Powerpoint Templates and Google slides for User Threat Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS V
Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction, blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS V Dispense information and present a thorough explanation of Introduction To Blockchain, Blockchain Security Risks, Smart Contracts Development using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
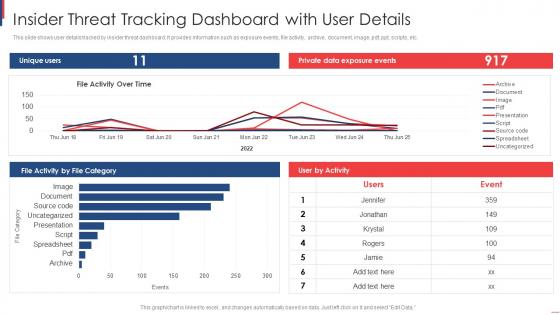 Insider Threat Tracking Dashboard With User Details
Insider Threat Tracking Dashboard With User DetailsThis slide shows user details tracked by insider threat dashboard. It provides information such as exposure events, file activity, archive, document, image, pdf, ppt, scripts, etc. Introducing our Insider Threat Tracking Dashboard With User Details set of slides. The topics discussed in these slides are Insider Threat, Tracking Dashboard, User Details. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
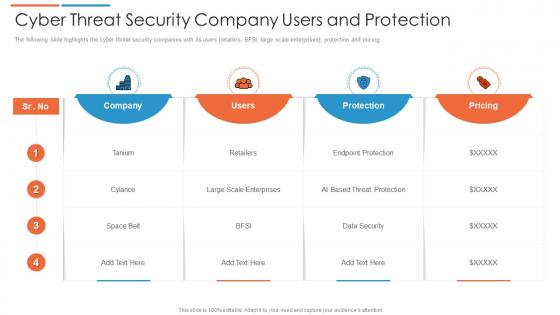 Cyber threat security company users and protection
Cyber threat security company users and protectionThe following slide highlights the cyber threat security companies with its users retailers, BFSI, large scale enterprises, protection and pricing. Introducing our Cyber Threat Security Company Users And Protection set of slides. The topics discussed in these slides are Pricing, Company, Users. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
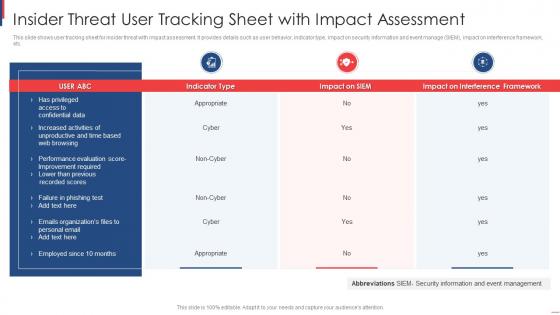 Insider Threat User Tracking Sheet With Impact Assessment
Insider Threat User Tracking Sheet With Impact AssessmentThis slide shows user tracking sheet for insider threat with impact assessment. It provides details such as user behavior, indicator type, impact on security information and event manage SIEM, impact on interference framework, etc. Presenting our well-structured Insider Threat User Tracking Sheet With Impact Assessment. The topics discussed in this slide are Insider Threat, User Tracking Sheet, Impact Assessment. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
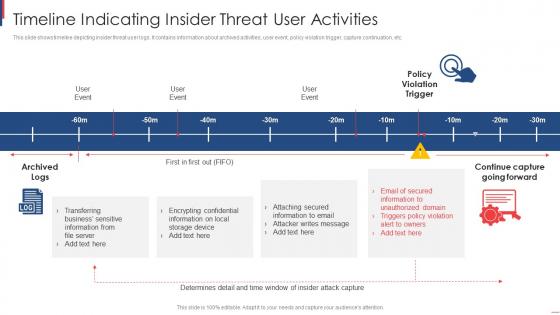 Timeline Indicating Insider Threat User Activities
Timeline Indicating Insider Threat User ActivitiesThis slide shows timeline depicting insider threat user logs. It contains information about archived activities, user event, policy violation trigger, capture continuation, etc. Presenting our set of slides with name Timeline Indicating Insider Threat User Activities. This exhibits information on two stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Timeline Indicating Insider, Threat User Activities.
