Powerpoint Templates and Google slides for Security Automation With IaC
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
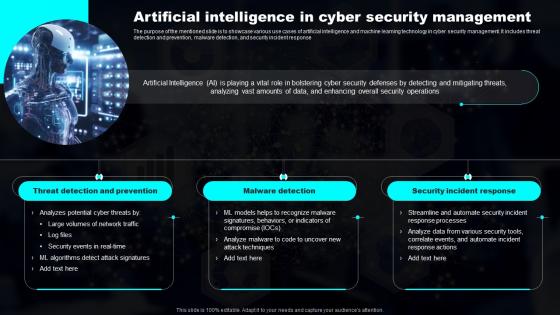 Artificial Intelligence In Cyber Security Transforming Industries With AI ML And NLP Strategy
Artificial Intelligence In Cyber Security Transforming Industries With AI ML And NLP StrategyThe purpose of the mentioned slide is to showcase various use cases of artificial intelligence and machine learning technology in cyber security management. It includes threat detection and prevention, malware detection, and security incident response Increase audience engagement and knowledge by dispensing information using Artificial Intelligence In Cyber Security Transforming Industries With AI ML And NLP Strategy. This template helps you present information on three stages. You can also present information on Prevention, Detection, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
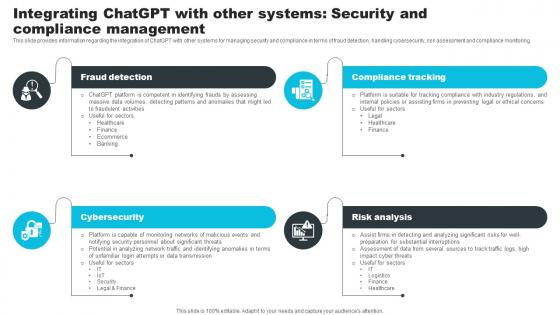 Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS V
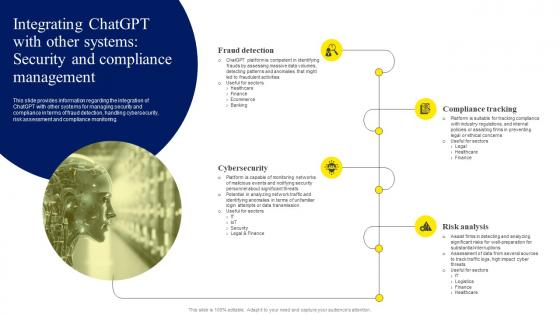
Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Increase audience engagement and knowledge by dispensing information using Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS V. This template helps you present information on four stages. You can also present information on Fraud Detection, Compliance Tracking, Risk Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
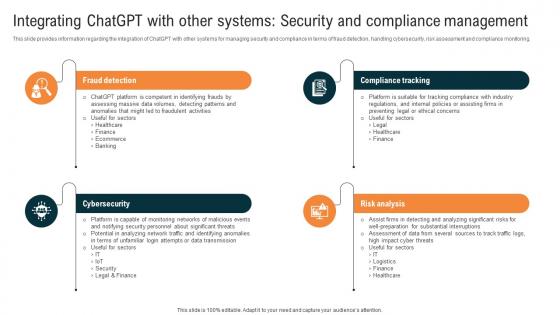 Integrating ChatGPT With Other Systems Security And Compliance Glimpse About ChatGPT As AI ChatGPT SS V
Integrating ChatGPT With Other Systems Security And Compliance Glimpse About ChatGPT As AI ChatGPT SS VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Introducing Integrating ChatGPT With Other Systems Security And Compliance Glimpse About ChatGPT As AI ChatGPT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Fraud Detection, Compliance Tracking, Risk Analysis, Cybersecurity, Security And Compliance Management, using this template. Grab it now to reap its full benefits.
