Powerpoint Templates and Google slides for Security Considerations
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
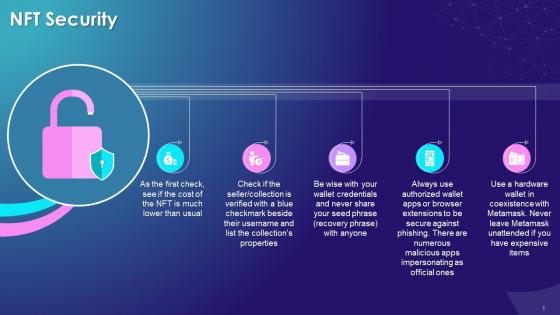 Security Factors To Consider While Buying Nfts Training Ppt
Security Factors To Consider While Buying Nfts Training PptPresenting Security Factors to Consider while Buying NFTs. Our PowerPoint experts have included all the necessary templates, designs, icons, graphs, and other essential material. This deck is well crafted by extensive research. Slides consist of amazing visuals and appropriate content. These PPT slides can be instantly downloaded with just a click. Compatible with all screen types and monitors. Supports Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
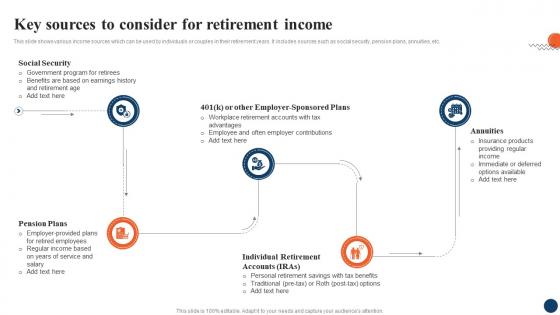 Key Sources To Consider Strategic Retirement Planning To Build Secure Future Fin SS
Key Sources To Consider Strategic Retirement Planning To Build Secure Future Fin SSThis slide shows various income sources which can be used by individuals or couples in their retirement years. It includes sources such as social security, pension plans, annuities, etc. Introducing Key Sources To Consider Strategic Retirement Planning To Build Secure Future Fin SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Social Security, Pension Plans, Annuities, using this template. Grab it now to reap its full benefits.
-
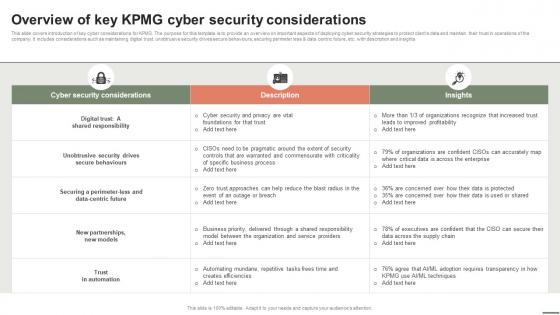 Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS V
Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS VThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less and data centric future, etc. with description and insights Present the topic in a bit more detail with this Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS V. Use it as a tool for discussion and navigation on Cyber Security Considerations, Description, Insights. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security considerations website ppt powerpoint presentation layouts background image cpb
Security considerations website ppt powerpoint presentation layouts background image cpbPresenting Security Considerations Website Ppt Powerpoint Presentation Layouts Background Image Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Considerations Website. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
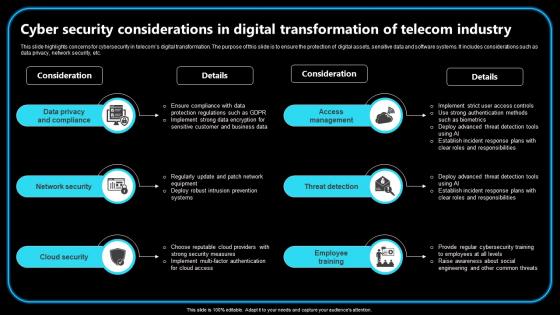 Cyber Security Considerations In Digital Transformation Of Telecom Industry
Cyber Security Considerations In Digital Transformation Of Telecom IndustryThis slide highlights concerns for cybersecurity in telecoms digital transformation. The purpose of this slide is to ensure the protection of digital assets, sensitive data and software systems. It includes considerations such as data privacy, network security, etc.Presenting our set of slides with Cyber Security Considerations In Digital Transformation Of Telecom Industry. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Security, Threat Detection, Employee Training.
