Powerpoint Templates and Google slides for Traditional Security Model
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
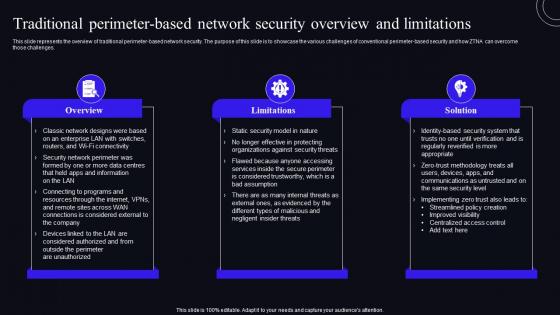 Traditional Perimeter Based Network Security Overview And Limitations Zero Trust Security Model
Traditional Perimeter Based Network Security Overview And Limitations Zero Trust Security ModelThis slide represents the overview of traditional perimeter-based network security. The purpose of this slide is to showcase the various challenges of conventional perimeter-based security and how ZTNA can overcome those challenges. Deliver an outstanding presentation on the topic using this Traditional Perimeter Based Network Security Overview And Limitations Zero Trust Security Model. Dispense information and present a thorough explanation of Traditional, Overview, Limitations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
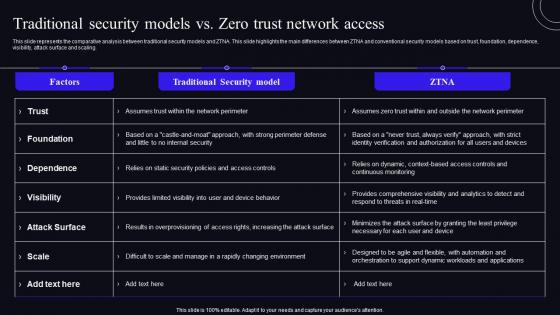 Traditional Security Models Vs Zero Trust Network Access Zero Trust Security Model
Traditional Security Models Vs Zero Trust Network Access Zero Trust Security ModelThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Present the topic in a bit more detail with this Traditional Security Models Vs Zero Trust Network Access Zero Trust Security Model. Use it as a tool for discussion and navigation on Dependence, Foundation, Attack Surface. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
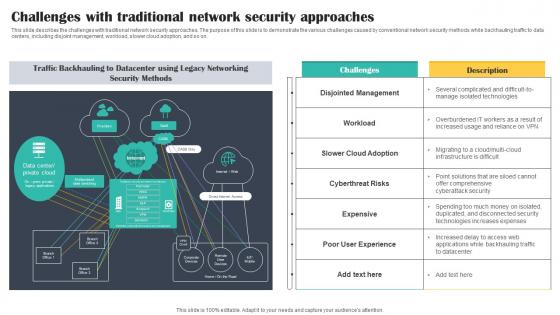 Challenges With Traditional Network Security Approaches Cloud Security Model
Challenges With Traditional Network Security Approaches Cloud Security ModelThis slide describes the challenges with traditional network security approaches. The purpose of this slide is to demonstrate the various challenges caused by conventional network security methods while backhauling traffic to data centers, including disjoint management, workload, slower cloud adoption, and so on. Deliver an outstanding presentation on the topic using this Challenges With Traditional Network Security Approaches Cloud Security Model. Dispense information and present a thorough explanation of Approaches, Security, Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
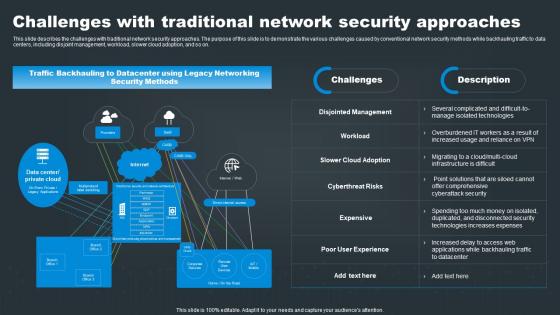 Challenges With Traditional Network Security Approaches SASE Network Security
Challenges With Traditional Network Security Approaches SASE Network SecurityThis slide describes the challenges with traditional network security approaches. The purpose of this slide is to demonstrate the various challenges caused by conventional network security methods while backhauling traffic to data centers, including disjoint management, workload, slower cloud adoption, and so on. Present the topic in a bit more detail with this Challenges With Traditional Network Security Approaches SASE Network Security. Use it as a tool for discussion and navigation on Security, Traditional, Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
