Powerpoint Templates and Google slides for Symmetric And Asymmetric Encryption
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Comparison Symmetric And Asymmetric Encryption Encryption For Data Privacy In Digital Age It
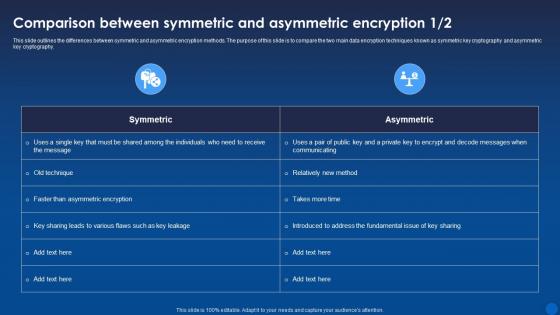
Comparison Symmetric And Asymmetric Encryption Encryption For Data Privacy In Digital Age ItThis slide outlines the differences between symmetric and asymmetric encryption methods. The purpose of this slide is to compare the two main data encryption techniques known as symmetric key cryptography and asymmetric key cryptography. Present the topic in a bit more detail with this Comparison Symmetric And Asymmetric Encryption Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric, Encryption, Comparison. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparative Analysis Of Symmetric And Asymmetric Encryption Cloud Cryptography
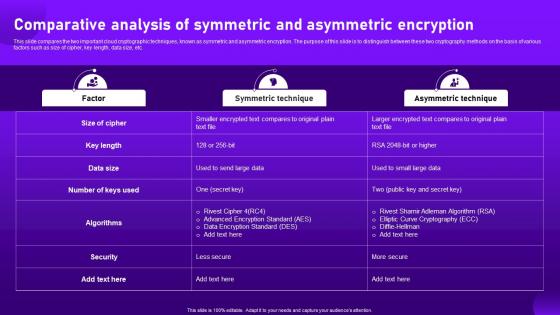
Comparative Analysis Of Symmetric And Asymmetric Encryption Cloud CryptographyThis slide compares the two important cloud cryptographic techniques, known as symmetric and asymmetric encryption. The purpose of this slide is to distinguish between these two cryptography methods on the basis of various factors such as size of cipher, key length, data size, etc. Present the topic in a bit more detail with this Comparative Analysis Of Symmetric And Asymmetric Encryption Cloud Cryptography. Use it as a tool for discussion and navigation on Comparative, Analysis, Asymmetric Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption Algorithms
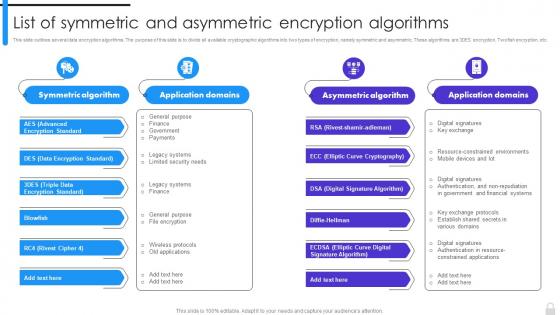
Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption AlgorithmsThis slide outlines several data encryption algorithms. The purpose of this slide is to divide all available cryptographic algorithms into two types of encryption, namely symmetric and asymmetric. These algorithms are 3DES encryption, Twofish encryption, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption Algorithms. Dispense information and present a thorough explanation of Data Encryption Standard, Triple Data Encryption Standard, Digital Signature Algorithm, Elliptic Curve Cryptography using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
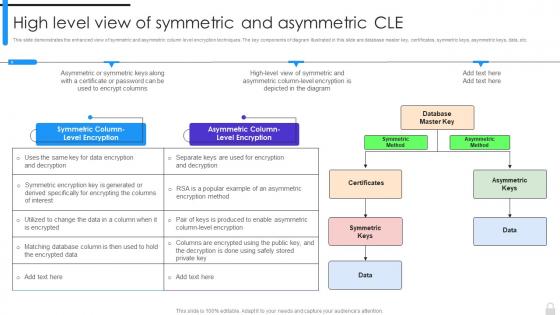 Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric Cle
Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric CleThis slide demonstrates the enhanced view of symmetric and asymmetric column level encryption techniques. The key components of diagram illustrated in this slide are database master key, certificates, symmetric keys, asymmetric keys, data, etc. Introducing Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric Cle to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Symmetric Method, Asymmetric Method, Asymmetric Column Level Encryption, Symmetric Column Level Encryption, using this template. Grab it now to reap its full benefits.
-
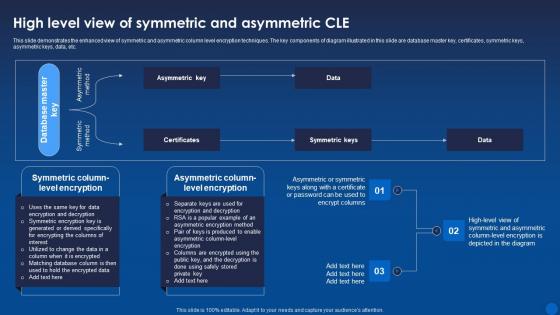 High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age It
High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age ItThis slide demonstrates the enhanced view of symmetric and asymmetric column level encryption techniques. The key components of diagram illustrated in this slide are database master key, certificates, symmetric keys, asymmetric keys, data, etc. Deliver an outstanding presentation on the topic using this High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Symmetric, Asymmetric, Certificates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
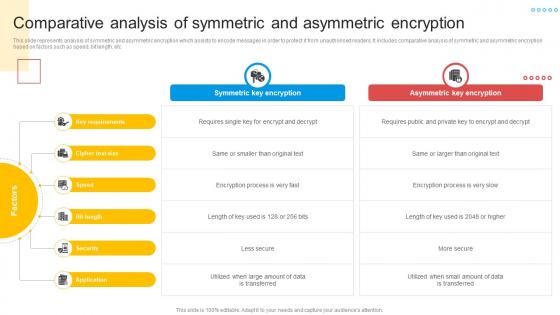 Comparative Analysis Of Symmetric And Asymmetric Encryption
Comparative Analysis Of Symmetric And Asymmetric EncryptionThis slide represents analysis of symmetric and asymmetric encryption which assists to encode messages in order to protect it from unauthorised readers. It includes comparative analysis of symmetric and asymmetric encryption based on factors such as speed, bit length, etc. Introducing our premium set of slides with name Comparative Analysis Of Symmetric And Asymmetric Encryption. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Symmetric Key Encryption, Asymmetric Key Encryption, Key Requirements. So download instantly and tailor it with your information.
-
 Symmetric Asymmetric Encryption In Powerpoint And Google Slides Cpb
Symmetric Asymmetric Encryption In Powerpoint And Google Slides CpbPresenting our Symmetric Asymmetric Encryption In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Symmetric Asymmetric Encryption. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Asymmetric Symmetric In Powerpoint And Google Slides Cpb
Asymmetric Symmetric In Powerpoint And Google Slides CpbPresenting Asymmetric Symmetric In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Asymmetric Symmetric. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.