Powerpoint Templates and Google slides for Secured Working Environment
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyber Security Working From Home Powerpoint Presentation And Google Slides ICP
Cyber Security Working From Home Powerpoint Presentation And Google Slides ICPElevate your presentation to visual excellence using our adaptable Icon PowerPoint template, accessible in editable PPTx and customizable PNG formats. With this deck, enjoy complete editability to finely tune it for effective message delivery. You will also retain full image ownership, granting you the flexibility to utilize them to your advantage, all within a user-friendly PowerPoint environment.
-
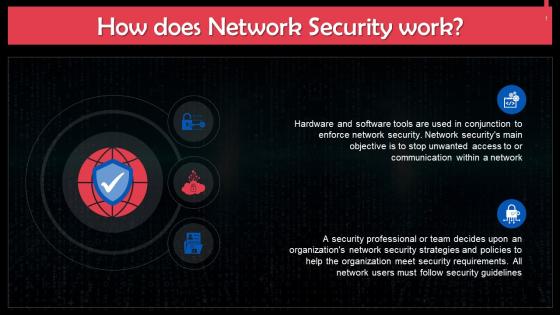 Understanding The Working Of Network Security Training Ppt
Understanding The Working Of Network Security Training PptPresenting Understanding the Working of Network Security. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Overview Of Working Of Endpoint Security Training Ppt
Overview Of Working Of Endpoint Security Training PptPresenting Overview of Working of Endpoint Security. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
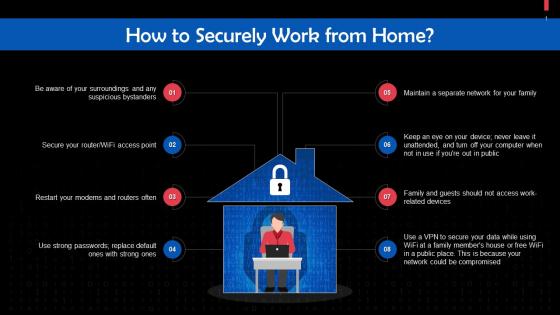 Tips To Securely Work From Home Training Ppt
Tips To Securely Work From Home Training PptPresenting Tips to Securely Work From Home. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Overview Of Working Of Security Tokens Training Ppt
Overview Of Working Of Security Tokens Training PptPresenting Overview of Working of Security Tokens. These slides are 100 percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
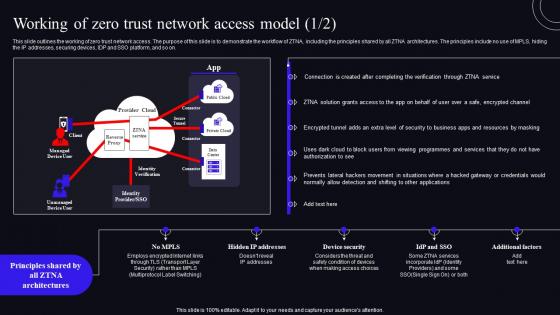 Working Of Zero Trust Network Access Model Zero Trust Security Model
Working Of Zero Trust Network Access Model Zero Trust Security ModelThis slide outlines the working of zero trust network access. The purpose of this slide is to demonstrate the workflow of ZTNA, including the principles shared by all ZTNA architectures. The principles include no use of MPLS, hiding the IP addresses, securing devices, IDP and SSO platform, and so on. Deliver an outstanding presentation on the topic using this Working Of Zero Trust Network Access Model Zero Trust Security Model. Dispense information and present a thorough explanation of Demonstrate, Architectures, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
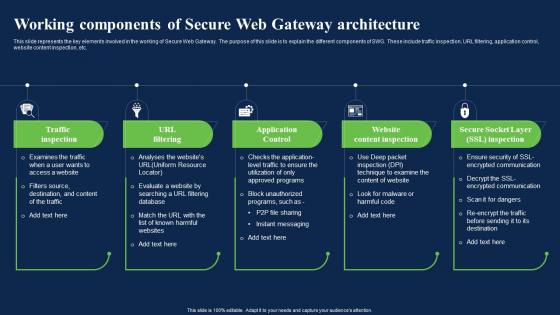 Working Components Of Secure Web Gateway Architecture Network Security Using Secure Web Gateway
Working Components Of Secure Web Gateway Architecture Network Security Using Secure Web GatewayThis slide represents the key elements involved in the working of Secure Web Gateway. The purpose of this slide is to explain the different components of SWG. These include traffic inspection, URL filtering, application control, website content inspection, etc. Increase audience engagement and knowledge by dispensing information using Working Components Of Secure Web Gateway Architecture Network Security Using Secure Web Gateway. This template helps you present information on five stages. You can also present information on Application Control, Website Content Inspection, Gateway Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
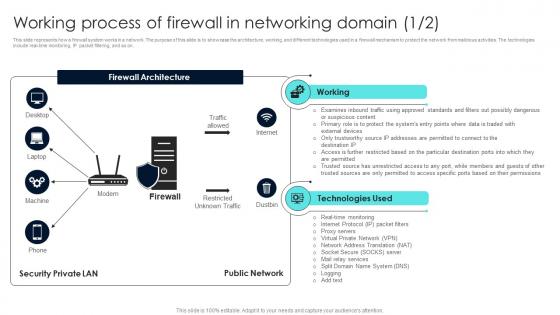 Firewall Network Security Working Process Of Firewall In Networking Domain
Firewall Network Security Working Process Of Firewall In Networking DomainThis slide represents how a firewall system works in a network. The purpose of this slide is to showcase the architecture, working, and different technologies used in a firewall mechanism to protect the network from malicious activities. The technologies include real-time monitoring, IP packet filtering, and so on. Deliver an outstanding presentation on the topic using this Firewall Network Security Working Process Of Firewall In Networking Domain Dispense information and present a thorough explanation of Working, Technologies Used, Firewall Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data security it what is data security and how does it work
Data security it what is data security and how does it workThis slide defines the meaning of data security and how it helps to prevent data through different methods and techniques. Introducing Data Security IT What Is Data Security And How Does IT Work to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Collective Methods, Protect Data, Computer Systems, Networks, Servers And Mobile Devices, using this template. Grab it now to reap its full benefits.
-
 Computer system security what is computer security and how does it work
Computer system security what is computer security and how does it workThis slide defines the meaning of cyber security and how it helps to prevent data through different methods and techniques. Introducing Computer System Security What Is Computer Security And How Does It Work to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Techniques, Collective, Networks, Computer Systems, using this template. Grab it now to reap its full benefits.