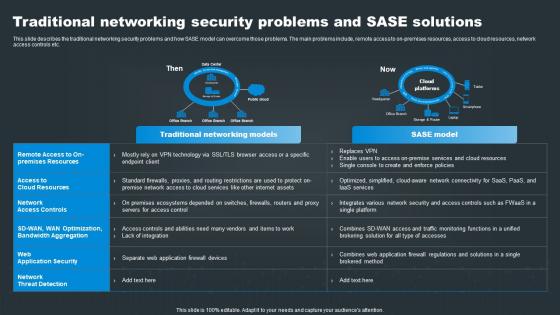 SASE Network Security Traditional Networking Security Problems And SASE Solutions
SASE Network Security Traditional Networking Security Problems And SASE SolutionsThis slide describes the traditional networking security problems and how SASE model can overcome those problems. The main problems include, remote access to on premises resources, access to cloud resources, network access controls etc. Deliver an outstanding presentation on the topic using this SASE Network Security Traditional Networking Security Problems And SASE Solutions. Dispense information and present a thorough explanation of Networking, Solutions, Problems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
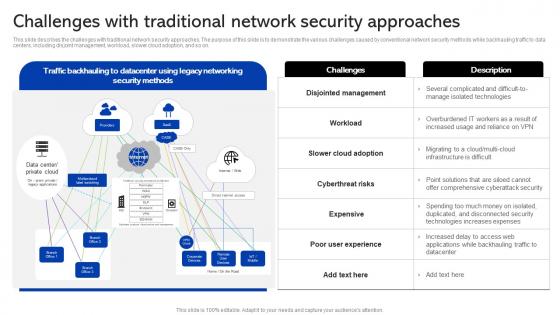 Sase Security Challenges With Traditional Network Security Approaches
Sase Security Challenges With Traditional Network Security ApproachesThis slide describes the challenges with traditional network security approaches. The purpose of this slide is to demonstrate the various challenges caused by conventional network security methods while backhauling traffic to data centers, including disjoint management, workload, slower cloud adoption, and so on. Deliver an outstanding presentation on the topic using this Sase Security Challenges With Traditional Network Security Approaches. Dispense information and present a thorough explanation of Cyberthreat Risks, Disjointed Management, Poor User Experience using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
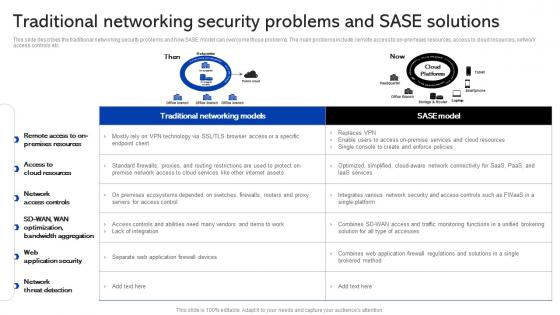 Sase Security Traditional Networking Security Problems And Sase Solutions
Sase Security Traditional Networking Security Problems And Sase SolutionsThis slide describes the traditional networking security problems and how SASE model can overcome those problems. The main problems include, remote access to on-premises resources, access to cloud resources, network access controls etc. Present the topic in a bit more detail with this Sase Security Traditional Networking Security Problems And Sase Solutions. Use it as a tool for discussion and navigation on Traditional, Networking, Solutions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
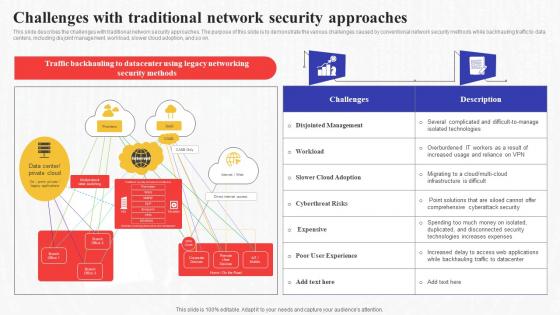 Challenges With Traditional Network Security Approaches Secure Access Service Edge Sase
Challenges With Traditional Network Security Approaches Secure Access Service Edge SaseThis slide describes the challenges with traditional network security approaches. The purpose of this slide is to demonstrate the various challenges caused by conventional network security methods while backhauling traffic to data centers, including disjoint management, workload, slower cloud adoption, and so on. Present the topic in a bit more detail with this Challenges With Traditional Network Security Approaches Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Approaches, Demonstrate, Conventional. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