-
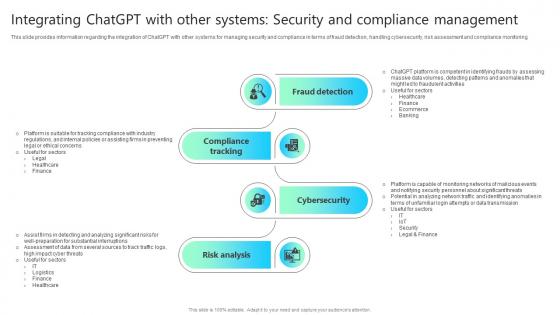 Integrating Chatgpt With Other Systems Security And Compliance Chatgpt Impact How ChatGPT SS V
Integrating Chatgpt With Other Systems Security And Compliance Chatgpt Impact How ChatGPT SS VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Increase audience engagement and knowledge by dispensing information using Integrating Chatgpt With Other Systems Security And Compliance Chatgpt Impact How ChatGPT SS V This template helps you present information on Four stages. You can also present information on Consumer Assistance, Sales Support, Customization, Consumer Feedback Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
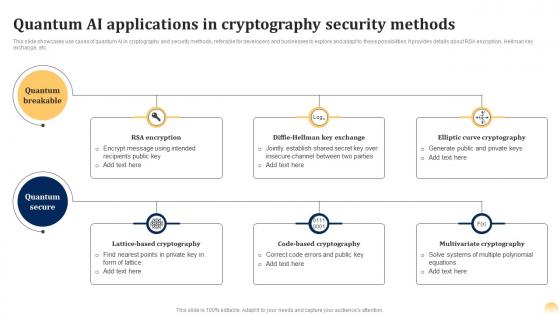 Quantum Cryptography Security Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Quantum Cryptography Security Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide showcases use cases of quantum AI in cryptography and security methods, referable for developers and businesses to explore and adapt to these possibilities. It provides details about RSA encryption, Hellman key exchange, etc. Present the topic in a bit more detail with this Quantum Cryptography Security Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Use it as a tool for discussion and navigation on Elliptic Curve Cryptography, Code Based Cryptography, Multivariate Cryptography. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Time To Fix Security Threat With Manual Testing Security Orchestration Automation And Response Guide
Time To Fix Security Threat With Manual Testing Security Orchestration Automation And Response GuideThis slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Present the topic in a bit more detail with this Time To Fix Security Threat With Manual Testing Security Orchestration Automation And Response Guide. Use it as a tool for discussion and navigation on Time To Fix, Security Threat, Manual Testing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
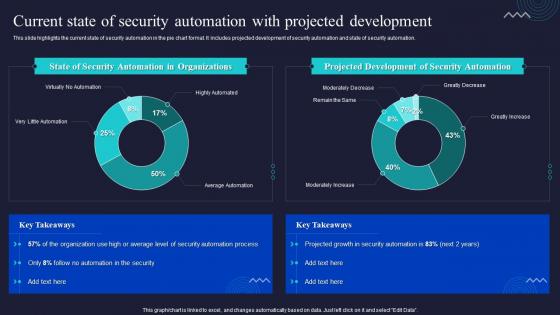 Current State Of Security Automation With Projected Development Enabling Automation In Cyber Security
Current State Of Security Automation With Projected Development Enabling Automation In Cyber SecurityThis slide highlights the current state of security automation in the pie chart format. It includes projected development of security automation and state of security automation. Deliver an outstanding presentation on the topic using this Current State Of Security Automation With Projected Development Enabling Automation In Cyber Security. Dispense information and present a thorough explanation of Automation, Development, Organizations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
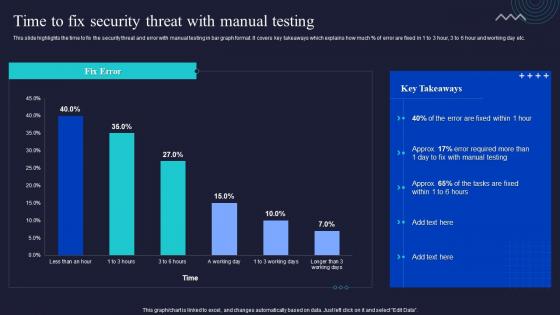 Enabling Automation In Cyber Security Operations Time To Fix Security Threat With Manual Testing
Enabling Automation In Cyber Security Operations Time To Fix Security Threat With Manual TestingThis slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Present the topic in a bit more detail with this Enabling Automation In Cyber Security Operations Time To Fix Security Threat With Manual Testing. Use it as a tool for discussion and navigation on Manual, Testing, Security Threat. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
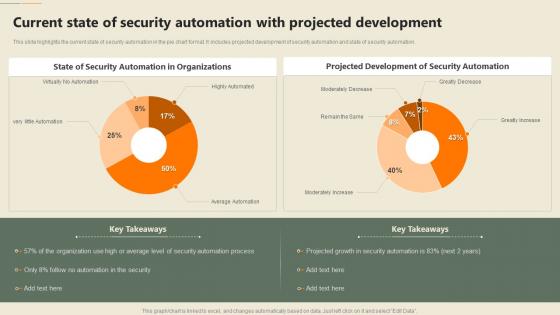 Security Automation In Information Technology Current State Of Security Automation With Projected Development