-
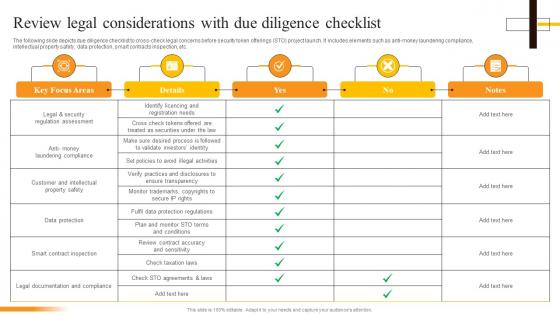 Review Legal Considerations With Due Diligence Checklist Security Token Offerings BCT SS
Review Legal Considerations With Due Diligence Checklist Security Token Offerings BCT SSThe following slide depicts due diligence checklist to cross-check legal concerns before security token offerings STO project launch. It includes elements such as anti-money laundering compliance, intellectual property safety, data protection, smart contracts inspection, etc. Present the topic in a bit more detail with this Review Legal Considerations With Due Diligence Checklist Security Token Offerings BCT SS. Use it as a tool for discussion and navigation on Regulation Assessment, Data Protection, Smart Contract Inspection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
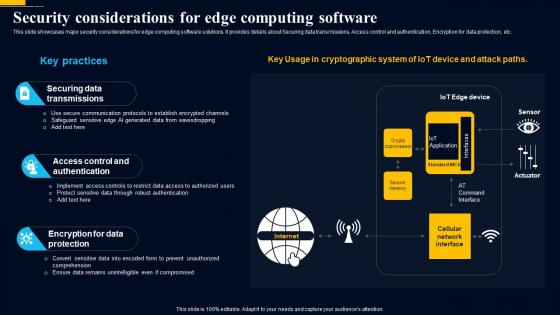 Edge Computing Technology Security Considerations For Edge Computing Software AI SS
Edge Computing Technology Security Considerations For Edge Computing Software AI SSThis slide showcases major security considerations for edge computing software solutions. It provides details about Securing data transmissions, Access control and authentication, Encryption for data protection, etc. Present the topic in a bit more detail with this Edge Computing Technology Security Considerations For Edge Computing Software AI SS. Use it as a tool for discussion and navigation on Securing Data Transmissions, Access Control And Authentication, Encryption For Data Protection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
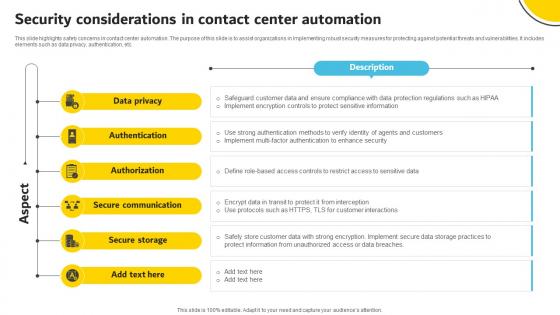 Security Considerations In Contact Center Automation
Security Considerations In Contact Center AutomationThis slide highlights safety concerns in contact center automation. The purpose of this slide is to assist organizations in Implementing robust security measures for protecting against potential threats and vulnerabilities. It includes elements such as data privacy, authentication, etc.Presenting our well structured Security Considerations In Contact Center Automation. The topics discussed in this slide are Secure Communication, Secure Storage, Authorization. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
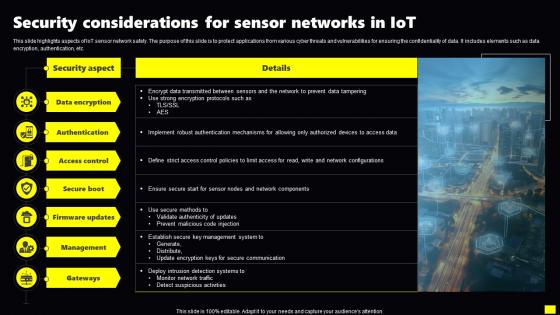 Security Considerations For Sensor Networks In IoT
Security Considerations For Sensor Networks In IoTThis slide highlights aspects of IoT sensor network safety. The purpose of this slide is to protect applications from various cyber threats and vulnerabilities for ensuring the confidentiality of data. It includes elements such as data encryption, authentication, etc.Introducing our Security Considerations For Sensor Networks In IoT set of slides. The topics discussed in these slides are Data Encryption, Firmware Updates, Key Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Key Cyber Security Considerations For Saas Companies
Key Cyber Security Considerations For Saas CompaniesThis slide represents crucial cyber security concerns for SaaS providers. It aims to integrate robust security practices into operations, to protect systems, data and customers trust. It includes various factors such as checking current security measures, gaining customers trust, etc. Introducing our premium set of slides with Key Cyber Security Considerations For Saas Companies Ellicudate the Two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Consider Thinking Differently, Gain Customers Trust, Meet GDPR Requirements. So download instantly and tailor it with your information.