-
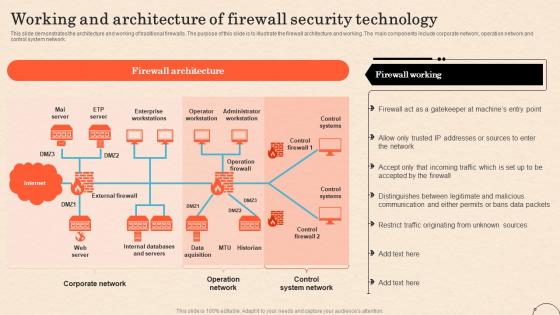 Firewall As A Service Fwaas Working And Architecture Of Firewall Security Technology
Firewall As A Service Fwaas Working And Architecture Of Firewall Security TechnologyThis slide demonstrates the architecture and working of traditional firewalls. The purpose of this slide is to illustrate the firewall architecture and working. The main components include corporate network, operation network and control system network. Present the topic in a bit more detail with this Firewall As A Service Fwaas Working And Architecture Of Firewall Security Technology. Use it as a tool for discussion and navigation on Operator Workstation, Administrator Workstation, Control Systems, Data Acquisition, Internal Databases And Servers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
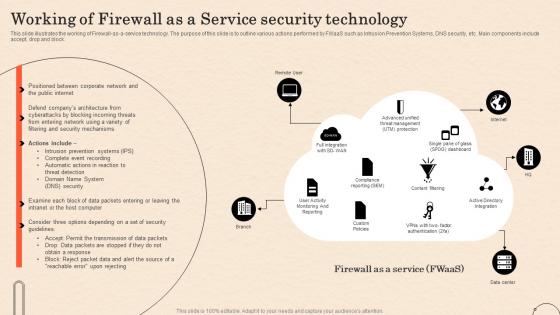 Working Of Firewall As A Service Security Technology Ppt Ideas Graphic Images
Working Of Firewall As A Service Security Technology Ppt Ideas Graphic ImagesThis slide illustrates the working of Firewall-as-a-service technology. The purpose of this slide is to outline various actions performed by FWaaS such as Intrusion Prevention Systems, DNS security, etc. Main components include accept, drop and block. Deliver an outstanding presentation on the topic using this Working Of Firewall As A Service Security Technology Ppt Ideas Graphic Images. Dispense information and present a thorough explanation of Advanced Unified Threat Management, Active Directory Integration, Compliance Reporting, Single Pane Of Glass using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Analyst Work In Powerpoint And Google Slides Cpb
Cyber Security Analyst Work In Powerpoint And Google Slides CpbPresenting our Cyber Security Analyst Work In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Cyber Security Analyst Work This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
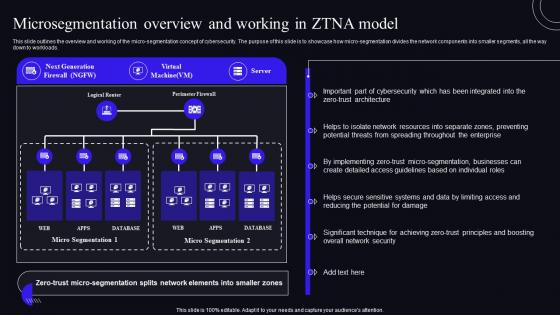 Microsegmentation Overview And Working In ZTNA Model Zero Trust Security Model
Microsegmentation Overview And Working In ZTNA Model Zero Trust Security ModelThis slide outlines the overview and working of the micro-segmentation concept of cybersecurity. The purpose of this slide is to showcase how micro-segmentation divides the network components into smaller segments, all the way down to workloads. Deliver an outstanding presentation on the topic using this Microsegmentation Overview And Working In ZTNA Model Zero Trust Security Model. Dispense information and present a thorough explanation of Microsegmentation, Overview, Businesses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Business Analyst Work In Powerpoint And Google Slides Cpb
Security Business Analyst Work In Powerpoint And Google Slides CpbPresenting our Security Business Analyst Work In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Security Business Analyst Work This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
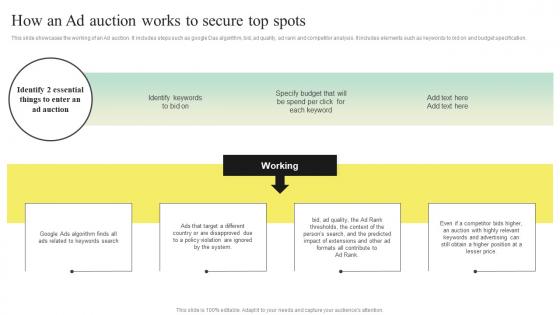 Search Engine Marketing Strategy To Enhance How An Ad Auction Works To Secure Top Spots MKT SS V
Search Engine Marketing Strategy To Enhance How An Ad Auction Works To Secure Top Spots MKT SS VThis slide showcases the working of an Ad auction. It includes steps such as google Das algorithm, bid, ad quality, ad rank and competitor analysis. It includes elements such as keywords to bid on and budget specification. Introducing Search Engine Marketing Strategy To Enhance How An Ad Auction Works To Secure Top Spots MKT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Algorithm, Violation Are Ignored, Extensions, using this template. Grab it now to reap its full benefits.