Security Automation In Information Technology Current State Of Security Automation With Projected DevelopmentThis slide highlights the current state of security automation in the pie chart format. It includes projected development of security automation and state of security automation. Deliver an outstanding presentation on the topic using this Security Automation In Information Technology Current State Of Security Automation With Projected Development. Dispense information and present a thorough explanation of Projected Development, Security Automation, Organizations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Automation In Information Technology Time To Fix Security Threat With Manual Testing
Security Automation In Information Technology Time To Fix Security Threat With Manual TestingThis slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Deliver an outstanding presentation on the topic using this Security Automation In Information Technology Time To Fix Security Threat With Manual Testing. Dispense information and present a thorough explanation of Security, Threat, Manual Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
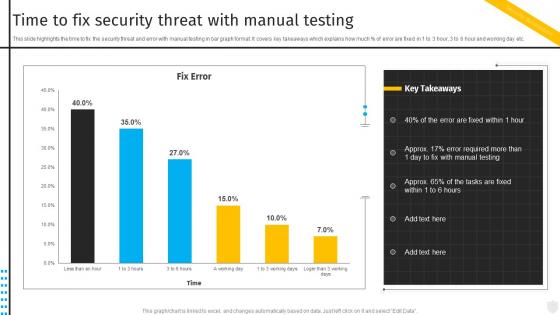 Time To Fix Security Threat With Manual Testing Security Automation To Investigate And Remediate Cyberthreats
Time To Fix Security Threat With Manual Testing Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Deliver an outstanding presentation on the topic using this Time To Fix Security Threat With Manual Testing Security Automation To Investigate And Remediate Cyberthreats. Dispense information and present a thorough explanation of Security, Threat, Manual Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
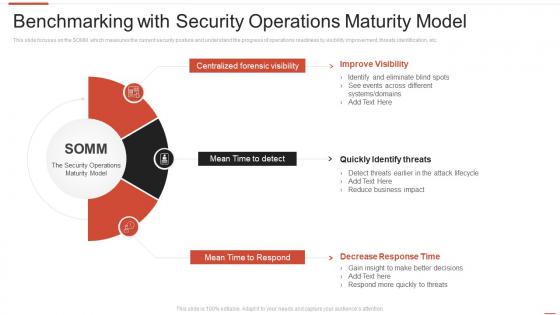 Benchmarking with security operations maturity model automating threat identification
Benchmarking with security operations maturity model automating threat identificationThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Introducing Benchmarking With Security Operations Maturity Model Automating Threat Identification to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Forensic Visibility, Mean Time To Detect, Mean Time To Respond, using this template. Grab it now to reap its full benefits.
-
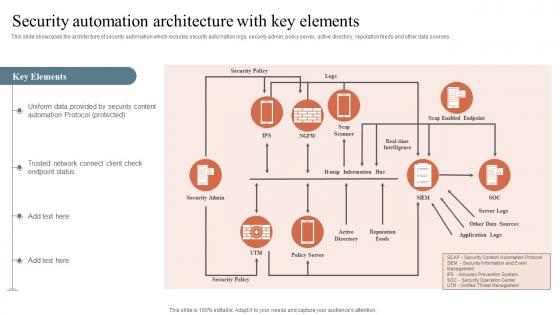 Security Automation Architecture With Key Elements Security Orchestration Automation And Response
Security Automation Architecture With Key Elements Security Orchestration Automation And ResponseThis slide showcases the architecture of security automation which includes security automation logs, security admin, policy server, active directory, reputation feeds and other data sources. Deliver an outstanding presentation on the topic using this Security Automation Architecture With Key Elements Security Orchestration Automation And Response. Dispense information and present a thorough explanation of Security Automation, Architecture, Trusted Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
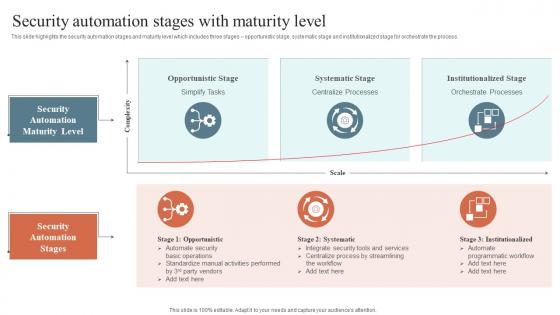 Security Automation Stages With Maturity Level Security Orchestration Automation And Response Guide