-
 Hypervisor security considerations to maintain virtualized environment
Hypervisor security considerations to maintain virtualized environmentThis slide covers security considerations for hypervisor such as hypervisor vulnerabilities, access control, network security etc. to manage virtualization process.Presenting our set of slides with Hypervisor security considerations to maintain virtualized environment This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Hypervisor Vulnerabilities, Secure Management Interfaces, Network Security.
-
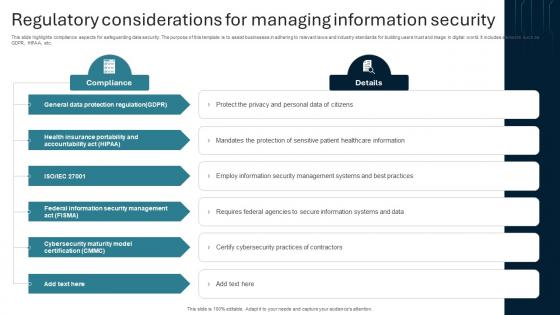 Regulatory Considerations For Managing Information Security
Regulatory Considerations For Managing Information SecurityThis slide highlights compliance aspects for safeguarding data security. The purpose of this template is to assist businesses in adhering to relevant laws and industry standards for building users trust and image in digital world. It includes elements such as GDPR, HIPAA, etc. Introducing our premium set of slides with Regulatory Considerations For Managing Information Security. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Threat Detection, Predictive Analysis, Phishing Detection. So download instantly and tailor it with your information.
-
 Review Legal Considerations Beginners Guide To Successfully Launch Security Token BCT SS V
Review Legal Considerations Beginners Guide To Successfully Launch Security Token BCT SS VThe following slide depicts due diligence checklist to cross-check legal concerns before security token offerings STO project launch. It includes elements such as anti-money laundering compliance, intellectual property safety, data protection, smart contracts inspection, etc. Present the topic in a bit more detail with this Review Legal Considerations Beginners Guide To Successfully Launch Security Token BCT SS V. Use it as a tool for discussion and navigation on Legal, Security, Data Protection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
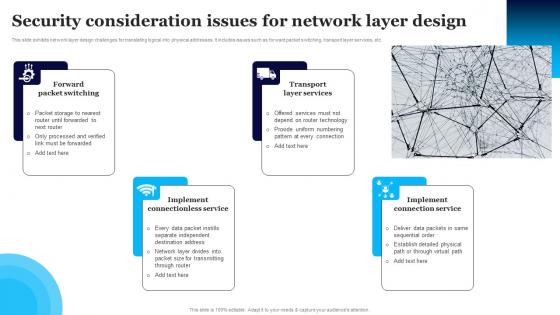 Security Consideration Issues For Network Layer Design
Security Consideration Issues For Network Layer DesignThis slide exhibits network layer design challenges for translating logical into physical addresses. It includes issues such as forward packet switching, transport layer services, etc. Presenting our well structured Security Consideration Issues For Network Layer Design. The topics discussed in this slide are Forward Packet Switching, Implement Connectionless Service, Implement Connection Service. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
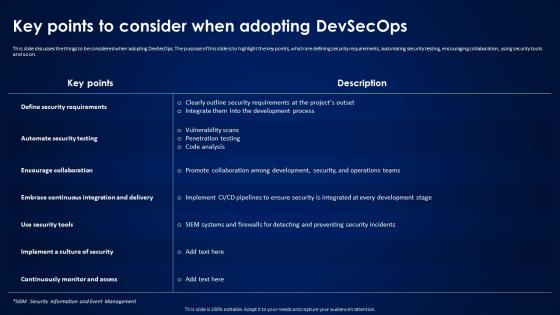 Devsecops Best Practices For Secure Key Points To Consider When Adopting Devsecops
Devsecops Best Practices For Secure Key Points To Consider When Adopting DevsecopsThis slide discusses the things to be considered when adopting DevSecOps. The purpose of this slide is to highlight the key points, which are defining security requirements, automating security testing, encouraging collaboration, using security tools and so on. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Key Points To Consider When Adopting Devsecops. Dispense information and present a thorough explanation of Automate Security Testing, Encourage Collaboration, Continuously Monitor And Assess using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
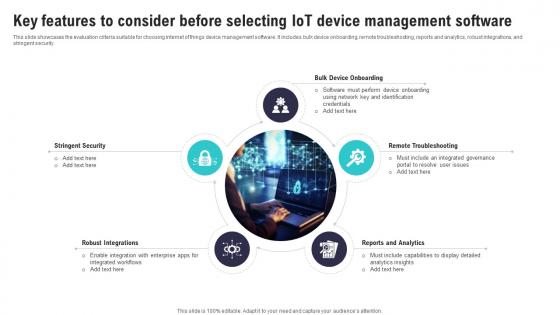 Key Features To Consider Before Selecting IoT Security And Privacy Safeguarding IoT SS
