Powerpoint Templates and Google slides for Sybil Attacks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Threats Sybil Attack Poses To Blockchain Technology Training Ppt
Threats Sybil Attack Poses To Blockchain Technology Training PptPresenting Threats Sybil Attack Poses to Blockchain Technology. This slide is well crafted and designed by our PowerPoint specialists. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
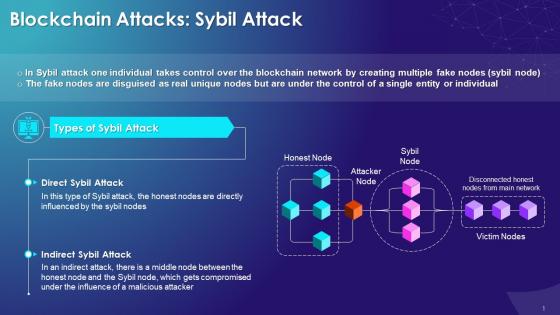
 Sybil Attack On Blockchain Network Training Ppt
Sybil Attack On Blockchain Network Training PptPresenting Sybil Attack on Blockchain Network. This slide is well crafted and designed by our PowerPoint specialists. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. You can add or delete the content as per your need.
-
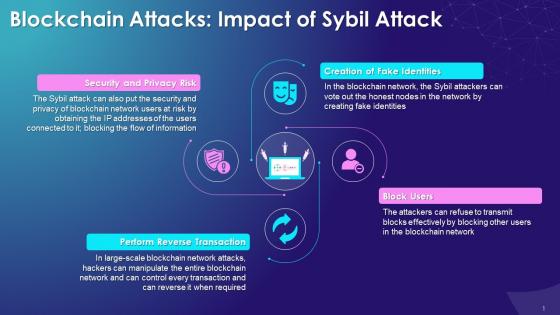 Impact Of Sybil Attack On Blockchain Network Training Ppt
Impact Of Sybil Attack On Blockchain Network Training PptPresenting Impact of Sybil Attack on Blockchain Network. These slides are 100 Percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
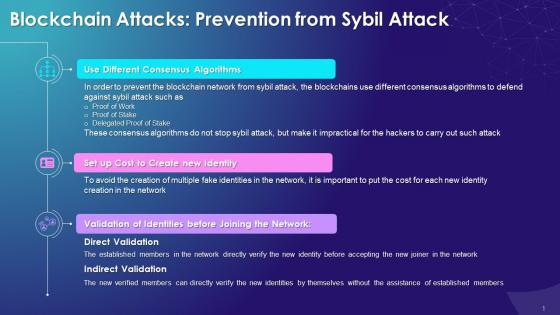 Prevention From Sybil Attack On Blockchain Network Training Ppt
Prevention From Sybil Attack On Blockchain Network Training PptPresenting Prevention from Sybil Attack on Blockchain Network. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
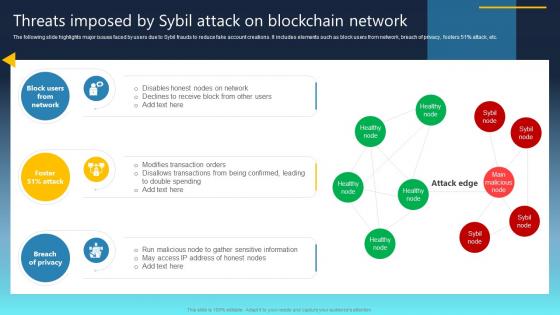 Ultimate Guide For Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS
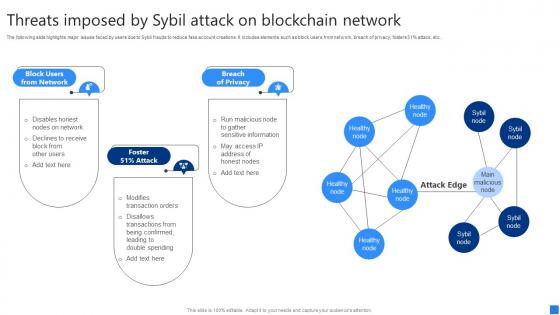
Ultimate Guide For Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SSThe following slide represents the number of cryptocurrencies theft incidents by total amount to prevent attackers from unauthorized access. It includes elements such as ronin, poly network, wormhole, bitmart, venus, cream finance, along with key insights, etc. Deliver an outstanding presentation on the topic using this Ultimate Guide For Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS Dispense information and present a thorough explanation of Breach Of Privacy, Block Users From Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
