Powerpoint Templates and Google slides for Threats Checklist Icon
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Checklist For Bomb Threat At A Hotel Training Ppt
Checklist For Bomb Threat At A Hotel Training PptPresenting Checklist for Bomb Threat at a Hotel. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
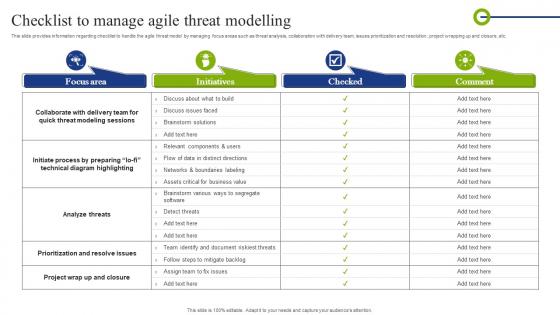 Checklist To Manage Agile Threat Modelling Playbook To Mitigate Negative Of Technology
Checklist To Manage Agile Threat Modelling Playbook To Mitigate Negative Of TechnologyThis slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Present the topic in a bit more detail with this Checklist To Manage Agile Threat Modelling Playbook To Mitigate Negative Of Technology. Use it as a tool for discussion and navigation on Collaborate, Prioritization, Initiate Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
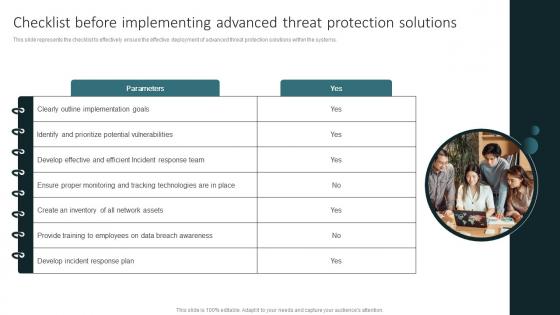 Checklist Before Implementing Advanced Threat Protection Solutions
Checklist Before Implementing Advanced Threat Protection SolutionsThis slide represents the checklist to effectively ensure the effective deployment of advanced threat protection solutions within the systems. Presenting our set of slides with Checklist Before Implementing Advanced Threat Protection Solutions. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementing, Advanced, Protection.
-
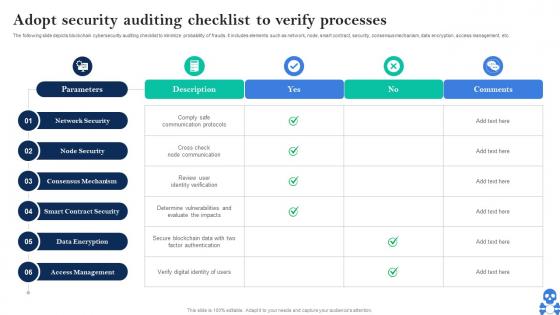 Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V
Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS VThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V Dispense information and present a thorough explanation of Consensus Mechanism, Smart Contract Security, Data Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
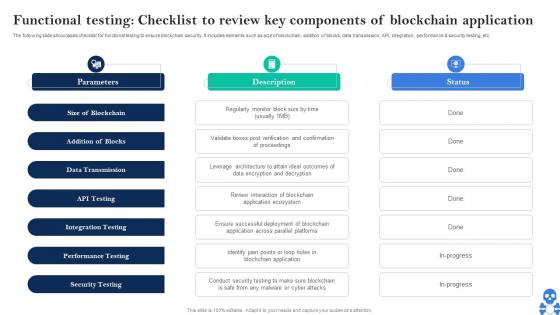 Cyber Threats In Blockchain Functional Testing Checklist To Review Key Components Of Blockchain BCT SS V
Cyber Threats In Blockchain Functional Testing Checklist To Review Key Components Of Blockchain BCT SS VThe following slide showcases checklist for functional testing to ensure blockchain security. It includes elements such as size of blockchain, addition of blocks, data transmission, API, integration, performance and security testing, etc. Introducing Cyber Threats In Blockchain Functional Testing Checklist To Review Key Components Of Blockchain BCT SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Size Of Blockchain, Addition Of Blocks, Data Transmission using this template. Grab it now to reap its full benefits.
