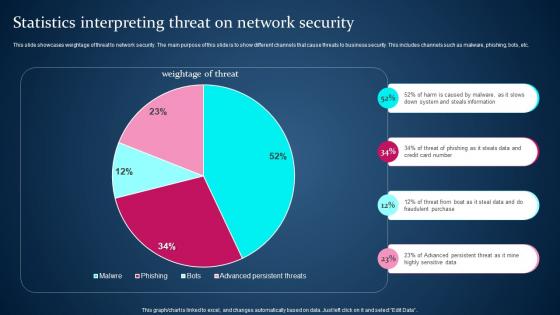 Statistics Interpreting Threat On Network Security
Statistics Interpreting Threat On Network SecurityThis slide showcases weightage of threat to network security. The main purpose of this slide is to show different channels that cause threats to business security. This includes channels such as malware, phishing, bots, etc. Presenting our well structured Statistics Interpreting Threat On Network Security. The topics discussed in this slide are Steals Information, Credit Card Number.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Secops V2 Effective Implementation Impact On Security Breaches
Secops V2 Effective Implementation Impact On Security BreachesThis slide outlines the successful implementation impact of SecOps on organizational security breaches. The purpose of this slide is to highlight the number of reduced security breaches inside a company after implementing SecOps. Security breaches include phishing, network intrusion, and so on. Present the topic in a bit more detail with this Secops V2 Effective Implementation Impact On Security Breaches. Use it as a tool for discussion and navigation on Network Intrusion, Security Breaches, Sensitive Data Leakage, Configuration Information Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Credit And Debit Payment On Business Enhancing Transaction Security With E Payment
Impact Of Credit And Debit Payment On Business Enhancing Transaction Security With E PaymentMentioned slide demonstrates impact of multiple card payment adoption on business growth. It includes key metrics such as business sales, customer satisfaction, convenience and expense tracking accuracy. Present the topic in a bit more detail with this Impact Of Credit And Debit Payment On Business Enhancing Transaction Security With E Payment Use it as a tool for discussion and navigation on Business Sales, Payment, Business This template is free to edit as deemed fit for your organization. Therefore download it now.
-
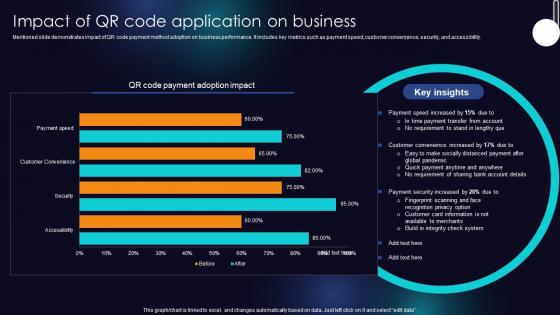 Impact Of QR Code Application On Business Enhancing Transaction Security With E Payment
Impact Of QR Code Application On Business Enhancing Transaction Security With E PaymentMentioned slide demonstrates impact of QR code payment method adoption on business performance. It includes key metrics such as payment speed, customer convenience, security, and accessibility. Present the topic in a bit more detail with this Impact Of QR Code Application On Business Enhancing Transaction Security With E Payment Use it as a tool for discussion and navigation on Payment Speed, Account Details, Customer This template is free to edit as deemed fit for your organization. Therefore download it now.
-
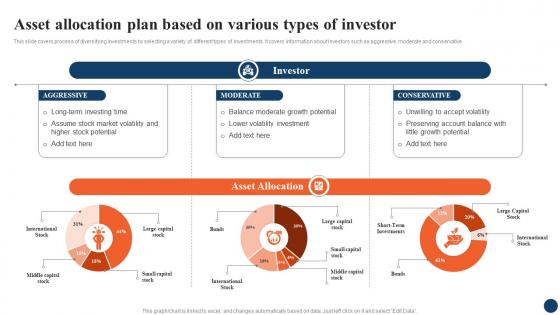 Asset Allocation Plan Based On Various Strategic Retirement Planning To Build Secure Future Fin SS
Asset Allocation Plan Based On Various Strategic Retirement Planning To Build Secure Future Fin SSThis slide covers process of diversifying investments by selecting a variety of different types of investments. It covers information about investors such as aggressive, moderate and conservative. Present the topic in a bit more detail with this Asset Allocation Plan Based On Various Strategic Retirement Planning To Build Secure Future Fin SS. Use it as a tool for discussion and navigation on Aggressive, Moderate, Conservative. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
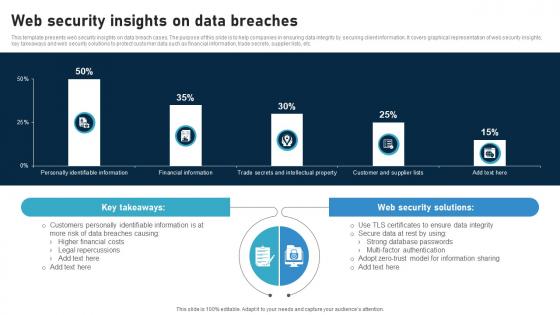 Web Security Insights On Data Breaches