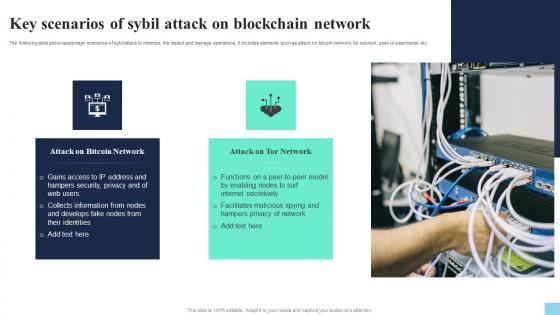 Key Scenarios Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V
Key Scenarios Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide showcases major scenarios of sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer-to-peer model, etc. Introducing Key Scenarios Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Attack On Bitcoin Network, Attack On Tor Network, using this template. Grab it now to reap its full benefits.
-
 Methods To Avoid Sybil Attack For Protecting Tokens Hands On Blockchain Security Risk BCT SS V
Methods To Avoid Sybil Attack For Protecting Tokens Hands On Blockchain Security Risk BCT SS VThe following slide illustrates various ways to minimize and prevent sybil attacks and ensure safe blockchain transactions. It includes elements such as identity validation, hierarchical, defense system, cost of new nodes, social trust graphs, etc. Increase audience engagement and knowledge by dispensing information using Methods To Avoid Sybil Attack For Protecting Tokens Hands On Blockchain Security Risk BCT SS V. This template helps you present information on five stages. You can also present information on Identity Validation, Defense System, Cost Of New Node using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
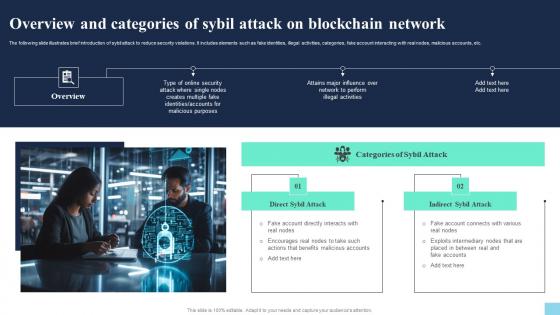 Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V
Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Introducing Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Direct Sybil Attack, Indirect Sybil Attack, using this template. Grab it now to reap its full benefits.