-
 Cyber Terrorism Attacks Checklist To Deal With Cyber Terrorism Threats
Cyber Terrorism Attacks Checklist To Deal With Cyber Terrorism ThreatsThis slide represents the checklist to deal with cyber terrorism attacks threats which involve 24 7 monitoring, employee training, keeping software updated. Increase audience engagement and knowledge by dispensing information using Cyber Terrorism Attacks Checklist To Deal With Cyber Terrorism Threats. This template helps you present information on nine stages. You can also present information on Cyber Security Assessment, Limited Access Privileges, Employee Training, External Cyber Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability Administration At Workplace Key Activities Checklist Associated To Insider Threat Program
Vulnerability Administration At Workplace Key Activities Checklist Associated To Insider Threat ProgramThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Key Activities Checklist Associated To Insider Threat Program. Dispense information and present a thorough explanation of Processes, Effectiveness, Review And Analyze using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
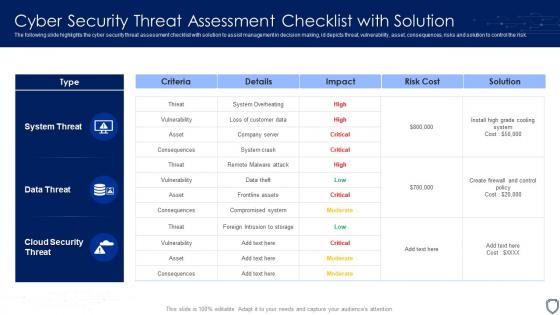 Cyber Security Threat Assessment Checklist With Solution
Cyber Security Threat Assessment Checklist With SolutionThe following slide highlights the cyber security threat assessment checklist with solution to assist management in decision making, id depicts threat, vulnerability, asset, consequences, risks and solution to control the risk. Introducing our Cyber Security Threat Assessment Checklist With Solution set of slides. The topics discussed in these slides are System Threat, Data Threat, Cloud Security Threat. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
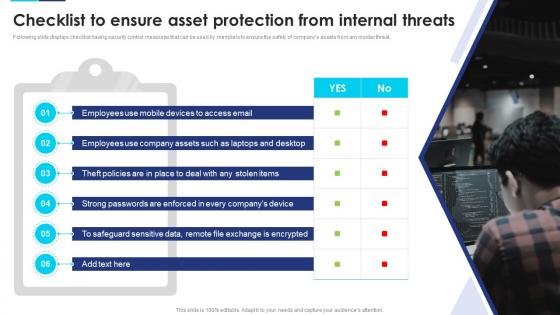 Incident Response Playbook Checklist To Ensure Asset Protection From Internal Threats
Incident Response Playbook Checklist To Ensure Asset Protection From Internal ThreatsFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Introducing Incident Response Playbook Checklist To Ensure Asset Protection From Internal Threats to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Mobile Devices, Company Assets, Employees, using this template. Grab it now to reap its full benefits.
-
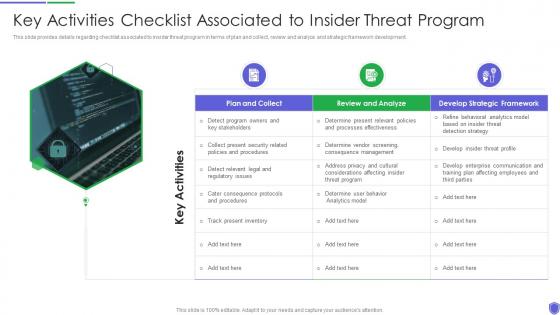 Key activities checklist associated to managing critical threat vulnerabilities and security threats
Key activities checklist associated to managing critical threat vulnerabilities and security threatsThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Introducing Key Activities Checklist Associated To Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Plan And Collect, Review And Analyze, Develop Strategic Framework, using this template. Grab it now to reap its full benefits.
