Powerpoint Templates and Google slides for Suitable Security Protocol
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
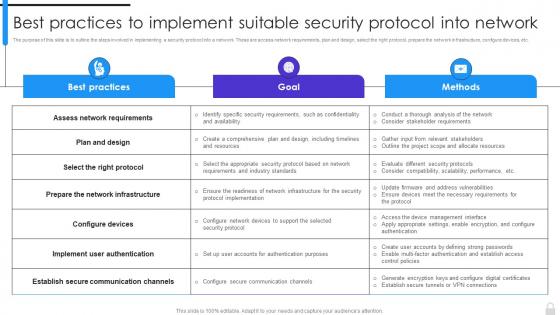 Encryption Implementation Strategies Best Practices To Implement Suitable Security Protocol Into Network
Encryption Implementation Strategies Best Practices To Implement Suitable Security Protocol Into NetworkThe purpose of this slide is to outline the steps involved in implementing a security protocol into a network. These are access network requirements, plan and design, select the right protocol, prepare the network infrastructure, configure devices, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Best Practices To Implement Suitable Security Protocol Into Network. Dispense information and present a thorough explanation of Assess Network Requirements, Implement User Authentication, Suitable Security Protocol using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Selecting Suitable Software For Information Risk Assessment And Management Plan For Information Security
Selecting Suitable Software For Information Risk Assessment And Management Plan For Information SecurityThis slide showcases software that can help organization to monitor and manage the risk. It provides information about Cyber Risk Quantification, vvulnerability management, Ccentralized rrepository for aassets etc Deliver an outstanding presentation on the topic using this Selecting Suitable Software For Information Risk Assessment And Management Plan For Information Security. Dispense information and present a thorough explanation of Software, Information, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
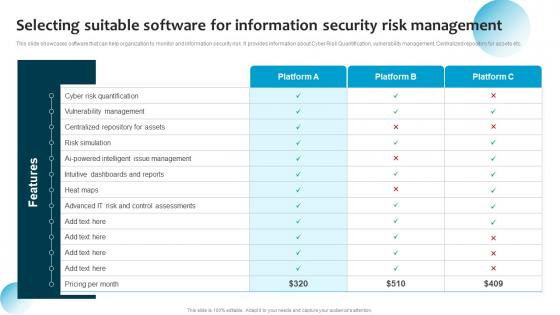 C15 Selecting Suitable Software For Information Security Risk Management Ppt Styles Background Image
C15 Selecting Suitable Software For Information Security Risk Management Ppt Styles Background ImageThis slide showcases software that can help organization to monitor and information security risk. It provides information about Cyber Risk Quantification, vulnerability management, Centralized repository for assets etc. Present the topic in a bit more detail with this C15 Selecting Suitable Software For Information Security Risk Management Ppt Styles Background Image. Use it as a tool for discussion and navigation on Cyber Risk Quantification, Vulnerability Management, Centralized Repository For Assets. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Selecting Suitable Software For Information Security Cybersecurity Risk Analysis And Management Plan
Selecting Suitable Software For Information Security Cybersecurity Risk Analysis And Management PlanThis slide showcases software that can help organization to monitor and manage the information security risk. It provides information about cyber risk quantification, vulnerability management, centralized repository for assets etc. Present the topic in a bit more detail with this Selecting Suitable Software For Information Security Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Software, Information, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
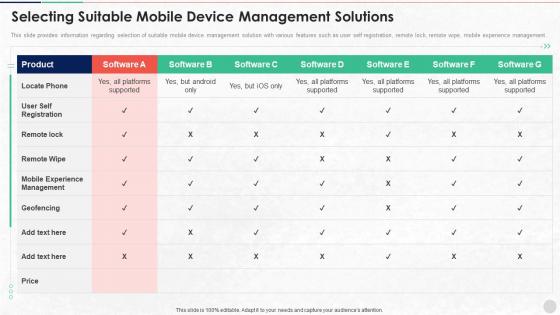 Selecting Suitable Mobile Device Management Solutions Unified Endpoint Security
Selecting Suitable Mobile Device Management Solutions Unified Endpoint SecurityThis slide provides information regarding selection of suitable mobile device management solution with various features such as user self registration, remote lock, remote wipe, mobile experience management. Deliver an outstanding presentation on the topic using this Selecting Suitable Mobile Device Management Solutions Unified Endpoint Security. Dispense information and present a thorough explanation of Experience Management, Geofencing, Platforms Supported using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
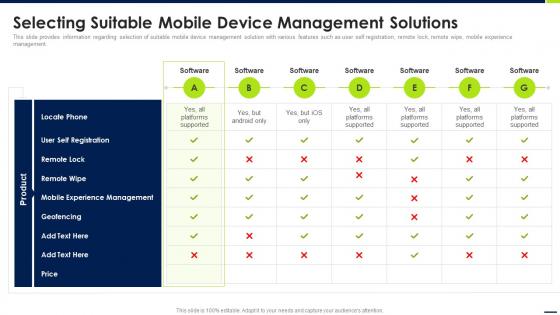 Selecting Suitable Mobile Device Management Solutions Android Device Security Management
Selecting Suitable Mobile Device Management Solutions Android Device Security ManagementThis slide provides information regarding selection of suitable mobile device management solution with various features such as user self registration, remote lock, remote wipe, mobile experience management. Present the topic in a bit more detail with this Selecting Suitable Mobile Device Management Solutions Android Device Security Management. Use it as a tool for discussion and navigation on Software, Platforms Supported, Mobile Experience Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Selecting Suitable Mobile Device Management Solutions Enterprise Mobile Security For On Device