Key Features To Consider Before Selecting IoT Security And Privacy Safeguarding IoT SSThis slide showcases the evaluation criteria suitable for choosing internet of things device management software. It includes bulk device onboarding, remote troubleshooting, reports and analytics, robust integrations, and stringent security.Introducing Key Features To Consider Before Selecting IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Remote Troubleshooting, Bulk Device Onboarding, Robust Integrations, using this template. Grab it now to reap its full benefits.
-
 Secure Your Digital Assets Factors To Consider While Selecting Cryptocurrency Wallet
Secure Your Digital Assets Factors To Consider While Selecting Cryptocurrency WalletThis slide discusses some attributes that should be considered while buying crypto wallets. This slide highlights factors such as customer service, fees, security, and types of crypto supported in the wallet, etc. Introducing Secure Your Digital Assets Factors To Consider While Selecting Cryptocurrency Wallet to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Buying Crypto Wallets, Customer Service, Security, Crypto Supported In The Wallet, using this template. Grab it now to reap its full benefits.
-
 Transforming From Traditional Ethical And Data Security Considerations For Digital Innovation DT SS
Transforming From Traditional Ethical And Data Security Considerations For Digital Innovation DT SSThis slide presents important ethical and legal considerations in the digital landscape. It mentions description, laws necessary for maintaining regulations including data privacy, cybersecurity and intellectual property. Introducing Transforming From Traditional Ethical And Data Security Considerations For Digital Innovation DT SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Data Privacy, Cybersecurity, Intellectual Property using this template. Grab it now to reap its full benefits.
-
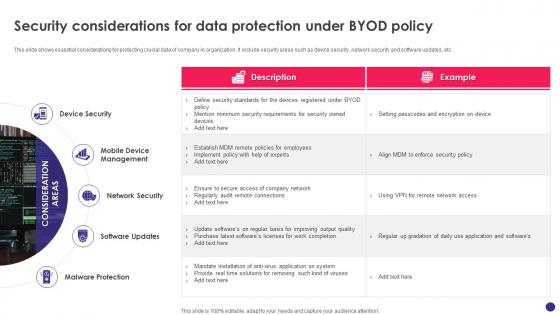 Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy
Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod PolicyThis slide shows essential considerations for protecting crucial data of company in organization. It include security areas such as device security, network security and software updates, etc. Increase audience engagement and knowledge by dispensing information using Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy. This template helps you present information on five stages. You can also present information on Device Security, Mobile Device Management, Network Security, Malware Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
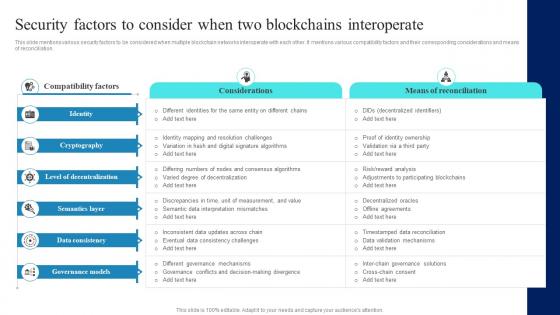 Connecting Ecosystems Introduction Security Factors To Consider When Two BCT SS
Connecting Ecosystems Introduction Security Factors To Consider When Two BCT SSThis slide mentions various security factors to be considered when multiple blockchain networks interoperate with each other. It mentions various compatibility factors and their corresponding considerations and means of reconciliation. Deliver an outstanding presentation on the topic using this Connecting Ecosystems Introduction Security Factors To Consider When Two BCT SS. Dispense information and present a thorough explanation of Cryptography, Decentralization, Consistency using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