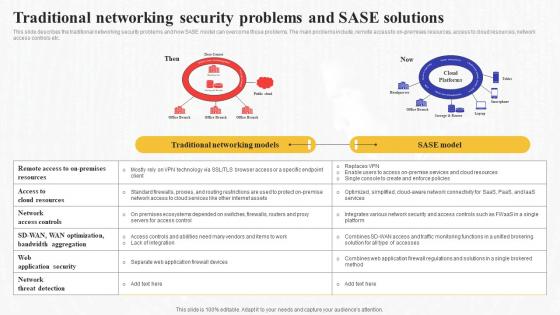 Traditional Networking Security Problems And Sase Solutions Secure Access Service Edge Sase
Traditional Networking Security Problems And Sase Solutions Secure Access Service Edge SaseThis slide describes the traditional networking security problems and how SASE model can overcome those problems. The main problems include, remote access to on-premises resources, access to cloud resources, network access controls etc. Present the topic in a bit more detail with this Traditional Networking Security Problems And Sase Solutions Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Traditional, Networking, Solutions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
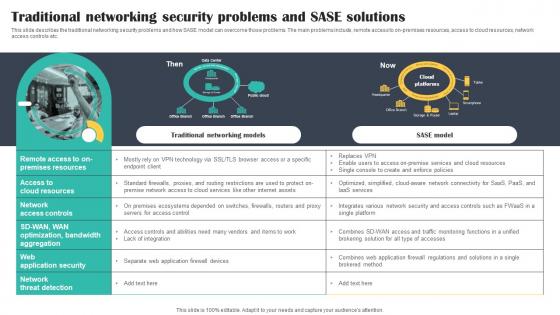 Traditional Networking Security Problems And SASE Solutions Cloud Security Model
Traditional Networking Security Problems And SASE Solutions Cloud Security ModelThis slide describes the traditional networking security problems and how SASE model can overcome those problems. The main problems include, remote access to on-premises resources, access to cloud resources, network access controls etc. Deliver an outstanding presentation on the topic using this Traditional Networking Security Problems And SASE Solutions Cloud Security Model. Dispense information and present a thorough explanation of Networking, Model, Solutions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
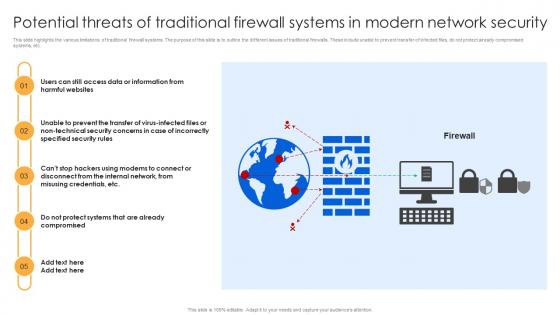 Potential Threats Of Traditional Firewall Systems In Modern Network Security Firewall Virtualization
Potential Threats Of Traditional Firewall Systems In Modern Network Security Firewall VirtualizationThis slide highlights the various limitations of traditional firewall systems. The purpose of this slide is to outline the different issues of traditional firewalls. These include unable to prevent transfer of infected files, do not protect already compromised systems, etc. Deliver an outstanding presentation on the topic using this Potential Threats Of Traditional Firewall Systems In Modern Network Security Firewall Virtualization. Dispense information and present a thorough explanation of Harmful Websites, Non Technical Security, Security Rules using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
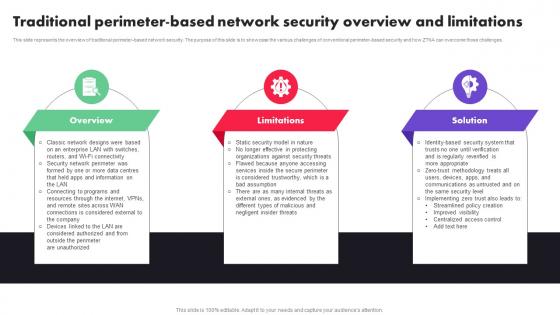 Zero Trust Architecture Traditional Perimeter Based Network Security Overview And Limitations Ppt File Guide
Zero Trust Architecture Traditional Perimeter Based Network Security Overview And Limitations Ppt File GuideThis slide represents the overview of traditional perimeter-based network security. The purpose of this slide is to showcase the various challenges of conventional perimeter-based security and how ZTNA can overcome those challenges. Introducing Zero Trust Architecture Traditional Perimeter Based Network Security Overview And Limitations Ppt File Guide to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Limitations, Solution, using this template. Grab it now to reap its full benefits.