Selecting Suitable Mobile Device Management Solutions Enterprise Mobile Security For On DeviceThis slide provides information regarding selection of suitable mobile device management solution with various features such as user self registration, remote lock, remote wipe, mobile experience management. Deliver an outstanding presentation on the topic using this Selecting Suitable Mobile Device Management Solutions Enterprise Mobile Security For On Device. Dispense information and present a thorough explanation of Experience Management, Self Registration, Remote Wipe using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Selecting Suitable Software For Information Security Risk Management
Selecting Suitable Software For Information Security Risk ManagementThis slide showcases software that can help organization to monitor and manage the risk. It provides information about cyber risk quantification, vulnerability management, centralized repository for assets etc. Deliver an outstanding presentation on the topic using this Selecting Suitable Software For Information Security Risk Management. Dispense information and present a thorough explanation of Cyber Risk Quantification, Vulnerability Management, Selecting Suitable Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
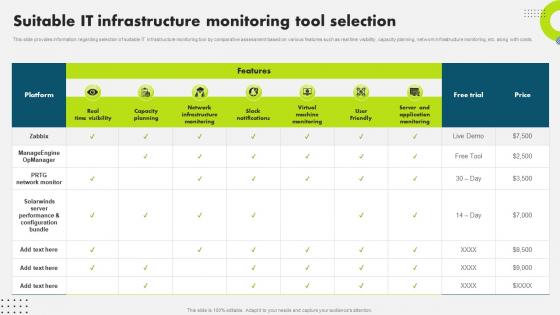 Suitable It Infrastructure Monitoring Tool Selection Strategic Plan To Secure It Infrastructure Strategy SS V
Suitable It Infrastructure Monitoring Tool Selection Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding selection of suitable IT infrastructure monitoring tool by comparative assessment based on various features such as real time visibility, capacity planning, network infrastructure monitoring, etc. along with costs. Present the topic in a bit more detail with this Suitable It Infrastructure Monitoring Tool Selection Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Comparative, Assessment, Infrastructure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
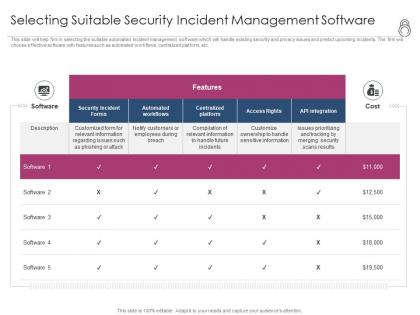 Enhanced security event management selecting suitable security incident management software ppt file
Enhanced security event management selecting suitable security incident management software ppt fileThis slide will help firm in selecting the suitable automated incident management software which will handle existing security and privacy issues and predict upcoming incidents. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Present the topic in a bit more detail with this Enhanced Security Event Management Selecting Suitable Security Incident Management Software Ppt File. Use it as a tool for discussion and navigation on Security Incident Forms, Access Rights, Automated Workflows, Centralized Platform. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It security operations selecting suitable security incident management software ppt image
It security operations selecting suitable security incident management software ppt imageThis slide will help firm in selecting the suitable automated incident management software which will handle existing security and privacy issues and predict upcoming incidents. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Present the topic in a bit more detail with this IT Security Operations Selecting Suitable Security Incident Management Software Ppt Image. Use it as a tool for discussion and navigation on Security Incident Forms, Access Rights, Automated Workflows, Centralized Platform. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
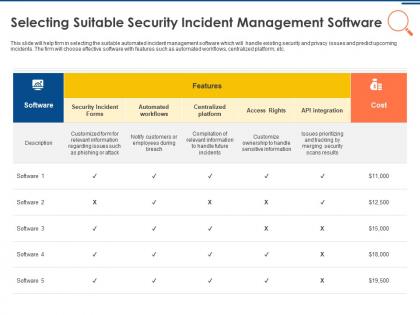
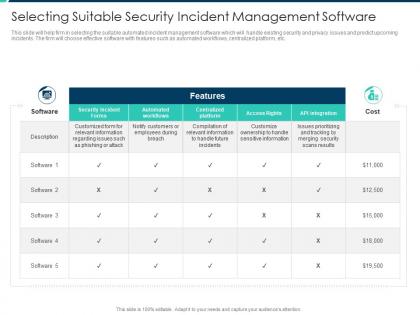 Selecting suitable security incident management software security operations integration ppt slides
Selecting suitable security incident management software security operations integration ppt slidesThis slide will help firm in selecting the suitable automated incident management software which will handle existing security and privacy issues and predict upcoming incidents. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Present the topic in a bit more detail with this Selecting Suitable Security Incident Management Software Security Operations Integration Ppt Slides Use it as a tool for discussion and navigation on Security Incident, Automated Workflows, Centralized Platform from . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
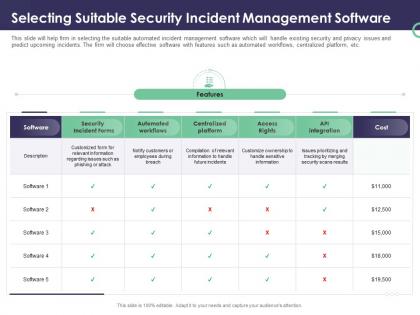 Enterprise security operations selecting suitable security incident management software ppt aids
Enterprise security operations selecting suitable security incident management software ppt aidsThis slide will help firm in selecting the suitable automated incident management software which will handle existing security and privacy issues and predict upcoming incidents. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Present the topic in a bit more detail with thisEnterprise Security Operations Selecting Suitable Security Incident Management Software Ppt Aids. Use it as a tool for discussion and navigation on Security Incident Forms, Access Rights, Automated Workflows, Centralized Platform. This template is free to edit as deemed fit for your organization. Therefore download it now.