Security Automation Stages With Maturity Level Security Orchestration Automation And Response GuideThis slide highlights the security automation stages and maturity level which includes three stages opportunistic stage, systematic stage and institutionalized stage for orchestrate the process. Increase audience engagement and knowledge by dispensing information using Security Automation Stages With Maturity Level Security Orchestration Automation And Response Guide. This template helps you present information on two stages. You can also present information on Opportunistic Stage, Systematic Stage, Institutionalized Stage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
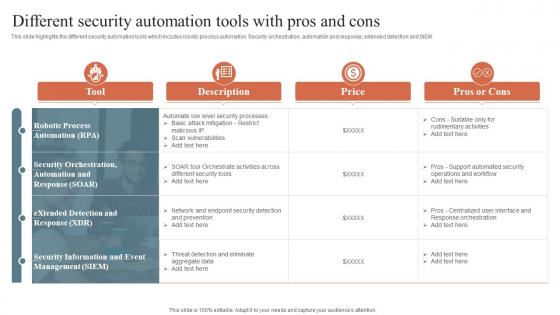 Security Orchestration Automation And Response Different Security Automation Tools With Pros And Cons
Security Orchestration Automation And Response Different Security Automation Tools With Pros And ConsThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Introducing Security Orchestration Automation And Response Different Security Automation Tools With Pros And Cons to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Security Automation, Integrates Tools, Systems And Processes, using this template. Grab it now to reap its full benefits.
-
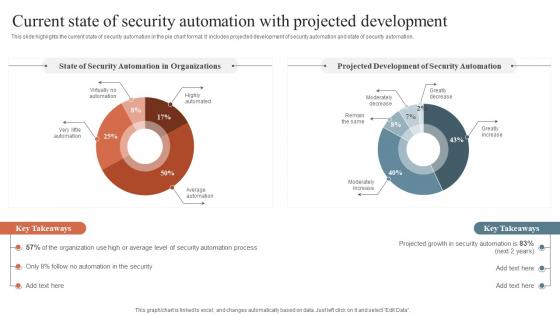 Security Orchestration Automation Current State Of Security Automation With Projected Development
Security Orchestration Automation Current State Of Security Automation With Projected DevelopmentThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Present the topic in a bit more detail with this Security Orchestration Automation Current State Of Security Automation With Projected Development. Use it as a tool for discussion and navigation on Security Information, Event Management, Security Orchestration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Automation System Icon With Gear
Security Automation System Icon With GearIntroducing our premium set of slides with Security Automation System Icon With Gear. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Automation System Icon, Gear. So download instantly and tailor it with your information.
-
 Security Automation Tools With Functions And Cost
Security Automation Tools With Functions And CostThe following slide highlights various tools that can assist company to automate security process. The various tools could be Robotic process automation security orchestration, automation and response and extended detection Introducing our premium set of slides with Security Automation Tools With Functions And Cost. Elucidate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Expected Cost, Key Functions. So download instantly and tailor it with your information.
-
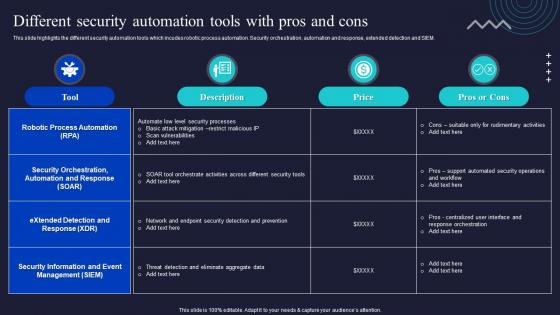 Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security Operations
Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security OperationsThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Present the topic in a bit more detail with this Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Security Information, Management, Automation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
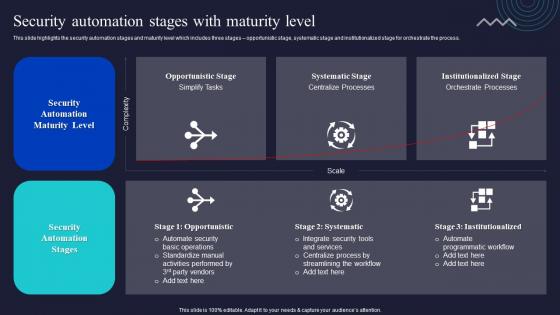 Security Automation Stages With Maturity Level Enabling Automation In Cyber Security Operations