Web Security Insights On Data BreachesThis template presents web security insights on data breach cases. The purpose of this slide is to help companies in ensuring data integrity by securing client information. It covers graphical representation of web security insights, key takeaways and web security solutions to protect customer data such as financial information, trade secrets, supplier lists, etc. Presenting our well structured Web Security Insights On Data Breaches The topics discussed in this slide are Web Security Solutions, Customers, Data This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
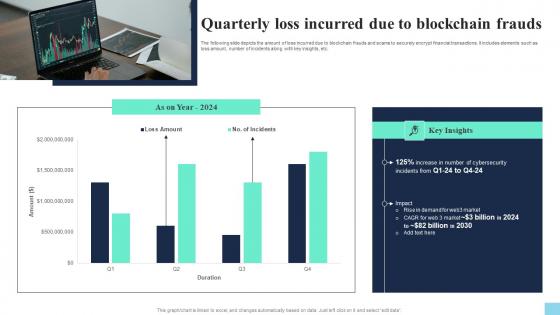 Quarterly Loss Incurred Due To Blockchain Frauds Hands On Blockchain Security Risk BCT SS V
Quarterly Loss Incurred Due To Blockchain Frauds Hands On Blockchain Security Risk BCT SS VThe following slide depicts the amount of loss incurred due to blockchain frauds and scams to securely encrypt financial transactions. It includes elements such as loss amount, number of incidents along with key insights, etc. Present the topic in a bit more detail with this Quarterly Loss Incurred Due To Blockchain Frauds Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Quarterly Loss Incurred Due. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
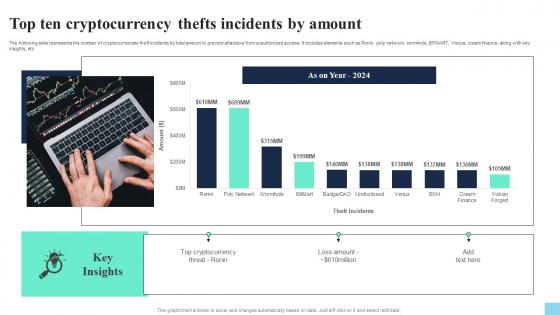 Top Ten Cryptocurrency Thefts Incidents By Amount Hands On Blockchain Security Risk BCT SS V
Top Ten Cryptocurrency Thefts Incidents By Amount Hands On Blockchain Security Risk BCT SS VThe following slide represents the number of cryptocurrencies theft incidents by total amount to prevent attackers from unauthorized access. It includes elements such as Ronin, poly network, wormhole, BITMART, Venus, cream finance, along with key insights, etc. Present the topic in a bit more detail with this Top Ten Cryptocurrency Thefts Incidents By Amount Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Top Ten Cryptocurrency, Thefts Incidents By Amount. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
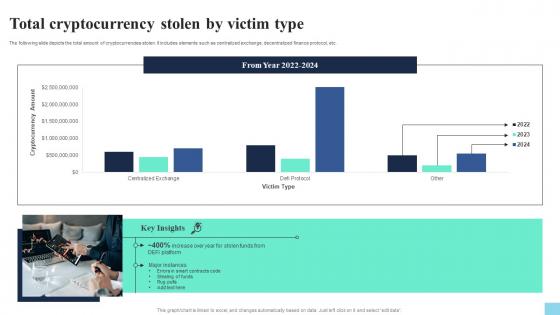 Total Cryptocurrency Stolen By Victim Type Hands On Blockchain Security Risk BCT SS V
Total Cryptocurrency Stolen By Victim Type Hands On Blockchain Security Risk BCT SS VThe following slide depicts the total amount of cryptocurrencies stolen. It includes elements such as centralized exchange, decentralized finance protocol, etc. Deliver an outstanding presentation on the topic using this Total Cryptocurrency Stolen By Victim Type Hands On Blockchain Security Risk BCT SS V. Dispense information and present a thorough explanation of Total Cryptocurrency, Stolen By Victim Type using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
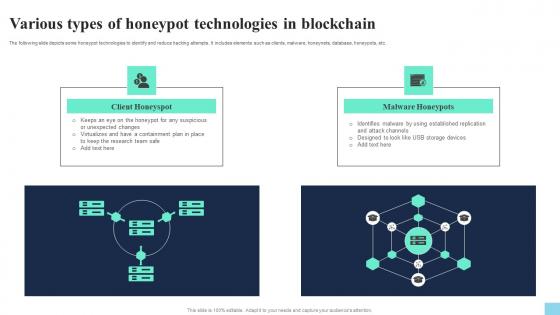 Various Types Of Honeypot Technologies In Blockchain Hands On Blockchain Security Risk BCT SS V
Various Types Of Honeypot Technologies In Blockchain Hands On Blockchain Security Risk BCT SS VThe following slide depicts some honeypot technologies to identify and reduce hacking attempts. It includes elements such as clients, malware, honeynets, database, honeypots, etc. Increase audience engagement and knowledge by dispensing information using Various Types Of Honeypot Technologies In Blockchain Hands On Blockchain Security Risk BCT SS V. This template helps you present information on two stages. You can also present information on Client Honeyspot, Malware Honeypots using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
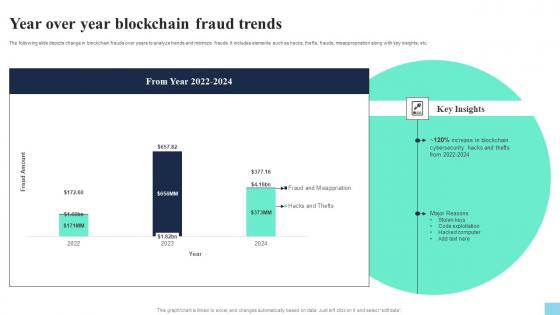 Year Over Year Blockchain Fraud Trends Hands On Blockchain Security Risk BCT SS V
Year Over Year Blockchain Fraud Trends Hands On Blockchain Security Risk BCT SS VThe following slide depicts change in blockchain frauds over years to analyze trends and minimize frauds. It includes elements such as hacks, thefts, frauds, misappropriation along with key insights, etc. Present the topic in a bit more detail with this Year Over Year Blockchain Fraud Trends Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Year Over Year, Blockchain Fraud Trends. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