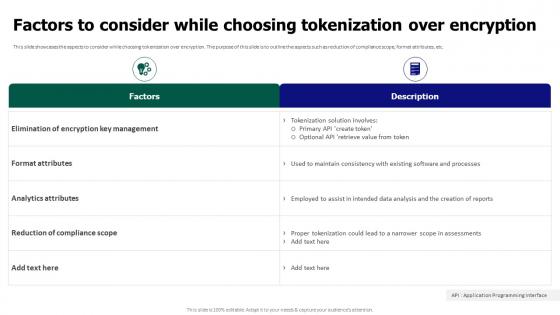 Tokenization For Improved Data Security Factors To Consider While Choosing Tokenization Over Encryption
Tokenization For Improved Data Security Factors To Consider While Choosing Tokenization Over EncryptionThis slide showcases the aspects to consider while choosing tokenization over encryption. The purpose of this slide is to outline the aspects such as reduction of compliance scope, format attributes, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Factors To Consider While Choosing Tokenization Over Encryption. Dispense information and present a thorough explanation of Elimination Of Encryption Key Management, Format Attributes, Reduction Of Compliance Scope using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
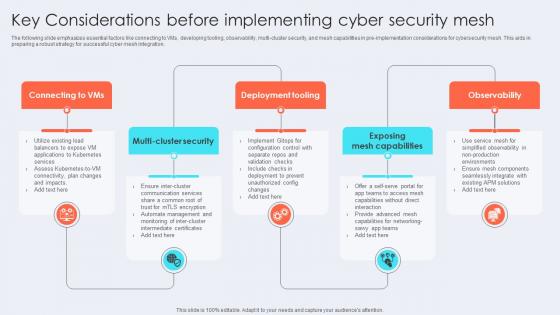 Key Considerations Before Implementing Cyber Security Mesh
Key Considerations Before Implementing Cyber Security MeshThe following slide emphasizes essential factors like connecting to VMs, developing tooling, observability, multi-cluster security, and mesh capabilities in pre-implementation considerations for cybersecurity mesh. This aids in preparing a robust strategy for successful cyber mesh integration. Presenting our set of slides with Key Considerations Before Implementing Cyber Security Mesh This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Deployment Tooling, Exposing Mesh Capabilities, Observability
-
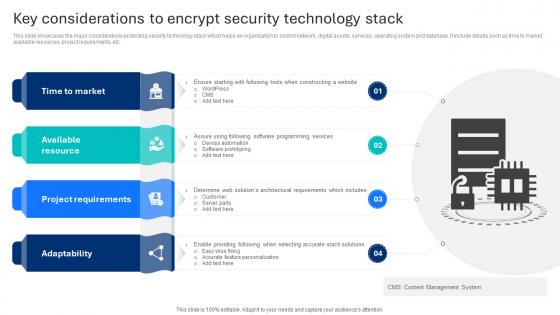 Key Considerations To Encrypt Security Technology Stack
Key Considerations To Encrypt Security Technology StackThis slide showcases the major considerations protecting security technology stack which helps an organization to control network, digital assets, services, operating system and database. It include details such as time to market, available resources, project requirements, etc. Presenting our set of slides with name Key Considerations To Encrypt Security Technology Stack This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Time To Market, Available Resource, Project Requirements
-
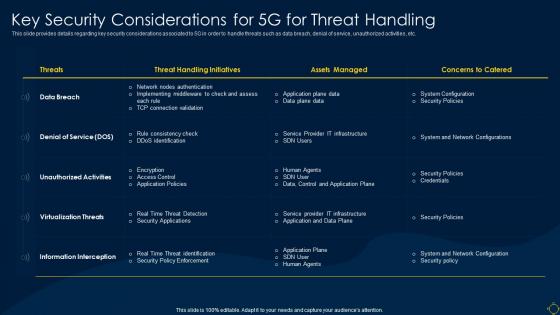 Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless System
Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless SystemThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless System. Use it as a tool for discussion and navigation on Considerations, Service, Unauthorized. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
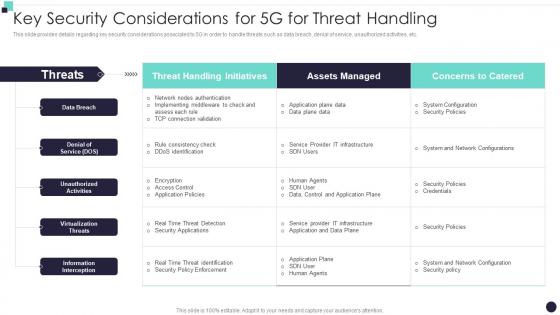 Key Security Considerations For 5G For Threat Handling Building 5G Wireless Mobile Network
Key Security Considerations For 5G For Threat Handling Building 5G Wireless Mobile NetworkThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this Key Security Considerations For 5G For Threat Handling Building 5G Wireless Mobile Network. Use it as a tool for discussion and navigation on Threat Handling Initiatives, Assets Managed, Denial Of Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Five Key Consideration For Hotel Safety And Security
Five Key Consideration For Hotel Safety And SecurityThis slide highlights five strategies to ensure safety and security in hotels. It involves strategies such as installation of proper lighting, CCTV security cameras, fire alarms, emergency power and manual. Presenting our set of slides with name Five Key Consideration For Hotel Safety And Security. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Cameras, Emergency, Consideration.