-
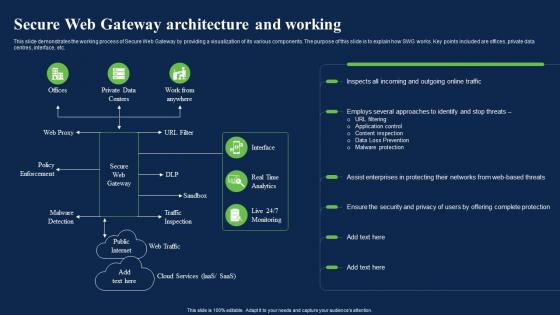 Secure Web Gateway Architecture And Working Network Security Using Secure Web Gateway
Secure Web Gateway Architecture And Working Network Security Using Secure Web GatewayThis slide demonstrates the working process of Secure Web Gateway by providing a visualization of its various components. The purpose of this slide is to explain how SWG works. Key points included are offices, private data centres, interface, etc. Present the topic in a bit more detail with this Secure Web Gateway Architecture And Working Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Architecture, Approaches, Enterprises. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
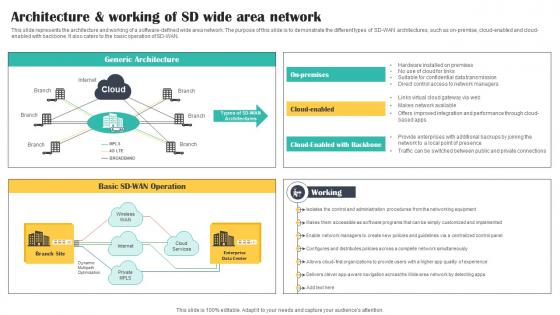 Architecture And Working Of SD Wide Area Network Cloud Security Model
Architecture And Working Of SD Wide Area Network Cloud Security ModelThis slide represents the architecture and working of a software defined wide area network. The purpose of this slide is to demonstrate the different types of SD WAN architectures, such as on premise, cloud enabled and cloud enabled with backbone. It also caters to the basic operation of SD WAN. Increase audience engagement and knowledge by dispensing information using Architecture And Working Of SD Wide Area Network Cloud Security Model. This template helps you present information on three stages. You can also present information on Working, Architecture, Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
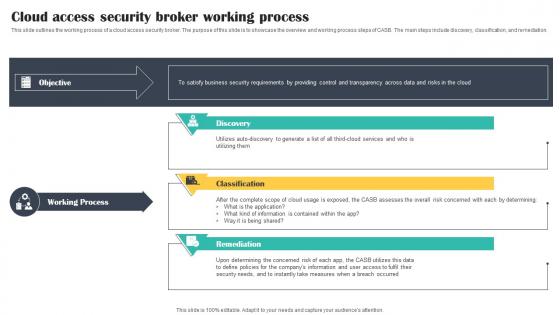 Cloud Access Security Broker Working Process Cloud Security Model
Cloud Access Security Broker Working Process Cloud Security ModelThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Working Process Cloud Security Model. This template helps you present information on three stages. You can also present information on Discovery, Classification, Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
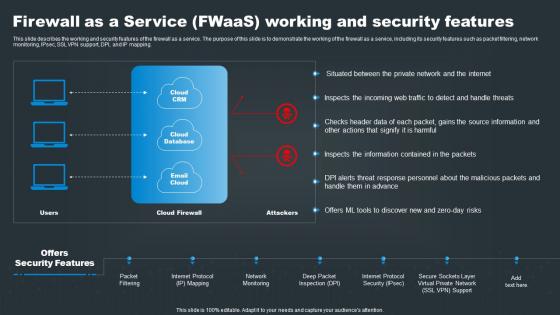 Firewall As A Service FWaaS Working And Security Features SASE Network Security
Firewall As A Service FWaaS Working And Security Features SASE Network SecurityThis slide describes the working and security features of the firewall as a service. The purpose of this slide is to demonstrate the working of the firewall as a service, including its security features such as packet filtering, network monitoring, IPsec, SSL VPN support, DPI, and IP mapping. Present the topic in a bit more detail with this Firewall As A Service FWaaS Working And Security Features SASE Network Security. Use it as a tool for discussion and navigation on Web, Source, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
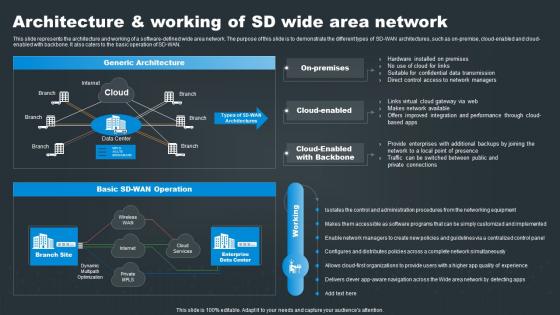 SASE Network Security Architecture And Working Of SD Wide Area Network
SASE Network Security Architecture And Working Of SD Wide Area NetworkThis slide represents the architecture and working of a software defined wide area network. The purpose of this slide is to demonstrate the different types of SD WAN architectures, such as on premise, cloud enabled and cloud enabled with backbone. It also caters to the basic operation of SD WAN. Present the topic in a bit more detail with this SASE Network Security Architecture And Working Of SD Wide Area Network. Use it as a tool for discussion and navigation on Architecture, Operation, Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
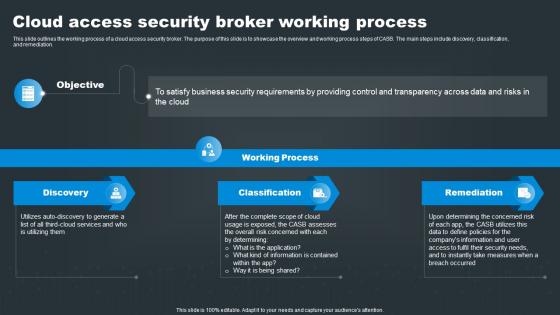 SASE Network Security Cloud Access Security Broker Working Process
SASE Network Security Cloud Access Security Broker Working ProcessThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using SASE Network Security Cloud Access Security Broker Working Process. This template helps you present information on three stages. You can also present information on Discovery, Classification, Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
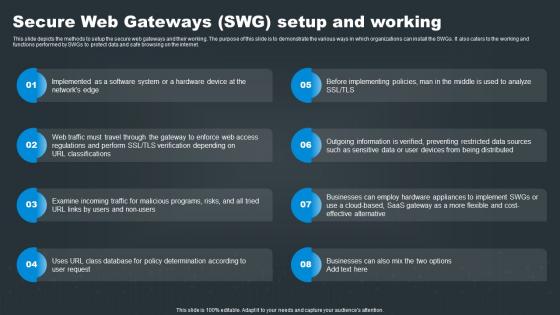 SASE Network Security Secure Web Gateways SWG Setup And Working
SASE Network Security Secure Web Gateways SWG Setup And WorkingThis slide depicts the methods to setup the secure web gateways and their working. The purpose of this slide is to demonstrate the various ways in which organizations can install the SWGs. It also caters to the working and functions performed by SWGs to protect data and safe browsing on the internet. Increase audience engagement and knowledge by dispensing information using SASE Network Security Secure Web Gateways SWG Setup And Working. This template helps you present information on eight stages. You can also present information on Regulations, Incoming, Effective using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