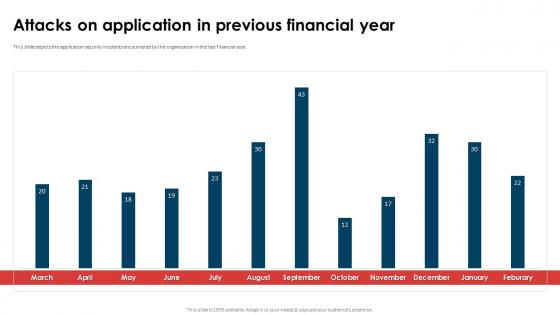 Application Security Implementation Plan Attacks On Application In Previous Financial Year
Application Security Implementation Plan Attacks On Application In Previous Financial YearThis slide depicts the threat scanning dashboard for application security to analyze and monitor vulnerabilities of application. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Attacks On Application In Previous Financial Year. Dispense information and present a thorough explanation of Attacks On Application, Previous Financial Year, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
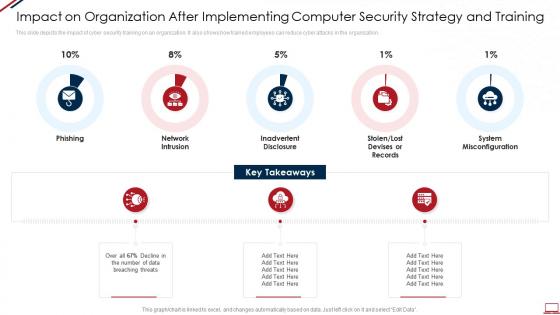 Computer system security impact on organization after implementing computer security strategy and training
Computer system security impact on organization after implementing computer security strategy and trainingThis slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Increase audience engagement and knowledge by dispensing information using Computer System Security Impact On Organization After Implementing Computer Security Strategy And Training. This template helps you present information on five stages. You can also present information on Phishing, Network Intrusion, Inadvertent Disclosure, Stolen Or Lost Devises Or Records, System Misconfiguration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 E mail safeguard industry report on premise e mail security ppt slides format
E mail safeguard industry report on premise e mail security ppt slides formatThis slide displays the overview and key features of On Premise E Mail Security. Increase audience engagement and knowledge by dispensing information using E Mail Safeguard Industry Report On Premise E Mail Security Ppt Slides Format. This template helps you present information on eight stages. You can also present information on Integrated Other Systems, Authenticated Protection Over Server Keys, Integrates Existing System, E Mail Encryption, IT Data Connected And Encrypted using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
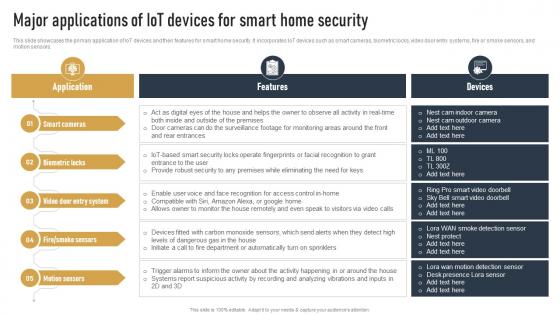 Major Applications Of IOT Devices For Smart Home Security Impact Of IOT On Various Industries IOT SS
Major Applications Of IOT Devices For Smart Home Security Impact Of IOT On Various Industries IOT SSThis slide showcases the primary application of IoT devices and their features for smart home security. It incorporates IoT devices such as smart cameras, biometric locks, video door entry systems, fire or smoke sensors, and motion sensors. Deliver an outstanding presentation on the topic using this Major Applications Of IOT Devices For Smart Home Security Impact Of IOT On Various Industries IOT SS. Dispense information and present a thorough explanation of Smart Cameras, Biometric Locks, Video Door Entry System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
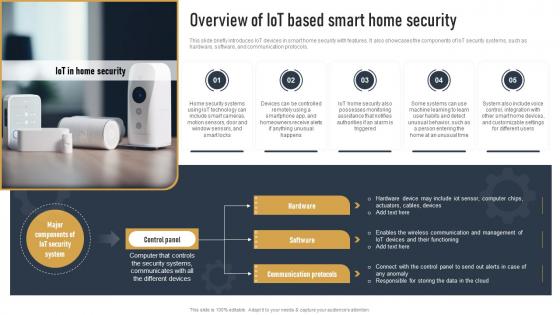 Overview Of IOT Based Smart Home Security Impact Of IOT On Various Industries IOT SS
Overview Of IOT Based Smart Home Security Impact Of IOT On Various Industries IOT SSThis slide briefly introduces IoT devices in smart home security with features. It also showcases the components of IoT security systems, such as hardware, software, and communication protocols. Introducing Overview Of IOT Based Smart Home Security Impact Of IOT On Various Industries IOT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Hardware, Software, Communication Protocols, using this template. Grab it now to reap its full benefits.