Security Automation Stages With Maturity Level Enabling Automation In Cyber Security OperationsThis slide highlights the security automation stages and maturity level which includes three stages opportunistic stage, systematic stage and institutionalized stage for orchestrate the process. Deliver an outstanding presentation on the topic using this Security Automation Stages With Maturity Level Enabling Automation In Cyber Security Operations. Dispense information and present a thorough explanation of Security Automation, Services, Programmatic Workflow using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
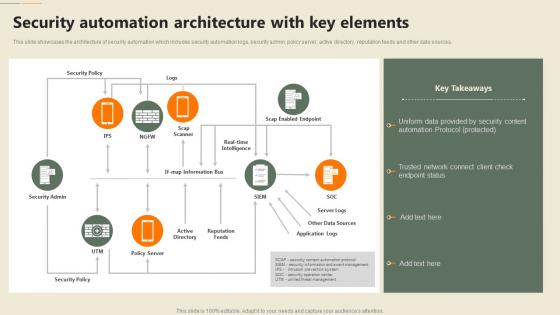 F651 Security Automation In Information Technology Security Automation Architecture With Key Elements
F651 Security Automation In Information Technology Security Automation Architecture With Key ElementsThis slide showcases the architecture of security automation which includes security automation logs, security admin, policy server, active directory, reputation feeds and other data sources. Present the topic in a bit more detail with this F651 Security Automation In Information Technology Security Automation Architecture With Key Elements. Use it as a tool for discussion and navigation on Security, Automation, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
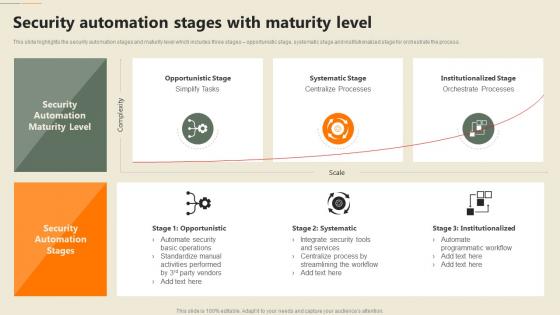 F653 Security Automation In Information Technology Security Automation Stages With Maturity Level
F653 Security Automation In Information Technology Security Automation Stages With Maturity LevelThis slide highlights the security automation stages and maturity level which includes three stages opportunistic stage, systematic stage and institutionalized stage for orchestrate the process. Present the topic in a bit more detail with this F653 Security Automation In Information Technology Security Automation Stages With Maturity Level. Use it as a tool for discussion and navigation on Systematic Stage, Institutionalized Stage, Opportunistic Stage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
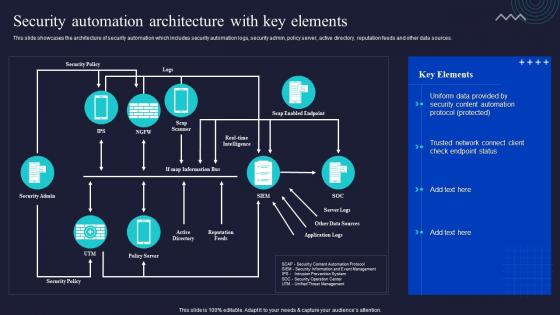 Security Automation Architecture With Key Elements Enabling Automation In Cyber Security Operations
Security Automation Architecture With Key Elements Enabling Automation In Cyber Security OperationsThis slide showcases the architecture of security automation which includes security automation logs, security admin, policy server, active directory, reputation feeds and other data sources. Deliver an outstanding presentation on the topic using this Security Automation Architecture With Key Elements Enabling Automation In Cyber Security Operations. Dispense information and present a thorough explanation of Automation, Architecture, Sources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
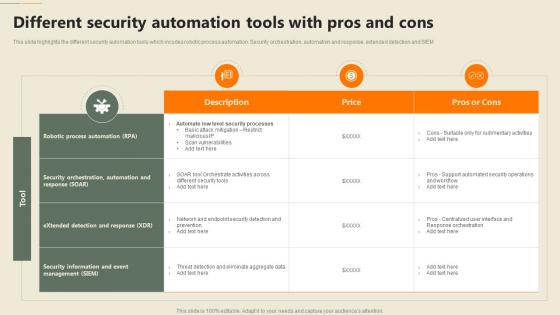 Different Security Automation Tools With Pros And Cons Security Automation In Information Technology
Different Security Automation Tools With Pros And Cons Security Automation In Information TechnologyThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM Deliver an outstanding presentation on the topic using this Different Security Automation Tools With Pros And Cons Security Automation In Information Technology. Dispense information and present a thorough explanation of Automation, Security Orchestration, Process Automation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
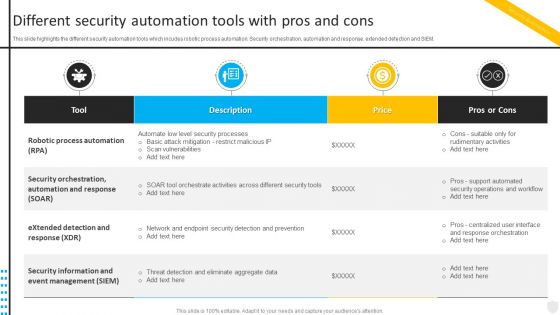 Different Security Automation Tools With Pros Security Automation To Investigate And Remediate Cyberthreats