-
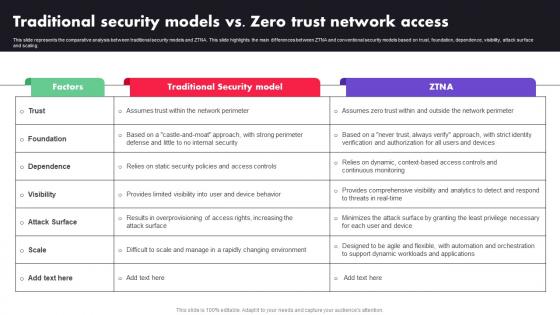 M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTA
M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTAThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Deliver an outstanding presentation on the topic using this M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTA. Dispense information and present a thorough explanation of Factors, Traditional Security Model, ZTNA using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
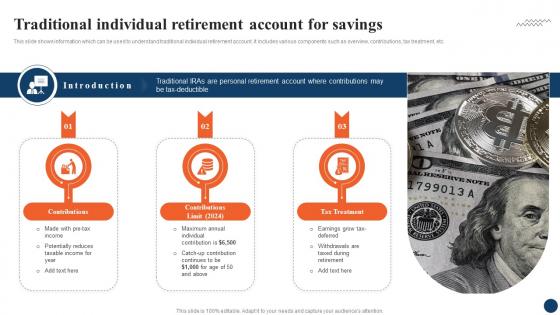 Traditional Individual Retirement Strategic Retirement Planning To Build Secure Future Fin SS
Traditional Individual Retirement Strategic Retirement Planning To Build Secure Future Fin SSThis slide shows information which can be used to understand traditional individual retirement account. It includes various components such as overview, contributions, tax treatment, etc. Increase audience engagement and knowledge by dispensing information using Traditional Individual Retirement Strategic Retirement Planning To Build Secure Future Fin SS. This template helps you present information on three stages. You can also present information on Tax Treatment, Contributions, Annual Individual using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
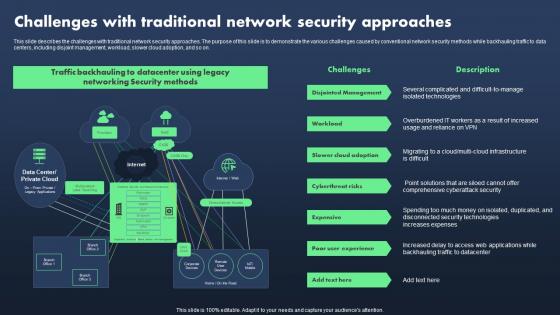 Sase Model Challenges With Traditional Network Security Approaches
Sase Model Challenges With Traditional Network Security ApproachesThis slide describes the challenges with traditional network security approaches. The purpose of this slide is to demonstrate the various challenges caused by conventional network security methods while backhauling traffic to data centers, including disjoint management, workload, slower cloud adoption, and so on. Present the topic in a bit more detail with this Sase Model Challenges With Traditional Network Security Approaches. Use it as a tool for discussion and navigation on Disjointed Management, Workload, Slower Cloud Adoption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
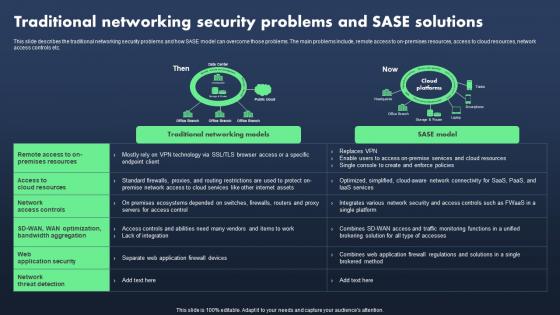 Sase Model Traditional Networking Security Problems And Sase Solutions