-
 Capital One Secured Mastercard Reviews In Powerpoint And Google Slides Cpb
Capital One Secured Mastercard Reviews In Powerpoint And Google Slides CpbPresenting Capital One Secured Mastercard Reviews In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Capital One Secured Mastercard Reviews. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Impact Of Encryption Implementation On Cloud Security Cloud Data Encryption
Impact Of Encryption Implementation On Cloud Security Cloud Data EncryptionThis slide represents the various factors that showcase the improvement of application security after adopting encryption. The parameters discussed are unauthorized access, data breaches, malware and ransomware, phishing attacks, etc. Deliver an outstanding presentation on the topic using this Impact Of Encryption Implementation On Cloud Security Cloud Data Encryption. Dispense information and present a thorough explanation of Unauthorized Access, Data Breaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
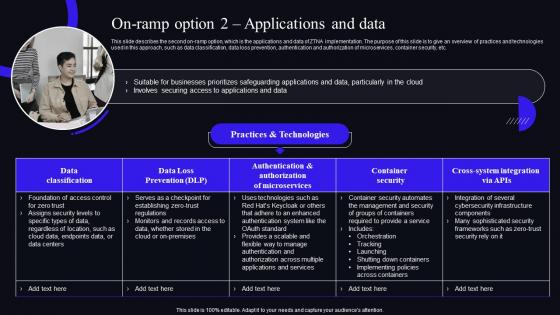 On Ramp Option 2 Applications And Data Zero Trust Security Model
On Ramp Option 2 Applications And Data Zero Trust Security ModelThis slide describes the second on-ramp option, which is the applications and data of ZTNA implementation. The purpose of this slide is to give an overview of practices and technologies used in this approach, such as data classification, data loss prevention, authentication and authorization of microservices, container security, etc. Deliver an outstanding presentation on the topic using this On Ramp Option 2 Applications And Data Zero Trust Security Model. Dispense information and present a thorough explanation of Authentication, Authorization, Microservices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
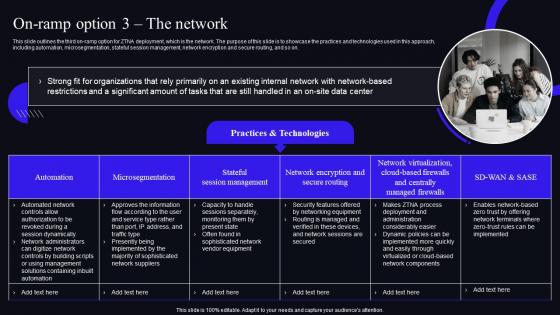 On Ramp Option 3 The Network Zero Trust Security Model
On Ramp Option 3 The Network Zero Trust Security ModelThis slide outlines the third on-ramp option for ZTNA deployment, which is the network. The purpose of this slide is to showcase the practices and technologies used in this approach, including automation, microsegmentation, stateful session management, network encryption and secure routing, and so on. Present the topic in a bit more detail with this On Ramp Option 3 The Network Zero Trust Security Model. Use it as a tool for discussion and navigation on Organizations, Microsegmentation, Stateful Session Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
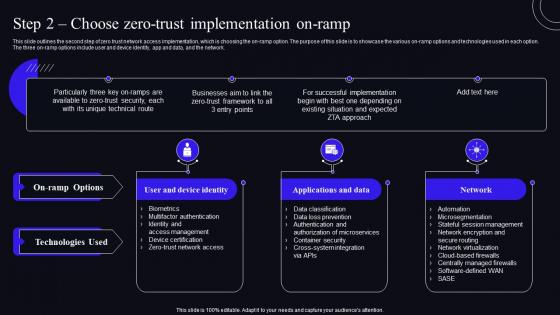 Step 2 Choose Zero Trust Implementation On Ramp Zero Trust Security Model
Step 2 Choose Zero Trust Implementation On Ramp Zero Trust Security ModelThis slide outlines the second step of zero trust network access implementation, which is choosing the on-ramp option. The purpose of this slide is to showcase the various on-ramp options and technologies used in each option. The three on-ramp options include user and device identity, app and data, and the network. Present the topic in a bit more detail with this Step 2 Choose Zero Trust Implementation On Ramp Zero Trust Security Model. Use it as a tool for discussion and navigation on User And Device Identity, Applications And Data, Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
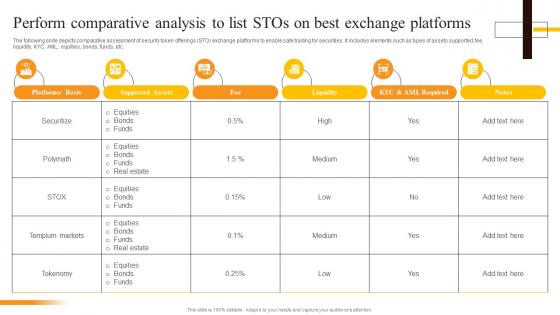 Perform Comparative Analysis To List STOs On Best Exchange Security Token Offerings BCT SS