-
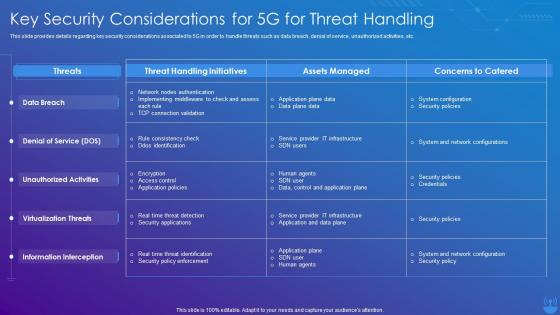 5G Technology Enabling Key Security Considerations For 5G For Threat Handling
5G Technology Enabling Key Security Considerations For 5G For Threat HandlingThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver an outstanding presentation on the topic using this 5G Technology Enabling Key Security Considerations For 5G For Threat Handling. Dispense information and present a thorough explanation of Threat Handling Initiatives, Concerns To Catered, Assets Managed using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
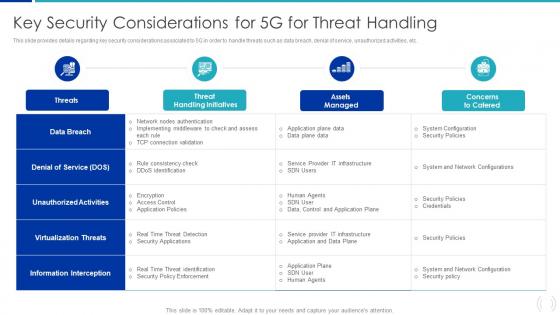 Key Security Considerations For 5G For Threat Handling Proactive Approach For 5G Deployment
Key Security Considerations For 5G For Threat Handling Proactive Approach For 5G DeploymentThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this Key Security Considerations For 5G For Threat Handling Proactive Approach For 5G Deployment. Use it as a tool for discussion and navigation on Virtualization Threats, Information Interception, Unauthorized Activities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
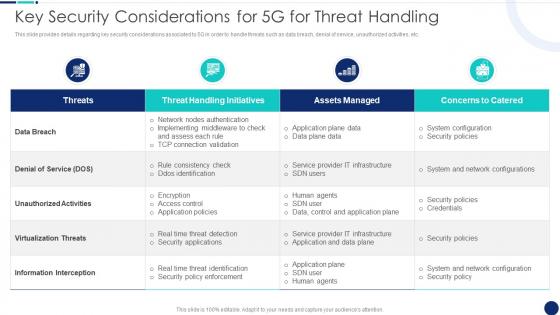 Key Security Considerations Road To 5G Era Technology And Architecture
Key Security Considerations Road To 5G Era Technology And ArchitectureThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver an outstanding presentation on the topic using this Key Security Considerations Road To 5G Era Technology And Architecture. Dispense information and present a thorough explanation of Threat Handling Initiatives, Denial Service, Information Interception using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
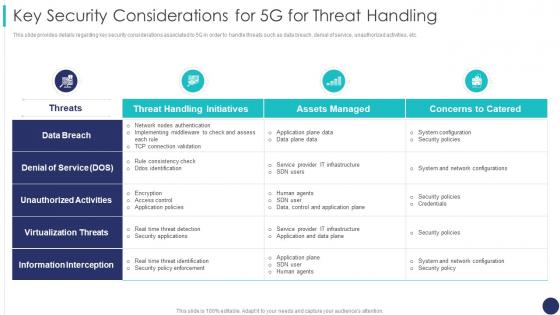 Key Security Considerations For 5g For Threat Handling 5g Mobile Technology Guidelines Operators
Key Security Considerations For 5g For Threat Handling 5g Mobile Technology Guidelines OperatorsThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver an outstanding presentation on the topic using this Key Security Considerations For 5g For Threat Handling 5g Mobile Technology Guidelines Operators. Dispense information and present a thorough explanation of Unauthorized Activities, Virtualization Threats, Information Interception using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 5g Network Architecture Guidelines Key Security Considerations For 5g For Threat Handling
5g Network Architecture Guidelines Key Security Considerations For 5g For Threat HandlingThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this 5g Network Architecture Guidelines Key Security Considerations For 5g For Threat Handling. Use it as a tool for discussion and navigation on Considerations, Associated, Unauthorized. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security considerations cloud computing ppt powerpoint presentation show mockup cpb
Security considerations cloud computing ppt powerpoint presentation show mockup cpbPresenting Security Considerations Cloud Computing Ppt Powerpoint Presentation Show Mockup Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Considerations Cloud Computing. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
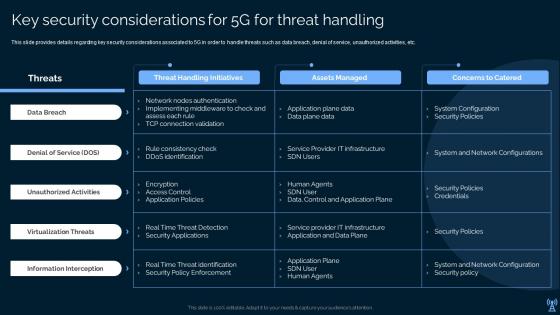 Key Security Considerations For 5g For Threat Handling Leading And Preparing For 5g World