Different Security Automation Tools With Pros Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Present the topic in a bit more detail with this Different Security Automation Tools With Pros Security Automation To Investigate And Remediate Cyberthreats. Use it as a tool for discussion and navigation on Automation, Security Orchestration, Response. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
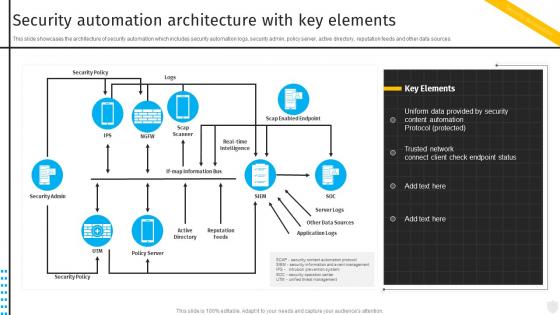 Security Automation Architecture With Key Elements Security Automation To Investigate And Remediate Cyberthreats
Security Automation Architecture With Key Elements Security Automation To Investigate And Remediate CyberthreatsThis slide showcases the architecture of security automation which includes security automation logs, security admin, policy server, active directory, reputation feeds and other data sources. Deliver an outstanding presentation on the topic using this Security Automation Architecture With Key Elements Security Automation To Investigate And Remediate Cyberthreats. Dispense information and present a thorough explanation of Automation, Architecture, Sources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
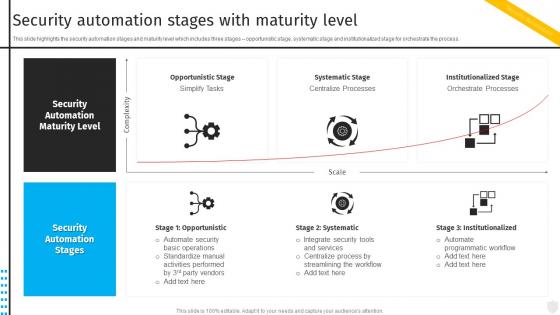 Security Automation Stages With Maturity Level Security Automation To Investigate And Remediate Cyberthreats
Security Automation Stages With Maturity Level Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the security automation stages and maturity level which includes three stages opportunistic stage, systematic stage and institutionalized stage for orchestrate the process. Present the topic in a bit more detail with this Security Automation Stages With Maturity Level Security Automation To Investigate And Remediate Cyberthreats. Use it as a tool for discussion and navigation on Opportunistic Stage, Systematic Stage, Institutionalized Stage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Integrating ChatGPT With Other Systems Security Everything About Chat GPT Generative ChatGPT SS
Integrating ChatGPT With Other Systems Security Everything About Chat GPT Generative ChatGPT SSThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Introducing Integrating ChatGPT With Other Systems Security Everything About Chat GPT Generative ChatGPT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Fraud Detection, Compliance Tracking, Cybersecurity, using this template. Grab it now to reap its full benefits.
-
 Industrial security framework with automation management
Industrial security framework with automation managementPresenting this set of slides with name Industrial Security Framework With Automation Management. The topics discussed in these slides are OT Partners and Service, Enterprise Network, Demilitarized Zone, Process, Supervisory. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Integrating ChatGPT With Other Systems Security ChatGPT OpenAI Conversation AI Chatbot ChatGPT CD V
Integrating ChatGPT With Other Systems Security ChatGPT OpenAI Conversation AI Chatbot ChatGPT CD VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Increase audience engagement and knowledge by dispensing information using Integrating ChatGPT With Other Systems Security ChatGPT OpenAI Conversation AI Chatbot ChatGPT CD V. This template helps you present information on four stages. You can also present information on Risk Analysis, Compliance Tracking, Cybersecurity, Fraud Detection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