-
 Cyberterrorism it checklist to deal with cyber terrorism threats ppt slides templates
Cyberterrorism it checklist to deal with cyber terrorism threats ppt slides templatesThis slide represents the checklist to deal with cyber terrorism threats which involve 24 7 monitoring, employee training, keeping software updated. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Checklist To Deal With Cyber Terrorism Threats Ppt Slides Templates. This template helps you present information on one stages. You can also present information on Incident Response Plan, Limited Access Privileges, Evaluating Risk Third Party Vendor, Cyber Security Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
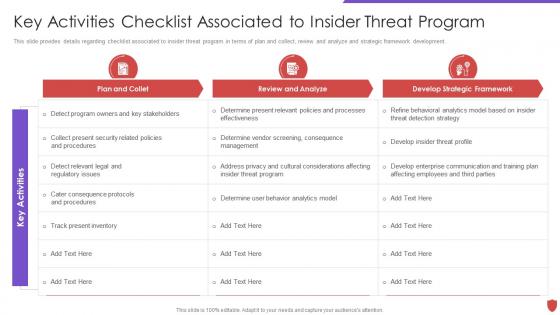 Cyber security risk management key activities checklist associated to insider threat
Cyber security risk management key activities checklist associated to insider threatThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Deliver an outstanding presentation on the topic using this Cyber Security Risk Management Key Activities Checklist Associated To Insider Threat. Dispense information and present a thorough explanation of Plan And Collet, Review And Analyze, Develop Strategic Framework, Track Present Inventory using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
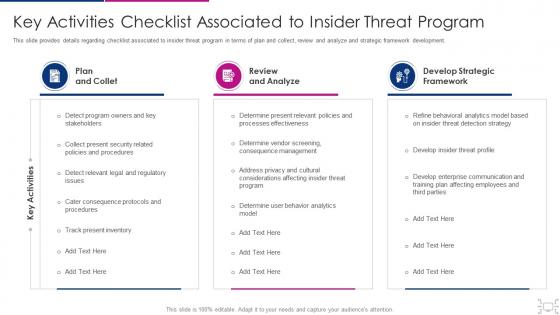 Cyber threat management workplace key activities checklist associated insider
Cyber threat management workplace key activities checklist associated insiderThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Present the topic in a bit more detail with this Cyber Threat Management Workplace Key Activities Checklist Associated Insider. Use it as a tool for discussion and navigation on Plan And Collet, Review And Analyze, Develop Strategic Framework, Track Present Inventory, Determine User Behavior Analytics Model . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Checklist To Mitigate Threats Of Attack
Cyber Security Checklist To Mitigate Threats Of AttackThe given slide provides the key activities to be done to alleviate the effects of cyber threats. It includes managing social media profiles, backing up the data, crosschecking privacy and security settings etc. Introducing our premium set of slides with Cyber Security Checklist To Mitigate Threats Of Attack. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Checklist, Mitigate Threats Attack. So download instantly and tailor it with your information.
-
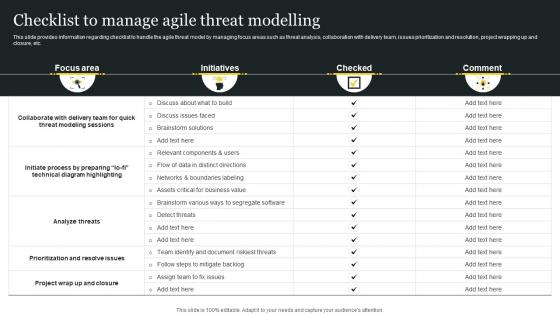 Responsible Tech Playbook To Leverage Checklist To Manage Agile Threat Modelling Ppt Ideas Tips
Responsible Tech Playbook To Leverage Checklist To Manage Agile Threat Modelling Ppt Ideas TipsThis slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Deliver an outstanding presentation on the topic using this Responsible Tech Playbook To Leverage Checklist To Manage Agile Threat Modelling Ppt Ideas Tips. Dispense information and present a thorough explanation of Collaborate With Delivery Team, Analyze Threats, Prioritization And Resolve Issues using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability
Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And VulnerabilityFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Introducing Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Email, Mobile Devices, using this template. Grab it now to reap its full benefits.