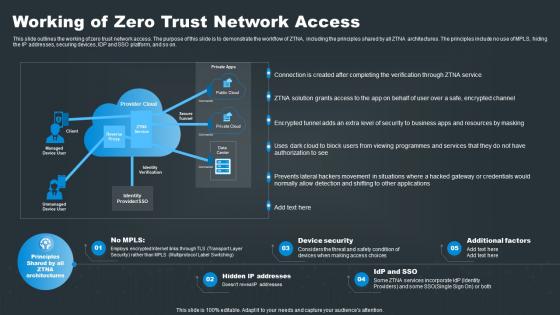 SASE Network Security Working Of Zero Trust Network Access
SASE Network Security Working Of Zero Trust Network AccessThis slide outlines the working of zero trust network access. The purpose of this slide is to demonstrate the workflow of ZTNA, including the principles shared by all ZTNA architectures. The principles include no use of MPLS, hiding the IP addresses, securing devices, IDP and SSO platform, and so on. Increase audience engagement and knowledge by dispensing information using SASE Network Security Working Of Zero Trust Network Access. This template helps you present information on five stages. You can also present information on Access, Connection, Resources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
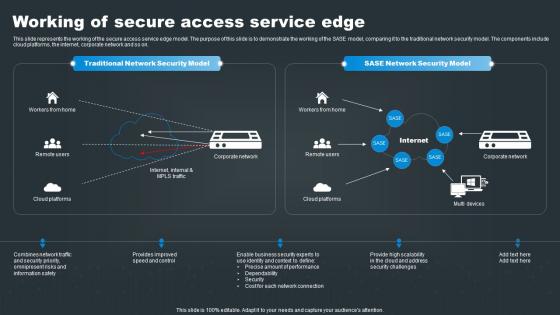 Working Of Secure Access Service Edge SASE Network Security
Working Of Secure Access Service Edge SASE Network SecurityThis slide represents the working of the secure access service edge model. The purpose of this slide is to demonstrate the working of the SASE model, comparing it to the traditional network security model. The components include cloud platforms, the internet, corporate network and so on. Deliver an outstanding presentation on the topic using this Working Of Secure Access Service Edge SASE Network Security. Dispense information and present a thorough explanation of Security, Network, Challenges using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
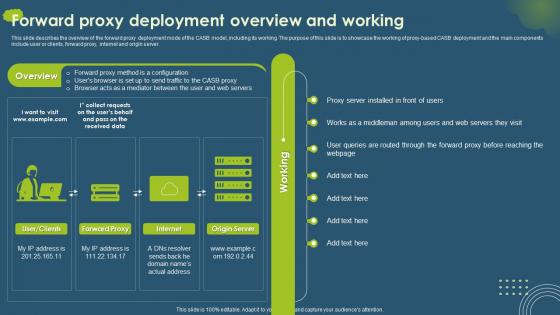 Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And Working
Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And WorkingThis slide describes the overview of the forward proxy deployment mode of the CASB model, including its working. The purpose of this slide is to showcase the working of proxy-based CASB deployment and the main components include user or clients, forward proxy, internet and origin server. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And Working. Use it as a tool for discussion and navigation on Deployment Overview And Working, Web Servers They Visit, Forward Proxy Method Is A Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 Working Process Ppt Ideas Graphics Example
Cloud Access Security Broker CASB V2 Working Process Ppt Ideas Graphics ExampleThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Working Process Ppt Ideas Graphics Example. This template helps you present information on three stages. You can also present information on Cloud Access Security, Broker Working Process, Classification And Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Securities Business Work In Powerpoint And Google Slides Cpb
Securities Business Work In Powerpoint And Google Slides CpbPresenting our Securities Business Work In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Securities Business Work This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Secured Credit Cards Work In Powerpoint And Google Slides Cpb
Secured Credit Cards Work In Powerpoint And Google Slides CpbPresenting our Secured Credit Cards Work In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Secured Credit Cards Work This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
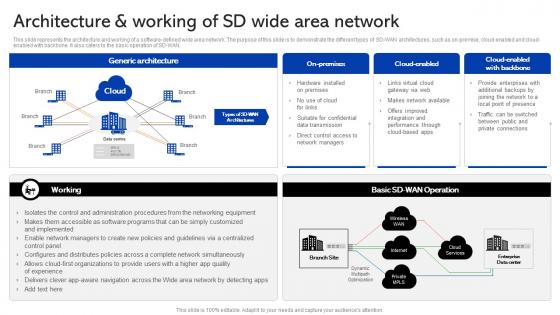 Sase Security Architecture And Working Of Sd Wide Area Network
Sase Security Architecture And Working Of Sd Wide Area NetworkThis slide represents the architecture and working of a software-defined wide area network. The purpose of this slide is to demonstrate the different types of SD-WAN architectures, such as on-premise, cloud-enabled and cloud-enabled with backbone. It also caters to the basic operation of SD-WAN. Present the topic in a bit more detail with this Sase Security Architecture And Working Of Sd Wide Area Network. Use it as a tool for discussion and navigation on Architecture, Enterprises, Connections. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Sase Security Cloud Access Security Broker Working Process
Sase Security Cloud Access Security Broker Working ProcessThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, an remediation. Deliver an outstanding presentation on the topic using this Sase Security Cloud Access Security Broker Working Process. Dispense information and present a thorough explanation of Remediation, Classification, Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
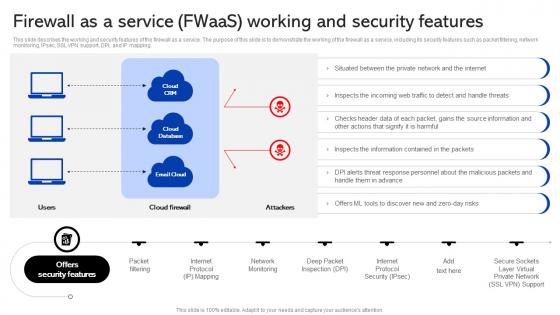 Sase Security Firewall Fwaas Working And Security Features Ppt Show Graphics Example