Key Security Considerations For 5g For Threat Handling Leading And Preparing For 5g WorldPresent the topic in a bit more detail with this Key Security Considerations For 5g For Threat Handling Leading And Preparing For 5g World. Use it as a tool for discussion and navigation on Data Breach, Denial Of Service, Unauthorized Activities . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
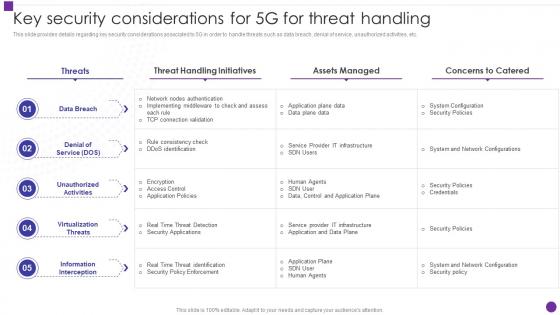 Key Security Considerations For 5g For Threat Handling Developing 5g Transformative Technology
Key Security Considerations For 5g For Threat Handling Developing 5g Transformative TechnologyThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver an outstanding presentation on the topic using this Key Security Considerations For 5g For Threat Handling Developing 5g Transformative Technology. Dispense information and present a thorough explanation of Considerations, Unauthorized Activities, Unauthorized Activities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Policy Vendor Management Policy Overview And Considerations
Cyber Security Policy Vendor Management Policy Overview And ConsiderationsThis slide represents the vendor management policy, and it also includes points to be considered when choosing a vendor. This policy is about the vendor with whom organizations share their critical information. Present the topic in a bit more detail with this Cyber Security Policy Vendor Management Policy Overview And Considerations. Use it as a tool for discussion and navigation on Management, Considerations, Overview. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
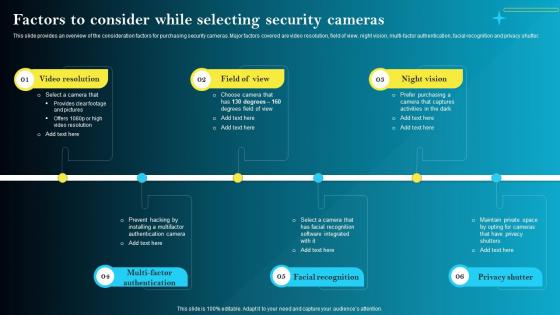 F1561 Factors To Consider While Selecting Security Cameras Iot Smart Homes Automation IOT SS
F1561 Factors To Consider While Selecting Security Cameras Iot Smart Homes Automation IOT SSThis slide provides an overview of the consideration factors for purchasing security cameras. Major factors covered are video resolution, field of view, night vision, multi-factor authentication, facial recognition and privacy shutter. Increase audience engagement and knowledge by dispensing information using F1561 Factors To Consider While Selecting Security Cameras Iot Smart Homes Automation IOT SS. This template helps you present information on six stages. You can also present information on Video Resolution, Field Of View, Night Vision using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security and privacy consideration presentation slides
Security and privacy consideration presentation slidesPresenting security and privacy consideration presentation slides which is 100% editable. This PPT template is crafted with attractive display and unique components. This PPT slide is easy to customize and enables you to personalize it as per your own criteria. The presentation slide is fully compatible with Google slides, multiple format and software options. In case of any assistance, kindly take instructions from our presentation design services and it is easy to download in a very short span of time. The images, layouts, designs are of high quality and ensures quality in widescreen. Generally, students, IT professionals and financialists makes the use of this PowerPoint presentation.
