Powerpoint Templates and Google slides for Security And Utility Token
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Overview Of Utility Tokens With Pros And Cons Security Token Offerings BCT SS
Overview Of Utility Tokens With Pros And Cons Security Token Offerings BCT SSThe following slide illustrates brief introduction of utility token offerings to facilitate tokenization of assets along with its pros and cons. It includes elements such as offering accessibility, providing rewards, ensuring high liquidity, changing market conditions, etc. Increase audience engagement and knowledge by dispensing information using Overview Of Utility Tokens With Pros And Cons Security Token Offerings BCT SS. This template helps you present information on two stages. You can also present information on Provides Accessibility, Particular Services, Market Conditions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Understanding Security Risk Related With Dark Data Dark Data And Its Utilization
Understanding Security Risk Related With Dark Data Dark Data And Its UtilizationThis slide focuses on the security risks associated with dark data. Some of the risks associated with dark data include vulnerability to hacking, negative impact on the business, and an increased workload for IT teams, etc. Introducing Understanding Security Risk Related With Dark Data Dark Data And Its Utilization to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability To Hacking, Negative Impact On Business, Increased Workload For IT Teams, using this template. Grab it now to reap its full benefits.
-
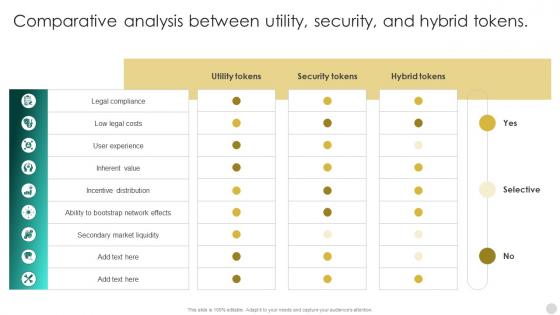 Crypto Tokens Unlocking Comparative Analysis Between Utility Security And Hybrid BCT SS
Crypto Tokens Unlocking Comparative Analysis Between Utility Security And Hybrid BCT SSThis slide compares security and utility tokens based on regulation, ownership rights, profitability, use case, liquidity, token value, security, redemption, etc. Present the topic in a bit more detail with this Crypto Tokens Unlocking Comparative Analysis Between Utility Security And Hybrid BCT SS Use it as a tool for discussion and navigation on Utility Tokens, Security Tokens, Hybrid Tokens This template is free to edit as deemed fit for your organization. Therefore download it now.
-
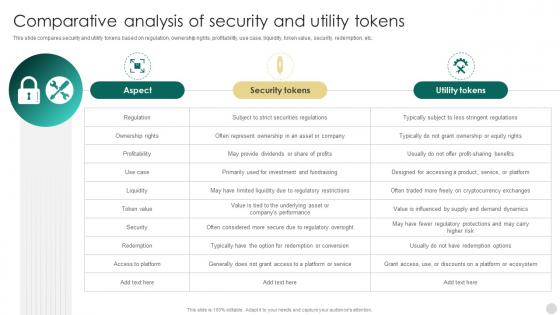 Crypto Tokens Unlocking Comparative Analysis Of Security And Utility Tokens BCT SS
Crypto Tokens Unlocking Comparative Analysis Of Security And Utility Tokens BCT SSDeliver an outstanding presentation on the topic using this Crypto Tokens Unlocking Comparative Analysis Of Security And Utility Tokens BCT SS Dispense information and present a thorough explanation of Aspect, Security Tokens, Utility Tokens using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
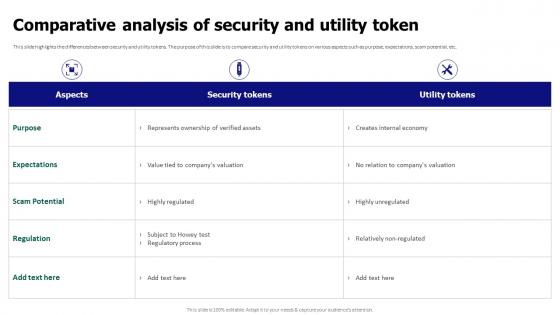 Comparative Analysis Of Security And Utility Token Tokenization For Improved Data Security