Sase Model Traditional Networking Security Problems And Sase SolutionsThis slide describes the traditional networking security problems and how SASE model can overcome those problems. The main problems include, remote access to on-premises resources, access to cloud resources, network access controls etc. Present the topic in a bit more detail with this Sase Model Traditional Networking Security Problems And Sase Solutions. Use it as a tool for discussion and navigation on Traditional Networking Models. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
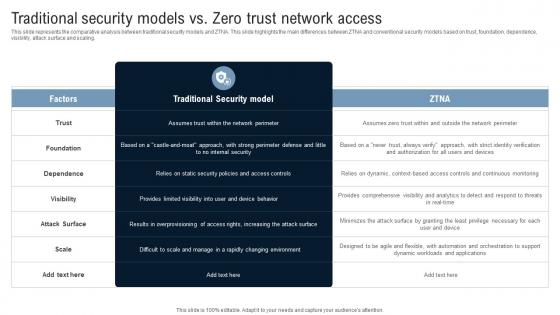 Traditional Security Models Vs Zero Trust Network Access Identity Defined Networking
Traditional Security Models Vs Zero Trust Network Access Identity Defined NetworkingThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Deliver an outstanding presentation on the topic using this Traditional Security Models Vs Zero Trust Network Access Identity Defined Networking Dispense information and present a thorough explanation of Traditional Security Model, Foundation, Dependence, Visibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Transforming From Traditional Ethical And Data Security Considerations For Digital Innovation DT SS
Transforming From Traditional Ethical And Data Security Considerations For Digital Innovation DT SSThis slide presents important ethical and legal considerations in the digital landscape. It mentions description, laws necessary for maintaining regulations including data privacy, cybersecurity and intellectual property. Introducing Transforming From Traditional Ethical And Data Security Considerations For Digital Innovation DT SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Data Privacy, Cybersecurity, Intellectual Property using this template. Grab it now to reap its full benefits.
-
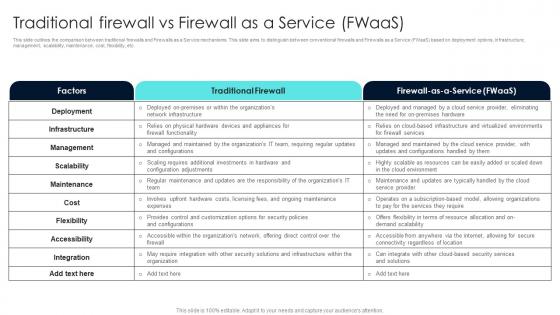 Firewall Network Security Traditional Firewall Vs Firewall As A Service FWaas
Firewall Network Security Traditional Firewall Vs Firewall As A Service FWaasThis slide outlines the comparison between traditional firewalls and Firewalls as a Service mechanisms. This slide aims to distinguish between conventional firewalls and Firewalls as a Service FWaaS based on deployment options, infrastructure, management, scalability, maintenance, cost, flexibility, etc. Present the topic in a bit more detail with this Firewall Network Security Traditional Firewall Vs Firewall As A Service FWaas Use it as a tool for discussion and navigation on Traditional Firewall, Factors, Maintenance This template is free to edit as deemed fit for your organization. Therefore download it now.