Sase Security Firewall Fwaas Working And Security Features Ppt Show Graphics ExampleThis slide describes the working and security features of the firewall as a service. The purpose of this slide is to demonstrate the working of the firewall as a service, including its security features such as packet filtering, network monitoring, IPsec, SSL VPN support, DPI, and IP mapping. Present the topic in a bit more detail with this Sase Security Firewall Fwaas Working And Security Features Ppt Show Graphics Example. Use it as a tool for discussion and navigation on Service, Demonstrate, Describes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
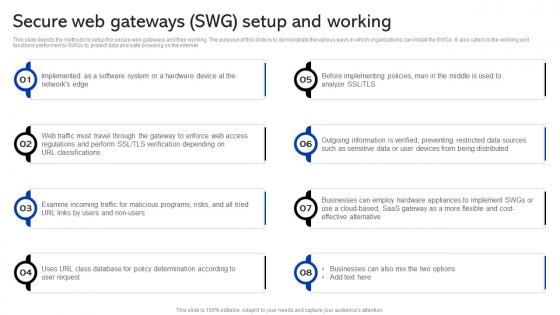 Sase Security Secure Web Gateways Swg Setup And Working
Sase Security Secure Web Gateways Swg Setup And WorkingThis slide depicts the methods to setup the secure web gateways and their working. The purpose of this slide is to demonstrate the various ways in which organizations can install the SWGs. It also caters to the working and functions performed by SWGs to protect data and safe browsing on the internet. Increase audience engagement and knowledge by dispensing information using Sase Security Secure Web Gateways Swg Setup And Working. This template helps you present information on eight stages. You can also present information on Implemented, Classifications, Businesses using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
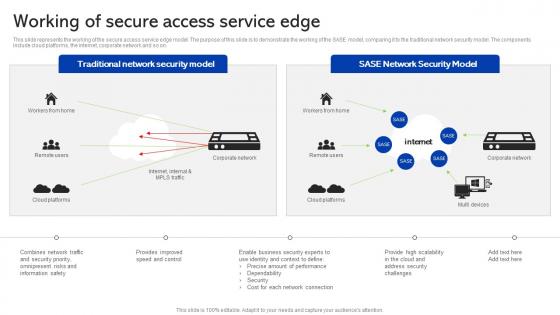 Sase Security Working Of Secure Access Service Edge
Sase Security Working Of Secure Access Service EdgeThis slide represents the working of the secure access service edge model. The purpose of this slide is to demonstrate the working of the SASE model, comparing it to the traditional network security model. The components include cloud platforms, the internet, corporate network and so on. Present the topic in a bit more detail with this Sase Security Working Of Secure Access Service Edge. Use it as a tool for discussion and navigation on Performance, Scalability, Omnipresent. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
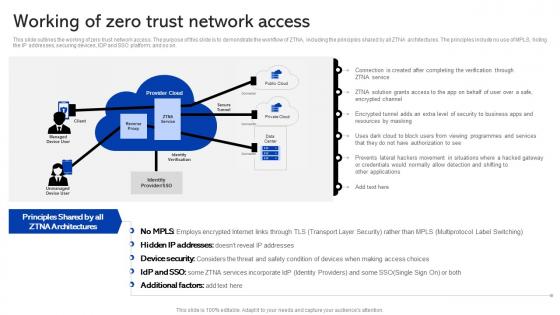 Sase Security Working Of Zero Trust Network Access
Sase Security Working Of Zero Trust Network AccessThis slide outlines the working of zero trust network access. The purpose of this slide is to demonstrate the workflow of ZTNA, including the principles shared by all ZTNA architectures. The principles include no use of MPLS, hiding the IP addresses, securing devices, IDP and SSO platform, and so on. Deliver an outstanding presentation on the topic using this Sase Security Working Of Zero Trust Network Access. Dispense information and present a thorough explanation of Resources, Situations, Multiprotocol using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
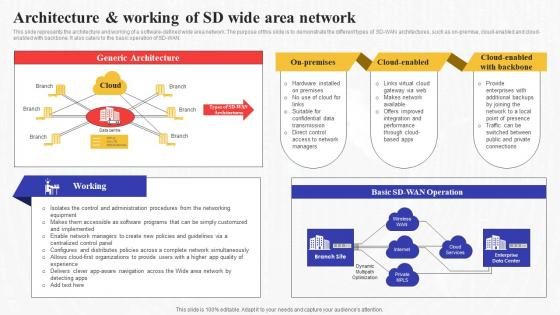 Architecture And Working Of Sd Wide Area Network Secure Access Service Edge Sase
Architecture And Working Of Sd Wide Area Network Secure Access Service Edge SaseThis slide represents the architecture and working of a software-defined wide area network. The purpose of this slide is to demonstrate the different types of SD-WAN architectures, such as on-premise, cloud-enabled and cloud-enabled with backbone. It also caters to the basic operation of SD-WAN. Present the topic in a bit more detail with this Architecture And Working Of Sd Wide Area Network Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Architecture, Enterprises, Connections. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
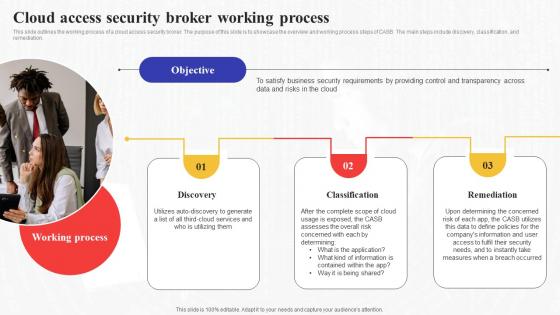 Cloud Access Security Broker Working Process Secure Access Service Edge Sase
Cloud Access Security Broker Working Process Secure Access Service Edge SaseThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Working Process Secure Access Service Edge Sase. This template helps you present information on three stages. You can also present information on Information, Classification, Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
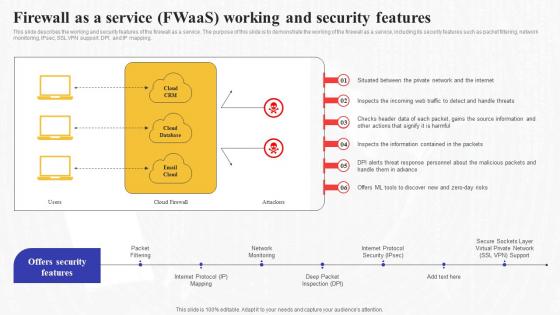 Firewall As A Service Fwaas Working And Security Features Secure Access Service Edge Sase
Firewall As A Service Fwaas Working And Security Features Secure Access Service Edge SaseThis slide describes the working and security features of the firewall as a service. The purpose of this slide is to demonstrate the working of the firewall as a service, including its security features such as packet filtering, network monitoring, IPsec, SSL VPN support, DPI, and IP mapping. Present the topic in a bit more detail with this Firewall As A Service Fwaas Working And Security Features Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Information, Demonstrate, Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