Comparative Analysis Of Security And Utility Token Tokenization For Improved Data SecurityThis slide highlights the differences between security and utility tokens. The purpose of this slide is to compare security and utility tokens on various aspects such as purpose, expectations, scam potential, etc. Present the topic in a bit more detail with this Comparative Analysis Of Security And Utility Token Tokenization For Improved Data Security. Use it as a tool for discussion and navigation on Comparative Analysis, Security And Utility Token, Expectations, Scam Potential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
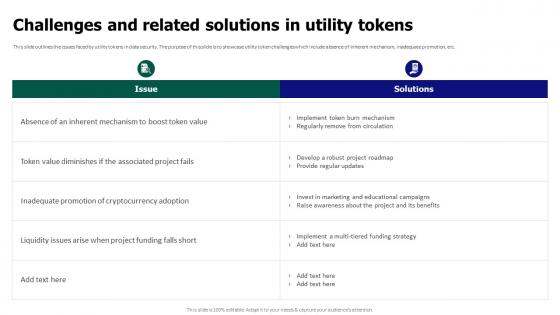 Tokenization For Improved Data Security Challenges And Related Solutions In Utility Tokens
Tokenization For Improved Data Security Challenges And Related Solutions In Utility TokensThis slide outlines the issues faced by utility tokens in data security. The purpose of this slide is to showcase utility token challenges which include absence of inherent mechanism, inadequate promotion, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Challenges And Related Solutions In Utility Tokens. Dispense information and present a thorough explanation of Regularly Remove From Circulation, Inadequate Promotion, Cryptocurrency Adoption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
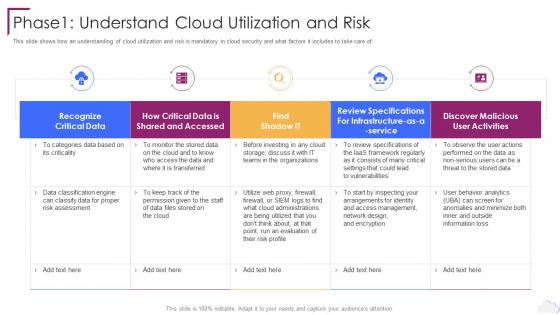 Cloud Computing Security Phase1 Understand Cloud Utilization And Risk
Cloud Computing Security Phase1 Understand Cloud Utilization And RiskThis slide shows how an understanding of cloud utilization and risk is mandatory in cloud security and what factors it includes to take care of. Present the topic in a bit more detail with this Cloud Computing Security Phase1 Understand Cloud Utilization And Risk. Use it as a tool for discussion and navigation on Recognize Critical Data, User Activities, Risk Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Phase 1 Understand Cloud Utilization And Risk Cloud Information Security
Phase 1 Understand Cloud Utilization And Risk Cloud Information SecurityThis slide shows how an understanding of cloud utilization and risk is mandatory in cloud security and what factors it includes to take care of.Introducing Phase 1 Understand Cloud Utilization And Risk Cloud Information Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Authentication Process, Cloud Access, Eliminate Malware using this template. Grab it now to reap its full benefits.
-
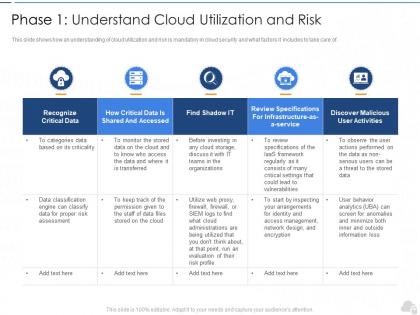 Phase 1 understand cloud utilization and risk cloud security it ppt information
Phase 1 understand cloud utilization and risk cloud security it ppt informationThis slide shows how an understanding of cloud utilization and risk is mandatory in cloud security and what factors it includes to take care of.Present the topic in a bit more detail with this Phase 1 Understand Cloud Utilization And Risk Cloud Security IT Ppt Information. Use it as a tool for discussion and navigation on Recognize Critical Data, Discover Malicious User Activities, Find Shadow It. This template is free to edit as deemed fit for your organization. Therefore download it now.