-
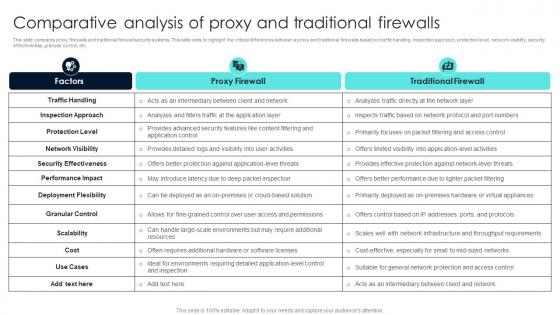 Firewall Network Security Comparative Analysis Of Proxy And Traditional Firewalls
Firewall Network Security Comparative Analysis Of Proxy And Traditional FirewallsThis slide compares proxy firewalls and traditional firewall security systems. This slide aims to highlight the critical differences between a proxy and traditional firewalls based on traffic handling, inspection approach, protection level, network visibility, security effectiveness, granular control, etc. Deliver an outstanding presentation on the topic using this Firewall Network Security Comparative Analysis Of Proxy And Traditional Firewalls Dispense information and present a thorough explanation of Proxy Firewall, Traditional Firewall using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Difference Between Cloud Security Solutions And Traditional Cloud Data Protection
Difference Between Cloud Security Solutions And Traditional Cloud Data ProtectionThis slide represents the difference between cloud security solutions and traditional IT solutions based on information centers, cost, scalability, and expenses. Deliver an outstanding presentation on the topic using this Difference Between Cloud Security Solutions And Traditional Cloud Data Protection. Dispense information and present a thorough explanation of Opportunity, Low Efficiency, Cloud Security, Expense using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Siem For Security Analysis Traditional Siem Deployment Model
Siem For Security Analysis Traditional Siem Deployment ModelThis slide covers the traditional in house SIEM model wherein the client take care of all the security incident and event management process on its own. Present the topic in a bit more detail with this Siem For Security Analysis Traditional Siem Deployment Model. Use it as a tool for discussion and navigation on Vulnerability, Management, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Computing Security Difference Between Cloud Security Solutions And Traditional IT Solutions
Cloud Computing Security Difference Between Cloud Security Solutions And Traditional IT SolutionsThis slide represents the difference between cloud security solutions and traditional IT solutions based on information centers, cost, scalability, and expenses. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security Difference Between Cloud Security Solutions And Traditional IT Solutions. This template helps you present information on two stages. You can also present information on Cloud Security, Traditional It Security, Low Efficiency using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
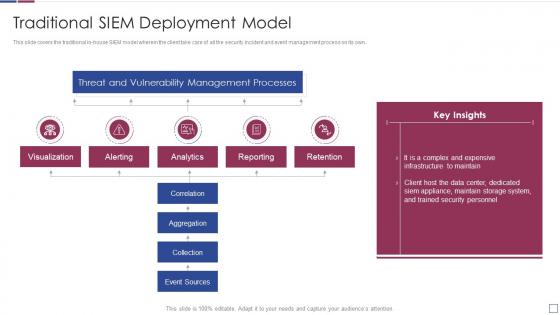 Real time analysis of security alerts traditional siem deployment model
Real time analysis of security alerts traditional siem deployment modelThis slide covers the traditional in house SIEM model wherein the client take care of all the security incident and event management process on its own. Deliver an outstanding presentation on the topic using this Real Time Analysis Of Security Alerts Traditional Siem Deployment Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
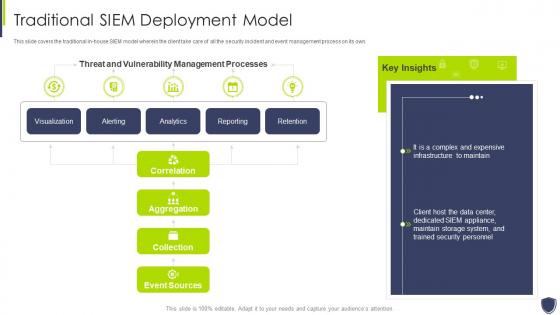 Improve it security with vulnerability management traditional siem deployment model
Improve it security with vulnerability management traditional siem deployment modelThis slide covers the traditional in house SIEM model wherein the client take care of all the security incident and event management process on its own. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Traditional Siem Deployment Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
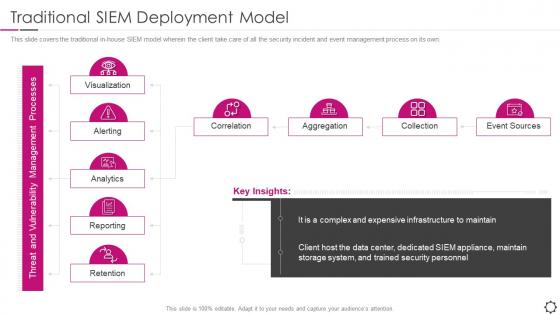 Security information and event management traditional siem deployment
Security information and event management traditional siem deploymentThis slide covers the traditional in house SIEM model wherein the client take care of all the security incident and event management process on its own. Present the topic in a bit more detail with this Security Information And Event Management Traditional SIEM Deployment. Use it as a tool for discussion and navigation on Visualization, Collection, Aggregation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Security Traditional Security In Powerpoint And Google Slides Cpb
Cloud Security Traditional Security In Powerpoint And Google Slides CpbPresenting Cloud Security Traditional Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cloud Security Traditional Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Icon For Traditional Vs Cloud IT Security
Icon For Traditional Vs Cloud IT SecurityPresenting our set of slides with Icon For Traditional Vs Cloud IT Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon Traditional, Cloud It Security .
