Powerpoint Templates and Google slides for Theft And Data Breach
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
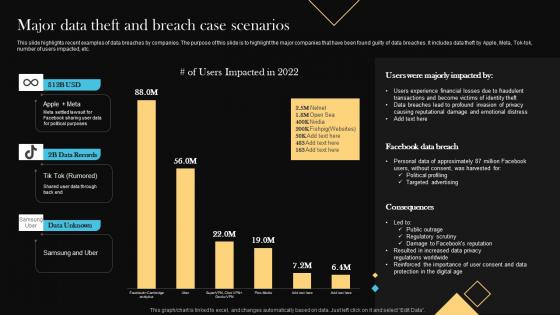 Major Data Theft And Breach Case Scenarios
Major Data Theft And Breach Case ScenariosThis slide highlights recent examples of data breaches by companies. The purpose of this slide is to highlight the major companies that have been found guilty of data breaches. It includes data theft by Apple, Meta, Tok tok, number of users impacted, etc. Presenting our well structured Major Data Theft And Breach Case Scenarios. The topics discussed in this slide are Majorly, Consequences, Harvested. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Data Breach Prevention About Identity Theft Overview And Techniques
Data Breach Prevention About Identity Theft Overview And TechniquesThis slide talks about the major crime committed by phishers, named as identity theft. The purpose of this slide is to outline the ways of stealing information, such as robbery, computer fraud, social networking sites, mail theft, and dumpster diving. Present the topic in a bit more detail with this Data Breach Prevention About Identity Theft Overview And Techniques. Use it as a tool for discussion and navigation on Drivers License, Social Security Card, Debit Or Credit Cards, Social Media Account. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 File Protection And Data Theft Prevention Icon
File Protection And Data Theft Prevention IconPresenting our well structured File Protection And Data Theft Prevention Icon. The topics discussed in this slide are Protection, Data, Prevention. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
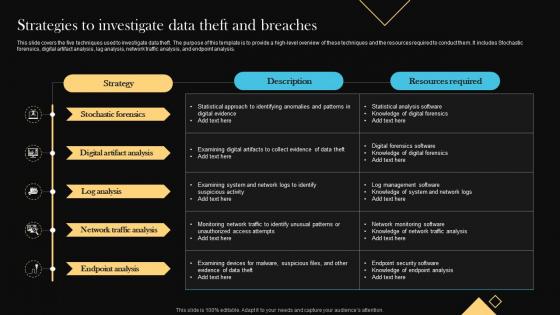 Strategies To Investigate Data Theft And Breaches
Strategies To Investigate Data Theft And BreachesThis slide covers the five techniques used to investigate data theft. The purpose of this template is to provide a high level overview of these techniques and the resources required to conduct them. It includes Stochastic forensics, digital artifact analysis, lag analysis, network traffic analysis, and endpoint analysis. Introducing our Strategies To Investigate Data Theft And Breaches set of slides. The topics discussed in these slides are Analysis, Digital, Endpoint. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Crypto Wallets Types And Applications Data Theft And Financial Fraud Privacy Concerns
Crypto Wallets Types And Applications Data Theft And Financial Fraud Privacy ConcernsThis slide represents the data theft and financial fraud happening in the crypto world. The purpose of this slide is to highlight the concerns such as lack of rules, exposure of data, uncertainty existing because of data rules, etc. Introducing Crypto Wallets Types And Applications Data Theft And Financial Fraud Privacy Concerns to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Financial Fraud Happening, Lack Of Rules, Exposure Of Data, Financial Fraud Privacy Concerns, using this template. Grab it now to reap its full benefits.
-
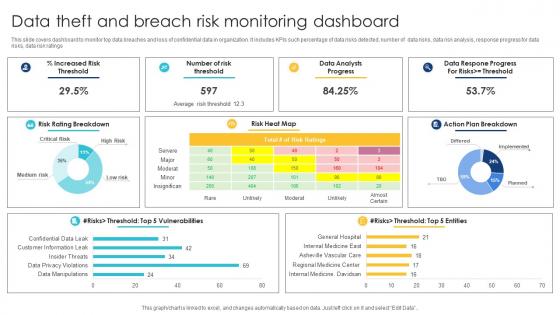 Data Theft And Breach Risk Monitoring Dashboard
Data Theft And Breach Risk Monitoring DashboardThis slide covers dashboard to monitor top data breaches and loss of confidential data in organization. It includes KPIs such percentage of data risks detected, number of data risks, data risk analysis, response progress for data risks, data risk ratings. Presenting our well structured Data Theft And Breach Risk Monitoring Dashboard. The topics discussed in this slide are Data Theft And Breach, Risk Monitoring, Dashboard. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
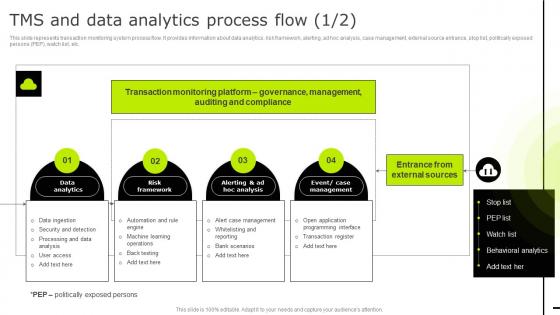 Tms And Data Analytics Process Flow Reducing Business Frauds And Thefts Through Effective Financial Alm
Tms And Data Analytics Process Flow Reducing Business Frauds And Thefts Through Effective Financial AlmThis slide represents transaction monitoring system process flow. It provides information about data analytics, risk framework, alerting, ad hoc analysis, case management, external source entrance, stop list, politically exposed persons PEP, watch list, etc. Present the topic in a bit more detail with this Tms And Data Analytics Process Flow Reducing Business Frauds And Thefts Through Effective Financial Alm. Use it as a tool for discussion and navigation on Analytics, Process, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Data Theft Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Confidential Data Theft Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Confidential data theft colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Confidential Data Theft Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Confidential Data Theft Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Confidential data theft monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Cyber Data Theft Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Data Theft Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cyber data theft colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cyber Data Theft Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Data Theft Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cyber data theft monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Digital Data Theft Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Data Theft Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Digital data theft colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Digital Data Theft Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Data Theft Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Digital data theft monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Audit Action Plan Icon To Reduce Data Theft And Money Laundering
Audit Action Plan Icon To Reduce Data Theft And Money LaunderingPresenting our set of slides with name Audit Action Plan Icon To Reduce Data Theft And Money Laundering. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Audit Action Plan, Icon, Reduce Data, Money Laundering.
-
 Data Theft Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Theft Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Data theft colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Data Theft Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Theft Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Data theft monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.