Perform Comparative Analysis To List STOs On Best Exchange Security Token Offerings BCT SSThe following slide depicts comparative assessment of security token offerings STO exchange platforms to enable safe trading for securities. It includes elements such as types of assets supported, fee, liquidity, KYC, AML, equities, bonds, funds, etc. Present the topic in a bit more detail with this Perform Comparative Analysis To List STOs On Best Exchange Security Token Offerings BCT SS. Use it as a tool for discussion and navigation on Platforms, Supported Assets, Liquidity, Perform Comparative. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Secure Web Gateway On Application Security Network Security Using Secure Web Gateway
Impact Of Secure Web Gateway On Application Security Network Security Using Secure Web GatewayThis slide represents the various factors which showcase the improvement of application security after adopting SWG. The parameters discussed are enhanced protection against web-based attacks, content filtering, policy enforcement, Data Loss Prevention, etc. Present the topic in a bit more detail with this Impact Of Secure Web Gateway On Application Security Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Enforcement, Application, Prevention. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Methods To Implement Security Policies On Network Security Using Secure Web Gateway
Methods To Implement Security Policies On Network Security Using Secure Web GatewayThis slide demonstrates the different ways to enforce policies on remote and on-site employees using SWG. These are data loss prevention, encrypted traffic examination, protocol support, integration with anti-malware zero-day products, location flexibility, etc. Deliver an outstanding presentation on the topic using this Methods To Implement Security Policies On Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Organizational, Examination, Integration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
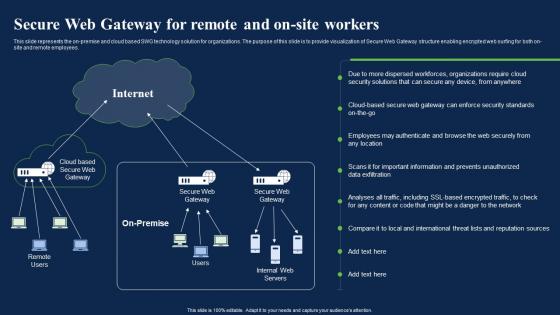 Secure Web Gateway For Remote And On Site Workers Network Security Using Secure Web Gateway
Secure Web Gateway For Remote And On Site Workers Network Security Using Secure Web GatewayThis slide represents the on-premise and cloud based SWG technology solution for organizations. The purpose of this slide is to provide visualization of Secure Web Gateway structure enabling encrypted web surfing for both on-site and remote employees. Present the topic in a bit more detail with this Secure Web Gateway For Remote And On Site Workers Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Authenticate, Information, Sources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
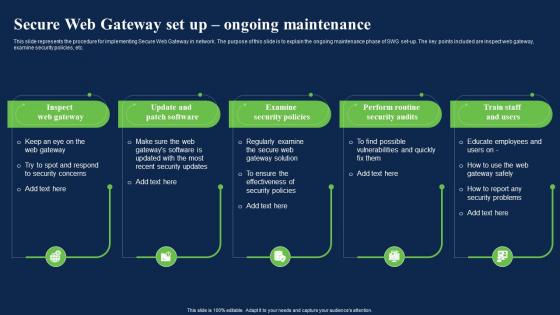 Secure Web Gateway Ongoing Maintenance Network Security Using Secure Web Gateway
Secure Web Gateway Ongoing Maintenance Network Security Using Secure Web GatewayThis slide represents the procedure for implementing Secure Web Gateway in network. The purpose of this slide is to explain the ongoing maintenance phase of SWG set-up. The key points included are inspect web gateway, examine security policies, etc. Introducing Secure Web Gateway Ongoing Maintenance Network Security Using Secure Web Gateway to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Inspect Web Gateway, Examine Security Policies, Perform Routine Security Audits, using this template. Grab it now to reap its full benefits.