-
 Icon For Traditional Vs Cloud Analysis It Security
Icon For Traditional Vs Cloud Analysis It SecurityPresenting our set of slides with Icon For Traditional Vs Cloud Analysis It Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon Traditional,Cloud It Security .
-
 Traditional Vs Cloud Information Security Icon
Traditional Vs Cloud Information Security IconPresenting our set of slides with name Traditional Vs Cloud Information Security Icon. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Traditional, Cloud Information Security, Icon.
-
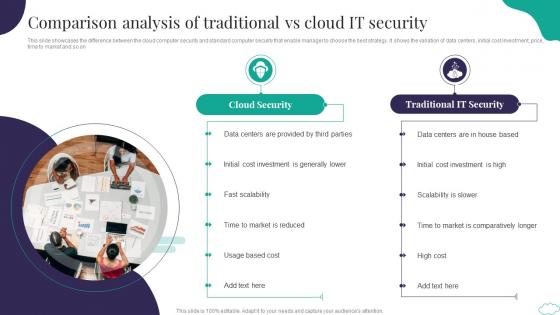 Comparison Analysis Of Traditional Vs Cloud It Security
Comparison Analysis Of Traditional Vs Cloud It SecurityThis slide showcases the difference between the cloud computer security and standard computer security that enable manager to choose the best strategy. It shows the variation of data centers, initial cost investment, price, time to market and so on Introducing our premium set of slides with Comparison Analysis Of Traditional Vs Cloud It Security. Elucidate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Security, Traditional IT Security. So download instantly and tailor it with your information.
-
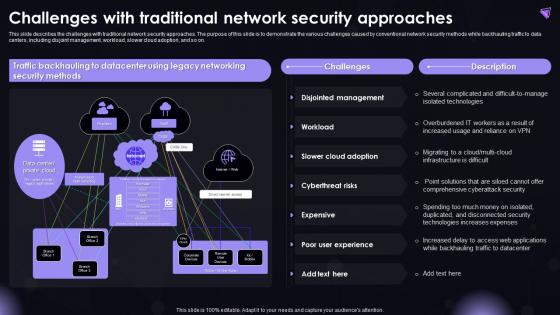 SASE IT Challenges With Traditional Network Security Approaches Ppt Powerpoint Elements
SASE IT Challenges With Traditional Network Security Approaches Ppt Powerpoint ElementsThis slide describes the challenges with traditional network security approaches. The purpose of this slide is to demonstrate the various challenges caused by conventional network security methods while backhauling traffic to data centers, including disjoint management, workload, slower cloud adoption, and so on. Deliver an outstanding presentation on the topic using this SASE IT Challenges With Traditional Network Security Approaches Ppt Powerpoint Elements. Dispense information and present a thorough explanation of Networking Security Methods, Slower Cloud Adoption, Cyberthreat Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparison Traditional Digital Globally Mobile Banking For Convenient And Secure Online Payments Fin SS
Comparison Traditional Digital Globally Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide shows data related to different types of banking users with different age groups. It includes percentage of population uses traditional, digital and mobile banking services. Deliver an outstanding presentation on the topic using this Comparison Traditional Digital Globally Mobile Banking For Convenient And Secure Online Payments Fin SS. Dispense information and present a thorough explanation of Comparison, Traditional, Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 ZTNA Traditional Perimeter Based Network Security Overview And Limitations