-
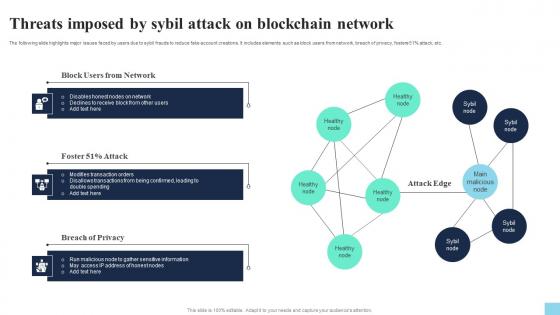 Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V
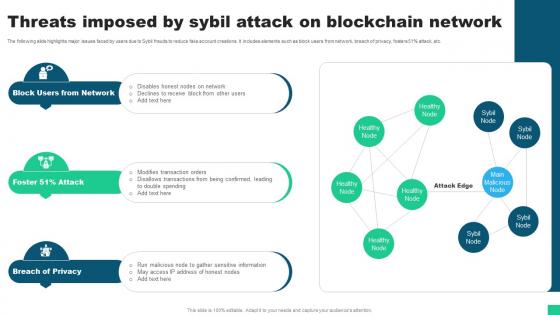
Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide highlights major issues faced by users due to sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percentage attack, etc. Increase audience engagement and knowledge by dispensing information using Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V. This template helps you present information on three stages. You can also present information on Block Users From Network, Attack, Breach Of Privacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
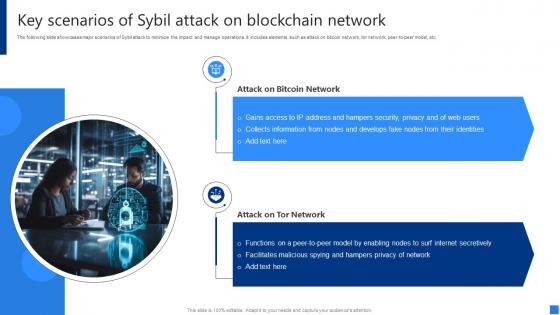 Key Scenarios Of Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V
Key Scenarios Of Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases major scenarios of Sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer to peer model, etc. Increase audience engagement and knowledge by dispensing information using Key Scenarios Of Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on two stages. You can also present information on Attack Bitcoin Network, Attack Tor Network, Hampers Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V
Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Introducing Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Block Users Network, Foster Attack, Breach Privacy, using this template. Grab it now to reap its full benefits.
-
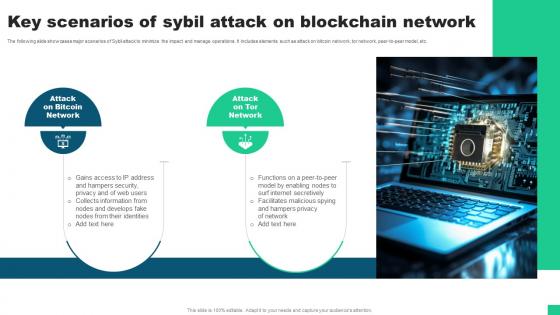 Key Scenarios Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V
Key Scenarios Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS VThe following slide showcases major scenarios of Sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer-to-peer model, etc. Introducing Key Scenarios Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Attack On Bitcoin Network, Attack On Tor Network using this template. Grab it now to reap its full benefits.
-
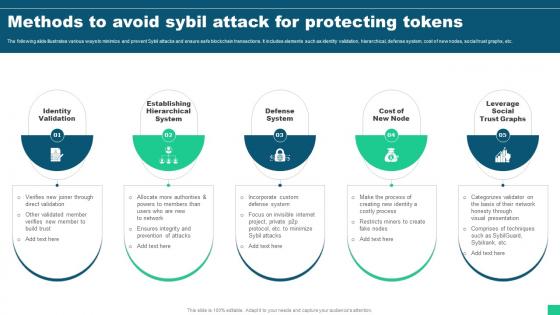 Methods To Avoid Sybil Attack For Protecting Tokens Guide For Blockchain BCT SS V
Methods To Avoid Sybil Attack For Protecting Tokens Guide For Blockchain BCT SS VThe following slide illustrates various ways to minimize and prevent Sybil attacks and ensure safe blockchain transactions. It includes elements such as identity validation, hierarchical, defense system, cost of new nodes, social trust graphs Introducing Methods To Avoid Sybil Attack For Protecting Tokens Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Identity Validation, Hierarchical System, Defense System using this template. Grab it now to reap its full benefits.