-
 Secured Mastercard Capital One In Powerpoint And Google Slides Cpb
Secured Mastercard Capital One In Powerpoint And Google Slides CpbPresenting Secured Mastercard Capital One In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Secured Mastercard Capital One. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
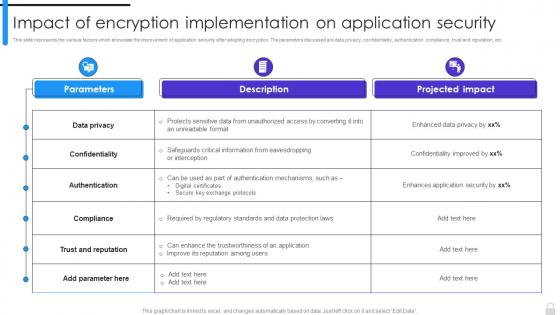 Encryption Implementation Strategies Impact Of Encryption Implementation On Application Security
Encryption Implementation Strategies Impact Of Encryption Implementation On Application SecurityThis slide represents the various factors which showcase the improvement of application security after adopting encryption. The parameters discussed are data privacy, confidentiality, authentication, compliance, trust and reputation, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Impact Of Encryption Implementation On Application Security. Dispense information and present a thorough explanation of Confidentiality, Data Privacy, Trust And Reputation, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
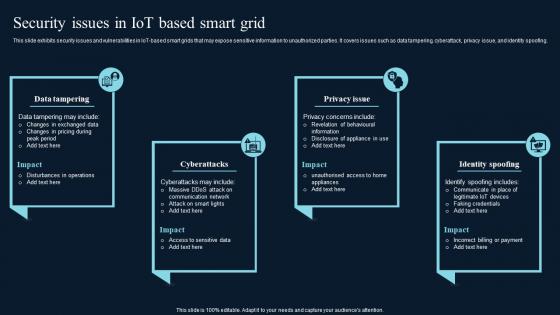 Security Issues In IoT Based Smart Grid Comprehensive Guide On IoT Enabled IoT SS
Security Issues In IoT Based Smart Grid Comprehensive Guide On IoT Enabled IoT SSThis slide exhibits security issues and vulnerabilities in IoT based smart grids that may expose sensitive information to unauthorized parties. It covers issues such as data tampering, cyberattack, privacy issue, and identity spoofing.Increase audience engagement and knowledge by dispensing information using Security Issues In IoT Based Smart Grid Comprehensive Guide On IoT Enabled IoT SS. This template helps you present information on four stages. You can also present information on Data Tampering, Communication Network, Identify Spoofing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
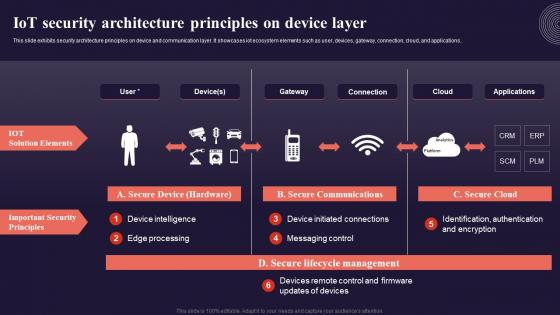 Iot Security Architecture Principles On Device Layer Introduction To Internet Of Things IoT SS
Iot Security Architecture Principles On Device Layer Introduction To Internet Of Things IoT SSThis slide exhibits security architecture principles on device and communication layer. It showcases iot ecosystem elements such as user, devices, gateway, connection, cloud, and applications. Present the topic in a bit more detail with this Iot Security Architecture Principles On Device Layer Introduction To Internet Of Things IoT SS. Use it as a tool for discussion and navigation on Iot Solution Elements, Important Security Principles. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Consequences Of Security Challenge On Mining How IoT Technology Is Transforming IoT SS
Consequences Of Security Challenge On Mining How IoT Technology Is Transforming IoT SSThe following slide showcases impact of Internet of Things IoT security challenges on mining companies. The slide covers information about unsafe working conditions, lost data, higher downtime, data leak, cost associated with security incident, loss of productivity, etc.Increase audience engagement and knowledge by dispensing information using Consequences Of Security Challenge On Mining How IoT Technology Is Transforming IoT SS. This template helps you present information on five stages. You can also present information on Compromised Smart, Working Conditions, Higher Downtime using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secured Card Capital One In Powerpoint And Google Slides Cpb
Secured Card Capital One In Powerpoint And Google Slides CpbPresenting Secured Card Capital One In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Secured Card Capital One. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
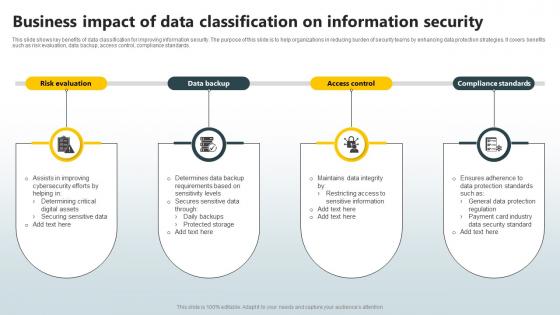 Business Impact Of Data Classification On Information Security
Business Impact Of Data Classification On Information SecurityThis slide shows key benefits of data classification for improving information security. The purpose of this slide is to help organizations in reducing burden of security teams by enhancing data protection strategies. It covers benefits such as risk evaluation, data backup, access control, compliance standards. Presenting our set of slides with Business Impact Of Data Classification On Information Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on General Data Protection Regulation, Compliance Standard, Protected Storage.