-
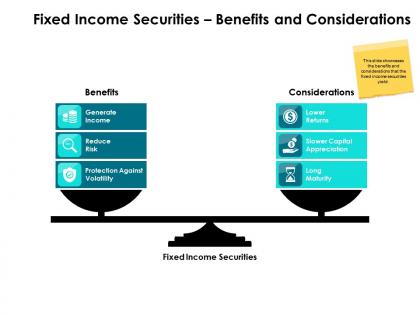 Fixed income securities benefits and considerations ppt powerpoint aids
Fixed income securities benefits and considerations ppt powerpoint aidsPresenting this set of slides with name Fixed Income Securities Benefits And Considerations Ppt Powerpoint Aids. This is a two stage process. The stages in this process are Fixed, Income, Securities, Benefits, Considerations. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
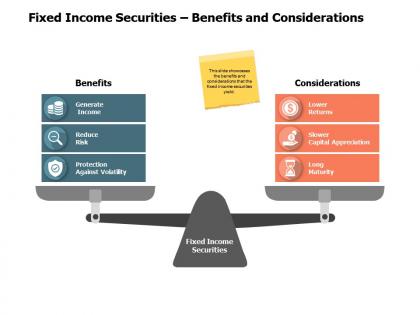 Fixed income securities benefits and considerations a549 ppt powerpoint presentation slides icon
Fixed income securities benefits and considerations a549 ppt powerpoint presentation slides iconPresenting this set of slides with name Fixed Income Securities Benefits And Considerations A549 Ppt Powerpoint Presentation Slides Icon. This is a two stage process. The stages in this process are Reduce Risk, Long Maturity, Lower Returns, Generate Income, Finance. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
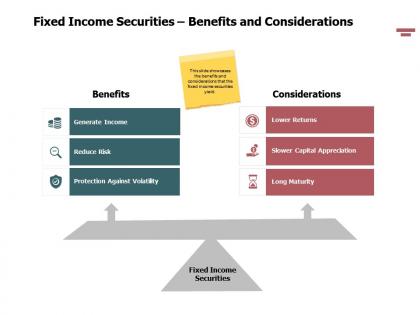 Fixed income securities benefits and considerations powerpoint presentation grid
Fixed income securities benefits and considerations powerpoint presentation gridPresenting this set of slides with name Fixed Income Securities Benefits And Considerations Powerpoint Presentation Grid. This is a three stage process. The stages in this process are Finance, Marketing, Management, Investment, Analysis. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
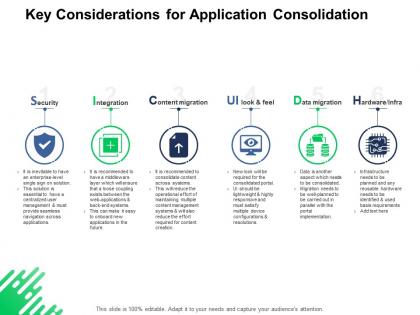 Key considerations for application consolidation security integration ppt powerpoint presentation
Key considerations for application consolidation security integration ppt powerpoint presentationPresenting this set of slides with name Key Considerations For Application Consolidation Security Integration Ppt Powerpoint Presentation. This is a six stage process. The stages in this process are Process, Business, Planning, Strategy, Marketing. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