-
 Checklist For Digital Safety Threat And Risk Assessment
Checklist For Digital Safety Threat And Risk AssessmentThis slide represents digital safety threat and assessment checklist which ensure risk management in cost effective manner. It provides information regarding conducting assessment, perform threat analysis, risk mitigation and process completion. Introducing our Checklist For Digital Safety Threat And Risk Assessment set of slides. The topics discussed in these slides are Conduct Assessment, Perform Threat Analysis, Result And Completion. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook
Checklist To Ensure Asset Protection From Internal Threats Security Incident Response PlaybookFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Deliver an outstanding presentation on the topic using this Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook. Dispense information and present a thorough explanation of Protection, Measures, Ensure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
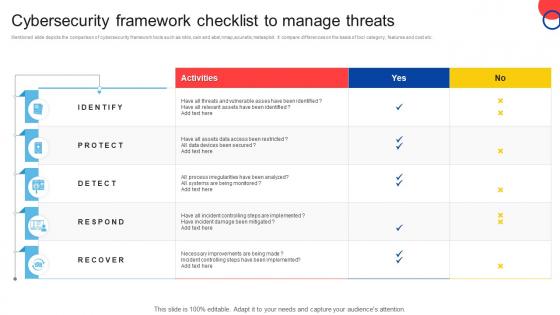 Cybersecurity Framework Checklist To Manage Threats
Cybersecurity Framework Checklist To Manage ThreatsMentioned slide depicts the comparison of cybersecurity framework tools such as nikto,cain and abel,nmap,acunetix,metasploit. It compare differences on the basis of tool category, features and cost etc. Introducing our Cybersecurity Framework Checklist To Manage Threats set of slides. The topics discussed in these slides are Identify, Protect, Respond. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
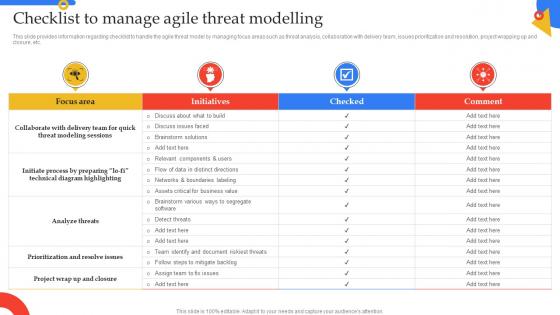 Checklist To Manage Agile Threat Modelling Guide To Manage Responsible Technology Playbook
Checklist To Manage Agile Threat Modelling Guide To Manage Responsible Technology PlaybookThis slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Present the topic in a bit more detail with this Checklist To Manage Agile Threat Modelling Guide To Manage Responsible Technology Playbook. Use it as a tool for discussion and navigation on Analysis, Collaboration, Resolution. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ultimate Guide To Handle Business Checklist To Manage Agile Threat Modelling
Ultimate Guide To Handle Business Checklist To Manage Agile Threat ModellingThis slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Present the topic in a bit more detail with this Ultimate Guide To Handle Business Checklist To Manage Agile Threat Modelling. Use it as a tool for discussion and navigation on Agile Threat Modelling, Prioritization And Resolve Issues, Brainstorm Solutions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
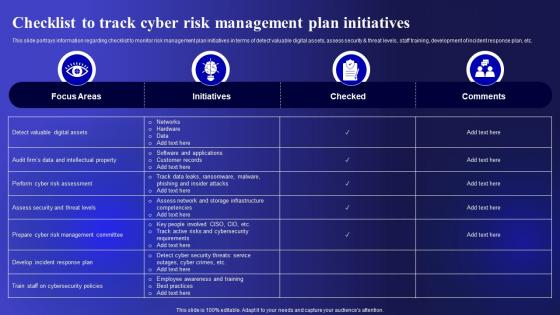 Checklist To Track Cyber Risk Management Cyber Threats Management To Enable Digital Assets Security
Checklist To Track Cyber Risk Management Cyber Threats Management To Enable Digital Assets SecurityThis slide portrays information regarding checklist to monitor risk management plan initiatives in terms of detect valuable digital assets, assess security and threat levels, staff training, development of incident response plan, etc. Present the topic in a bit more detail with this Checklist To Track Cyber Risk Management Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Management, Initiatives, Development. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Activities Checklist Associated To Insider Cyber Threats Management To Enable Digital Assets Security
Key Activities Checklist Associated To Insider Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Increase audience engagement and knowledge by dispensing information using Key Activities Checklist Associated To Insider Cyber Threats Management To Enable Digital Assets Security. This template helps you present information on three stages. You can also present information on Plan And Collect, Review And Analyze, Strategic Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Macro Analysis Of Threats Checklist Icon
Macro Analysis Of Threats Checklist IconPresenting our set of slides with Macro Analysis Of Threats Checklist Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Macro Analysis, Threats Checklist Icon.