-
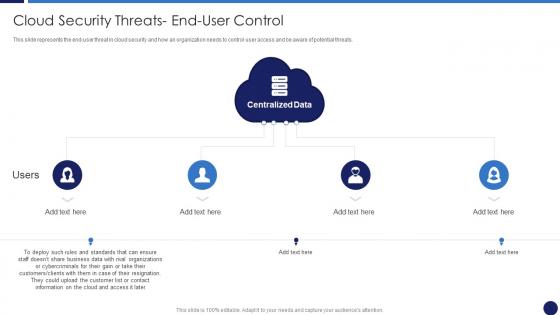 Cloud Security Threats End User Control Cloud Data Protection
Cloud Security Threats End User Control Cloud Data ProtectionThis slide represents the end-user threat in cloud security and how an organization needs to control user access and be aware of potential threats. Introducing Cloud Security Threats End User Control Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Business Data, Customers, Centralized Data, using this template. Grab it now to reap its full benefits.
-
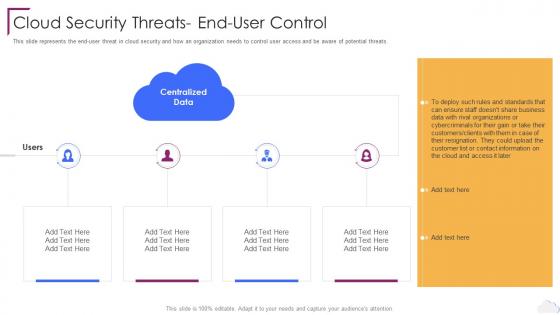 Cloud Security Threats End User Control Cloud Computing Security
Cloud Security Threats End User Control Cloud Computing SecurityThis slide represents the end user threat in cloud security and how an organization needs to control user access and be aware of potential threats. Introducing Cloud Security Threats End User Control Cloud Computing Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Data, Cloud Security Threats, End User Control, using this template. Grab it now to reap its full benefits.
-
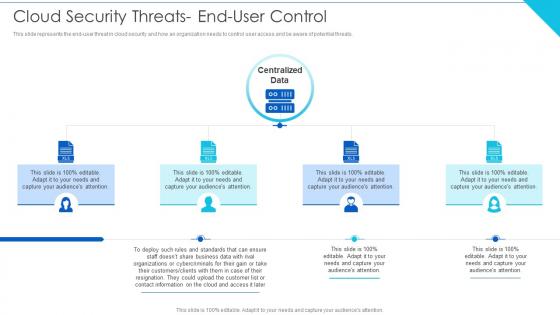 Cloud Security Threats End User Control Cloud Information Security
Cloud Security Threats End User Control Cloud Information SecurityThis slide represents the end user threat in cloud security and how an organization needs to control user access and be aware of potential threats.Introducing Cloud Security Threats End User Control Cloud Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Wisely Considering, Storage Location, Procedures Strategies using this template. Grab it now to reap its full benefits.
-
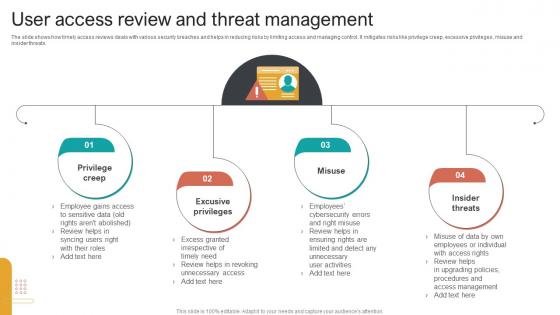 User Access Review And Threat Management
User Access Review And Threat ManagementThe slide shows how timely access reviews deals with various security breaches and helps in reducing risks by limiting access and managing control. It mitigates risks like privilege creep, excessive privileges, misuse and insider threats. Introducing our premium set of slides with User Access Review And Threat Management. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Privilege Creep, Excusive Privileges, Misuse Insider, Threats. So download instantly and tailor it with your information.
-
 Threat entrance threat substitute user interface need recognition
Threat entrance threat substitute user interface need recognitionPresenting this set of slides with name - Threat Entrance Threat Substitute User Interface Need Recognition. This is an editable four graphic that deals with topics like Threat Entrance, Threat Substitute, User Interface, Need Recognition to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cloud security threats end user control cloud security it ppt graphics
Cloud security threats end user control cloud security it ppt graphicsThis slide represents the end-user threat in cloud security and how an organization needs to control user access and be aware of potential threats.Increase audience engagement and knowledge by dispensing information using Cloud Security Threats End user Control Cloud Security IT Ppt Graphics. This template helps you present information on four stages. You can also present information on Organizations Or Cybercriminals, Contact Information, Rules And Standards using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Swot analysis threats case competition declining user base telecom company ppt tips
Swot analysis threats case competition declining user base telecom company ppt tipsThe slide shows the key threats which might affect the companys operations in future. Major points include competitive market, government policies, declining ARPU etc. Introducing Swot Analysis Threats Case Competition Declining User Base Telecom Company Ppt Tips to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Government Policies, Average Revenue, using this template. Grab it now to reap its full benefits.