-
 Analyse Impact Of Cyber Attack On Valuable Implementing Strategies To Mitigate Cyber Security Threats
Analyse Impact Of Cyber Attack On Valuable Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the consequences of data breach threats to prevent information leakage. It mainly includes elements such as impact on revenue, protection cost, liability if lost, weightage criteria, asset importance etc. Deliver an outstanding presentation on the topic using this Analyse Impact Of Cyber Attack On Valuable Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Criteria, Impact On Revenue, Protection Cost using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
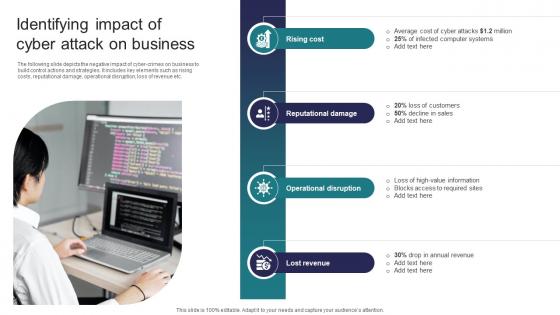 Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security Threats
Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the negative impact of cyber crimes on business to build control actions and strategies. It includes key elements such as rising costs, reputational damage, operational disruption, loss of revenue etc. Introducing Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Rising Cost, Reputational Damage, Operational Disruption using this template. Grab it now to reap its full benefits.
-
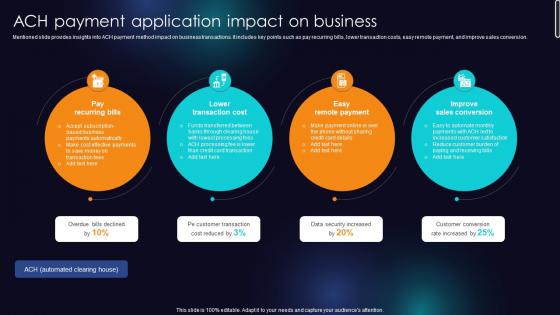 ACH Payment Application Impact On Business Enhancing Transaction Security With E Payment
ACH Payment Application Impact On Business Enhancing Transaction Security With E PaymentMentioned slide provides insights into ACH payment method impact on business transactions. It includes key points such as pay recurring bills, lower transaction costs, easy remote payment, and improve sales conversion. Introducing ACH Payment Application Impact On Business Enhancing Transaction Security With E Payment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Pay Recurring Bills, Lower Transaction Cost, Easy Remote Payment using this template. Grab it now to reap its full benefits.
-
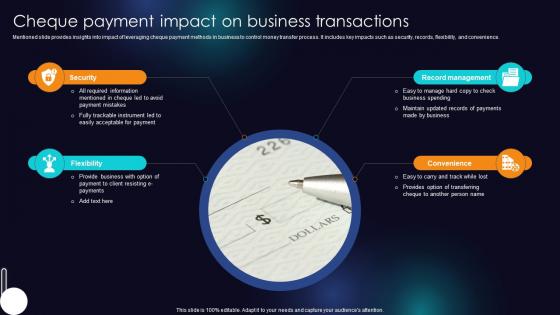 Cheque Payment Impact On Business Transactions Enhancing Transaction Security With E Payment
Cheque Payment Impact On Business Transactions Enhancing Transaction Security With E PaymentMentioned slide provides insights into impact of leveraging cheque payment methods in business to control money transfer process. It includes key impacts such as security, records, flexibility, and convenience. Introducing Cheque Payment Impact On Business Transactions Enhancing Transaction Security With E Payment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Security, Flexibility, Record Management using this template. Grab it now to reap its full benefits.
-
 Impact Of Accepting Cryptocurrency Payments On Business Sales Enhancing Transaction Security With E Payment
Impact Of Accepting Cryptocurrency Payments On Business Sales Enhancing Transaction Security With E PaymentMentioned slide showcases statistics associates with impact of cryptocurrency implementation in business. It includes key metrics such as transaction cost, merchant protection, customer convenience and business sales. Present the topic in a bit more detail with this Impact Of Accepting Cryptocurrency Payments On Business Sales Enhancing Transaction Security With E Payment Use it as a tool for discussion and navigation on Transaction Cost, Merchant Protection Level, Customer Convenience This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Cashless Payment On Different Stakeholder Enhancing Transaction Security With E Payment
Impact Of Cashless Payment On Different Stakeholder Enhancing Transaction Security With E PaymentFollowing slide provides information about various benefits of cashless payment availed by business stakeholders. It includes key stakeholders such as business owners, customers, sponsors, partners and marketing employees. Introducing Impact Of Cashless Payment On Different Stakeholder Enhancing Transaction Security With E Payment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Business Owners, Customers, Sponsors And Partners using this template. Grab it now to reap its full benefits.
-
 KYC Verification Icon For Secure Merchant Onboarding
KYC Verification Icon For Secure Merchant OnboardingIntroducing our premium set of slides with KYC Verification Icon For Secure Merchant Onboarding. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like KYC Verification Icon, Secure Merchant Onboarding. So download instantly and tailor it with your information.