-
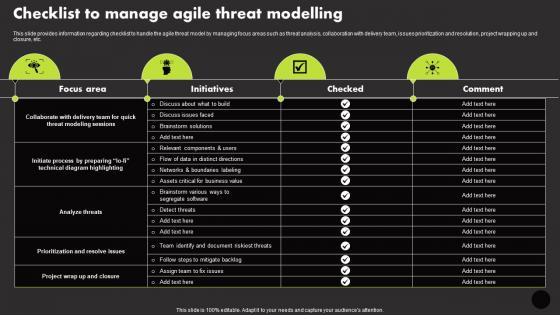 Checklist To Manage Agile Threat Modelling Manage Technology Interaction With Society Playbook
Checklist To Manage Agile Threat Modelling Manage Technology Interaction With Society PlaybookThis slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Present the topic in a bit more detail with this Checklist To Manage Agile Threat Modelling Manage Technology Interaction With Society Playbook. Use it as a tool for discussion and navigation on Focus Area, Initiatives, Checked. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
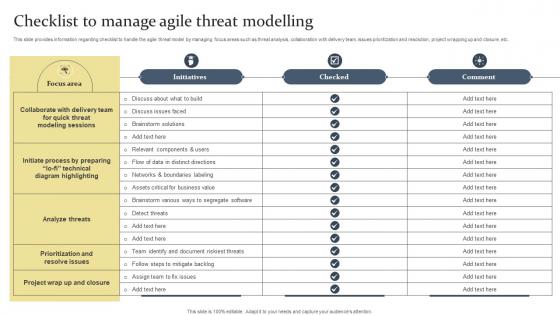 Checklist To Manage Agile Threat Modelling Ethical Tech Governance Playbook
Checklist To Manage Agile Threat Modelling Ethical Tech Governance PlaybookThis slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Deliver an outstanding presentation on the topic using this Checklist To Manage Agile Threat Modelling Ethical Tech Governance Playbook. Dispense information and present a thorough explanation of Analyze Threats, Prioritization And Resolve Issues, Collaborate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
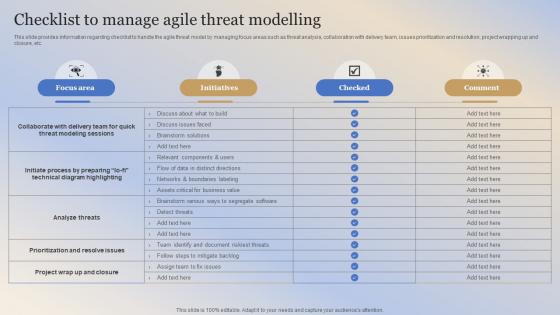 Building Responsible Organization Checklist To Manage Agile Threat Modelling
Building Responsible Organization Checklist To Manage Agile Threat ModellingThis slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Present the topic in a bit more detail with this Building Responsible Organization Checklist To Manage Agile Threat Modelling. Use it as a tool for discussion and navigation on Threat Modeling Sessions, Technical Diagram Highlighting, Agile Threat Modelling. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
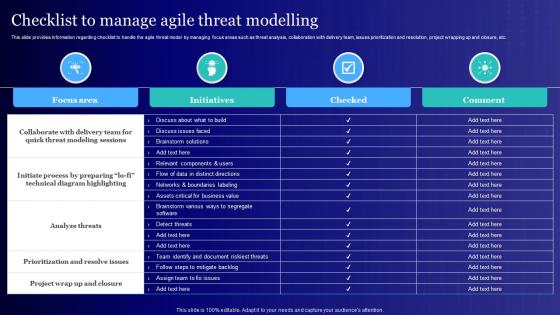 Checklist To Manage Agile Threat Modelling Usage Of Technology Ethically
Checklist To Manage Agile Threat Modelling Usage Of Technology EthicallyThis slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc.Deliver an outstanding presentation on the topic using this Checklist To Manage Agile Threat Modelling Usage Of Technology Ethically. Dispense information and present a thorough explanation of Prioritization Resolve Issues, Analyze Threats, Modeling Sessions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
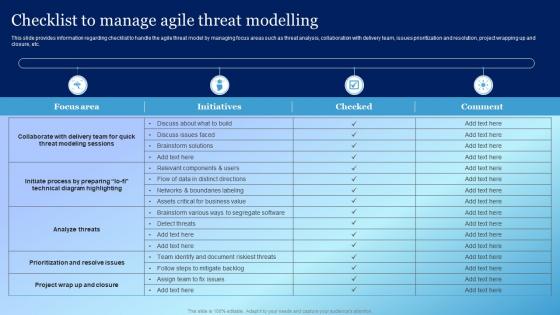 Checklist To Manage Agile Threat Modelling Playbook For Responsible Tech Tools
Checklist To Manage Agile Threat Modelling Playbook For Responsible Tech ToolsThis slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Deliver an outstanding presentation on the topic using this Checklist To Manage Agile Threat Modelling Playbook For Responsible Tech Tools. Dispense information and present a thorough explanation of Modeling Sessions, Technical Diagram, Project using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.