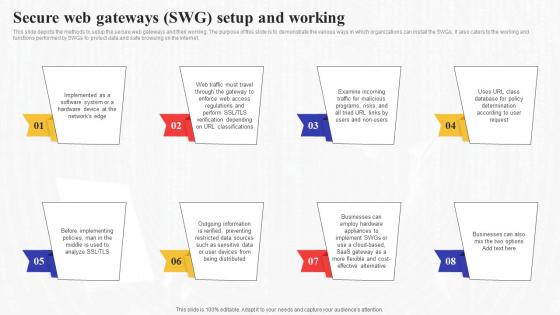 Secure Web Gateways Swg Setup And Working Secure Access Service Edge Sase
Secure Web Gateways Swg Setup And Working Secure Access Service Edge SaseThis slide depicts the methods to setup the secure web gateways and their working. The purpose of this slide is to demonstrate the various ways in which organizations can install the SWGs. It also caters to the working and functions performed by SWGs to protect data and safe browsing on the internet. Increase audience engagement and knowledge by dispensing information using Secure Web Gateways Swg Setup And Working Secure Access Service Edge Sase. This template helps you present information on eight stages. You can also present information on Information, Businesses, Determination using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
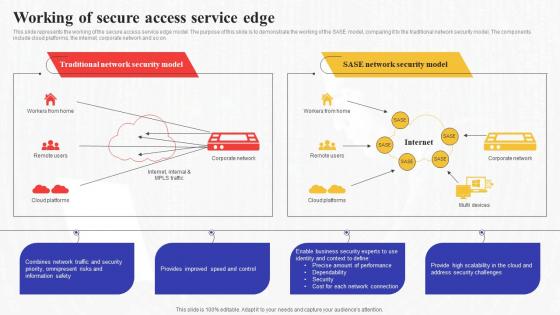 Working Of Secure Access Service Edge Secure Access Service Edge Sase
Working Of Secure Access Service Edge Secure Access Service Edge SaseThis slide represents the working of the secure access service edge model. The purpose of this slide is to demonstrate the working of the SASE model, comparing it to the traditional network security model. The components include cloud platforms, the internet, corporate network and so on. Present the topic in a bit more detail with this Working Of Secure Access Service Edge Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Service, Performance, Dependability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
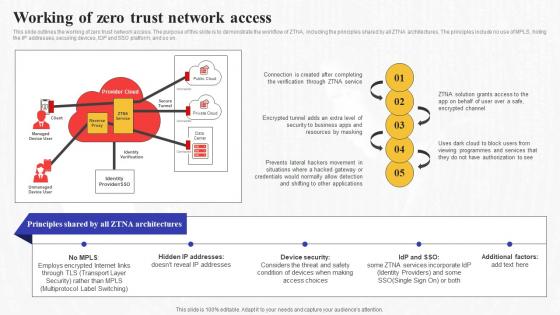 Working Of Zero Trust Network Access Secure Access Service Edge Sase
Working Of Zero Trust Network Access Secure Access Service Edge SaseThis slide outlines the working of zero trust network access. The purpose of this slide is to demonstrate the workflow of ZTNA, including the principles shared by all ZTNA architectures. The principles include no use of MPLS, hiding the IP addresses, securing devices, IDP and SSO platform, and so on. Deliver an outstanding presentation on the topic using this Working Of Zero Trust Network Access Secure Access Service Edge Sase. Dispense information and present a thorough explanation of Verification, Authorization, Applications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
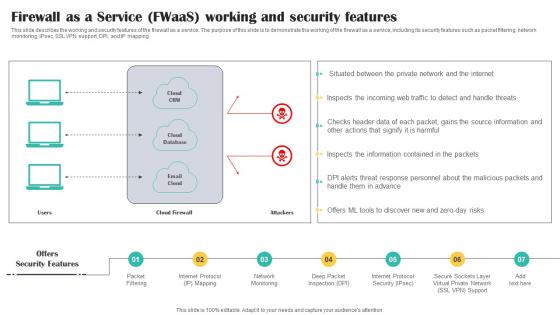 Firewall As A Service FWaaS Working And Security Features Cloud Security Model
Firewall As A Service FWaaS Working And Security Features Cloud Security ModelThis slide describes the working and security features of the firewall as a service. The purpose of this slide is to demonstrate the working of the firewall as a service, including its security features such as packet filtering, network monitoring, IPsec, SSL VPN support, DPI, and IP mapping. Introducing Firewall As A Service FWaaS Working And Security Features Cloud Security Model to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Packet, Internet, Network, using this template. Grab it now to reap its full benefits.
-
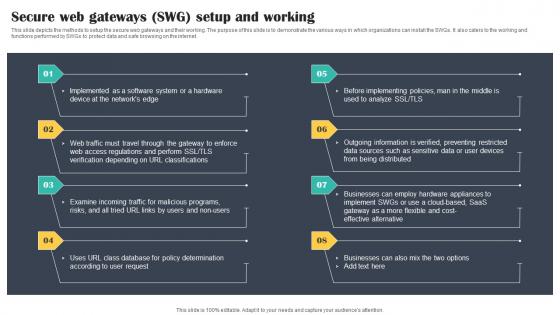 Secure Web Gateways SWG Setup And Working Cloud Security Model
Secure Web Gateways SWG Setup And Working Cloud Security ModelThis slide depicts the methods to setup the secure web gateways and their working. The purpose of this slide is to demonstrate the various ways in which organizations can install the SWGs. It also caters to the working and functions performed by SWGs to protect data and safe browsing on the internet. Increase audience engagement and knowledge by dispensing information using Secure Web Gateways SWG Setup And Working Cloud Security Model. This template helps you present information on eight stages. You can also present information on Implemented, Classifications, Programs using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
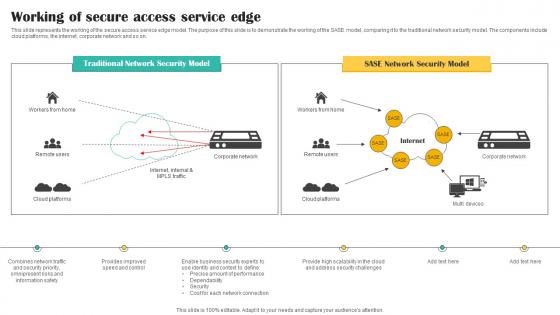 Working Of Secure Access Service Edge Cloud Security Model
Working Of Secure Access Service Edge Cloud Security ModelThis slide represents the working of the secure access service edge model. The purpose of this slide is to demonstrate the working of the SASE model, comparing it to the traditional network security model. The components include cloud platforms, the internet, corporate network and so on. Present the topic in a bit more detail with this Working Of Secure Access Service Edge Cloud Security Model. Use it as a tool for discussion and navigation on Network, Security, Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
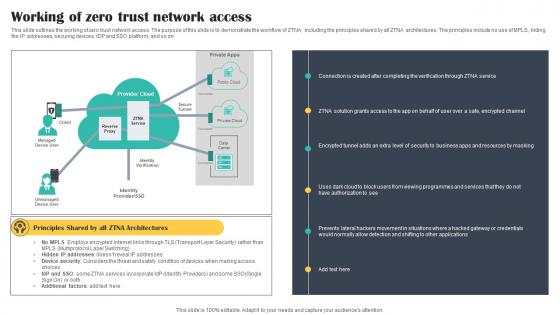 Working Of Zero Trust Network Access Cloud Security Model