-
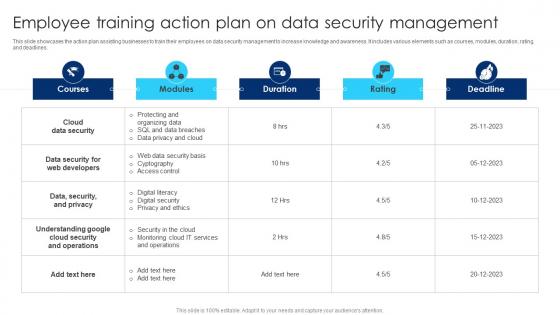 Employee Training Action Plan On Data Security Management
Employee Training Action Plan On Data Security ManagementThis slide showcases the action plan assisting businesses to train their employees on data security management to increase knowledge and awareness. It includes various elements such as courses, modules, duration, rating and deadlines. Introducing our Employee Training Action Plan On Data Security Management set of slides. The topics discussed in these slides are Cloud Data Security, Security And Privacy, Cloud Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Impact Of Cyber Security Threats On Organisational Policy
Impact Of Cyber Security Threats On Organisational PolicyThis slide covers the negative impacts of prevalent cybersecurity threats. This template aims to highlight two key negative impacts of threats, including DNS Attacks, SQL Injection, Malware, Phishing, and Ransomware. Presenting our set of slides with Impact Of Cyber Security Threats On Organisational Policy This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware, DNS Attack, SQL Injection
-
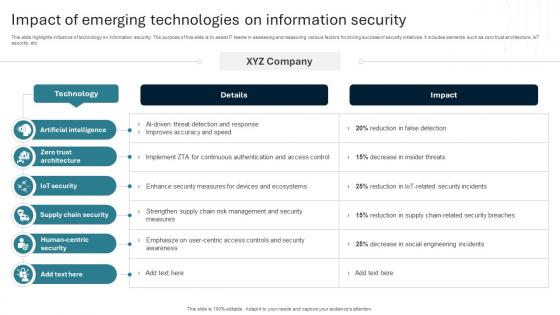 Impact Of Emerging Technologies On Information Security
Impact Of Emerging Technologies On Information SecurityThis slide highlights influence of technology on information security. The purpose of this slide is to assist IT teams in assessing and measuring various factors for driving success of security initiatives. It includes elements such as zero trust architecture, IoT security, etc.Introducing our Impact Of Emerging Technologies On Information Security set of slides. The topics discussed in these slides are Artificial Intelligence, Zero Trust Architecture, Iot Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
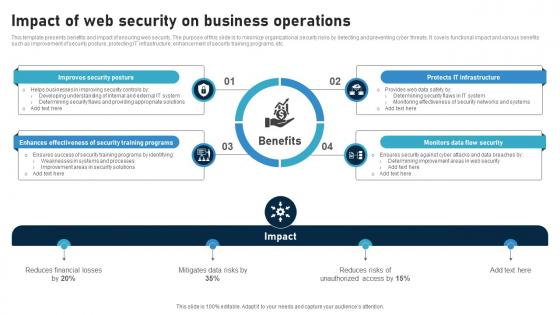 Impact Of Web Security On Business Operations
Impact Of Web Security On Business OperationsThis template presents benefits and impact of ensuring web security. The purpose of this slide is to minimize organizational security risks by detecting and preventing cyber threats. It covers functional impact and various benefits such as improvement of security posture, protecting IT infrastructure, enhancement of security training programs, etc. Introducing our Impact Of Web Security On Business Operations set of slides. The topics discussed in these slides are Monitors Data Flow Security, Protects IT Infrastructure, Improves Security Posture This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security Testing Case Study On Forensic Investigation
Security Testing Case Study On Forensic InvestigationThis slide represents the security testing case study of IT health check with objectives, skills used, and approaches to be used. Deliver an outstanding presentation on the topic using this Security Testing Case Study On Forensic Investigation. Dispense information and present a thorough explanation of Client Requirements, Aiming For Enhanced Security, Addressing Potential Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
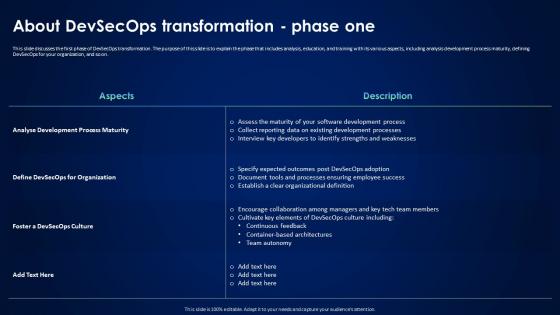 About Devsecops Transformation Phase One Devsecops Best Practices For Secure
About Devsecops Transformation Phase One Devsecops Best Practices For SecureThis slide discusses the first phase of DevSecOps transformation. The purpose of this slide is to explain the phase that includes analysis, education, and training with its various aspects, including analysis development process maturity, defining DevSecOps for your organization, and so on. Present the topic in a bit more detail with this About Devsecops Transformation Phase One Devsecops Best Practices For Secure. Use it as a tool for discussion and navigation on Analyse Development Process Maturity, Continuous Feedback, Container Based Architectures, Team Autonomy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Devsecops Transformation Phase Five Execute On Devsecops
Devsecops Best Practices For Secure Devsecops Transformation Phase Five Execute On DevsecopsThis slide discusses the fifth phase of DevSecOps transformation. The purpose of this slide is to explain the phase executed on DevSecOps, including phased execution in DevSecOps transformation and the advantages of starting with the new project. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Devsecops Transformation Phase Five Execute On Devsecops. Dispense information and present a thorough explanation of Phased Execution In Devsecops Transformation, Advantages Of Starting With New Projects, Facilitates Alignment Of Expectations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.