ZTNA Traditional Perimeter Based Network Security Overview And LimitationsThis slide represents the overview of traditional perimeter based network security. The purpose of this slide is to showcase the various challenges of conventional perimeter based security and how ZTNA can overcomethose challenges. Increase audience engagement and knowledge by dispensing information using ZTNA Traditional Perimeter Based Network Security Overview And Limitations. This template helps you present information on three stages. You can also present information on Overview, Limitations, Solution using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 ZTNA Traditional Security Models Vs Zero Trust Network Access
ZTNA Traditional Security Models Vs Zero Trust Network AccessThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Deliver an outstanding presentation on the topic using this ZTNA Traditional Security Models Vs Zero Trust Network Access. Dispense information and present a thorough explanation of Traditional Security Model, Static Security, Changing Environment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
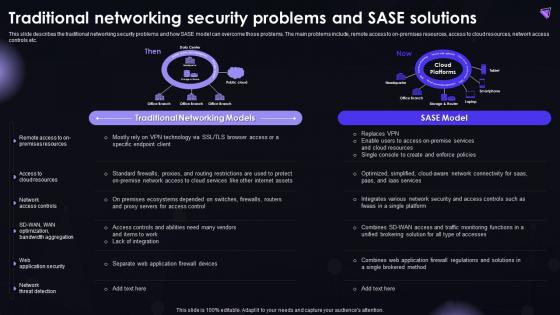 SASE IT Traditional Networking Security Problems And SASE Solutions Ppt Powerpoint Mockup
SASE IT Traditional Networking Security Problems And SASE Solutions Ppt Powerpoint MockupThis slide describes the traditional networking security problems and how SASE model can overcome those problems. The main problems include, remote access to on-premises resources, access to cloud resources, network access controls etc. Deliver an outstanding presentation on the topic using this SASE IT Traditional Networking Security Problems And SASE Solutions Ppt Powerpoint Mockup. Dispense information and present a thorough explanation of Traditional Networking Models, SASE Model, Web Application Security, Network Threat Detection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
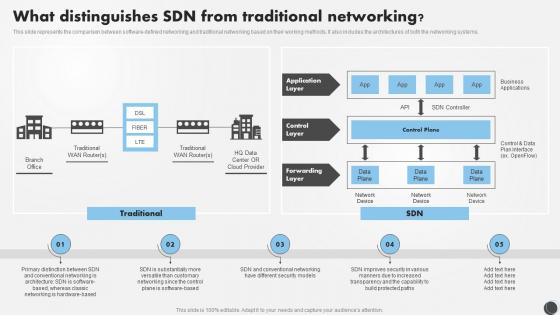 SDN Security IT What Distinguishes SDN From Traditional Networking
SDN Security IT What Distinguishes SDN From Traditional NetworkingThis slide represents the comparison between software defined networking and traditional networking based on their working methods. It also includes the architectures of both the networking systems. Deliver an outstanding presentation on the topic using this SDN Security IT What Distinguishes SDN From Traditional Networking. Dispense information and present a thorough explanation of Traditional, Networking, Distinguishes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
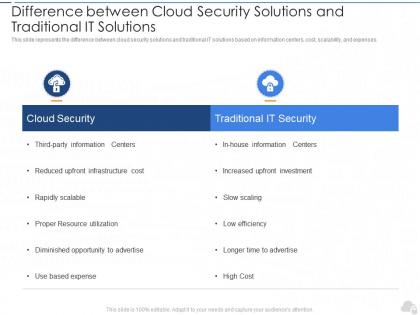 Difference between cloud security solutions and traditional it solutions cloud security it
Difference between cloud security solutions and traditional it solutions cloud security itThis slide represents the difference between cloud security solutions and traditional IT solutions based on information centers, cost, scalability, and expenses.Present the topic in a bit more detail with this Difference Between Cloud Security Solutions And Traditional IT Solutions Cloud Security IT. Use it as a tool for discussion and navigation on Cloud Security, Traditional IT Security, Rapidly Scalable. This template is free to edit as deemed fit for your organization. Therefore download it now.