Working Of Zero Trust Network Access Cloud Security ModelThis slide outlines the working of zero trust network access. The purpose of this slide is to demonstrate the workflow of ZTNA, including the principles shared by all ZTNA architectures. The principles include no use of MPLS, hiding the IP addresses, securing devices, IDP and SSO platform, and so on. Deliver an outstanding presentation on the topic using this Working Of Zero Trust Network Access Cloud Security Model. Dispense information and present a thorough explanation of Working, Network, Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Security Website Not Working In Powerpoint And Google Slides Cpb
Social Security Website Not Working In Powerpoint And Google Slides CpbPresenting Social Security Website Not Working In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Social Security Website Not Working. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Secured Credit Card Work In Powerpoint And Google Slides Cpb
Secured Credit Card Work In Powerpoint And Google Slides CpbPresenting our Secured Credit Card Work In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Secured Credit Card Work. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
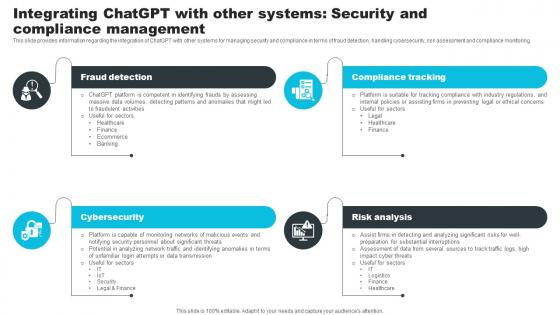 Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS V
Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Increase audience engagement and knowledge by dispensing information using Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS V. This template helps you present information on four stages. You can also present information on Fraud Detection, Compliance Tracking, Risk Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
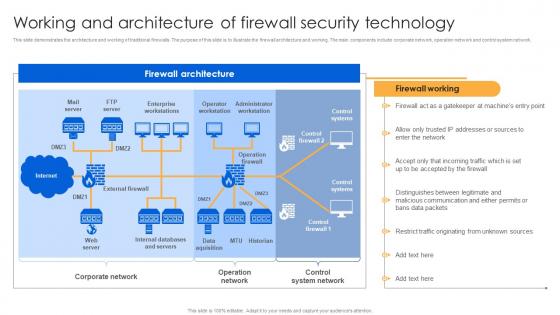 Working And Architecture Of Firewall Security Technology Firewall Virtualization
Working And Architecture Of Firewall Security Technology Firewall VirtualizationThis slide demonstrates the architecture and working of traditional firewalls. The purpose of this slide is to illustrate the firewall architecture and working. The main components include corporate network, operation network and control system network. Deliver an outstanding presentation on the topic using this Working And Architecture Of Firewall Security Technology Firewall Virtualization. Dispense information and present a thorough explanation of Firewall Architecture, Corporate Network, Control System Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
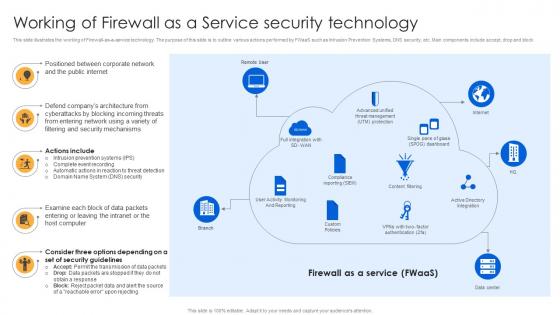 Working Of Firewall As A Service Security Technology Firewall Virtualization
Working Of Firewall As A Service Security Technology Firewall VirtualizationThis slide illustrates the working of Firewall-as-a-service technology. The purpose of this slide is to outline various actions performed by FWaaS such as Intrusion Prevention Systems, DNS security, etc. Main components include accept, drop and block. Increase audience engagement and knowledge by dispensing information using Working Of Firewall As A Service Security Technology Firewall Virtualization. This template helps you present information on five stages. You can also present information on Public Internet, Corporate Network, Companys Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
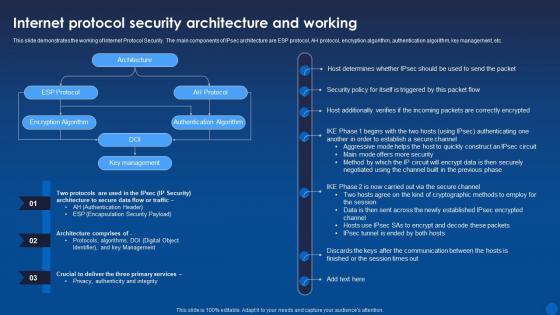 Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age It
Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age ItThis slide demonstrates the working of Internet Protocol Security. The main components of IPsec architecture are ESP protocol, AH protocol, encryption algorithm, authentication algorithm, key management, etc. Present the topic in a bit more detail with this Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Protocol Security, Architecture, Encryption Algorithm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
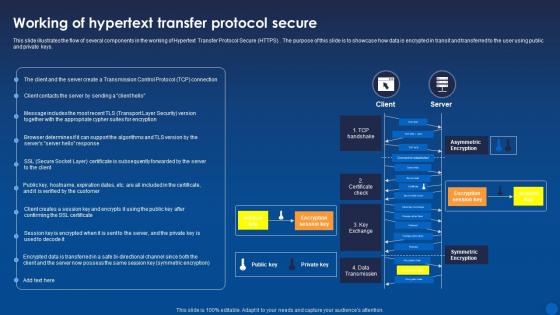 Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide illustrates the flow of several components in the working of Hypertext Transfer Protocol Secure HTTPS. The purpose of this slide is to showcase how data is encrypted in transit and transferred to the user using public and private keys. Present the topic in a bit more detail with this Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric Encryption, Symmetric Encryption, Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Email Authentication And Security Working Process
Email Authentication And Security Working ProcessThis slide highlights the email authentication and security working process which includes sender establishes authentication rules, and sender configuration. Presenting our set of slides with Email Authentication And Security Working Process. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Email Infrastructure, Authentication Rules, Authentication Results.