-
 Overview And Categories Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V
Overview And Categories Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS VThe following slide illustrates brief introduction of Sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Increase audience engagement and knowledge by dispensing information using Overview And Categories Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V This template helps you present information on two stages. You can also present information on Direct Sybil Attack, Categories Of Sybil Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Threats Imposed By Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V
Threats Imposed By Sybil Attack On Blockchain Network Guide For Blockchain BCT SS VThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51 percent attack, etc. Increase audience engagement and knowledge by dispensing information using Threats Imposed By Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V This template helps you present information on three stages. You can also present information on Block Users From Network, Breach Of Privacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
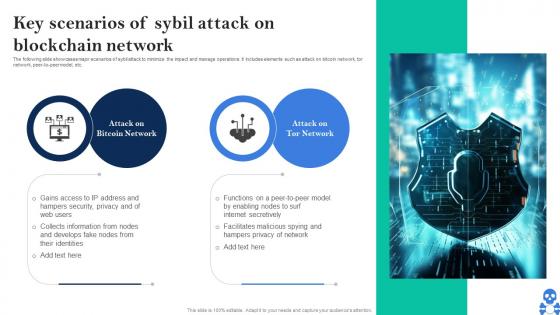 Cyber Threats In Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS V
Cyber Threats In Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS VThe following slide showcases major scenarios of sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer-to-peer model, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS V Dispense information and present a thorough explanation of Bitcoin Network, Attack On Tor Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
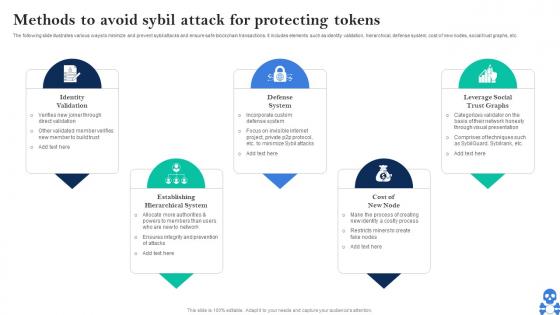 Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V
Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS VThe following slide illustrates various ways to minimize and prevent sybil attacks and ensure safe blockchain transactions. It includes elements such as identity validation, hierarchical, defense system, cost of new nodes, social trust graphs, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V This template helps you present information on Five stages. You can also present information on Identity Validation, Defense System, Cost Of New Node using this PPT design. This layout is completely editable so personaize it now
-
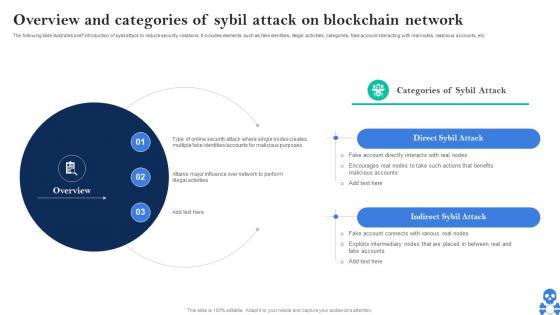 Cyber Threats In Blockchain Overview And Categories Of Sybil Attack On Blockchain Network BCT SS V
Cyber Threats In Blockchain Overview And Categories Of Sybil Attack On Blockchain Network BCT SS VThe following slide illustrates brief introduction of sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Overview And Categories Of Sybil Attack On Blockchain Network BCT SS V This template helps you present information on Two stages. You can also present information on Direct Sybil Attack, Indirect Sybil Attack using this PPT design. This layout is completely editable so personaize it now
-
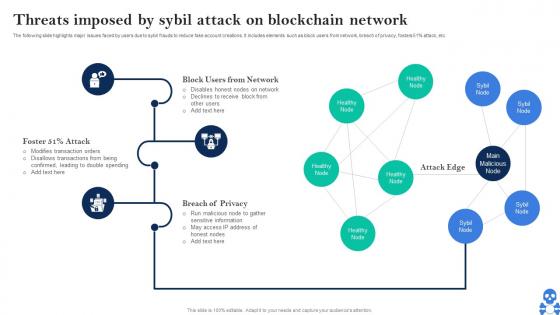 Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS V
Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS VThe following slide highlights major issues faced by users due to sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS V Dispense information and present a thorough explanation of Block Users From Network, Breach Of Privacy, Attack Edge using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Sybil Attack And Computer Connectivity Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Sybil Attack And Computer Connectivity Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Sybil attack and computer connectivity colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Sybil Attack And Computer Connectivity Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Sybil Attack And Computer Connectivity Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Sybil attack and computer connectivity monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Sybil Attack And Cyber Crime Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Sybil Attack And Cyber Crime Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Sybil attack and cyber crime colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Sybil Attack And Cyber Crime Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Sybil Attack And Cyber Crime Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Sybil attack and cyber crime monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Sybil Attack Network Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Sybil Attack Network Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Sybil attack network colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Sybil Attack Network Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Sybil Attack Network Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Sybil attack network monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
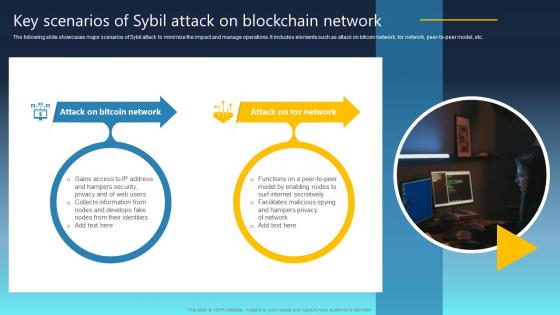 Ultimate Guide For Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS
Ultimate Guide For Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SSThe following slide showcases major scenarios of Sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer-to-peer model, etc. Increase audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS This template helps you present information on Two stages. You can also present information on Attack On Bitcoin Network, Attack On Tor Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ultimate Guide For Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS
Ultimate Guide For Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SSIntroducing Ultimate Guide For Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Identity Validation, Establishing Hierarchical System using this template. Grab it now to reap its full benefits.
-
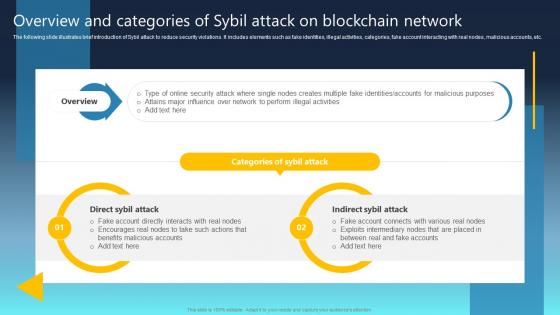 Ultimate Guide For Blockchain Overview And Categories Of Sybil Attack On Blockchain BCT SS
Ultimate Guide For Blockchain Overview And Categories Of Sybil Attack On Blockchain BCT SSThe following slide illustrates brief introduction of Sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Increase audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Overview And Categories Of Sybil Attack On Blockchain BCT SS This template helps you present information on Two stages. You can also present information on Direct Sybil Attack, Indirect Sybil Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
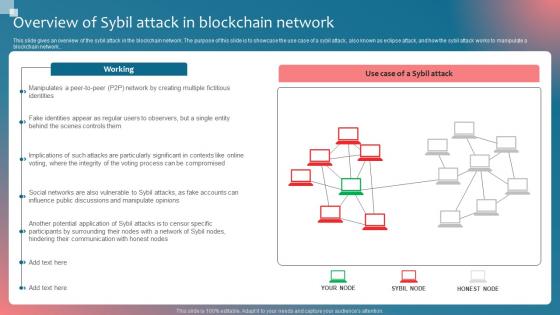 Overview Of Sybil Attack In Implementing Blockchain Security Solutions
Overview Of Sybil Attack In Implementing Blockchain Security SolutionsThis slide gives an overview of the sybil attack in the blockchain network. The purpose of this slide is to showcase the use case of a sybil attack, also known as eclipse attack, and how the sybil attack works to manipulate a blockchain network.Deliver an outstanding presentation on the topic using this Overview Of Sybil Attack In Implementing Blockchain Security Solutions. Dispense information and present a thorough explanation of Hindering Communication, Potential Application, Fake Identities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.