-
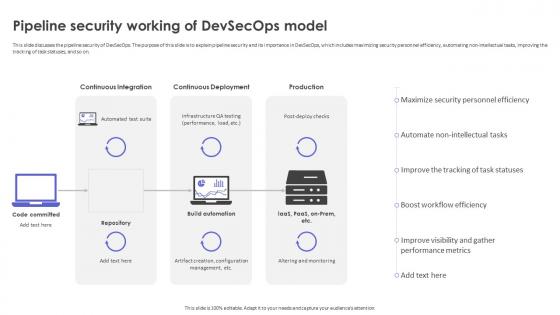 Strategic Roadmap To Implement DevSecOps Pipeline Security Working Of DevSecOps Model
Strategic Roadmap To Implement DevSecOps Pipeline Security Working Of DevSecOps ModelThis slide discusses the pipeline security of DevSecOps. The purpose of this slide is to explain pipeline security and its importance in DevSecOps, which includes maximizing security personnel efficiency, automating non-intellectual tasks, improving the tracking of task statuses, and so on. Deliver an outstanding presentation on the topic using this Strategic Roadmap To Implement DevSecOps Pipeline Security Working Of DevSecOps Model. Dispense information and present a thorough explanation of Boost Workflow Efficiency, Performance Metrics, Pipeline Security Working using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure About Devsecops Introduction And Working Process
Devsecops Best Practices For Secure About Devsecops Introduction And Working ProcessThis slide gives an overview of DevSecOps and its process. The purpose of this slide is to explain DevSecOps, including its process steps, which are release, deploy, operate, monitor, plan, code, build, and test. Present the topic in a bit more detail with this Devsecops Best Practices For Secure About Devsecops Introduction And Working Process. Use it as a tool for discussion and navigation on Development, Security, Operations, Smooth Integration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Overview Of Working Process Of Devsecops Model
Devsecops Best Practices For Secure Overview Of Working Process Of Devsecops ModelThis slide discusses the workflow procedure of DevSecOps model. The purpose of this slide is to showcase the working steps of DevSecOps model for software building and enhancing security at each level these include coding, branch, repo, CI or CD, production, etc. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Overview Of Working Process Of Devsecops Model. Use it as a tool for discussion and navigation on Workflow Procedure Of Devsecops, Software Building, Enhancing Security, Production. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
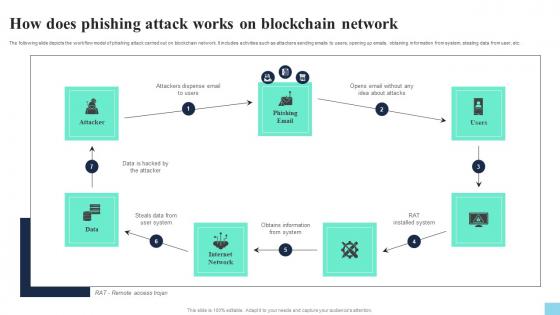 How Does Phishing Attack Works On Blockchain Network Hands On Blockchain Security Risk BCT SS V
How Does Phishing Attack Works On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Present the topic in a bit more detail with this How Does Phishing Attack Works On Blockchain Network Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Attacker, Phishing Email, Internet Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
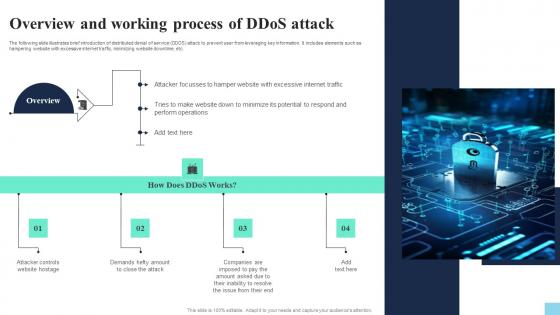 Overview And Working Process Of Ddos Attack Hands On Blockchain Security Risk BCT SS V
Overview And Working Process Of Ddos Attack Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of distributed denial of service DDOS attack to prevent user from leveraging key information. It includes elements such as hampering website with excessive internet traffic, minimizing website downtime, etc. Increase audience engagement and knowledge by dispensing information using Overview And Working Process Of Ddos Attack Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Website Hostage, Close The Attack, Inability To Resolve using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
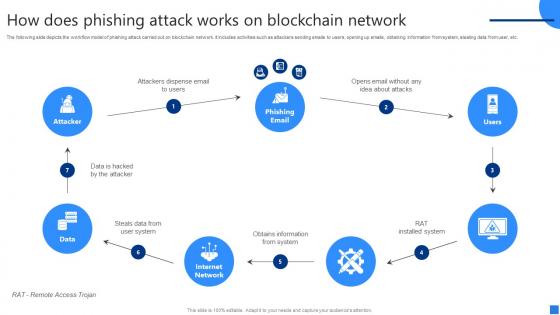 How Does Phishing Attack Works Securing Blockchain Transactions A Beginners Guide BCT SS V
How Does Phishing Attack Works Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using How Does Phishing Attack Works Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on six stages. You can also present information on Attackers Dispense Email, Steals Data, Obtains Information From System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
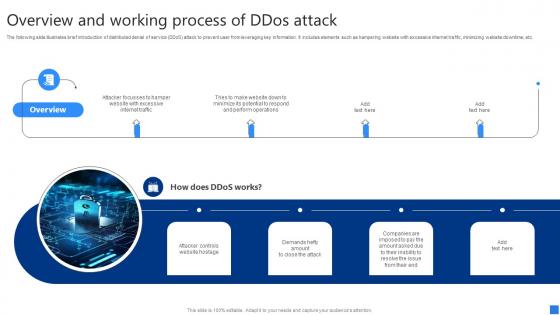 Overview And Working Process Securing Blockchain Transactions A Beginners Guide BCT SS V
Overview And Working Process Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates brief introduction of distributed denial of service DDoS attack to prevent user from leveraging key information. It includes elements such as hampering website with excessive internet traffic, minimizing website downtime, etc. Increase audience engagement and knowledge by dispensing information using Overview And Working Process Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Attacker Controls Website Hostage, Demands Hefty Amount, Companies Are Imposed using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


